Powerpoint Templates and Google slides for Risks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Determine Cyber Security Risks And Threats Implementing Cyber Risk Management Process
Determine Cyber Security Risks And Threats Implementing Cyber Risk Management ProcessThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Present the topic in a bit more detail with this Determine Cyber Security Risks And Threats Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Details, Objectives, Issue Identifier. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
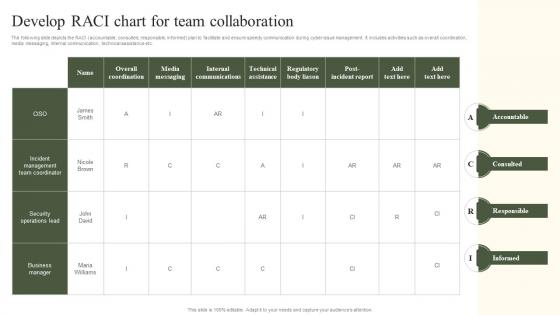 Develop RACI Chart For Team Collaboration Implementing Cyber Risk Management Process
Develop RACI Chart For Team Collaboration Implementing Cyber Risk Management ProcessThe following slide depicts the RACI accountable, consulted, responsible, informed plan to facilitate and ensure speedy communication during cyber issue management. It includes activities such as overall coordination, media messaging, internal communication, technical assistance etc. Deliver an outstanding presentation on the topic using this Develop RACI Chart For Team Collaboration Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Accountable, Consulted, Responsible, Informed using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
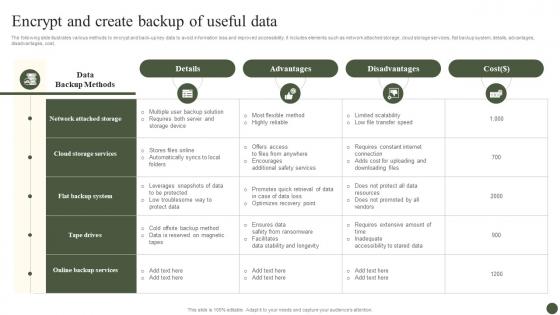 Encrypt And Create Backup Of Useful Data Implementing Cyber Risk Management Process
Encrypt And Create Backup Of Useful Data Implementing Cyber Risk Management ProcessThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost. Present the topic in a bit more detail with this Encrypt And Create Backup Of Useful Data Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Details, Advantages, Disadvantages. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
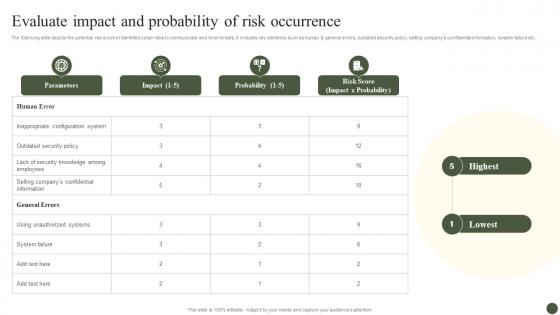 Evaluate Impact And Probability Of Risk Occurrence Implementing Cyber Risk Management Process
Evaluate Impact And Probability Of Risk Occurrence Implementing Cyber Risk Management ProcessThe following slide depicts the potential risk score of identified cyber risks to communicate and level threats. It includes key elements such as human and general errors, outdated security policy, selling companys confidential information, system failure etc. Deliver an outstanding presentation on the topic using this Evaluate Impact And Probability Of Risk Occurrence Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Parameters, Impact, Probability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
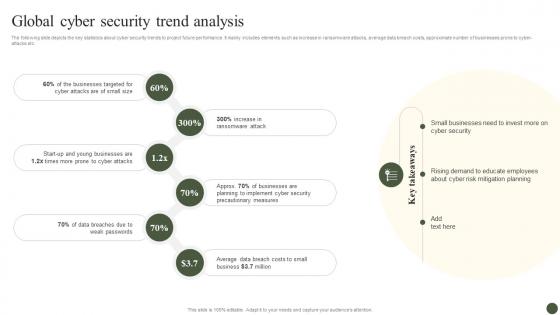 Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process
Global Cyber Security Trend Analysis Implementing Cyber Risk Management ProcessThe following slide depicts the key statistics about cyber security trends to project future performance. It mainly includes elements such as increase in ransomware attacks, average data breach costs, approximate number of businesses prone to cyber-attacks etc. Introducing Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Businesses Targeted, Ransomware Attack, Cyber Attacks, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Implementing Cyber Risk Management Process
Icons Slide For Implementing Cyber Risk Management ProcessIntroducing our well researched set of slides titled Icons Slide For Implementing Cyber Risk Management Process. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
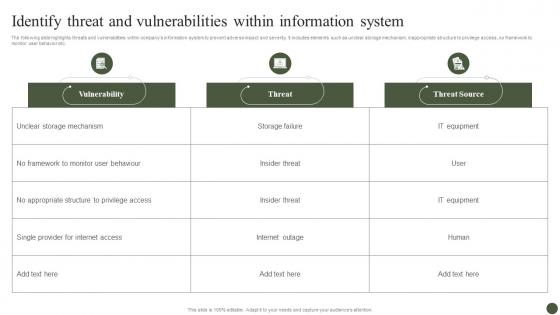 Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process
Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management ProcessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Present the topic in a bit more detail with this Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Vulnerability, Threat, Threat Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
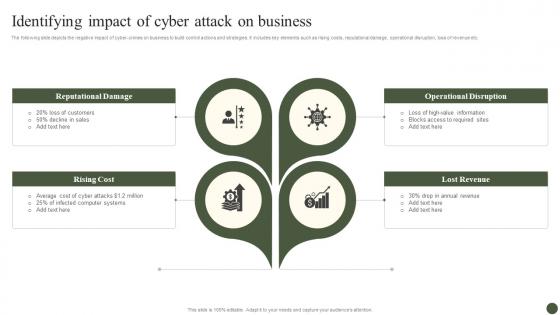 Identifying Impact Of Cyber Attack On Business Implementing Cyber Risk Management Process
Identifying Impact Of Cyber Attack On Business Implementing Cyber Risk Management ProcessThe following slide depicts the negative impact of cyber-crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Increase audience engagement and knowledge by dispensing information using Identifying Impact Of Cyber Attack On Business Implementing Cyber Risk Management Process. This template helps you present information on four stages. You can also present information on Reputational Damage, Rising Cost, Operational Disruption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Impact Of Cyber Safety Security Measures Implementing Cyber Risk Management Process
