Powerpoint Templates and Google slides for Security Management Plan
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
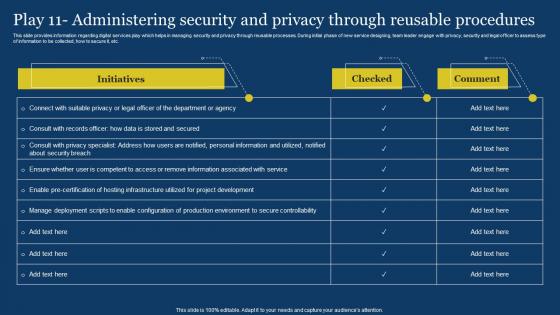 US Digital Services Management Play 11 Administering Security And Privacy Through ReUSable
US Digital Services Management Play 11 Administering Security And Privacy Through ReUSableThis slide provides information regarding digital services play which helps in managing security and privacy through reUSable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc. Deliver an outstanding presentation on the topic USing this US Digital Services Management Play 11 Administering Security And Privacy Through ReUSable Dispense information and present a thorough explanation of Department Or Agency, Secure Controllability USing the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Account Manager Salary In Powerpoint And Google Slides Cpb
Security Account Manager Salary In Powerpoint And Google Slides CpbPresenting our Security Account Manager Salary In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Security Account Manager Salary This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Manage Information Security In Powerpoint And Google Slides Cpb
Manage Information Security In Powerpoint And Google Slides CpbPresenting Manage Information Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase Six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Manage Information Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
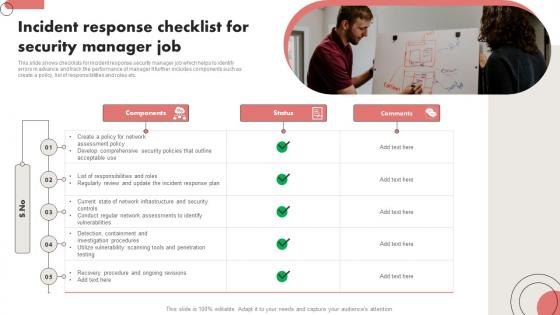 Incident Response Checklist For Security Manager Job
Incident Response Checklist For Security Manager JobThis slide shows checklists for incident response security manager job which helps to identify errors in advance and track the performance of manager It further includes components such as create a policy, list of responsibilities and roles etc. Presenting our set of slides with Incident Response Checklist For Security Manager Job. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Components, Status, Manager.
-
 Risk Management Cyber Security In Powerpoint And Google Slides Cpb
Risk Management Cyber Security In Powerpoint And Google Slides CpbPresenting our Risk Management Cyber Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Risk Management Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
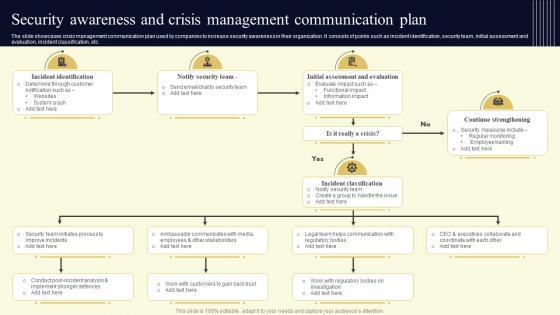 Security Awareness And Crisis Management Communication Plan
Security Awareness And Crisis Management Communication PlanThe slide showcases crisis management communication plan used by companies to increase security awareness in their organization. It consists of points such as incident identification, security team, initial assessment and evaluation, incident classification, etc. Presenting our well structured Security Awareness And Crisis Management Communication Plan. The topics discussed in this slide are Identification, Security, Evaluation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Analyse And Rank Impact Of Cyber Threat Improving Cyber Security Risks Management
Analyse And Rank Impact Of Cyber Threat Improving Cyber Security Risks ManagementThe following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Present the topic in a bit more detail with this Analyse And Rank Impact Of Cyber Threat Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Vulnerability, Threat Source, Appropriate Structure, Privilege Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
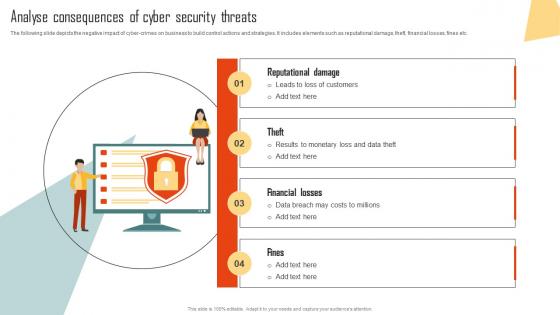 Analyse Consequences Of Cyber Security Threats Improving Cyber Security Risks Management
Analyse Consequences Of Cyber Security Threats Improving Cyber Security Risks ManagementThe following slide depicts the negative impact of cyber-crimes on business to build control actions and strategies. It includes elements such as reputational damage, theft, financial losses, fines etc. Introducing Analyse Consequences Of Cyber Security Threats Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reputational Damage, Financial Losses, Security Threats, using this template. Grab it now to reap its full benefits.
