Powerpoint Templates and Google slides for Security Control Catalogue
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Key Security Controls To Be Addressed In The Program Risk Based Methodology To Cyber
Key Security Controls To Be Addressed In The Program Risk Based Methodology To CyberPurpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications.Present the topic in a bit more detail with this Key Security Controls To Be Addressed In The Program Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Prevents Attacks, Limits Extent Of Attacks, Data Recovery This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Security Controls To Be Addressed In The Program Introducing A Risk Based Approach
Key Security Controls To Be Addressed In The Program Introducing A Risk Based ApproachPurpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications.Deliver an outstanding presentation on the topic using this Key Security Controls To Be Addressed In The Program Introducing A Risk Based Approach Dispense information and present a thorough explanation of Restrict Admin Privileges, Factor Authentication, Limits Extent Of Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
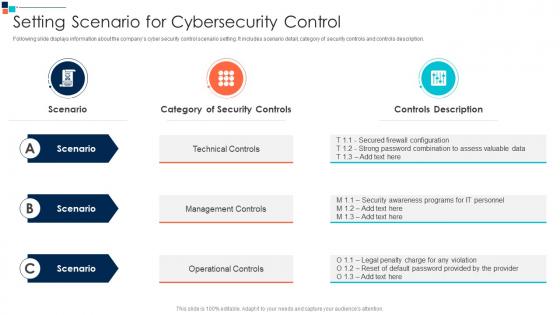 Setting Scenario For Cybersecurity Control Introducing A Risk Based Approach To Cyber Security
Setting Scenario For Cybersecurity Control Introducing A Risk Based Approach To Cyber SecurityFollowing slide displays information about the companys cyber security control scenario setting. It includes scenario detail, category of security controls and controls description.Present the topic in a bit more detail with this Setting Scenario For Cybersecurity Control Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Technical Controls, Management Controls, Operational Controls This template is free to edit as deemed fit for your organization. Therefore download it now.
-
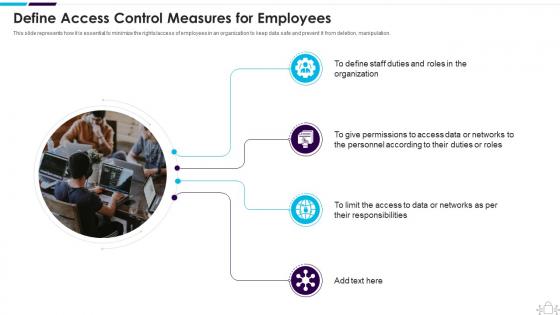 Information Technology Security Define Access Control Measures For Employees
Information Technology Security Define Access Control Measures For EmployeesThis slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. Increase audience engagement and knowledge by dispensing information using Information Technology Security Define Access Control Measures For Employees. This template helps you present information on four stages. You can also present information on Organization, Permissions, Responsibilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
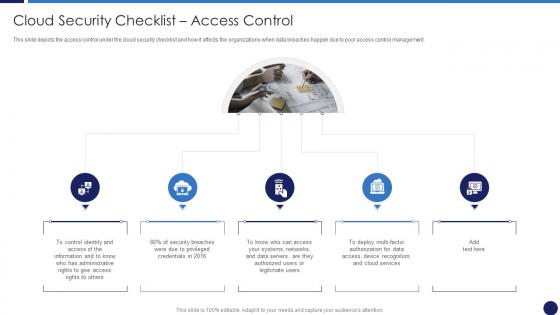 Cloud Security Checklist Access Control Cloud Data Protection
Cloud Security Checklist Access Control Cloud Data ProtectionThis slide depicts the access control under the cloud security checklist and how it affects the organizations when data breaches happen due to poor access control management. Introducing Cloud Security Checklist Access Control Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Cloud Services, Information, Data Servers, using this template. Grab it now to reap its full benefits.
-
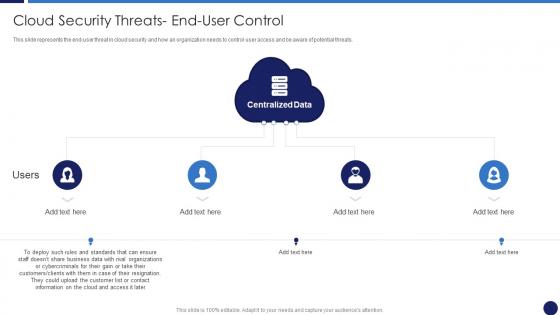 Cloud Security Threats End User Control Cloud Data Protection
Cloud Security Threats End User Control Cloud Data ProtectionThis slide represents the end-user threat in cloud security and how an organization needs to control user access and be aware of potential threats. Introducing Cloud Security Threats End User Control Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Business Data, Customers, Centralized Data, using this template. Grab it now to reap its full benefits.
-
 Measures And Controls In Cloud Security Cloud Data Protection
Measures And Controls In Cloud Security Cloud Data ProtectionThis slide depicts the measures and controls taken in cloud security systems, namely preventive controls, deterrent controls, detective controls, and corrective controls. Introducing Measures And Controls In Cloud Security Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Corrective Control, Detective Control, Preventive Control, using this template. Grab it now to reap its full benefits.