Impact Of Cyber Safety Security Measures Implementing Cyber Risk Management ProcessThe following slide depicts the projected consequences of implementing cyber security preventive measures. It includes data about number of cyber attracts pre and post adopting latest strategies. Present the topic in a bit more detail with this Impact Of Cyber Safety Security Measures Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Cyber Attack Type, Remarks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Cyber Security Policies And Practices Implementing Cyber Risk Management Process
Impact Of Cyber Security Policies And Practices Implementing Cyber Risk Management ProcessThe following slide focuses on drafting cyber security policies to manage data control and breach. It mainly includes elements such as impact of existing cyber safety policies, mitigation actions. Deliver an outstanding presentation on the topic using this Impact Of Cyber Security Policies And Practices Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Inadequate Security Guidelines, Inappropriate Privacy Policies, Insufficient Background Check using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
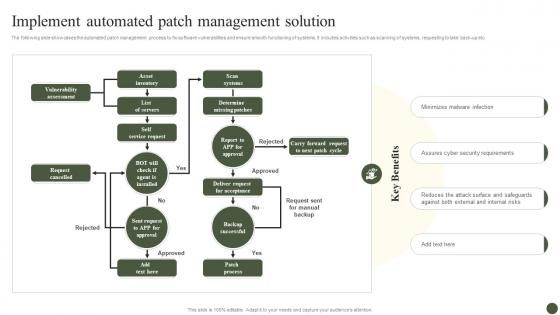 Implement Automated Patch Management Solution Implementing Cyber Risk Management Process
Implement Automated Patch Management Solution Implementing Cyber Risk Management ProcessThe following slide showcases the automated patch management process to fix software vulnerabilities and ensure smooth functioning of systems. It includes activities such as scanning of systems, requesting to take back-up etc. Present the topic in a bit more detail with this Implement Automated Patch Management Solution Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Vulnerability Assessment, List Of Servers, Determine Missing Patches. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementing Cyber Risk Management Process Table Of Contents
Implementing Cyber Risk Management Process Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Implementing Cyber Risk Management Process Table Of Contents. This template helps you present information on one stages. You can also present information on Understanding Cyber Security, Risk Management Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
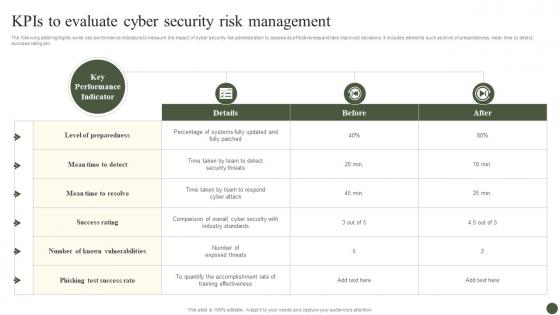 KPIs To Evaluate Cyber Security Risk Management Implementing Cyber Risk Management Process
KPIs To Evaluate Cyber Security Risk Management Implementing Cyber Risk Management ProcessThe following slide highlights some key performance indicators to measure the impact of cyber security risk administration to assess its effectiveness and take improved decisions. It includes elements such as level of preparedness, mean time to detect, success rating etc. Present the topic in a bit more detail with this KPIs To Evaluate Cyber Security Risk Management Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Details, Before, After. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
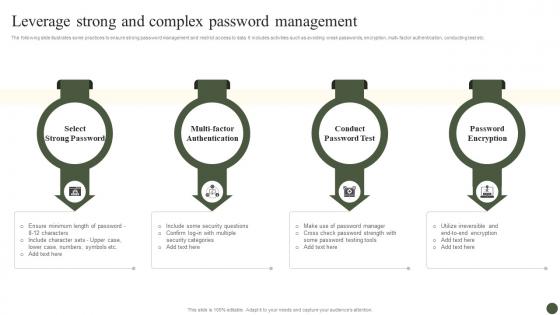 Leverage Strong And Complex Password Management Implementing Cyber Risk Management Process
Leverage Strong And Complex Password Management Implementing Cyber Risk Management ProcessThe following slide illustrates some practices to ensure strong password management and restrict access to data. It includes activities such as avoiding weak passwords, encryption, multi-factor authentication, conducting test etc. Introducing Leverage Strong And Complex Password Management Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Select Strong Password, Conduct Password Test, Password Encryption, using this template. Grab it now to reap its full benefits.
-
 Monitor And Assess Vendor Risk Management Implementing Cyber Risk Management Process
Monitor And Assess Vendor Risk Management Implementing Cyber Risk Management ProcessThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Introducing Monitor And Assess Vendor Risk Management Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Details, Reviews, using this template. Grab it now to reap its full benefits.
