Powerpoint Templates and Google slides for Phishing Techniques Misused For Cyber Assault
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Phishing As A Social Engineering Technique Training Ppt
Phishing As A Social Engineering Technique Training PptPresenting Phishing as a Social Engineering Technique. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
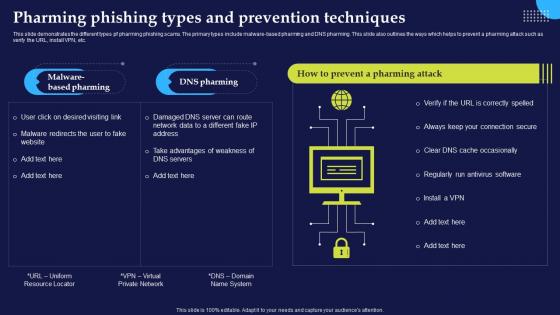 Phishing Attacks And Strategies To Mitigate Them V2 Pharming Phishing Types And Prevention Techniques
Phishing Attacks And Strategies To Mitigate Them V2 Pharming Phishing Types And Prevention TechniquesThis slide demonstrates the different types pf pharming phishing scams. The primary types include malware-based pharming and DNS pharming. This slide also outlines the ways which helps to prevent a pharming attack such as verify the URL, install VPN, etc. Deliver an outstanding presentation on the topic using this Phishing Attacks And Strategies To Mitigate Them V2 Pharming Phishing Types And Prevention Techniques. Dispense information and present a thorough explanation of Pharming Phishing Scams, Malware Based Pharming, Pharming Attack, Prevention Techniques using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Phishing Attacks And Strategies To Mitigate Them V2 Primary Techniques Employed In Phishing Attacks
Phishing Attacks And Strategies To Mitigate Them V2 Primary Techniques Employed In Phishing AttacksThis slide demonstrates the ways utilized by phishers to attack victims. The purpose of this slide is to outline the different methods used by attackers to trick victims. The primary means of attacks are text messages, emails and phone calls from unknown sources. Increase audience engagement and knowledge by dispensing information using Phishing Attacks And Strategies To Mitigate Them V2 Primary Techniques Employed In Phishing Attacks. This template helps you present information on three stages. You can also present information on Primary Techniques Employed, Phishing Attacks, Phishers To Attack Victims, Attackers To Trick Victims using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
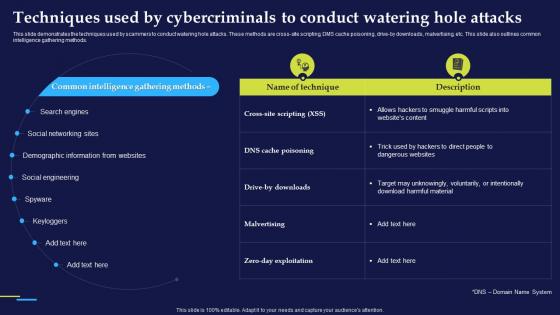 Phishing Attacks And Strategies To Mitigate Them V2 Techniques Used By Cybercriminals To Conduct
Phishing Attacks And Strategies To Mitigate Them V2 Techniques Used By Cybercriminals To ConductThis slide demonstrates the techniques used by scammers to conduct watering hole attacks. These methods are cross-site scripting, DMS cache poisoning, drive-by downloads, malvertising, etc. This slide also outlines common intelligence gathering methods. Present the topic in a bit more detail with this Phishing Attacks And Strategies To Mitigate Them V2 Techniques Used By Cybercriminals To Conduct. Use it as a tool for discussion and navigation on Social Networking Sites, Demographic Information From Websites, Social Engineering, Keyloggers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
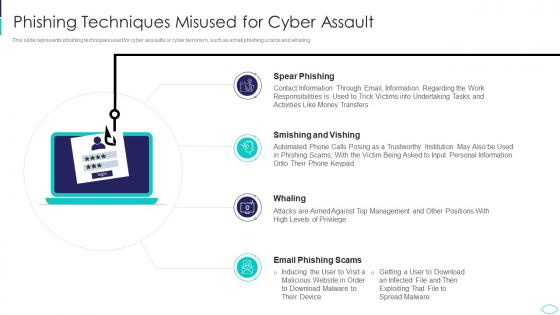 Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks
Phishing Techniques Misused For Cyber Assault Cyber Terrorism AttacksThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Introducing Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Techniques Misused For Cyber Assault, using this template. Grab it now to reap its full benefits.
