Powerpoint Templates and Google slides for Security Privacy
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 IoT Security And Privacy Safeguarding The Digital Ecosystem Powerpoint Presentation Slides IoT CD
IoT Security And Privacy Safeguarding The Digital Ecosystem Powerpoint Presentation Slides IoT CDDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this IoT Security And Privacy Safeguarding The Digital Ecosystem Powerpoint Presentation Slides IoT CD is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the seventy six slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Security And Privacy Powerpoint Ppt Template Bundles
Security And Privacy Powerpoint Ppt Template BundlesIntroduce your topic and host expert discussion sessions with this Security And Privacy Powerpoint Ppt Template Bundles. This template is designed using high-quality visuals, images, graphics, etc, that can be used to showcase your expertise. Different topics can be tackled using the nineteen slides included in this template. You can present each topic on a different slide to help your audience interpret the information more effectively. Apart from this, this PPT slideshow is available in two screen sizes, standard and widescreen making its delivery more impactful. This will not only help in presenting a birds-eye view of the topic but also keep your audience engaged. Since this PPT slideshow utilizes well-researched content, it induces strategic thinking and helps you convey your message in the best possible manner. The biggest feature of this design is that it comes with a host of editable features like color, font, background, etc. So, grab it now to deliver a unique presentation every time.
-
 Data Privacy Management For Cyber Security Training Ppt
Data Privacy Management For Cyber Security Training PptPresenting Data Privacy Management for Cyber Security. Each slide is well crafted and designed by our PowerPoint experts. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Not just this, you can also make the required changes in the charts and graphs. Download this professionally designed business presentation, add your content and present it with confidence.
-
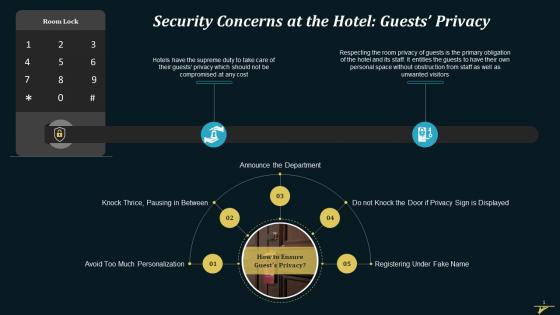 Security Concern Of Guests Privacy At A Hotel Training Ppt
Security Concern Of Guests Privacy At A Hotel Training PptPresenting Security Concern of Guests Privacy at a Hotel . This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizablealter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
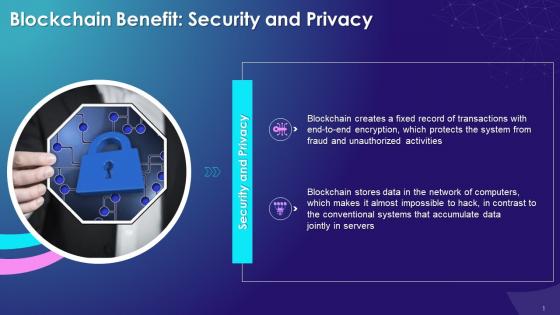 Security And Privacy Benefit Of Blockchain Technology Training Ppt
Security And Privacy Benefit Of Blockchain Technology Training PptPresenting Security and Privacy Benefit of Blockchain Technology. This slide is well crafted and designed by our PowerPoint specialists. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. You can add or delete the content as per your need.
