Powerpoint Templates and Google slides for Protection Of Intellectual
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
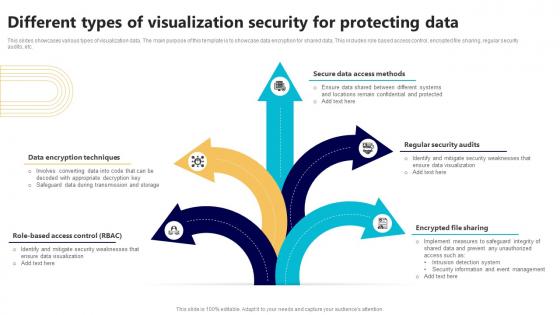 Different Types Of Visualization Security For Protecting Data
Different Types Of Visualization Security For Protecting DataThis slides showcases various types of visualization data. The main purpose of this template is to showcase data encryption for shared data. This includes role based access control, encrypted file sharing, regular security audits, etc. Introducing our premium set of slides with Different Types Of Visualization Security For Protecting Data. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Methods, Regular Security Audits, Encrypted File Sharing. So download instantly and tailor it with your information.
-
 Types Of Wireless Internet Security For Data Protection
Types Of Wireless Internet Security For Data ProtectionThe following slide highlights key points such as WEP, WPA, WPA2, and WPA3 protocols to show types of wireless internet security for privacy protection. It helps in understanding and comparing different safety procedures for effective data protection. Introducing our premium set of slides with Types Of Wireless Internet Security For Data Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Protection, Wireless Internet. So download instantly and tailor it with your information.
-
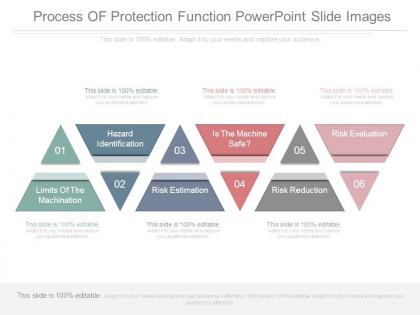 Process of protection function powerpoint slide images
Process of protection function powerpoint slide imagesPresenting process of protection function powerpoint slide images. This is a process of protection function powerpoint slide images. This is a six stage process. The stages in this process are risk evaluation, risk reduction, is the machine safe, risk estimation, hazard identification, limits of the machination.
-
 Methods of network protection sample diagram ppt design
Methods of network protection sample diagram ppt designPresenting methods of network protection sample diagram ppt design. This is a methods of network protection sample diagram ppt design. This is a six stage process. The stages in this process are error handing, controlled access, session management, network security, server and code management, data access.
-
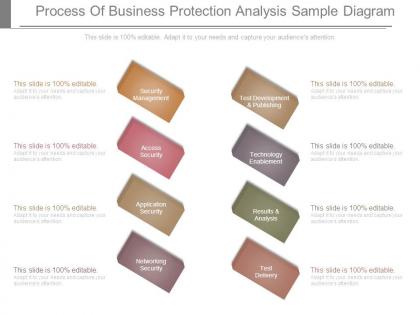 Process of business protection analysis sample diagram
Process of business protection analysis sample diagramPresenting process of business protection analysis sample diagram. This is a process of business protection analysis sample diagram. This is a eight stage process. The stages in this process are security management, access security, application security, networking security, test delivery, results and analysis, technology enablement, test development and publishing.
-
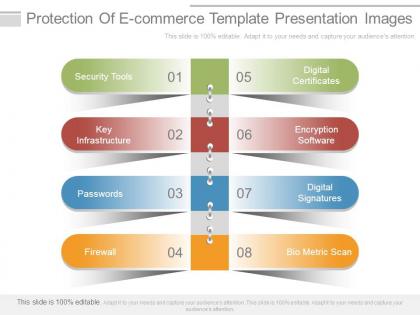 Protection of e commerce template presentation images
Protection of e commerce template presentation imagesPresenting protection of e commerce template presentation images. Presenting protection of e commerce template presentation images. This is a protection of e commerce template presentation images. This is a eight stage process. The stages in this process are digital certificates, encryption software, digital signatures, bio metric scan, firewall, passwords, key infrastructure, security tools.
-
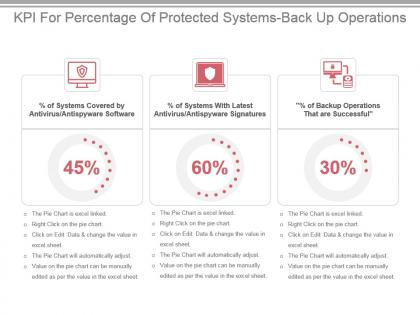 Kpi for percentage of protected systems back up operations ppt slide
Kpi for percentage of protected systems back up operations ppt slidePresenting kpi for percentage of protected systems back up operations ppt slide. This presentation slide shows three Key Performance Indicators or KPIs in a Dashboard style design. The first KPI that can be shown is percentage of Systems Covered by Antivirus Antispyware Software. The second KPI is percentage of Systems With Latest Antivirus Antispyware Signatures and the third is percentage of Backup Operations That are Successful. These KPI Powerpoint graphics are all data driven,and the shape automatically adjusts according to your data. Just right click on the KPI graphic,enter the right value and the shape will adjust automatically. Make a visual impact with our KPI slides.
