Powerpoint Templates and Google slides for Security Layers
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Multi Layer Security Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Multi Layer Security Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone PowerPoint icon depicts layered security, emphasizing the importance of multiple layers of protection to keep data and systems secure. It is ideal for presentations and reports on cybersecurity, data protection, and IT security.
-
 Webpage Layered Security Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Webpage Layered Security Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful PowerPoint icon depicts layered security, a concept that involves multiple layers of security measures to protect digital data. It is a great visual aid for presentations on cyber security, data protection, and online safety.
-
 Webpage Layered Security Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Webpage Layered Security Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone PowerPoint icon depicts layered security, emphasizing the importance of multiple layers of protection to keep data and systems secure. It is ideal for presentations and reports on cybersecurity, data protection, and IT security.
-
 Survey analytics security layer collect across touch points
Survey analytics security layer collect across touch pointsPresenting this set of slides with name - Survey Analytics Security Layer Collect Across Touch Points. This is an editable three stages graphic that deals with topics like Survey Analytics, Security Layer, Collect Across Touch Points to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
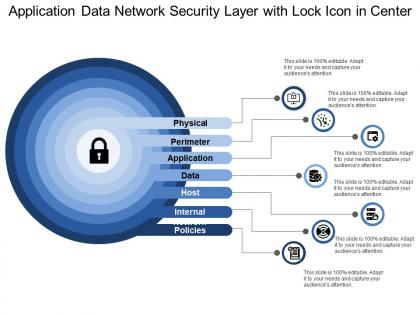 Application data network security layer with lock icon in center
Application data network security layer with lock icon in centerPresenting this set of slides with name - Application Data Network Security Layer With Lock Icon In Center. This is a stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
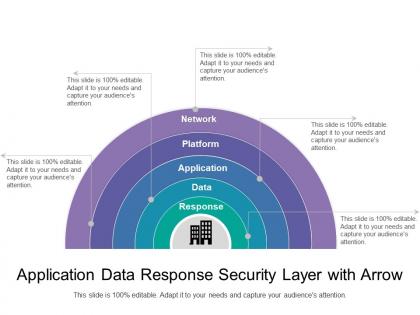 Application data response security layer with arrow
Application data response security layer with arrowPresenting this set of slides with name - Application Data Response Security Layer With Arrow. This is a five stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Multiple security layers with key icon
Multiple security layers with key iconPresenting this set of slides with name - Multiple Security Layers With Key Icon. This is a three stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
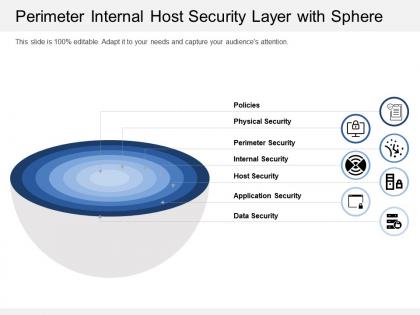 Perimeter internal host security layer with sphere
Perimeter internal host security layer with spherePresenting this set of slides with name - Perimeter Internal Host Security Layer With Sphere. This is a seven stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
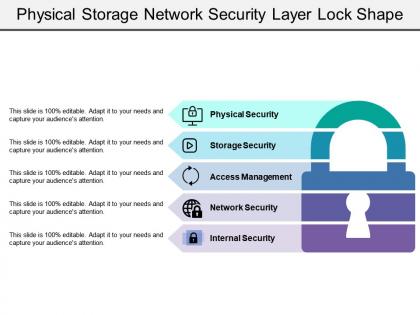 Physical storage network security layer lock shape
Physical storage network security layer lock shapePresenting this set of slides with name - Physical Storage Network Security Layer Lock Shape. This is a one stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Security layer icon with arrows and monitor with lock
Security layer icon with arrows and monitor with lockPresenting this set of slides with name - Security Layer Icon With Arrows And Monitor With Lock. This is a one stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Security layer icon with boxes and lock in center
Security layer icon with boxes and lock in centerPresenting this set of slides with name - Security Layer Icon With Boxes And Lock In Center. This is a one stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Security layer icon with three rows and lock icon
Security layer icon with three rows and lock iconPresenting this set of slides with name - Security Layer Icon With Three Rows And Lock Icon. This is a one stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
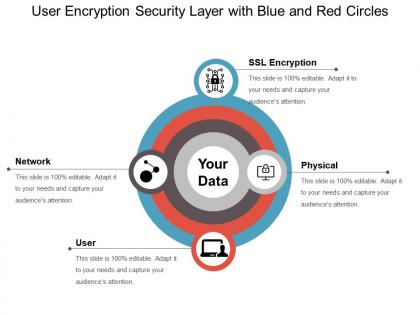 User encryption security layer with blue and red circles
User encryption security layer with blue and red circlesPresenting this set of slides with name - User Encryption Security Layer With Blue And Red Circles. This is a four stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Verified encrypted data security layer with arrows
Verified encrypted data security layer with arrowsPresenting this set of slides with name - Verified Encrypted Data Security Layer With Arrows. This is a six stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
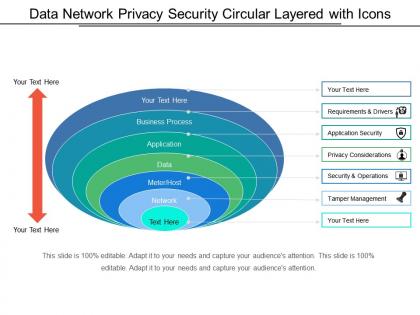 Data network privacy security circular layered with icons
Data network privacy security circular layered with iconsPresenting this set of slides with name - Data Network Privacy Security Circular Layered With Icons. This is a six stage process. The stages in this process are Circular Layered, Circle Layered, Cyclic Layered.