-
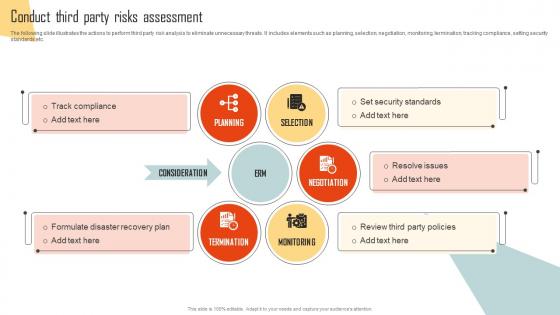 Conduct Third Party Risks Assessment Improving Cyber Security Risks Management
Conduct Third Party Risks Assessment Improving Cyber Security Risks ManagementThe following slide illustrates the actions to perform third party risk analysis to eliminate unnecessary threats. It includes elements such as planning, selection, negotiation, monitoring, termination, tracking compliance, setting security standards etc. Introducing Conduct Third Party Risks Assessment Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Planning, Selection, Negotiation, Monitoring, Termination, using this template. Grab it now to reap its full benefits.
-
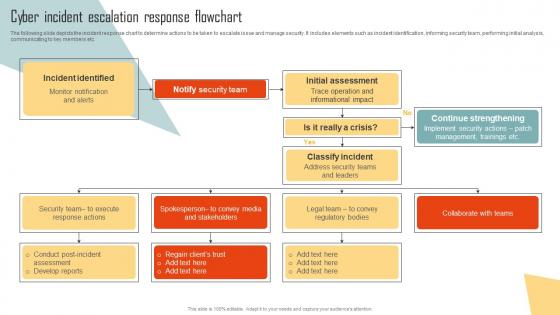 Cyber Incident Escalation Response Flowchart Improving Cyber Security Risks Management
Cyber Incident Escalation Response Flowchart Improving Cyber Security Risks ManagementThe following slide depicts the incident response chart to determine actions to be taken to escalate issue and manage security. It includes elements such as incident identification, informing security team, performing initial analysis, communicating to key members etc. Present the topic in a bit more detail with this Cyber Incident Escalation Response Flowchart Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Incident Identified, Notify Security Team, Initial Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
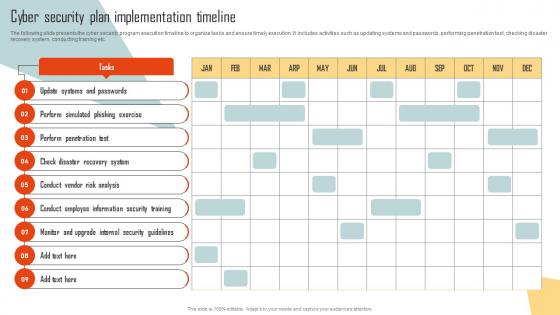 Cyber Security Plan Implementation Timeline Improving Cyber Security Risks Management
Cyber Security Plan Implementation Timeline Improving Cyber Security Risks ManagementThe following slide presents the cyber security program execution timeline to organize tasks and ensure timely execution. It includes activities such as updating systems and passwords, performing penetration test, checking disaster recovery system, conducting training etc. Introducing Cyber Security Plan Implementation Timeline Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Systems And Passwords, Perform Simulated, Phishing Exercise, using this template. Grab it now to reap its full benefits.
-
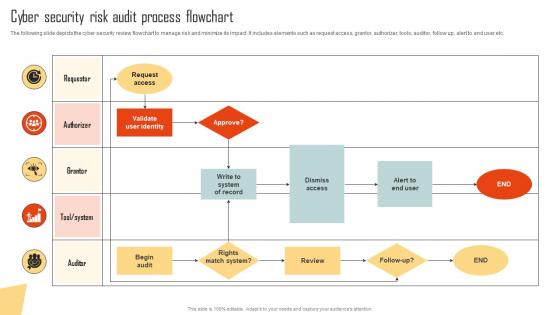 Cyber Security Risk Audit Process Flowchart Improving Cyber Security Risks Management
Cyber Security Risk Audit Process Flowchart Improving Cyber Security Risks ManagementThe following slide depicts the cyber security review flowchart to manage risk and minimize its impact. It includes elements such as request access, grantor, authorizer, tools, auditor, follow up, alert to end user etc. Present the topic in a bit more detail with this Cyber Security Risk Audit Process Flowchart Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Request Access, Validate User Identity, Dismiss Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Deploy Tools To Minimize Impact Of Cyber Security Risks Improving Cyber Security Risks Management
Deploy Tools To Minimize Impact Of Cyber Security Risks Improving Cyber Security Risks ManagementThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool name, features, trial period, cost and reviews etc. Deliver an outstanding presentation on the topic using this Deploy Tools To Minimize Impact Of Cyber Security Risks Improving Cyber Security Risks Management. Dispense information and present a thorough explanation of Determines Suspicious, Features, Cyber Security Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
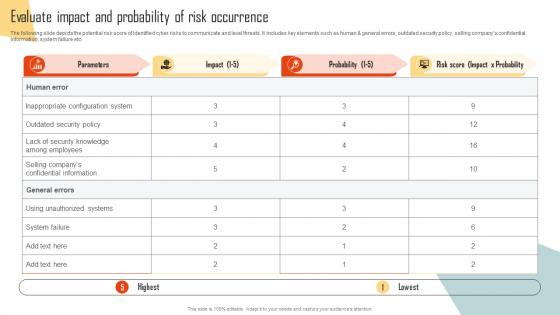 Evaluate Impact And Probability Of Risk Occurrence Improving Cyber Security Risks Management
Evaluate Impact And Probability Of Risk Occurrence Improving Cyber Security Risks ManagementThe following slide depicts the potential risk score of identified cyber risks to communicate and level threats. It includes key elements such as human and general errors, outdated security policy, selling companys confidential information, system failure etc. Present the topic in a bit more detail with this Evaluate Impact And Probability Of Risk Occurrence Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Parameters, Inappropriate Configuration System, Unauthorized Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
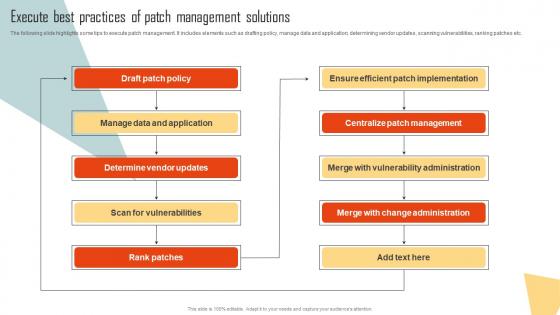 Execute Best Practices Of Patch Management Solutions Improving Cyber Security Risks Management
Execute Best Practices Of Patch Management Solutions Improving Cyber Security Risks ManagementThe following slide highlights some tips to execute patch management. It includes elements such as drafting policy, manage data and application, determining vendor updates, scanning vulnerabilities, ranking patches etc. Deliver an outstanding presentation on the topic using this Execute Best Practices Of Patch Management Solutions Improving Cyber Security Risks Management. Dispense information and present a thorough explanation of Draft Patch Policy, Manage Data And Application, Determine Vendor Updates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management
Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks ManagementThe following slide showcases the various types of cyber-attacks faced by employees to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service etc. Introducing Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Spear Phishing, Advanced Persistent Threats, Ransomware, Phishing, using this template. Grab it now to reap its full benefits.