-
 Use Of Protective Equipment At Workplace Post Pandemic Business Playbook
Use Of Protective Equipment At Workplace Post Pandemic Business PlaybookThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Introducing Use Of Protective Equipment At Workplace Post Pandemic Business Playbook to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Masks And Respirators, Gloves, Face Shields, using this template. Grab it now to reap its full benefits.
-
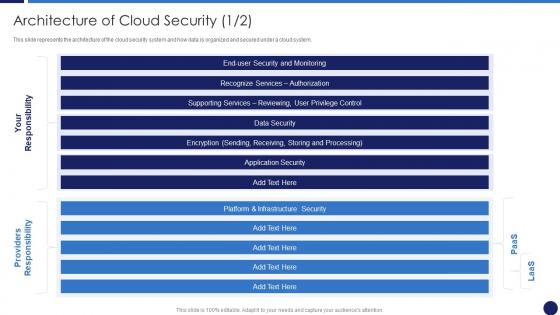 Architecture Of Cloud Security Cloud Data Protection
Architecture Of Cloud Security Cloud Data ProtectionThis slide represents the architecture of the cloud security system and how data is organized and secured under a cloud system. Deliver an outstanding presentation on the topic using this Architecture Of Cloud Security Cloud Data Protection. Dispense information and present a thorough explanation of Infrastructure Security, Monitoring, Processing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
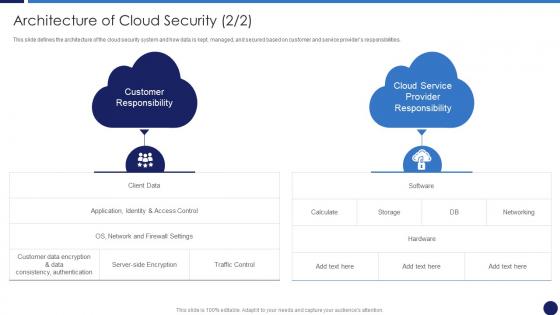 Cloud Data Protection Architecture Of Cloud Security
Cloud Data Protection Architecture Of Cloud SecurityThis slide defines the architecture of the cloud security system and how data is kept, managed, and secured based on customer and service providers responsibilities. Increase audience engagement and knowledge by dispensing information using Cloud Data Protection Architecture Of Cloud Security. This template helps you present information on two stages. You can also present information on Customer Data, Customer Responsibility, Cloud Service using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Data Protection Essential Pillars Of Cloud Security
Cloud Data Protection Essential Pillars Of Cloud SecurityThis slide shows the four essential pillars of cloud security, namely visibility and consistency, process based security, network security, and identity security. Introducing Cloud Data Protection Essential Pillars Of Cloud Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Process Based Security, Network Security, Identity Security, using this template. Grab it now to reap its full benefits.
-
 Cloud Data Protection What Are The Downsides Of A Cloud Security
Cloud Data Protection What Are The Downsides Of A Cloud SecurityThis slide describes the downsides of the cloud security system, including loss of control over data, data loss, insider theft, and data breaches. Introducing Cloud Data Protection What Are The Downsides Of A Cloud Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Data Security, Organizations, Data Breaches, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Loss Of Data Cloud Data Protection
Cloud Security Threats Loss Of Data Cloud Data ProtectionThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Data Protection. This template helps you present information on four stages. You can also present information on Storage Locations, Organization, Strategies using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Pillars Of Cloud Security Identity Security Cloud Data Protection
Pillars Of Cloud Security Identity Security Cloud Data ProtectionThis slide depicts the identity security pillar of cloud security. It also shows how it could be beneficial to protect data from loss. Increase audience engagement and knowledge by dispensing information using Pillars Of Cloud Security Identity Security Cloud Data Protection. This template helps you present information on four stages. You can also present information on Pillars Of Cloud Security Identity Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
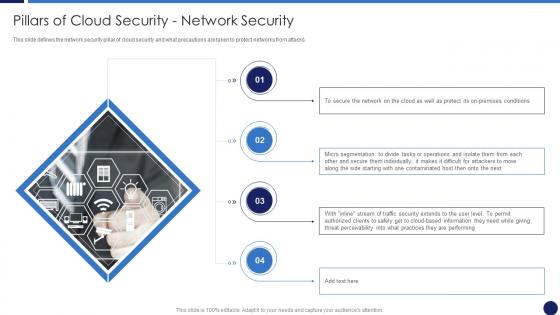 Pillars Of Cloud Security Network Security Cloud Data Protection
Pillars Of Cloud Security Network Security Cloud Data ProtectionThis slide defines the network security pillar of cloud security and what precautions are taken to protect networks from attacks. Introducing Pillars Of Cloud Security Network Security Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Micro Segmentation, Operations, Security, using this template. Grab it now to reap its full benefits.
