Powerpoint Templates and Google slides for Securing A Enterprise
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 SASE Network Security Business Benefits Of Firewall As A Service
SASE Network Security Business Benefits Of Firewall As A ServiceThis slide illustrates the advantages of firewall as a service to businesses. The purpose of this slide is to demonstrate the business benefits of FWaaS, such as easy maintenance, simple infrastructure, better visibility, easy configuration, scalability and protection of remote workers. Present the topic in a bit more detail with this SASE Network Security Business Benefits Of Firewall As A Service. Use it as a tool for discussion and navigation on Infrastructure, Visibility, Scalability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
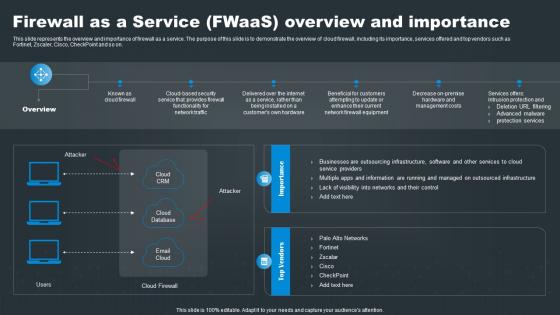 SASE Network Security Firewall As A Service FWaaS Overview And Importance
SASE Network Security Firewall As A Service FWaaS Overview And ImportanceThis slide represents the overview and importance of firewall as a service. The purpose of this slide is to demonstrate the overview of cloud firewall, including its importance, services offered and top vendors such as Fortinet, Zscaler, Cisco, CheckPoint and so on. Introducing SASE Network Security Firewall As A Service FWaaS Overview And Importance to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Information, Networks, Managed, using this template. Grab it now to reap its full benefits.
-
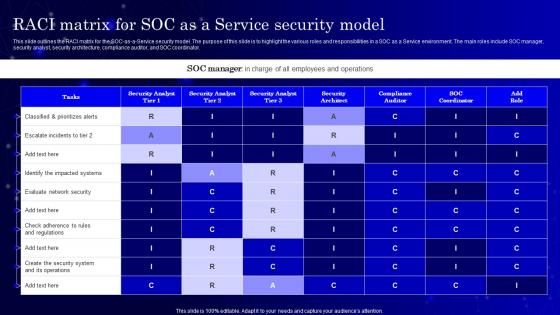 Secops V2 RACI Matrix For Soc As A Service Security Model
Secops V2 RACI Matrix For Soc As A Service Security ModelThis slide outlines the RACI matrix for the SOC-as-a-Service security model. The purpose of this slide is to highlight the various roles and responsibilities in a SOC as a Service environment. The main roles include SOC manager, security analyst, security architecture, compliance auditor, and SOC coordinator. Present the topic in a bit more detail with this Secops V2 RACI Matrix For Soc As A Service Security Model. Use it as a tool for discussion and navigation on Classified And Prioritizes Alerts, Evaluate Network Security, Service Security Model, Compliance Auditor. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
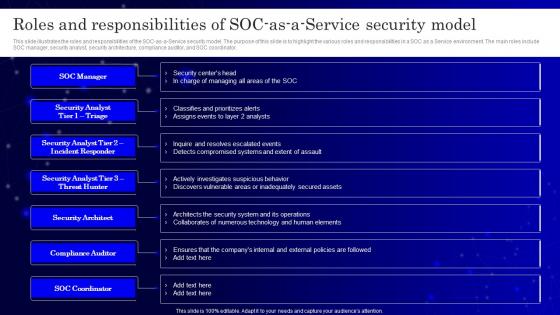 Secops V2 Roles And Responsibilities Of Soc As A Service Security Model
Secops V2 Roles And Responsibilities Of Soc As A Service Security ModelThis slide illustrates the roles and responsibilities of the SOC-as-a-Service security model. The purpose of this slide is to highlight the various roles and responsibilities in a SOC as a Service environment. The main roles include SOC manager, security analyst, security architecture, compliance auditor, and SOC coordinator. Increase audience engagement and knowledge by dispensing information using Secops V2 Roles And Responsibilities Of Soc As A Service Security Model. This template helps you present information on seven stages. You can also present information on Roles And Responsibilities, Security Analyst, Security Architecture, Compliance Auditor using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
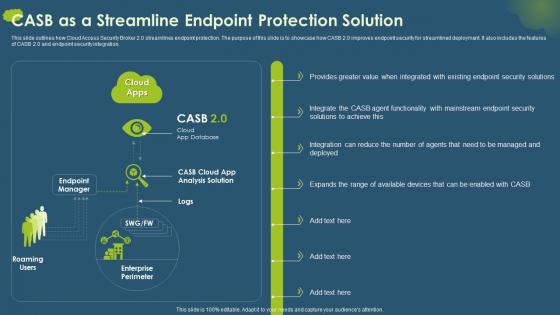 Cloud Access Security Broker CASB V2 CASB As A Streamline Endpoint Protection Solution
Cloud Access Security Broker CASB V2 CASB As A Streamline Endpoint Protection SolutionThis slide outlines how Cloud Access Security Broker 2.0 streamlines endpoint protection. The purpose of this slide is to showcase how CASB 2.0 improves endpoint security for streamlined deployment. It also includes the features of CASB 2.0 and endpoint security integration. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 CASB As A Streamline Endpoint Protection Solution. Use it as a tool for discussion and navigation on Cloud Access Security Broker, Streamlines Endpoint Protection, Streamlined Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
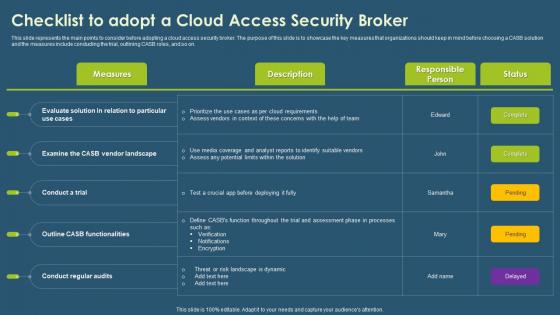 Cloud Access Security Broker CASB V2 Checklist To Adopt A Cloud Access Security Broker
Cloud Access Security Broker CASB V2 Checklist To Adopt A Cloud Access Security BrokerThis slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Checklist To Adopt A Cloud Access Security Broker. Use it as a tool for discussion and navigation on Cloud Access Security Broker, Cloud Requirements, Conduct Regular Audits. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