-
 Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids Cpb
Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids CpbPresenting our Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Access Control Methods Information Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
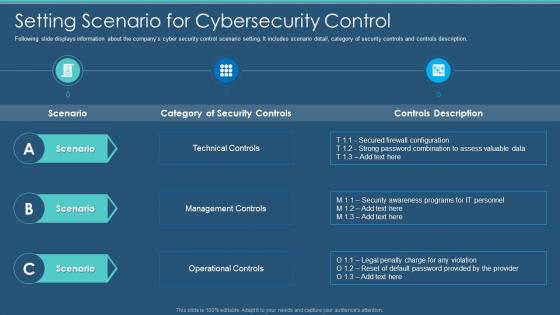 Information Security Program Cybersecurity Setting Scenario For Cybersecurity Control
Information Security Program Cybersecurity Setting Scenario For Cybersecurity ControlFollowing slide displays information about the companys cyber security control scenario setting. It includes scenario detail, category of security controls and controls description. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Setting Scenario For Cybersecurity Control. Dispense information and present a thorough explanation of Technical Controls, Management Controls, Operational Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Key Security Controls To Be Addressed In The Program
Information Security Program Key Security Controls To Be Addressed In The ProgramPurpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications. Deliver an outstanding presentation on the topic using this Information Security Program Key Security Controls To Be Addressed In The Program. Dispense information and present a thorough explanation of Prevents Attacks, Limits Extent Of Attacks, Data Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Management Framework For Information Security Setting Scenario For Security Control
Risk Management Framework For Information Security Setting Scenario For Security ControlFollowing slide displays security control scenario setting. It includes scenario detail, category of security controls and controls description. Present the topic in a bit more detail with this Risk Management Framework For Information Security Setting Scenario For Security Control. Use it as a tool for discussion and navigation on Category Security Controls, Controls Description, Operational Controls, Management Controls, Technical Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Types Security Controls Ppt Powerpoint Presentation Model Samples Cpb
Types Security Controls Ppt Powerpoint Presentation Model Samples CpbPresenting our Types Security Controls Ppt Powerpoint Presentation Model Samples Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Types Security Controls. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
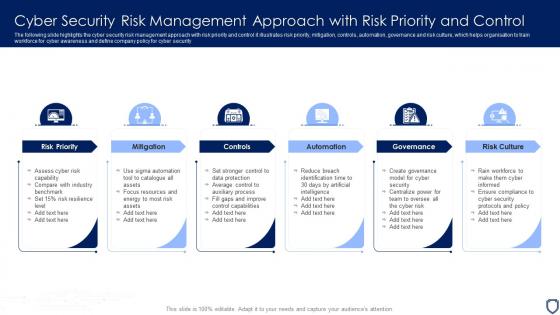 Cyber Security Risk Management Approach With Risk Priority And Control
Cyber Security Risk Management Approach With Risk Priority And ControlThe following slide highlights the cyber security risk management approach with risk priority and control it illustrates risk priority, mitigation, controls, automation, governance and risk culture, which helps organisation to train workforce for cyber awareness and define company policy for cyber security. Presenting our set of slides with name Cyber Security Risk Management Approach With Risk Priority And Control. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Governance, Risk Priority, Mitigation.
-
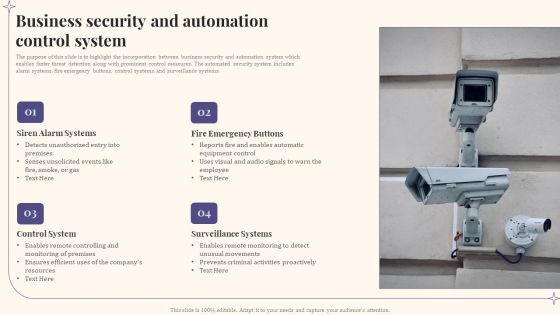 Business Security And Automation Control System
Business Security And Automation Control SystemThe purpose of this slide is to highlight the incorporation between business security and automation system which enables faster threat detection along with prominent control measures. The automated security system includes alarm systems, fire emergency buttons, control systems, and surveillance systems. Introducing our Business Security And Automation Control System set of slides. The topics discussed in these slides are Siren Alarm Systems, Fire Emergency Buttons, Control System. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
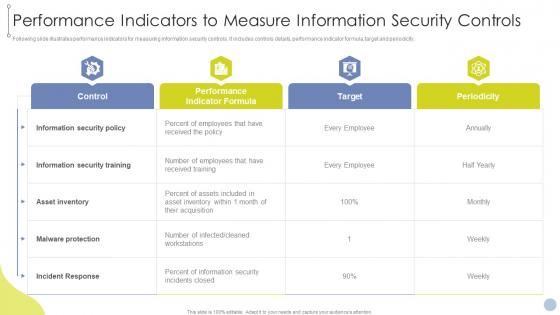 Obtaining ISO 27001 Certificate Performance Indicators To Measure Information Security Controls
Obtaining ISO 27001 Certificate Performance Indicators To Measure Information Security ControlsFollowing slide illustrates performance indicators for measuring information security controls. It includes controls details, performance indicator formula, target and periodicity. Deliver an outstanding presentation on the topic using this Obtaining ISO 27001 Certificate Performance Indicators To Measure Information Security Controls. Dispense information and present a thorough explanation of Control, Performance Indicator Formula, Target, Periodicity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Risk Review And Control Matrix