-
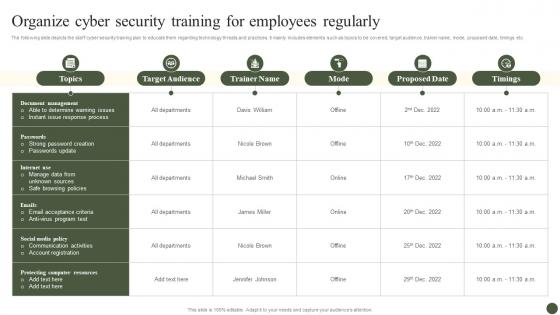 Organize Cyber Security Training For Employees Regularly Implementing Cyber Risk Management Process
Organize Cyber Security Training For Employees Regularly Implementing Cyber Risk Management ProcessThe following slide depicts the staff cyber security training plan to educate them regarding technology threats and practices. It mainly includes elements such as topics to be covered, target audience, trainer name, mode, proposed date, timings etc. Present the topic in a bit more detail with this Organize Cyber Security Training For Employees Regularly Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Target Audience, Trainer Name, Mode. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Plan Useful Data Backup Schedule Implementing Cyber Risk Management Process
Plan Useful Data Backup Schedule Implementing Cyber Risk Management ProcessThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Deliver an outstanding presentation on the topic using this Plan Useful Data Backup Schedule Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Monday, Tuesday, Wednesday, Thursday using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
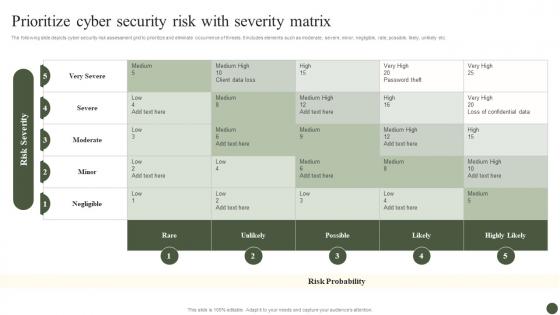 Prioritize Cyber Security Risk With Severity Matrix Implementing Cyber Risk Management Process
Prioritize Cyber Security Risk With Severity Matrix Implementing Cyber Risk Management ProcessThe following slide depicts cyber security risk assessment grid to prioritize and eliminate occurrence of threats. It includes elements such as moderate, severe, minor, negligible, rate, possible, likely, unlikely etc. Present the topic in a bit more detail with this Prioritize Cyber Security Risk With Severity Matrix Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Rare, Unlikely, Possible. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
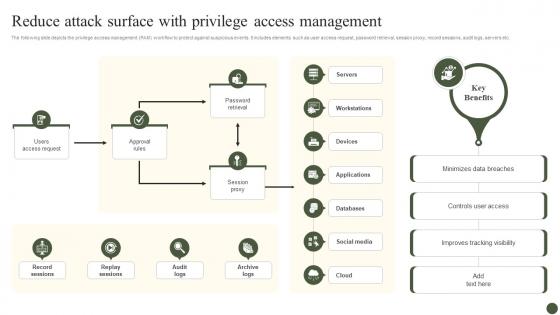 Reduce Attack Surface With Privilege Access Management Implementing Cyber Risk Management Process
Reduce Attack Surface With Privilege Access Management Implementing Cyber Risk Management ProcessThe following slide depicts the privilege access management PAM workflow to protect against suspicious events. It includes elements such as user access request, password retrieval, session proxy, record sessions, audit logs, servers etc. Deliver an outstanding presentation on the topic using this Reduce Attack Surface With Privilege Access Management Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Users Access Request, Approval Rules, Session Proxy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
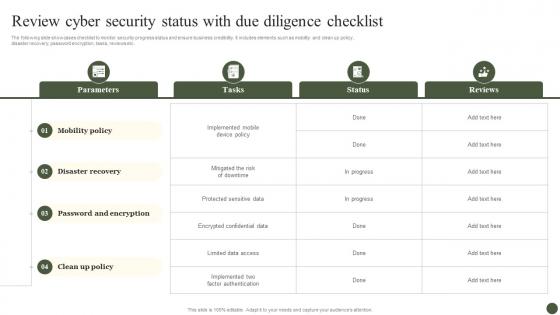 Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management Process
Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management ProcessThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Present the topic in a bit more detail with this Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Parameters, Tasks, Status, Reviews. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
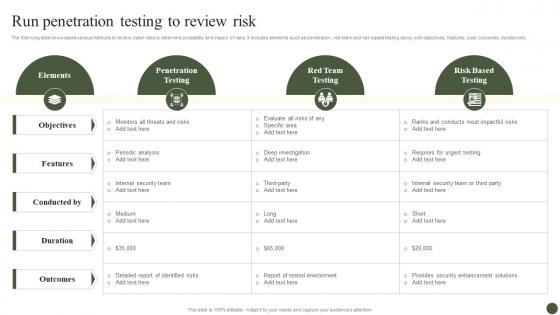 Run Penetration Testing To Review Risk Implementing Cyber Risk Management Process
Run Penetration Testing To Review Risk Implementing Cyber Risk Management ProcessThe following slide showcases various methods to review cyber risks to determine probability and impact of risks. It includes elements such as penetration, red team and risk based testing along with objectives, features, cost, outcomes, duration etc. Deliver an outstanding presentation on the topic using this Run Penetration Testing To Review Risk Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Elements, Penetration Testing, Red Team Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Select Cybersecurity Training Program Courses Implementing Cyber Risk Management Process
Select Cybersecurity Training Program Courses Implementing Cyber Risk Management ProcessThe following slide showcases the best cybersecurity training courses to educate employees and minimize the possibility of cyber-attacks. It includes cloud, disaster recovery, hardware, information security programs, duration, mode and cost. Present the topic in a bit more detail with this Select Cybersecurity Training Program Courses Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Course Name, Duration, Mode, Start Date. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Select Tools To Reduce Cyber Security Failure Implementing Cyber Risk Management Process