-
 Privacy And Security Concerns In Metaverse Training Ppt
Privacy And Security Concerns In Metaverse Training PptPresenting Privacy and Security Concerns in Metaverse. These slides are 100 percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
 Privacy And Data Security As A Major Challenge To Metaverse Training Ppt
Privacy And Data Security As A Major Challenge To Metaverse Training PptPresenting Privacy and Data Security as a Major Challenge to Metaverse. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
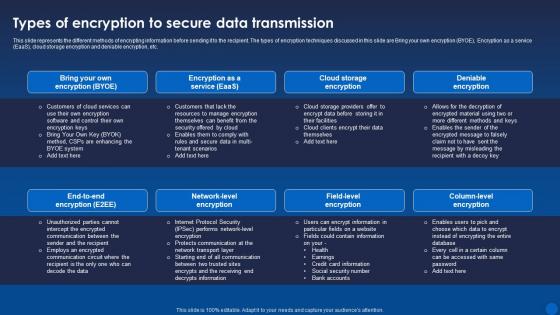 Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It
Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age ItThis slide represents the different methods of encrypting information before sending it to the recipient. The types of encryption techniques discussed in this slide are Bring your own encryption BYOE, Encryption as a service EaaS, cloud storage encryption and deniable encryption, etc. Present the topic in a bit more detail with this Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Data Transmission, Encryption, Deniable Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
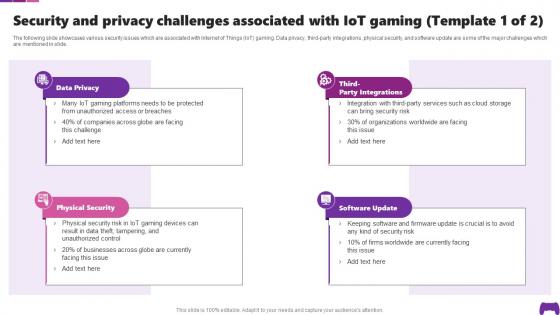 Security And Privacy Challenges Associated With IoT Transforming Future Of Gaming IoT SS
Security And Privacy Challenges Associated With IoT Transforming Future Of Gaming IoT SSThe following slide showcases various security issues which are associated with Internet of Things IoT gaming. Data privacy, third-party integrations, physical security, and software update are some of the major challenges which are mentioned in slide. Introducing Security And Privacy Challenges Associated With IoT Transforming Future Of Gaming IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Privacy, Physical Security, Software Update, using this template. Grab it now to reap its full benefits.
-
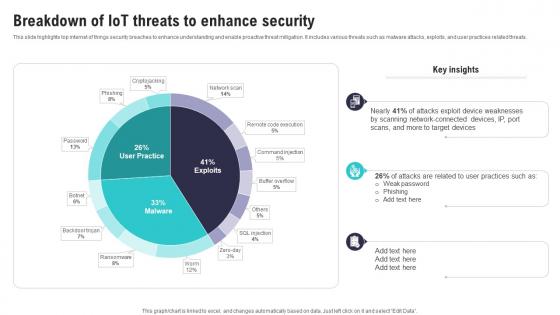 Breakdown Of IoT Threats To Enhance Security IoT Security And Privacy Safeguarding IoT SS
Breakdown Of IoT Threats To Enhance Security IoT Security And Privacy Safeguarding IoT SSThis slide highlights top internet of things security breaches to enhance understanding and enable proactive threat mitigation. It includes various threats such as malware attacks, exploits, and user practices related threats. Present the topic in a bit more detail with this Breakdown Of IoT Threats To Enhance Security IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Scanning Network Connected, Attacks Exploit, Device Weaknesses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
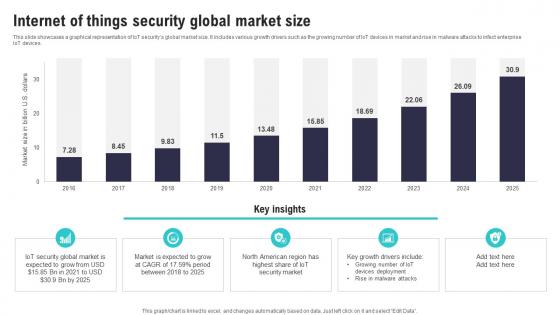 Internet Of Things Security Global Market Size IoT Security And Privacy Safeguarding IoT SS