Cyber Security Risk Review And Control MatrixThe purpose of this slide is to define the level of hazards and their severity in cybersecurity management along with priority levels 1-5 to manage risks. This is categorized as certain, likely, possible, unlikely, and rare. Introducing our Cyber Security Risk Review And Control Matrix set of slides. The topics discussed in these slides are Risk Matrix, Minor, Priority Levels. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
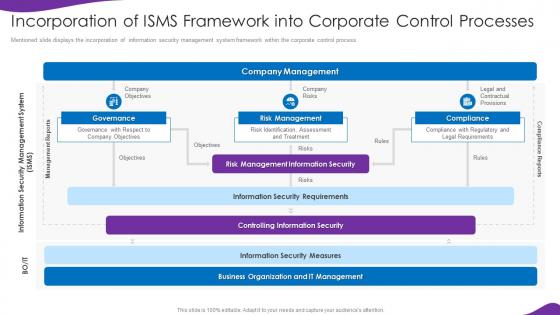 Information Security And Iso 27001 Incorporation Isms Framework Into Corporate Control Processes
Information Security And Iso 27001 Incorporation Isms Framework Into Corporate Control ProcessesMentioned slide displays the incorporation of information security management system framework within the corporate control process. Deliver an outstanding presentation on the topic using this Information Security And Iso 27001 Incorporation Isms Framework Into Corporate Control Processes. Dispense information and present a thorough explanation of Framework, Corporate, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
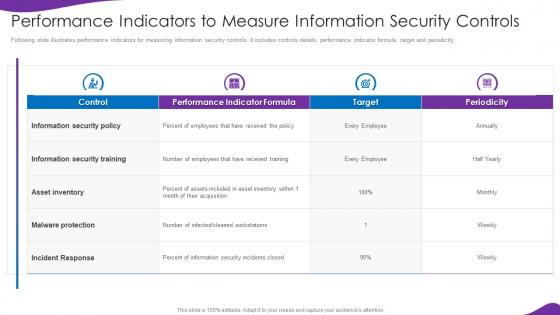 Information Security And Iso 27001 Performance Indicators To Measure Information Security Controls
Information Security And Iso 27001 Performance Indicators To Measure Information Security ControlsFollowing slide illustrates performance indicators for measuring information security controls. It includes controls details, performance indicator formula, target and periodicity. Present the topic in a bit more detail with this Information Security And Iso 27001 Performance Indicators To Measure Information Security Controls. Use it as a tool for discussion and navigation on Performance, Indicators, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Computing Security Measures And Controls In Cloud Security
Cloud Computing Security Measures And Controls In Cloud SecurityThis slide depicts the measures and controls taken in cloud security systems, namely preventive controls, deterrent controls, detective controls, and corrective controls. Introducing Cloud Computing Security Measures And Controls In Cloud Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Preventive Control, Corrective Control, Detective Control, Deterrent Control, Cloud Security, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Checklist Access Control Cloud Computing Security
Cloud Security Checklist Access Control Cloud Computing SecurityThis slide depicts the access control under the cloud security checklist and how it affects the organizations when data breaches happen due to poor access control management. Introducing Cloud Security Checklist Access Control Cloud Computing Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Multi Factor Authorization, Cloud Services, Networks, using this template. Grab it now to reap its full benefits.
-
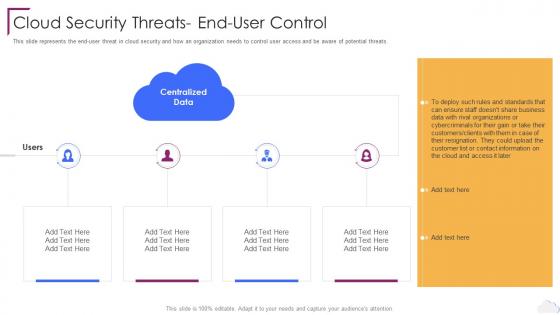 Cloud Security Threats End User Control Cloud Computing Security
Cloud Security Threats End User Control Cloud Computing SecurityThis slide represents the end user threat in cloud security and how an organization needs to control user access and be aware of potential threats. Introducing Cloud Security Threats End User Control Cloud Computing Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Data, Cloud Security Threats, End User Control, using this template. Grab it now to reap its full benefits.
-
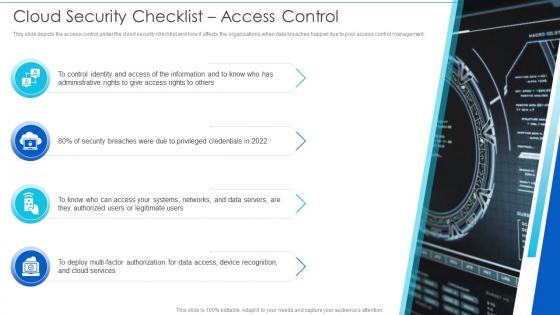 Cloud Security Checklist Access Control Cloud Information Security
Cloud Security Checklist Access Control Cloud Information SecurityThis slide depicts the access control under the cloud security checklist and how it affects the organizations when data breaches happen due to poor access control management.Introducing Cloud Security Checklist Access Control Cloud Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Service Provider, Physical Access, Natural Disasters using this template. Grab it now to reap its full benefits.
-
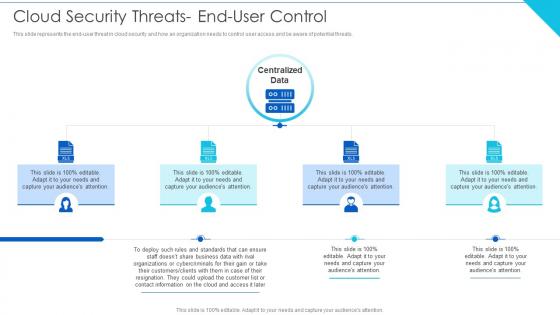 Cloud Security Threats End User Control Cloud Information Security
Cloud Security Threats End User Control Cloud Information SecurityThis slide represents the end user threat in cloud security and how an organization needs to control user access and be aware of potential threats.Introducing Cloud Security Threats End User Control Cloud Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Wisely Considering, Storage Location, Procedures Strategies using this template. Grab it now to reap its full benefits.