Select Tools To Reduce Cyber Security Failure Implementing Cyber Risk Management ProcessThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Deliver an outstanding presentation on the topic using this Select Tools To Reduce Cyber Security Failure Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Features, Free Trial, Cost using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
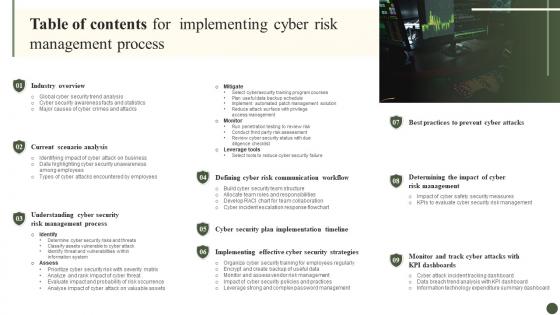 Table Of Contents For Implementing Cyber Risk Management Process
Table Of Contents For Implementing Cyber Risk Management ProcessIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Implementing Cyber Risk Management Process. This template helps you present information on nine stages. You can also present information on Industry Overview, Current Scenario Analysis, Prevent Cyber Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Types Of Cyber Attacks Encountered By Employees Implementing Cyber Risk Management Process
Types Of Cyber Attacks Encountered By Employees Implementing Cyber Risk Management ProcessThe following slide showcases the various types of cyber-attacks faced by staff to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service etc. Introducing Types Of Cyber Attacks Encountered By Employees Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Ransomware, Phishing, using this template. Grab it now to reap its full benefits.
-
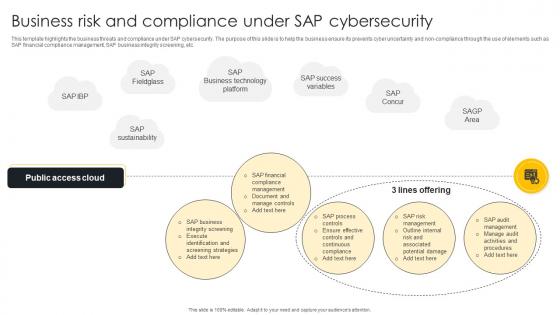 Business Risk And Compliance Under SAP Cybersecurity
Business Risk And Compliance Under SAP CybersecurityThis template highlights the business threats and compliance under SAP cybersecurity. The purpose of this slide is to help the business ensure its prevents cyber uncertainty and non compliance through the use of elements such as SAP financial compliance management, SAP business integrity screening, etc. Introducing our Business Risk And Compliance Under SAP Cybersecurity set of slides. The topics discussed in these slides are SAP Process Controls, SAP Risk Management, Outline Internal Risk. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
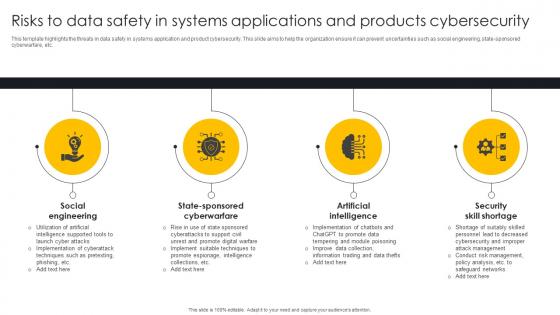 Risks To Data Safety In Systems Applications And Products Cybersecurity
Risks To Data Safety In Systems Applications And Products CybersecurityThis template highlights the threats in data safety in systems application and product cybersecurity. This slide aims to help the organization ensure it can prevent uncertainties such as social engineering, state sponsored cyberwarfare, etc. Presenting our set of slides with Risks To Data Safety In Systems Applications And Products Cybersecurity. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Social Engineering, State Sponsored Cyberwarfare, Artificial Intelligence.
-
 Risks Of Implementing It Solutions In Manufacturing Industry
Risks Of Implementing It Solutions In Manufacturing IndustryThis slide showcases the challenges of implementing IT solutions in the manufacturing industry. This slide aims to ensure the business safeguards its IT technologies to prevent supply chain attacks, intellectual property theft, etc. Presenting our set of slides with Risks Of Implementing It Solutions In Manufacturing Industry This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Breaches, Supply Chain Attacks, Intellectual Property Theft
-
 Credit Assessment And Risk Navigating The World Of Microfinance Basics To Innovation Fin SS
Credit Assessment And Risk Navigating The World Of Microfinance Basics To Innovation Fin SSThe below slide exhibits the credit assessment and risk management for microfinance. The different factors responsible are credit evaluation, collateral, portfolio diversification, and risk mitigation. Introducing Credit Assessment And Risk Navigating The World Of Microfinance Basics To Innovation Fin SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Credit Evaluation, Collateral And Guarantees, Portfolio Diversification, using this template. Grab it now to reap its full benefits.