Internet Of Things Security Global Market Size IoT Security And Privacy Safeguarding IoT SSThis slide showcases a graphical representation of IoT securitys global market size. It includes various growth drivers such as the growing number of IoT devices in market and rise in malware attacks to infect enterprise IoT devices.Deliver an outstanding presentation on the topic using this Internet Of Things Security Global Market Size IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Security Global Market, American Region, Rise Malware Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
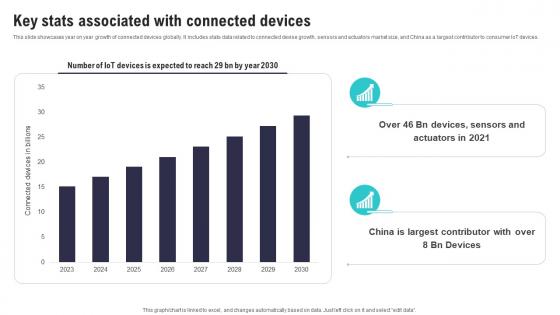 Key Stats Associated With Connected Devices IoT Security And Privacy Safeguarding IoT SS
Key Stats Associated With Connected Devices IoT Security And Privacy Safeguarding IoT SSThis slide showcases year on year growth of connected devices globally. It includes stats data related to connected devise growth, sensors and actuators market size, and China as a largest contributor to consumer IoT devices. Present the topic in a bit more detail with this Key Stats Associated With Connected Devices IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Largest Contributor, Associated Connected, Devices Expected. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS
Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS. This template helps you present information on five stages. You can also present information on Introduction Iot Security, Need Iot, Security Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
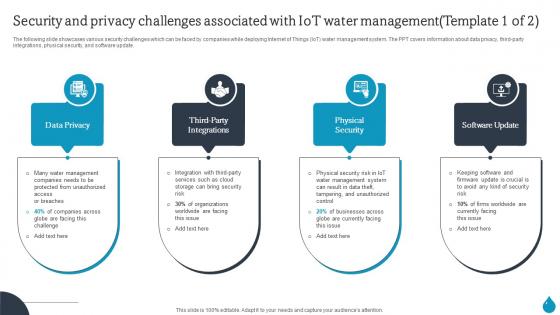 Smart Water Management Security And Privacy Challenges Associated With Iot Water Management IoT SS
Smart Water Management Security And Privacy Challenges Associated With Iot Water Management IoT SSThe following slide showcases various security challenges which can be faced by companies while deploying Internet of Things IoT water management system. The PPT covers information about data privacy, third-party integrations, physical security, and software update. Introducing Smart Water Management Security And Privacy Challenges Associated With Iot Water Management IoT SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Smart Water Management Key Benefits Of Using Iot In Water Management IoT SS using this template. Grab it now to reap its full benefits.
-
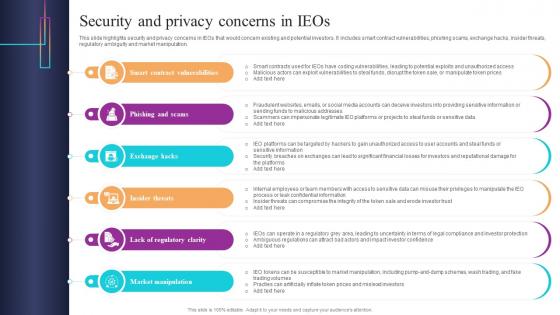 Security And Privacy Concerns In IEOs Introduction To Blockchain Based Initial BCT SS
Security And Privacy Concerns In IEOs Introduction To Blockchain Based Initial BCT SSThis slide highlights security and privacy concerns in IEOs that would concern existing and potential investors. It includes smart contract vulnerabilities, phishing scams, exchange hacks, insider threats, regulatory ambiguity and market manipulation. Introducing Security And Privacy Concerns In IEOs Introduction To Blockchain Based Initial BCT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Scams, Exchange, Market, using this template. Grab it now to reap its full benefits.
