Powerpoint Templates and Google slides for Security Assessment
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 It security operations assessment of security maturity spectrum ppt powerpoint ideas elements
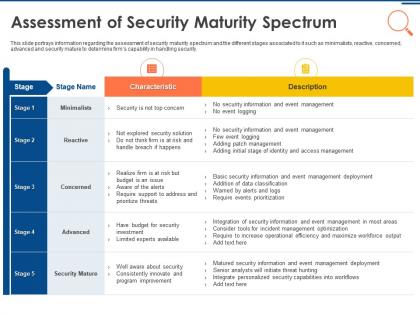
It security operations assessment of security maturity spectrum ppt powerpoint ideas elementsThis slide portrays information regarding the assessment of security maturity spectrum and the different stages associated to it such as minimalists, reactive, concerned, advanced and security mature to determine firms capability in handling security. Deliver an outstanding presentation on the topic using this IT Security Operations Assessment Of Security Maturity Spectrum Ppt Powerpoint Ideas Elements. Dispense information and present a thorough explanation of Minimalists, Reactive, Concerned, Advanced, Security Mature using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 It security operations insider attacker method and behaviour assessment ppt graphics tutorials
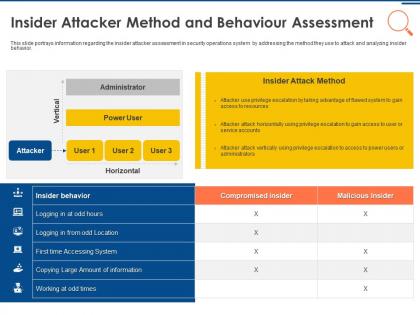
It security operations insider attacker method and behaviour assessment ppt graphics tutorialsThis slide portrays information regarding the insider attacker assessment in security operations system by addressing the method they use to attack and analyzing insider behavior. Present the topic in a bit more detail with this IT Security Operations Insider Attacker Method And Behaviour Assessment Ppt Graphics Tutorials. Use it as a tool for discussion and navigation on Insider Attacker Method And Behaviour Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk assessment and analysis steps set up advanced security management plan ppt designs
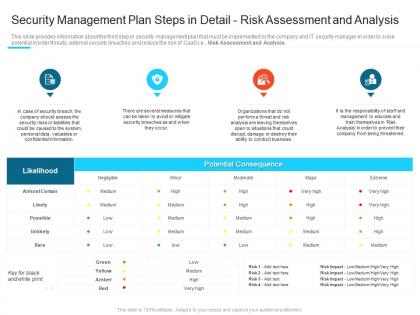
Risk assessment and analysis steps set up advanced security management plan ppt designsThis slide provides information about the third step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Risk Assessment and Analysis. Present the topic in a bit more detail with this Risk Assessment And Analysis Steps Set Up Advanced Security Management Plan Ppt Designs. Use it as a tool for discussion and navigation on Security Management Plan Steps In Detail Risk Assessment And Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security risk management assessment checklist steps set up advanced security management plan
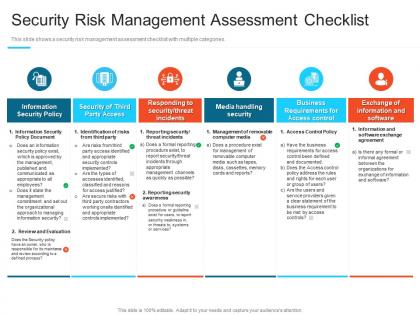
Security risk management assessment checklist steps set up advanced security management planThis slide shows a security risk management assessment checklist with multiple categories. Present the topic in a bit more detail with this Security Risk Management Assessment Checklist Steps Set Up Advanced Security Management Plan. Use it as a tool for discussion and navigation on Information Security Policy, Security Of Third Party Access, Responding To Security Threat Incidents. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
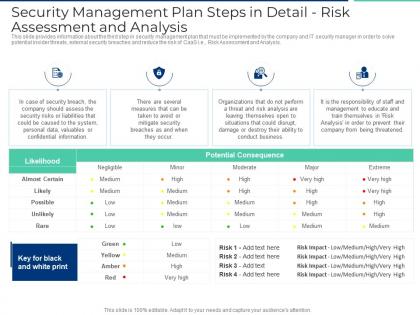 Security management plan steps in detail risk assessment and analysis ppt guidelines
Security management plan steps in detail risk assessment and analysis ppt guidelinesThis slide provides information about the third step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Risk Assessment and Analysis. Deliver an outstanding presentation on the topic using this Security Management Plan Steps In Detail Risk Assessment And Analysis Ppt Guidelines. Dispense information and present a thorough explanation of Potential Consequence, Low, Medium, High, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