-
 Microfinance Funding Risk Navigating The World Of Microfinance Basics To Innovation Fin SS
Microfinance Funding Risk Navigating The World Of Microfinance Basics To Innovation Fin SSThis slide provides the microfinance risk management for investors to minimize certain risks associated with wealth development. The different risk management categories are credit risk, operational risk and market risk. Increase audience engagement and knowledge by dispensing information using Microfinance Funding Risk Navigating The World Of Microfinance Basics To Innovation Fin SS. This template helps you present information on three stages. You can also present information on Credit Risk Management, Operational Risk Management, Market Risk Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
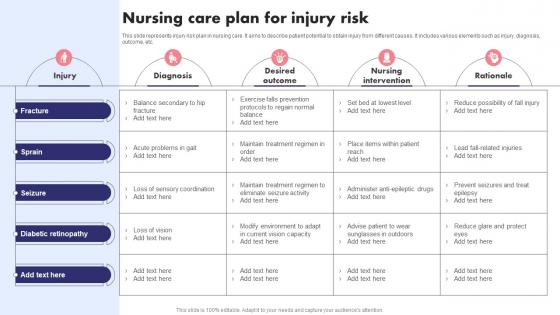 Nursing Care Plan For Injury Risk
Nursing Care Plan For Injury RiskThis slide represents injury risk plan in nursing care. It aims to describe patient potential to obtain injury from different causes. It includes various elements such as injury, diagnosis, outcome, etc. Presenting our well structured Nursing Care Plan For Injury Risk. The topics discussed in this slide are Nursing Care Plan, Injury Risk. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Risk Evaluation Within Food And Beverage Industry Global Food And Beverage Industry IR SS
Risk Evaluation Within Food And Beverage Industry Global Food And Beverage Industry IR SSThe slide depicts risk assessment for the food and beverage industry. It aims to educate the audience on the need of successfully recognizing and managing risks to maintain the stability. It covers potential hazards associated with the foodborne illness, supply chain disruption, consumer preferences, labor shortages. Present the topic in a bit more detail with this Risk Evaluation Within Food And Beverage Industry Global Food And Beverage Industry IR SS. Use it as a tool for discussion and navigation on Type Of Risk, Consequences, Risk Profile. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
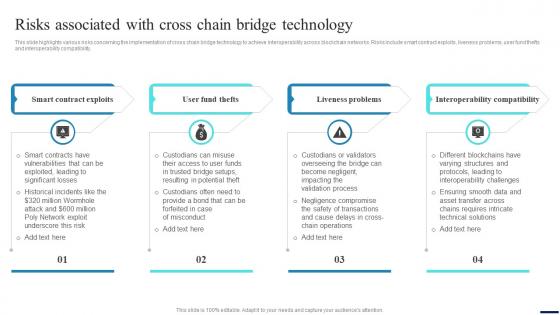 Connecting Ecosystems Introduction Risks Associated With Cross Chain Bridge BCT SS
Connecting Ecosystems Introduction Risks Associated With Cross Chain Bridge BCT SSThis slide highlights various risks concerning the implementation of cross chain bridge technology to achieve interoperability across blockchain networks. Risks include smart contract exploits, liveness problems, user fund thefts and interoperability compatibility. Introducing Connecting Ecosystems Introduction Risks Associated With Cross Chain Bridge BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Problems, Compatibility, Technology, using this template. Grab it now to reap its full benefits.
-
 Risks Associated With Decentralised Financing For Investors Understanding Role Of Decentralized BCT SS
Risks Associated With Decentralised Financing For Investors Understanding Role Of Decentralized BCT SSThis slide covers risks and challenges that investors may encounter when engaging with decentralized finance DeFi. It includes risks such as complexity due to multiple DeFi applications, outright scams, gas fees along with fluctuating yields, etc. Introducing Risks Associated With Decentralised Financing For Investors Understanding Role Of Decentralized BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Complexity, Outright Scams, Fluctuating Yields using this template. Grab it now to reap its full benefits.
-
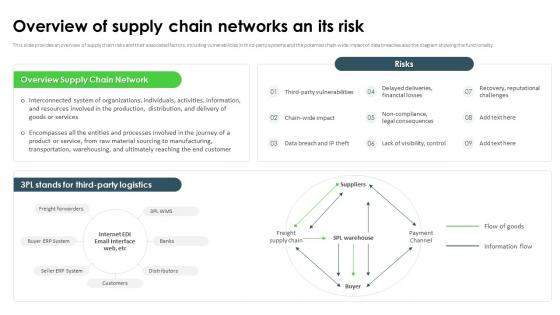 Ransomware In Digital Age Overview Of Supply Chain Networks An Its Risk
Ransomware In Digital Age Overview Of Supply Chain Networks An Its RiskThis slide provides an overview of supply chain risks and their associated factors, including vulnerabilities in third-party systems and the potential chain-wide impact of data breaches also the diagram showing the functionality. Increase audience engagement and knowledge by dispensing information using Ransomware In Digital Age Overview Of Supply Chain Networks An Its Risk. This template helps you present information on seven stages. You can also present information on Supply Chain Network, Freight Supply Chain, Raw Material Sourcing To Manufacturing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
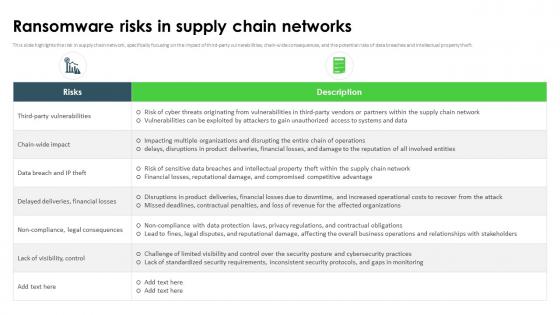 Ransomware In Digital Age Ransomware Risks In Supply Chain Networks