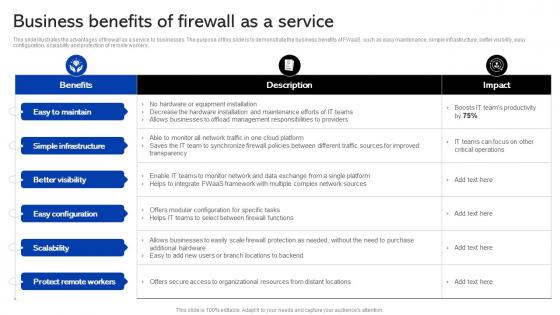 Sase Security Business Benefits Of Firewall As A Service
Sase Security Business Benefits Of Firewall As A ServiceThis slide illustrates the advantages of firewall as a service to businesses. The purpose of this slide is to demonstrate the business benefits of FWaaS, such as easy maintenance, simple infrastructure, better visibility, easy configuration, scalability and protection of remote workers. Deliver an outstanding presentation on the topic using this Sase Security Business Benefits Of Firewall As A Service. Dispense information and present a thorough explanation of Business, Service, Maintenance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
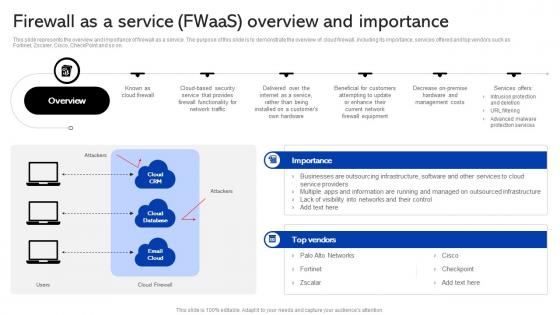 Sase Security Firewall As A Service Fwaas Overview And Importance
Sase Security Firewall As A Service Fwaas Overview And ImportanceThis slide represents the overview and importance of firewall as a service. The purpose of this slide is to demonstrate the overview of cloud firewall, including its importance, services offered and top vendors such as Fortinet, Zscaler, Cisco, CheckPoint and so on. Deliver an outstanding presentation on the topic using this Sase Security Firewall As A Service Fwaas Overview And Importance. Dispense information and present a thorough explanation of Overview, Equipment, Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
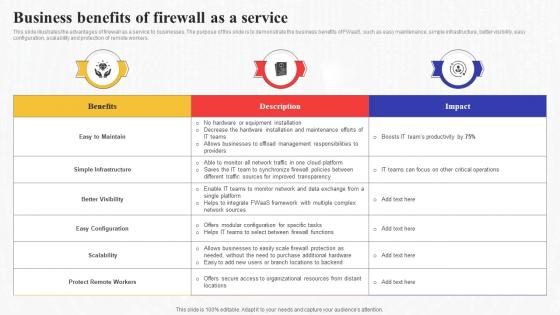 Business Benefits Of Firewall As A Service Secure Access Service Edge Sase
Business Benefits Of Firewall As A Service Secure Access Service Edge SaseThis slide illustrates the advantages of firewall as a service to businesses. The purpose of this slide is to demonstrate the business benefits of FWaaS, such as easy maintenance, simple infrastructure, better visibility, easy configuration, scalability and protection of remote workers. Deliver an outstanding presentation on the topic using this Business Benefits Of Firewall As A Service Secure Access Service Edge Sase. Dispense information and present a thorough explanation of Management, Responsibilities, Businesses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
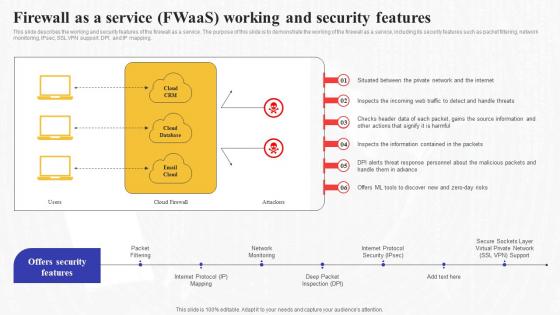 Firewall As A Service Fwaas Working And Security Features Secure Access Service Edge Sase
Firewall As A Service Fwaas Working And Security Features Secure Access Service Edge SaseThis slide describes the working and security features of the firewall as a service. The purpose of this slide is to demonstrate the working of the firewall as a service, including its security features such as packet filtering, network monitoring, IPsec, SSL VPN support, DPI, and IP mapping. Present the topic in a bit more detail with this Firewall As A Service Fwaas Working And Security Features Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Information, Demonstrate, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
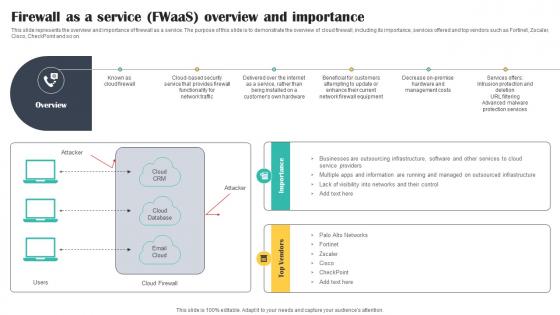 Firewall As A Service FWaaS Overview And Importance Cloud Security Model
Firewall As A Service FWaaS Overview And Importance Cloud Security ModelThis slide represents the overview and importance of firewall as a service. The purpose of this slide is to demonstrate the overview of cloud firewall, including its importance, services offered and top vendors such as Fortinet, Zscaler, Cisco, CheckPoint and so on. Increase audience engagement and knowledge by dispensing information using Firewall As A Service FWaaS Overview And Importance Cloud Security Model. This template helps you present information on two stages. You can also present information on Businesses, Providers, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
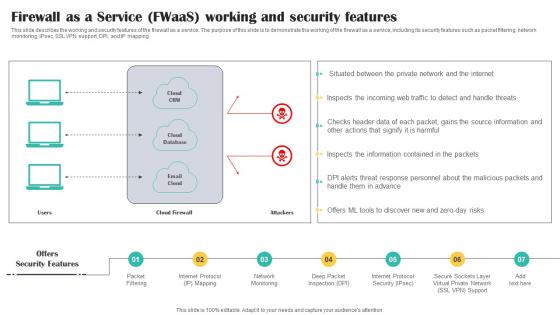 Firewall As A Service FWaaS Working And Security Features Cloud Security Model
Firewall As A Service FWaaS Working And Security Features Cloud Security ModelThis slide describes the working and security features of the firewall as a service. The purpose of this slide is to demonstrate the working of the firewall as a service, including its security features such as packet filtering, network monitoring, IPsec, SSL VPN support, DPI, and IP mapping. Introducing Firewall As A Service FWaaS Working And Security Features Cloud Security Model to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Packet, Internet, Network, using this template. Grab it now to reap its full benefits.