-
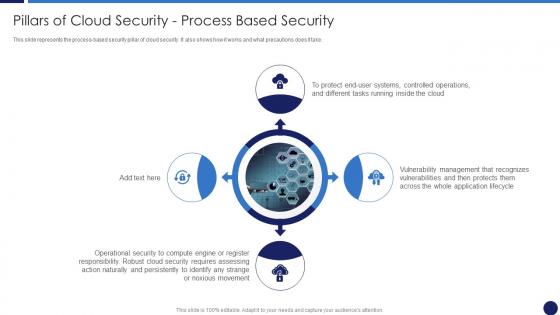 Pillars Of Cloud Security Process Based Security Cloud Data Protection
Pillars Of Cloud Security Process Based Security Cloud Data ProtectionThis slide represents the process-based security pillar of cloud security. It also shows how it works and what precautions does it take. Increase audience engagement and knowledge by dispensing information using Pillars Of Cloud Security Process Based Security Cloud Data Protection. This template helps you present information on four stages. You can also present information on Operational Security, Management, Operations using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Pillars Of Cloud Security Visibility And Consistency Cloud Data Protection
Pillars Of Cloud Security Visibility And Consistency Cloud Data ProtectionThis slide depicts the visibility and consistency pillar of cloud security, and it further includes asset inventory, best cloud framework, and data security. Introducing Pillars Of Cloud Security Visibility And Consistency Cloud Data Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Cloud Framework, Data Security, Asset Inventory, using this template. Grab it now to reap its full benefits.
-
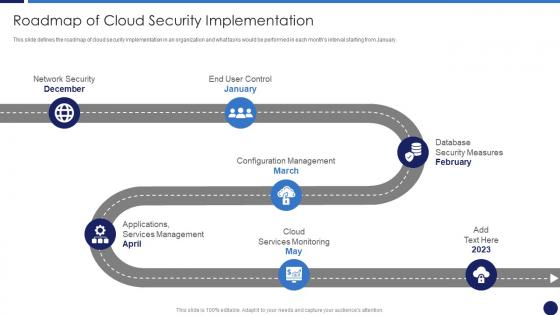 Roadmap Of Cloud Security Implementation Cloud Data Protection
Roadmap Of Cloud Security Implementation Cloud Data ProtectionThis slide defines the roadmap of cloud security implementation in an organization and what tasks would be performed in each months interval starting from January. Introducing Roadmap Of Cloud Security Implementation Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Cloud Services Monitoring, Services Management, Database Security Measures, Network Security, using this template. Grab it now to reap its full benefits.
-
 Segmentation Of Cloud Security Responsibilities Cloud Data Protection
Segmentation Of Cloud Security Responsibilities Cloud Data ProtectionThis slide shows cloud security responsibilities based on service type, namely Software as a Service SaaS, Platform as a service PaaS, Infrastructure as a Service IaaS. Increase audience engagement and knowledge by dispensing information using Segmentation Of Cloud Security Responsibilities Cloud Data Protection. This template helps you present information on three stages. You can also present information on Segmentation Of Cloud Security Responsibilities using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Table Of Contents For Cloud Data Protection Ppt Demonstration
Table Of Contents For Cloud Data Protection Ppt DemonstrationIntroducing Table Of Contents For Cloud Data Protection Ppt Demonstration to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Benefits Of Cloud Security, Architecture Of Cloud Security, Cloud Security Important, using this template. Grab it now to reap its full benefits.
-
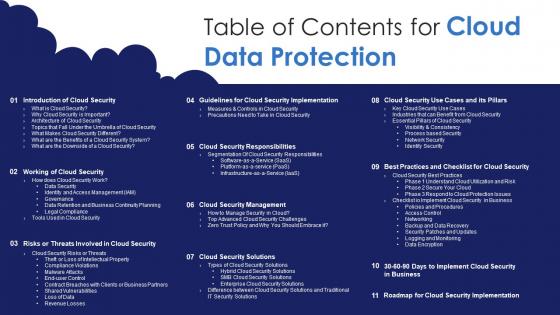 Table Of Contents For Cloud Data Protection Ppt Powerpoint Icons
Table Of Contents For Cloud Data Protection Ppt Powerpoint IconsIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Cloud Data Protection Ppt Powerpoint Icons. This template helps you present information on eleven stages. You can also present information on Cloud Security Responsibilities, Cloud Security Management, Working Of Cloud Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
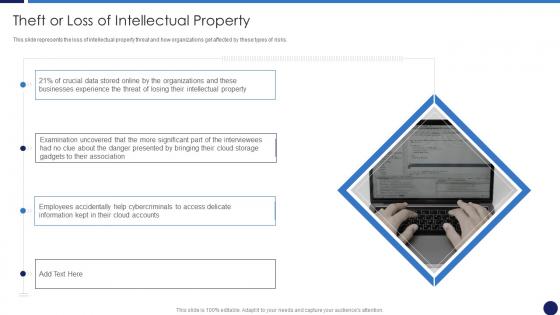 Theft Or Loss Of Intellectual Property Cloud Data Protection
Theft Or Loss Of Intellectual Property Cloud Data ProtectionThis slide represents the loss of intellectual property threat and how organizations get affected by these types of risks. Introducing Theft Or Loss Of Intellectual Property Cloud Data Protection to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Businesses Experience, Organizations, Cloud Storage, using this template. Grab it now to reap its full benefits.