Ransomware In Digital Age Ransomware Risks In Supply Chain NetworksThis slide highlights the risk in supply chain network, specifically focusing on the impact of third-party vulnerabilities, chain-wide consequences, and the potential risks of data breaches and intellectual property theft. Present the topic in a bit more detail with this Ransomware In Digital Age Ransomware Risks In Supply Chain Networks. Use it as a tool for discussion and navigation on Third Party Vulnerabilities, Financial Losses, Standardized Security Requirements, Inconsistent Security Protocols. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Evaluating Types Of Risk In Defense Global Defense Industry Report IR SS
Evaluating Types Of Risk In Defense Global Defense Industry Report IR SSThis slide highlights the potential risks associated with the global Defense industry. This slide comprises the major concerns such as economic, geopolitical, technological, manufacturing, pandemic, environmental, safety, and information security threats. Deliver an outstanding presentation on the topic using this Evaluating Types Of Risk In Defense Global Defense Industry Report IR SS. Dispense information and present a thorough explanation of Brand Reputation, Regulatory Compliance, Competitive Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
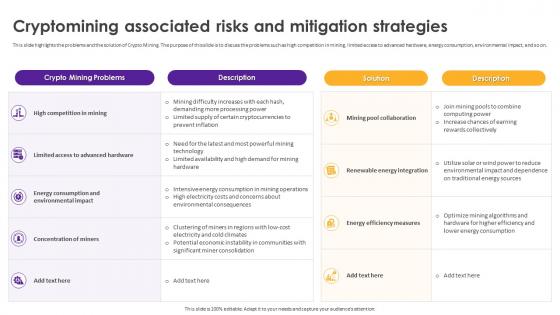 Cryptomining Innovations And Trends Cryptomining Associated Risks And Mitigation Strategies
Cryptomining Innovations And Trends Cryptomining Associated Risks And Mitigation StrategiesThis slide highlights the problems and the solution of Crypto Mining. The purpose of this slide is to discuss the problems such as high competition in mining, limited access to advanced hardware, energy consumption, environmental impact, and so on. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Cryptomining Associated Risks And Mitigation Strategies. Use it as a tool for discussion and navigation on High Competition In Mining, Concentration Of Miners, Energy Consumption, Environmental Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risks Assessment For Global Telemedicine Industry Outlook IR SS
Risks Assessment For Global Telemedicine Industry Outlook IR SSThis slide exhibits the risks assessment for global Telemedicine industry which includes risk type, consequences, risk profile and rating. It further includes risk type such as vendor risk, reimbursements, etc. Deliver an outstanding presentation on the topic using this Risks Assessment For Global Telemedicine Industry Outlook IR SS. Dispense information and present a thorough explanation of Reimbursements, Compliance Documentation, Malpractice Insurance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icon For Automation Compliance Risk Management
Icon For Automation Compliance Risk ManagementPresenting our set of slides with name Icon For Automation Compliance Risk Management. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon For Automation Compliance, Risk Management.
-
 Continuity Operations Plan For Risk Mitigation
Continuity Operations Plan For Risk MitigationThis slide represents continuity of operation plan for business risk mitigation including loss of facility access, workforce reduction, and equipment failure. Introducing our Continuity Operations Plan For Risk Mitigation set of slides. The topics discussed in these slides are Loss Of Facility Access, Workforce Reduction, Equipment Failure.This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Operation Continuity Plan Icon For Risk Mitigation
Operation Continuity Plan Icon For Risk MitigationPresenting our set of slides with Operation Continuity Plan Icon For Risk Mitigation. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Operation Continuity Plan Icon, Risk Mitigation.
-
 Features Of Effective Insurance Mitigating Travelling Risks
Features Of Effective Insurance Mitigating Travelling RisksThis slide represents various features of effective travel insurance assisting companies to mitigate all risks during business trips. It include features such as trip cancellation coverage, trip delay coverage, trip interruption coverage, etc. Presenting our well structured Features Of Effective Insurance Mitigating Travelling Risks. The topics discussed in this slide are Trip Cancellation Coverage, Trip Delay Coverage, Trip Interruption Coverage. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Travel Insurance Icon For Mitigating Aviation Risk Incidents
Travel Insurance Icon For Mitigating Aviation Risk IncidentsIntroducing our premium set of slides with Travel Insurance Icon For Mitigating Aviation Risk Incidents. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Travel Insurance Icon, Mitigating Aviation Risk Incidents. So download instantly and tailor it with your information.
