Powerpoint Templates and Google slides for Security Assessment
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Impact assessment matrix effective information security risk management process
Impact assessment matrix effective information security risk management processPresent the topic in a bit more detail with this Impact Assessment Matrix Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Minor To No Infringement, Suspected Malicious Intent, Impact Medium. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
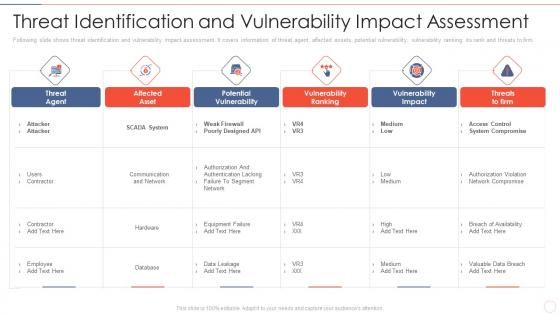 Threat assessment effective information security risk management process
Threat assessment effective information security risk management processFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Threat Assessment Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Affected Asset, Potential Vulnerability, Vulnerability Ranking using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security threat assessment ppt powerpoint presentation diagram ppt cpb
Security threat assessment ppt powerpoint presentation diagram ppt cpbPresenting Security Threat Assessment Ppt Powerpoint Presentation Diagram Ppt Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Threat Assessment. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
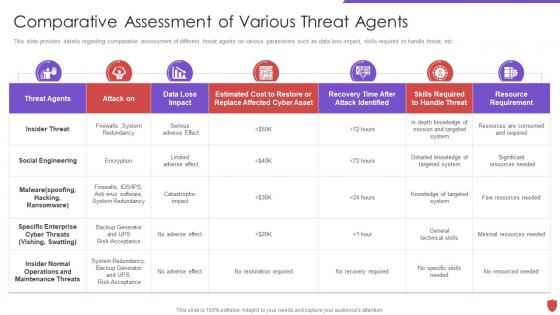 Cyber security risk management comparative assessment various threat agents
Cyber security risk management comparative assessment various threat agentsThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Deliver an outstanding presentation on the topic using this Cyber Security Risk Management Comparative Assessment Various Threat Agents. Dispense information and present a thorough explanation of Insider Threat, Social Engineering, Threat Agents, Cyber Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
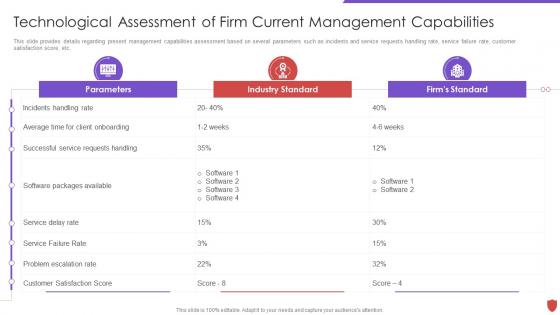 Technological assessment of firm current capabilities cyber security risk management
Technological assessment of firm current capabilities cyber security risk managementThis slide provides details regarding present management capabilities assessment based on several parameters such as incidents and service requests handling rate, service failure rate, customer satisfaction score, etc. Deliver an outstanding presentation on the topic using this Technological Assessment Of Firm Current Capabilities Cyber Security Risk Management. Dispense information and present a thorough explanation of Parameters, Industry Standard, Firms Standard, Service Delay Rate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
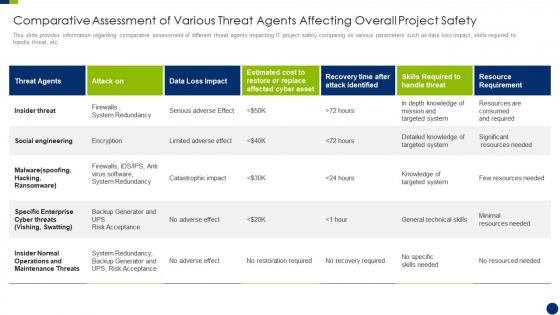 Enhancing overall project security it comparative assessment of various threat agents affecting
Enhancing overall project security it comparative assessment of various threat agents affectingThis slide provides information regarding comparative assessment of different threat agents impacting IT project safety comparing on various parameters such as data loss impact, skills required to handle threat, etc. Present the topic in a bit more detail with this Enhancing Overall Project Security It Comparative Assessment Of Various Threat Agents Affecting. Use it as a tool for discussion and navigation on Assessment, Operations, Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
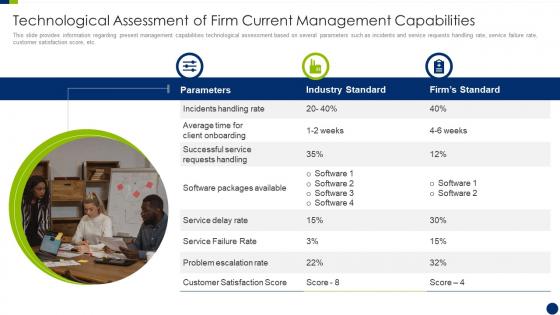 Enhancing overall project security it technological assessment of firm current
Enhancing overall project security it technological assessment of firm currentThis slide provides information regarding present management capabilities technological assessment based on several parameters such as incidents and service requests handling rate, service failure rate, customer satisfaction score, etc. Present the topic in a bit more detail with this Enhancing Overall Project Security It Technological Assessment Of Firm Current. Use it as a tool for discussion and navigation on Technological, Assessment, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
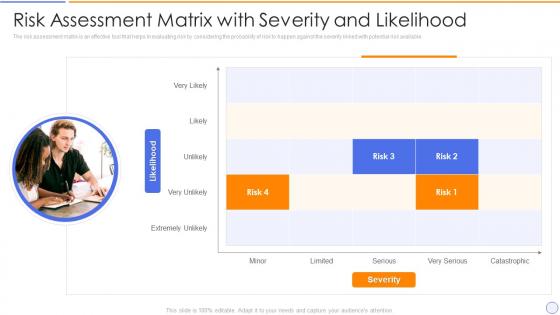 Building organizational security strategy plan risk assessment matrix with severity and likelihood