-
 Types Of Cloud Security Solutions Cloud Data Protection
Types Of Cloud Security Solutions Cloud Data ProtectionThis slide represents the cloud security solutions such as hybrid cloud security solutions, SMB cloud security solutions, and enterprise cloud security solutions. Increase audience engagement and knowledge by dispensing information using Types Of Cloud Security Solutions Cloud Data Protection. This template helps you present information on three stages. You can also present information on Enterprise Cloud Security, Hybrid Cloud Security, Cloud Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 What Are The Benefits Of A Cloud Security System Cloud Data Protection
What Are The Benefits Of A Cloud Security System Cloud Data ProtectionThis slide represents the benefits of a cloud security system, such as efficient recovery, openness, no hardware requirement, DDOS protection, and data security. Introducing What Are The Benefits Of A Cloud Security System Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Efficient Recovery, Efficient Data Security, Business Capacity, using this template. Grab it now to reap its full benefits.
-
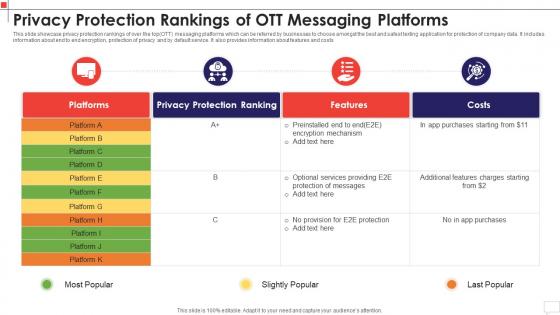 Privacy Protection Rankings Of Ott Messaging Platforms
Privacy Protection Rankings Of Ott Messaging PlatformsIntroducing our premium set of slides with Privacy Protection Rankings Of Ott Messaging Platforms. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Pricing Plans For Best Messaging Platforms. So download instantly and tailor it with your information.
-
 Icon Of Computer Security Program For Protection
Icon Of Computer Security Program For ProtectionIntroducing our premium set of slides with Icon Of Computer Security Program For Protection. Elucidate the one stage and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon Of Computer Security Program For Protection. So download instantly and tailor it with your information.
-
 Offsite data protection services ppt powerpoint presentation portfolio cpb
Offsite data protection services ppt powerpoint presentation portfolio cpbPresenting our Offsite Data Protection Services Ppt Powerpoint Presentation Portfolio Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Offsite Data Protection Services This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Banks offering payroll protection program ppt powerpoint presentation pictures deck cpb
Banks offering payroll protection program ppt powerpoint presentation pictures deck cpbPresenting our Banks Offering Payroll Protection Program Ppt Powerpoint Presentation Pictures Deck Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Banks Offering Payroll Protection Program. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
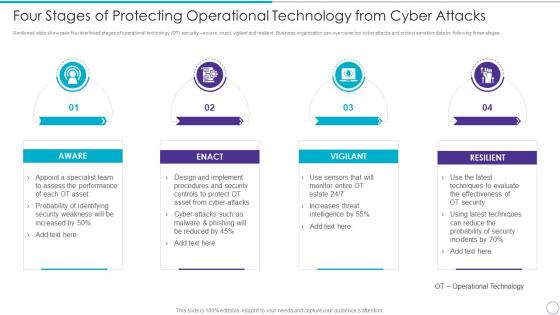 Four Stages Of Protecting Operational Technology From Cyber Attacks
Four Stages Of Protecting Operational Technology From Cyber AttacksMentioned slide showcase four interlinked stages of operational technology OT security aware, enact, vigilant and resilient. Business organization can overcome top cyber attacks and protect sensitive data by following these stages. Increase audience engagement and knowledge by dispensing information using four Stages Of Protecting Operational Technology From Cyber Attacks. This template helps you present information on four stages. You can also present information on Aware, Enact, Vigilant, Resilient using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
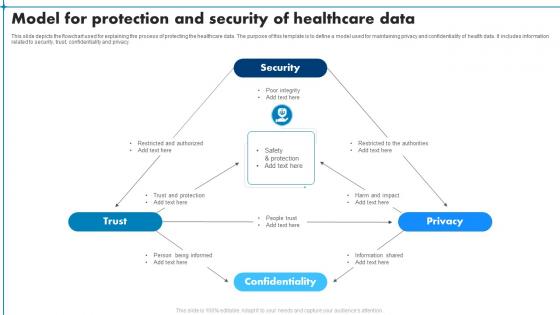 Model For Protection And Security Of Healthcare Data
Model For Protection And Security Of Healthcare DataThis slide depicts the flowchart used for explaining the process of protecting the healthcare data. The purpose of this template is to define a model used for maintaining privacy and confidentiality of health data. It includes information related to security, trust, confidentiality and privacy. Introducing our Model For Protection And Security Of Healthcare Data set of slides. The topics discussed in these slides are Security, Trust, Confidentiality, Privacy. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Post COVID Business Recovery Playbook Use Of Protective Equipment At Workplace
Post COVID Business Recovery Playbook Use Of Protective Equipment At WorkplaceThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Introducing Post COVID Business Recovery Playbook Use Of Protective Equipment At Workplace to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Masks And Respirators, Gloves, Face Shields, using this template. Grab it now to reap its full benefits.