-
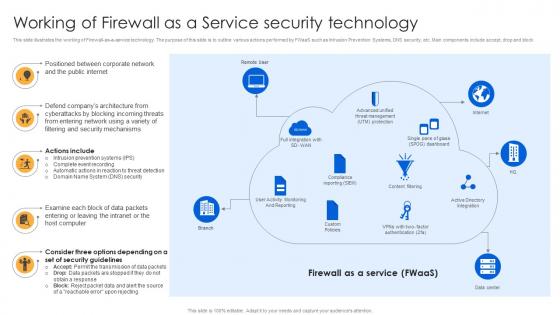 Working Of Firewall As A Service Security Technology Firewall Virtualization
Working Of Firewall As A Service Security Technology Firewall VirtualizationThis slide illustrates the working of Firewall-as-a-service technology. The purpose of this slide is to outline various actions performed by FWaaS such as Intrusion Prevention Systems, DNS security, etc. Main components include accept, drop and block. Increase audience engagement and knowledge by dispensing information using Working Of Firewall As A Service Security Technology Firewall Virtualization. This template helps you present information on five stages. You can also present information on Public Internet, Corporate Network, Companys Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
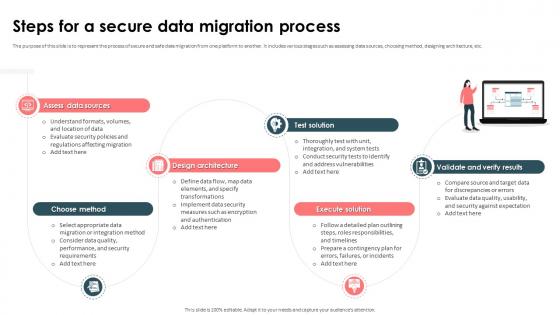 Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process
Strategic Approach For Effective Data Migration Steps For A Secure Data Migration ProcessThe purpose of this slide is to represent the process of secure and safe data migration from one platform to another. It includes various stages such as assessing data sources, choosing method, designing architecture, etc. Introducing Strategic Approach For Effective Data Migration Steps For A Secure Data Migration Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Design Architecture, Validate And Verify Results, Assess Data Sources, Data Migration Process, using this template. Grab it now to reap its full benefits.
-
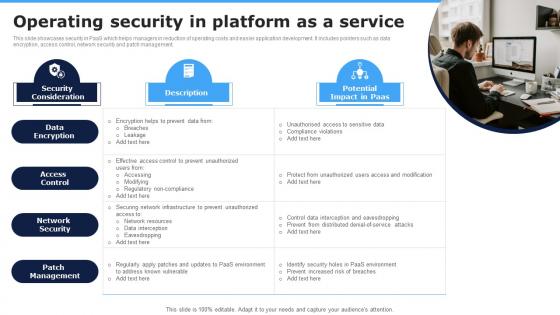 Operating Security In Platform As A Service
Operating Security In Platform As A ServiceThis slide showcases security in PaaS which helps managers in reduction of operating costs and easier application development. It includes pointers such as data encryption, access control, network security and patch management. Presenting our set of slides with Operating Security In Platform As A Service. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Encryption, Access Control, Network Security.
-
 Adopt Security Auditing Checklist Securing Blockchain Transactions A Beginners Guide BCT SS V
Adopt Security Auditing Checklist Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Present the topic in a bit more detail with this Adopt Security Auditing Checklist Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Parameters, Comments, Comply Safe Communication Protocols. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
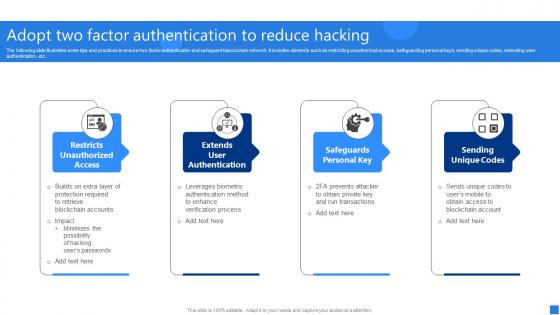 Adopt Two Factor Authentication Securing Blockchain Transactions A Beginners Guide BCT SS V
Adopt Two Factor Authentication Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some tips and practices to ensure two factor authentication and safeguard blaockchain network. It includes elements such as restricting unauthorized access, safeguarding personal keys, sending unique codes, extending user authentication, etc. Introducing Adopt Two Factor Authentication Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Restricts Unauthorized Access, Extends User Authentication, Safeguards Personal Key, using this template. Grab it now to reap its full benefits.
-
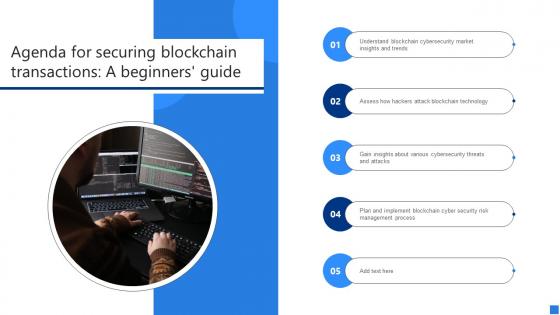 Agenda For Securing Blockchain Transactions A Beginners Guide BCT SS V
Agenda For Securing Blockchain Transactions A Beginners Guide BCT SS VIncrease audience engagement and knowledge by dispensing information using Agenda For Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on five stages. You can also present information on Blockchain Cybersecurity Market, Blockchain Technology, Various Cybersecurity Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
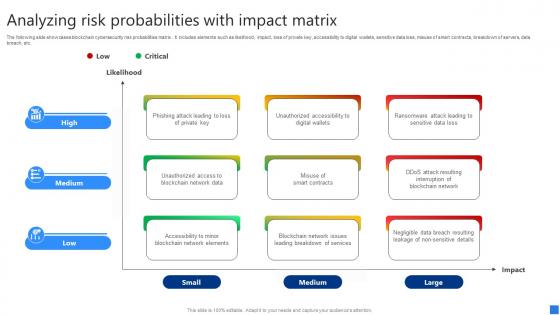 Analyzing Risk Probabilities Securing Blockchain Transactions A Beginners Guide BCT SS V
Analyzing Risk Probabilities Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity risk probabilities matrix . It includes elements such as likelihood, impact, loss of private key, accessibility to digital wallets, sensitive data loss, misuse of smart contracts, breakdown of servers, data breach, etc. Deliver an outstanding presentation on the topic using this Analyzing Risk Probabilities Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Phishing Attack Leading, Unauthorized Accessibility, Ransomware Attack Leading using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
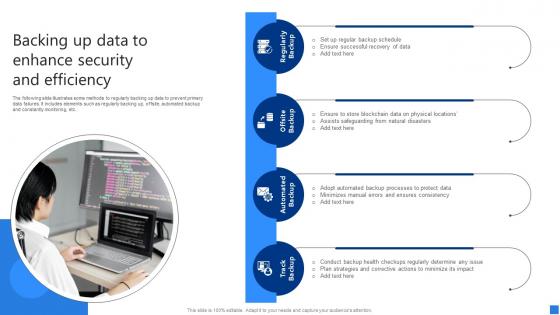 Backing Up Data To Enhance Securing Blockchain Transactions A Beginners Guide BCT SS V
Backing Up Data To Enhance Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Backing Up Data To Enhance Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Offsite Backup, Automated Backup, using this template. Grab it now to reap its full benefits.