-
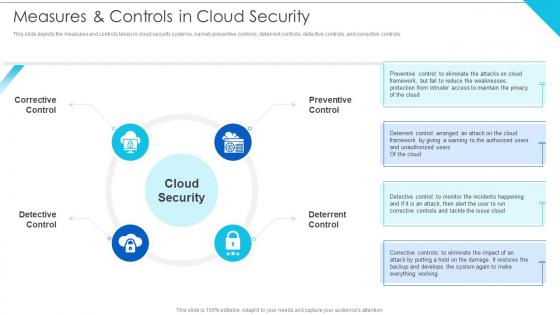 Measures And Controls In Cloud Security Cloud Information Security
Measures And Controls In Cloud Security Cloud Information SecurityThis slide depicts the measures and controls taken in cloud security systems, namely preventive controls, deterrent controls, detective controls, and corrective controls.Increase audience engagement and knowledge by dispensing information using Measures And Controls In Cloud Security Cloud Information Security This template helps you present information on four stages. You can also present information on Implement Information, Restrict Data, Implement Advanced using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
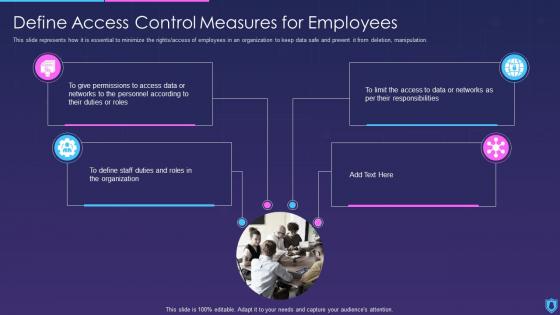 Information Security Define Access Control Measures For Employees
Information Security Define Access Control Measures For EmployeesThis slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. Introducing Information Security Define Access Control Measures For Employees to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Control, Measures, Employees, using this template. Grab it now to reap its full benefits.
-
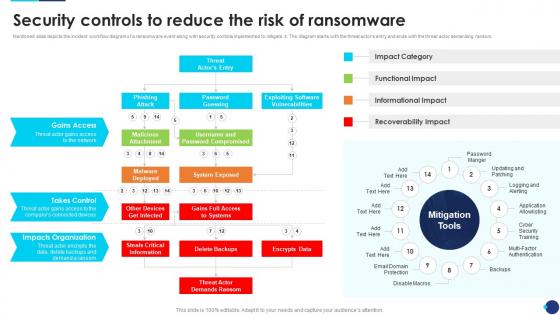 Incident Response Playbook Security Controls To Reduce The Risk Of Ransomware
Incident Response Playbook Security Controls To Reduce The Risk Of RansomwareMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Present the topic in a bit more detail with this Incident Response Playbook Security Controls To Reduce The Risk Of Ransomware. Use it as a tool for discussion and navigation on Impact Category, Functional Impact, Informational Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
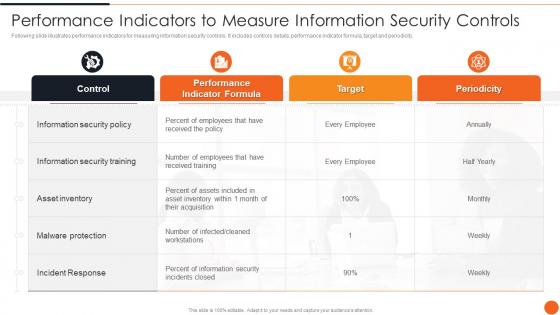 Performance Indicators To Measure Information Security Controls Iso 27001certification Process
Performance Indicators To Measure Information Security Controls Iso 27001certification ProcessFollowing slide illustrates performance indicators for measuring information security controls. It includes controls details, performance indicator formula, target and periodicity. Deliver an outstanding presentation on the topic using this Performance Indicators To Measure Information Security Controls Iso 27001certification Process. Dispense information and present a thorough explanation of Performance, Measure, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Controls Ppt Powerpoint Presentation Model Professional Cpb
Information Security Controls Ppt Powerpoint Presentation Model Professional CpbPresenting Information Security Controls Ppt Powerpoint Presentation Model Professional Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Information Security Controls. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Network Security Control Devices In Powerpoint And Google Slides Cpb
Network Security Control Devices In Powerpoint And Google Slides CpbPresenting our Network Security Control Devices In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Network Security Control Devices. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 How financial risk can be controlled managing critical threat vulnerabilities and security threats
How financial risk can be controlled managing critical threat vulnerabilities and security threatsThis slide provides details regarding various ways through financial risks can be controlled by handling liquidity risk, foreign exchange risk and credit exchange risk. Increase audience engagement and knowledge by dispensing information using How Financial Risk Can Be Controlled Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on three stages. You can also present information on Liquidity Risk, Exchange Risk, Credit Exchange Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
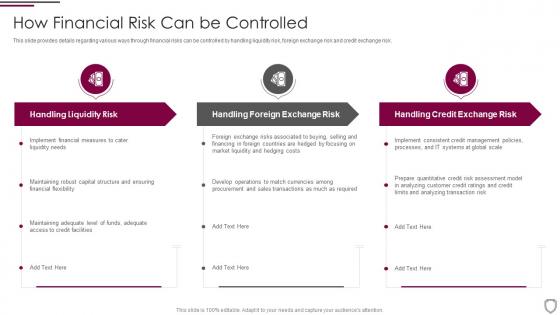 How financial risk can be controlled corporate security management
How financial risk can be controlled corporate security managementThis slide provides details regarding various ways through financial risks can be controlled by handling liquidity risk, foreign exchange risk and credit exchange risk. Increase audience engagement and knowledge by dispensing information using How Financial Risk Can Be Controlled Corporate Security Management. This template helps you present information on three stages. You can also present information on Handling Liquidity Risk, Foreign Exchange Risk, Credit Exchange Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint security controls checklist ppt powerpoint presentation infographic template cpb
Endpoint security controls checklist ppt powerpoint presentation infographic template cpbPresenting our Endpoint Security Controls Checklist Ppt Powerpoint Presentation Infographic Template Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Endpoint Security Controls Checklist This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Setting scenario security control effective information security risk management process
Setting scenario security control effective information security risk management processFollowing slide displays security control scenario setting. It includes scenario detail, category of security controls and controls description.Introducing Setting Scenario Security Control Effective Information Security Risk Management Process to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Controls, Operational Controls, Technical Controls, using this template. Grab it now to reap its full benefits.
