Powerpoint Templates and Google slides for Security Of Supply
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
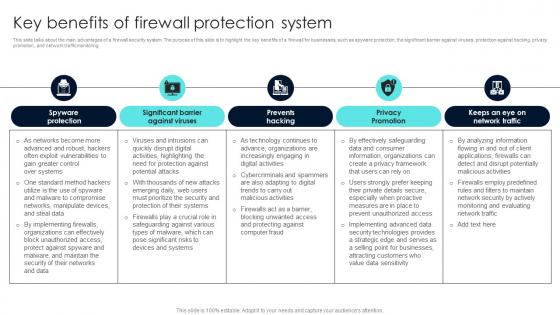 Firewall Network Security Key Benefits Of Firewall Protection System
Firewall Network Security Key Benefits Of Firewall Protection SystemThis slide talks about the main advantages of a firewall security system. The purpose of this slide is to highlight the key benefits of a firewall for businesses, such as spyware protection, the significant barrier against viruses, protection against hacking, privacy promotion, and network traffic monitoring. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Key Benefits Of Firewall Protection System This template helps you present information on Five stages. You can also present information on Intelligent Protection, Traffic Filtering, Communication Protocol Administration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
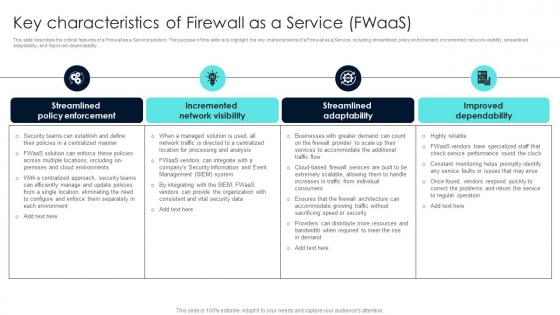 Firewall Network Security Key Characteristics Of Firewall As A Service FWaas
Firewall Network Security Key Characteristics Of Firewall As A Service FWaasThis slide describes the critical features of a Firewall as a Service solution. The purpose of this slide is to highlight the key characteristics of a Firewall as a Service, including streamlined policy enforcement, incremented network visibility, streamlined adaptability, and improved dependability. Introducing Firewall Network Security Key Characteristics Of Firewall As A Service FWaas to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Graphical Interface, Device Management, Scalability using this template. Grab it now to reap its full benefits.
-
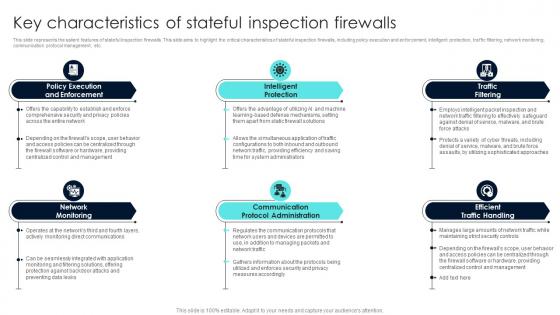 Firewall Network Security Key Characteristics Of Stateful Inspection Firewalls
Firewall Network Security Key Characteristics Of Stateful Inspection FirewallsThis slide represents the salient features of stateful inspection firewalls. This slide aims to highlight the critical characteristics of stateful inspection firewalls, including policy execution and enforcement, intelligent protection, traffic filtering, network monitoring, communication protocol management, etc. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Key Characteristics Of Stateful Inspection Firewalls This template helps you present information on Six stages. You can also present information on Advanced Authentication, Packet Filtering using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
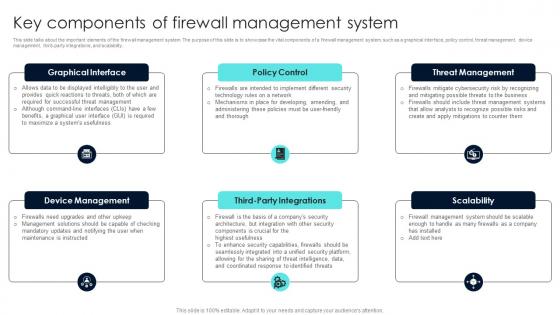 Firewall Network Security Key Components Of Firewall Management System
Firewall Network Security Key Components Of Firewall Management SystemThis slide talks about the important elements of the firewall management system. The purpose of this slide is to showcase the vital components of a firewall management system, such as a graphical interface, policy control, threat management, device management, third-party integrations, and scalability. Introducing Firewall Network Security Key Components Of Firewall Management System to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Access Service, Artificial Intelligence using this template. Grab it now to reap its full benefits.
-
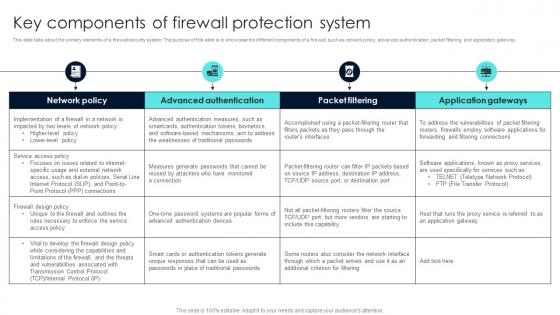 Firewall Network Security Key Components Of Firewall Protection System
Firewall Network Security Key Components Of Firewall Protection SystemThis slide talks about the primary elements of a firewall security system. The purpose of this slide is to showcase the different components of a firewall, such as network policy, advanced authentication, packet filtering, and application gateway. Present the topic in a bit more detail with this Firewall Network Security Key Components Of Firewall Protection System Use it as a tool for discussion and navigation on Misconfiguration, Software Vulnerabilities, Missing Firewall Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
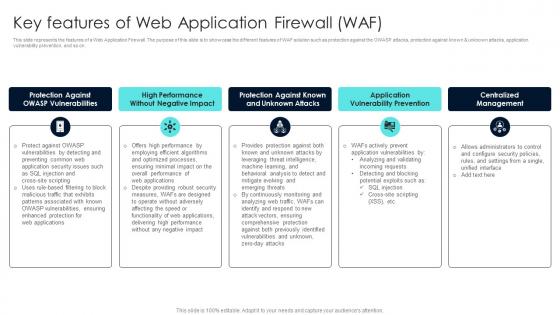 Firewall Network Security Key Features Of Web Application Firewall WAF
Firewall Network Security Key Features Of Web Application Firewall WAFThis slide represents the features of a Web Application Firewall. The purpose of this slide is to showcase the different features of WAF solution such as protection against the OWASP attacks, protection against known and unknown attacks, application vulnerability prevention, and so on. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Key Features Of Web Application Firewall WAF This template helps you present information on Five stages. You can also present information on Cisco Firepower, Bitdefender BOX using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
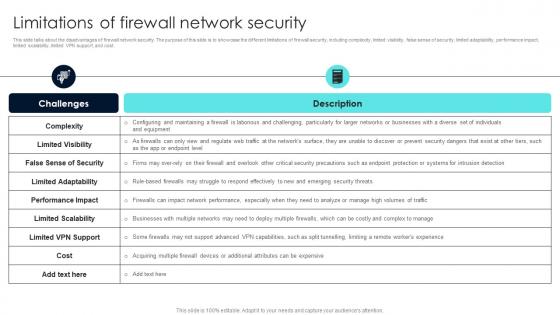 Firewall Network Security Limitations Of Firewall Network Security
