Powerpoint Templates and Google slides for Securing A Enterprise
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Techniques To Prevent Eclipse Securing Blockchain Transactions A Beginners Guide BCT SS V
Techniques To Prevent Eclipse Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Increase audience engagement and knowledge by dispensing information using Techniques To Prevent Eclipse Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Random Node Selection, New Node Restrictions, Increased Node Connections using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
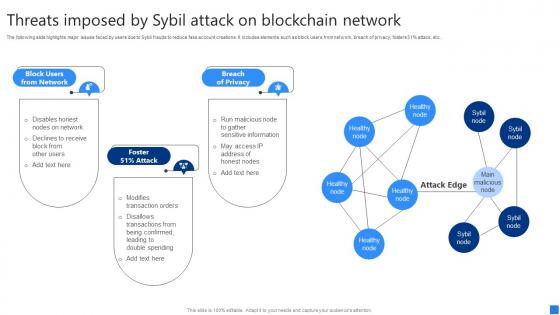 Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Introducing Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Block Users Network, Foster Attack, Breach Privacy, using this template. Grab it now to reap its full benefits.
-
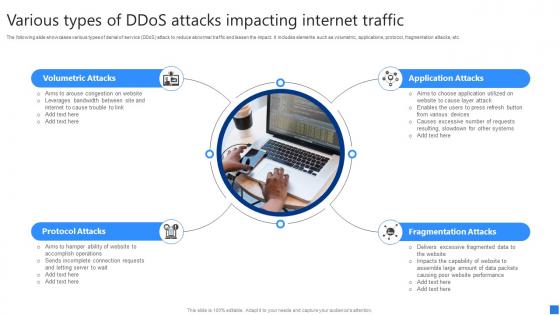 Various Types Of DDoS Attacks Securing Blockchain Transactions A Beginners Guide BCT SS V
Various Types Of DDoS Attacks Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases various types of denial of service DDoS attack to reduce abnormal traffic and lessen the impact. It includes elements such as volumetric, applications, protocol, fragmentation attacks, etc. Introducing Various Types Of DDoS Attacks Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Volumetric Attacks, Protocol Attacks, Fragmentation Attacks, using this template. Grab it now to reap its full benefits.
-
 Ways To Minimize 51 Percent Attacks Securing Blockchain Transactions A Beginners Guide BCT SS V
Ways To Minimize 51 Percent Attacks Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates various methods to reduce the impact of 51percent attacks and optimize hash rate. It includes elements such as restriction on single user, constant updates, establishing strong network system, leveraging proof of stake, performing security audits, etc. Increase audience engagement and knowledge by dispensing information using Ways To Minimize 51 Percent Attacks Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on five stages. You can also present information on Constant Updates, Establish Strong Network System, Leverage Proof Stake using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ways To Prevent Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V
Ways To Prevent Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some methods to minimize blockchain routing attacks to safeguard network from wrong routing table. It includes elements such as strong passwords, updating firmware, managing access control lists, monitoring logs, etc. Introducing Ways To Prevent Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strong Passwords, Update Firmware, Manage Access Control List, using this template. Grab it now to reap its full benefits.
-
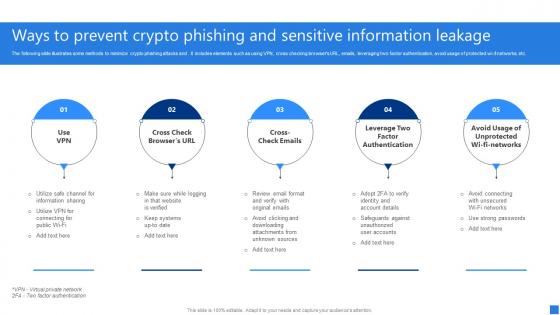 Ways To Prevent Crypto Phishing Securing Blockchain Transactions A Beginners Guide BCT SS V
Ways To Prevent Crypto Phishing Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some methods to minimize crypto phishing attacks and . It includes elements such as using VPN, cross checking browsers URL, emails, leveraging two factor authentication, avoid usage of protected wi fi networks, etc. Increase audience engagement and knowledge by dispensing information using Ways To Prevent Crypto Phishing Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on five stages. You can also present information on Use VPN, Cross Check Browsers URL, Cross Check Emails using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
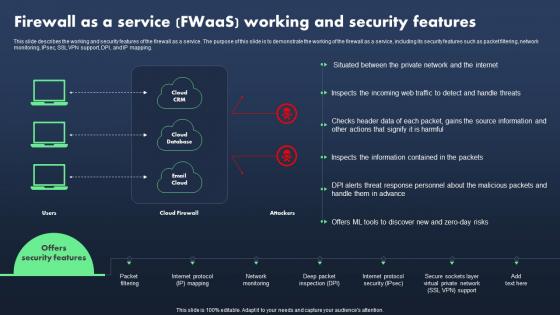 Sase Model Firewall As A Service Fwaas Working And Security Features
Sase Model Firewall As A Service Fwaas Working And Security FeaturesThis slide describes the working and security features of the firewall as a service. The purpose of this slide is to demonstrate the working of the firewall as a service, including its security features such as packet filtering, network monitoring, IPsec, SSL VPN support, DPI, and IP mapping. Deliver an outstanding presentation on the topic using this Sase Model Firewall As A Service Fwaas Working And Security Features. Dispense information and present a thorough explanation of Cloud Database, Email Cloud using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Your Digital Assets Essentials For Opening A Cryptocurrency Wallet Account
Secure Your Digital Assets Essentials For Opening A Cryptocurrency Wallet AccountThis slide discusses the key information required while opening the crypto wallet. The purpose of this slide is to outline the two aspects that should be considered personal information and public and private keys. Present the topic in a bit more detail with this Secure Your Digital Assets Essentials For Opening A Cryptocurrency Wallet Account. Use it as a tool for discussion and navigation on Cryptocurrency Wallet Account, Crypto Wallet, Public And Private Keys, Password To Your Wallet. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Secure Your Digital Assets Immediate Actions To Undertake Following A Scam Incident
Secure Your Digital Assets Immediate Actions To Undertake Following A Scam IncidentThe purpose of this slide is to outline the steps to follow after the scam. This slide highlights the actions to be taken after the fraud, such as maintaining calm and composure, documenting the incident, and contacting the authorities. Introducing Secure Your Digital Assets Immediate Actions To Undertake Following A Scam Incident to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Documenting The Incident, Contacting The Authorities, Maintaining Calm And Composure, using this template. Grab it now to reap its full benefits.