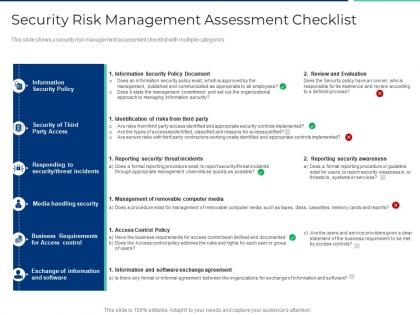 Security risk management assessment checklist ppt ideas graphics tutorials
Security risk management assessment checklist ppt ideas graphics tutorialsThis slide shows a security risk management assessment checklist with multiple categories. Present the topic in a bit more detail with this Security Risk Management Assessment Checklist Ppt Ideas Graphics Tutorials. Use it as a tool for discussion and navigation on Security Policy, Identification Of Risks, Reporting Security, Security Awareness, Review And Evaluation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
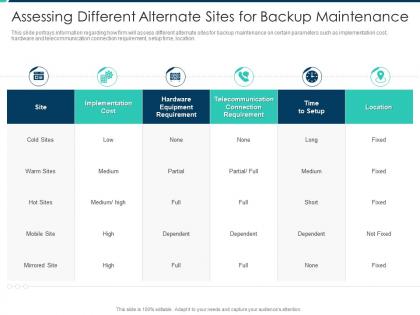 Assessing different alternate sites for backup maintenance security operations integration
Assessing different alternate sites for backup maintenance security operations integrationThis slide portrays information regarding how firm will assess different alternate sites for backup maintenance on certain parameters such as implementation cost, hardware and telecommunication connection requirement, setup time, location.Present the topic in a bit more detail with this Assessing Different Alternate Sites For Backup Maintenance Security Operations Integration. Use it as a tool for discussion and navigation on Implementation Cost, Hardware Equipment Requirement, Telecommunication Connection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
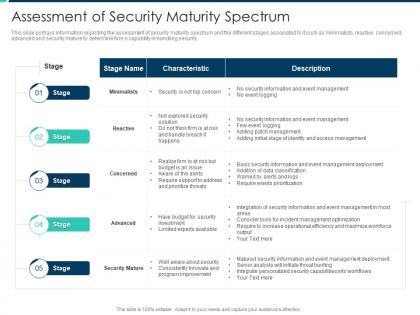 Assessment of security maturity spectrum security operations integration ppt summary
Assessment of security maturity spectrum security operations integration ppt summaryThis slide portrays information regarding the assessment of security maturity spectrum and the different stages associated to it such as minimalists, reactive, concerned, advanced and security mature to determine firms capability in handling security.Deliver an outstanding presentation on the topic using this Assessment Of Security Maturity Spectrum Security Operations Integration Ppt Summary. Dispense information and present a thorough explanation of Assessment Of Security Maturity Spectrum using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
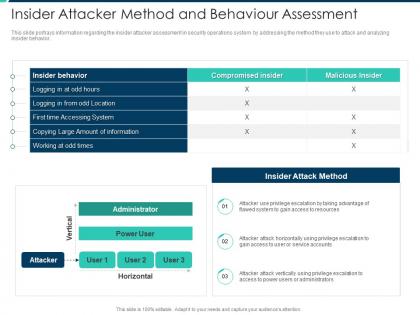 Insider attacker method and behaviour assessment security operations integration ppt themes
Insider attacker method and behaviour assessment security operations integration ppt themesThis slide portrays information regarding the insider attacker assessment in security operations system by addressing the method they use to attack and analyzing insider behavior. Deliver an outstanding presentation on the topic using this Insider Attacker Method And Behaviour Assessment Security Operations Integration Ppt Themes. Dispense information and present a thorough explanation of Insider Behavior, Insider Attack Method, Compromised Insider using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
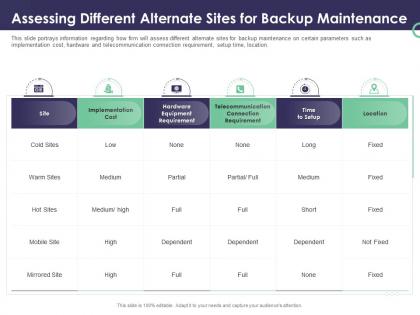 Enterprise security operations assessing different alternate sites for backup maintenance ppt aids