Firewall Network Security Limitations Of Firewall Network SecurityThis slide talks about the disadvantages of firewall network security. The purpose of this slide is to showcase the different limitations of firewall security, including complexity, limited visibility, false sense of security, limited adaptability, performance impact, limited scalability, limited VPN support, and cost. Deliver an outstanding presentation on the topic using this Firewall Network Security Limitations Of Firewall Network Security Dispense information and present a thorough explanation of Techniques, Features, Security Benefits using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
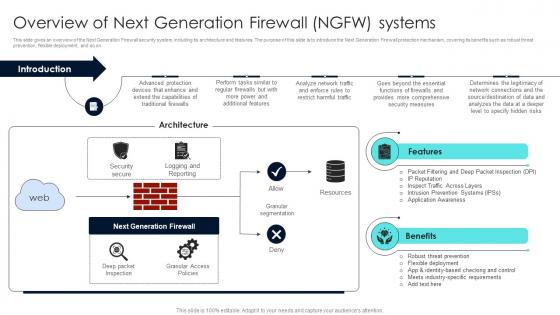 Firewall Network Security Overview Of Next Generation Firewall NGFW Systems
Firewall Network Security Overview Of Next Generation Firewall NGFW SystemsThis slide gives an overview of the Next Generation Firewall security system, including its architecture and features. The purpose of this slide is to introduce the Next Generation Firewall protection mechanism, covering its benefits such as robust threat prevention, flexible deployment, and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Overview Of Next Generation Firewall NGFW Systems Dispense information and present a thorough explanation of Architecture, Internet, Dynamic Packet Filtering using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
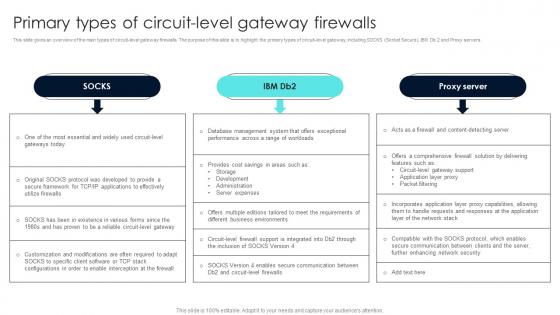 Firewall Network Security Primary Types Of Circuit Level Gateway Firewalls
Firewall Network Security Primary Types Of Circuit Level Gateway FirewallsThis slide gives an overview of the main types of circuit-level gateway firewalls. The purpose of this slide is to highlight the primary types of circuit-level gateway, including SOCKS Socket Secure, IBM Db 2 and Proxy servers. Introducing Firewall Network Security Primary Types Of Circuit Level Gateway Firewalls to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Pros, Cons, Availability, Costs using this template. Grab it now to reap its full benefits.
-
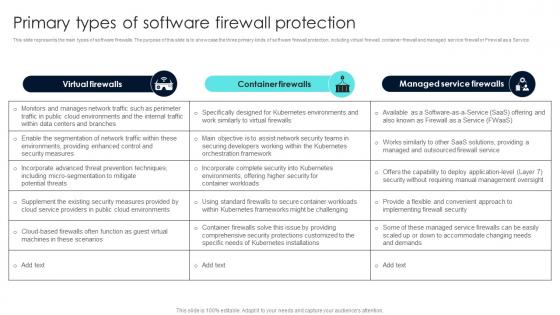 Firewall Network Security Primary Types Of Software Firewall Protection
Firewall Network Security Primary Types Of Software Firewall ProtectionThis slide represents the main types of software firewalls. The purpose of this slide is to showcase the three primary kinds of software firewall protection, including virtual firewall, container firewall and managed service firewall or Firewall as a Service. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Primary Types Of Software Firewall Protection This template helps you present information on Three stages. You can also present information on Advantages, Disadvantages using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
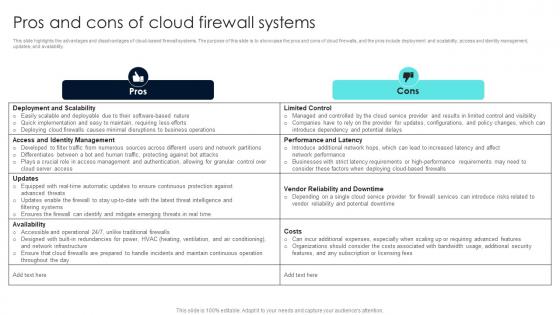 Firewall Network Security Pros And Cons Of Cloud Firewall Systems
Firewall Network Security Pros And Cons Of Cloud Firewall SystemsThis slide highlights the advantages and disadvantages of cloud-based firewall systems. The purpose of this slide is to showcase the pros and cons of cloud firewalls, and the pros include deployment and scalability, access and identity management, updates, and availability. Introducing Firewall Network Security Pros And Cons Of Cloud Firewall Systems to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Pros, Cons, Speed, Embedded Malware using this template. Grab it now to reap its full benefits.
-
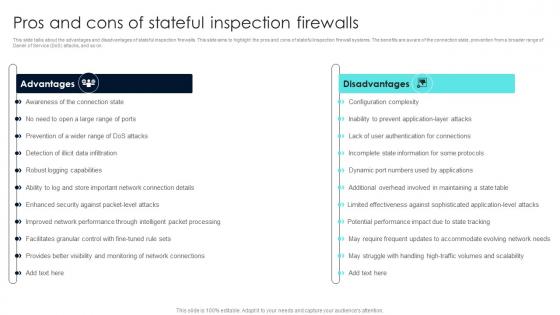 Firewall Network Security Pros And Cons Of Stateful Inspection Firewalls
Firewall Network Security Pros And Cons Of Stateful Inspection FirewallsThis slide talks about the advantages and disadvantages of stateful inspection firewalls. This slide aims to highlight the pros and cons of stateful inspection firewall systems. The benefits are aware of the connection state, prevention from a broader range of Daniel of Service DoS attacks, and so on. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Pros And Cons Of Stateful Inspection Firewalls This template helps you present information on Two stages. You can also present information on Corporate Networks, Government Organizations, Service Providers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
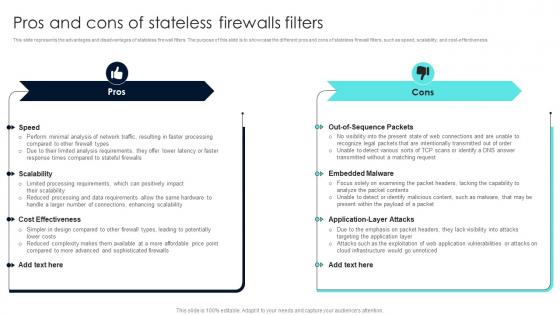 Firewall Network Security Pros And Cons Of Stateless Firewalls Filters
Firewall Network Security Pros And Cons Of Stateless Firewalls FiltersThis slide represents the advantages and disadvantages of stateless firewall filters. The purpose of this slide is to showcase the different pros and cons of stateless firewall filters, such as speed, scalability, and cost-effectiveness. Introducing Firewall Network Security Pros And Cons Of Stateless Firewalls Filters to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Monitor, Maintain, And Update, Rules And Policies using this template. Grab it now to reap its full benefits.