-
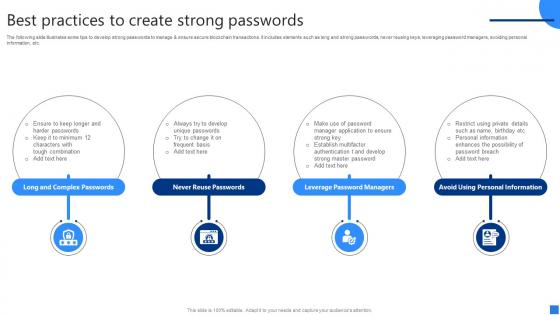 Best Practices To Create Securing Blockchain Transactions A Beginners Guide BCT SS V
Best Practices To Create Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some tips to develop strong passwords to manage and ensure secure blockchain transactions. It includes elements such as long and strong passwords, never reusing keys, leveraging password managers, avoiding personal information, etc. Increase audience engagement and knowledge by dispensing information using Best Practices To Create Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Long And Complex Passwords, Never Reuse Passwords, Leverage Password Managers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
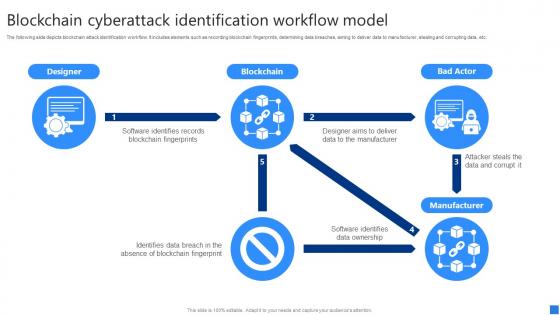 Blockchain Cyberattack Securing Blockchain Transactions A Beginners Guide BCT SS V
Blockchain Cyberattack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Blockchain Cyberattack Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Designer, Blockchain, Bad Actor. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparative Analysis Multiple Securing Blockchain Transactions A Beginners Guide BCT SS V
Comparative Analysis Multiple Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases comparative analysis of blockchain cybersecurity vendors. It includes elements such as experience, services, technical capabilities, response time, costing, offering competitive pricing, reviews, 24 7 availability, etc. Deliver an outstanding presentation on the topic using this Comparative Analysis Multiple Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Highly Experience Offering, Cybersecurity Solutions, Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
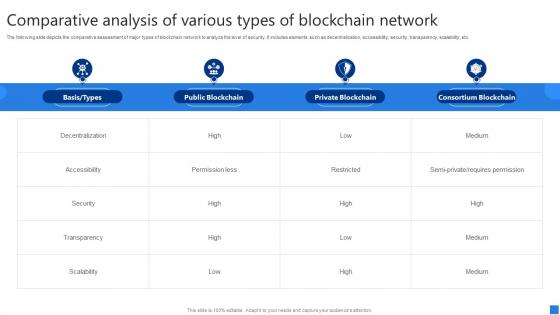 Comparative Analysis Various Securing Blockchain Transactions A Beginners Guide BCT SS V
Comparative Analysis Various Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts the comparative assessment of major types of blockchain network to analyze the level of security. It includes elements such as decentralization, accessibility, security, transparency, scalability, etc. Present the topic in a bit more detail with this Comparative Analysis Various Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Decentralization, Accessibility, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Conducting Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V
Conducting Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction ,blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Conducting Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Introduction Blockchain, Blockchain Security Risks, Smart Contracts Development using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
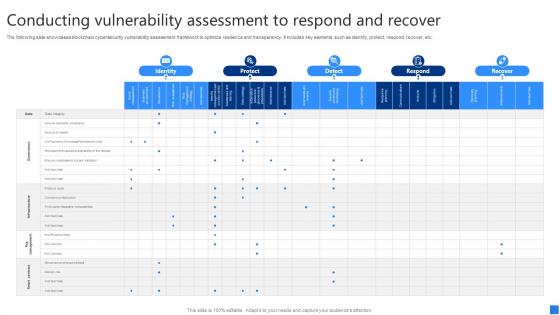 Conducting Vulnerability Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V
Conducting Vulnerability Assessment Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Conducting Vulnerability Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Identity, Protect, Detect. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
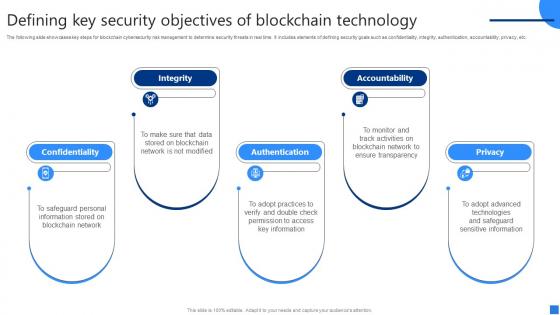 Defining Key Security Objectives Securing Blockchain Transactions A Beginners Guide BCT SS V
Defining Key Security Objectives Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases key steps for blockchain cybersecurity risk management to determine security threats in real time. It includes elements of defining security goals such as confidentiality, integrity, authentication, accountability, privacy, etc. Introducing Defining Key Security Objectives Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, Authentication, using this template. Grab it now to reap its full benefits.