Building organizational security strategy plan risk assessment matrix with severity and likelihoodThe risk assessment matrix is an effective tool that helps in evaluating risk by considering the probability of risk to happen against the severity linked with potential risk available. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Risk Assessment Matrix With Severity And Likelihood. Use it as a tool for discussion and navigation on Assessment, Evaluating, Potential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
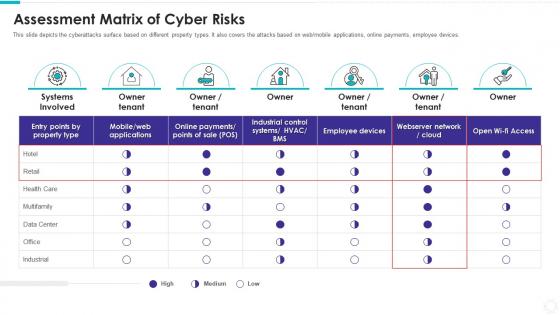 Electronic information security assessment matrix of cyber risks
Electronic information security assessment matrix of cyber risksThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Present the topic in a bit more detail with this Electronic Information Security Assessment Matrix Of Cyber Risks. Use it as a tool for discussion and navigation on Systems Involved, Owner Tenant, Data Center, Industrial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
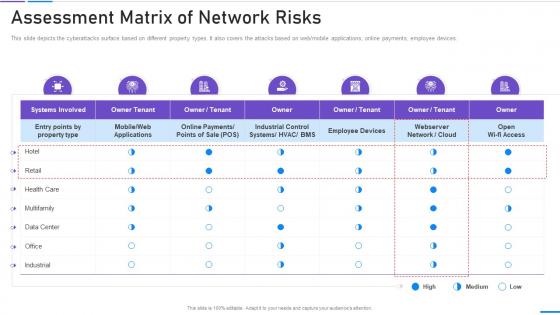 Network Security Assessment Matrix Of Network Risks
Network Security Assessment Matrix Of Network RisksThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web mobile applications, online payments, employee devices. Present the topic in a bit more detail with this Network Security Assessment Matrix Of Network Risks. Use it as a tool for discussion and navigation on Assessment Matrix Of Network Risks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
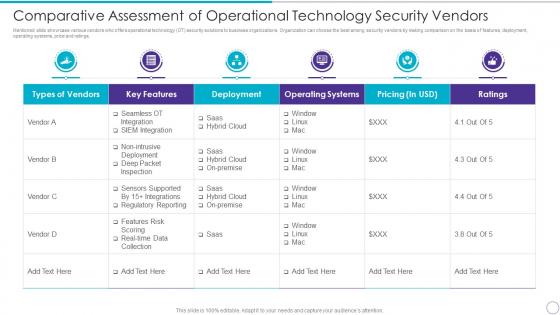 Comparative Assessment Of Operational Technology Security Vendors
Comparative Assessment Of Operational Technology Security VendorsMentioned slide showcase various vendors who offers operational technology OT security solutions to business organizations. Organization can choose the best among security vendors by making comparison on the basis of features, deployment, operating systems, price and ratings. Present the topic in a bit more detail with this Comparative Assessment Of Operational Technology Security Vendors. Use it as a tool for discussion and navigation on Types Vendors, Key Features, Deployment, Operating Systems, Pricing In USD, Ratings. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
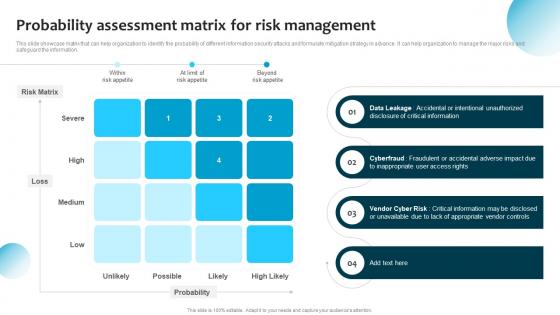 Probability Assessment Matrix For Risk Management Information System Security And Risk Administration Plan
Probability Assessment Matrix For Risk Management Information System Security And Risk Administration PlanThis slide showcase matrix that can help organization to identify the probability of different information security attacks and formulate mitigation strategy in advance. It can help organization to manage the major risks and safeguard the information. Deliver an outstanding presentation on the topic using this Probability Assessment Matrix For Risk Management Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Risk Matrix, Data Leakage, Vendor Cyber Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Process For Information Security Risk Assessment Information System Security And Risk Administration Plan
Process For Information Security Risk Assessment Information System Security And Risk Administration PlanThis slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. Increase audience engagement and knowledge by dispensing information using Process For Information Security Risk Assessment Information System Security And Risk Administration Plan. This template helps you present information on four stages. You can also present information on Security Threats, Information Assets, Risk Associated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan
Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Vulnerability Severity, Threat Source, Risk Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
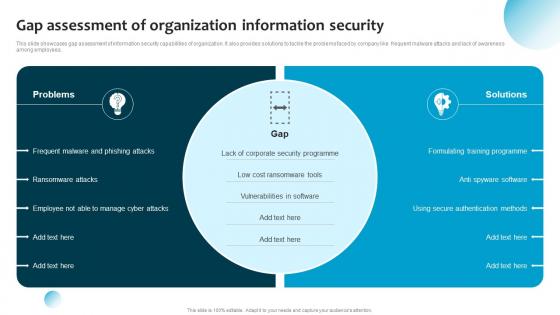 Information System Security And Risk Administration Plan Gap Assessment Of Organization Information Security
Information System Security And Risk Administration Plan Gap Assessment Of Organization Information SecurityThis slide showcases gap assessment of information security capabilities of organization. It also provides solutions to tackle the problems faced by company like frequent malware attacks and lack of awareness among employees. Present the topic in a bit more detail with this Information System Security And Risk Administration Plan Gap Assessment Of Organization Information Security. Use it as a tool for discussion and navigation on Corporate Security Programme, Low Cost Ransomware Tools, Vulnerabilities In Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