-
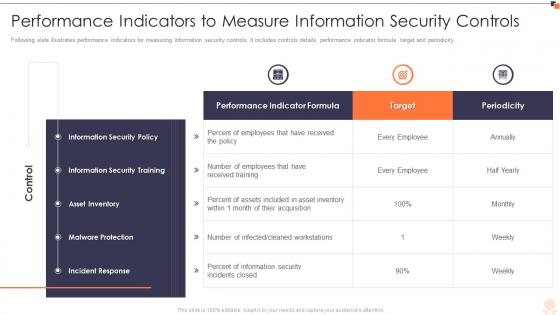 Iso 27001 performance indicators to measure information security controls ppt slides
Iso 27001 performance indicators to measure information security controls ppt slidesFollowing slide illustrates performance indicators for measuring information security controls. It includes controls details, performance indicator formula, target and periodicity. Deliver an outstanding presentation on the topic using this ISO 27001 Performance Indicators To Measure Information Security Controls Ppt Slides. Dispense information and present a thorough explanation of Information Security Policy, Information Security Training, Asset Inventory using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Wireless remote control for system security
Wireless remote control for system securityPresenting our set of slides with Wireless Remote Control For System Security. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Wireless Remote Control For System Security.
-
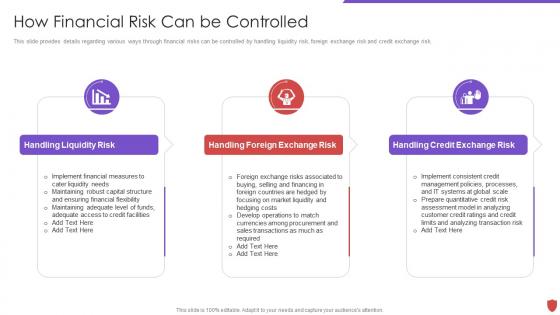 Cyber security risk management how financial risk can be controlled
Cyber security risk management how financial risk can be controlledThis slide provides details regarding various ways through financial risks can be controlled by handling liquidity risk, foreign exchange risk and credit exchange risk. Introducing Cyber Security Risk Management How Financial Risk Can Be Controlled to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Handling Liquidity Risk, Handling Foreign Exchange Risk, Handling Credit Exchange Risk, using this template. Grab it now to reap its full benefits.
-
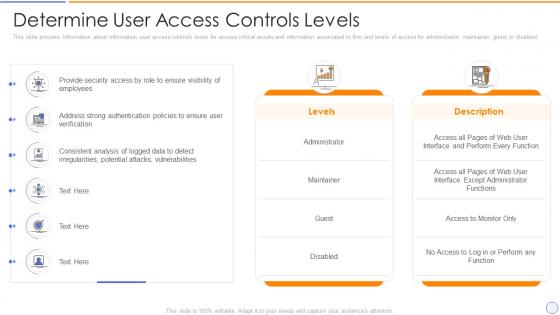 Building organizational security strategy plan determine user access controls levels
Building organizational security strategy plan determine user access controls levelsThis slide provides information about information user access controls levels for access critical assets and information associated to firm and levels of access for administrator, maintainer, guest or disabled. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Determine User Access Controls Levels. Use it as a tool for discussion and navigation on Information, Administrator, Associated. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity and digital business risk management key security controls to be addressed
Cybersecurity and digital business risk management key security controls to be addressedPurpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications. Increase audience engagement and knowledge by dispensing information using Cybersecurity And Digital Business Risk Management Key Security Controls To Be Addressed. This template helps you present information on three stages. You can also present information on Framework, Authentification, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Generation internet security controls ppt powerpoint presentation outline grid cpb
Generation internet security controls ppt powerpoint presentation outline grid cpbPresenting our Generation Internet Security Controls Ppt Powerpoint Presentation Outline Grid Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Generation Internet Security Controls. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Electronic information security define access control measures employees
Electronic information security define access control measures employeesThis slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. Introducing Electronic Information Security Define Access Control Measures Employees to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Organization, Data Or Networks, Personnel According, Responsibilities, using this template. Grab it now to reap its full benefits.