-
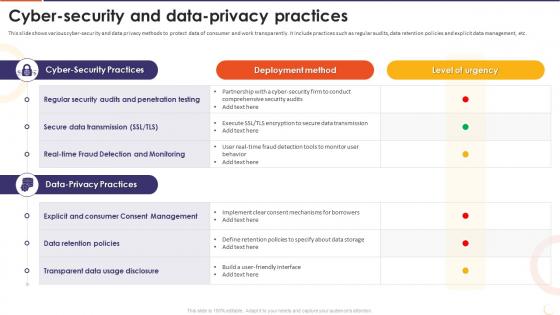 The Future Of Financing Digital Cyber Security And Data Privacy Practices
The Future Of Financing Digital Cyber Security And Data Privacy PracticesThis slide shows various cyber-security and data privacy methods to protect data of consumer and work transparently. It include practices such as regular audits, data retention policies and explicit data management, etc. Present the topic in a bit more detail with this The Future Of Financing Digital Cyber Security And Data Privacy Practices. Use it as a tool for discussion and navigation on Regular Security Audits, Penetration Testing, Secure Data Transmission, Data Retention Policies, Transparent Data Usage Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Privacy Secure In Powerpoint And Google Slides Cpb
Privacy Secure In Powerpoint And Google Slides CpbPresenting Privacy Secure In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Privacy Secure. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Security Privacy Issues Digital Marketing In Powerpoint And Google Slides Cpb
Security Privacy Issues Digital Marketing In Powerpoint And Google Slides CpbPresenting Security Privacy Issues Digital Marketing In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Privacy Issues Digital Marketing. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
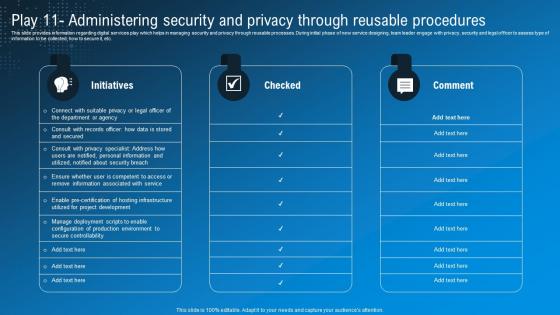
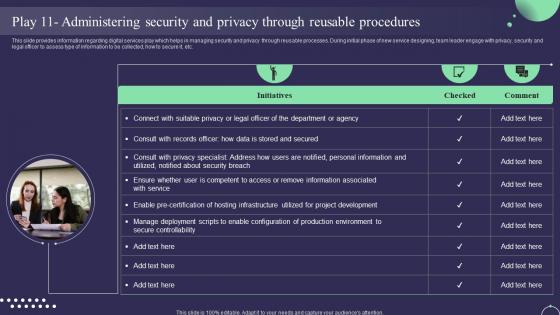 Play 11 Administering Security And Privacy Through Reusable Digital Service Management Playbook
Play 11 Administering Security And Privacy Through Reusable Digital Service Management PlaybookThis slide provides information regarding digital services play which helps in managing security and privacy through reusable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc. Present the topic in a bit more detail with this Play 11 Administering Security And Privacy Through Reusable Digital Service Management Playbook. Use it as a tool for discussion and navigation on Procedures, Administering, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
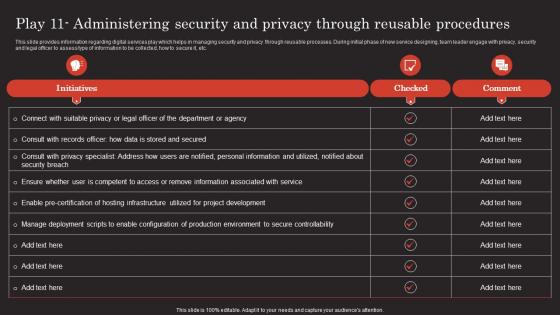
 Play 11 Administering Security And Privacy Through Leadership Playbook For Digital Transformation
Play 11 Administering Security And Privacy Through Leadership Playbook For Digital TransformationThis slide provides information regarding digital services play which helps in managing security and privacy through reusable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc. Present the topic in a bit more detail with this Play 11 Administering Security And Privacy Through Leadership Playbook For Digital Transformation. Use it as a tool for discussion and navigation on Procedures, Administering, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
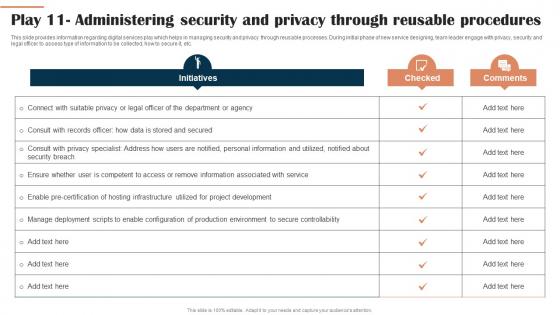
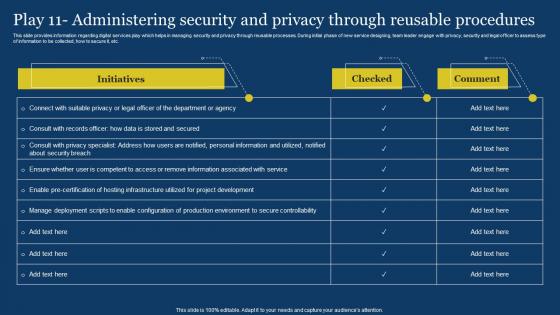 US Digital Services Management Play 11 Administering Security And Privacy Through ReUSable
US Digital Services Management Play 11 Administering Security And Privacy Through ReUSableThis slide provides information regarding digital services play which helps in managing security and privacy through reUSable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc. Deliver an outstanding presentation on the topic USing this US Digital Services Management Play 11 Administering Security And Privacy Through ReUSable Dispense information and present a thorough explanation of Department Or Agency, Secure Controllability USing the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Play 11 Administering Security And Privacy Through Reusable Modern Technology Stack Playbook