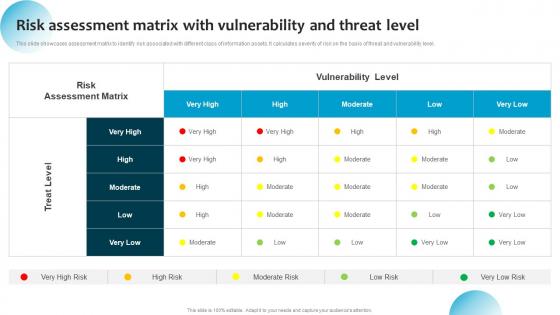 Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat Level
Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat LevelThis slide showcases assessment matrix to identify risk associated with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level. Present the topic in a bit more detail with this Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat Level. Use it as a tool for discussion and navigation on Treat Level, Vulnerability Level, Risk Assessment Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Erp Assessment Checklist To Improve It Security
Erp Assessment Checklist To Improve It SecurityThis slide signifies the enterprise resource planning evaluation to increase IT security. It covers information about automated testing tool, check system functionality and quality assurance etc. Presenting our well structured Erp Assessment Checklist To Improve It Security. The topics discussed in this slide are Business, Framework, Systems. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
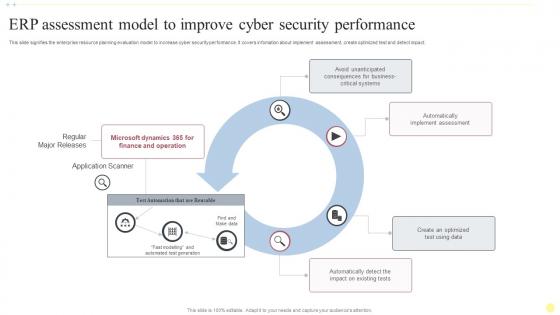 Erp Assessment Model To Improve Cyber Security Performance
Erp Assessment Model To Improve Cyber Security PerformanceThis slide signifies the enterprise resource planning evaluation model to increase cyber security performance. It covers infomation about implement assessment, create optimized test and detect impact. Presenting our well structured Erp Assessment Model To Improve Cyber Security Performance. The topics discussed in this slide are Data, Assessment, Application Scanner. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Importance Risk Assessment Cyber Security In Powerpoint And Google Slides Cpb
Importance Risk Assessment Cyber Security In Powerpoint And Google Slides CpbPresenting our Importance Risk Assessment Cyber Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases two stages. It is useful to share insightful information on Importance Risk Assessment Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 It Security Assessment Report Icon
It Security Assessment Report IconPresenting our set of slides with It Security Assessment Report Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security, Assessment.
-
 It Security Risk Assessment Framework
It Security Risk Assessment FrameworkThe following slide highlights the structure to identify best practices to fix risk tolerances. It constitutes of activities such as identify, protect, detect, respond and recover. Presenting our set of slides with It Security Risk Assessment Framework. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Protect, Detect .
-
 It Security Risk Assessment Grid
It Security Risk Assessment GridThe following slide depicts the analysis of IT security to prevent loss of confidentiality and integrity. The matrix constitutes of elements such as risk, likelihood, its impact and overall threat level. Introducing our premium set of slides with It Security Risk Assessment Grid. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Likelihood, Risk, Impact. So download instantly and tailor it with your information.
-
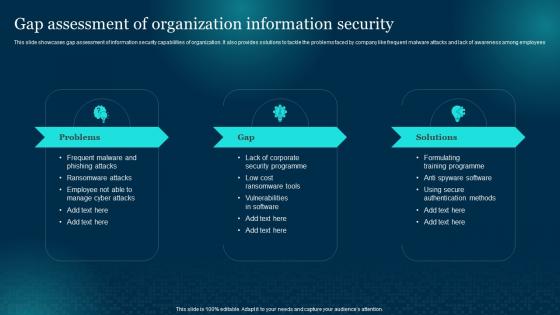 Gap Assessment Of Organization Information Security Cybersecurity Risk Analysis And Management Plan
Gap Assessment Of Organization Information Security Cybersecurity Risk Analysis And Management PlanThis slide showcases gap assessment of information security capabilities of organization. It also provides solutions to tackle the problems faced by company like frequent malware attacks and lack of awareness among employees Present the topic in a bit more detail with this Gap Assessment Of Organization Information Security Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Assessment, Organization, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
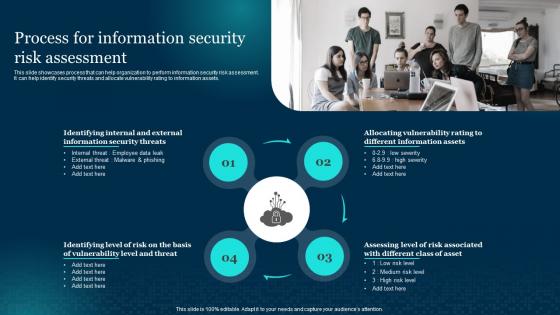 Process For Information Security Risk Assessment Cybersecurity Risk Analysis And Management Plan
Process For Information Security Risk Assessment Cybersecurity Risk Analysis And Management PlanThis slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. Introducing Process For Information Security Risk Assessment Cybersecurity Risk Analysis And Management Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Process, Assessment, Information, using this template. Grab it now to reap its full benefits.