-
 Network Security Define Access Control Measures For Employees
Network Security Define Access Control Measures For EmployeesThis slide represents how it is essential to minimize the rights access of employees in an organization to keep data safe and prevent it from deletion, manipulation. Increase audience engagement and knowledge by dispensing information using Network Security Define Access Control Measures For Employees. This template helps you present information on four stages. You can also present information on Organization, Duties, Roles, Permissions, Personnel using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
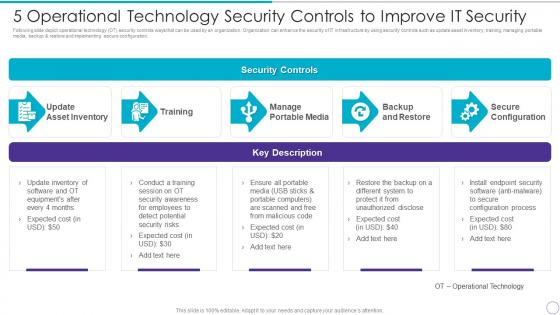 5 Operational Technology Security Controls To Improve It Security
5 Operational Technology Security Controls To Improve It SecurityFollowing slide depict operational technology OT security controls ways that can be used by an organization. Organization can enhance the security of IT infrastructure by using security controls such as update asset inventory, training, managing portable media, backup and restore and implementing secure configuration. Present the topic in a bit more detail with this 5 Operational Technology Security Controls To Improve IT Security. Use it as a tool for discussion and navigation on Update Asset Inventory, Training Manage, Portable Media, Backup And Restore, Secure Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
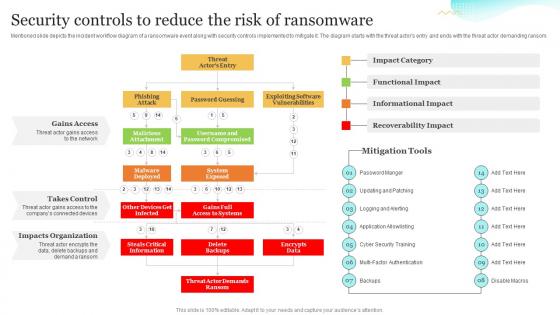 Security Controls To Reduce The Risk Of Ransomware Upgrading Cybersecurity With Incident Response Playbook
Security Controls To Reduce The Risk Of Ransomware Upgrading Cybersecurity With Incident Response PlaybookMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Present the topic in a bit more detail with this Security Controls To Reduce The Risk Of Ransomware Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Ransomware, Informational Impact, Recoverability Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Nist Framework Process For Security Control Selection
Nist Framework Process For Security Control SelectionMentioned Slide Showcases The Process To Choose Security Controls Based On Nist Security Control. It Include Steps Like Security Categorization Using Fips 199, Identify Baseline Security Controls, Tailoring Baseline Security Controls And Document The Control Selection Process. Presenting Our Well Structured Nist Framework Process For Security Control Selection. The Topics Discussed In This Slide Are Framework, Process, Categorization. This Is An Instantly Available Powerpoint Presentation That Can Be Edited Conveniently. Download It Right Away And Captivate Your Audience.
-
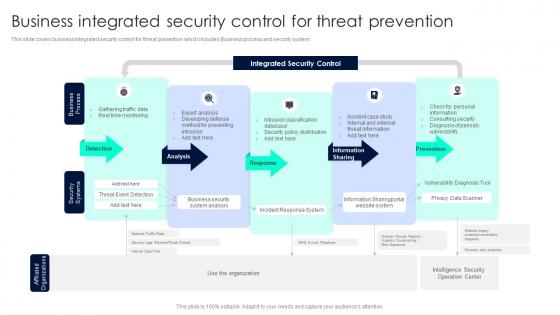 Business Integrated Security Control For Threat Prevention
Business Integrated Security Control For Threat PreventionThis slide covers business integrated security control for threat prevention which includes Business process and security system. Introducing our Business Integrated Security Control For Threat Prevention set of slides. The topics discussed in these slides are Integrated Security, Detection, Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
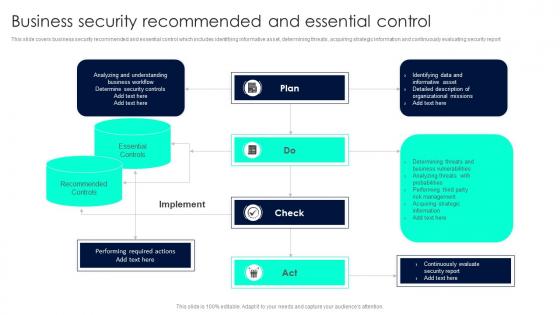 Business Security Recommended And Essential Control
Business Security Recommended And Essential ControlThis slide covers business security recommended and essential control which includes identifying informative asset, determining threats, acquiring strategic information and continuously evaluating security report. Introducing our Business Security Recommended And Essential Control set of slides. The topics discussed in these slides are Essential, Recommended Controls, Implement. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
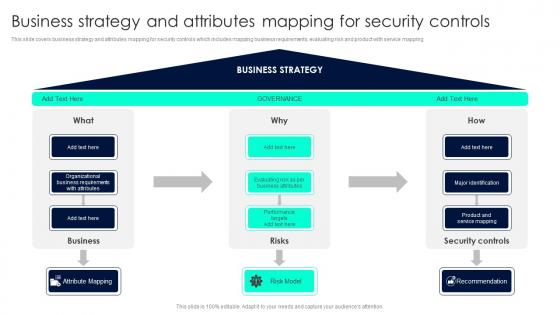 Business Strategy And Attributes Mapping For Security Controls
Business Strategy And Attributes Mapping For Security ControlsThis slide covers business strategy and attributes mapping for security controls which includes mapping business requirements, evaluating risk and product with service mapping. Introducing our Business Strategy And Attributes Mapping For Security Controls set of slides. The topics discussed in these slides are Governance, Business Strategy, Security Controls. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
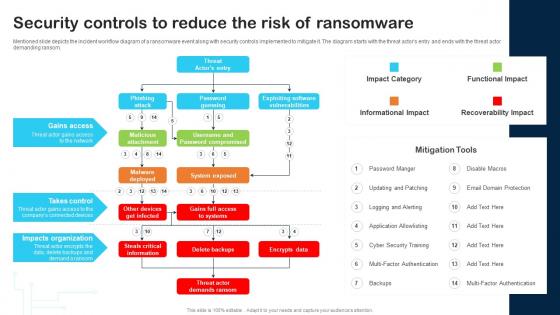 Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability
Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And VulnerabilityMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Gains Access, Takes Control, Impacts Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IT Risk Management Strategies Detection And Prevention Of Management Security Controls
IT Risk Management Strategies Detection And Prevention Of Management Security ControlsThe following slide highlights the management security controls which includes preventive management security controls showcasing IT security polices and guidelines with detection management security controls. Introducing IT Risk Management Strategies Detection And Prevention Of Management Security Controls to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Preventive Management, Security Controls, Detection Management, using this template. Grab it now to reap its full benefits.