-
 Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks Management
Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks ManagementThe following slide illustrates some best practices to execute preventive actions for cyber attacks. It includes elements such as train employees, updating systems and software, developing incident response plan, backing up data, maintaining compliance etc. Increase audience engagement and knowledge by dispensing information using Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks Management. This template helps you present information on six stages. You can also present information on Train Employees, Maintain Compliance, Develop Incident Response Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Plan Useful Data Backup Schedule Improving Cyber Security Risks Management
Plan Useful Data Backup Schedule Improving Cyber Security Risks ManagementThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Present the topic in a bit more detail with this Plan Useful Data Backup Schedule Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Incremental Backup, Plan Useful, Data Backup Schedule. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Prioritize Cyber Security Risks With Matrix Improving Cyber Security Risks Management
Prioritize Cyber Security Risks With Matrix Improving Cyber Security Risks ManagementThe following slide presents cyber security risks exposure grid to determine and plan mitigation actions. It includes elements such as restricting permissions, remediating constantly, postponing remediation, tracking risk escalation etc. Introducing Prioritize Cyber Security Risks With Matrix Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Restrict Permissions, Postpone Remediation, Track Risk Escalation, using this template. Grab it now to reap its full benefits.
-
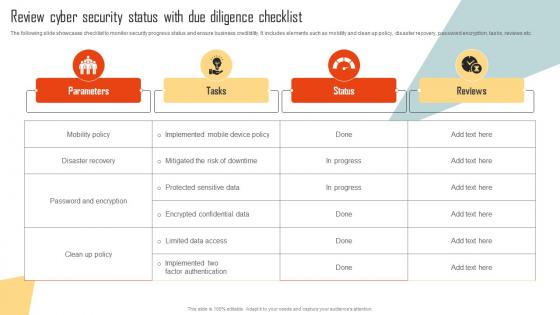 Review Cyber Security Status With Due Diligence Checklist Improving Cyber Security Risks Management
Review Cyber Security Status With Due Diligence Checklist Improving Cyber Security Risks ManagementThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Present the topic in a bit more detail with this Review Cyber Security Status With Due Diligence Checklist Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Disaster Recovery, Password And Encryption, Parameters. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
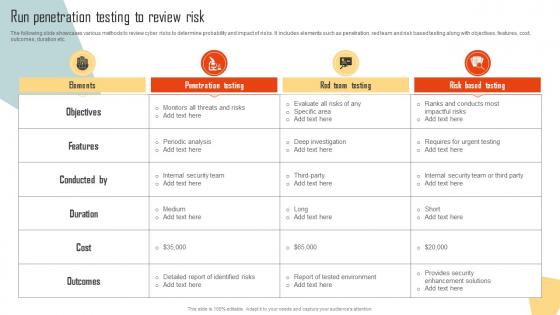 Run Penetration Testing To Review Risk Improving Cyber Security Risks Management
Run Penetration Testing To Review Risk Improving Cyber Security Risks ManagementThe following slide showcases various methods to review cyber risks to determine probability and impact of risks. It includes elements such as penetration, red team and risk based testing along with objectives, features, cost, outcomes, duration etc. Deliver an outstanding presentation on the topic using this Run Penetration Testing To Review Risk Improving Cyber Security Risks Management. Dispense information and present a thorough explanation of Objectives, Features, Conducted, Duration, Outcomes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Select Cybersecurity Training Program Courses Improving Cyber Security Risks Management
Select Cybersecurity Training Program Courses Improving Cyber Security Risks ManagementThe following slide showcases the best cybersecurity training courses to educate employees and minimize the possibility of cyber-attacks. It includes cloud, disaster recovery, hardware, information security programs, duration, mode and cost. Present the topic in a bit more detail with this Select Cybersecurity Training Program Courses Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Cloud Security, Information Security, Cybersecurity Fundamentals. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents For Improving Cyber Security Risk Management Process
Table Of Contents For Improving Cyber Security Risk Management ProcessIntroducing Table Of Contents For Improving Cyber Security Risk Management Process to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risks And Attacks, Management Solutions, Program Courses, using this template. Grab it now to reap its full benefits.