-
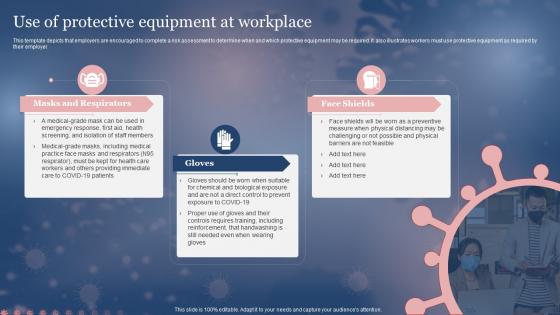 Use Of Protective Equipment At Workplace Framework For Post Pandemic Business Planning
Use Of Protective Equipment At Workplace Framework For Post Pandemic Business PlanningThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Increase audience engagement and knowledge by dispensing information using Use Of Protective Equipment At Workplace Framework For Post Pandemic Business Planning. This template helps you present information on three stages. You can also present information on Protective, Equipment, Workplace using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Application Firewall Features of WAF Protection Against Known and Unknown Attacks
Application Firewall Features of WAF Protection Against Known and Unknown AttacksThis slide describes another web application firewall feature that protects against known and unknown attacks by incorporating security models such as the negative model, hybrid model, and positive model. Increase audience engagement and knowledge by dispensing information using Application Firewall Features of WAF Protection Against Known and Unknown Attacks. This template helps you present information on three stages. You can also present information on Negative Model, Hybrid Model, Positive Model using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
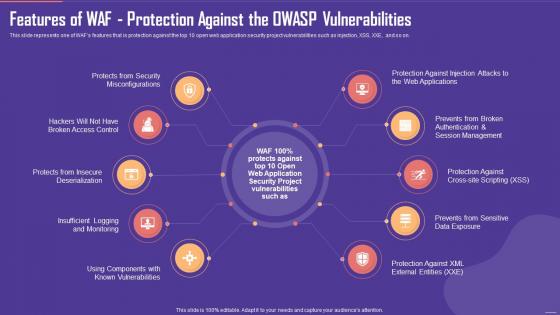 Application Firewall Features of WAF Protection Against the OWASP Vulnerabilities
Application Firewall Features of WAF Protection Against the OWASP VulnerabilitiesThis slide represents one of WAFs features that is protection against the top 10 open web application security project vulnerabilities such as injection, XSS, XXE, and so on. Introducing Application Firewall Features of WAF Protection Against the OWASP Vulnerabilities to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Web Applications, Security Misconfigurations, Insecure Deserialization, using this template. Grab it now to reap its full benefits.
-
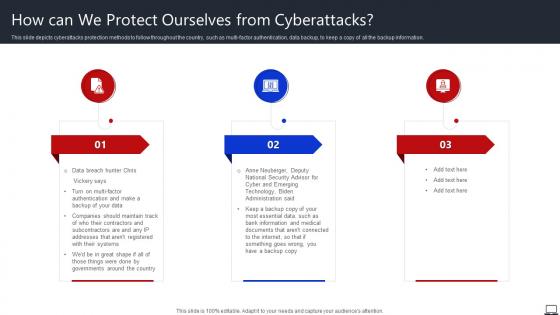 How Can We Protect Ourselves From Cyberattacks String Of Cyber Attacks Against
How Can We Protect Ourselves From Cyberattacks String Of Cyber Attacks AgainstThis slide depicts cyberattacks protection methods to follow throughout the country, such as multi factor authentication, data backup, to keep a copy of all the backup information. Increase audience engagement and knowledge by dispensing information using How Can We Protect Ourselves From Cyberattacks String Of Cyber Attacks Against. This template helps you present information on three stages. You can also present information on Governments, Backup Copy, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
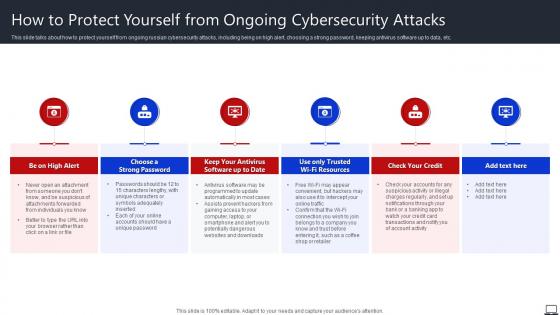 How To Protect Yourself From Ongoing Cybersecurity Attacks String Of Cyber Attacks
How To Protect Yourself From Ongoing Cybersecurity Attacks String Of Cyber AttacksThis slide talks about how to protect yourself from ongoing russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Introducing How To Protect Yourself From Ongoing Cybersecurity Attacks String Of Cyber Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Choose A Strong Password, Check Your Credit, Unique Password, using this template. Grab it now to reap its full benefits.
-
 Personal Protective Equipment For Construction Enhancing Safety Of Civil Construction Site
Personal Protective Equipment For Construction Enhancing Safety Of Civil Construction SiteThis slide showcase the overview of personal protective equipment that construction site workers must wear to prevent injuries. It also contains details of key components of the construction PPE kit such as eye, face, foot, hand, head, and hearing protection.Introducing Personal Protective Equipment For Construction Enhancing Safety Of Civil Construction Site to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Head Protection, Foot Protection, Hearing Protection, using this template. Grab it now to reap its full benefits.
-
 Icon Of Security Incident Management For Data Protection
Icon Of Security Incident Management For Data ProtectionIntroducing our premium set of slides with Icon Of Security Incident Management For Data Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon Of Security Incident, Management For Data ProtectionIcon Of Security Incident, Management For Data Protection. So download instantly and tailor it with your information.