-
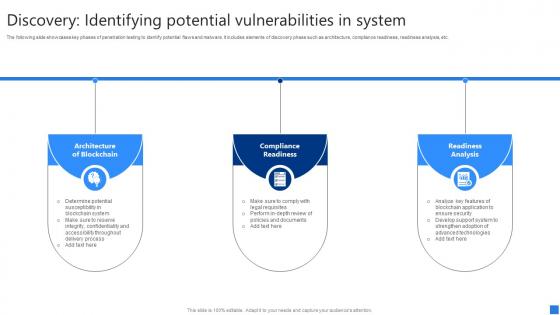 Discovery Identifying Potential Securing Blockchain Transactions A Beginners Guide BCT SS V
Discovery Identifying Potential Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Increase audience engagement and knowledge by dispensing information using Discovery Identifying Potential Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on three stages. You can also present information on Architecture Blockchain, Compliance Readiness, Readiness Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
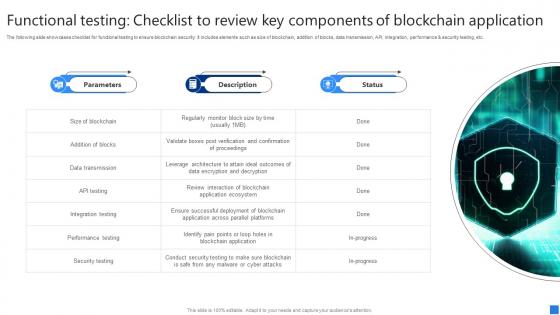 Functional Testing Checklist Securing Blockchain Transactions A Beginners Guide BCT SS V
Functional Testing Checklist Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases checklist for functional testing to ensure blockchain security. It includes elements such as size of blockchain, addition of blocks, data transmission, API, integration, performance and security testing, etc. Introducing Functional Testing Checklist Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Size Of Blockchain, Addition Blocks, Data Transmission, using this template. Grab it now to reap its full benefits.
-
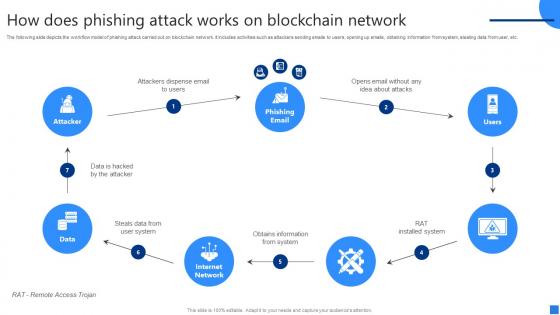 How Does Phishing Attack Works Securing Blockchain Transactions A Beginners Guide BCT SS V
How Does Phishing Attack Works Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using How Does Phishing Attack Works Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on six stages. You can also present information on Attackers Dispense Email, Steals Data, Obtains Information From System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
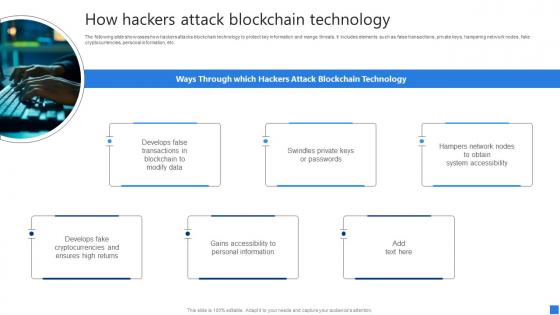 How Hackers Attack Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V
How Hackers Attack Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases how hackers attacks blockchain technology to protect key information and mange threats. It includes elements such as false transactions, private keys, hampering network nodes, fake cryptocurrencies, personal information, etc. Introducing How Hackers Attack Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Develops False, Swindles Private, Hampers Network Nodes, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Securing Blockchain Transactions A Beginners Guide BCT SS V
Icons Slide For Securing Blockchain Transactions A Beginners Guide BCT SS VIntroducing our well researched set of slides titled Icons Slide For Securing Blockchain Transactions A Beginners Guide BCT SS V. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
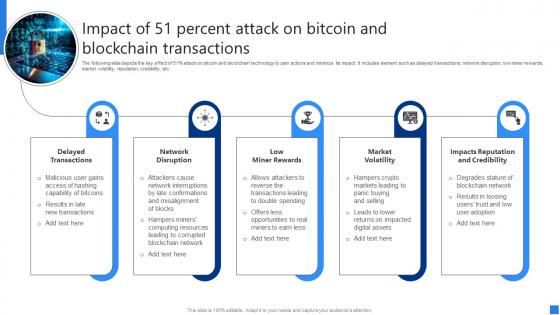 Impact Of 51 Percent Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Impact Of 51 Percent Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts the key effect of 51percent attack on bitcoin and blockchain technology to plan actions and minimize its impact. It includes element such as delayed transactions, network disruption, low miner rewards, market volatility, reputation, credibility, etc. Increase audience engagement and knowledge by dispensing information using Impact Of 51 Percent Attack Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on five stages. You can also present information on Delayed Transactions, Network Disruption, Low Miner Rewards using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
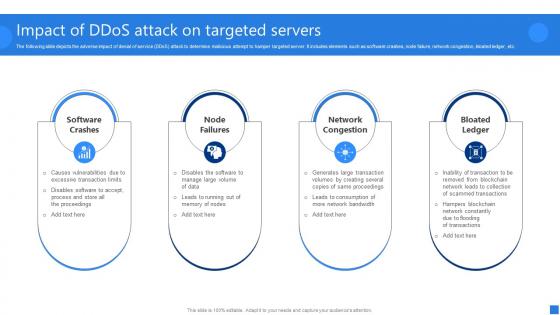 Impact Of DDoS Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Impact Of DDoS Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts the adverse impact of denial of service DDoS attack to determine malicious attempt to hamper targeted server. It includes elements such as software crashes, node failure, network congestion, bloated ledger, etc. Introducing Impact Of DDoS Attack Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Software Crashes, Node Failures, Network Congestion, using this template. Grab it now to reap its full benefits.