Play 11 Administering Security And Privacy Through Reusable Modern Technology Stack PlaybookThis slide provides information regarding digital services play which helps in managing security and privacy through reusable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc. Present the topic in a bit more detail with this Play 11 Administering Security And Privacy Through Reusable Modern Technology Stack Playbook. Use it as a tool for discussion and navigation on Security, Privacy, Procedures. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Play 11 Administering Security And Privacy Through Digital Hosting Environment Playbook
Play 11 Administering Security And Privacy Through Digital Hosting Environment PlaybookThis slide provides information regarding digital services play which helps in managing security and privacy through reusable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc. Deliver an outstanding presentation on the topic using this Play 11 Administering Security And Privacy Through Digital Hosting Environment Playbook. Dispense information and present a thorough explanation of Deployment, Configuration, Environment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
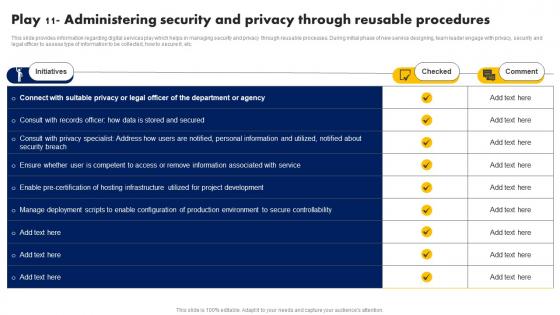 Digital Advancement Playbook Play 11 Administering Security And Privacy Through Reusable
Digital Advancement Playbook Play 11 Administering Security And Privacy Through ReusableThis slide provides information regarding digital services play which helps in managing security and privacy through reusable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc. Deliver an outstanding presentation on the topic using this Digital Advancement Playbook Play 11 Administering Security And Privacy Through Reusable. Dispense information and present a thorough explanation of Initiatives, Checked, Comment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Play 11 Administering Security And Privacy Technological Advancement Playbook
Play 11 Administering Security And Privacy Technological Advancement PlaybookThis slide provides information regarding digital services play which helps in managing security and privacy through reusable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc.Deliver an outstanding presentation on the topic using this Play 11 Administering Security And Privacy Technological Advancement Playbook. Dispense information and present a thorough explanation of Develop Automated, Metrics Tracking, Customer Satisfaction using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
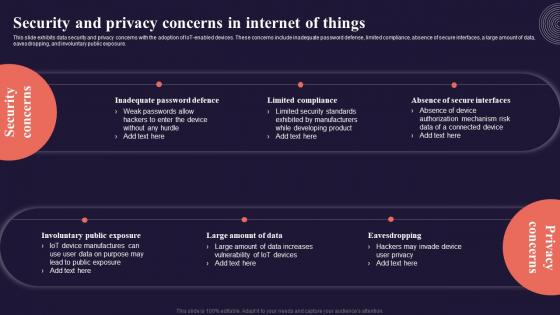 Security And Privacy Concerns In Internet Of Things Introduction To Internet Of Things IoT SS
Security And Privacy Concerns In Internet Of Things Introduction To Internet Of Things IoT SSThis slide exhibits data security and privacy concerns with the adoption of IoT enabled devices. These concerns include inadequate password defense, limited compliance, absence of secure interfaces, a large amount of data, eavesdropping, and involuntary public exposure. Introducing Security And Privacy Concerns In Internet Of Things Introduction To Internet Of Things IoT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Inadequate Password Defence, Limited Compliance, using this template. Grab it now to reap its full benefits.