-
 Use Of Protective Equipment At Workplace Pandemic Business Strategy Playbook
Use Of Protective Equipment At Workplace Pandemic Business Strategy PlaybookThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Introducing Use Of Protective Equipment At Workplace Pandemic Business Strategy Playbook to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Masks And Respirators, Gloves, Face Shields, using this template. Grab it now to reap its full benefits.
-
 Use Of Protective Equipment At Workplace Pandemic Business Playbook
Use Of Protective Equipment At Workplace Pandemic Business PlaybookThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer Present the topic in a bit more detail with this Use Of Protective Equipment At Workplace Pandemic Business Playbook. Use it as a tool for discussion and navigation on Protective, Equipment, Workplace. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Use Of Protective Equipment At Workplace New Normal Adaption Playbook
Use Of Protective Equipment At Workplace New Normal Adaption PlaybookThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Introducing Use Of Protective Equipment At Workplace New Normal Adaption Playbook to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Masks And Respirators, Gloves, Face Shields, using this template. Grab it now to reap its full benefits.
-
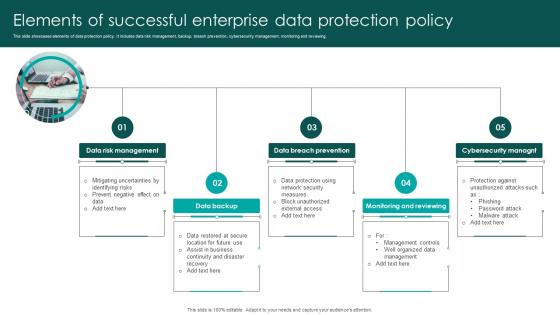 Elements Of Successful Enterprise Data Protection Policy
Elements Of Successful Enterprise Data Protection PolicyThis slide showcases elements of data protection policy. It includes data risk management, backup, breach prevention, cybersecurity management, monitoring and reviewing. Introducing our premium set of slides with Elements Of Successful Enterprise Data Protection Policy. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Risk Management, Data Breach Prevention, Monitoring And Reviewing. So download instantly and tailor it with your information.
-
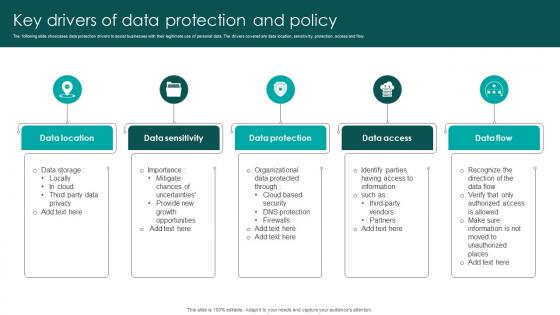 Key Drivers Of Data Protection And Policy
Key Drivers Of Data Protection And PolicyThe following slide showcases data protection drivers to assist businesses with their legitimate use of personal data. The drivers covered are data location, sensitivity, protection, access and flow. Presenting our set of slides with Key Drivers Of Data Protection And Policy. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Location, Data Sensitivity, Data Protection, Data Access.
-
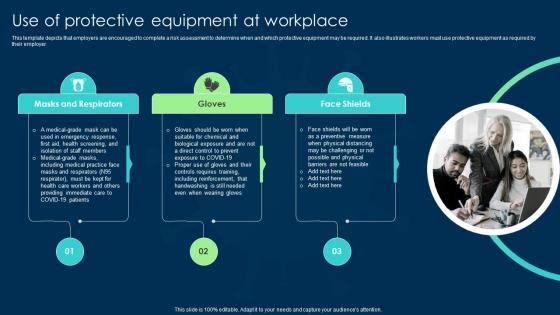 Use Of Protective Equipment At Workplace Business Transformation Guidelines
Use Of Protective Equipment At Workplace Business Transformation GuidelinesIntroducing Use Of Protective Equipment At Workplace Business Transformation Guidelines to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Including Reinforcement, Controls Requires, Handwashing Still, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents AML Transaction Assessment Tool For Protecting Organizations From Frauds
Table Of Contents AML Transaction Assessment Tool For Protecting Organizations From FraudsPresent the topic in a bit more detail with this Table Of Contents AML Transaction Assessment Tool For Protecting Organizations From Frauds. Use it as a tool for discussion and navigation on Transactions Profiles, Blockchain Technology, Transactions Alerts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
