Powerpoint Templates and Google slides for Protection Of Intellectual
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
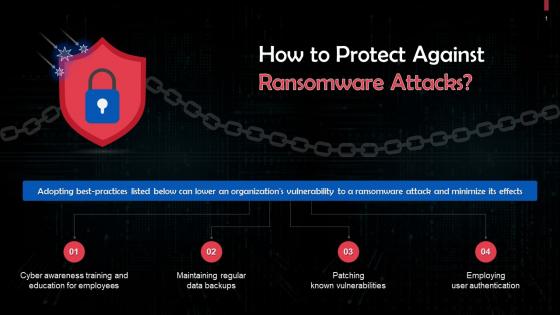 Overview Of Protection Against Ransomware Attacks Training Ppt
Overview Of Protection Against Ransomware Attacks Training PptPresenting Overview of Protection Against Ransomware Attacks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Types Of Strategies For Endpoint Protection Platforms Training Ppt
Types Of Strategies For Endpoint Protection Platforms Training PptPresenting Types of Strategies for Endpoint Protection Platforms. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Core Functionality Of Endpoint Protection Training Ppt
Core Functionality Of Endpoint Protection Training PptPresenting Core Functionality of Endpoint Protection. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
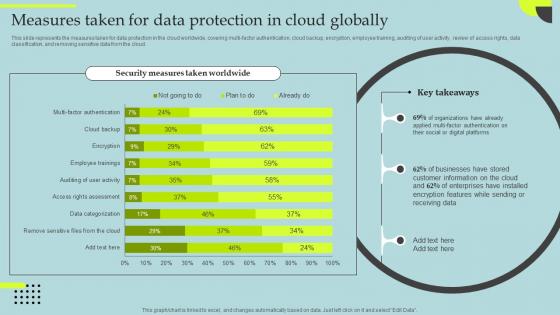 Datafication Of HR Measures Taken For Data Protection In Cloud Globally
Datafication Of HR Measures Taken For Data Protection In Cloud GloballyThis slide represents the measures taken for data protection in the cloud worldwide, covering multi-factor authentication, cloud backup, encryption, employee training, auditing of user activity, review of access rights, data classification, and removing sensitive data from the cloud. Deliver an outstanding presentation on the topic using this Datafication Of HR Measures Taken For Data Protection In Cloud Globally. Dispense information and present a thorough explanation of Measures, Protection, Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Of Facility Protections At A Hotel Training Ppt
Security Of Facility Protections At A Hotel Training PptPresenting Security of Facility Protections at a Hotel. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizablealter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
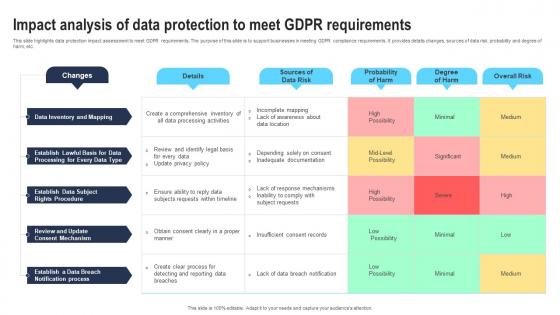 Impact analysis of data protection to meet GDPR requirements
Impact analysis of data protection to meet GDPR requirementsThis slide highlights data protection impact assessment to meet GDPR requirements. The purpose of this slide is to support businesses in meeting GDPR compliance requirements. It provides details changes, sources of data risk, probability and degree of harm, etc. Presenting our well structured Impact analysis of data protection to meet GDPR requirements. The topics discussed in this slide are Inadequate Documentation, Comprehensive Inventory, Update Privacy. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Unlocking The Impact Of Technology Cybersecurity Architecture Framework To Protect Organisations
Unlocking The Impact Of Technology Cybersecurity Architecture Framework To Protect OrganisationsThis This slide showcases framework for cybersecurity in organisations. This template focuses on reducing cyber breaches and protecting assets from digital harm. It includes information related to enterprise goals, creating safety solution, etc. Present the topic in a bit more detail with this Unlocking The Impact Of Technology Cybersecurity Architecture Framework To Protect Organisations. Use it as a tool for discussion and navigation on Cybersecurity Architecture, Framework To Protect Organisations, Assets From Digital Harm, Enterprise Goals. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
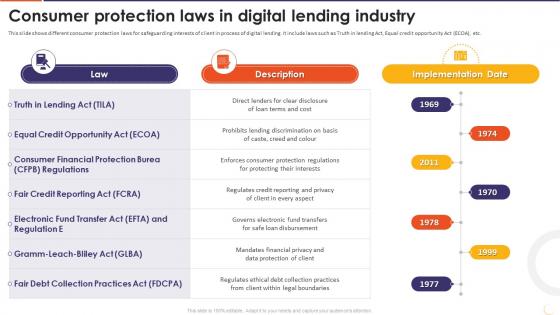 The Future Of Financing Digital Consumer Protection Laws In Digital Lending Industry
The Future Of Financing Digital Consumer Protection Laws In Digital Lending IndustryThis slide shows different consumer protection laws for safeguarding interests of client in process of digital lending. It include laws such as Truth in lending Act, Equal credit opportunity Act ECOA, etc. Increase audience engagement and knowledge by dispensing information using The Future Of Financing Digital Consumer Protection Laws In Digital Lending Industry. This template helps you present information on seven stages. You can also present information on Electronic Fund Transfer Act, Prohibits Lending Discrimination, Mandates Financial Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
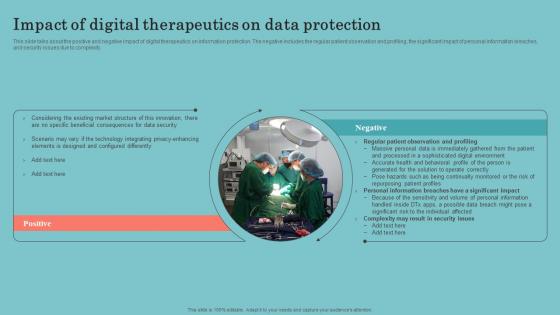 Digital Therapeutics Development Impact Of Digital Therapeutics On Data Protection
Digital Therapeutics Development Impact Of Digital Therapeutics On Data ProtectionThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Introducing Digital Therapeutics Development Impact Of Digital Therapeutics On Data Protection to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Positive, Negative, using this template. Grab it now to reap its full benefits.