-
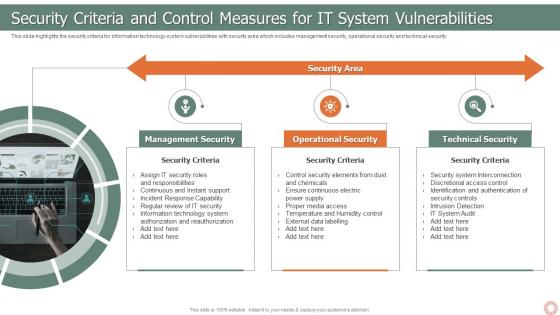 IT Risk Management Strategies Security Criteria And Control Measures For IT System Vulnerabilities
IT Risk Management Strategies Security Criteria And Control Measures For IT System VulnerabilitiesThis slide highlights the security criteria for information technology system vulnerabilities with security area which includes management security, operational security and technical security. Introducing IT Risk Management Strategies Security Criteria And Control Measures For It System Vulnerabilities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Security, Operational Security, Technical Security, using this template. Grab it now to reap its full benefits.
-
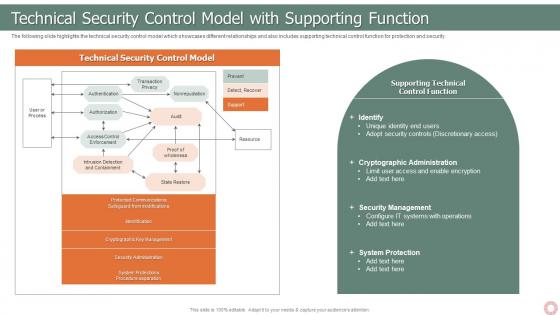 IT Risk Management Strategies Technical Security Control Model With Supporting Function
IT Risk Management Strategies Technical Security Control Model With Supporting FunctionThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Introducing IT Risk Management Strategies Technical Security Control Model With Supporting Function to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Technical Security, Control Model, Transaction Privacy, State Restore, using this template. Grab it now to reap its full benefits.
-
 Enterprise Risk Management Detection And Prevention Of Management Security Controls
Enterprise Risk Management Detection And Prevention Of Management Security ControlsThe following slide highlights the management security controls which includes preventive management security controls showcasing IT security polices and guidelines with detection management security controls. Increase audience engagement and knowledge by dispensing information using Enterprise Risk Management Detection And Prevention Of Management Security Controls. This template helps you present information on two stages. You can also present information on Preventive Management, Security Controls, Detection Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
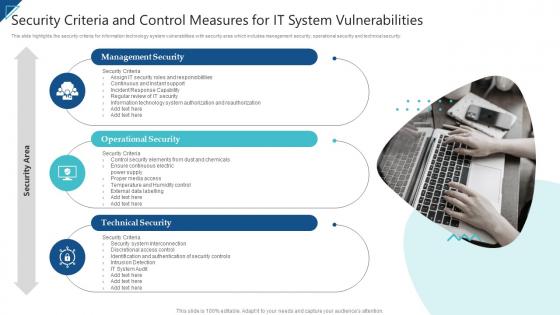 Enterprise Risk Management Security Criteria And Control Measures For IT System Vulnerabilities
Enterprise Risk Management Security Criteria And Control Measures For IT System VulnerabilitiesThis slide highlights the security criteria for information technology system vulnerabilities with security area which includes management security, operational security and technical security. Introducing Enterprise Risk Management Security Criteria And Control Measures For IT System Vulnerabilities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Security, Operational Security, Technical Security, using this template. Grab it now to reap its full benefits.
-
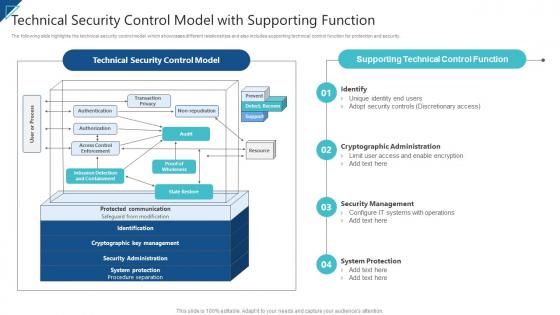 Enterprise Risk Management Technical Security Control Model With Supporting Function
Enterprise Risk Management Technical Security Control Model With Supporting FunctionThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Introducing Enterprise Risk Management Technical Security Control Model With Supporting Function to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Identify, Cryptographic Administration, Security Management, System Protection, using this template. Grab it now to reap its full benefits.