-
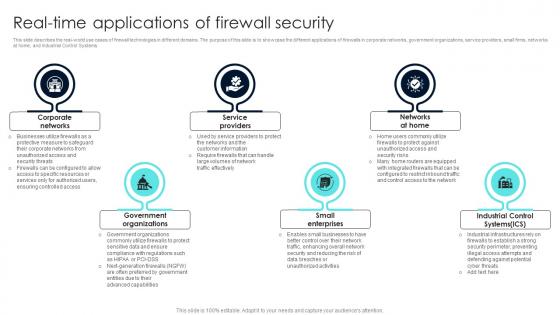 Firewall Network Security Real Time Applications Of Firewall Security
Firewall Network Security Real Time Applications Of Firewall SecurityThis slide describes the real-world use cases of firewall technologies in different domains. The purpose of this slide is to showcase the different applications of firewalls in corporate networks, government organizations, service providers, small firms, networks at home, and Industrial Control Systems. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Real Time Applications Of Firewall Security This template helps you present information on Six stages. You can also present information on Boundary Enforcement, Network Traffic, Improved Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
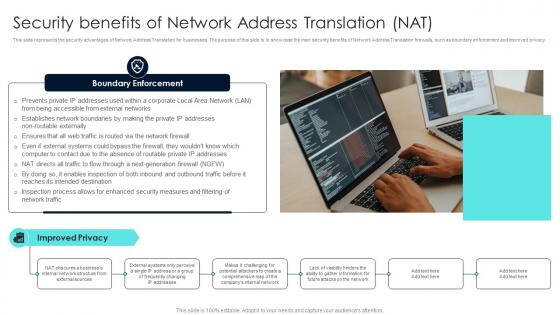 Firewall Network Security Security Benefits Of Network Address Translation NAT
Firewall Network Security Security Benefits Of Network Address Translation NATThis slide represents the security advantages of Network Address Translation for businesses. The purpose of this slide is to showcase the main security benefits of Network Address Translation firewalls, such as boundary enforcement and improved privacy. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Security Benefits Of Network Address Translation NAT This template helps you present information on One stages. You can also present information on Packet Filtering Router, Screened Host Firewalls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
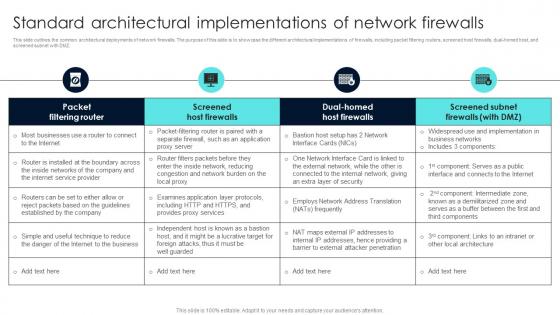 Firewall Network Security Standard Architectural Implementations Of Network Firewalls
Firewall Network Security Standard Architectural Implementations Of Network FirewallsThis slide outlines the common architectural deployments of network firewalls. The purpose of this slide is to showcase the different architectural implementations of firewalls, including packet filtering routers, screened host firewalls, dual-homed host, and screened subnet with DMZ. Present the topic in a bit more detail with this Firewall Network Security Standard Architectural Implementations Of Network Firewalls Use it as a tool for discussion and navigation on Access Control List, Workflow, Overview This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Benefits Of Cloud Access Security Broker 2 0 Next Generation CASB
Benefits Of Cloud Access Security Broker 2 0 Next Generation CASBThis slide represents the advantages of cloud access security broker version 2.0. The purpose of this slide is to highlight the main benefits of CASB 2.0, including comprehensive coverage, cost-effectiveness, enhanced security efficacy, improved visibility, app database, and so on. Introducing Benefits Of Cloud Access Security Broker 2 0 Next Generation CASB to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Comprehensive Coverage, Cost Effective, Improved Visibility using this template. Grab it now to reap its full benefits.
-
 Benefits Of Cloud Access Security Broker Next Generation CASB
Benefits Of Cloud Access Security Broker Next Generation CASBThis slide outlines the different advantages of cloud access security broker technology. This slide highlights the pros of CASB technology, including risk visibility, cyber threat prevention, granular cloud usage control, shadow IT assessment and management, DLP, managing privileged accounts and admin and controlled data sharing. Present the topic in a bit more detail with this Benefits Of Cloud Access Security Broker Next Generation CASB Use it as a tool for discussion and navigation on Risk Visibility, Threat Prevention, Assessment And Management This template is free to edit as deemed fit for your organization. Therefore download it now.
-
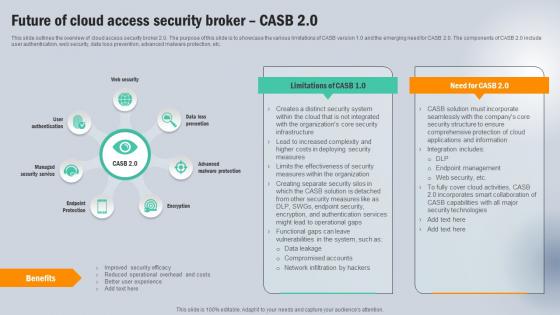 Future Of Cloud Access Security Broker CASB 2 0 Next Generation CASB
Future Of Cloud Access Security Broker CASB 2 0 Next Generation CASBThis slide outlines the overview of cloud access security broker 2.0. The purpose of this slide is to showcase the various limitations of CASB version 1.0 and the emerging need for CASB 2.0. The components of CASB 2.0 include user authentication, web security, data loss prevention, advanced malware protection, etc. Introducing Future Of Cloud Access Security Broker CASB 2 0 Next Generation CASB to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Endpoint Protection, Encryption, Benefits using this template. Grab it now to reap its full benefits.