-
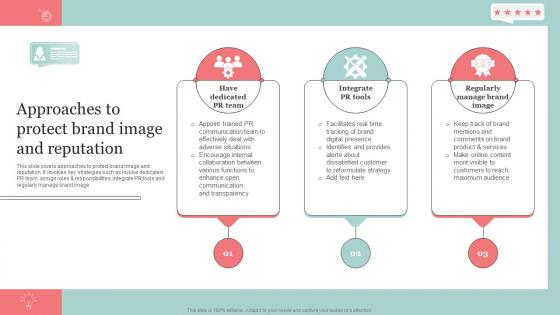 Approaches To Protect Brand Image And Reputation The Ultimate Guide Of Online Strategy SS
Approaches To Protect Brand Image And Reputation The Ultimate Guide Of Online Strategy SSThis slide covers approaches to protect brand image and reputation. It involves key strategies such as involve dedicated PR team, assign roles and responsibilities, integrate PR tools and regularly manage brand image. Increase audience engagement and knowledge by dispensing information using Approaches To Protect Brand Image And Reputation The Ultimate Guide Of Online Strategy SS. This template helps you present information on three stages. You can also present information on Have Dedicated PR Team, Integrate PR Tools, Regularly Manage Brand Image using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Overview To Protecting Brand Image Introduction The Ultimate Guide Of Online Strategy SS
Overview To Protecting Brand Image Introduction The Ultimate Guide Of Online Strategy SSThis slide covers overview to protecting brand image to improve customer retention rate. It involves key benefits such as enhanced customer loyalty, improved business growth and reduced customer acquisition costs. Increase audience engagement and knowledge by dispensing information using Overview To Protecting Brand Image Introduction The Ultimate Guide Of Online Strategy SS. This template helps you present information on three stages. You can also present information on Protecting Brand, Customer Loyalty, Business Growth using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Analysis Of Business Protection Process Icon
Risk Analysis Of Business Protection Process IconIntroducing our Risk Analysis Of Business Protection Process Icon set of slides. The topics discussed in these slides are Risk Analysis Business, Protection Process Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
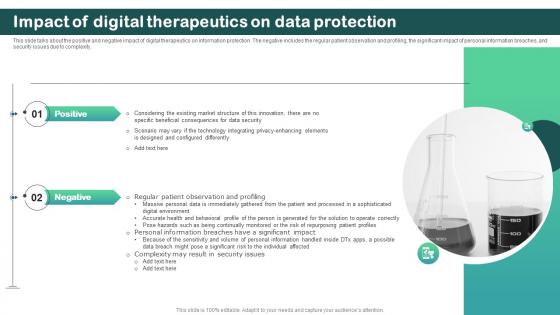 Impact Of Digital Therapeutics On Data Protection Digital Therapeutics Regulatory
Impact Of Digital Therapeutics On Data Protection Digital Therapeutics RegulatoryThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Introducing Impact Of Digital Therapeutics On Data Protection Digital Therapeutics Regulatory to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Positive, Negative, using this template. Grab it now to reap its full benefits.
-
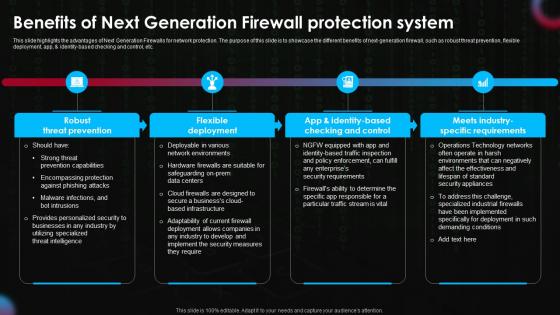 Benefits Of Next Generation Firewall Protection System Next Generation Firewall Implementation
Benefits Of Next Generation Firewall Protection System Next Generation Firewall ImplementationThis slide highlights the advantages of Next Generation Firewalls for network protection The purpose of this slide is to showcase the different benefits of next generation firewall such as robust threat prevention flexible deployment app identitybased checking and control etc Increase audience engagement and knowledge by dispensing information using Benefits Of Next Generation Firewall Protection System Next Generation Firewall Implementation. This template helps you present information on four stages. You can also present information on Prevention, Deployment, Checking using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
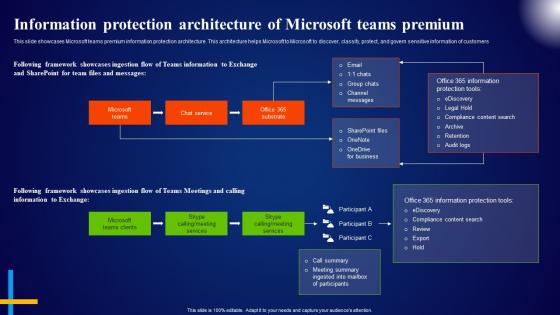 Information Protection Architecture Of Microsoft Teams Premium Microsoft AI Solutions AI SS
Information Protection Architecture Of Microsoft Teams Premium Microsoft AI Solutions AI SSThis slide showcases Microsoft teams premium information protection architecture. This architecture helps Microsoft to Microsoft to discover, classify, protect, and govern sensitive information of customers. Present the topic in a bit more detail with this Information Protection Architecture Of Microsoft Teams Premium Microsoft AI Solutions AI SS. Use it as a tool for discussion and navigation on Microsoft Teams, Chat Service, Framework Showcases. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
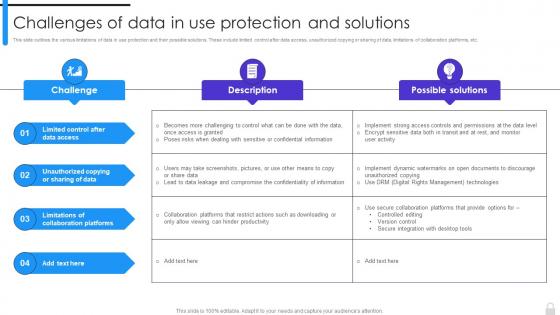 Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions
Encryption Implementation Strategies Challenges Of Data In Use Protection And SolutionsThis slide outlines the various limitations of data in use protection and their possible solutions. These include limited control after data access, unauthorized copying or sharing of data, limitations of collaboration platforms, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions. Use it as a tool for discussion and navigation on Limitations Of Collaboration Platforms, Unauthorized Copying Or Sharing Of Data, Limited Control After Data Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
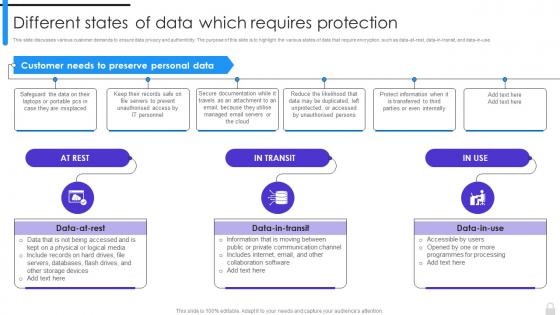 Encryption Implementation Strategies Different States Of Data Which Requires Protection
Encryption Implementation Strategies Different States Of Data Which Requires ProtectionThis slide discusses various customer demands to ensure data privacy and authenticity. The purpose of this slide is to highlight the various states of data that require encryption, such as data-at-rest, data-in-transit, and data-in-use. Introducing Encryption Implementation Strategies Different States Of Data Which Requires Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Demands, Data Privacy And Authenticity, Require Encryption, Collaboration Software, using this template. Grab it now to reap its full benefits.