-
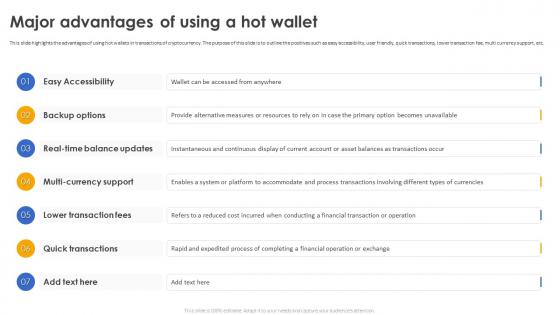 Secure Your Digital Assets Major Advantages Of Using A Hot Wallet
Secure Your Digital Assets Major Advantages Of Using A Hot WalletThis slide highlights the advantages of using hot wallets in transactions of cryptocurrency. The purpose of this slide is to outline the positives such as easy accessibility, user friendly, quick transactions, lower transaction fee, multi currency support, etc. Introducing Secure Your Digital Assets Major Advantages Of Using A Hot Wallet to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Real Time Balance Updates, Multi Currency Support, Lower Transaction Fees, Quick Transactions, using this template. Grab it now to reap its full benefits.
-
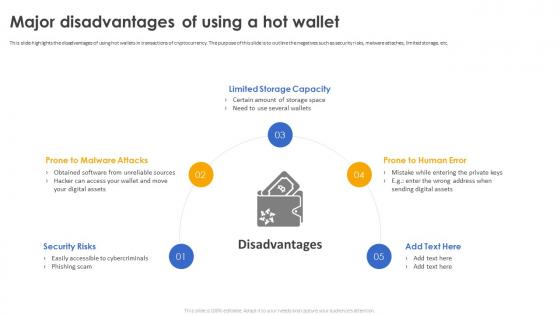 Secure Your Digital Assets Major Disadvantages Of Using A Hot Wallet
Secure Your Digital Assets Major Disadvantages Of Using A Hot WalletThis slide highlights the disadvantages of using hot wallets in transactions of cryptocurrency. The purpose of this slide is to outline the negatives such as security risks, malware attaches, limited storage, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Major Disadvantages Of Using A Hot Wallet. This template helps you present information on five stages. You can also present information on Limited Storage Capacity, Prone To Human Error, Prone To Malware Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Your Digital Assets Steps To Follow For Creating A Crypto Wallet
Secure Your Digital Assets Steps To Follow For Creating A Crypto WalletThe purpose of this slide is to discuss the steps to follow while opening the crypto wallet. This slide highlights those steps, such as selecting the software app, downloading the wallet app, creating the account, transferring the assets, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Steps To Follow For Creating A Crypto Wallet. This template helps you present information on five stages. You can also present information on Crypto Wallet, Transferring The Assets, Downloading The Wallet App using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Terms Security Types Unlocking Venture Capital A Strategic Guide For Entrepreneurs Fin SS
Terms Security Types Unlocking Venture Capital A Strategic Guide For Entrepreneurs Fin SSThis slide explains the various types of securities or financial instruments involved in a venture capital deal. The options include common stock, preferred stock, convertible notes, or other instruments used to raise capital and manage ownership. Deliver an outstanding presentation on the topic using this Terms Security Types Unlocking Venture Capital A Strategic Guide For Entrepreneurs Fin SS. Dispense information and present a thorough explanation of Common Stock, Preferred Stock, Restricted Stock using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
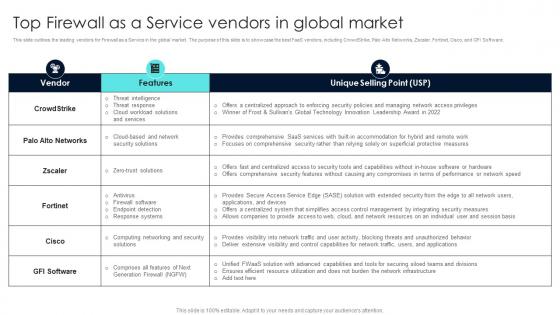 Firewall Network Security Top Firewall As A Service Vendors In Global Market
Firewall Network Security Top Firewall As A Service Vendors In Global MarketThis slide outlines the leading vendors for Firewall as a Service in the global market. The purpose of this slide is to showcase the best FaaS vendors, including CrowdStrike, Palo Alto Networks, Zscaler, Fortinet, Cisco, and GFI Software. Present the topic in a bit more detail with this Firewall Network Security Top Firewall As A Service Vendors In Global Market Use it as a tool for discussion and navigation on Unique Selling Point, Network Infrastructure This template is free to edit as deemed fit for your organization. Therefore download it now.
-
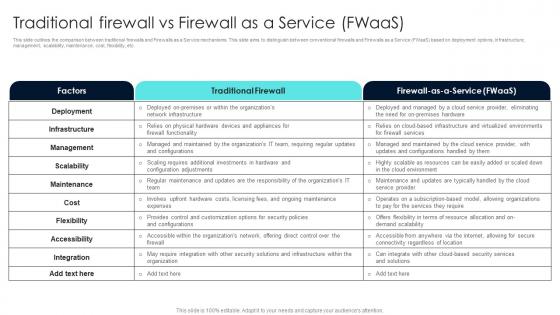 Firewall Network Security Traditional Firewall Vs Firewall As A Service FWaas
Firewall Network Security Traditional Firewall Vs Firewall As A Service FWaasThis slide outlines the comparison between traditional firewalls and Firewalls as a Service mechanisms. This slide aims to distinguish between conventional firewalls and Firewalls as a Service FWaaS based on deployment options, infrastructure, management, scalability, maintenance, cost, flexibility, etc. Present the topic in a bit more detail with this Firewall Network Security Traditional Firewall Vs Firewall As A Service FWaas Use it as a tool for discussion and navigation on Traditional Firewall, Factors, Maintenance This template is free to edit as deemed fit for your organization. Therefore download it now.