-
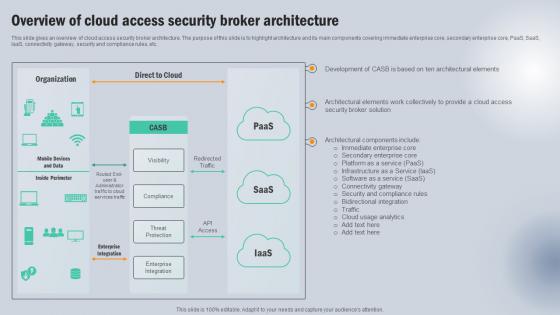 Overview Of Cloud Access Security Broker Architecture Next Generation CASB
Overview Of Cloud Access Security Broker Architecture Next Generation CASBThis slide gives an overview of cloud access security broker architecture. The purpose of this slide is to highlight architecture and its main components covering immediate enterprise core, secondary enterprise core, PaaS, SaaS, IaaS, connectivity gateway, security and compliance rules, etc. Present the topic in a bit more detail with this Overview Of Cloud Access Security Broker Architecture Next Generation CASB Use it as a tool for discussion and navigation on Organization, Direct To Cloud, Broker Architecture This template is free to edit as deemed fit for your organization. Therefore download it now.
-
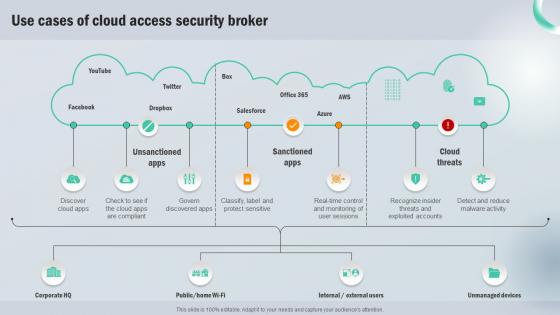 Use Cases Of Cloud Access Security Broker Next Generation CASB
Use Cases Of Cloud Access Security Broker Next Generation CASBPresent the topic in a bit more detail with this Use Cases Of Cloud Access Security Broker Next Generation CASB Use it as a tool for discussion and navigation on Unsanctioned Apps, Sanctioned Apps, Cloud Threats This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Cyber Safety Security Measures Implementing Cyber Risk Management Process
Impact Of Cyber Safety Security Measures Implementing Cyber Risk Management ProcessThe following slide depicts the projected consequences of implementing cyber security preventive measures. It includes data about number of cyber attracts pre and post adopting latest strategies. Present the topic in a bit more detail with this Impact Of Cyber Safety Security Measures Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Cyber Attack Type, Remarks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Cyber Security Policies And Practices Implementing Cyber Risk Management Process
Impact Of Cyber Security Policies And Practices Implementing Cyber Risk Management ProcessThe following slide focuses on drafting cyber security policies to manage data control and breach. It mainly includes elements such as impact of existing cyber safety policies, mitigation actions. Deliver an outstanding presentation on the topic using this Impact Of Cyber Security Policies And Practices Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Inadequate Security Guidelines, Inappropriate Privacy Policies, Insufficient Background Check using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
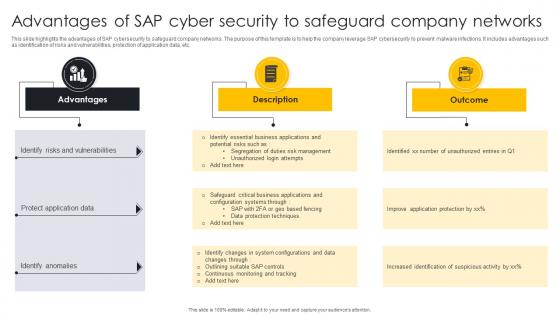 Advantages Of SAP Cyber Security To Safeguard Company Networks
Advantages Of SAP Cyber Security To Safeguard Company NetworksThis slide highlights the advantages of SAP cybersecurity to safeguard company networks. The purpose of this template is to help the company leverage SAP cybersecurity to prevent malware infections. It includes advantages such as identification of risks and vulnerabilities, protection of application data, etc. Presenting our set of slides with Advantages Of SAP Cyber Security To Safeguard Company Networks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify Risks And Vulnerabilities, Protect Application Data, Identify Anomalies.
-
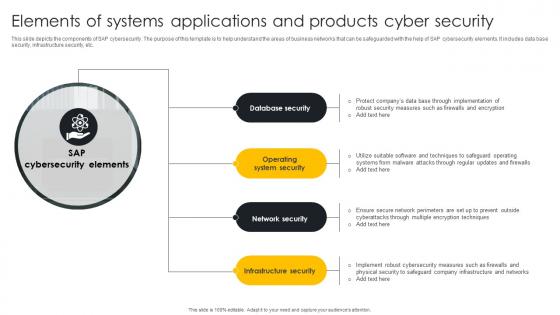 Elements Of Systems Applications And Products Cyber Security
Elements Of Systems Applications And Products Cyber SecurityThis slide depicts the components of SAP cybersecurity. The purpose of this template is to help understand the areas of business networks that can be safeguarded with the help of SAP cybersecurity elements. It includes data base security, infrastructure security, etc. Presenting our set of slides with Elements Of Systems Applications And Products Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Database Security, Operating System Security, Network Security, Infrastructure Security.
-
 Product Services Offered By SAP Security Solutions
Product Services Offered By SAP Security SolutionsThis template showcases the SAP product services offered by the organization. The purpose of this slide is to help the business ensure it utilizes suitable services in order to meet its business needs. It includes services such as SAP cloud identity access governance, SAP enterprise detection, etc. Introducing our premium set of slides with Product Services Offered By SAP Security Solutio. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like SAPenterprise Detections, SAP Data Custodian, Streamlining Governance Procedures. So download instantly and tailor it with your information.