-
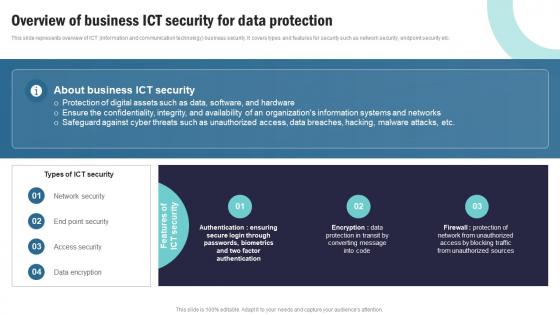 Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V
Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Incident Management, Request Fulfillment using this template. Grab it now to reap its full benefits.
-
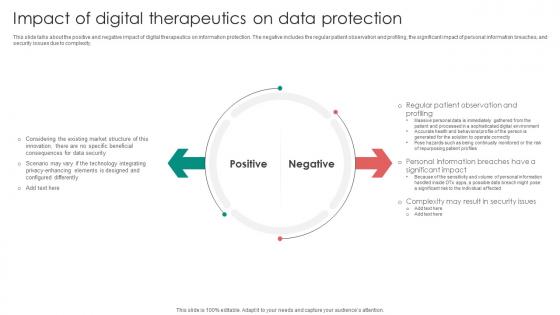 Digital Therapeutics Functions Impact Of Digital Therapeutics On Data Protection
Digital Therapeutics Functions Impact Of Digital Therapeutics On Data ProtectionThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Introducing Digital Therapeutics Functions Impact Of Digital Therapeutics On Data Protection to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Positive, Negative, Data Protection using this template. Grab it now to reap its full benefits.
-
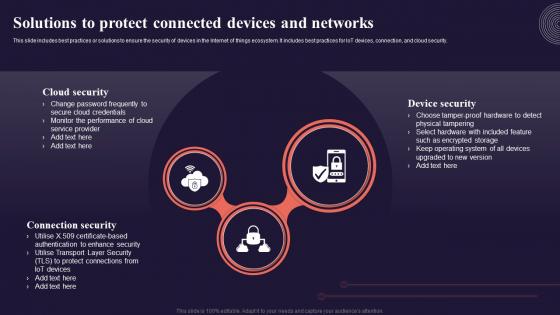 Solutions To Protect Connected Devices And Networks Introduction To Internet Of Things IoT SS
Solutions To Protect Connected Devices And Networks Introduction To Internet Of Things IoT SSThis slide includes best practices or solutions to ensure the security of devices in the Internet of things ecosystem. It includes best practices for IoT devices, connection, and cloud security. Introducing Solutions To Protect Connected Devices And Networks Introduction To Internet Of Things IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Security, Connection Security, using this template. Grab it now to reap its full benefits.
-
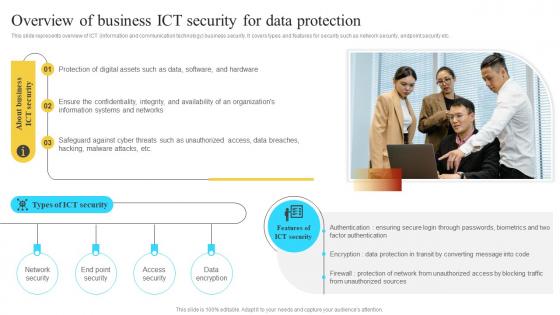 Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V
Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Protection Of Digital, Safeguard Against Cyber, using this template. Grab it now to reap its full benefits.
-
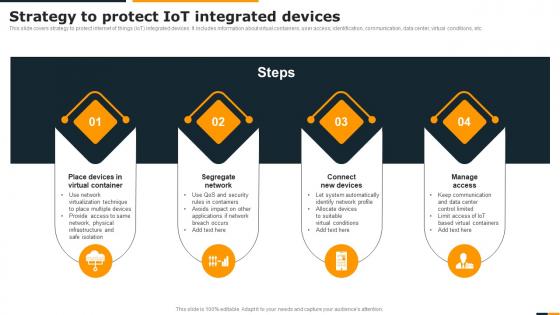 Guide Of Integrating Industrial Internet Strategy To Protect IOT Integrated Devices
Guide Of Integrating Industrial Internet Strategy To Protect IOT Integrated DevicesThis slide covers strategy to protect internet of things IoT integrated devices. It includes information about virtual containers, user access, identification, communication, data center, virtual conditions, etc. Increase audience engagement and knowledge by dispensing information using Guide Of Integrating Industrial Internet Strategy To Protect IOT Integrated Devices. This template helps you present information on four stages. You can also present information on Virtual Container, Segregate Network, Connect New Devices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
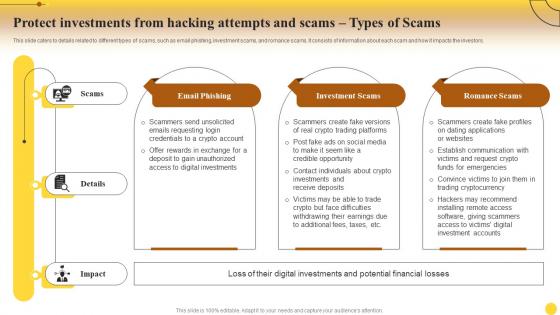 Protect Attempts And Scams Types Of Scams Comprehensive Cryptocurrency Investments Fin SS
Protect Attempts And Scams Types Of Scams Comprehensive Cryptocurrency Investments Fin SSThis slide caters to the details related to cryptocurrency investments. It includes information about reasons people invest in cryptocurrency, such as speculation, diversification, hedging against inflation, etc. Deliver an outstanding presentation on the topic using this Protect Attempts And Scams Types Of Scams Comprehensive Cryptocurrency Investments Fin SS. Dispense information and present a thorough explanation of Investment, Cryptocurrency, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Advantages Of Utilizing Advanced Threat Protection In Cyber Security
Advantages Of Utilizing Advanced Threat Protection In Cyber SecurityThe following slide highlights the possible benefits of implementing advanced threat protection against sophisticated cyber threats and attacks. Presenting our set of slides with Advantages Of Utilizing Advanced Threat Protection In Cyber Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security, Analytics, Protection.