-
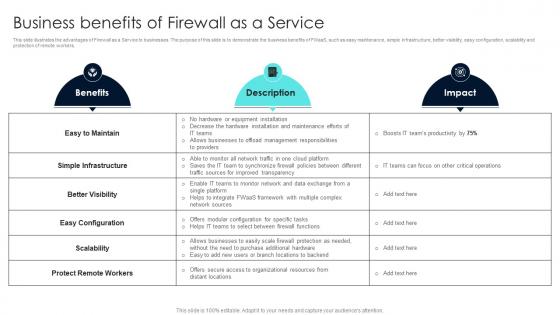 Firewall Network Security Business Benefits Of Firewall As A Service
Firewall Network Security Business Benefits Of Firewall As A ServiceThis slide illustrates the advantages of Firewall as a Service to businesses. The purpose of this slide is to demonstrate the business benefits of FWaas, such as easy maintenance,simple infrastructure, better visibility, easy configuration, scalability and protectionof remote workers. Deliver an outstanding presentation on the topic using this Firewall Network Security Business Benefits Of Firewall As A Service Dispense information and present a thorough explanation of Benefits, Description, Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
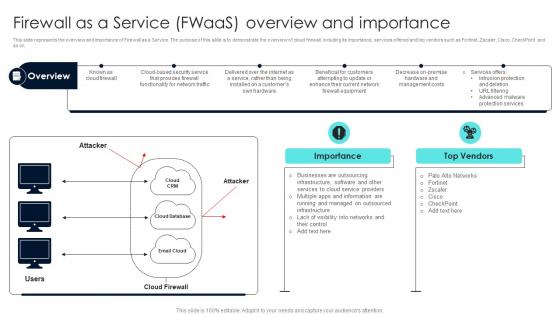 Firewall Network Security Firewall As A Service FWaas Overview And Importance
Firewall Network Security Firewall As A Service FWaas Overview And ImportanceThis slide represents the overview and importance of Firewall as a Service. The purpose of this slide is to demonstrate the overview of cloud firewall, including its importance, services offered and top vendors such as Fortinet,Zscaler, Cisco, CheckPoint and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Firewall As A Service FWaas Overview And Importance Dispense information and present a thorough explanation of Cloud Firewall, Attackers, Working using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
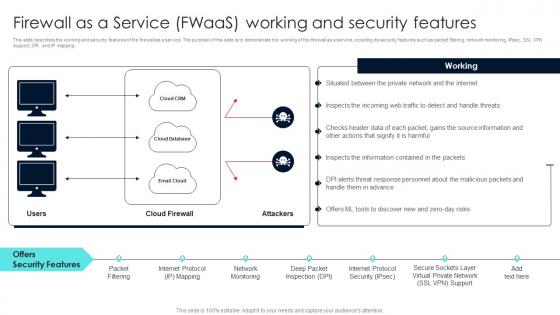 Firewall Network Security Firewall As A Service FWaas Working And Security Features
Firewall Network Security Firewall As A Service FWaas Working And Security FeaturesThis slide describes the working and security features of the firewall as a service. The purpose of this slide is to demonstrate the working of the firewall as a service, including its security features such as packet filtering, network monitoring, IPsec, SSL VPN support, DPI, andIP mapping. Present the topic in a bit more detail with this Firewall Network Security Firewall As A Service FWaas Working And Security Features Use it as a tool for discussion and navigation on Firewall Correctly, Audit Software And Logs This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Firewall Network Security How Does A Hardware Firewall Works
Firewall Network Security How Does A Hardware Firewall WorksThis slide provides an overview of the working of hardware firewalls. The purpose of this slide is to showcase the various steps a hardware firewall takes to protect a network and devices from malicious activities. The components of a network containing hardware firewall include LAN, hardware firewall, and internet. Deliver an outstanding presentation on the topic using this Firewall Network Security How Does A Hardware Firewall Works Dispense information and present a thorough explanation of Security From Insider Attacks, Intrusion Detection, Service Exposure And Port Scanning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
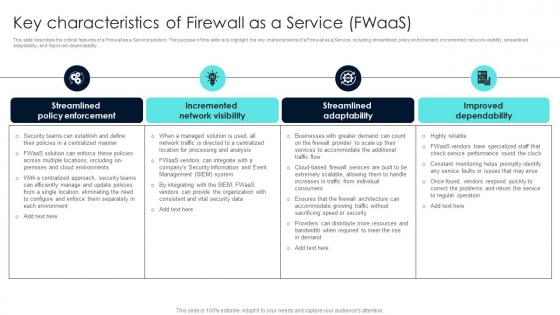 Firewall Network Security Key Characteristics Of Firewall As A Service FWaas
Firewall Network Security Key Characteristics Of Firewall As A Service FWaasThis slide describes the critical features of a Firewall as a Service solution. The purpose of this slide is to highlight the key characteristics of a Firewall as a Service, including streamlined policy enforcement, incremented network visibility, streamlined adaptability, and improved dependability. Introducing Firewall Network Security Key Characteristics Of Firewall As A Service FWaas to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Graphical Interface, Device Management, Scalability using this template. Grab it now to reap its full benefits.