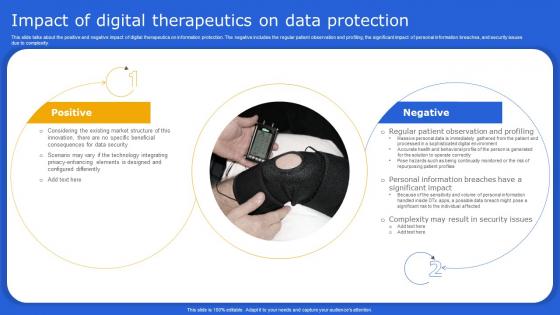 Digital Therapeutics It Impact Of Digital Therapeutics On Data Protection Ppt Show Microsoft
Digital Therapeutics It Impact Of Digital Therapeutics On Data Protection Ppt Show MicrosoftThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Increase audience engagement and knowledge by dispensing information using Digital Therapeutics It Impact Of Digital Therapeutics On Data Protection Ppt Show Microsoft This template helps you present information on two stages. You can also present information on Security Issues, Result, Significant Impact, Observation And Profiling using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
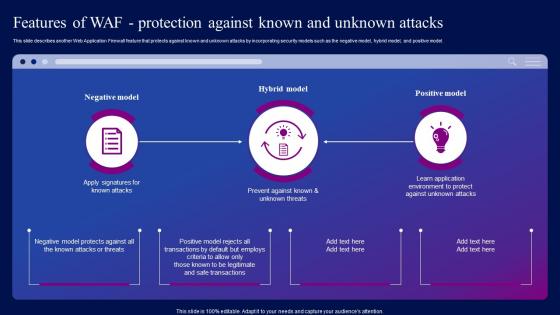 Features Of WAF Protection Against Known And Web Application Firewall Features Ppt Brochure
Features Of WAF Protection Against Known And Web Application Firewall Features Ppt BrochureThis slide describes another Web Application Firewall feature that protects against known and unknown attacks by incorporating security models such as the negative model, hybrid model, and positive model. Deliver an outstanding presentation on the topic using this Features Of WAF Protection Against Known And Web Application Firewall Features Ppt Brochure. Dispense information and present a thorough explanation of Protection, Attacks, Positive using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
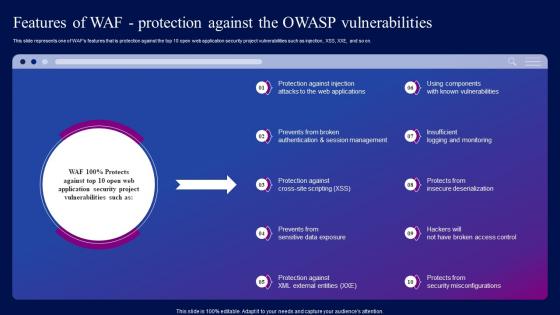 Web Application Firewall Features Of WAF Protection Against The OWASP Vulnerabilities Ppt Inspiration
Web Application Firewall Features Of WAF Protection Against The OWASP Vulnerabilities Ppt InspirationThis slide represents one of WAFs features that is protection against the top 10 open web application security project vulnerabilities such as injection, XSS, XXE, and so on. Present the topic in a bit more detail with this Web Application Firewall Features Of WAF Protection Against The OWASP Vulnerabilities Ppt Inspiration. Use it as a tool for discussion and navigation on Protection, Vulnerabilities, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
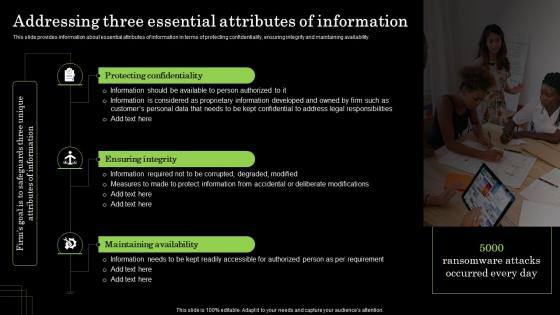 Addressing Three Essential Attributes Of Information Defense Plan To Protect Firm Assets
Addressing Three Essential Attributes Of Information Defense Plan To Protect Firm AssetsThis slide provides information about essential attributes of information in terms of protecting confidentiality, ensuring integrity and maintaining availability. Increase audience engagement and knowledge by dispensing information using Addressing Three Essential Attributes Of Information Defense Plan To Protect Firm Assets. This template helps you present information on Three stages. You can also present information on Protecting Confidentiality, Ensuring Integrity, Maintaining Availability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Defense Plan To Protect Firm
Table Of Contents Defense Plan To Protect FirmIntroducing Table Of Contents Defense Plan To Protect Firm to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Security Centre, Sensitive Data, Brand Protection, using this template. Grab it now to reap its full benefits.