-
 Healthcare Security Measures And Assessment Analysis
Healthcare Security Measures And Assessment AnalysisThis slide covers the details related to the measures for healthcare security and its assessment analysis. The purpose of this template is to define privacy and security of healthcare organization. It includes information related to physical, administrative and technical safeguards. Presenting our well structured Healthcare Security Measures And Assessment Analysis. The topics discussed in this slide are Security Areas, Details, Potential Security Measures. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cloud Security Maturity Model Assessment To Improve Business Operations
Cloud Security Maturity Model Assessment To Improve Business OperationsThis slide represents cloud security maturity assessment model which helps improve cloud optimization and flexibility. It provides information regarding automation, manual scripts, managed stage and optimization. Introducing our premium set of slides with Cloud Security Maturity Model Assessment To Improve Business Operations. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Automation Optimized, Minimal Automation, Minimal Automation. So download instantly and tailor it with your information.
-
 Cyber Security Environment Vulnerability Assessment In Powerpoint And Google Slides Cpb
Cyber Security Environment Vulnerability Assessment In Powerpoint And Google Slides CpbPresenting our Cyber Security Environment Vulnerability Assessment In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases eight stages. It is useful to share insightful information on Cyber Security Environment Vulnerability Assessment. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
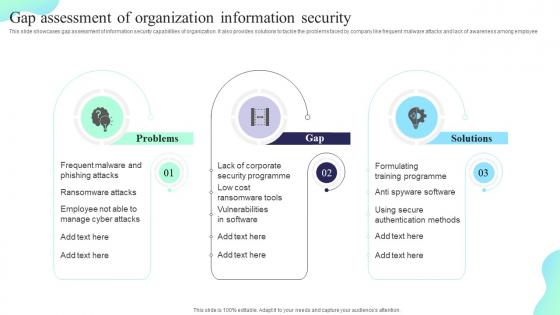 Gap Assessment Of Organization Information Security Formulating Cybersecurity Plan
Gap Assessment Of Organization Information Security Formulating Cybersecurity PlanThis slide showcases gap assessment of information security capabilities of organization. It also provides solutions to tackle the problems faced by company like frequent malware attacks and lack of awareness among employee. Increase audience engagement and knowledge by dispensing information using Gap Assessment Of Organization Information Security Formulating Cybersecurity Plan. This template helps you present information on three stages. You can also present information on Security Programme, Vulnerabilities In Software, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
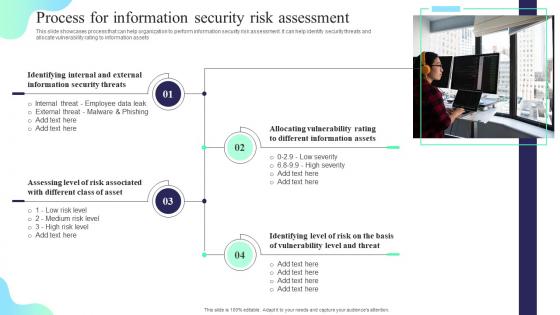 Process For Information Security Risk Assessment Formulating Cybersecurity Plan
Process For Information Security Risk Assessment Formulating Cybersecurity PlanThis slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. Introducing Process For Information Security Risk Assessment Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Identifying Internal, Information Security Threats, Information Assets, using this template. Grab it now to reap its full benefits.
-
 Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness Training
Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness TrainingThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Implementing Security Awareness Training. This template helps you present information on four stages. You can also present information on Describes Spam, Cyberbullying, Protect The Confidential Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Comparative Assessment Of Security Awareness Implementing Security Awareness Training
Comparative Assessment Of Security Awareness Implementing Security Awareness TrainingThe purpose of this slide is to showcase comparison of various advance cyber security training courses. The comparison is drawn on the basis of course description, level, duration, no. of companies enrolled for this course etc. Present the topic in a bit more detail with this Comparative Assessment Of Security Awareness Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Comparative Assessment, Security Awareness, Online Courses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Security Governance Tool Assessment Matrix
Data Security Governance Tool Assessment MatrixThis slide highlights a tools comparison matrix for data security governance and management. It includes key components such as threat intelligence, advanced data governance, source score, data helpdesk, price and customer satisfaction. Introducing our premium set of slides with Data Security Governance Tool Assessment Matrix. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Threat Intelligence, Advanced Data Governance. So download instantly and tailor it with your information.