-
 Various Sources Of Cyber Security Incidents Improving Cyber Security Risks Management
Various Sources Of Cyber Security Incidents Improving Cyber Security Risks ManagementThe following slide depicts some multiple drivers of cyber security incidents to generate awareness about cyber crimes. It includes elements such as corporate spies, malicious insiders, criminal groups, hackers, hacktivists, terrorist groups etc. Increase audience engagement and knowledge by dispensing information using Various Sources Of Cyber Security Incidents Improving Cyber Security Risks Management. This template helps you present information on seven stages. You can also present information on Criminal Groups, Terrorist Groups, Malicious Insiders, Corporate Spies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Digital Security Management In Powerpoint And Google Slides Cpb
Digital Security Management In Powerpoint And Google Slides CpbPresenting our Digital Security Management In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Digital Security Management. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Manage Investor Relations With Effective Communication Security Token Offerings BCT SS
Manage Investor Relations With Effective Communication Security Token Offerings BCT SSThe following slide illustrates some ways to maintain effective and healthy relations with investors. It includes elements such as transparent communication, building investor relations team, conducting feedbacks and surveys, ensuring investor integration, etc. Increase audience engagement and knowledge by dispensing information using Manage Investor Relations With Effective Communication Security Token Offerings BCT SS. This template helps you present information on four stages. You can also present information on Transparent Communication, Investor Relations Team, Feedback And Surveys using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
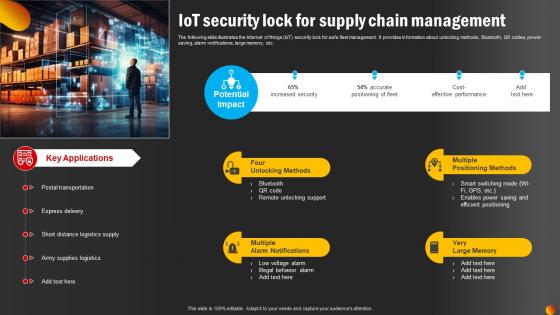 IoT Security Lock For Supply Chain Management
IoT Security Lock For Supply Chain ManagementThe following slide illustrates the Internet of things IoT security lock for safe fleet management. It provides information about unlocking methods, Bluetooth, QR codes, power saving, alarm notifications, large memory, etc. Introducing our premium set of slides with IoT Security Lock For Supply Chain Management. Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Four Unlocking Methods, Multiple Positioning Methods. So download instantly and tailor it with your information.
-
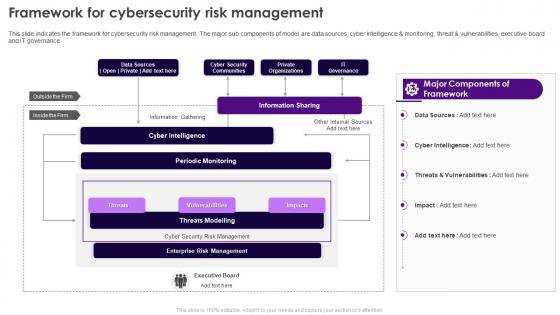 Security Plan To Prevent Cyber Framework For Cybersecurity Risk Management
Security Plan To Prevent Cyber Framework For Cybersecurity Risk ManagementThis slide indicates the framework for cybersecurity risk management. The major sub components of model are data sources, cyber intelligence and monitoring, threat and vulnerabilities, executive board and IT governance. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Framework For Cybersecurity Risk Management. Use it as a tool for discussion and navigation on Cyber Security Communities, Information Sharing, Private Organizations, IT Governance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
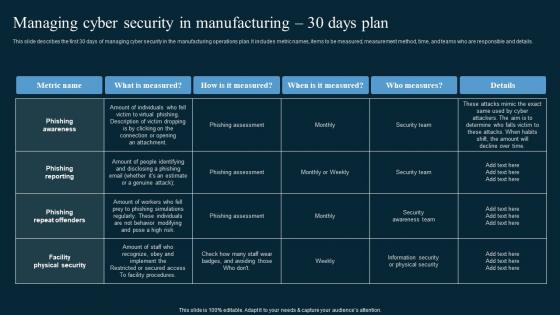 Managing Cyber Security In Manufacturing 30 Days Plan AI In Manufacturing
Managing Cyber Security In Manufacturing 30 Days Plan AI In ManufacturingThis slide describes the first 30 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Present the topic in a bit more detail with this Managing Cyber Security In Manufacturing 30 Days Plan AI In Manufacturing. Use it as a tool for discussion and navigation on Phishing Awareness, Phishing Reporting, Phishing Repeat Offenders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
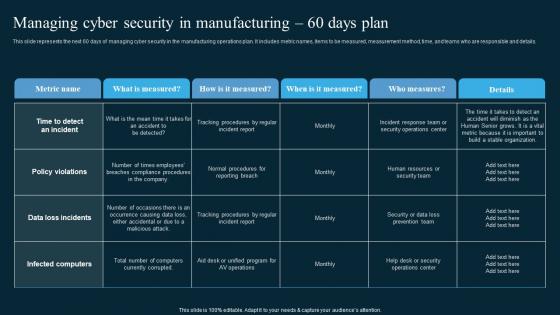 Managing Cyber Security In Manufacturing 60 Days Plan AI In Manufacturing