-
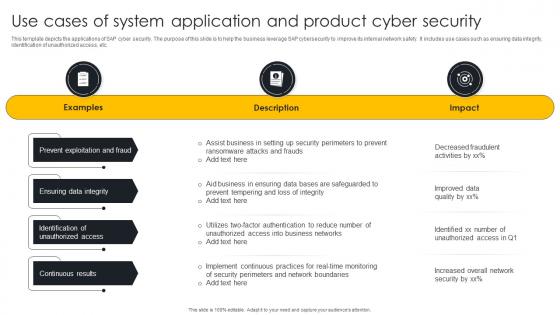 Use Cases Of System Application And Product Cyber Security
Use Cases Of System Application And Product Cyber SecurityThis template depicts the applications of SAP cyber security. The purpose of this slide is to help the business leverage SAP cybersecurity to improve its internal network safety. It includes use cases such as ensuring data integrity, identification of unauthorized access, etc. Presenting our well structured Use Cases Of System Application And Product Cyber Security. The topics discussed in this slide are Prevent Exploitation And Fraud, Ensuring Data Integrity, Continuous Results. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
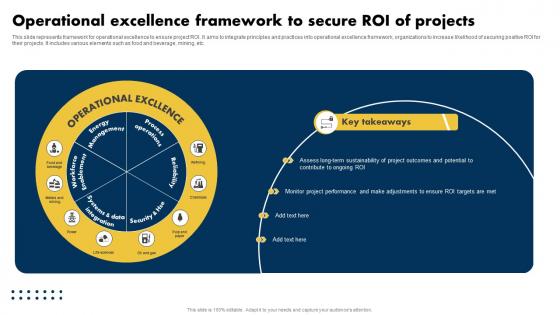 Operational Excellence Framework To Secure Roi Of Projects
Operational Excellence Framework To Secure Roi Of ProjectsThis slide represents framework for operational excellence to ensure project ROI. It aims to integrate principles and practices into operational excellence framework, organizations to increase likelihood of securing positive ROI for their projects. It includes various elements such as food and beverage, mining, etc. Presenting our well structured Operational Excellence Framework To Secure Roi Of Projects. The topics discussed in this slide are Excellence, Secure, Projects. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
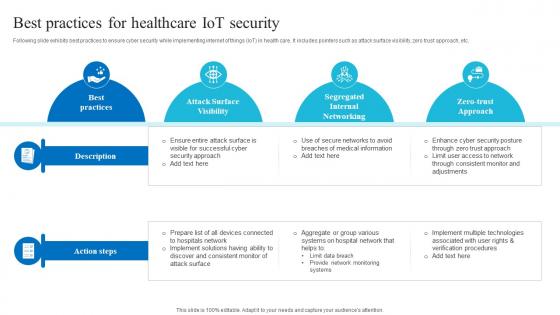 Best For Healthcare Iot Security Role Of Iot And Technology In Healthcare Industry IoT SS V
Best For Healthcare Iot Security Role Of Iot And Technology In Healthcare Industry IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Deliver an outstanding presentation on the topic using this Best For Healthcare Iot Security Role Of Iot And Technology In Healthcare Industry IoT SS V. Dispense information and present a thorough explanation of Attack Surface Visibility, Segregated Internal Networking, Zero Trust Approach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Stages Of Cyber Security And Compliance Automation
Stages Of Cyber Security And Compliance AutomationThis slide represents stages of cyber security and compliance automation which assists in cyber risk and policy adherence. It includes stages of cyber security and compliance automation such as initial, developing, define, etc. Presenting our set of slides with name Stages Of Cyber Security And Compliance Automation. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Stages Of Cyber Security, Compliance Automation, Developing, Risk And Policy Adherence.
-
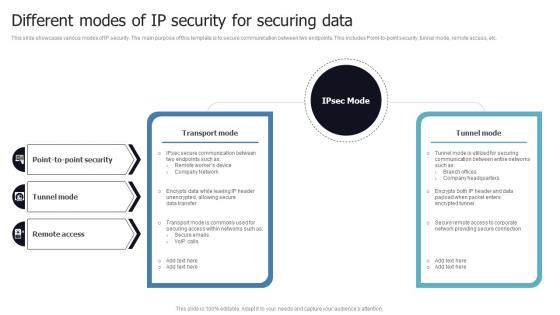 Different Modes Of IP Security For Securing Data
Different Modes Of IP Security For Securing DataThis slide showcases various modes of IP security. The main purpose of this template is to secure communication between two endpoints. This includes Point-to-point security, tunnel mode, remote access, etc. Introducing our Different Modes Of IP Security For Securing Data set of slides. The topics discussed in these slides are IP Security, Secure Communication, Point To Point Security, Tunnel Mode. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
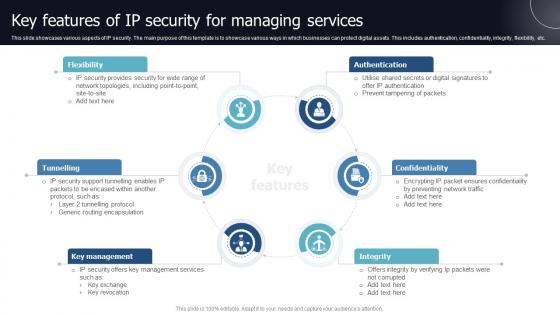 Key Features Of IP Security For Managing Services
Key Features Of IP Security For Managing ServicesThis slide showcases various aspects of IP security. The main purpose of this template is to showcase various ways in which businesses can protect digital assets. This includes authentication, confidentiality, integrity, flexibility, etc. Introducing our premium set of slides with name Key Features Of IP Security For Managing Services. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Authentication, Confidentiality, Key Management, Tunnelling, Flexibility. So download instantly and tailor it with your information.
-
 Major Components Of IP Security To Protect Sensitive Data
Major Components Of IP Security To Protect Sensitive DataThis slide showcases key elements of IP security for protecting data. The main purpose of this template is to showcase protection and trustworthiness of data. This includes encapsulating security payload, authentication header, and internet key exchange. Presenting our set of slides with name Major Components Of IP Security To Protect Sensitive Data. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Internet Key Exchange, Authentication Header, Encapsulating Security Payload.