Enterprise security operations assessing different alternate sites for backup maintenance ppt aidsThis slide portrays information regarding how firm will assess different alternate sites for backup maintenance on certain parameters such as implementation cost, hardware and telecommunication connection requirement, setup time, location. Present the topic in a bit more detail with this Enterprise Security Operations Assessing Different Alternate Sites For Backup Maintenance Ppt Aids. Use it as a tool for discussion and navigation on Implementation, Cost, Location, Telecommunication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
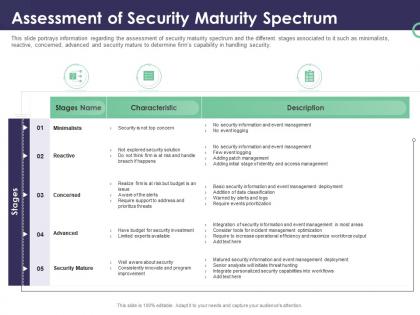 Enterprise security operations assessment of security maturity spectrum ppt powerpoint visual aids
Enterprise security operations assessment of security maturity spectrum ppt powerpoint visual aidsThis slide portrays information regarding the assessment of security maturity spectrum and the different stages associated to it such as minimalists, reactive, concerned, advanced and security mature to determine firms capability in handling security. Deliver an outstanding presentation on the topic using this Enterprise Security Operations Assessment Of Security Maturity Spectrum Ppt Powerpoint Visual Aids. Dispense information and present a thorough explanation of Minimalists, Reactive, Concerned, Advanced, Security Mature using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
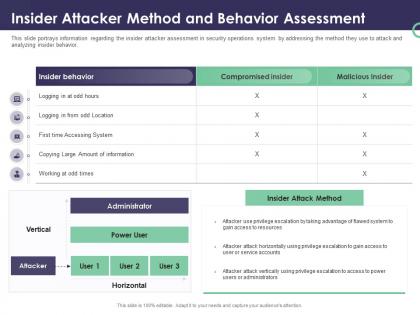 Enterprise security operations insider attacker method and behavior assessment ppt gridlines
Enterprise security operations insider attacker method and behavior assessment ppt gridlinesThis slide portrays information regarding the insider attacker assessment in security operations system by addressing the method they use to attack and analyzing insider behavior. Present the topic in a bit more detail with this Enterprise Security Operations Insider Attacker Method And Behavior Assessment Ppt Gridlines. Use it as a tool for discussion and navigation on Insider Attacker Method And Behaviour Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information security risk assessment tools ppt powerpoint presentation styles gallery cpb
Information security risk assessment tools ppt powerpoint presentation styles gallery cpbPresenting Information Security Risk Assessment Tools Ppt Powerpoint Presentation Styles Gallery Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Information Security Risk Assessment Tools. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
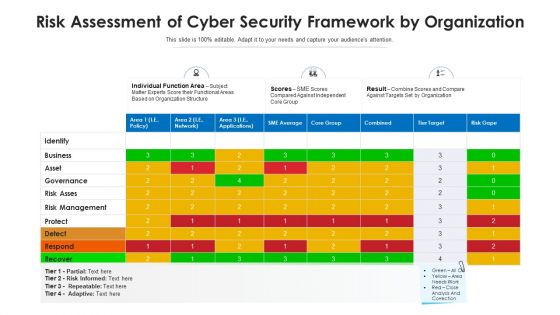 Risk assessment of cyber security framework by organization
Risk assessment of cyber security framework by organizationIntroducing our Risk Assessment Of Cyber Security Framework By Organization set of slides. The topics discussed in these slides are Business, Identify, Risk Management, Governance, Protect. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
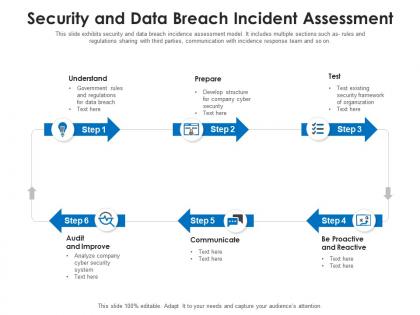 Security and data breach incident assessment
Security and data breach incident assessmentThis slide exhibits security and data breach incidence assessment model. It includes multiple sections such as- rules and regulations sharing with third parties, communication with incidence response team and so on. Presenting our set of slides with Security And Data Breach Incident Assessment. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Survey, Limit, Learn, Engage, Record.