-
 Real World Example Of Advanced Threat Protection Effectiveness
Real World Example Of Advanced Threat Protection EffectivenessThe mentioned slide showcases real life instances of utilizing advanced threat protection solutions that contribute to a proactive defense strategy. Introducing our premium set of slides with Real World Example Of Advanced Threat Protection Effectiveness. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransomware, Destructive, Analytics. So download instantly and tailor it with your information.
-
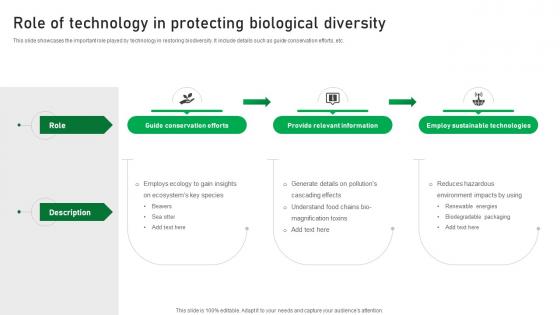 Role Of Technology In Protecting Biological Diversity
Role Of Technology In Protecting Biological DiversityThis slide showcases the important role played by technology in restoring biodiversity. It include details such as guide conservation efforts,etc. Introducing our premium set of slides with Role Of Technology In Protecting Biological Diversity. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Guide Conservation Efforts,Provide Relevant Information,Employ Sustainable Technologies. So download instantly and tailor it with your information.
-
 Conservation Agriculture Overview For Protecting Arable Land Complete Guide Of Sustainable Agriculture
Conservation Agriculture Overview For Protecting Arable Land Complete Guide Of Sustainable AgricultureThis slide provides glimpse about summary of conservation agriculture that can help farming businesses in protecting and maintaining soil cover. It includes benefits such as economic benefits, agronomic benefits, environment benefits, etc. Present the topic in a bit more detail with this Conservation Agriculture Overview For Protecting Arable Land Complete Guide Of Sustainable Agriculture Use it as a tool for discussion and navigation on Economic Benefits, Agronomic Benefits, Environmental Benefits This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Organic Farming Overview For Protecting Natural Resources Complete Guide Of Sustainable Agriculture
Organic Farming Overview For Protecting Natural Resources Complete Guide Of Sustainable AgricultureThis slide provides glimpse about summary of organic farming that can help in conserving biodiversity and natural resources. It includes benefits such as no harmful pesticides, sustainably healthy soil, etc. Deliver an outstanding presentation on the topic using this Organic Farming Overview For Protecting Natural Resources Complete Guide Of Sustainable Agriculture Dispense information and present a thorough explanation of No Harmful Pesticides, Sustainably Healthy Soil, Biodiversity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
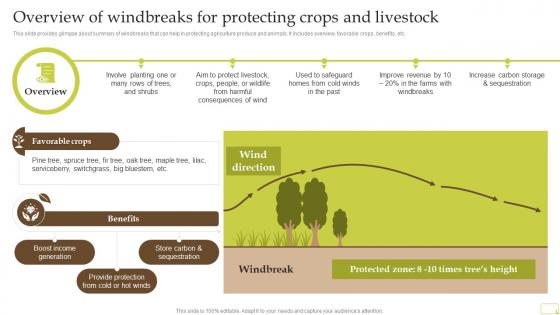 Overview Of Windbreaks For Protecting Crops And Livestock Complete Guide Of Sustainable Agriculture Practices
Overview Of Windbreaks For Protecting Crops And Livestock Complete Guide Of Sustainable Agriculture PracticesThis slide provides glimpse about summary of windbreaks that can help in protecting agriculture produce and animals. It includes overview, favorable crops, benefits, etc. Present the topic in a bit more detail with this Overview Of Windbreaks For Protecting Crops And Livestock Complete Guide Of Sustainable Agriculture Practices Use it as a tool for discussion and navigation on Boost Income Generation, Benefits, Store Carbon And Sequestration This template is free to edit as deemed fit for your organization. Therefore download it now.
-
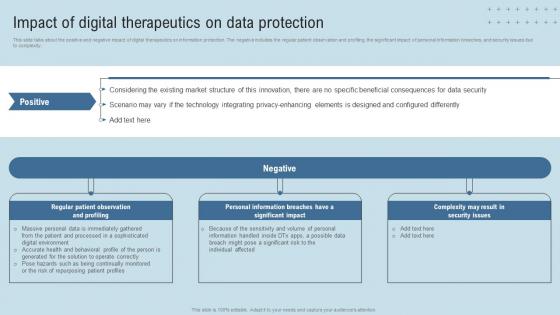 DTx Enablers Impact Of Digital Therapeutics On Data Protection
DTx Enablers Impact Of Digital Therapeutics On Data ProtectionThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Present the topic in a bit more detail with this DTx Enablers Impact Of Digital Therapeutics On Data Protection. Use it as a tool for discussion and navigation on Market Structure, Technology, Data Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Essential Protection Types Of Mobile Security
Essential Protection Types Of Mobile SecurityThis slide is a representation of types of mobile security which includes screen lock, biometrics and remote lock and wipe and so on. Presenting our set of slides with name Essential Protection Types Of Mobile Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Remote Lock And Wipe, Essential Protection, Types Of Mobile Security.
