Powerpoint Templates and Google slides for Privacy And Confidentiality
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cloud Storage Encryption Introduction And Features Encryption For Data Privacy In Digital Age It
Cloud Storage Encryption Introduction And Features Encryption For Data Privacy In Digital Age ItThis slide demonstrates the importance of encrypting data before storing or sending it to the cloud. This slide also outlines the features and benefits of cloud encryption such as collaboration, security, scalability, access control, confidentiality, etc. Deliver an outstanding presentation on the topic using this Cloud Storage Encryption Introduction And Features Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Introduction, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
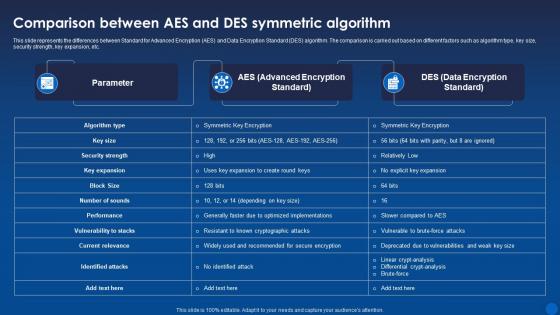 Comparison Aes And Des Symmetric Algorithm Encryption For Data Privacy In Digital Age It
Comparison Aes And Des Symmetric Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the differences between Standard for Advanced Encryption AES and Data Encryption Standard DES algorithm. The comparison is carried out based on different factors such as algorithm type, key size, security strength, key expansion, etc. Deliver an outstanding presentation on the topic using this Comparison Aes And Des Symmetric Algorithm Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Comparison, Key Expansion, Symmetric Algorithm using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
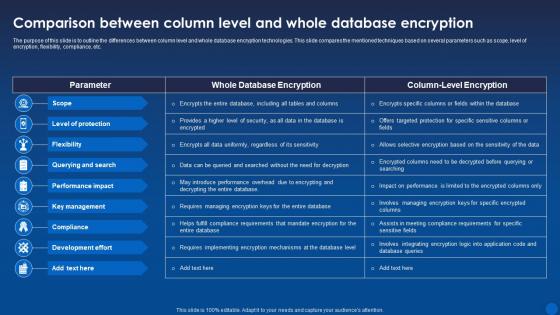 Comparison Between Column Level And Whole Database Encryption For Data Privacy In Digital Age It
Comparison Between Column Level And Whole Database Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the differences between column level and whole database encryption technologies. This slide compares the mentioned techniques based on several parameters such as scope, level of encryption, flexibility, compliance, etc. Present the topic in a bit more detail with this Comparison Between Column Level And Whole Database Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Comparison, Database, Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
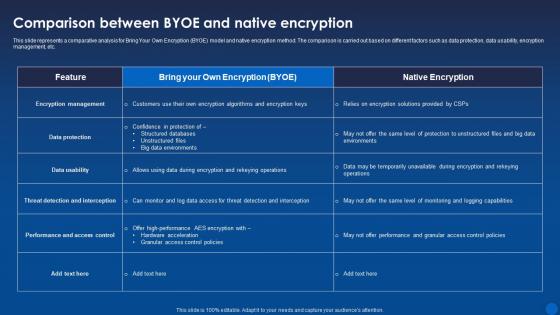 Comparison Byoe And Native Encryption Encryption For Data Privacy In Digital Age It
Comparison Byoe And Native Encryption Encryption For Data Privacy In Digital Age ItThis slide represents a comparative analysis for Bring Your Own Encryption BYOE model and native encryption method. The comparison is carried out based on different factors such as data protection, data usability, encryption management, etc. Deliver an outstanding presentation on the topic using this Comparison Byoe And Native Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Comparison, Comparative, Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
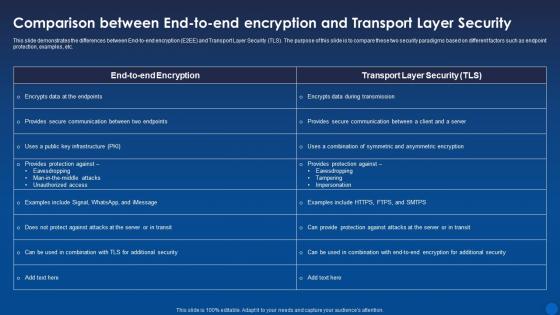 Comparison End To End Encryption And Transport Layer Encryption For Data Privacy In Digital Age It
Comparison End To End Encryption And Transport Layer Encryption For Data Privacy In Digital Age ItThis slide demonstrates the differences between End-to-end encryption E2EE and Transport Layer Security TLS. The purpose of this slide is to compare these two security paradigms based on different factors such as endpoint protection, examples, etc. Present the topic in a bit more detail with this Comparison End To End Encryption And Transport Layer Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Comparison, Protection, Demonstrates. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
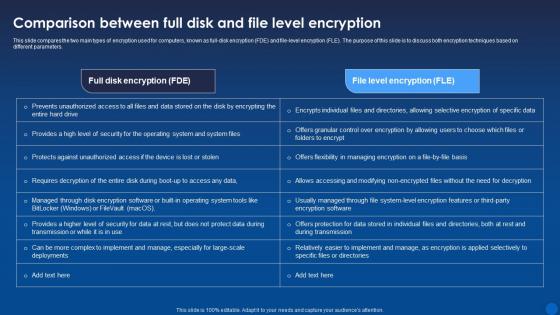 Comparison Full Disk And File Level Encryption Encryption For Data Privacy In Digital Age It
Comparison Full Disk And File Level Encryption Encryption For Data Privacy In Digital Age ItThis slide compares the two main types of encryption used for computers, known as full-disk encryption FDE and file-level encryption FLE. The purpose of this slide is to discuss both encryption techniques based on different parameters. Present the topic in a bit more detail with this Comparison Full Disk And File Level Encryption Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Comparison, Encryption, Techniques. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
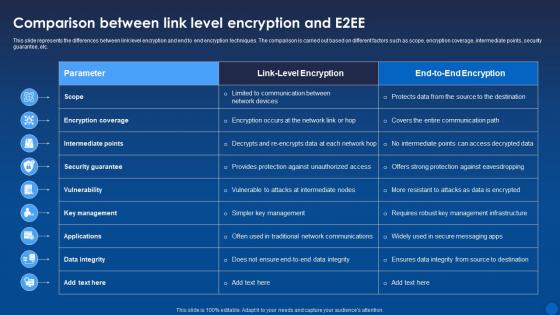 Comparison Link Level Encryption And E2ee Encryption For Data Privacy In Digital Age It
Comparison Link Level Encryption And E2ee Encryption For Data Privacy In Digital Age ItThis slide represents the differences between link level encryption and end to end encryption techniques. The comparison is carried out based on different factors such as scope, encryption coverage, intermediate points, security guarantee, etc. Deliver an outstanding presentation on the topic using this Comparison Link Level Encryption And E2ee Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Comparison, Encryption, Intermediate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