-
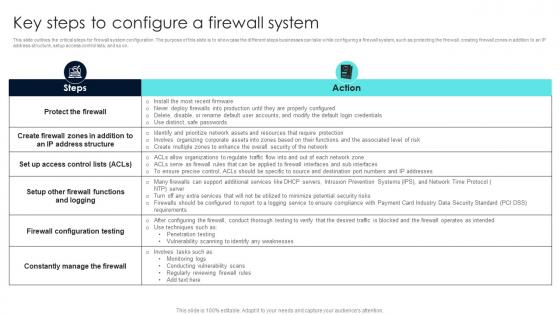 Firewall Network Security Key Steps To Configure A Firewall System
Firewall Network Security Key Steps To Configure A Firewall SystemThis slide outlines the critical steps for firewall system configuration. The purpose of this slide is to showcase the different steps businesses can take while configuring a firewall system, such as protecting the firewall, creating firewall zones in addition to an IP address structure, setup access control lists, and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Key Steps To Configure A Firewall System Dispense information and present a thorough explanation of Complexity, False Sense Of Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
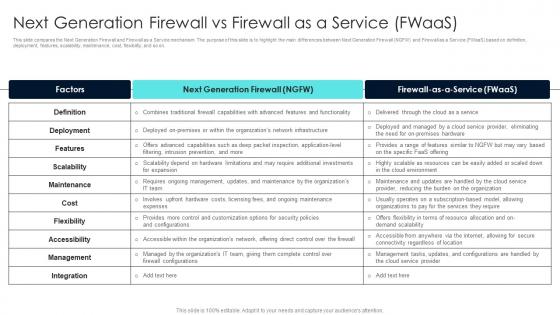 Firewall Network Security Next Generation Firewall Vs Firewall As A Service FWaas
Firewall Network Security Next Generation Firewall Vs Firewall As A Service FWaasThis slide compares the Next Generation Firewall and Firewall as a Service mechanism. The purpose of this slide is to highlight the main differences between Next Generation Firewall NGFW and Firewall as a Service FWaas based on definition, deployment, features, scalability, maintenance, cost, flexibility, and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Next Generation Firewall Vs Firewall As A Service FWaas Dispense information and present a thorough explanation of Make Decisions, Protocol Usage, Passing Through, Implementing These Policies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
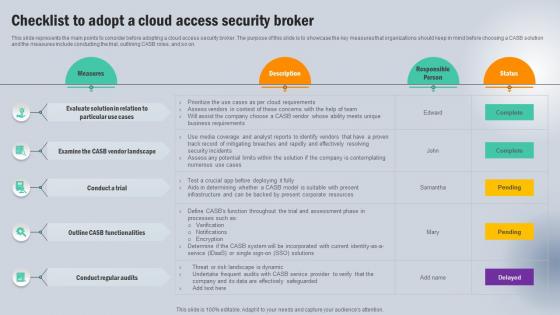 Checklist To Adopt A Cloud Access Security Broker Next Generation CASB
Checklist To Adopt A Cloud Access Security Broker Next Generation CASBThis slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Deliver an outstanding presentation on the topic using this Checklist To Adopt A Cloud Access Security Broker Next Generation CASB Dispense information and present a thorough explanation of Vendor Landscape, Conduct A Trial, Functionalities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
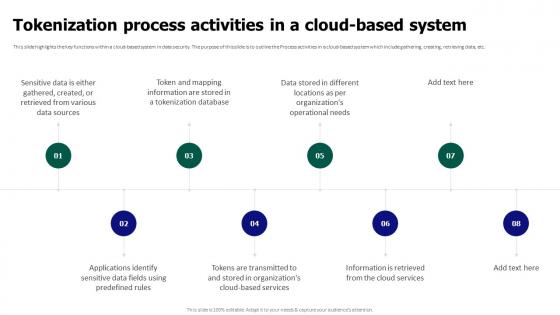 Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System
Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based SystemThis slide highlights the key functions within a cloud-based system in data security. The purpose of this slide is to outline the Process activities in a cloud-based system which include gathering, creating, retrieving data, etc. Introducing Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization Process Activities, Cloud Based System, Retrieving Data, using this template. Grab it now to reap its full benefits.
-
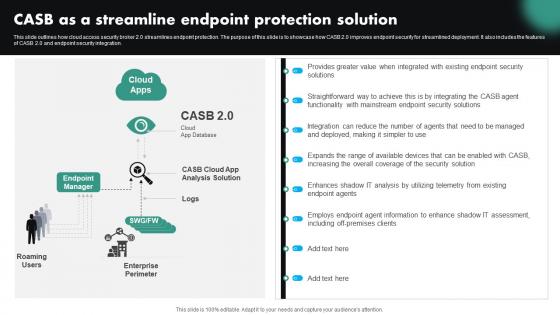 CASB As A Streamline Endpoint Protection Solution CASB Cloud Security
CASB As A Streamline Endpoint Protection Solution CASB Cloud SecurityThis slide outlines how cloud access security broker 2.0 streamlines endpoint protection. The purpose of this slide is to showcase how CASB 2.0 improves endpoint security for streamlined deployment. It also includes the features of CASB 2.0 and endpoint security integration. Deliver an outstanding presentation on the topic using this CASB As A Streamline Endpoint Protection Solution CASB Cloud Security. Dispense information and present a thorough explanation of Streamline Endpoint Protection Solution, Endpoint Security Integration, Streamlined Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist To Adopt A Cloud Access Security Broker CASB Cloud Security
Checklist To Adopt A Cloud Access Security Broker CASB Cloud SecurityThis slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Deliver an outstanding presentation on the topic using this Checklist To Adopt A Cloud Access Security Broker CASB Cloud Security. Dispense information and present a thorough explanation of Cloud Access Security Broker, Contemplating Numerous, Threat Or Risk Landscape Is Dynamic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
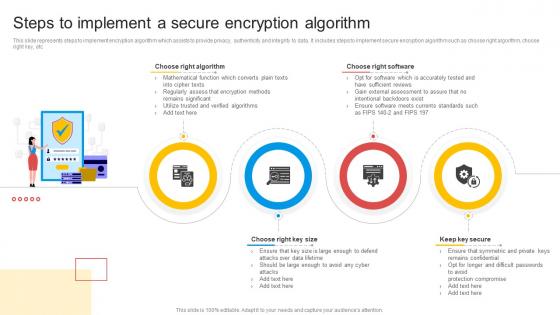 Steps To Implement A Secure Encryption Algorithm
Steps To Implement A Secure Encryption AlgorithmThis slide represents steps to implement encryption algorithm which assists to provide privacy, authenticity and integrity to data. It includes steps to implement secure encryption algorithm such as choose right algorithm, choose right key, etc. Presenting our set of slides with name Steps To Implement A Secure Encryption Algorithm. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Choose Right Algorithm, Choose Right Software, Keep Key Secure.
-
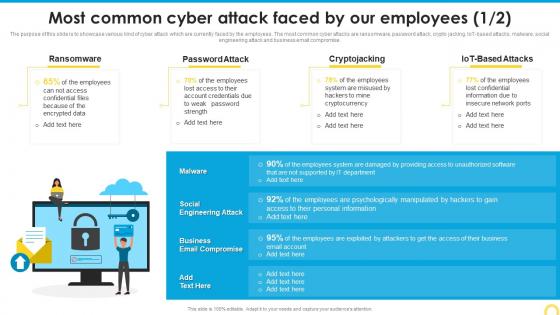 Most Common Cyber Attack Building A Security Awareness Program
Most Common Cyber Attack Building A Security Awareness ProgramThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT based attacks, malware, social engineering attack and business email compromise. Present the topic in a bit more detail with this Most Common Cyber Attack Building A Security Awareness Program. Use it as a tool for discussion and navigation on Ransomware, Password Attack, Cryptojacking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Awareness Training Program Challenges Building A Security Awareness Program
Security Awareness Training Program Challenges Building A Security Awareness ProgramThe purpose of this slide is to exhibit biggest cyber security awareness challenges which is faced by the organization. Outdated content, burden on administrators, low employee participation rate and employees losing interest are some of the key challenges which are highlighted in the slide. Present the topic in a bit more detail with this Security Awareness Training Program Challenges Building A Security Awareness Program. Use it as a tool for discussion and navigation on Outdated Content, Burden Administrators, Employee Participation Rate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 A vendor application security testing diagram example ppt presentation
A vendor application security testing diagram example ppt presentationPresenting a vendor application security testing diagram example ppt presentation. This is a vendor application security testing diagram example ppt presentation. This is a three stage process. The stages in this process are enterprise customer, vast program, 3rd party vendor.