-
 Comprehensive Guide For Understanding Overview Of Life Insurance For Financial Protection Fin SS
Comprehensive Guide For Understanding Overview Of Life Insurance For Financial Protection Fin SSThis slide carries an overview of life insurance containing its definition, importance and its various types such as term life insurance, whole life insurance, universal life insurance and so on Increase audience engagement and knowledge by dispensing information using Comprehensive Guide For Understanding Overview Of Life Insurance For Financial Protection Fin SS This template helps you present information on Two stages. You can also present information on Term Life Insurance, Whole Life Insurance, Universal Life Insurance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
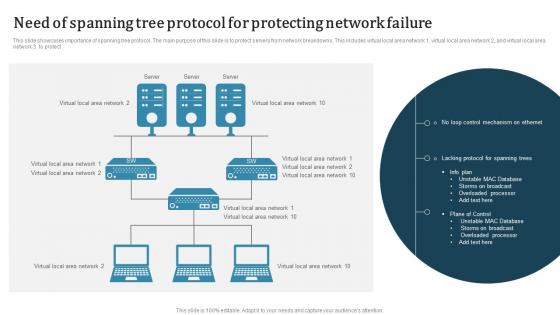 Need Of Spanning Tree Protocol For Protecting Network Failure
Need Of Spanning Tree Protocol For Protecting Network FailureThis slide showcases importance of spanning tree protocol. The main purpose of this slide is to protect servers from network breakdowns. This includes virtual local area network 1, virtual local area network 2 and virtual local area network 3 to protect. Introducing our Need Of Spanning Tree Protocol For Protecting Network Failure set of slides. The topics discussed in these slides are Need Of Spanning, Tree Protocol, Protecting Network Failure. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
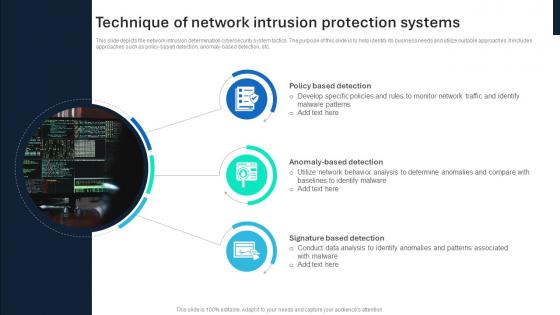 Technique Of Network Intrusion Protection Systems
Technique Of Network Intrusion Protection SystemsThis slide depicts the network intrusion determination cybersecurity system tactics. The purpose of this slide is to help identify its business needs and utilize suitable approaches. It includes approaches such as policy based detection, anomaly based detection, etc. Introducing our Technique Of Network Intrusion Protection Systems set of slides. The topics discussed in these slides are Policy Based Detection, Anomaly Based Detection, Signature Based Detection This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
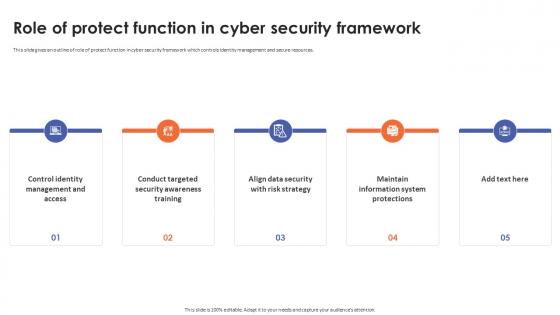 Role Of Protect Function In Cyber Security Framework
Role Of Protect Function In Cyber Security FrameworkThis slide gives an outline of role of protect function in cyber security framework which controls identity management and secure resources. Introducing Role Of Protect Function In Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Security Awareness Training, Data Security With Risk Strategy, Maintain Information System Protections, using this template. Grab it now to reap its full benefits.
-
 Use Cases Of Blockchain Privacy Protection In Comprehensive Approach To Privacy BCT SS
Use Cases Of Blockchain Privacy Protection In Comprehensive Approach To Privacy BCT SSThis slide covers various sectors where blockchain is helping to increase privacy such as financial transactions, healthcare records, legal services, shipping and logistics,etc. Introducing Use Cases Of Blockchain Privacy Protection In Comprehensive Approach To Privacy BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Financial Transactions, Healthcare Records, Legal Services, Shipping And Logistics, using this template. Grab it now to reap its full benefits.
-
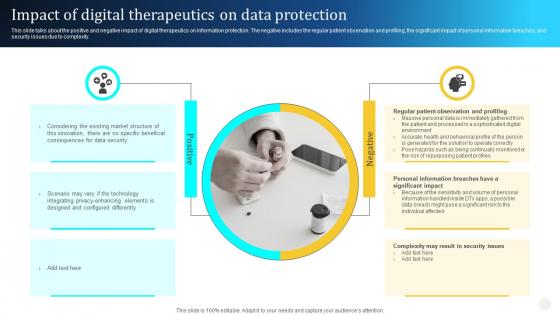 Digital Therapeutics Types Impact Of Digital Therapeutics On Data Protection Ppt Professional
Digital Therapeutics Types Impact Of Digital Therapeutics On Data Protection Ppt ProfessionalThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Introducing Digital Therapeutics Types Impact Of Digital Therapeutics On Data Protection Ppt Professional to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Positive, Negative, Regular Patient Observation, using this template. Grab it now to reap its full benefits.