-
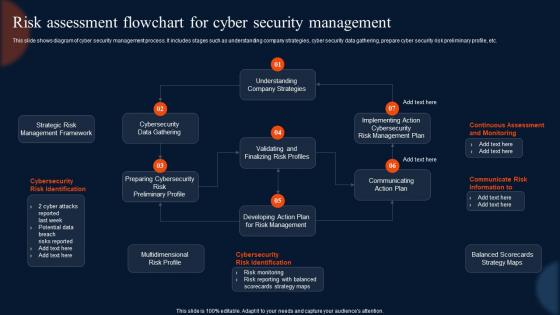 Risk Assessment Flowchart For Cyber Security Management
Risk Assessment Flowchart For Cyber Security ManagementThis slide shows diagram of cyber security management process. It includes stages such as understanding company strategies, cyber security data gathering, prepare cyber security risk preliminary profile, etc. Introducing our Risk Assessment Flowchart For Cyber Security Management set of slides. The topics discussed in these slides are Assessment, Flowchart, Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
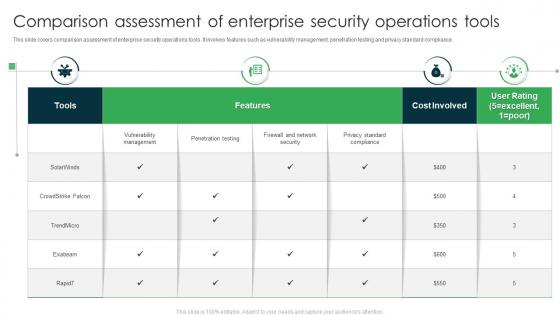 Comparison Assessment Of Enterprise Security Operations Tools
Comparison Assessment Of Enterprise Security Operations ToolsThis slide covers comparison assessment of enterprise security operations tools. It involves features such as vulnerability management, penetration testing and privacy standard compliance. Introducing our Comparison Assessment Of Enterprise Security Operations Tools set of slides. The topics discussed in these slides are Features, Cost Involved, User Rating. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 IT Security Assessment Method Framework
IT Security Assessment Method FrameworkThe following slide represents the security assessment of technological assets to assist IT team in improving the data structure. It includes key elements such as risk identification, security threat, vulnerabilities, impact analysis, risk level, controllable actions etc. Presenting our set of slides with IT Security Assessment Method Framework. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Identification, Security Threat, Impact Analysis.
-
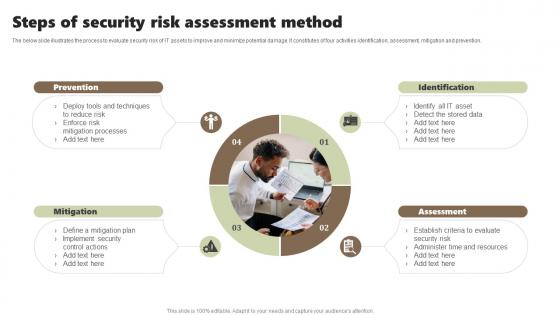 Steps Of Security Risk Assessment Method
Steps Of Security Risk Assessment MethodThe below slide illustrates the process to evaluate security risk of IT assets to improve and minimize potential damage. It constitutes of four activities identification, assessment, mitigation and prevention. Introducing our premium set of slides with Steps Of Security Risk Assessment Method. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Prevention, Identification, Assessment, Mitigation. So download instantly and tailor it with your information.
-
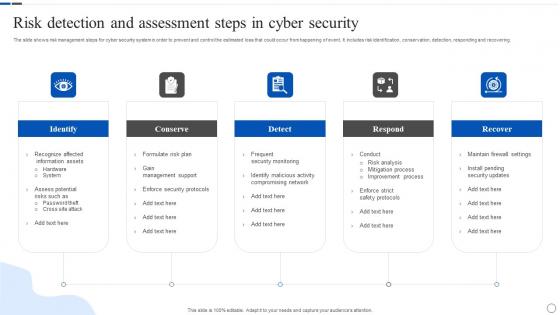 Risk Detection And Assessment Steps In Cyber Security
Risk Detection And Assessment Steps In Cyber SecurityThe slide shows risk management steps for cyber security system in order to prevent and control the estimated loss that could occur from happening of event. It includes risk identification, conservation, detection, responding and recovering. Presenting our set of slides with Risk Detection And Assessment Steps In Cyber Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Conserve, Respond, Recover.
-
 Risk Assessment Cyber Security In Powerpoint And Google Slides Cpb
Risk Assessment Cyber Security In Powerpoint And Google Slides CpbPresenting Risk Assessment Cyber Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Risk Assessment Cyber Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
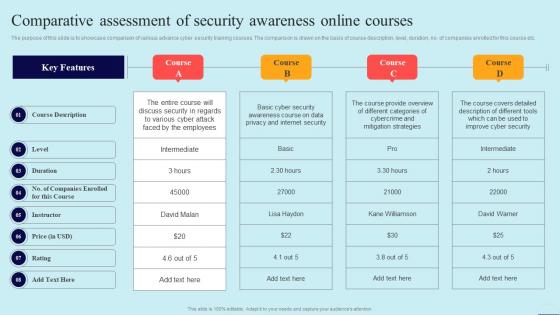 Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security
Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase comparison of various advance cyber security training courses. The comparison is drawn on the basis of course description, level, duration, no. of companies enrolled for this course etc. Present the topic in a bit more detail with this Comparative Assessment Of Security Awareness Online Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Course Description, Instructor, Rating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
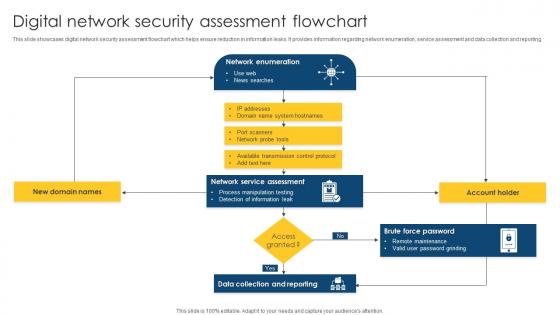 Digital Network Security Assessment Flowchart
Digital Network Security Assessment FlowchartThis slide showcases digital network security assessment flowchart which helps ensure reduction in information leaks. It provides information regarding network enumeration, service assessment and data collection and reporting. Presenting our well structured Digital Network Security Assessment Flowchart. The topics discussed in this slide are Assessment, Flowchart, Assessment. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
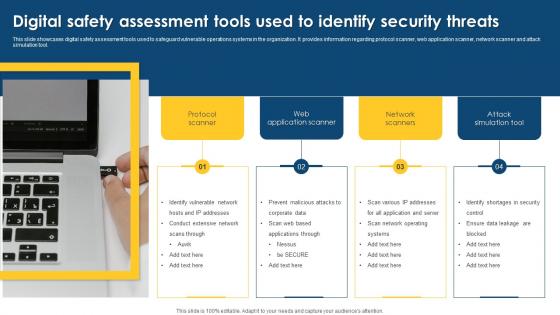 Digital Safety Assessment Tools Used To Identify Security Threats