-
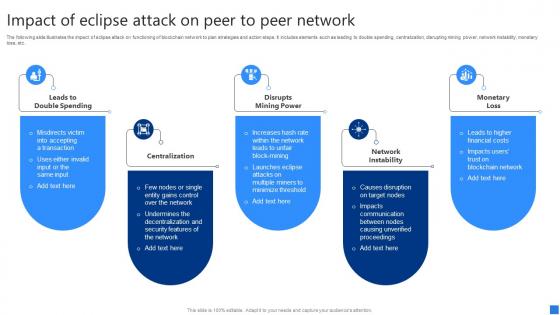 Impact Of Eclipse Attack On Securing Blockchain Transactions A Beginners Guide BCT SS V
Impact Of Eclipse Attack On Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates the impact of eclipse attack on functioning of blockchain network to plan strategies and action steps. It includes elements such as leading to double spending, centralization, disrupting mining power, network instability, monetary loss, etc. Increase audience engagement and knowledge by dispensing information using Impact Of Eclipse Attack On Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on five stages. You can also present information on Leads Double Spending, Centralization, Disrupts Mining Power using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implementing Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V
Implementing Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Introducing Implementing Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reduce, Accept, Transfer, using this template. Grab it now to reap its full benefits.
-
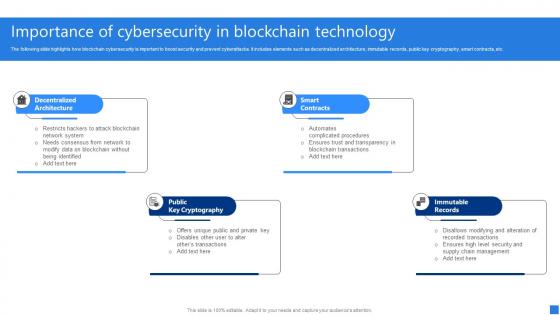 Importance Of Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V
Importance Of Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Increase audience engagement and knowledge by dispensing information using Importance Of Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Decentralized Architecture, Public Key Cryptography, Smart Contracts, Immutable Records using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Approaches To Protect Securing Blockchain Transactions A Beginners Guide BCT SS V
Key Approaches To Protect Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some methods to protect blockchain network users from honeypot scams and implement defensive actions. It includes elements such as no dead coins, audits, check social media, scrutinize website, etc. Introducing Key Approaches To Protect Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on No Dead Coins, Audits, Check Social Media, using this template. Grab it now to reap its full benefits.
-
 Key Scenarios Of Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Key Scenarios Of Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases major scenarios of Sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer to peer model, etc. Increase audience engagement and knowledge by dispensing information using Key Scenarios Of Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on two stages. You can also present information on Attack Bitcoin Network, Attack Tor Network, Hampers Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
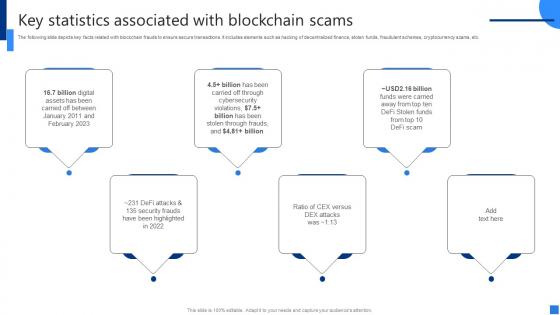 Key Statistics Associated Securing Blockchain Transactions A Beginners Guide BCT SS V
Key Statistics Associated Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts key facts related with blockchain frauds to ensure secure transactions. It includes elements such as hacking of decentralized finance, stolen funds, fraudulent schemes, cryptocurrency scams, etc. Introducing Key Statistics Associated Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Violations, Security Frauds, Statistics Associated, using this template. Grab it now to reap its full benefits.
-
 Leverage Cryptography Boost Securing Blockchain Transactions A Beginners Guide BCT SS V
Leverage Cryptography Boost Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases how cryptography assists in securing blockchain transactions and maintaining confidentiality. It includes elements such as data confidentiality, data integrity, digital signatures, consensus mechanism, etc. Increase audience engagement and knowledge by dispensing information using Leverage Cryptography Boost Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Data Confidentiality, Digital Signatures, Consensus Mechanisms using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Cryptocurrency Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V
Major Cryptocurrency Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases major cryptocurrency and blockchain cybersecurity scams throughout the globe. It includes elements such as Decentralized autonomous organization DAO attack, gox attack, plus token scams, etc. Introducing Major Cryptocurrency Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on DAO Hack, Quadrigacx Attack, Plus Token Scam, using this template. Grab it now to reap its full benefits.
-
 Major Cybersecurity Challenges Securing Blockchain Transactions A Beginners Guide BCT SS V
Major Cybersecurity Challenges Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates various issues faced by blockchain users. It includes elements such as smart contract vulnerabilities, privacy, confidentiality, weak consensus mechanism, private key management, phishing, along with its impact, etc. Increase audience engagement and knowledge by dispensing information using Major Cybersecurity Challenges Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on one stages. You can also present information on Smart Contract Vulnerabilities, Weak Consensus Mechanism, Private Key Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Methods To Avoid Sybil Securing Blockchain Transactions A Beginners Guide BCT SS V
Methods To Avoid Sybil Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates various ways to minimize and prevent Sybil attacks and ensure safe blockchain transactions. It includes elements such as identity validation, hierarchical, defense system, cost of new nodes, social trust graphs, etc. Introducing Methods To Avoid Sybil Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identity Validation, Establishing Hierarchical System, Defense System, using this template. Grab it now to reap its full benefits.
-
 Methods To Ensure Smart Securing Blockchain Transactions A Beginners Guide BCT SS V
Methods To Ensure Smart Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases some tips and practices to ensure smart contract security. It includes elements such as careful rollouts, keeping them simple, updating and monitoring new developments, reviewing fundamental tradeoffs, etc. Increase audience engagement and knowledge by dispensing information using Methods To Ensure Smart Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Careful Rollouts, Ensure Keep Contracts Simple, Keep Updated Monitor using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
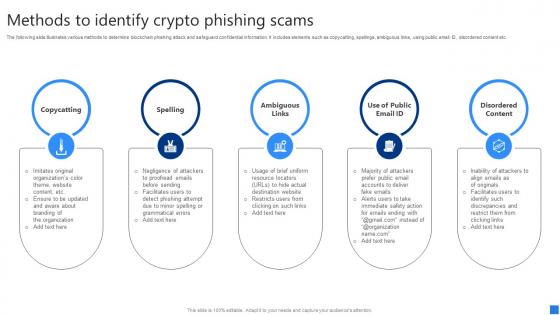 Methods To Identify Crypto Securing Blockchain Transactions A Beginners Guide BCT SS V
Methods To Identify Crypto Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates various methods to determine blockchain phishing attack and safeguard confidential information. It includes elements such as copycatting, spellings, ambiguous links, using public email ID, disordered content etc. Introducing Methods To Identify Crypto Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Copycatting, Spelling, Ambiguous Links, using this template. Grab it now to reap its full benefits.