-
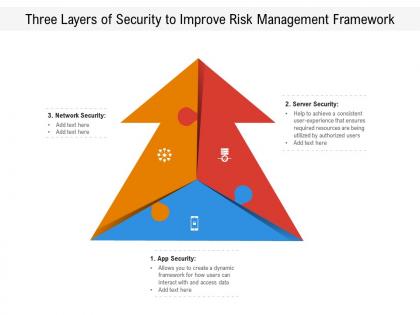 Three layers of security to improve risk management framework
Three layers of security to improve risk management frameworkPresenting this set of slides with name Three Layers Of Security To Improve Risk Management Framework. This is a three stage process. The stages in this process are Three Layers, Security Improve, Risk Management, Framework. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
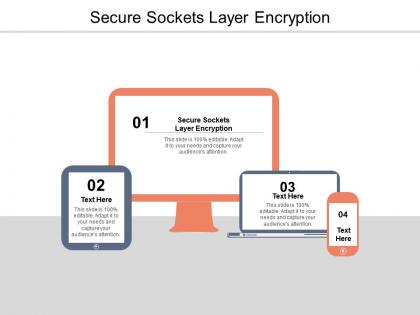 Secure sockets layer encryption ppt powerpoint presentation model cpb
Secure sockets layer encryption ppt powerpoint presentation model cpbPresenting this set of slides with name Secure Sockets Layer Encryption Ppt Powerpoint Presentation Model Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Secure Sockets Layer Encryption to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
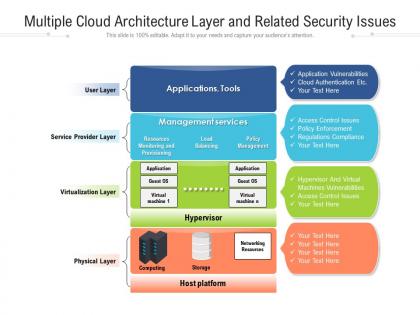 Multiple cloud architecture layer and related security issues
Multiple cloud architecture layer and related security issuesPresenting this set of slides with name Multiple Cloud Architecture Layer And Related Security Issues. The topics discussed in these slides are Multiple Cloud, Architecture Layer, Related Security, Issues. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Seven layer diagram of mortgage back security infographic template
Seven layer diagram of mortgage back security infographic templateThis is a single slide titled Seven Layer Diagram Of Mortgage Back Security Infographic Template. It is crafted using high quality vector based visuals that are 100 percent editable and available for immediate download in standard and widescreen aspect ratios.
-
 Layered security approach ppt powerpoint presentation show inspiration cpb
Layered security approach ppt powerpoint presentation show inspiration cpbPresenting Layered Security Approach Ppt Powerpoint Presentation Show Inspiration Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Layered Security Approach. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Secure socket layer technology ppt powerpoint presentation model graphics pictures cpb
Secure socket layer technology ppt powerpoint presentation model graphics pictures cpbPresenting our Secure Socket Layer Technology Ppt Powerpoint Presentation Model Graphics Pictures Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Secure Socket Layer Technology This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
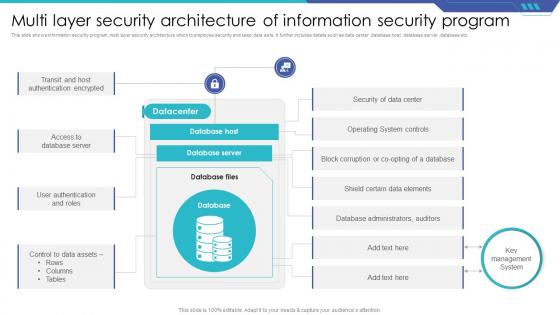 Multi Layer Security Architecture Of Information Security Program
Multi Layer Security Architecture Of Information Security ProgramThis slide shows information security program ,multi layer security architecture which to employee security and keep data safe. It further includes details such as data center ,database host ,database server ,database etc. Introducing our Multi Layer Security Architecture Of Information Security Program set of slides. The topics discussed in these slides are Datacenter, Database Host, Database Server. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.