Managing Cyber Security In Manufacturing 60 Days Plan AI In ManufacturingThis slide represents the next 60 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this Managing Cyber Security In Manufacturing 60 Days Plan AI In Manufacturing. Dispense information and present a thorough explanation of Policy Violations, Data Loss Incidents, Infected Computers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Cyber Security In Manufacturing 90 Days Plan AI In Manufacturing
Managing Cyber Security In Manufacturing 90 Days Plan AI In ManufacturingThis slide depicts the next 90 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Present the topic in a bit more detail with this Managing Cyber Security In Manufacturing 90 Days Plan AI In Manufacturing. Use it as a tool for discussion and navigation on Training Completion, Communication Methods, Who Measures. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Managed Security Service Provider Market In Powerpoint And Google Slides Cpb
Managed Security Service Provider Market In Powerpoint And Google Slides CpbPresenting our Managed Security Service Provider Market In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Managed Security Service Provider Market This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Risk Management Company In Powerpoint And Google Slides Cpb
Cyber Security Risk Management Company In Powerpoint And Google Slides CpbPresenting Cyber Security Risk Management Company In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Risk Management Company. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Website Security Management Action Plan Virtual Shop Designing For Attracting Customers
Website Security Management Action Plan Virtual Shop Designing For Attracting CustomersMentioned slide provides insights into site security management tips which can be implemented by businesses to prevent website hacking. It includes key components such as select secure domain registrar, use safe plugins, anti malware programs, regular backup, SSL certification, etc. Introducing Website Security Management Action Plan Virtual Shop Designing For Attracting Customers to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Criteria, Description, Priority, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Risk Management Jobs In Powerpoint And Google Slides Cpb
Cyber Security Risk Management Jobs In Powerpoint And Google Slides CpbPresenting our Cyber Security Risk Management Jobs In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Security Risk Management Jobs This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
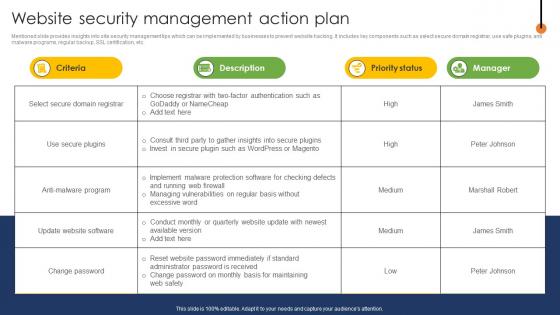 Web Page Designing Website Security Management Action Plan
Web Page Designing Website Security Management Action PlanMentioned slide provides insights into site security management tips which can be implemented by businesses to prevent website hacking. It includes key components such as select secure domain registrar, use safe plugins, anti malware programs, regular backup, SSL certification, etc. Deliver an outstanding presentation on the topic using this Web Page Designing Website Security Management Action Plan Dispense information and present a thorough explanation of Criteria, Description, Priority Status, Manager using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
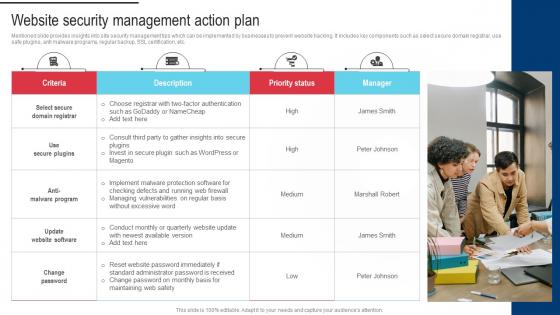 Procedure For Successful Website Security Management Action Plan
Procedure For Successful Website Security Management Action PlanMentioned slide provides insights into site security management tips which can be implemented by businesses to prevent website hacking. It includes key components such as select secure domain registrar, use safe plugins, anti malware programs, regular backup, SSL certification, etc. Introducing Procedure For Successful Website Security Management Action Plan to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Leverage Themes And Plugin, Improve Loading Time, Implement CSS using this template. Grab it now to reap its full benefits.
-
 IT In Manufacturing Industry V2 Managing Cyber Security In Manufacturing 90 Days Plan