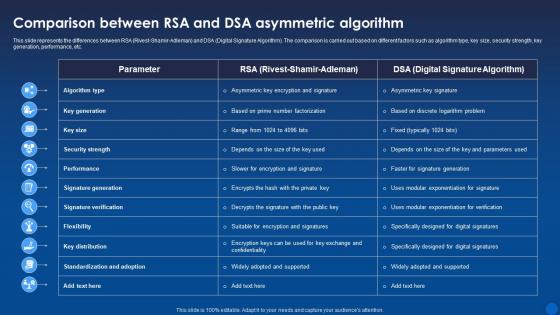 Comparison Rsa And Dsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age It
Comparison Rsa And Dsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age ItThis slide represents the differences between RSA Rivest-Shamir-Adleman and DSA Digital Signature Algorithm. The comparison is carried out based on different factors such as algorithm type, key size, security strength, key generation, performance, etc. Present the topic in a bit more detail with this Comparison Rsa And Dsa Asymmetric Algorithm Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric Algorithm, Comparison, Performance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
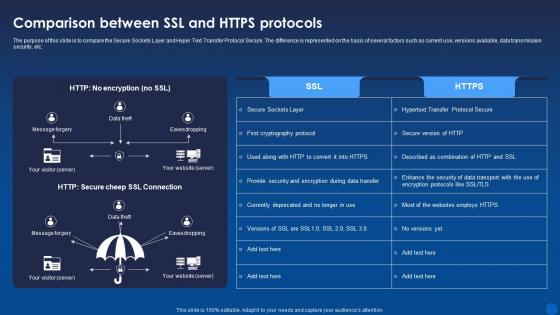 Comparison Ssl And Https Protocols Encryption For Data Privacy In Digital Age It
Comparison Ssl And Https Protocols Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to compare the Secure Sockets Layer and Hyper Text Transfer Protocol Secure. The difference is represented on the basis of several factors such as current use, versions available, data transmission security, etc. Deliver an outstanding presentation on the topic using this Comparison Ssl And Https Protocols Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Comparison, Encryption, Data Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
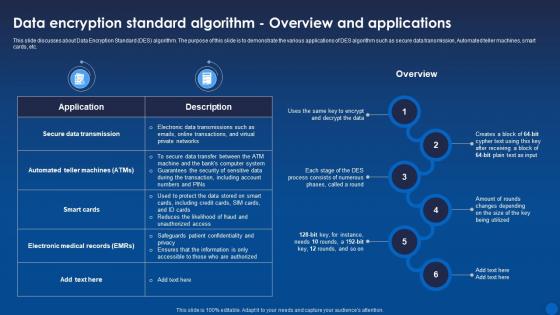 Data Standard Algorithm Overview And Applications Encryption For Data Privacy In Digital Age It
Data Standard Algorithm Overview And Applications Encryption For Data Privacy In Digital Age ItThis slide discusses about Data Encryption Standard DES algorithm. The purpose of this slide is to demonstrate the various applications of DES algorithm such as secure data transmission, Automated teller machines, smart cards, etc. Present the topic in a bit more detail with this Data Standard Algorithm Overview And Applications Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Overview, Applications, Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
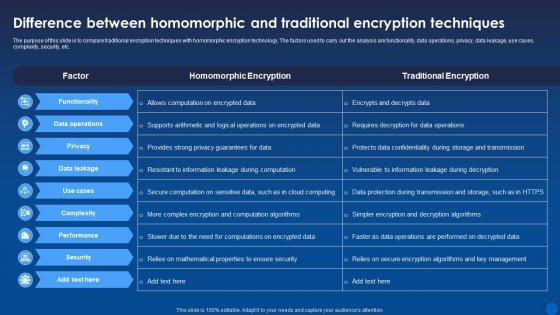 Difference And Traditional Encryption Techniques Encryption For Data Privacy In Digital Age It
Difference And Traditional Encryption Techniques Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to compare traditional encryption techniques with homomorphic encryption technology. The factors used to carry out the analysis are functionality, data operations, privacy, data leakage, use cases, complexity, security, etc. Deliver an outstanding presentation on the topic using this Difference And Traditional Encryption Techniques Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Homomorphic, Encryption, Techniques using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
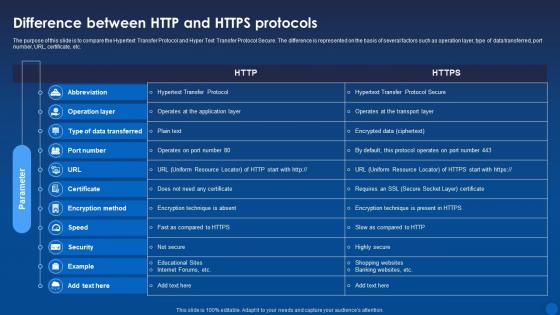 Difference Between Http And Https Protocols Encryption For Data Privacy In Digital Age It
Difference Between Http And Https Protocols Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to compare the Hypertext Transfer Protocol and Hyper Text Transfer Protocol Secure. The difference is represented on the basis of several factors such as operation layer, type of data transferred, port number, URL, certificate, etc. Present the topic in a bit more detail with this Difference Between Http And Https Protocols Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Transfer Protocol, Operation, Data Transferred. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
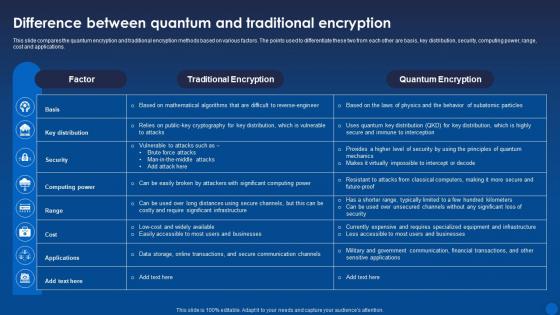 Difference Quantum And Traditional Encryption Encryption For Data Privacy In Digital Age It
Difference Quantum And Traditional Encryption Encryption For Data Privacy In Digital Age ItThis slide compares the quantum encryption and traditional encryption methods based on various factors. The points used to differentiate these two from each other are basis, key distribution, security, computing power, range, cost and applications. Deliver an outstanding presentation on the topic using this Difference Quantum And Traditional Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Traditional Encryption, Quantum Encryption, Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
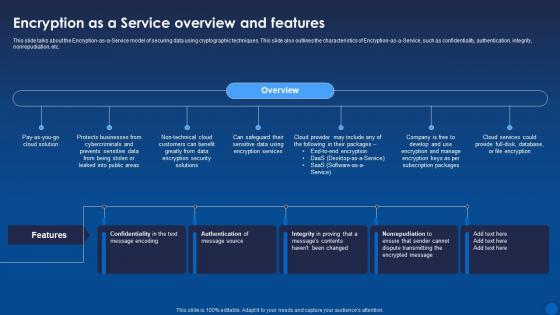 Encryption As A Service Overview And Features Encryption For Data Privacy In Digital Age It
Encryption As A Service Overview And Features Encryption For Data Privacy In Digital Age ItThis slide talks about the Encryption-as-a-Service model of securing data using cryptographic techniques. This slide also outlines the characteristics of Encryption-as-a-Service, such as confidentiality, authentication, integrity, nonrepudiation, etc. Deliver an outstanding presentation on the topic using this Encryption As A Service Overview And Features Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Service, Overview, Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