-
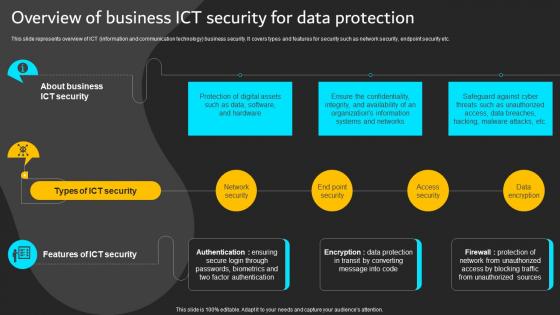 Overview Of Business ICT Security Data Protection Implementation ICT Strategic Plan Strategy SS
Overview Of Business ICT Security Data Protection Implementation ICT Strategic Plan Strategy SSThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc.Present the topic in a bit more detail with this Overview Of Business ICT Security Data Protection Implementation ICT Strategic Plan Strategy SS. Use it as a tool for discussion and navigation on Factor Authentication, Organizations Information, Ensure Confidentiality. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
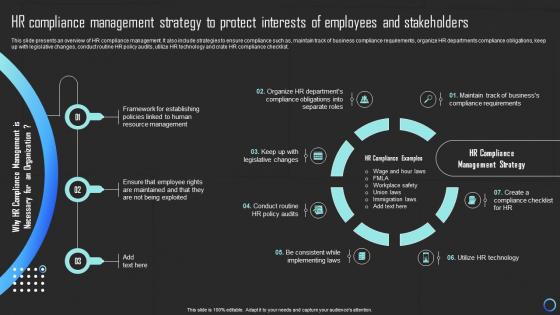 HR Compliance Management Strategy To Protect Interests Of Employees And Stakeholders Strategy SS
HR Compliance Management Strategy To Protect Interests Of Employees And Stakeholders Strategy SSThis slide presents an overview of HR compliance management. It also include strategies to ensure compliance such as, maintain track of business compliance requirements, organize HR departments compliance obligations, keep up with legislative changes, conduct routine HR policy audits, utilize HR technology and crate HR compliance checklist. Present the topic in a bit more detail with this HR Compliance Management Strategy To Protect Interests Of Employees And Stakeholders Strategy SS. Use it as a tool for discussion and navigation on Strategy, Employees, Stakeholders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
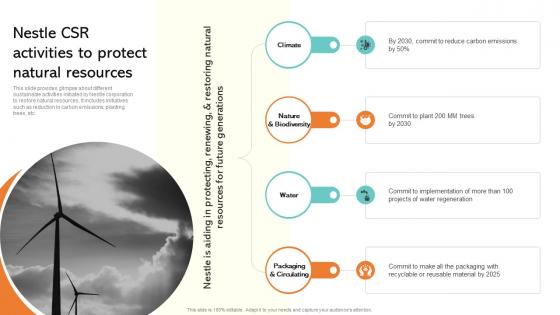 Nestle CSR Activities To Protect Natural Resources Strategic Management Report Of Consumer MKT SS V
Nestle CSR Activities To Protect Natural Resources Strategic Management Report Of Consumer MKT SS VThis slide provides glimpse about different sustainable activities initiated by Nestle corporation to restore natural resources. It includes initiatives such as reduction in carbon emissions, planting trees, etc. Increase audience engagement and knowledge by dispensing information using Nestle CSR Activities To Protect Natural Resources Strategic Management Report Of Consumer MKT SS V. This template helps you present information on four stages. You can also present information on Climate, Nature, Material using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
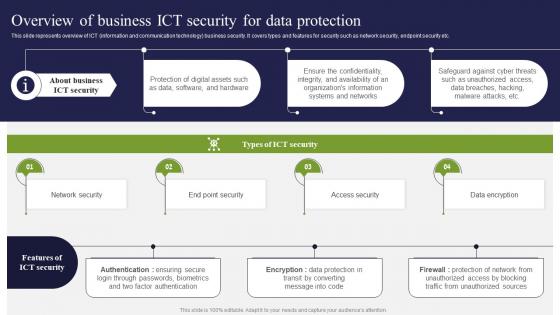 Overview Of Business ICT Security For Data Protection ICT Strategic Framework Strategy SS V
Overview Of Business ICT Security For Data Protection ICT Strategic Framework Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Present the topic in a bit more detail with this Overview Of Business ICT Security For Data Protection ICT Strategic Framework Strategy SS V. Use it as a tool for discussion and navigation on Network Security, Access Security, Data Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 5 padlock and metal chain concept of protection
5 padlock and metal chain concept of protectionPresenting 5 padlock and metal chain concept of protection. This is a 5 padlock and metal chain concept of protection. This is a five stage process. The stages in this process are padlock, lock, locker.
-
 Money bag protection of finance bag exchange of currencies ppt icons graphics
Money bag protection of finance bag exchange of currencies ppt icons graphicsWe are proud to present our money bag protection of finance bag exchange of currencies ppt icons graphics. Graphic of currency, bag and protection icons has been used to design this power point icon template. This icon template diagram contains the concept of currency exchange and money protection. This icon template is suitable for business and finance related presentations.
-
 Protect the carton data management settings of document search ppt icons graphics
Protect the carton data management settings of document search ppt icons graphicsPresenting protect the carton data management settings of document search ppt icons graphics. This Power Point icons template slide has been crafted with graphic of four data icons. This PPT diagram contains the concept of protection and data management . Use this PPT diagram for business and marketing related presentations.
-
 House to protect cycle of sale ppt icons graphics
House to protect cycle of sale ppt icons graphicsPresenting house to protect cycle of sale ppt icons graphics. This Power Point icon template slide has been crafted with graphic of house icons. This icon PPT slide contains the concept of sales cycle representation. Use this PPT slide for business and real-estate related presentations.
-
 Safety ring certificate financial safety notes protection of currencies ppt icons graphics
Safety ring certificate financial safety notes protection of currencies ppt icons graphicsPresenting safety ring certificate financial safety notes protection of currencies ppt icons graphics. Presenting safety ring certificate financial safety notes protection of currencies ppt icons graphics. This Power Point icons template slide has been crafted with graphic of safety ring, certificate and finance icons. This icon template contains the concept of currency protection. Use this PPT slide for business and finance related presentations.
-
 Shopping basket size protected data afraid of water ppt icons graphics
Shopping basket size protected data afraid of water ppt icons graphicsPresenting shopping basket size protected data afraid of water ppt icons graphics. This Power Point icon template has been crafted with graphic of shopping basket and data icons. This PPT icon slide contains the concept of data protection and shopping skills representation. This icon template diagram can be used for sales and safety related presentations.