-
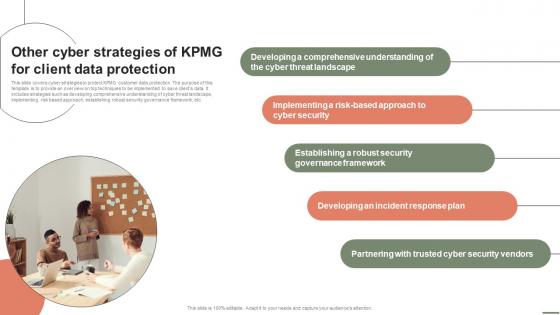 Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS VThis slide covers cyber strategies to protect KPMG customer data protection. The purpose of this template is to provide an overview on top techniques to be implemented to save clients data. It includes strategies such as developing comprehensive understanding of cyber threat landscape, implementing risk based approach, establishing robust security governance framework, etc. Increase audience engagement and knowledge by dispensing information using Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V. This template helps you present information on five stages. You can also present information on Threat Landscape, Cyber Security, Governance Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Role Of Digital Rights Management In Copyright Protection
Role Of Digital Rights Management In Copyright ProtectionThis slide exhibits digital rights management role in copyright protection by providing technological tools and mechanisms to safeguard content creators, distributors rights. It includes aspects such as unauthorized distribution, protect content creators, vulnerable hacking, etc. Presenting our set of slides with Role Of Digital Rights Management In Copyright Protection This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Protect Content Creators, Vulnerable Hacking, Intellectual Property Rights
-
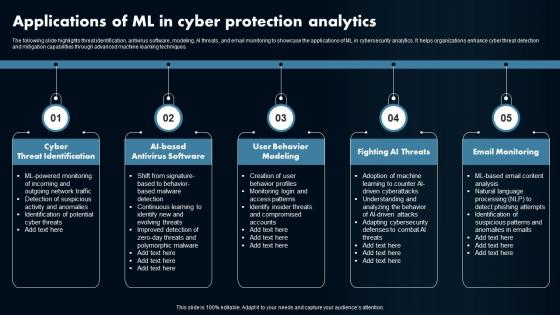 Applications Of ML In Cyber Protection Analytics
Applications Of ML In Cyber Protection AnalyticsThe following slide highlights threat identification, antivirus software, modeling, AI threats, and email monitoring to showcase the applications of ML in cybersecurity analytics. It helps organizations enhance cyber threat detection and mitigation capabilities through advanced machine learning techniques Presenting our set of slides with Applications Of ML In Cyber Protection Analytics. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Threat Identification, Antivirus Software, User Behavior Modeling.
-
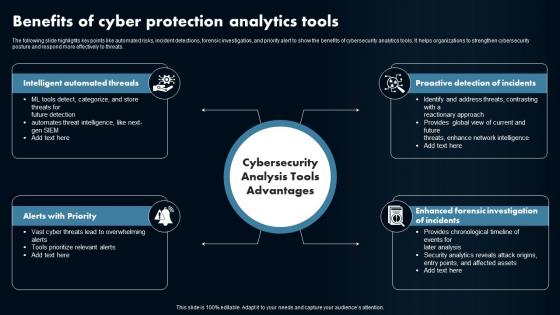 Benefits Of Cyber Protection Analytics Tools
Benefits Of Cyber Protection Analytics ToolsThe following slide highlights key points like automated risks, incident detections, forensic investigation, and priority alert to show the benefits of cybersecurity analytics tools. It helps organizations to strengthen cybersecurity posture and respond more effectively to threats. Introducing our premium set of slides with Benefits Of Cyber Protection Analytics Tools. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Alerts with Priority, Intelligent Automated Threads. So download instantly and tailor it with your information.
-
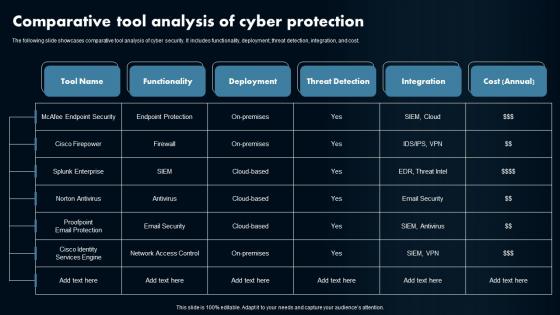 Comparative Tool Analysis Of Cyber Protection
Comparative Tool Analysis Of Cyber ProtectionThe following slide showcases comparative tool analysis of cyber security. It includes functionality, deployment, threat detection, integration, and cost Introducing our Comparative Tool Analysis Of Cyber Protection set of slides. The topics discussed in these slides are Tool Name, Functionality, Deployment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
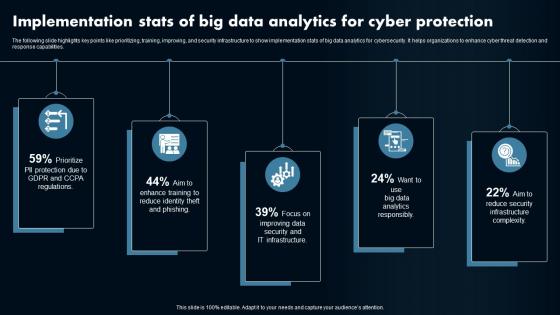 Implementation Stats Of Big Data Analytics For Cyber Protection
Implementation Stats Of Big Data Analytics For Cyber ProtectionThe following slide highlights key points like prioritizing, training, improving, and security infrastructure to show implementation stats of big data analytics for cybersecurity. It helps organizations to enhance cyber threat detection and response capabilities. Presenting our set of slides with Implementation Stats Of Big Data Analytics For Cyber Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Data Analytics, Cybersecurity.
-
 Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS
Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SSThis slide presents key strategies to ensure data security in retail industry to protect consumer data. It includes PCI DSS compliance, POS security, customer data protection, secure online transactions, inventory management security, and employee training and awareness. Increase audience engagement and knowledge by dispensing information using Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS This template helps you present information on six stages. You can also present information on Customer Data Protection, Online Transactions, Management Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implement General Data Protection Regulation Digital Transformation Of Retail DT SS
Implement General Data Protection Regulation Digital Transformation Of Retail DT SSThis slide presents actions to establish a safe-custodian image in retail industry. It includes integrating general data protection and regulation with steps understand GDPR, data audit, consent and legal basis, privacy notices and policies, data security and breach notification and ongoing compliance. Introducing Implement General Data Protection Regulation Digital Transformation Of Retail DT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Ongoing Compliance, Data Security, Consent And Legal Basis using this template. Grab it now to reap its full benefits.