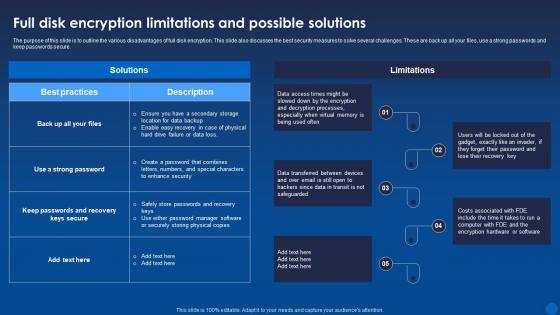 Full Disk Encryption Limitations And Possible Solutions Encryption For Data Privacy In Digital Age It
Full Disk Encryption Limitations And Possible Solutions Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the various disadvantages of full disk encryption. This slide also discusses the best security measures to solve several challenges. These are back up all your files, use a strong passwords and keep passwords secure. Present the topic in a bit more detail with this Full Disk Encryption Limitations And Possible Solutions Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Limitations, Safeguarded. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
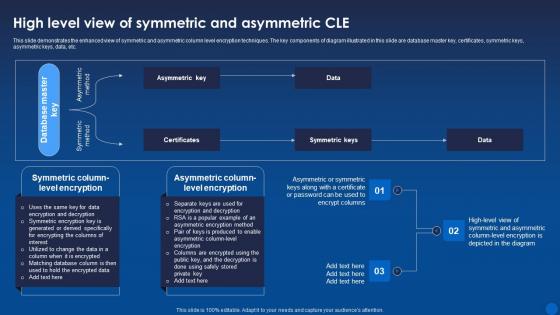 High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age It
High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age ItThis slide demonstrates the enhanced view of symmetric and asymmetric column level encryption techniques. The key components of diagram illustrated in this slide are database master key, certificates, symmetric keys, asymmetric keys, data, etc. Deliver an outstanding presentation on the topic using this High Level View Of Symmetric And Asymmetric Cle Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Symmetric, Asymmetric, Certificates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
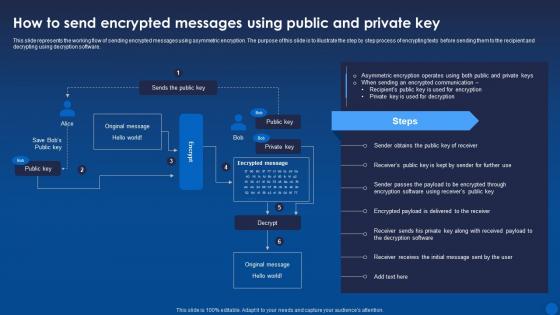 How To Messages Using Public And Private Key Encryption For Data Privacy In Digital Age It
How To Messages Using Public And Private Key Encryption For Data Privacy In Digital Age ItThis slide represents the working flow of sending encrypted messages using asymmetric encryption. The purpose of this slide is to illustrate the step by step process of encrypting texts before sending them to the recipient and decrypting using decryption software. Present the topic in a bit more detail with this How To Messages Using Public And Private Key Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric, ncryption, Communication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
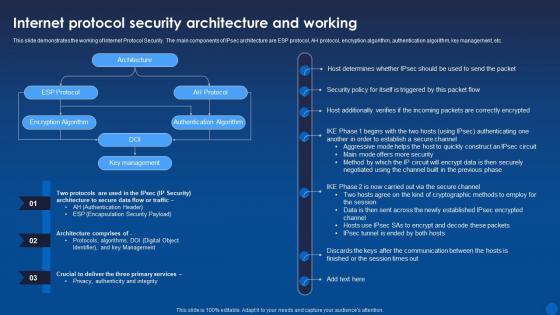 Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It
Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age ItThis slide demonstrates the working of Internet Protocol Security. The main components of IPsec architecture are ESP protocol, AH protocol, encryption algorithm, authentication algorithm, key management, etc. Present the topic in a bit more detail with this Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Protocol Security, Architecture, Encryption Algorithm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
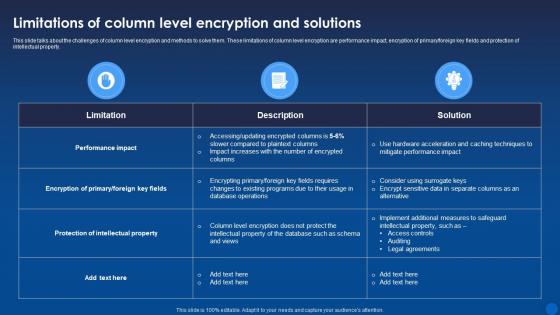 Limitations Of Column Level Encryption And Solutions Encryption For Data Privacy In Digital Age It
Limitations Of Column Level Encryption And Solutions Encryption For Data Privacy In Digital Age ItThis slide talks about the challenges of column level encryption and methods to solve them. These limitations of column level encryption are performance impact, encryption of primary or foreign key fields and protection of intellectual property. Present the topic in a bit more detail with this Limitations Of Column Level Encryption And Solutions Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Limitations, Level Encryption, Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
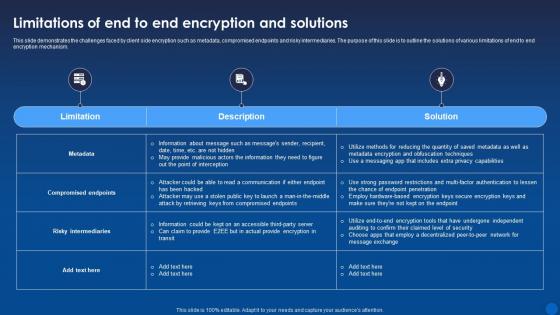 Limitations Of End To End Encryption And Solutions Encryption For Data Privacy In Digital Age It
Limitations Of End To End Encryption And Solutions Encryption For Data Privacy In Digital Age ItThis slide demonstrates the challenges faced by client side encryption such as metadata, compromised endpoints and risky intermediaries. The purpose of this slide is to outline the solutions of various limitations of end to end encryption mechanism. Deliver an outstanding presentation on the topic using this Limitations Of End To End Encryption And Solutions Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Solutions, Limitations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age It
Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age ItThis slide talks about the challenges of Hypertext Transfer Protocol Secure HTTPS and their possible solutions. These challenges are lack of end-to-end encryption, certificate authority vulnerabilities, difficulty in detecting malicious content, and complexity and cost of certificate management. Present the topic in a bit more detail with this Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Limitations, Solutions, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