-
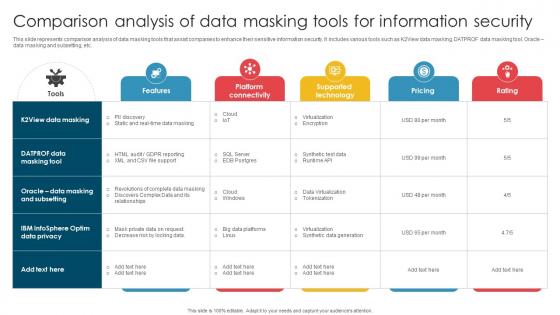 Comparison Analysis Of Data Masking Tools For Information Security
Comparison Analysis Of Data Masking Tools For Information SecurityThis slide represents comparison analysis of data masking tools that assist companies to enhance their sensitive information security. It includes various tools such as K2View data masking, DATPROF data masking tool, Oracle data masking and subsetting, etc. Presenting our well structured Comparison Analysis Of Data Masking Tools For Information Security. The topics discussed in this slide are Virtualization, Synthetic Data Generation, Tokenization. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Incident Response Report Documentation Of Security Department
Incident Response Report Documentation Of Security DepartmentThis slide showcases incident response document that assist security department in maintaining compliance within operations. It further covers name, date of incident, report, email, location of incident and incident description, etc. Presenting our well structured Incident Response Report Documentation Of Security Department. The topics discussed in this slide are Action Taken, Systems Affected, Method Of Detection. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
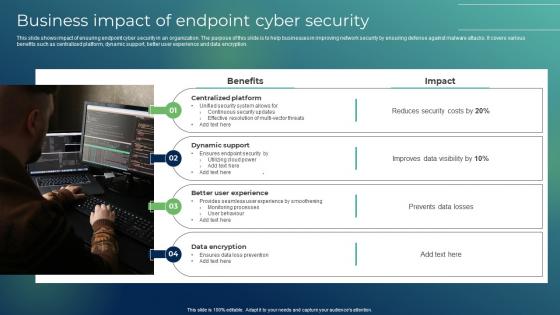 Business Impact Of Endpoint Cyber Security
Business Impact Of Endpoint Cyber SecurityThis slide shows impact of ensuring endpoint cyber security in an organization. The purpose of this slide is to help businesses in improving network security by ensuring defense against malware attacks. It covers various benefits such as centralized platform, dynamic support, better user experience and data encryption. Presenting our set of slides with Business Impact Of Endpoint Cyber Security This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Centralized Platform, Dynamic Support, Better User Experience
-
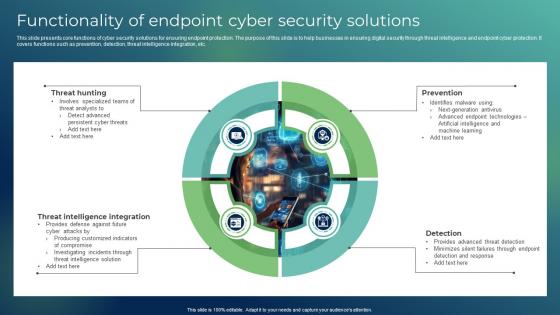 Functionality Of Endpoint Cyber Security Solutions
Functionality Of Endpoint Cyber Security SolutionsThis slide presents core functions of cyber security solutions for ensuring endpoint protection. The purpose of this slide is to help businesses in ensuring digital security through threat intelligence and endpoint cyber protection. It covers functions such as prevention, detection, threat intelligence integration, etc. Presenting our well structured Functionality Of Endpoint Cyber Security Solutions The topics discussed in this slide are Threat Hunting, Threat Intelligence Integration, Prevention This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
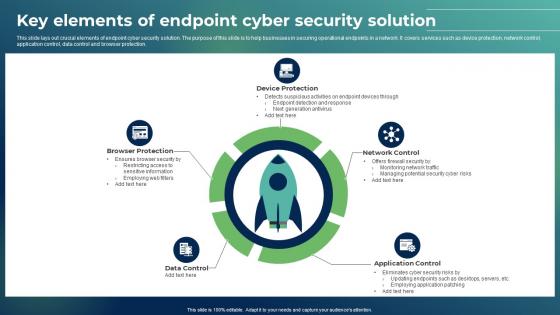 Key Elements Of Endpoint Cyber Security Solution
Key Elements Of Endpoint Cyber Security SolutionThis slide lays out crucial elements of endpoint cyber security solution. The purpose of this slide is to help businesses in securing operational endpoints in a network. It covers services such as device protection, network control, application control, data control and browser protection. Presenting our set of slides with Key Elements Of Endpoint Cyber Security Solution This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Browser Protection, Device Protection, Network Control
-
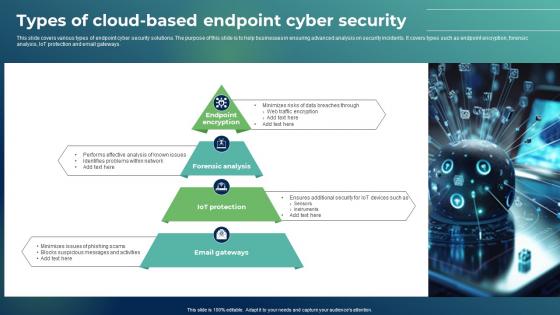 Types Of Cloud Based Endpoint Cyber Security
Types Of Cloud Based Endpoint Cyber SecurityThis slide covers various types of endpoint cyber security solutions. The purpose of this slide is to help businesses in ensuring advanced analysis on security incidents. It covers types such as endpoint encryption, forensic analysis, IoT protection and email gateways. Presenting our well structured Types Of Cloud Based Endpoint Cyber Security The topics discussed in this slide are Forensic Analysis, Iot Protection, Email Gateways This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
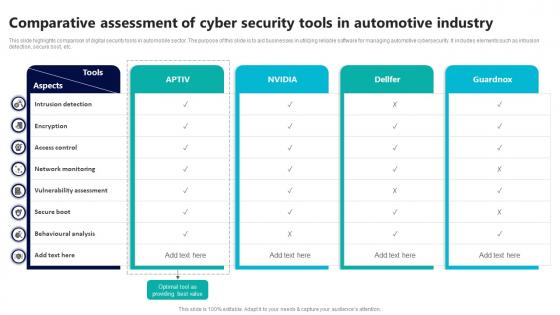 Comparative Assessment Of Cyber Security Tools In Automotive Industry
Comparative Assessment Of Cyber Security Tools In Automotive IndustryThis slide highlights comparison of digital security tools in automobile sector. The purpose of this slide is to aid businesses in utilizing reliable software for managing automotive cybersecurity. It includes elements such as intrusion detection, secure boot, etc. Introducing our Comparative Assessment Of Cyber Security Tools In Automotive Industry set of slides. The topics discussed in these slides are Intrusion Detection, Access Control, Network Monitoring This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon For Role Of 5g Technology In Automotive Cyber Security
Icon For Role Of 5g Technology In Automotive Cyber SecurityIntroducing our premium set of slides with Icon For Role Of 5g Technology In Automotive Cyber Security Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon For Role, 5G Technology In Automotive, Cyber Security So download instantly and tailor it with your information.
-
 Icon For Utilization Of Blockchain In Automotive Cyber Security
Icon For Utilization Of Blockchain In Automotive Cyber SecurityPresenting our set of slides with Icon For Utilization Of Blockchain In Automotive Cyber Security This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon For Utilization, Blockchain In Automotive, Cyber Security
-
 Impact Analysis Of Cyber Security Threats In Automotive Industry
Impact Analysis Of Cyber Security Threats In Automotive IndustryThis slide highlights influence assessment cyber security risks in automobile industry. The purpose of this slide is to aid businesses in evaluating potential consequences of digital factors. It includes elements such as data privacy, supply chain disruption, etc. Introducing our premium set of slides with Impact Analysis Of Cyber Security Threats In Automotive Industry Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Privacy, Intellectual Property, Supply Chain Disruption So download instantly and tailor it with your information.
-
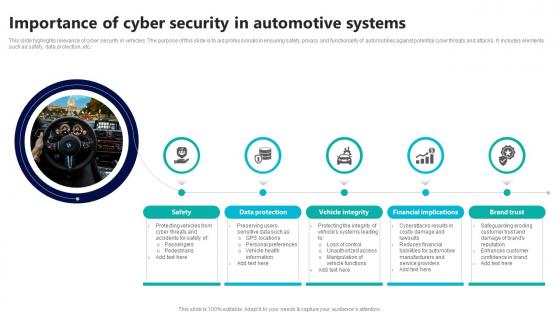 Importance Of Cyber Security In Automotive Systems
Importance Of Cyber Security In Automotive SystemsThis slide highlights relevance of cyber security in vehicles. The purpose of this slide is to aid professionals in ensuring safety, privacy and functionality of automobiles against potential cyber threats and attacks. It includes elements such as safety, data protection, etc. Presenting our set of slides with Importance Of Cyber Security In Automotive Systems This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Vehicle Integrity, Financial Implications.