-
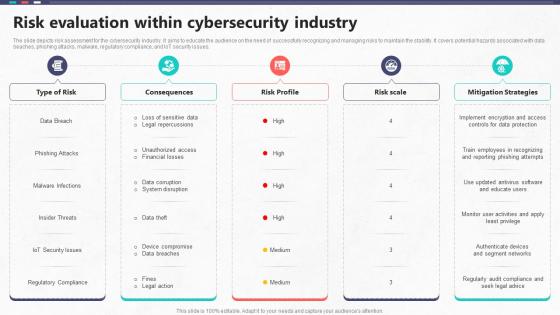 Risk Evaluation Within Cybersecurity Industry Global Cybersecurity Industry Outlook
Risk Evaluation Within Cybersecurity Industry Global Cybersecurity Industry OutlookThe slide depicts risk assessment for the cybersecurity industry. It aims to educate the audience on the need of successfully recognizing and managing risks to maintain the stability. It covers potential hazards associated with data beaches, phishing attacks, malware, regulatory compliance, and IoT security issues. Present the topic in a bit more detail with this Risk Evaluation Within Cybersecurity Industry Global Cybersecurity Industry Outlook. Use it as a tool for discussion and navigation on Type Of Risk, Risk Profile, Mitigation Strategies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
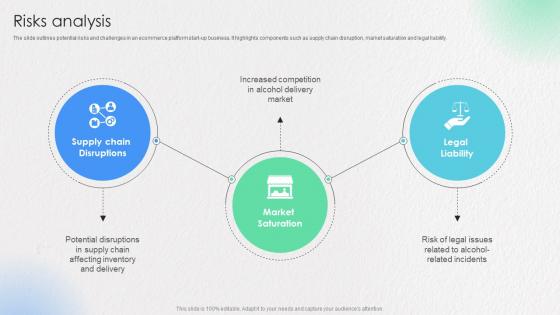 Risks Analysis Ecommerce Startup Go To Market Strategy GTM SS
Risks Analysis Ecommerce Startup Go To Market Strategy GTM SSThe slide outlines potential risks and challenges in an ecommerce platform start up business. It highlights components such as supply chain disruption, market saturation and legal liability. Deliver an outstanding presentation on the topic using this Risks Analysis Ecommerce Startup Go To Market Strategy GTM SS Dispense information and present a thorough explanation of Supply Chain, Market Saturation, Legal Liability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
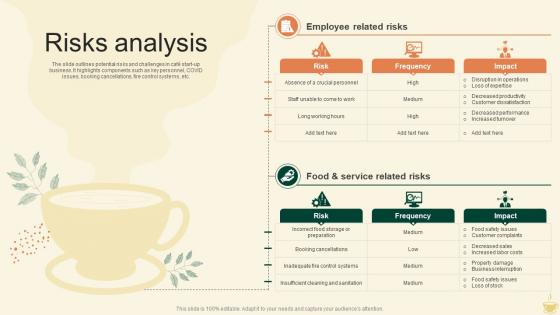 Risks Analysis Cafe Startup Go To Market Strategy GTM SS
Risks Analysis Cafe Startup Go To Market Strategy GTM SSThe slide outlines potential risks and challenges in cafe start up business. It highlights components such as key personnel, COVID issues, booking cancellations, fire control systems, etc. Present the topic in a bit more detail with this Risks Analysis Cafe Startup Go To Market Strategy GTM SS Use it as a tool for discussion and navigation on Risk, Frequency, Impact This template is free to edit as deemed fit for your organization. Therefore download it now.
-
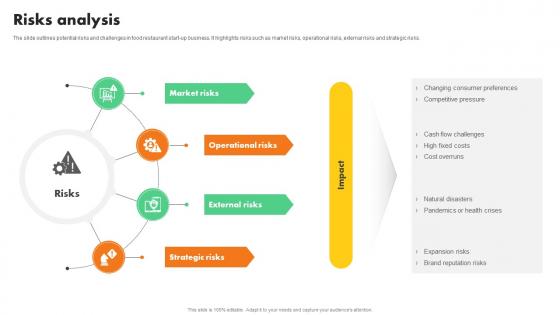 Risks Analysis Online Food Restaurant Startup Go To Market Strategy GTM SS
Risks Analysis Online Food Restaurant Startup Go To Market Strategy GTM SSThe slide outlines potential risks and challenges in food restaurant start up business. It highlights risks such as market risks, operational risks, external risks and strategic risks. Present the topic in a bit more detail with this Risks Analysis Online Food Restaurant Startup Go To Market Strategy GTM SS Use it as a tool for discussion and navigation on Market Risks, Operational Risks, External Risks This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Best Practices In Cyber Security Risk Management
Best Practices In Cyber Security Risk ManagementThis slide exhibits cyber risk management practices which enable businesses to prioritize risks and apply the right kinds of security controls to minimize impact. It include adaptive and continuous risk management, strict security protocols, cyber security risk management strategy. Introducing our premium set of slides with Best Practices In Cyber Security Risk Management. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Know Organizations IT Environment And Assets. Impose Strict Security Protocols, Adaptive And Continuous Risk Management . So download instantly and tailor it with your information.
-
 Computer Security Icon For Cyber Risk Management
Computer Security Icon For Cyber Risk ManagementPresenting our set of slides with Computer Security Icon For Cyber Risk Management. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Computer Security Icon, Cyber Risk Management.
-
 Cyber Security Risk Management Lifecycle
Cyber Security Risk Management LifecycleFollowing slide highlights risk management lifecycle of cyber security for maintaining customer trust. It further covers evaluate, analyse, implement and decision and further includes preparing cyber security policy, risk in data collection, etc. Introducing our premium set of slides with Cyber Security Risk Management Lifecycle. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Implement, Evaluate, Decision. So download instantly and tailor it with your information.