-
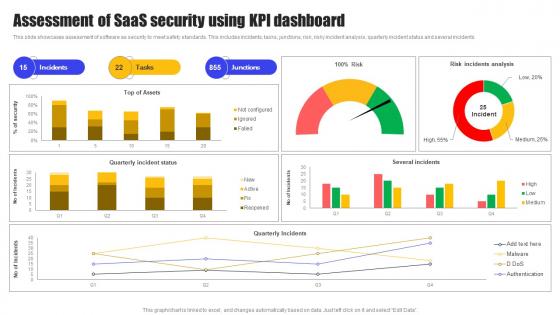 Assessment Of SaaS Security Using KPI Dashboard
Assessment Of SaaS Security Using KPI DashboardThis slide showcases assessment of software as security to meet safety standards. This includes incidents, tasks, junctions, risk, risky incident analysis, quarterly incident status and several incidents. Introducing our Assessment Of SaaS Security Using KPI Dashboard set of slides. The topics discussed in these slides are Quarterly Incident Status, Risk Incidents Analysis, Several Incidents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Information Security System Audit And Risk Assessment
Information Security System Audit And Risk AssessmentThe following slide highlights the information security system audit and risk assessment illustrating key headings which includes security risk assessment, security auditing, security incident monitoring, security incident response Presenting our set of slides with name Information Security System Audit And Risk Assessment. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Risk Assessment, Security Auditing, Security Incident Monitoring.
-
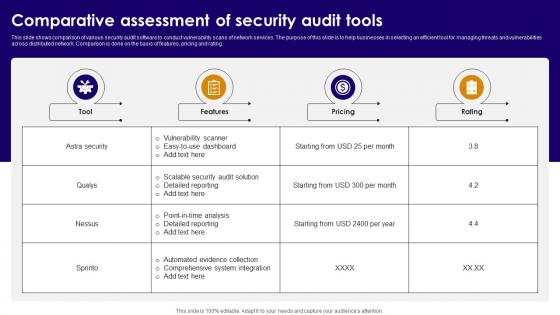 Comparative Assessment Of Security Audit Tools
Comparative Assessment Of Security Audit ToolsThis slide shows comparison of various security audit software to conduct vulnerability scans of network services. The purpose of this slide is to help businesses in selecting an efficient tool for managing threats and vulnerabilities across distributed network. Comparison is done on the basis of features, pricing and rating. Presenting our well structured Comparative Assessment Of Security Audit Tools. The topics discussed in this slide are Features, Pricing, Rating. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Information Security Audit Icon For Vulnerability Assessment
Information Security Audit Icon For Vulnerability AssessmentPresenting our set of slides with Information Security Audit Icon For Vulnerability Assessment. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Security Audit, Icon For Vulnerability Assessment
-
 IT Security Audit Workflow For Risk Assessment
IT Security Audit Workflow For Risk AssessmentThis slide presents four step workflow for conducting an IT security audit. The purpose of this slide is to help businesses in managing operational risks and compliance activities. It covers tasks such as deciding assessment criteria, planning security audit, executing and sharing results. Presenting our set of slides with IT Security Audit Workflow For Risk Assessment. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Decide Assessment Criteria, Plan Security Audit, Execute Security Audit
-
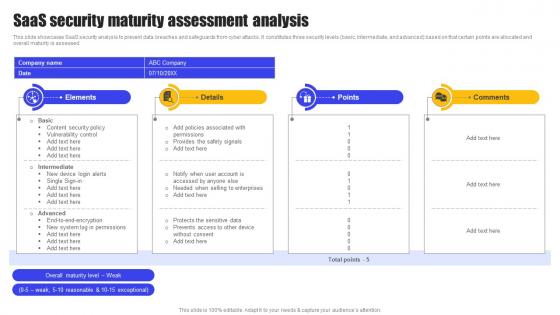 SaaS Security Maturity Assessment Analysis
SaaS Security Maturity Assessment AnalysisThis slide showcases SaaS security analysis to prevent data breaches and safeguards from cyber attacks. It constitutes three security levels basic, intermediate, and advanced based on that certain points are allocated and overall maturity is assessed. Presenting our well structured SaaS Security Maturity Assessment Analysis. The topics discussed in this slide are Prevents Access, Sensitive Data, Other Device. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Email Security Employee Skill Assessment
Email Security Employee Skill AssessmentThe purpose of this slide is to highlight how Email security employee skill assessment ensures a proactive approach to identify and address potential vulnerabilities, enhancing the organizations defense against cyber threats. Presenting our well structured Email Security Employee Skill Assessment. The topics discussed in this slide are Awareness, Phishing Detection, Password Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.