-
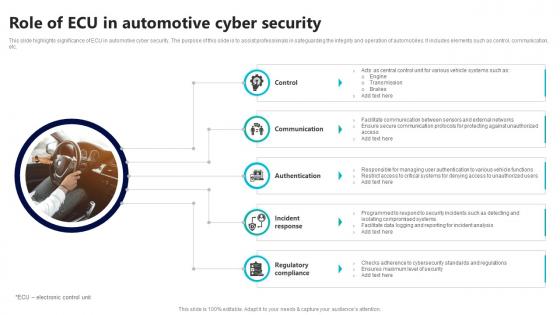 Role Of Ecu In Automotive Cyber Security
Role Of Ecu In Automotive Cyber SecurityThis slide highlights significance of ECU in automotive cyber security. The purpose of this slide is to assist professionals in safeguarding the integrity and operation of automobiles. It includes elements such as control, communication, etc. Presenting our set of slides with Role Of Ecu In Automotive Cyber Security This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Communication, Authentication, Incident Response
-
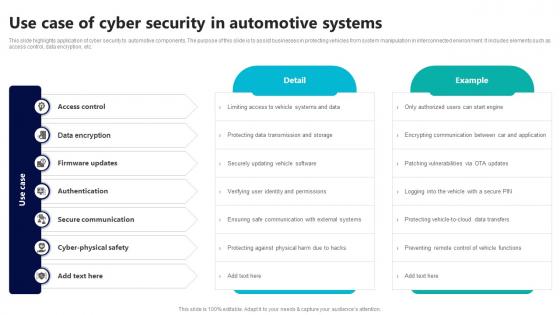 Use Case Of Cyber Security In Automotive Systems
Use Case Of Cyber Security In Automotive SystemsThis slide highlights application of cyber security to automotive components. The purpose of this slide is to assist businesses in protecting vehicles from system manipulation in interconnected environment. It includes elements such as access control, data encryption, etc. Introducing our premium set of slides with Use Case Of Cyber Security In Automotive Systems Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Control, Data Encryption, Firmware Updates So download instantly and tailor it with your information.
-
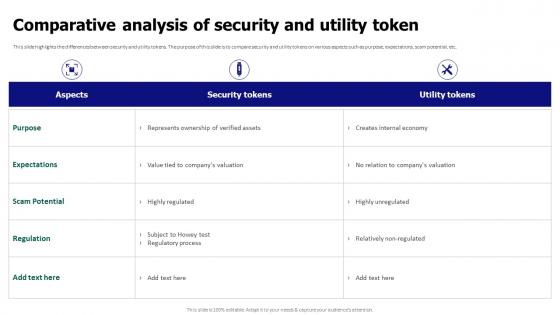 Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security
Comparative Analysis Of Security And Utility Token Tokenization For Improved Data SecurityThis slide highlights the differences between security and utility tokens. The purpose of this slide is to compare security and utility tokens on various aspects such as purpose, expectations, scam potential, etc. Present the topic in a bit more detail with this Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security. Use it as a tool for discussion and navigation on Comparative Analysis, Security And Utility Token, Expectations, Scam Potential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
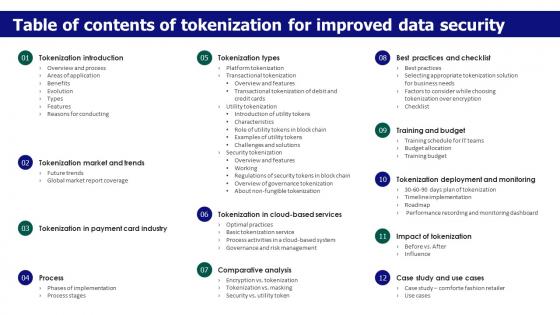 Table Of Contents Of Tokenization For Improved Data Security
Table Of Contents Of Tokenization For Improved Data SecurityIncrease audience engagement and knowledge by dispensing information using Table Of Contents Of Tokenization For Improved Data Security. This template helps you present information on twelve stages. You can also present information on Data Security, Tokenization Market And Trends, Comparative Analysis, Training And Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
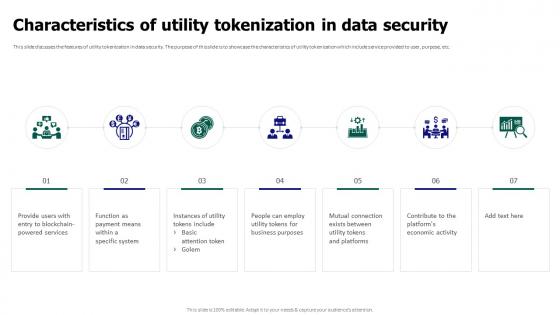 Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security
Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data SecurityThis slide discusses the features of utility tokenization in data security. The purpose of this slide is to showcase the characteristics of utility tokenization which include service provided to user, purpose, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security. This template helps you present information on seven stages. You can also present information on Utility Tokenization, Data Security, Platforms Economic Activity, Blockchain Powered Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
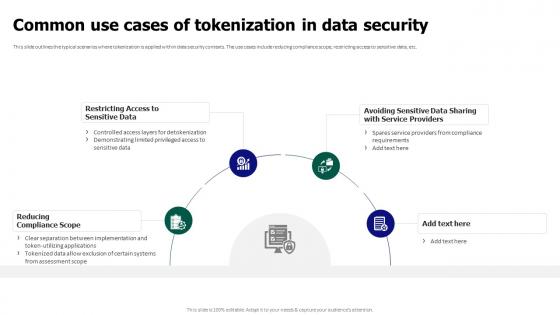 Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data Security
Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data SecurityThis slide outlines the typical scenarios where tokenization is applied within data security contexts. The use cases include reducing compliance scope, restricting access to sensitive data, etc. Introducing Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Restricting Access To Sensitive Data, Reducing Compliance Scope, Tokenization In Data Security, using this template. Grab it now to reap its full benefits.