Digital Safety Assessment Tools Used To Identify Security ThreatsThis slide showcases digital safety assessment tools used to safeguard vulnerable operations systems in the organization. It provides information regarding protocol scanner, web application scanner, network scanner and attack simulation tool. Presenting our well structured Digital Safety Assessment Tools Used To Identify Security Threats. The topics discussed in this slide are Assessment, Application, Identify Vulnerable. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
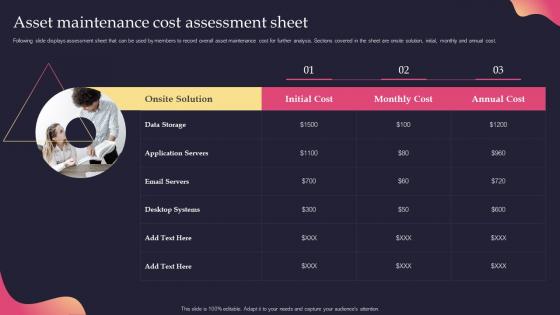 Asset Maintenance Cost Assessment Sheet Security Incident Response Playbook
Asset Maintenance Cost Assessment Sheet Security Incident Response PlaybookFollowing slide displays assessment sheet that can be used by members to record overall asset maintenance cost for further analysis. Sections covered in the sheet are onsite solution, initial, monthly and annual cost. Present the topic in a bit more detail with this Asset Maintenance Cost Assessment Sheet Security Incident Response Playbook. Use it as a tool for discussion and navigation on Assessment, Maintenance, Analysis. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Best Practices For Assessing Cyber Security Risk Scenario
Best Practices For Assessing Cyber Security Risk ScenarioThis slide depicts the best practices for assessing cybersecurity risk scenario which includes defining threat scenario, assessing inherent risk, evaluating impact of controls, assessing residual risks, actionable steps to improve, feedback loop, etc. Introducing our premium set of slides with Best Practices For Assessing Cyber Security Risk Scenario. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Feedback Loop, Define Threat Scenario, Assess Inherent Risk. So download instantly and tailor it with your information.
-
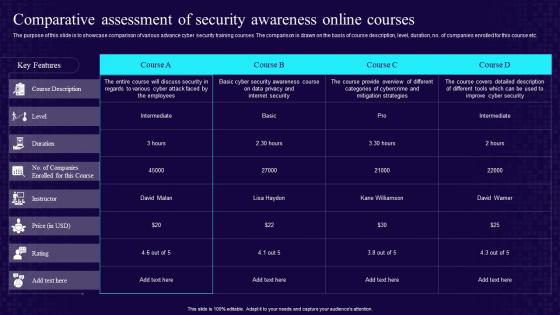 Comparative Assessment Of Security Awareness Online Courses Developing Cyber Security Awareness
Comparative Assessment Of Security Awareness Online Courses Developing Cyber Security AwarenessThe purpose of this slide is to showcase comparison of various advance cyber security training courses. The comparison is drawn on the basis of course description, level, duration, no. of companies enrolled for this course etc. Present the topic in a bit more detail with this Comparative Assessment Of Security Awareness Online Courses Developing Cyber Security Awareness. Use it as a tool for discussion and navigation on Comparative, Assessment Of Security, Awareness Online Courses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparative Assessment Of Security Incident Management Tools
Comparative Assessment Of Security Incident Management ToolsPresenting our well structured Comparative Assessment Of Security Incident Management Tools. The topics discussed in this slide are Customized Workflows, User Friendly Interface, Threat Intelligence Integration. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
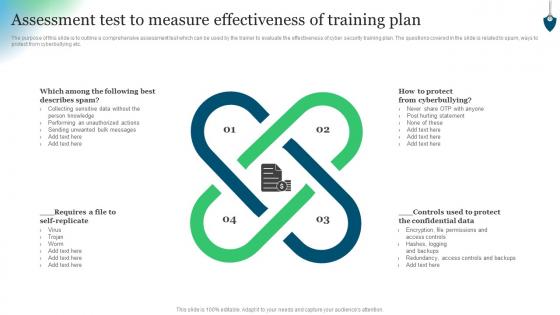 Assessment Test To Measure Effectiveness Of Training Plan Conducting Security Awareness
Assessment Test To Measure Effectiveness Of Training Plan Conducting Security AwarenessThe purpose of this slide is to outline a comprehensive assessment test which can be used by the trainer to evaluate the effectiveness of cyber security training plan. The questions covered in the slide is related to spam, ways to protect from cyberbullying etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Training Plan Conducting Security Awareness. This template helps you present information on four stages. You can also present information on Protect Confidential Data, Logging And Backups, Controls And Backups using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
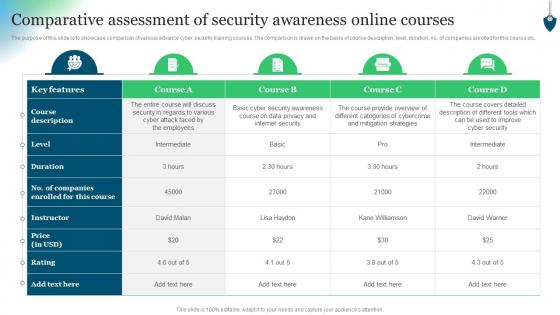 Comparative Assessment Of Security Awareness Online Courses Conducting Security Awareness
Comparative Assessment Of Security Awareness Online Courses Conducting Security AwarenessThe purpose of this slide is to showcase comparison of various advance cyber security training courses. The comparison is drawn on the basis of course description, level, duration, no. of companies enrolled for this course etc. Present the topic in a bit more detail with this Comparative Assessment Of Security Awareness Online Courses Conducting Security Awareness. Use it as a tool for discussion and navigation on Key Features, Course Description, Instructor. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