-
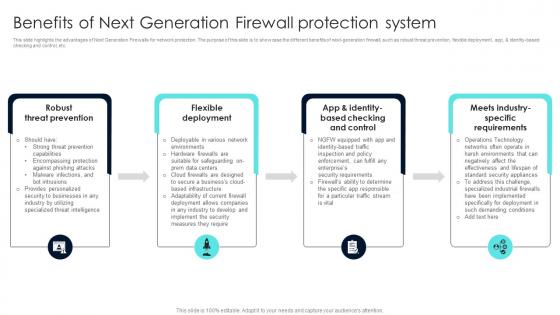 Firewall Network Security Benefits Of Next Generation Firewall Protection System
Firewall Network Security Benefits Of Next Generation Firewall Protection SystemThis slide highlights the advantages of Next Generation Firewalls for network protection. The purpose of this slide is to showcase the different benefits of next-generation firewall, such as robust threat prevention, flexible deployment, app, and identity-based checking and control, etc. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Benefits Of Next Generation Firewall Protection System This template helps you present information on Four stages. You can also present information on Firewall Network Security Benefits Of Next Generation Firewall Protection System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
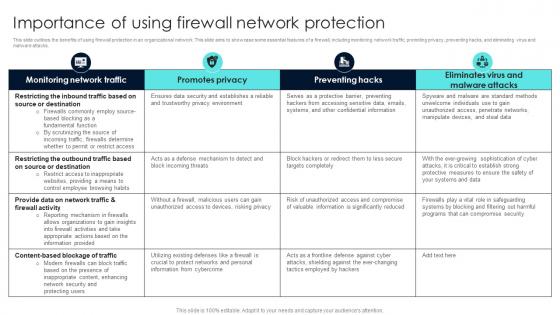 Firewall Network Security Importance Of Using Firewall Network Protection
Firewall Network Security Importance Of Using Firewall Network ProtectionThis slide outlines the benefits of using firewall protection in an organizational network. This slide aims to showcase some essential features of a firewall, including monitoring network traffic, promoting privacy, preventing hacks, and eliminating virus and malware attacks. Deliver an outstanding presentation on the topic using this Firewall Network Security Importance Of Using Firewall Network Protection Dispense information and present a thorough explanation of Enhance Security, IP Addresses, Malicious Content using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
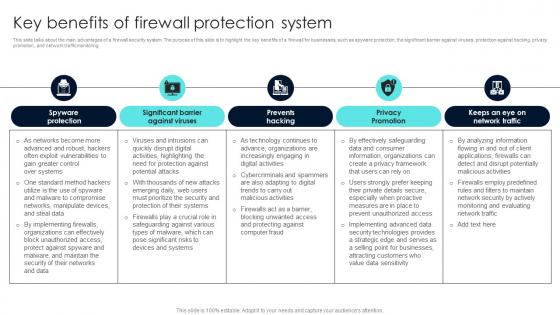 Firewall Network Security Key Benefits Of Firewall Protection System
Firewall Network Security Key Benefits Of Firewall Protection SystemThis slide talks about the main advantages of a firewall security system. The purpose of this slide is to highlight the key benefits of a firewall for businesses, such as spyware protection, the significant barrier against viruses, protection against hacking, privacy promotion, and network traffic monitoring. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Key Benefits Of Firewall Protection System This template helps you present information on Five stages. You can also present information on Intelligent Protection, Traffic Filtering, Communication Protocol Administration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
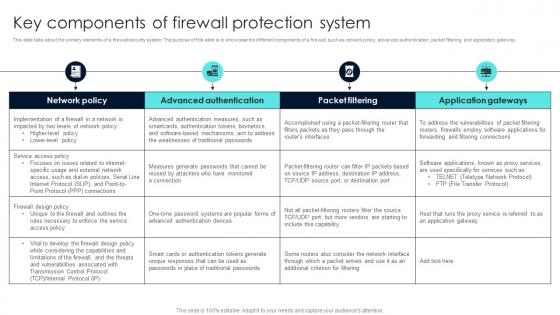 Firewall Network Security Key Components Of Firewall Protection System
Firewall Network Security Key Components Of Firewall Protection SystemThis slide talks about the primary elements of a firewall security system. The purpose of this slide is to showcase the different components of a firewall, such as network policy, advanced authentication, packet filtering, and application gateway. Present the topic in a bit more detail with this Firewall Network Security Key Components Of Firewall Protection System Use it as a tool for discussion and navigation on Misconfiguration, Software Vulnerabilities, Missing Firewall Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
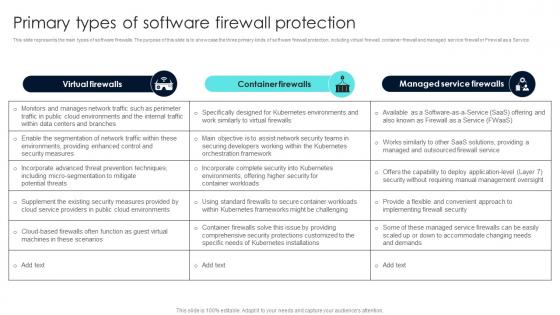 Firewall Network Security Primary Types Of Software Firewall Protection
Firewall Network Security Primary Types Of Software Firewall ProtectionThis slide represents the main types of software firewalls. The purpose of this slide is to showcase the three primary kinds of software firewall protection, including virtual firewall, container firewall and managed service firewall or Firewall as a Service. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Primary Types Of Software Firewall Protection This template helps you present information on Three stages. You can also present information on Advantages, Disadvantages using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Components Of IP Security To Protect Sensitive Data
Major Components Of IP Security To Protect Sensitive DataThis slide showcases key elements of IP security for protecting data. The main purpose of this template is to showcase protection and trustworthiness of data. This includes encapsulating security payload, authentication header, and internet key exchange. Presenting our set of slides with name Major Components Of IP Security To Protect Sensitive Data. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Internet Key Exchange, Authentication Header, Encapsulating Security Payload.
-
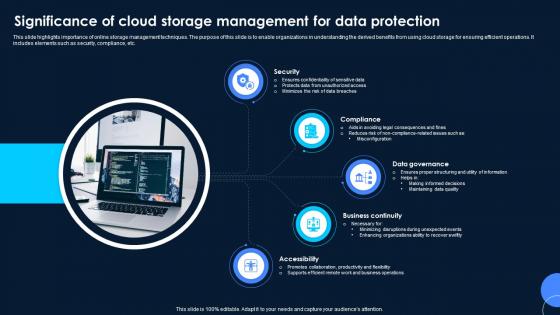 Significance Of Cloud Storage Management For Data Protection
Significance Of Cloud Storage Management For Data ProtectionThis slide highlights importance of online storage management techniques. The purpose of this slide is to enable organizations in understanding the derived benefits from using cloud storage for ensuring efficient operations. It includes elements such as security, compliance, etc. Introducing our premium set of slides with Significance Of Cloud Storage Management For Data Protection. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Compliance, Data Governance. So download instantly and tailor it with your information.