-
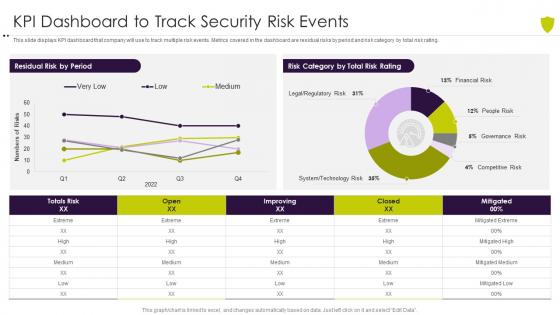 Kpi dashboard to track security risk events managing cyber risk in a digital age
Kpi dashboard to track security risk events managing cyber risk in a digital ageThis slide displays KPI dashboard that company will use to track multiple risk events. Metrics covered in the dashboard are residual risks by period and risk category by total risk rating. Deliver an outstanding presentation on the topic using this Kpi Dashboard To Track Security Risk Events Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of KPI Dashboard To Track Security Risk Events using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
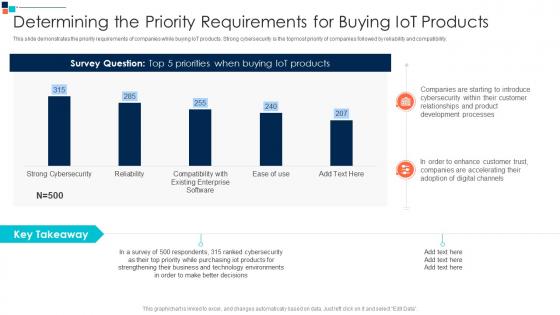 Determining The Priority A Risk Based Approach To Cyber Security
Determining The Priority A Risk Based Approach To Cyber SecurityThis slide demonstrates the priority requirements of companies while buying IoT products. Strong cybersecurity is the topmost priority of companies followed by reliability and compatibility.Deliver an outstanding presentation on the topic using this Determining The Priority A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Companies Are Starting, Relationships And Product, Development Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Global Market Insights Cybersecurity Introducing A Risk Based Approach To Cyber Security
Global Market Insights Cybersecurity Introducing A Risk Based Approach To Cyber SecurityFollowing slide illustrates the global market insights of cybersecurity covering statistics related to integrated risk management, investment in cybersecurity and digital transformation.Present the topic in a bit more detail with this Global Market Insights Cybersecurity Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Fastest Growing Market, Largest Market, Approach To Digital Risk This template is free to edit as deemed fit for your organization. Therefore download it now.
-
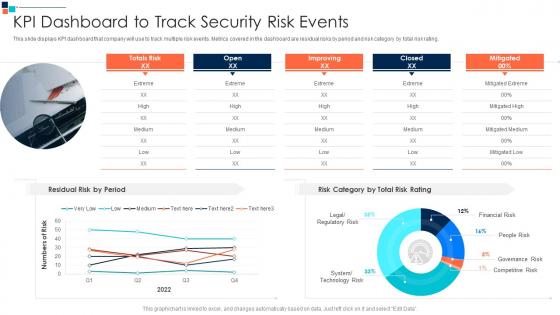 KPI Dashboard To Track Security Risk Events Introducing A Risk Based Approach To Cyber Security
KPI Dashboard To Track Security Risk Events Introducing A Risk Based Approach To Cyber SecurityThis slide displays KPI dashboard that company will use to track multiple risk events. Metrics covered in the dashboard are residual risks by period and risk category by total risk rating.Present the topic in a bit more detail with this KPI Dashboard To Track Security Risk Events Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Kpi Dashboard To Track Security Risk Events This template is free to edit as deemed fit for your organization. Therefore download it now.