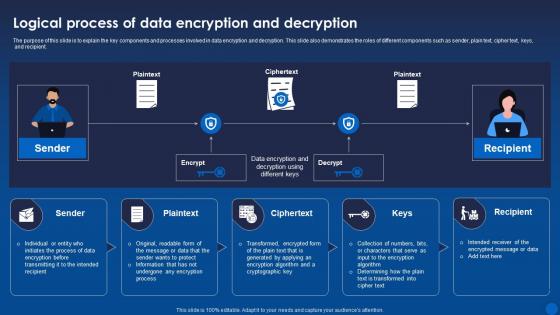 Logical Process Of Data Encryption And Decryption Encryption For Data Privacy In Digital Age It
Logical Process Of Data Encryption And Decryption Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the key components and processes involved in data encryption and decryption. This slide also demonstrates the roles of different components such as sender, plain text, cipher text, keys, and recipient. Deliver an outstanding presentation on the topic using this Logical Process Of Data Encryption And Decryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Decryption, Data Encryption, Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
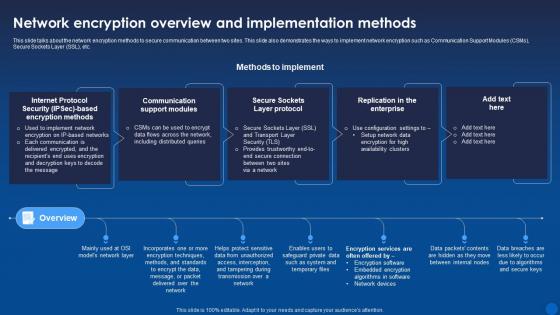 Network Encryption Overview And Implementation Methods Encryption For Data Privacy In Digital Age It
Network Encryption Overview And Implementation Methods Encryption For Data Privacy In Digital Age ItThis slide talks about the network encryption methods to secure communication between two sites. This slide also demonstrates the ways to implement network encryption such as Communication Support Modules CSMs, Secure Sockets Layer SSL, etc. Deliver an outstanding presentation on the topic using this Network Encryption Overview And Implementation Methods Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Overview, Implementation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
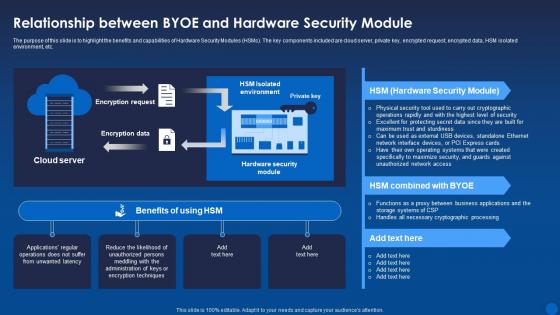 Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It
Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to highlight the benefits and capabilities of Hardware Security Modules HSMs. The key components included are cloud server, private key, encrypted request, encrypted data, HSM isolated environment, etc. Deliver an outstanding presentation on the topic using this Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Relationship, Hardware, Cryptographic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
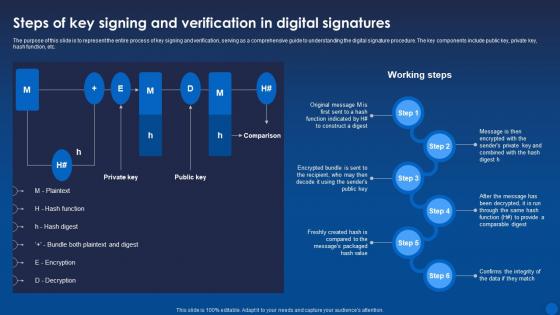 Steps Of Key Signing And Verification In Digital Signatures Encryption For Data Privacy In Digital Age It
Steps Of Key Signing And Verification In Digital Signatures Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to represent the entire process of key signing and verification, serving as a comprehensive guide to understanding the digital signature procedure. The key components include public key, private key, hash function, etc. Present the topic in a bit more detail with this Steps Of Key Signing And Verification In Digital Signatures Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Verification, Comparable, Procedure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
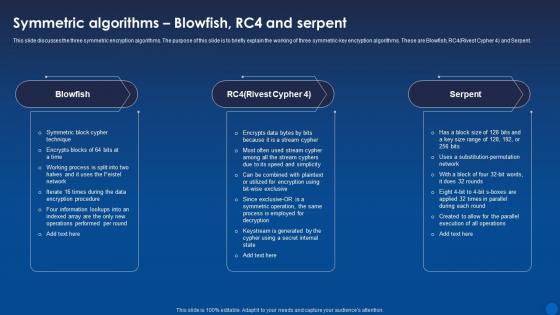 Symmetric Blowfish Rc4 And Serpent Encryption For Data Privacy In Digital Age It
Symmetric Blowfish Rc4 And Serpent Encryption For Data Privacy In Digital Age ItThis slide discusses the three symmetric encryption algorithms. The purpose of this slide is to briefly explain the working of three symmetric-key encryption algorithms. These are Blowfish RC4 Rivest Cypher 4 and Serpent. Introducing Symmetric Blowfish, Rc4 And Serpent Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric, Algorithms, Encryption, using this template. Grab it now to reap its full benefits.
-
 Privacy Health Information In Powerpoint And Google Slides Cpb
Privacy Health Information In Powerpoint And Google Slides CpbPresenting our Privacy Health Information In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Privacy Health Information This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
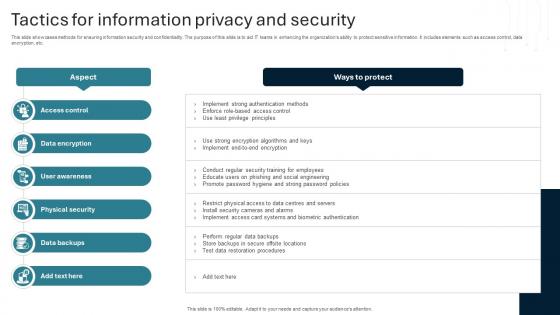 Tactics For Information Privacy And Security
Tactics For Information Privacy And SecurityThis slide showcases methods for ensuring information security and confidentiality. The purpose of this slide is to aid IT teams in enhancing the organizations ability to protect sensitive information. It includes elements such as access control, data encryption, etc. Introducing our premium set of slides with Tactics For Information Privacy And Security. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strong Password Policies, Test Data Restoration Procedures. So download instantly and tailor it with your information.
-
 Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SS
Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SSThis slide covers essential guidance on safeguarding blockchain data to ensure integrity and confidentiality such as keeping private key confidential, utilizing VPN, use of link checker, opting for trusted crypto wallets. Introducing Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SS to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Private Key Confidential, Security, Blockchain, Prevent Phishing Attacks, using this template. Grab it now to reap its full benefits.