-
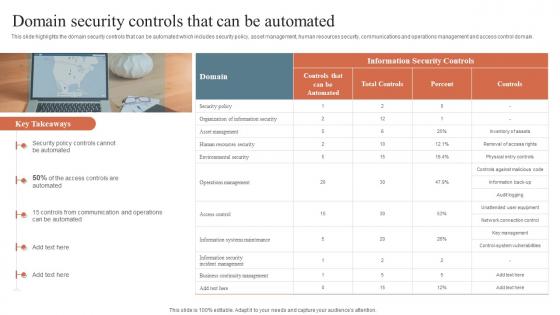 Domain Security Controls That Can Be Automated Security Orchestration Automation And Response Guide
Domain Security Controls That Can Be Automated Security Orchestration Automation And Response GuideThis slide highlights the domain security controls that can be automated which includes security policy, asset management, human resources security, communications and operations management and access control domain. Increase audience engagement and knowledge by dispensing information using Domain Security Controls That Can Be Automated Security Orchestration Automation And Response Guide. This template helps you present information on one stages. You can also present information on Security Policy, Communication And Operations, Security Controls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
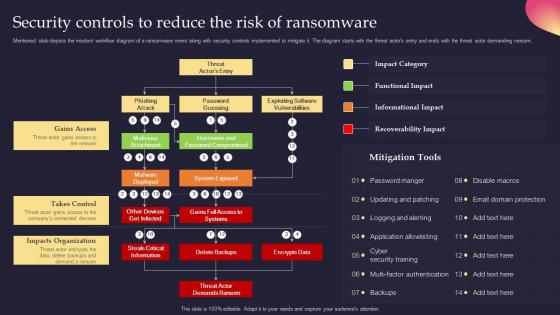 Security Controls To Reduce The Risk Of Ransomware Security Incident Response Playbook
Security Controls To Reduce The Risk Of Ransomware Security Incident Response PlaybookMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Present the topic in a bit more detail with this Security Controls To Reduce The Risk Of Ransomware Security Incident Response Playbook. Use it as a tool for discussion and navigation on Ransomwarem, Impacts Organization, Encrypts Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
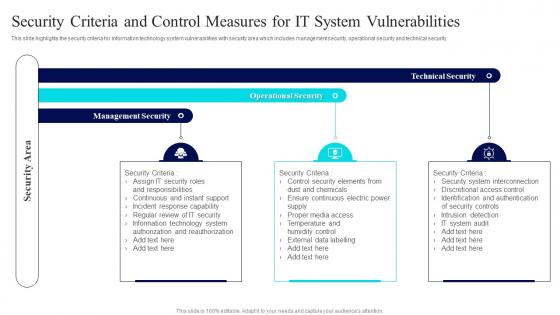 Security Criteria And Control Measures For IT System Vulnerabilities
Security Criteria And Control Measures For IT System VulnerabilitiesThis slide highlights the security criteria for information technology system vulnerabilities with security area which includes management security, operational security and technical security. Introducing Security Criteria And Control Measures For IT System Vulnerabilities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management Security, Operational Security, Technical Security, using this template. Grab it now to reap its full benefits.
-
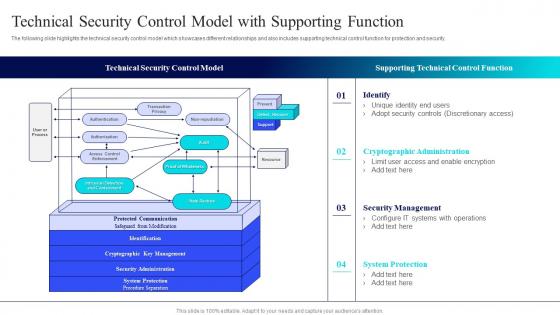 Technical Security Control Model With Isk Management Guide For Information Technology Systems
Technical Security Control Model With Isk Management Guide For Information Technology SystemsThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Deliver an outstanding presentation on the topic using this Technical Security Control Model With Isk Management Guide For Information Technology Systems. Dispense information and present a thorough explanation of Technical Security, Control Model, Supporting Technical, Control Function using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Role Based Access Control RBAC Securities Icon
Role Based Access Control RBAC Securities IconIntroducing our premium set of slides with name Role Based Access Control RBAC Securities Icon. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Control, Securities Icon, Audiences Attention. So download instantly and tailor it with your information.
-
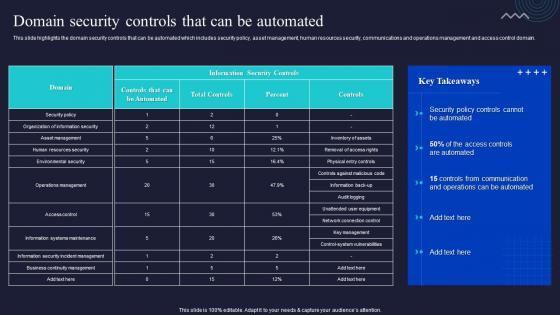 Enabling Automation In Cyber Security Operations Domain Security Controls That Can Be Automated
Enabling Automation In Cyber Security Operations Domain Security Controls That Can Be AutomatedThis slide highlights the domain security controls that can be automated which includes security policy, asset management, human resources security, communications and operations management and access control domain. Present the topic in a bit more detail with this Enabling Automation In Cyber Security Operations Domain Security Controls That Can Be Automated. Use it as a tool for discussion and navigation on Communication, Management, Human Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.