-
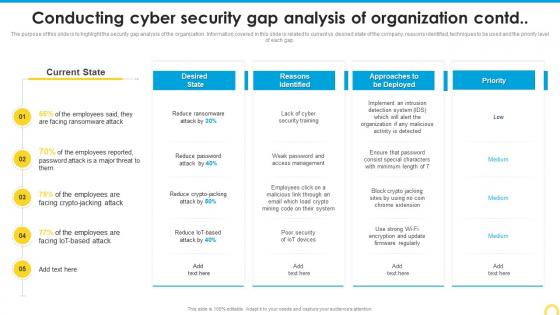 Conducting Cyber Security Building A Security Awareness Program
Conducting Cyber Security Building A Security Awareness ProgramThe purpose of this slide is to highlight the security gap analysis of the organization. Information covered in this slide is related to current vs desired state of the company, reasons identified, techniques to be used and the priority level of each gap. Present the topic in a bit more detail with this Conducting Cyber Security Building A Security Awareness Program. Use it as a tool for discussion and navigation on Reasons Identified, Analysis, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
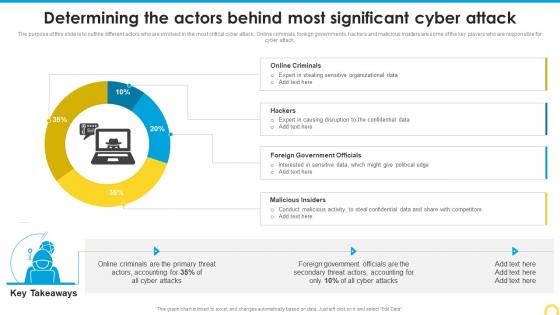 Determining The Actors Behind Building A Security Awareness Program
Determining The Actors Behind Building A Security Awareness ProgramThe purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Deliver an outstanding presentation on the topic using this Determining The Actors Behind Building A Security Awareness Program. Dispense information and present a thorough explanation of Foreign Government, Malicious Insiders, Significant Cyber Attack using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
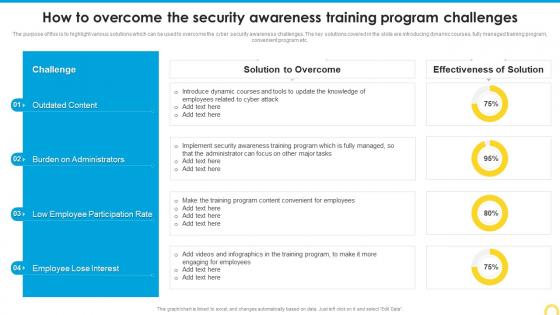 How To Overcome The Security Building A Security Awareness Program
How To Overcome The Security Building A Security Awareness ProgramThe purpose of this is to highlight various solutions which can be used to overcome the cyber security awareness challenges. The key solutions covered in the slide are introducing dynamic courses, fully managed training program, convenient program etc. Deliver an outstanding presentation on the topic using this How To Overcome The Security Building A Security Awareness Program. Dispense information and present a thorough explanation of Outdated Content, Participation Rate, Burden Administrators using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
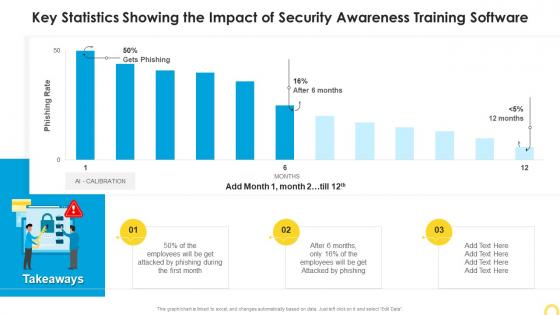 Key Statistics Showing The Impact Of Building A Security Awareness Program
Key Statistics Showing The Impact Of Building A Security Awareness ProgramPresent the topic in a bit more detail with this Key Statistics Showing The Impact Of Building A Security Awareness Program. Use it as a tool for discussion and navigation on Statistics Showing, Security Awareness, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
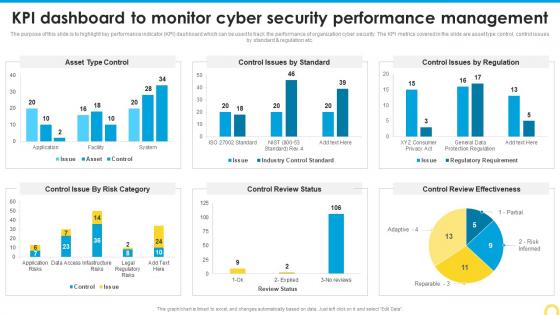 Kpi Dashboard To Monitor Cyber Building A Security Awareness Program
Kpi Dashboard To Monitor Cyber Building A Security Awareness ProgramThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Deliver an outstanding presentation on the topic using this KPI Dashboard To Monitor Cyber Building A Security Awareness Program. Dispense information and present a thorough explanation of Control Review Effectiveness, Performance Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
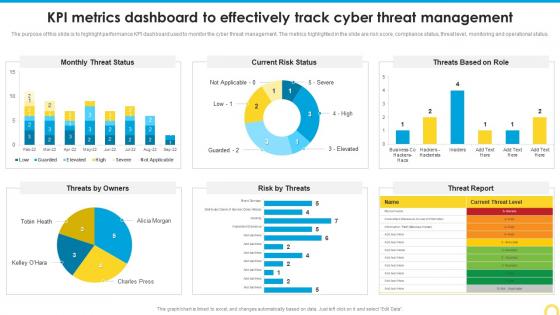 KPI Metrics Dashboard To Effectively Building A Security Awareness Program
KPI Metrics Dashboard To Effectively Building A Security Awareness ProgramThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this KPI Metrics Dashboard To Effectively Building A Security Awareness Program. Use it as a tool for discussion and navigation on Threat Management, Metrics Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
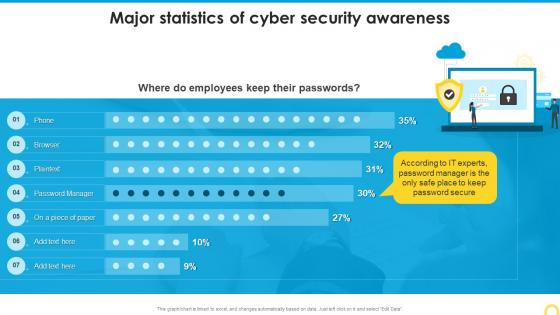 Major Statistics Of Cyber Security Awareness Building A Security Awareness Program
Major Statistics Of Cyber Security Awareness Building A Security Awareness ProgramDeliver an outstanding presentation on the topic using this Major Statistics Of Cyber Security Awareness Building A Security Awareness Program. Dispense information and present a thorough explanation of Major Statistics, Cyber Security Awareness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
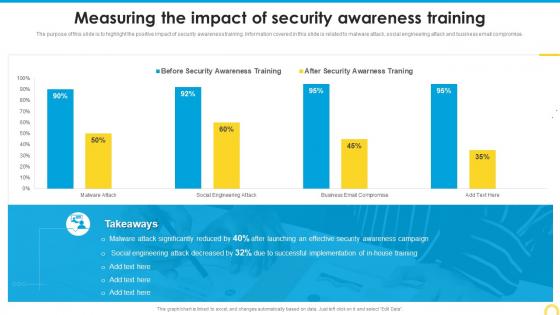 Measuring The Impact Of Security Building A Security Awareness Program
Measuring The Impact Of Security Building A Security Awareness ProgramThe purpose of this slide is to highlight the positive impact of security awareness training. Information covered in this slide is related to malware attack, social engineering attack and business email compromise. Deliver an outstanding presentation on the topic using this Measuring The Impact Of Security Building A Security Awareness Program. Dispense information and present a thorough explanation of Security Awareness, Training, Measuring Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
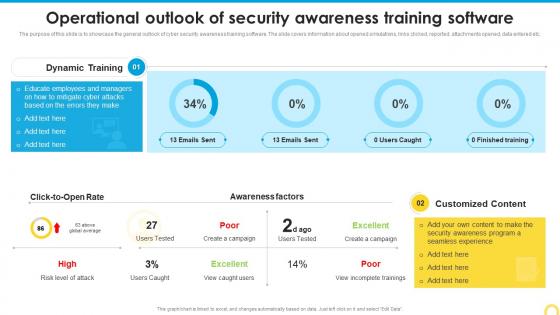 Operational Outlook Of Security Building A Security Awareness Program
Operational Outlook Of Security Building A Security Awareness ProgramThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Present the topic in a bit more detail with this Operational Outlook Of Security Building A Security Awareness Program. Use it as a tool for discussion and navigation on Customized Content, Awareness Factors, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
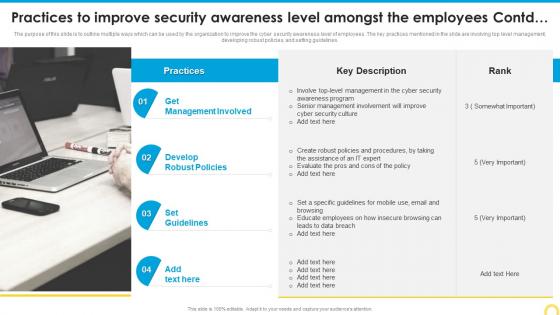 Practices To Improve Security Building A Security Awareness Program
Practices To Improve Security Building A Security Awareness ProgramThe purpose of this slide is to outline multiple ways which can be used by the organization to improve the cyber security awareness level of employees. The key practices mentioned in the slide are involving top level management, developing robust policies, and setting guidelines. Introducing Practices To Improve Security Building A Security Awareness Program to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management Involved, Develop Robust Policies, Set Guidelines, using this template. Grab it now to reap its full benefits.