-
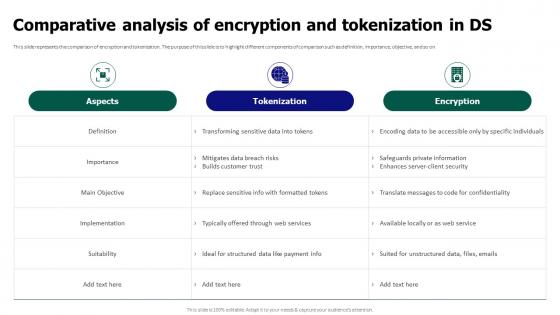 Tokenization For Improved Data Security Comparative Analysis Of Encryption And Tokenization In Ds
Tokenization For Improved Data Security Comparative Analysis Of Encryption And Tokenization In DsThis slide represents the comparison of encryption and tokenization. The purpose of this slide is to highlight different components of comparison such as definition, importance, objective, and so on. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Comparative Analysis Of Encryption And Tokenization In Ds. Dispense information and present a thorough explanation of Comparative Analysis, Encryption And Tokenization, Safeguards Private Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
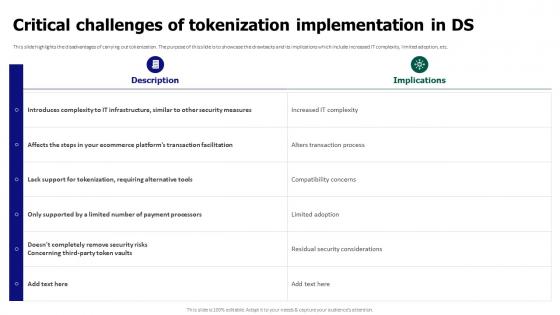 Tokenization For Improved Data Security Critical Challenges Of Tokenization Implementation In Ds
Tokenization For Improved Data Security Critical Challenges Of Tokenization Implementation In DsThis slide highlights the disadvantages of carrying out tokenization. The purpose of this slide is to showcase the drawbacks and its implications which include increased IT complexity, limited adoption, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Critical Challenges Of Tokenization Implementation In Ds. Use it as a tool for discussion and navigation on Critical Challenges, Tokenization Implementation, Alters Transaction Process, Compatibility Concerns. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
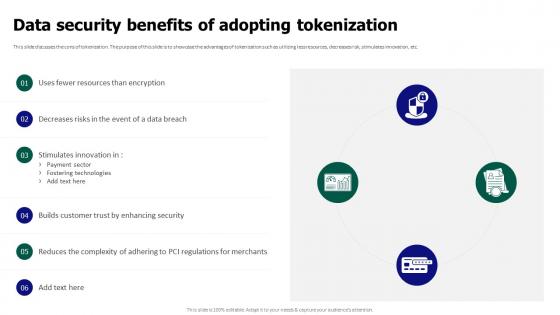 Tokenization For Improved Data Security Data Security Benefits Of Adopting Tokenization
Tokenization For Improved Data Security Data Security Benefits Of Adopting TokenizationThis slide discusses the cons of tokenization. The purpose of this slide is to showcase the advantages of tokenization such as utilizing less resources, decreases risk, stimulates innovation, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Data Security Benefits Of Adopting Tokenization. Dispense information and present a thorough explanation of Builds Customer Trust, Data Security Benefits, Adopting Tokenization, Fostering Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
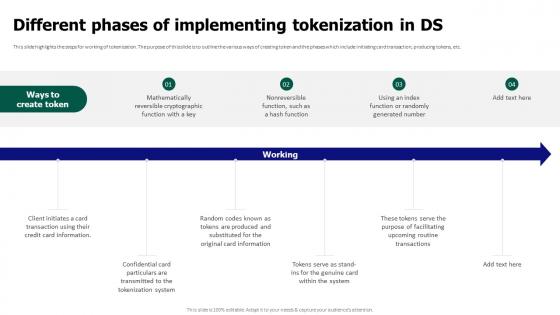 Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In Ds
Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In DsThis slide highlights the steps for working of tokenization. The purpose of this slide is to outline the various ways of creating token and the phases which include initiating card transaction, producing tokens, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In Ds. This template helps you present information on six stages. You can also present information on Mathematically Reversible, Cryptographic Function, Producing Tokens using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Evolution Of Tokenization From Ancient Times To Modern Era
Tokenization For Improved Data Security Evolution Of Tokenization From Ancient Times To Modern EraThis slide outlines the history of tokenization. The purpose of this slide is to showcase the years of evolution such as 1970s digital tokenization, data compliance in 2001, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Evolution Of Tokenization From Ancient Times To Modern Era. Use it as a tool for discussion and navigation on Evolution Of Tokenization, Tokenization Recently Secured, Payment Card Data Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tokenization For Improved Data Security For Table Of Contents
Tokenization For Improved Data Security For Table Of ContentsPresent the topic in a bit more detail with this Tokenization For Improved Data Security For Table Of Contents. Use it as a tool for discussion and navigation on Overview And Process, Areas Of Application, Reasons For Conducting. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
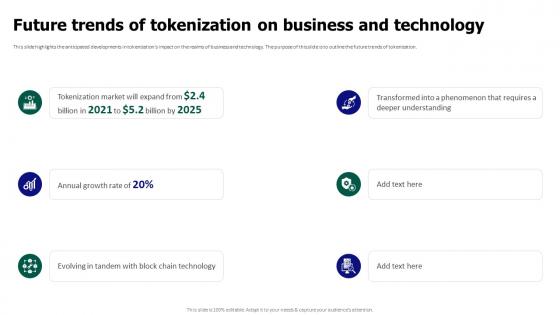 Tokenization For Improved Data Security Future Trends Of Tokenization On Business And Technology
Tokenization For Improved Data Security Future Trends Of Tokenization On Business And TechnologyThis slide highlights the anticipated developments in tokenizations impact on the realms of business and technology. The purpose of this slide is to outline the future trends of tokenization. Introducing Tokenization For Improved Data Security Future Trends Of Tokenization On Business And Technology to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Anticipated Developments, Business And Technology, Future Trends Of Tokenization, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Impact Of Tokenization On Different Industries
Tokenization For Improved Data Security Impact Of Tokenization On Different IndustriesThis slide showcases the after tokenization impact on data security. It highlights the various factors that have improved the overall security by reducing time of release, rapid defect detection, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Impact Of Tokenization On Different Industries. This template helps you present information on six stages. You can also present information on Tokenization, Data Security, Rapid Defect Detection, Ensuring Trust And Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Introduction Of Utility Token In Data Security
Tokenization For Improved Data Security Introduction Of Utility Token In Data SecurityThis slide showcases the overview of utility tokens in data security. The purpose of this slide is to discuss the introduction of utility tokens required for data security and preventing thefts. Introducing Tokenization For Improved Data Security Introduction Of Utility Token In Data Security to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Data Security, Utility Tokens, Preventing Thefts, Unique To Each Platform, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Key Applications And Use Cases Of Tokenization
Tokenization For Improved Data Security Key Applications And Use Cases Of TokenizationThis slide discusses various application fields of tokenization. The purpose of this slide is to highlight the areas of application which include mobile wallet services, online retail platforms, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Key Applications And Use Cases Of Tokenization. This template helps you present information on three stages. You can also present information on Mobile Wallet Services, Online Retail Platforms, Businesses Storing Customer, Card Data Securely using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.