-
 Additional Privacy And Security Techniques Comprehensive Approach To Privacy BCT SS
Additional Privacy And Security Techniques Comprehensive Approach To Privacy BCT SSThis slide covers methodologies to safeguard confidential information within blockchain system through techniques such as mixing, group signature, attribute based encryption, secure multi-party computation, etc with applications. Present the topic in a bit more detail with this Additional Privacy And Security Techniques Comprehensive Approach To Privacy BCT SS. Use it as a tool for discussion and navigation on Group Signature, Mixing, Attribute-Based Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
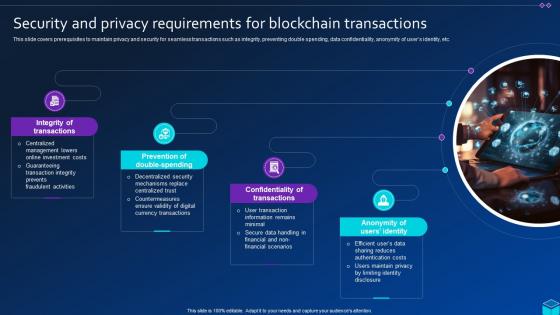 Security And Privacy Requirements For Blockchain Comprehensive Approach To Privacy BCT SS
Security And Privacy Requirements For Blockchain Comprehensive Approach To Privacy BCT SSThis slide covers prerequisites to maintain privacy and security for seamless transactions such as integrity, preventing double spending, data confidentiality, anonymity of users identity, etc. Increase audience engagement and knowledge by dispensing information using Security And Privacy Requirements For Blockchain Comprehensive Approach To Privacy BCT SS. This template helps you present information on four stages. You can also present information on Prevention Of Double-Spending, Confidentiality Of Transactions, Anonymity Of Users Identity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Importance Data Privacy Healthcare In Powerpoint And Google Slides Cpb
Importance Data Privacy Healthcare In Powerpoint And Google Slides CpbPresenting our Importance Data Privacy Healthcare In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Importance Data Privacy Healthcare This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
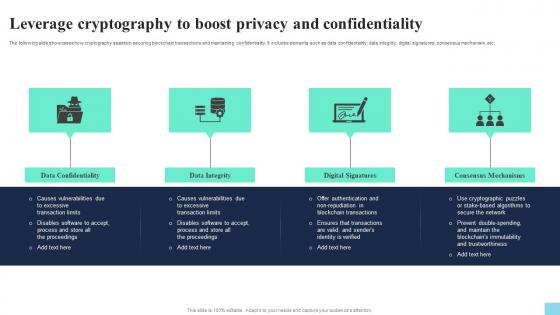 Leverage Cryptography To Boost Privacy And Confidentiality Hands On Blockchain Security Risk BCT SS V
Leverage Cryptography To Boost Privacy And Confidentiality Hands On Blockchain Security Risk BCT SS VThe following slide showcases how cryptography assists in securing blockchain transactions and maintaining confidentiality. It includes elements such as data confidentiality, data integrity, digital signatures, consensus mechanism, etc. Introducing Leverage Cryptography To Boost Privacy And Confidentiality Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Confidentiality, Data Integrity, Digital Signatures, using this template. Grab it now to reap its full benefits.
-
 Crypto Wallets Types And Applications Data Theft And Financial Fraud Privacy Concerns
Crypto Wallets Types And Applications Data Theft And Financial Fraud Privacy ConcernsThis slide represents the data theft and financial fraud happening in the crypto world. The purpose of this slide is to highlight the concerns such as lack of rules, exposure of data, uncertainty existing because of data rules, etc. Introducing Crypto Wallets Types And Applications Data Theft And Financial Fraud Privacy Concerns to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Financial Fraud Happening, Lack Of Rules, Exposure Of Data, Financial Fraud Privacy Concerns, using this template. Grab it now to reap its full benefits.
-
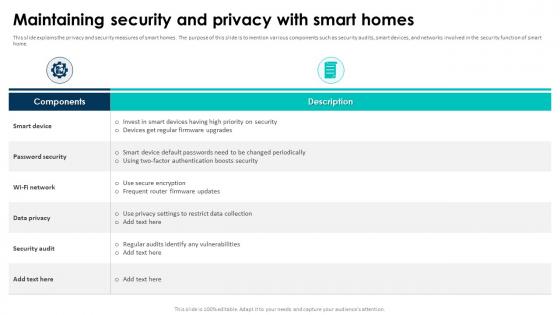 Elevating Living Spaces With Smart Maintaining Security And Privacy With Smart Homes
Elevating Living Spaces With Smart Maintaining Security And Privacy With Smart HomesThis slide explains the privacy and security measures of smart homes. The purpose of this slide is to mention various components such as security audits, smart devices, and networks involved in the security function of smart home. Deliver an outstanding presentation on the topic using this Elevating Living Spaces With Smart Maintaining Security And Privacy With Smart Homes. Dispense information and present a thorough explanation of Password Security, Data Privacy, Security Audit, High Priority On Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Security And Privacy Challenges Faced Transforming Future Of Gaming IoT SS
Impact Of Security And Privacy Challenges Faced Transforming Future Of Gaming IoT SSThe following slide showcases consequences of various security and privacy challenges faced by gaming companies. The slide covers information about misuse of personal information, data leakage, privacy violations, data theft, and access to unauthorized data. Introducing Impact Of Security And Privacy Challenges Faced Transforming Future Of Gaming IoT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Violations, Location Data, Data Theft, using this template. Grab it now to reap its full benefits.
-
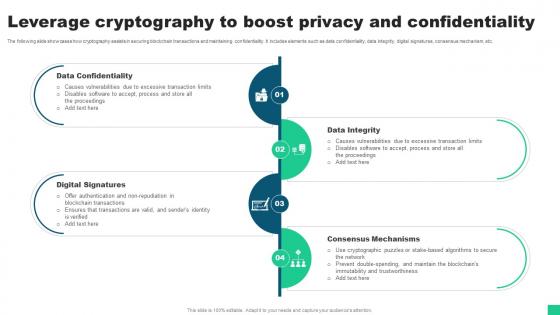 Leverage Cryptography To Boost Privacy And Confidentiality Guide For Blockchain BCT SS V
Leverage Cryptography To Boost Privacy And Confidentiality Guide For Blockchain BCT SS VThe following slide showcases how cryptography assists in securing blockchain transactions and maintaining confidentiality. It includes elements such as data confidentiality, data integrity, digital signatures, consensus mechanism, etc. Introducing Leverage Cryptography To Boost Privacy And Confidentiality Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Confidentiality, Digital Signatures, Data Integrity using this template. Grab it now to reap its full benefits.
-
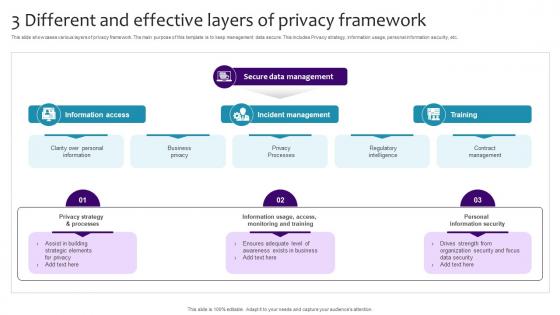 3 Different And Effective Layers Of Privacy Framework
3 Different And Effective Layers Of Privacy FrameworkThis slide showcases various layers of privacy framework. The main purpose of this template is to keep management data secure. This includes Privacy strategy, information usage, personal information security, etc.Presenting our set of slides with 3 Different And Effective Layers Of Privacy Framework. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Access, Incident Management, Ensures Adequate Level.