-
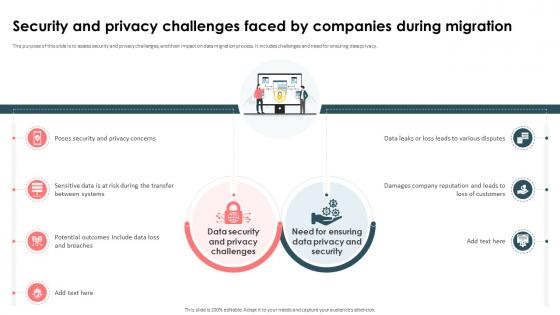 Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By Companies
Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By CompaniesThe purpose of this slide is to assess security and privacy challenges, and their impact on data migration process. It includes challenges and need for ensuring data privacy. Introducing Strategic Approach For Effective Data Migration Security And Privacy Challenges Faced By Companies to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Data Security And Privacy Challenges, Loss Of Customers, Sensitive Data, Poses Security And Privacy Concerns, using this template. Grab it now to reap its full benefits.
-
 About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It
About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role and functionality of IPsec Internet Protocol Security in securing connections between devices. This slide also outlines the uses of IPsec such as protecting data during transmission over open networks, use in building VPNs, etc. Deliver an outstanding presentation on the topic using this About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Overview, Protocol Security, Destination using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing Hypertext Transfer Protocol Secure HTTPS for website encryption. The advantages discussed in this slide are secure interaction, data integrity, privacy and security, better performance, user experience, etc. Introducing Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Interaction, Data Integrity, Better Performance, using this template. Grab it now to reap its full benefits.
-
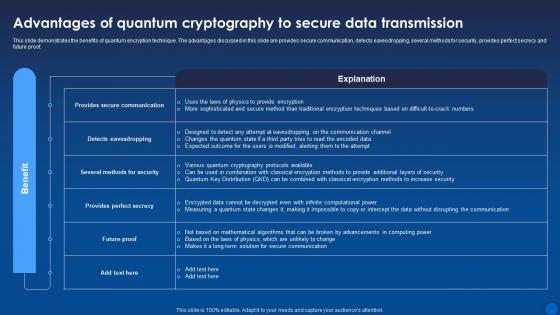 Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It
Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age ItThis slide demonstrates the benefits of quantum encryption technique. The advantages discussed in this slide are provides secure communication, detects eavesdropping, several methods for security, provides perfect secrecy and future proof. Present the topic in a bit more detail with this Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Quantum, Cryptography, Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
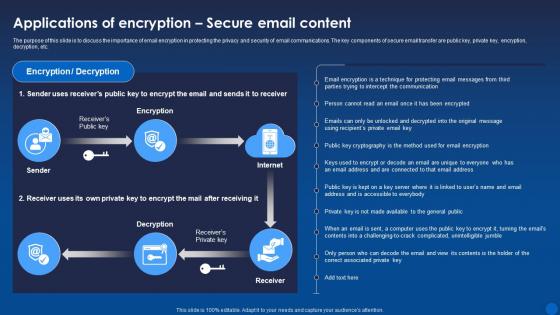 Applications Secure Email Content Encryption For Data Privacy In Digital Age It
Applications Secure Email Content Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss the importance of email encryption in protecting the privacy and security of email communications. The key components of secure email transfer are public key, private key, encryption, decryption, etc. Present the topic in a bit more detail with this Applications Secure Email Content Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Applications, Encryption, Decryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