-
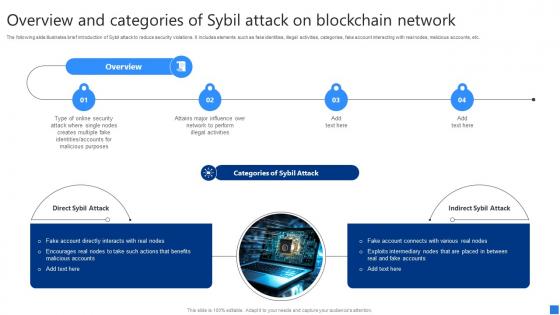 Overview And Categories Of Sybil Securing Blockchain Transactions A Beginners Guide BCT SS V
Overview And Categories Of Sybil Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates brief introduction of Sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Increase audience engagement and knowledge by dispensing information using Overview And Categories Of Sybil Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on two stages. You can also present information on Fake Account Directly, Encourages Real Nodes, Fake Account Connects using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
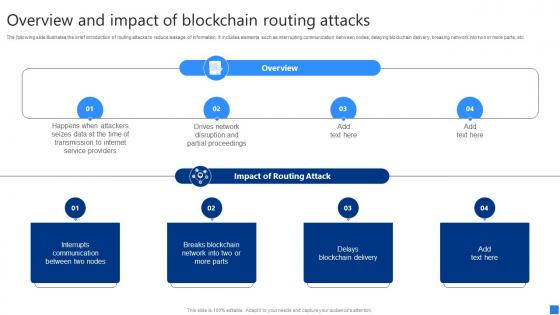 Overview And Impact Of Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V
Overview And Impact Of Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates the brief introduction of routing attacks to reduce leakage of information. It includes elements such as interrupting communication between nodes, delaying blockchain delivery, breaking network into two or more parts, etc. Introducing Overview And Impact Of Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Interrupts Communication Between, Breaks Blockchain Network, Delays Blockchain Delivery, using this template. Grab it now to reap its full benefits.
-
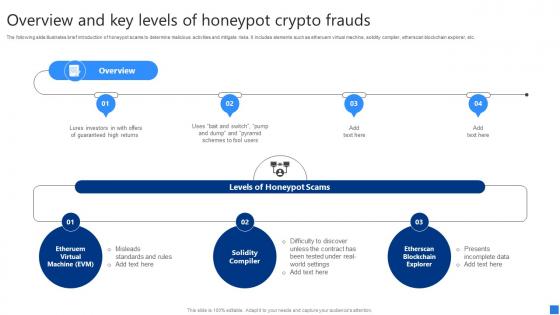 Overview And Key Levels Securing Blockchain Transactions A Beginners Guide BCT SS V
Overview And Key Levels Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates brief introduction of honeypot scams to determine malicious activities and mitigate risks. It includes elements such as etheruem virtual machine, solidity compiler, etherscan blockchain explorer, etc. Increase audience engagement and knowledge by dispensing information using Overview And Key Levels Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Etheruem Virtual Machine, Solidity Compiler, Etherscan Blockchain Explorer using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
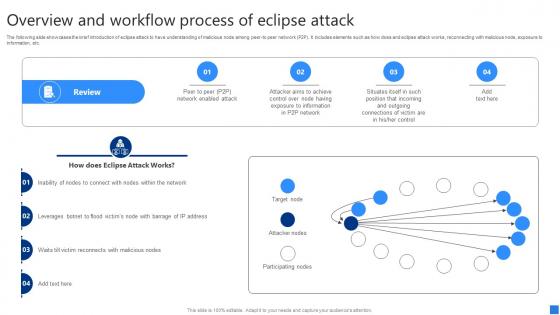 Overview And Workflow Process Securing Blockchain Transactions A Beginners Guide BCT SS V
Overview And Workflow Process Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases the brief introduction of eclipse attack to have understanding of malicious node among peer to peer network P2P. It includes elements such as how does and eclipse attack works, reconnecting with malicious node, exposure to information, etc. Present the topic in a bit more detail with this Overview And Workflow Process Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Target Node, Attacker Nodes, Participating Nodes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview And Workflow Securing Blockchain Transactions A Beginners Guide BCT SS V
Overview And Workflow Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Introducing Overview And Workflow Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Transaction Requested, Node Validates Transaction, Transaction Completed, using this template. Grab it now to reap its full benefits.
-
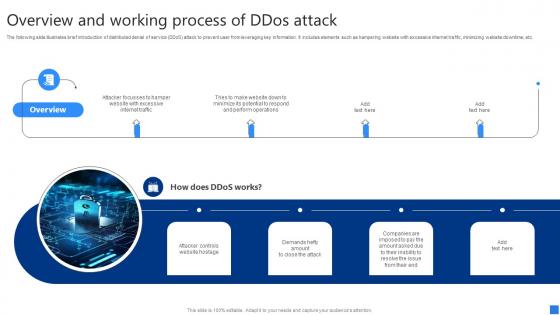 Overview And Working Process Securing Blockchain Transactions A Beginners Guide BCT SS V
Overview And Working Process Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates brief introduction of distributed denial of service DDoS attack to prevent user from leveraging key information. It includes elements such as hampering website with excessive internet traffic, minimizing website downtime, etc. Increase audience engagement and knowledge by dispensing information using Overview And Working Process Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Attacker Controls Website Hostage, Demands Hefty Amount, Companies Are Imposed using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
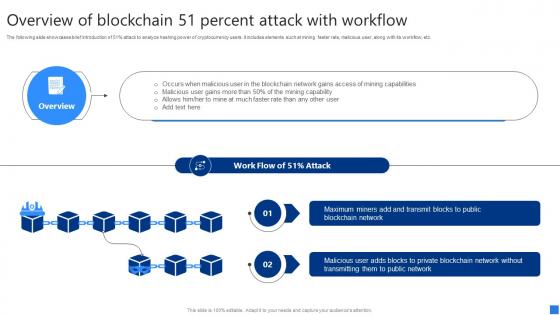 Overview Of Blockchain 51 Securing Blockchain Transactions A Beginners Guide BCT SS V
Overview Of Blockchain 51 Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases brief introduction of 51percent attack to analyze hashing power of cryptocurrency users. It includes elements such at mining faster rate, malicious user, along with its workflow, etc. Deliver an outstanding presentation on the topic using this Overview Of Blockchain 51 Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Blockchain Network Gains, Mining Capabilities, Public Blockchain Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
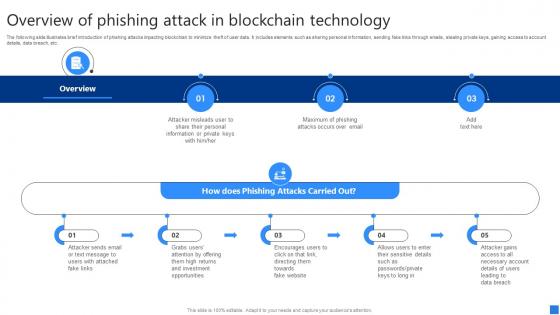 Overview Of Phishing Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Overview Of Phishing Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting blockchian to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Overview Of Phishing Attack Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Attacker Sends Email, Encourages Users, Sensitive Details, using this template. Grab it now to reap its full benefits.