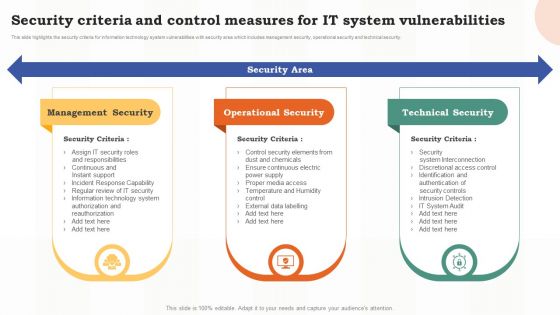 Risk Assessment Of It Systems Security Criteria And Control Measures For It System Vulnerabilities
Risk Assessment Of It Systems Security Criteria And Control Measures For It System VulnerabilitiesThis slide highlights the security criteria for information technology system vulnerabilities with security area which includes management security, operational security and technical security. Deliver an outstanding presentation on the topic using this Risk Assessment Of It Systems Security Criteria And Control Measures For It System Vulnerabilities. Dispense information and present a thorough explanation of Management Security, Operational Security, Technical Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
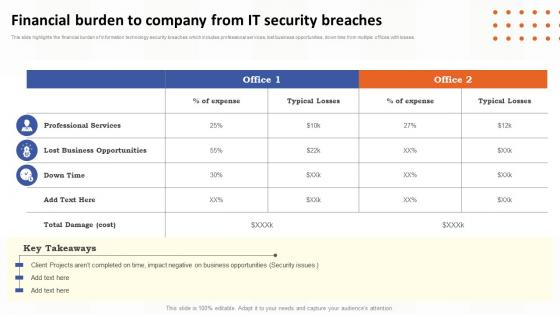 Financial Burden To Company From It Security Breaches Risk Assessment Of It Systems
Financial Burden To Company From It Security Breaches Risk Assessment Of It SystemsThis slide highlights the financial burden of information technology security breaches which includes professional services, lost business opportunities, down time from multiple offices with losses. Deliver an outstanding presentation on the topic using this Financial Burden To Company From It Security Breaches Risk Assessment Of It Systems. Dispense information and present a thorough explanation of Professional Services, Lost Business Opportunities, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
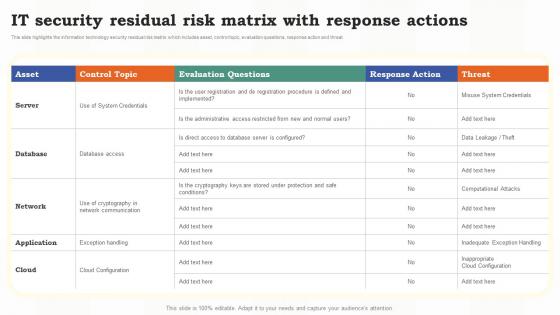 It Security Residual Risk Matrix With Response Actions Risk Assessment Of It Systems
It Security Residual Risk Matrix With Response Actions Risk Assessment Of It SystemsThis slide highlights the information technology security residual risk matrix which includes asset, control topic, evaluation questions, response action and threat. Deliver an outstanding presentation on the topic using this It Security Residual Risk Matrix With Response Actions Risk Assessment Of It Systems. Dispense information and present a thorough explanation of Information, Technology, Evaluation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems
Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Mitigation Plan Risk Assessment Of It Systems. Use it as a tool for discussion and navigation on Mitigation Plan, Prioritized, Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
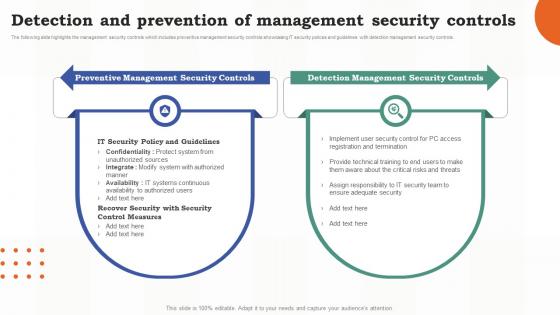 Risk Assessment Of It Systems Detection And Prevention Of Management Security Controls
Risk Assessment Of It Systems Detection And Prevention Of Management Security ControlsThe following slide highlights the management security controls which includes preventive management security controls showcasing IT security polices and guidelines with detection management security controls. Present the topic in a bit more detail with this Risk Assessment Of It Systems Detection And Prevention Of Management Security Controls. Use it as a tool for discussion and navigation on Prevention, Management, Security Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
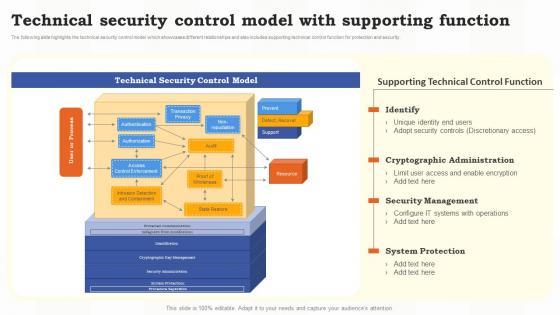 Technical Security Control Model With Supporting Function Risk Assessment Of It Systems
Technical Security Control Model With Supporting Function Risk Assessment Of It SystemsThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Deliver an outstanding presentation on the topic using this Technical Security Control Model With Supporting Function Risk Assessment Of It Systems. Dispense information and present a thorough explanation of Technical, Security Management, System Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparative Assessment Of Cyber Security Incident Response Tools
Comparative Assessment Of Cyber Security Incident Response ToolsThis slide covers comparative assessment of cyber security incident response tools. It involves features such as advanced threat hunting ability, net flow analysis, user behavior analytics and superior forensic analysis. Introducing our premium set of slides with name Comparative Assessment Of Cyber Security Incident Response Tools. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Comparative Assessment, Cyber Security, Incident Response Tools. So download instantly and tailor it with your information.