-
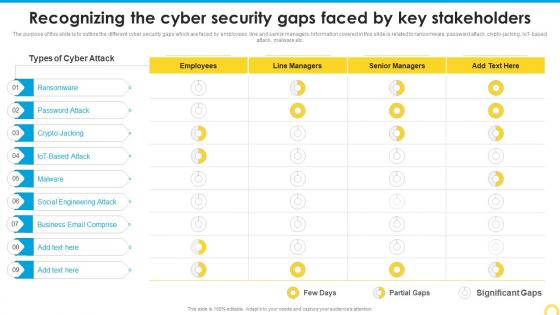 Recognizing The Cyber Security Building A Security Awareness Program
Recognizing The Cyber Security Building A Security Awareness ProgramThe purpose of this slide is to outline the different cyber security gaps which are faced by employees, line and senior managers. Information covered in this slide is related to ransomware, password attack, crypto-jacking, IoT based attack, malware etc. Present the topic in a bit more detail with this Recognizing The Cyber Security Building A Security Awareness Program. Use it as a tool for discussion and navigation on Ransomware, Social Engineering Attack, Business Email Comprise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
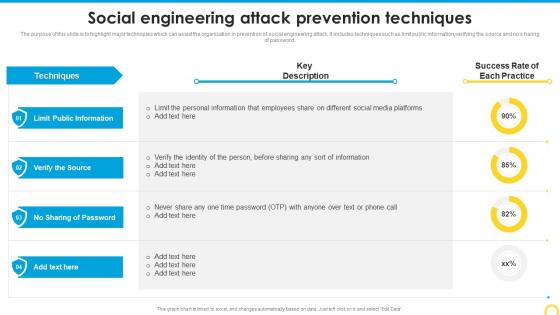 Social Engineering Attack Prevention Techniques Building A Security Awareness Program
Social Engineering Attack Prevention Techniques Building A Security Awareness ProgramThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no s haring of password. Deliver an outstanding presentation on the topic using this Social Engineering Attack Prevention Techniques Building A Security Awareness Program. Dispense information and present a thorough explanation of Public Information, Prevention Techniques, Social Engineering Attack using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
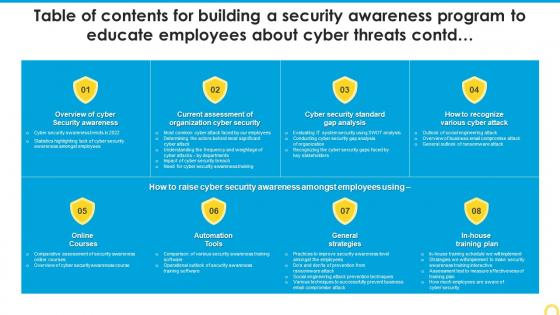 Table Of Contents For Building A Security Awareness Program To Educate Employees
Table Of Contents For Building A Security Awareness Program To Educate EmployeesDeliver an outstanding presentation on the topic using this Table Of Contents For Building A Security Awareness Program To Educate Employees. Dispense information and present a thorough explanation of Organization, Cyber Security, Current Assessment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Image of internet security with a lock
Image of internet security with a lockPresenting this set of slides with name Image Of Internet Security With A Lock. This is a one stage process. The stages in this process are Internet, Marketing, Internet Security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
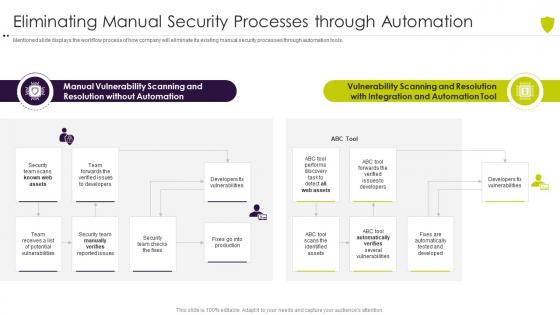 Eliminating manual security processes managing cyber risk in a digital age
Eliminating manual security processes managing cyber risk in a digital ageMentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools. Present the topic in a bit more detail with this Eliminating Manual Security Processes Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Vulnerability, Scanning, Resolution, Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
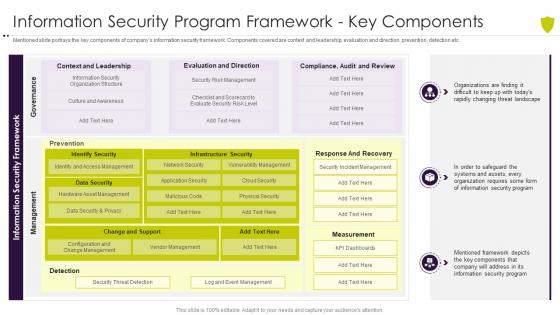 Information security program framework managing cyber risk in a digital age
Information security program framework managing cyber risk in a digital ageMentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc. Deliver an outstanding presentation on the topic using this Information Security Program Framework Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Information Security Program Framework Key Components using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
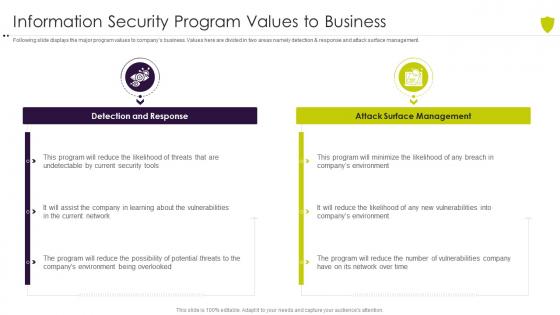 Managing cyber risk in a digital age information security program values to business
Managing cyber risk in a digital age information security program values to businessFollowing slide displays the major program values to companys business. Values here are divided in two areas namely detection and response and attack surface management. Introducing Managing Cyber Risk In A Digital Age Information Security Program Values To Business to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Response, Management, Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
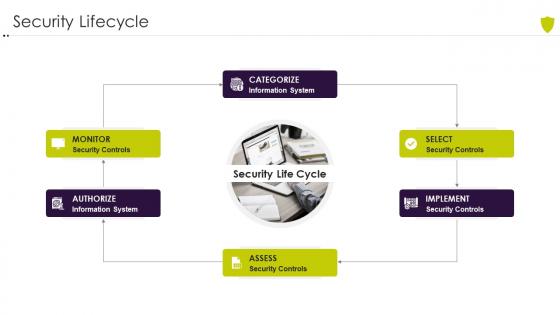 Security lifecycle managing cyber risk in a digital age