IT In Manufacturing Industry V2 Managing Cyber Security In Manufacturing 90 Days PlanThis slide depicts the next 90 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this IT In Manufacturing Industry V2 Managing Cyber Security In Manufacturing 90 Days Plan. Dispense information and present a thorough explanation of Managing Cyber Security, Manufacturing Operations Plan, Security Training Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Cyber Security In Manufacturing 30 Days IT In Manufacturing Industry V2
Managing Cyber Security In Manufacturing 30 Days IT In Manufacturing Industry V2This slide describes the first 30 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this Managing Cyber Security In Manufacturing 30 Days IT In Manufacturing Industry V2. Dispense information and present a thorough explanation of Phishing Awareness, Phishing Reporting, Phishing Repeat Offenders, Facility Physical Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Cyber Security In Manufacturing 60 Days IT In Manufacturing Industry V2
Managing Cyber Security In Manufacturing 60 Days IT In Manufacturing Industry V2This slide represents the next 60 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Present the topic in a bit more detail with this Managing Cyber Security In Manufacturing 60 Days IT In Manufacturing Industry V2. Use it as a tool for discussion and navigation on Managing Cyber Security, Manufacturing Operations Plan, Data Loss Incidents. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
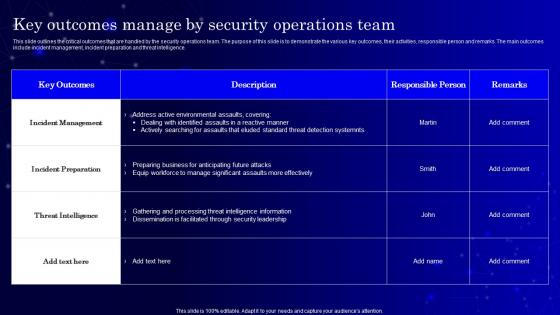 Secops V2 Key Outcomes Manage By Security Operations Team
Secops V2 Key Outcomes Manage By Security Operations TeamThis slide outlines the critical outcomes that are handled by the security operations team. The purpose of this slide is to demonstrate the various key outcomes, their activities, responsible person and remarks. The main outcomes include incident management, incident preparation and threat intelligence. Deliver an outstanding presentation on the topic using this Secops V2 Key Outcomes Manage By Security Operations Team. Dispense information and present a thorough explanation of Incident Management, Incident Preparation, Threat Intelligence, Security Leadership using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
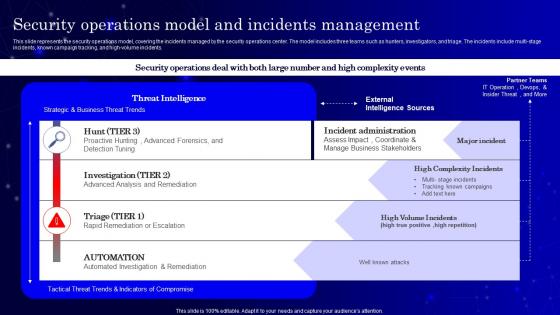 Secops V2 Security Operations Model And Incidents Management
Secops V2 Security Operations Model And Incidents ManagementThis slide represents the security operations model, covering the incidents managed by the security operations center. The model includes three teams such as hunters, investigators, and triage. The incidents include multi-stage incidents, known campaign tracking, and high-volume incidents. Present the topic in a bit more detail with this Secops V2 Security Operations Model And Incidents Management. Use it as a tool for discussion and navigation on Security Operations Model, Incidents Management, Known Campaign Tracking, Rapid Remediation Or Escalation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
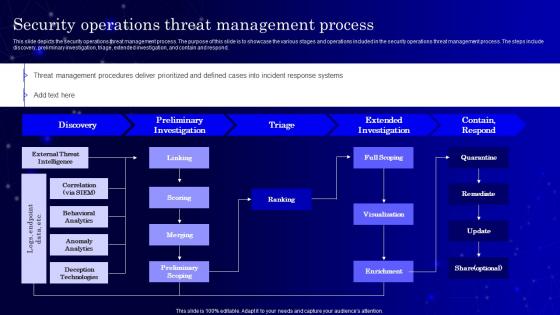 Secops V2 Security Operations Threat Management Process
Secops V2 Security Operations Threat Management ProcessThis slide depicts the security operations threat management process. The purpose of this slide is to showcase the various stages and operations included in the security operations threat management process. The steps include discovery, preliminary investigation, triage, extended investigation, and contain and respond. Deliver an outstanding presentation on the topic using this Secops V2 Security Operations Threat Management Process. Dispense information and present a thorough explanation of Extended Investigation, Preliminary Investigation, Security Operations Threat
-
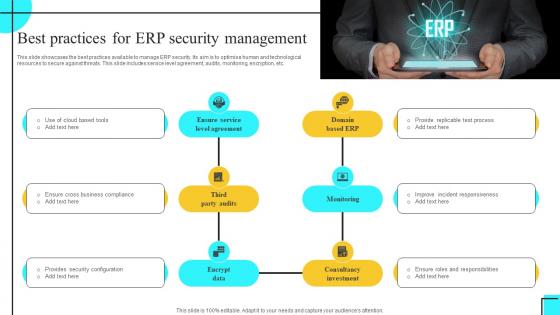 Best Practices For ERP Security Management
Best Practices For ERP Security ManagementThis slide showcases the best practices available to manage ERP security. Its aim is to optimise human and technological resources to secure against threats. This slide includes service level agreement, audits, monitoring, encryption, etc. Presenting our set of slides with Best Practices For ERP Security Management. This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Level Agreement, Domain Based ERP, Third Party Audits.