-
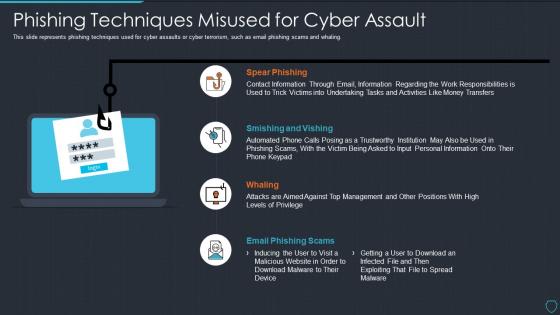 Cyberterrorism it phishing techniques misused for cyber assault
Cyberterrorism it phishing techniques misused for cyber assaultThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Phishing Techniques Misused For Cyber Assault. This template helps you present information on four stages. You can also present information on Spear Phishing, Smishing And Vishing, Whaling, Email Phishing Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Techniques In Phishing Awareness Training Program
Key Techniques In Phishing Awareness Training ProgramThis slide covers strategies to consider in phishing awareness training program. It involves strategies such as verify email address, consider every email as phishing attempt and update security software. Presenting our set of slides with name Key Techniques In Phishing Awareness Training Program. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Key Techniques, Phishing, Awareness Training Program.
-
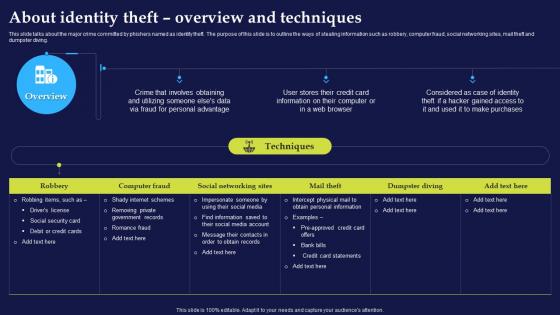 About Identity Theft Overview And Techniques Phishing Attacks And Strategies
About Identity Theft Overview And Techniques Phishing Attacks And StrategiesThis slide talks about the major crime committed by phishers named as identity theft. The purpose of this slide is to outline the ways of stealing information such as robbery, computer fraud, social networking sites, mail theft and dumpster diving.Deliver an outstanding presentation on the topic using this About Identity Theft Overview And Techniques Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Personal Advantage, Romance Fraud, Social Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Primary Techniques Employed In Phishing Attacks And Strategies
Primary Techniques Employed In Phishing Attacks And StrategiesThis slide demonstrates the ways utilized by phishers to attack victims. The purpose of this slide is to outline the different methods used by attackers to trick victims. The primary means of attacks are text messages, emails and phone calls from unknown sources.Increase audience engagement and knowledge by dispensing information using Primary Techniques Employed In Phishing Attacks And Strategies. This template helps you present information on five stages. You can also present information on Malicious Websites, Victims Receive, Personal Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
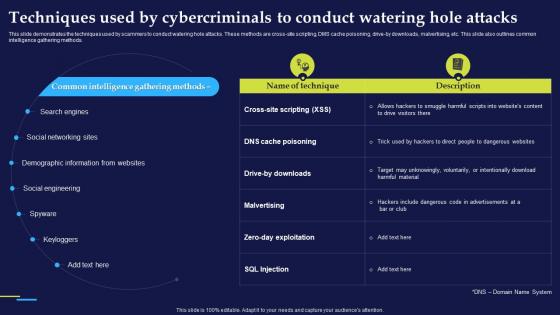 Techniques Used By Cybercriminals To Conduct Phishing Attacks And Strategies
Techniques Used By Cybercriminals To Conduct Phishing Attacks And StrategiesThis slide demonstrates the techniques used by scammers to conduct watering hole attacks. These methods are cross site scripting, DMS cache poisoning, drive by downloads, malvertising, etc. This slide also outlines common intelligence gathering methods.Deliver an outstanding presentation on the topic using this Techniques Used By Cybercriminals To Conduct Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Demographic Information, Social Engineering, Include Dangerous using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
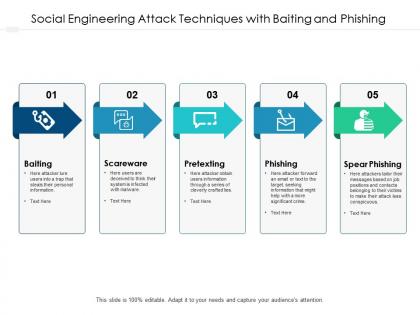 Social engineering attack techniques with baiting and phishing
Social engineering attack techniques with baiting and phishingPresenting this set of slides with name Social Engineering Attack Techniques With Baiting And Phishing. This is a five process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Types phishing techniques ppt powerpoint presentation show guidelines cpb
Types phishing techniques ppt powerpoint presentation show guidelines cpbPresenting this set of slides with name Types Phishing Techniques Ppt Powerpoint Presentation Show Guidelines Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Types Phishing Techniques to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