-
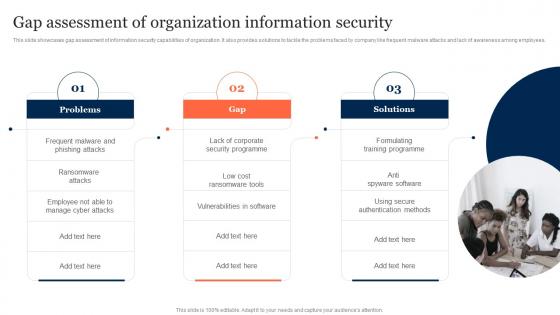 Gap Assessment Of Organization Information Security Information Security Risk Management
Gap Assessment Of Organization Information Security Information Security Risk ManagementThis slide showcases gap assessment of information security capabilities of organization. It also provides solutions to tackle the problems faced by company like frequent malware attacks and lack of awareness among employees. Increase audience engagement and knowledge by dispensing information using Gap Assessment Of Organization Information Security Information Security Risk Management. This template helps you present information on three stages. You can also present information on Gap Assessment, Organization Information Security, Ransomware Attacks using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Probability Assessment Matrix For Risk Management Information Security Risk Management
Probability Assessment Matrix For Risk Management Information Security Risk ManagementThis slide showcase matrix that can help organization to identify the probability of different information security attacks and formulate mitigation strategy in advance. It can help organization to manage the major risks and safeguard the information. Deliver an outstanding presentation on the topic using this Probability Assessment Matrix For Risk Management Information Security Risk Management. Dispense information and present a thorough explanation of Probability Assessment Matrix, Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
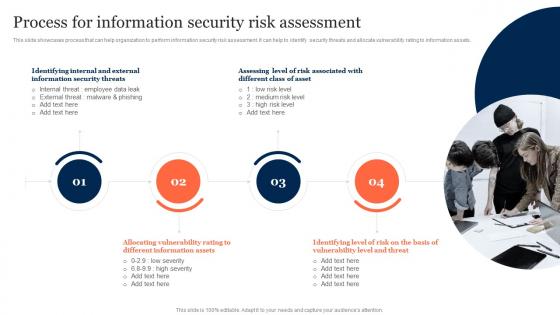 Process For Information Security Risk Assessment Information Security Risk Management
Process For Information Security Risk Assessment Information Security Risk ManagementThis slide showcases process that can help organization to perform information security risk assessment. It can help to identify security threats and allocate vulnerability rating to information assets. Introducing Process For Information Security Risk Assessment Information Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Information Security Threats, Allocating Vulnerability, Risk Assessment, using this template. Grab it now to reap its full benefits.
-
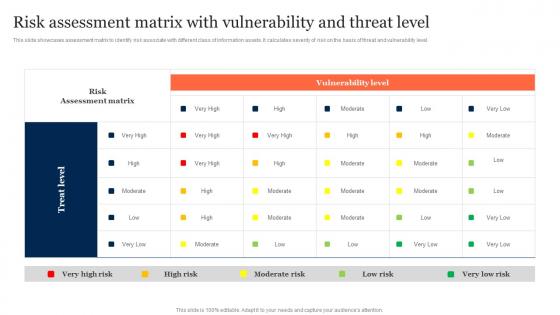 Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk Management
Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk ManagementThis slide showcases assessment matrix to identify risk associate with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level. Deliver an outstanding presentation on the topic using this Risk Assessment Matrix With Vulnerability And Threat Level Information Security Risk Management. Dispense information and present a thorough explanation of Risk Assessment Matrix, Vulnerability Level, Threat Level using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
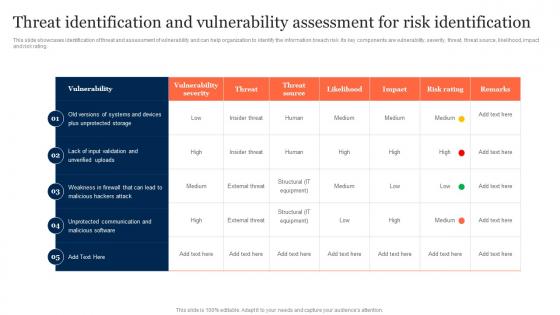 Threat Identification And Vulnerability Assessment Information Security Risk Management
Threat Identification And Vulnerability Assessment Information Security Risk ManagementThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Present the topic in a bit more detail with this Threat Identification And Vulnerability Assessment Information Security Risk Management. Use it as a tool for discussion and navigation on Threat Identification, Vulnerability Assessment, Risk Identification. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Cyber Security Risk Assessment And Management Matrix Ppt Powerpoint Presentation Layouts Skills
Cyber Security Risk Assessment And Management Matrix Ppt Powerpoint Presentation Layouts SkillsThis slide represents the assessment of vulnerability and consequences of the cyber security incidents on the operations of the company. It includes details related to threat, vulnerability, consequences, risk and solution. Present the topic in a bit more detail with this Cyber Security Risk Assessment And Management Matrix Ppt Powerpoint Presentation Layouts Skills. Use it as a tool for discussion and navigation on Cyber Security, Risk Assessment, Management Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.