-
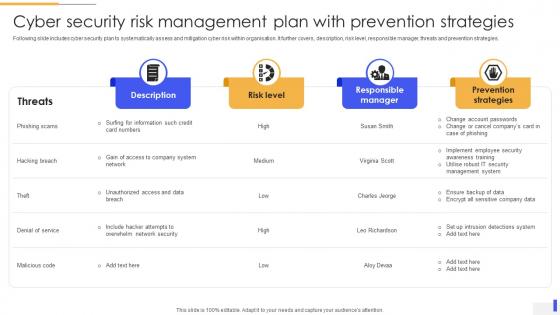 Cyber Security Risk Management Plan With Prevention Strategies
Cyber Security Risk Management Plan With Prevention StrategiesFollowing slide includes cyber security plan to systematically assess and mitigation cyber risk within organisation. It further covers, description, risk level, responsible manager, threats and prevention strategies. Introducing our Cyber Security Risk Management Plan With Prevention Strategies set of slides. The topics discussed in these slides are Risk Level, Responsible Manager, Prevention Strategies. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
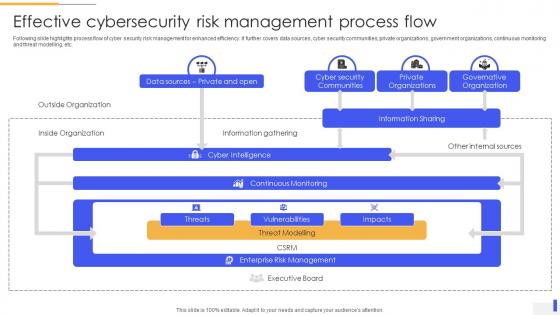 Effective Cybersecurity Risk Management Process Flow
Effective Cybersecurity Risk Management Process FlowFollowing slide highlights process flow of cyber security risk management for enhanced efficiency. It further covers data sources, cyber security communities, private organizations, government organizations, continuous monitoring and threat modelling, etc. Presenting our well structured Effective Cybersecurity Risk Management Process Flow. The topics discussed in this slide are Cyber Security Communities, Private Organizations, Governative Organization. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Key Strategies For Cybersecurity Risk Management
Key Strategies For Cybersecurity Risk ManagementFollowing slide highlights various risk management strategies to boost cyber security and sensitive data protection. It further covers capability assessments, program design, strategy, risk management, compliance, etc. Introducing our premium set of slides with Key Strategies For Cybersecurity Risk Management. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Third Party Risk Management, Capability Assessments, Risk Management. So download instantly and tailor it with your information.
-
 Supply Chain Cyber Security Risk Management Plan
Supply Chain Cyber Security Risk Management PlanThis slide includes cyber security management plan which can be used by supply chain managers to manage security threats. It includes various strategies such as upgrade minimum security baseline, assess process for further risks, and educate employees. Presenting our well structured Supply Chain Cyber Security Risk Management Plan. The topics discussed in this slide are Supervisor, Action Required, Mitigation Strategy. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
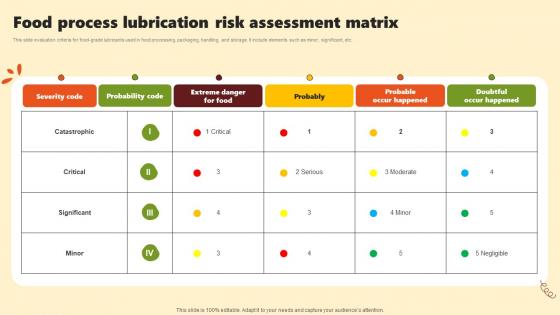 Food Process Lubrication Risk Assessment Matrix
Food Process Lubrication Risk Assessment MatrixThis slide evaluation criteria for food-grade lubricants used in food processing, packaging, handling, and storage. It include elements such as minor, significant, etc. Presenting our well structured Food Process Lubrication Risk Assessment Matrix. The topics discussed in this slide are Severity Code, Probability Code, Probable Occur Happened. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Construction Training Icon To Decrease Risk Incidents
Construction Training Icon To Decrease Risk IncidentsPresenting our set of slides with Construction Training Icon To Decrease Risk Incidents. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Construction Training Icon, Decrease Risk Incidents.
-
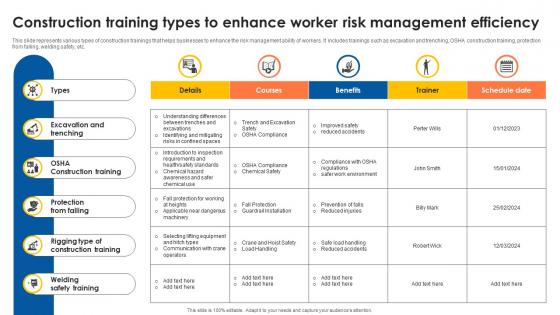 Construction Training Types To Enhance Worker Risk Management Efficiency
Construction Training Types To Enhance Worker Risk Management EfficiencyThis slide represents various types of construction trainings that helps businesses to enhance the risk management ability of workers. It includes trainings such as excavation and trenching, OSHA construction training, protection from falling, welding safety, etc. Introducing our Construction Training Types To Enhance Worker Risk Management Efficiency set of slides. The topics discussed in these slides are Types, Trenching, Construction Training. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Crisis Intervention Risk Assessment Framework
Crisis Intervention Risk Assessment FrameworkThe purpose of this slide is to assist clinicians in patient risk assessment based on various risk factors and domains. Presenting our well structured Crisis Intervention Risk Assessment Framework The topics discussed in this slide are Static, Dynamic, Protective This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
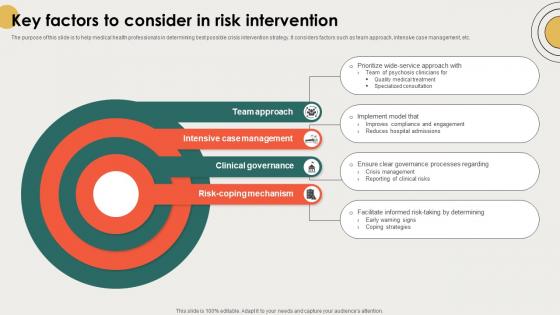 Key Factors To Consider In Risk Intervention
Key Factors To Consider In Risk InterventionThe purpose of this slide is to help medical health professionals in determining best possible crisis intervention strategy. It considers factors such as team approach, intensive case management, etc. Introducing our premium set of slides with Key Factors To Consider In Risk Intervention Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Team Approach, Intensive Case Management, Clinical Governance So download instantly and tailor it with your information.