Security lifecycle managing cyber risk in a digital ageIncrease audience engagement and knowledge by dispensing information using Security Lifecycle Managing Cyber Risk In A Digital Age. This template helps you present information on one stages. You can also present information on Security Lifecycle using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
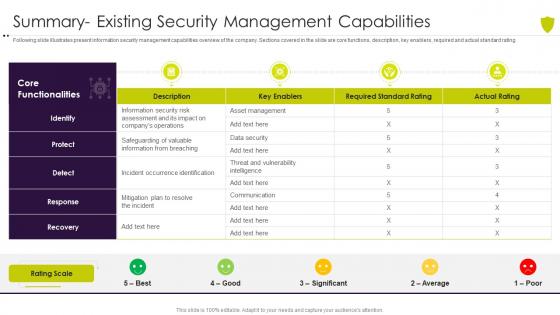 Summary existing security managing cyber risk in a digital age
Summary existing security managing cyber risk in a digital ageFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Present the topic in a bit more detail with this Summary Existing Security Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Summary Existing Security Management Capabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
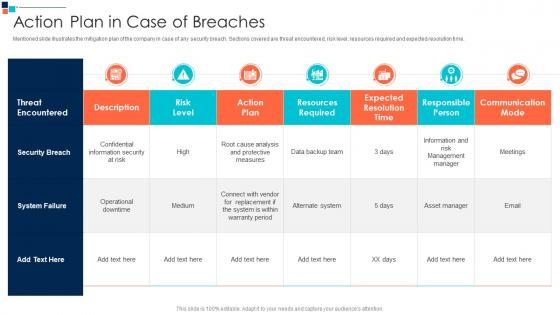 Action Plan In Case Of Breaches Introducing A Risk Based Approach To Cyber Security
Action Plan In Case Of Breaches Introducing A Risk Based Approach To Cyber SecurityMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time.Present the topic in a bit more detail with this Action Plan In Case Of Breaches Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Expected Resolution Time, Responsible Person, Communication Mode This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda Of Introducing A Risk Based Approach To Cyber Security
Agenda Of Introducing A Risk Based Approach To Cyber SecurityIntroducing Agenda Of Introducing A Risk Based Approach To Cyber Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Agenda using this template. Grab it now to reap its full benefits.
-
 Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach
Checklist For Effectively Managing Asset Security Introducing A Risk Based ApproachFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Introducing Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on System Monitoring, Virus Scanning, System Monitoring using this template. Grab it now to reap its full benefits.
-
 Communication Plan For Cyber Breaches Introducing A Risk Based Approach To Cyber Security
Communication Plan For Cyber Breaches Introducing A Risk Based Approach To Cyber SecurityMentioned slide portrays communication plan that company will use for effectively managing cyber breaches. Sections covered here are what to communicate, description, delivery method, frequency and responsible.Present the topic in a bit more detail with this Communication Plan For Cyber Breaches Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Evaluate Sprint Status, Quality Standards, Project Coordinator This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security
Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber SecurityFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost.Deliver an outstanding presentation on the topic using this Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Infrastructure Hardware, Routers And Switches, Server Computers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Defining Business Security Introducing A Risk Based Approach To Cyber Security
Defining Business Security Introducing A Risk Based Approach To Cyber SecurityThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security.Introducing Defining Business Security Introducing A Risk Based Approach To Cyber Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Efficient Risk Management, Standardized Incident, Management Process using this template. Grab it now to reap its full benefits.
-
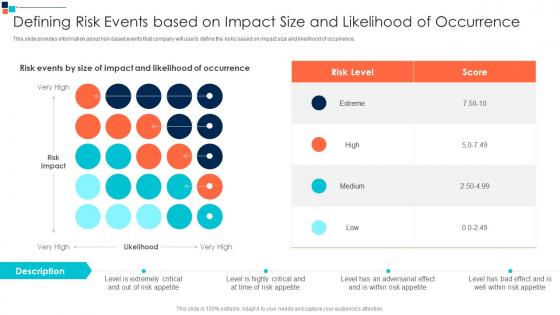 Defining Risk Events Based On Introducing A Risk Based Approach To Cyber Security
Defining Risk Events Based On Introducing A Risk Based Approach To Cyber SecurityThis slide provides information about risk based events that company will use to define the risks based on impact size and likelihood of occurrence.Present the topic in a bit more detail with this Defining Risk Events Based On Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Defining Risk Events Based On Impact Size And Likelihood Of Occurrence This template is free to edit as deemed fit for your organization. Therefore download it now.