-
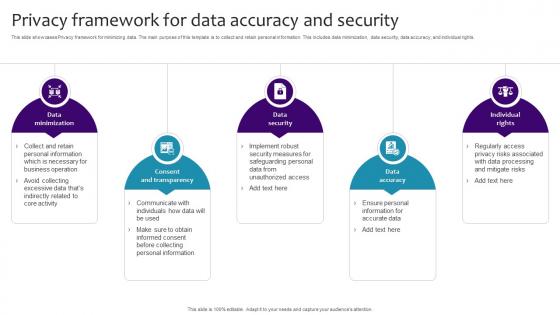 Privacy Framework For Data Accuracy And Security
Privacy Framework For Data Accuracy And SecurityThis slide showcases Privacy framework for minimizing data. The main purpose of this template is to collect and retain personal information. This includes data minimization, data security, data accuracy, and individual rights.Introducing our premium set of slides with Privacy Framework For Data Accuracy And Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Minimization, Consent Transparency, Data Accuracy. So download instantly and tailor it with your information.
-
 Agenda IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS
Agenda IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SSIntroducing Agenda IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Agenda, using this template. Grab it now to reap its full benefits.
-
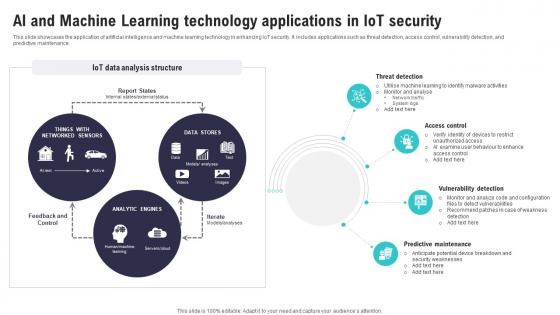 Ai And Machine Learning Technology IoT Security And Privacy Safeguarding IoT SS
Ai And Machine Learning Technology IoT Security And Privacy Safeguarding IoT SSThis slide showcases the application of artificial intelligence and machine learning technology in enhancing IoT security. It includes applications such as threat detection, access control, vulnerability detection, and predictive maintenance. Deliver an outstanding presentation on the topic using this Ai And Machine Learning Technology IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Threat Detection, Access Control, Vulnerability Detection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Automated Patch Management To Increase IoT Security And Privacy Safeguarding IoT SS
Automated Patch Management To Increase IoT Security And Privacy Safeguarding IoT SSThis slide includes an automated patch management process that ensures patch availability on devices in accordance with deployment policies. It includes steps such as scan for missing patches, collect patches from vendors, deploy patches, and report results. Introducing Automated Patch Management To Increase IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Deploy Patches, Report Results, Management Process, using this template. Grab it now to reap its full benefits.
-
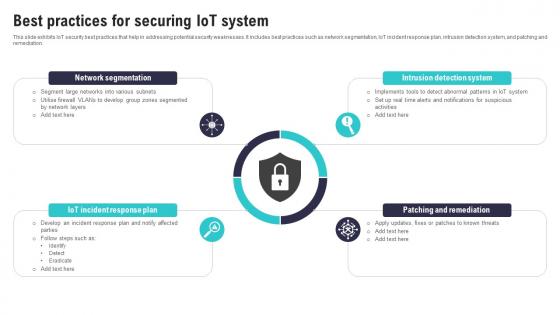 Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SS
Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SSThis slide exhibits IoT security best practices that help in addressing potential security weaknesses. It includes best practices such as network segmentation, IoT incident response plan, intrusion detection system, and patching and remediation. Increase audience engagement and knowledge by dispensing information using Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on four stages. You can also present information on Network Segmentation, Intrusion Detection System, Patching Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
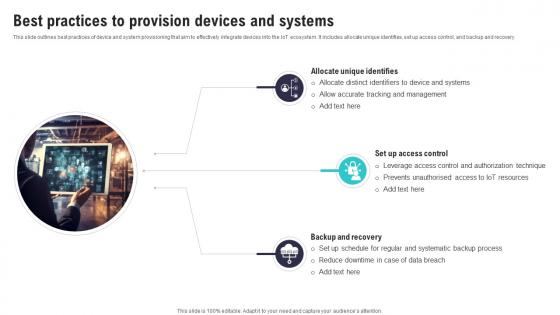 Best Practices To Provision Devices And Systems IoT Security And Privacy Safeguarding IoT SS
Best Practices To Provision Devices And Systems IoT Security And Privacy Safeguarding IoT SSThis slide outlines best practices of device and system provisioning that aim to effectively integrate devices into the IoT ecosystem. It includes allocate unique identifies, set up access control, and backup and recovery. Introducing Best Practices To Provision Devices And Systems IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Unique Identifies, Systematic Backup Process, Reduce Downtime, using this template. Grab it now to reap its full benefits.