-
 Complexities Involved In ERP Security Management
Complexities Involved In ERP Security ManagementThis slide showcases the complexities involved in preparing ERP security management. Its aim is to make user secure workshops. This slide includes preparation, trade-offs, realisation, etc. Introducing our Complexities Involved In ERP Security Management set of slides. The topics discussed in these slides are User Training, Review Effectiveness, Realisation. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
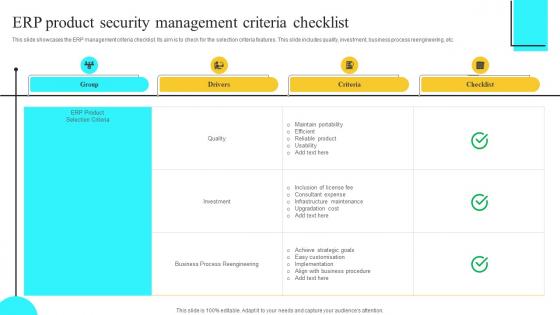 ERP Product Security Management Criteria Checklist
ERP Product Security Management Criteria ChecklistThis slide showcases the ERP management criteria checklist. Its aim is to check for the selection criteria features. This slide includes quality, investment, business process reengineering, etc. Presenting our well structured ERP Product Security Management Criteria Checklist. The topics discussed in this slide are Drivers, Criteria, Checklist. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
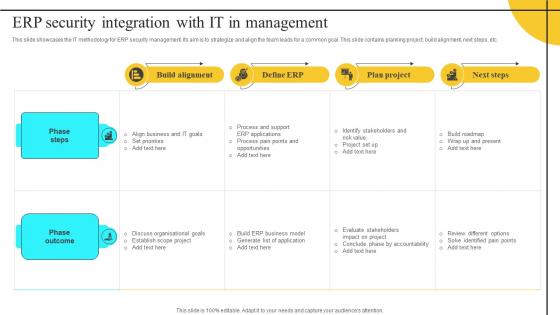 ERP Security Integration With It In Management
ERP Security Integration With It In ManagementThis slide showcases the IT methodology for ERP security management. Its aim is to strategize and align the team leads for a common goal. This slide contains planning project, build alignment, next steps, etc. Introducing our ERP Security Integration With It In Management set of slides. The topics discussed in these slides are Phase Steps, Phase Outcome. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
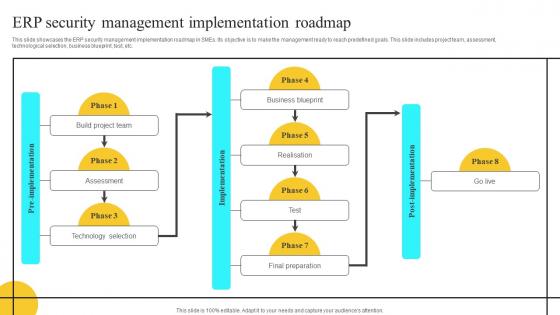 ERP Security Management Implementation Roadmap
ERP Security Management Implementation RoadmapThis slide showcases the ERP security management implementation roadmap in SMEs. Its objective is to make the management ready to reach predefined goals. This slide includes project team, assessment, technological selection, business blueprint, test, etc. Presenting our well structured ERP Security Management Implementation Roadmap. The topics discussed in this slide are Build Alignment, Define ERP, Plan Project. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
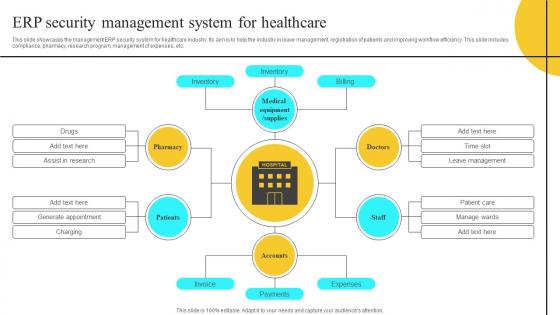 ERP Security Management System For Healthcare
ERP Security Management System For HealthcareThis slide showcases the management ERP security system for healthcare industry. Its aim is to help the industry in leave management, registration of patients and improving workflow efficiency. This slide includes compliance, pharmacy, research program, management of expenses, etc. Introducing our ERP Security Management System For Healthcare set of slides. The topics discussed in these slides are Build Project Team, Assessment, Technology Selection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 ERP Security Protection Management Icon
ERP Security Protection Management IconPresenting our set of slides with ERP Security Protection Management Icon. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on ERP Security Protection Management Icon.
-
 ERP Settings Security Management Icon
ERP Settings Security Management IconIntroducing our premium set of slides with ERP Settings Security Management Icon. Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like ERP Settings Security Management Icon. So download instantly and tailor it with your information.
-
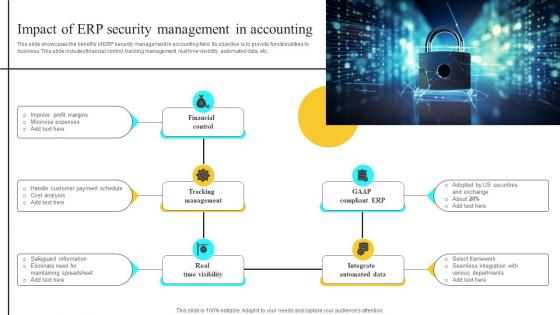 Impact Of ERP Security Management In Accounting
Impact Of ERP Security Management In AccountingThis slide showcases the benefits of ERP security management in accounting field. Its objective is to provide functionalities to business. This slide includes financial control, tracking management, real time visibility, automated data, etc. Presenting our well structured Impact Of ERP Security Management In Accounting. The topics discussed in this slide are Financial Control, Tracking Management, Real Time Visibility. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
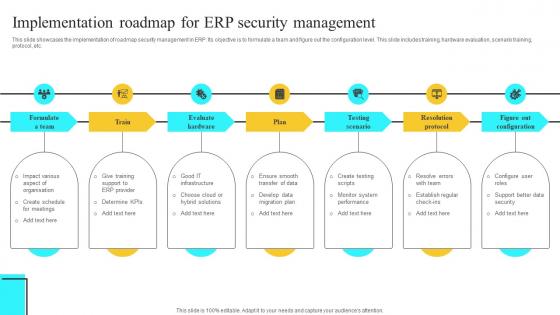 Implementation Roadmap For ERP Security Management
Implementation Roadmap For ERP Security ManagementThis slide showcases the implementation of roadmap security management in ERP. Its objective is to formulate a team and figure out the configuration level. This slide includes training, hardware evaluation, scenario training, protocol, etc. Presenting our set of slides with Implementation Roadmap For ERP Security Management. This exhibits information on Seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Resolution Protocol, Figure Out Configuration, Testing Scenario.