-
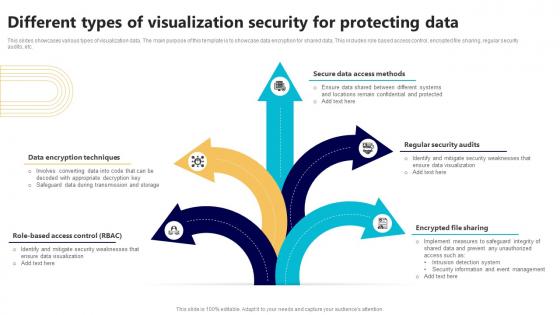 Different Types Of Visualization Security For Protecting Data
Different Types Of Visualization Security For Protecting DataThis slides showcases various types of visualization data. The main purpose of this template is to showcase data encryption for shared data. This includes role based access control, encrypted file sharing, regular security audits, etc. Introducing our premium set of slides with Different Types Of Visualization Security For Protecting Data. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Methods, Regular Security Audits, Encrypted File Sharing. So download instantly and tailor it with your information.
-
 Types Of Wireless Internet Security For Data Protection
Types Of Wireless Internet Security For Data ProtectionThe following slide highlights key points such as WEP, WPA, WPA2, and WPA3 protocols to show types of wireless internet security for privacy protection. It helps in understanding and comparing different safety procedures for effective data protection. Introducing our premium set of slides with Types Of Wireless Internet Security For Data Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Protection, Wireless Internet. So download instantly and tailor it with your information.
-
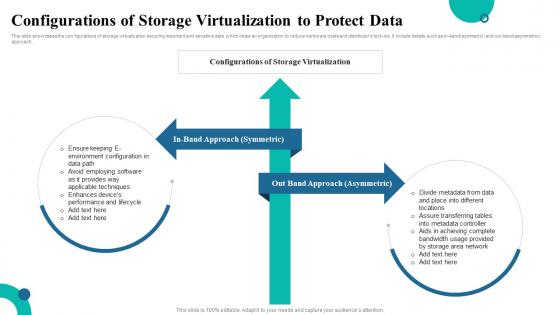 Configurations Of Storage Virtualization To Protect Data
Configurations Of Storage Virtualization To Protect DataThis slide showcases the con figurations of storage virtualization securing important and sensitive data which helps an organization to reduce hardware costs and distributors lock-ins. It include details such as in-band symmetric and out band asymmetric approach. Presenting our set of slides with name Configurations Of Storage Virtualization To Protect Data. This exhibits information on Two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on In Band Approach Symmetric, Out Band Approach Asymmetric.
-
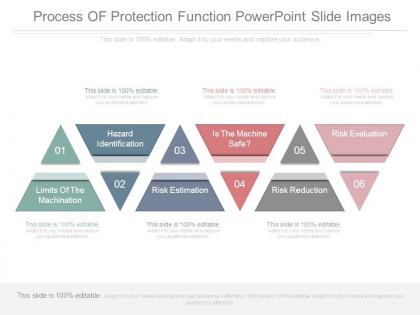 Process of protection function powerpoint slide images
Process of protection function powerpoint slide imagesPresenting process of protection function powerpoint slide images. This is a process of protection function powerpoint slide images. This is a six stage process. The stages in this process are risk evaluation, risk reduction, is the machine safe, risk estimation, hazard identification, limits of the machination.
-
 Methods of network protection sample diagram ppt design
Methods of network protection sample diagram ppt designPresenting methods of network protection sample diagram ppt design. This is a methods of network protection sample diagram ppt design. This is a six stage process. The stages in this process are error handing, controlled access, session management, network security, server and code management, data access.
-
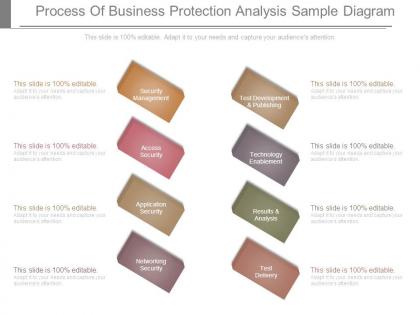 Process of business protection analysis sample diagram
Process of business protection analysis sample diagramPresenting process of business protection analysis sample diagram. This is a process of business protection analysis sample diagram. This is a eight stage process. The stages in this process are security management, access security, application security, networking security, test delivery, results and analysis, technology enablement, test development and publishing.
-
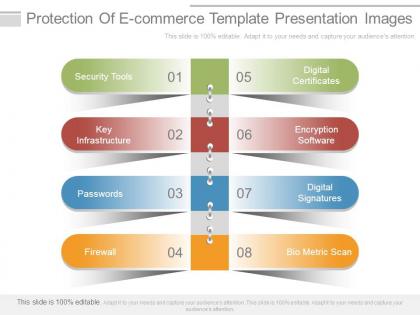 Protection of e commerce template presentation images
Protection of e commerce template presentation imagesPresenting protection of e commerce template presentation images. Presenting protection of e commerce template presentation images. This is a protection of e commerce template presentation images. This is a eight stage process. The stages in this process are digital certificates, encryption software, digital signatures, bio metric scan, firewall, passwords, key infrastructure, security tools.
-
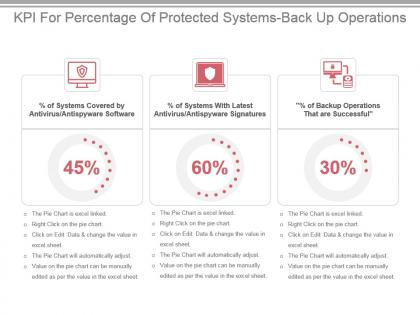 Kpi for percentage of protected systems back up operations ppt slide
Kpi for percentage of protected systems back up operations ppt slidePresenting kpi for percentage of protected systems back up operations ppt slide. This presentation slide shows three Key Performance Indicators or KPIs in a Dashboard style design. The first KPI that can be shown is percentage of Systems Covered by Antivirus Antispyware Software. The second KPI is percentage of Systems With Latest Antivirus Antispyware Signatures and the third is percentage of Backup Operations That are Successful. These KPI Powerpoint graphics are all data driven,and the shape automatically adjusts according to your data. Just right click on the KPI graphic,enter the right value and the shape will adjust automatically. Make a visual impact with our KPI slides.