-
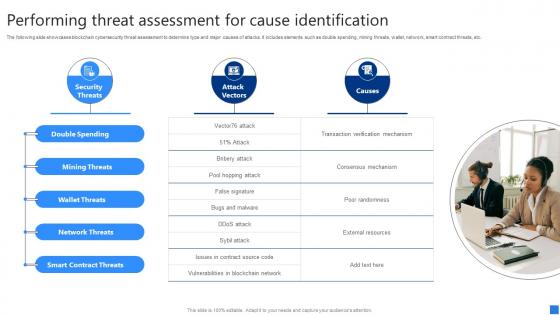 Performing Threat Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V
Performing Threat Assessment Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Increase audience engagement and knowledge by dispensing information using Performing Threat Assessment Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on one stages. You can also present information on Double Spending, Mining Threats, Wallet Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Remediation Comparative Analysis Securing Blockchain Transactions A Beginners Guide BCT SS V
Remediation Comparative Analysis Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts comparative analysis of penetration tools to remediate cybersecurity vulnerabilities. It includes elements such as services, features, reviews, security audits, compliance reporting, website and network security, etc. Deliver an outstanding presentation on the topic using this Remediation Comparative Analysis Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Astra Security, Intruder, Invicti using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
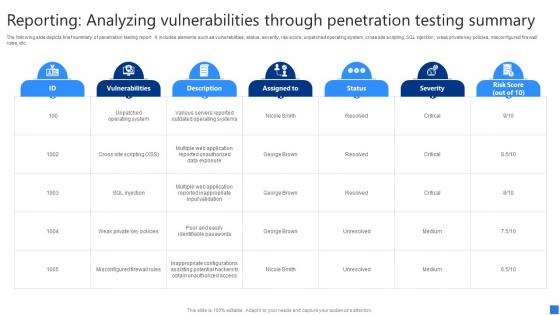 Reporting Analyzing Vulnerabilities Securing Blockchain Transactions A Beginners Guide BCT SS V
Reporting Analyzing Vulnerabilities Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts brief summary of penetration testing report . It includes elements such as vulnerabilities, status, severity, risk score, unpatched operating system, cross site scripting, SQL injection, weak private key policies, misconfigured firewall rules, etc. Present the topic in a bit more detail with this Reporting Analyzing Vulnerabilities Securing Blockchain Transactions A Beginners Guide BCT SS V. Use it as a tool for discussion and navigation on Vulnerabilities, Status, Severity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
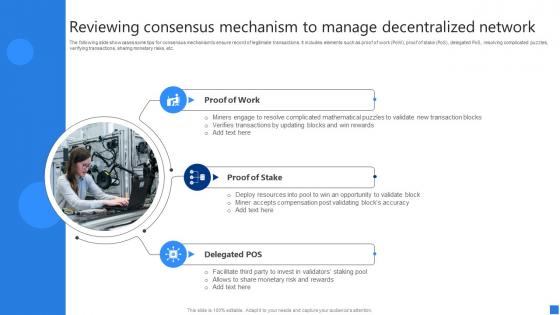 Reviewing Consensus Mechanism Securing Blockchain Transactions A Beginners Guide BCT SS V
Reviewing Consensus Mechanism Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases some tips for consensus mechanism to ensure record of legitimate transactions. It includes elements such as proof of work PoW, proof of stake PoS, delegated PoS, resolving complicated puzzles, verifying transactions, sharing monetary risks, etc. Introducing Reviewing Consensus Mechanism Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Proof Work, Proof Stake, Delegated POS, using this template. Grab it now to reap its full benefits.
-
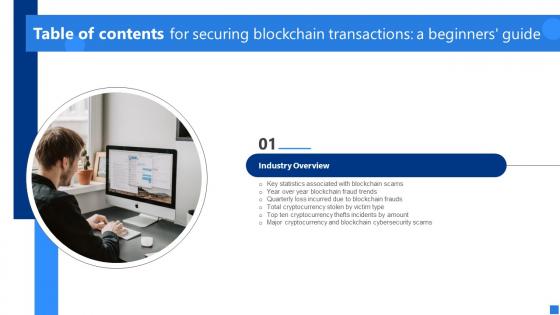 Securing Blockchain Transactions A Beginners Guide Table Of Contents BCT SS V
Securing Blockchain Transactions A Beginners Guide Table Of Contents BCT SS VIncrease audience engagement and knowledge by dispensing information using Securing Blockchain Transactions A Beginners Guide Table Of Contents BCT SS V. This template helps you present information on one stages. You can also present information on Industry Overview, Key Statistics Associated, Blockchain Fraud Trends using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
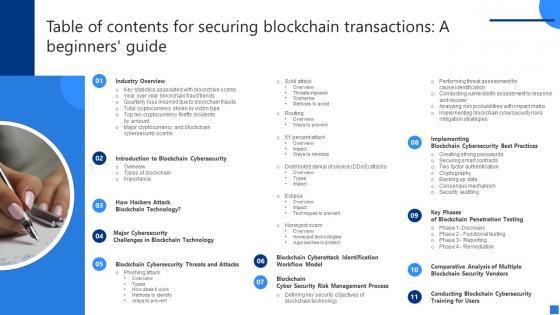 Table Of Contents For Securing Blockchain Transactions A Beginners Guide BCT SS V
Table Of Contents For Securing Blockchain Transactions A Beginners Guide BCT SS VIntroducing Table Of Contents For Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Industry Overview, Introduction Blockchain Cybersecurity, Blockchain Technology, using this template. Grab it now to reap its full benefits.