-
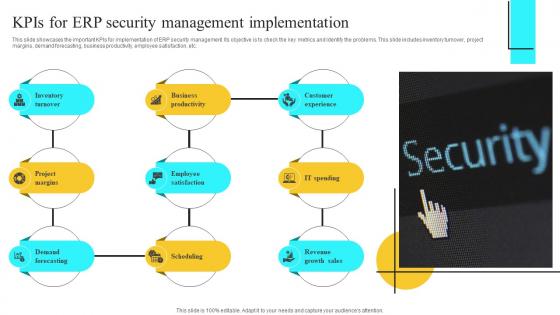 Kpis For ERP Security Management Implementation
Kpis For ERP Security Management ImplementationThis slide showcases the important KPIs for implementation of ERP security management. Its objective is to check the key metrics and identify the problems. This slide includes inventory turnover, project margins, demand forecasting, business productivity, employee satisfaction, etc. Introducing our premium set of slides with Kpis For ERP Security Management Implementation. Ellicudate the Nine stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Inventory Turnover, Business Productivity, Customer Experience. So download instantly and tailor it with your information.
-
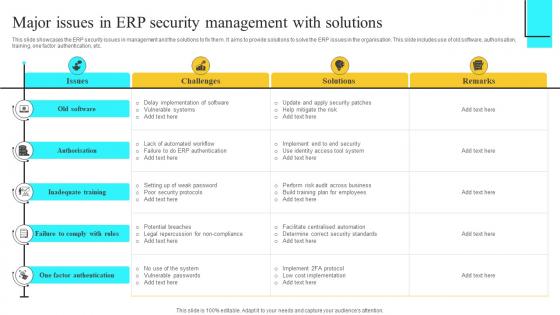 Major Issues In ERP Security Management With Solutions
Major Issues In ERP Security Management With SolutionsThis slide showcases the ERP security issues in management and the solutions to fix them. It aims to provide solutions to solve the ERP issues in the organisation. This slide includes use of old software, authorisation, training, one factor authentication, etc. Presenting our well structured Old Software, Authorisation, Inadequate Training. The topics discussed in this slide are Old Software, Authorisation, Inadequate Training. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
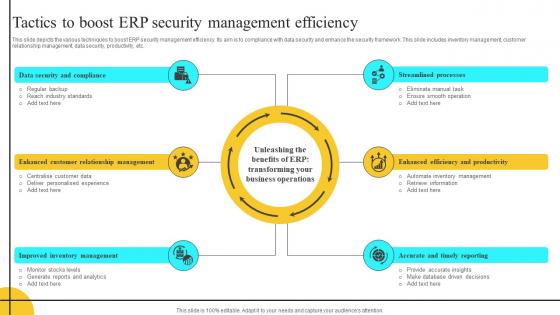 Tactics To Boost ERP Security Management Efficiency
Tactics To Boost ERP Security Management EfficiencyThis slide depicts the various techniques to boost ERP security management efficiency. Its aim is to compliance with data security and enhance the security framework. This slide includes inventory management, customer relationship management, data security, productivity, etc. Introducing our premium set of slides with Tactics To Boost ERP Security Management Efficiency. Ellicudate the Six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security And Compliance, Relationship Management, Inventory Management. So download instantly and tailor it with your information.
-
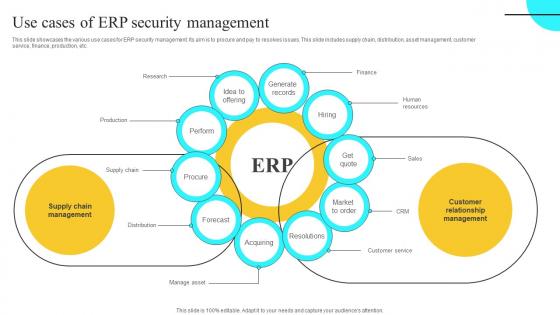 Use Cases Of ERP Security Management
Use Cases Of ERP Security ManagementThis slide showcases the various use cases for ERP security management. Its aim is to procure and pay to resolves issues. This slide includes supply chain, distribution, asset management, customer service, finance, production, etc. Presenting our well structured Use Cases Of ERP Security Management. The topics discussed in this slide are Supply Chain Management, Customer Relationship Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cloud Access Security Broker CASB V2 Shadow IT Management Lifecycle Overview
Cloud Access Security Broker CASB V2 Shadow IT Management Lifecycle OverviewThis slide outlines the lifecycle of shadow IT management for safely adopting cloud apps. The purpose of this slide is to showcase the various stages of the lifecycle, such as discovering shadow IT, knowing the risk level of apps, evaluating compliance, analyzing usage, governing cloud apps, and continuous monitoring. Introducing Cloud Access Security Broker CASB V2 Shadow IT Management Lifecycle Overview to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Evaluate Compliance, Govern Cloud Apps, Continuous Monitoring, Network Ecosystem, using this template. Grab it now to reap its full benefits.
-
 Best Practices For Security Compliance Management
Best Practices For Security Compliance ManagementThis slide shows best practices for security compliance helps to improve security posture, minimize exposure to non compliance risks. It further includes practices such as develop risk assessment plan, promote team communication etc. Presenting our set of slides with Best Practices For Security Compliance Management. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Develop Risk Assessment Plan, Promote Team Communication.
-
 Laws And Standards For Security Compliance Management
Laws And Standards For Security Compliance ManagementThis slide shows laws and standards for security compliance management helps in allow businesses to build a cyber security program. It further includes details as GDPR, CCPA and CPRA, soc, hipaa etc. Presenting our set of slides with Laws And Standards For Security Compliance Management. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Laws And Standards, Description.