-
 Blockchain Approaches To Enhance IoT Data Security IoT Security And Privacy Safeguarding IoT SS
Blockchain Approaches To Enhance IoT Data Security IoT Security And Privacy Safeguarding IoT SSThis slide encompasses blockchain technical applications to the IoT ecosystem aimed at enhancing data privacy and security. It includes decentralized system, an immutable ledger, and smart contracts. Increase audience engagement and knowledge by dispensing information using Blockchain Approaches To Enhance IoT Data Security IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on three stages. You can also present information on Decentralized System, Immutable Ledger, Smart Contracts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
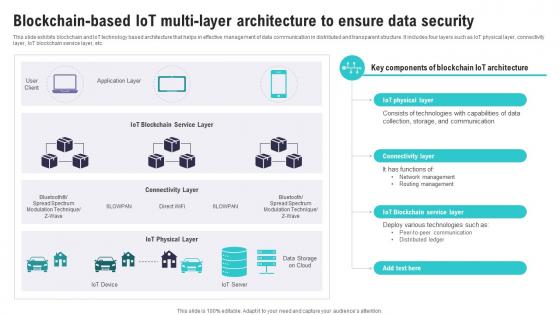 Blockchain Based IoT Multi Layer Architecture IoT Security And Privacy Safeguarding IoT SS
Blockchain Based IoT Multi Layer Architecture IoT Security And Privacy Safeguarding IoT SSThis slide exhibits blockchain and IoT technology based architecture that helps in effective management of data communication in distributed and transparent structure. It includes four layers such as IoT physical layer, connectivity layer, IoT blockchain service layer, etc. Present the topic in a bit more detail with this Blockchain Based IoT Multi Layer Architecture IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Storage Communication, Network Management, Routing Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
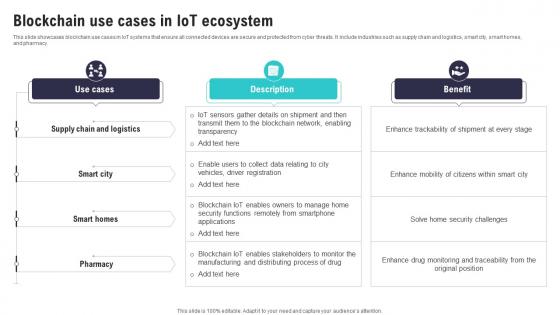 Blockchain Use Cases In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SS
Blockchain Use Cases In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SSThis slide showcases blockchain use cases in IoT systems that ensure all connected devices are secure and protected from cyber threats. It include industries such as supply chain and logistics, smart city, smart homes, and pharmacy.Deliver an outstanding presentation on the topic using this Blockchain Use Cases In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Security Functions, Enhance Trackability, Enhance Mobility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
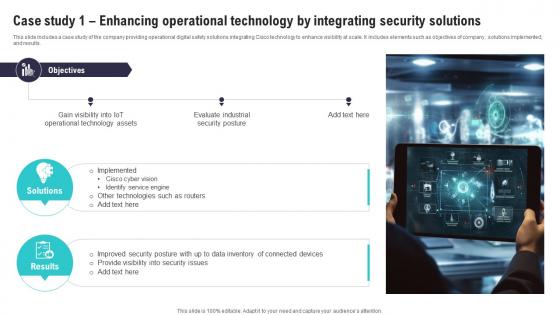 Case Study 1 Enhancing Operational Technology IoT Security And Privacy Safeguarding IoT SS
Case Study 1 Enhancing Operational Technology IoT Security And Privacy Safeguarding IoT SSThis slide includes a case study of the company providing operational digital safety solutions integrating Cisco technology to enhance visibility at scale. It includes elements such as objectives of company , solutions implemented, and results. Introducing Case Study 1 Enhancing Operational Technology IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Operational Technology, Identify Service Engine, Security Posture, using this template. Grab it now to reap its full benefits.
-
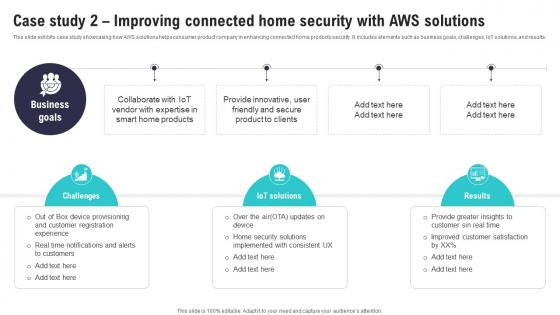 Case Study 2 Improving Connected Home Security IoT Security And Privacy Safeguarding IoT SS
Case Study 2 Improving Connected Home Security IoT Security And Privacy Safeguarding IoT SSThis slide exhibits case study showcasing how AWS solutions helps consumer product company in enhancing connected home products security. It includes elements such as business goals, challenges, IoT solutions, and results. Increase audience engagement and knowledge by dispensing information using Case Study 2 Improving Connected Home Security IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on three stages. You can also present information on Security Solutions, Improved Customer Satisfaction, Provide Innovative using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
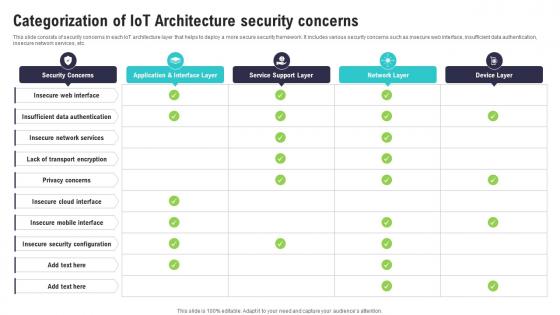 Categorization Of IoT Architecture Security Concerns IoT Security And Privacy Safeguarding IoT SS
Categorization Of IoT Architecture Security Concerns IoT Security And Privacy Safeguarding IoT SSThis slide consists of security concerns in each IoT architecture layer that helps to deploy a more secure security framework. It includes various security concerns such as insecure web interface, insufficient data authentication, insecure network services, etc. Present the topic in a bit more detail with this Categorization Of IoT Architecture Security Concerns IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Insecure Cloud Interface, Insecure Mobile Interface, Insecure Security Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
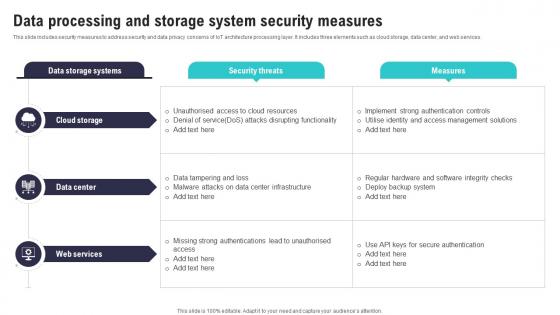 Data Processing And Storage System Security Measures IoT Security And Privacy Safeguarding IoT SS
Data Processing And Storage System Security Measures IoT Security And Privacy Safeguarding IoT SSThis slide includes security measures to address security and data privacy concerns of IoT architecture processing layer. It includes three elements such as cloud storage, data center, and web services. Deliver an outstanding presentation on the topic using this Data Processing And Storage System Security Measures IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Data Tampering, Strong Authentications, Regular Hardware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
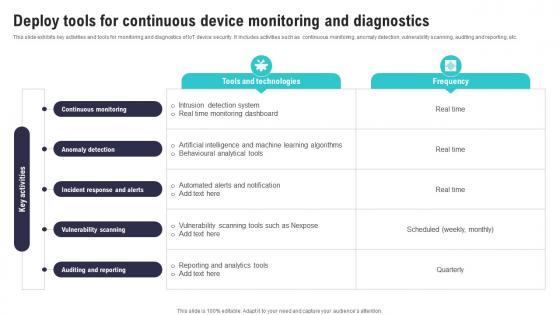 Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS
Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SSThis slide exhibits key activities and tools for monitoring and diagnostics of IoT device security. It includes activities such as continuous monitoring, anomaly detection, vulnerability scanning, auditing and reporting, etc. Present the topic in a bit more detail with this Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Vulnerability Scanning, Auditing Reporting, Anomaly Detection . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Edge Computing Role In Securing IoT Data IoT Security And Privacy Safeguarding IoT SS
Edge Computing Role In Securing IoT Data IoT Security And Privacy Safeguarding IoT SSThis slide showcases the significant role of edge computing in enhancing IoT data security and privacy. It include role such as data filtering and processing, localised threat identification, and reduce attack surface. Introducing Edge Computing Role In Securing IoT Data IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Filtering Processing, Reduce Attack Surface, Trusted Entities Interacting, using this template. Grab it now to reap its full benefits.
-
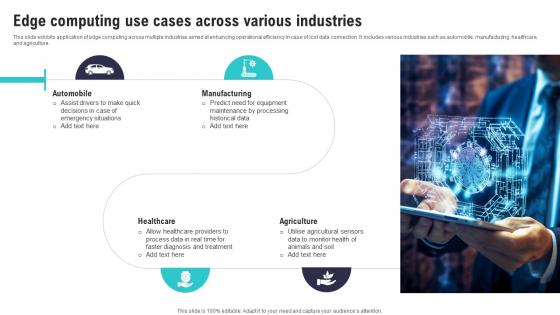 Edge Computing Use Cases Across Various Industries IoT Security And Privacy Safeguarding IoT SS
Edge Computing Use Cases Across Various Industries IoT Security And Privacy Safeguarding IoT SSThis slide exhibits application of edge computing across multiple industries aimed at enhancing operational efficiency in case of lost data connection. It includes various industries such as automobile, manufacturing, healthcare,and agriculture. Increase audience engagement and knowledge by dispensing information using Edge Computing Use Cases Across Various Industries IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on four stages. You can also present information on Diagnosis Treatment, Agricultural Sensors, Assist Drivers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
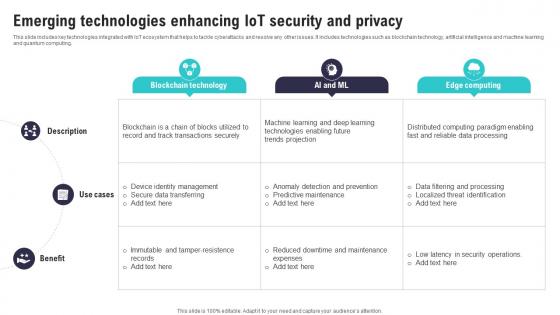 Emerging Technologies Enhancing IoT Security And IoT Security And Privacy Safeguarding IoT SS
Emerging Technologies Enhancing IoT Security And IoT Security And Privacy Safeguarding IoT SSThis slide includes key technologies integrated with IoT ecosystem that helps to tackle cyberattacks and resolve any other issues. It includes technologies such as blockchain technology, artificial intelligence and machine learning and quantum computing.Present the topic in a bit more detail with this Emerging Technologies Enhancing IoT Security And IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Transactions Securely, Identity Management, Predictive Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
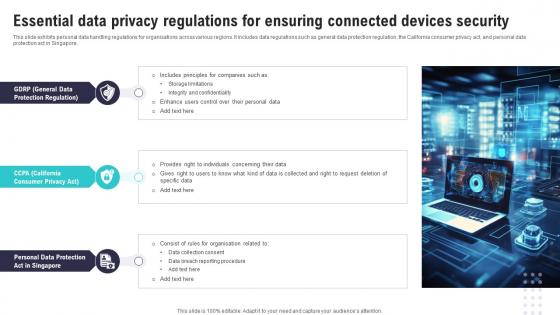 Essential Data Privacy Regulations For Ensuring IoT Security And Privacy Safeguarding IoT SS
Essential Data Privacy Regulations For Ensuring IoT Security And Privacy Safeguarding IoT SSThis slide exhibits personal data handling regulations for organisations across various regions. It includes data regulations such as general data protection regulation, the California consumer privacy act, and personal data protection act in Singapore. Increase audience engagement and knowledge by dispensing information using Essential Data Privacy Regulations For Ensuring IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on three stages. You can also present information on Protection Regulation, Data Collection Consent, Data Breach using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS
Icons Slide For IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SSPresenting our well crafted Icons Slide For IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly
-
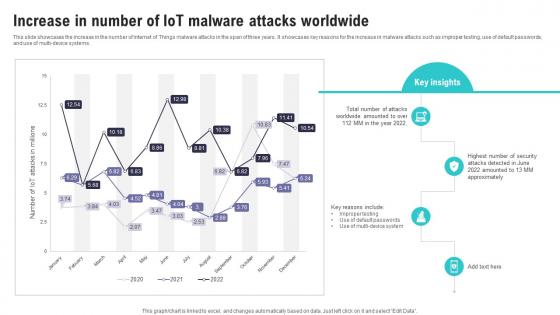 Increase In Number Of IoT Malware Attacks Worldwide IoT Security And Privacy Safeguarding IoT SS
Increase In Number Of IoT Malware Attacks Worldwide IoT Security And Privacy Safeguarding IoT SSThis slide showcases the increase in the number of Internet of Things malware attacks in the span of three years. It showcases key reasons for the increase in malware attacks such as improper testing, use of default passwords, and use of multi device systems. Present the topic in a bit more detail with this Increase In Number Of IoT Malware Attacks Worldwide IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Worldwide Amounted, Default Passwords, Attacks Detected. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
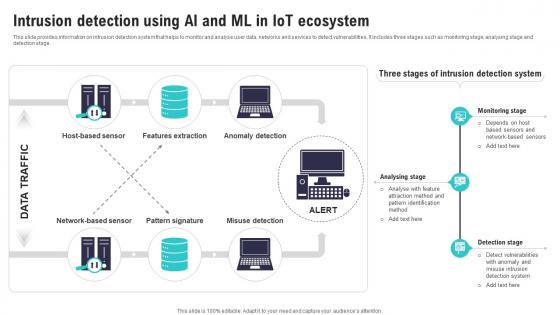 Intrusion Detection Using Ai And Ml In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SS
Intrusion Detection Using Ai And Ml In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SSThis slide provides information on intrusion detection system that helps to monitor and analyse user data, networks and services to detect vulnerabilities. It includes three stages such as monitoring stage, analysing stage and detection stage.Present the topic in a bit more detail with this Intrusion Detection Using Ai And Ml In IoT Ecosystem IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Features Extraction, Anomaly Detection, Pattern Signature. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
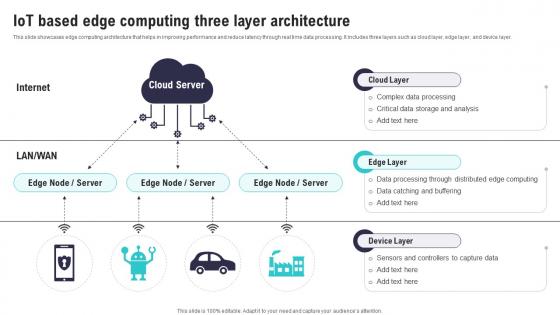 IoT Based Edge Computing Three Layer Architecture IoT Security And Privacy Safeguarding IoT SS
IoT Based Edge Computing Three Layer Architecture IoT Security And Privacy Safeguarding IoT SSThis slide showcases edge computing architecture that helps in improving performance and reduce latency through real time data processing. It includes three layers such as cloud layer, edge layer, and device layer. Deliver an outstanding presentation on the topic using this IoT Based Edge Computing Three Layer Architecture IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Data Processing, Data Catching, Critical Data Storage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