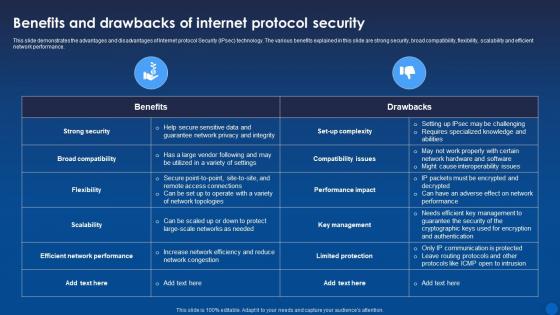 Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Internet protocol Security IPsec technology. The various benefits explained in this slide are strong security, broad compatibility, flexibility, scalability and efficient network performance. Deliver an outstanding presentation on the topic using this Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Key Management, Performance Impact, Compatibility Issues using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
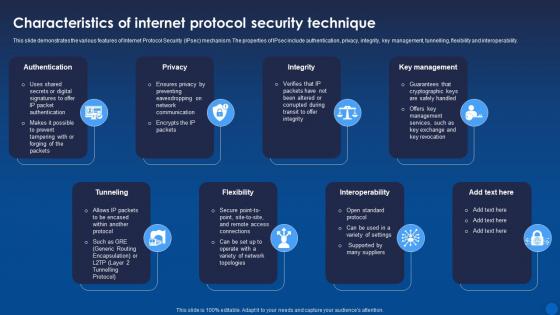 Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It
Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various features of Internet Protocol Security IPsec mechanism. The properties of IPsec include authentication, privacy, integrity, key management, tunnelling, flexibility and interoperability. Introducing Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Interoperability, using this template. Grab it now to reap its full benefits.
-
 Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age It
Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age ItThis slide describes the cloud cryptography trends. The purpose of this slide is to highlight the emerging trends in the field of cloud encryption. These include homomorphic encryption, quantum-safe cryptography, secure multi-party computation, etc. Introducing Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Homomorphic Encryption, Quantum Safe Cryptography, Secure Multi Party Computation, using this template. Grab it now to reap its full benefits.
-
 Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age It
Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age ItThis slide discusses about the increasing adoption of encryption to solve current cyber security issues. The key points discussed are more use of cloud encryption in banking sector, introduction of homomorphic encryption, increase in BYOE adoption, etc. Increase audience engagement and knowledge by dispensing information using Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age It. This template helps you present information on five stages. You can also present information on Homomorphic, Encryption, Introduction using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
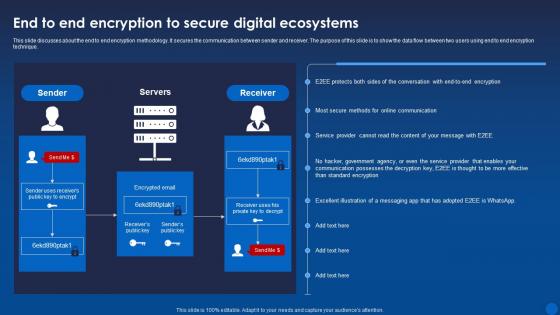 End To End Encryption To Secure Digital Ecosystems Encryption For Data Privacy In Digital Age It
End To End Encryption To Secure Digital Ecosystems Encryption For Data Privacy In Digital Age ItThis slide discusses about the end to end encryption methodology. It secures the communication between sender and receiver. The purpose of this slide is to show the data flow between two users using end to end encryption technique. Present the topic in a bit more detail with this End To End Encryption To Secure Digital Ecosystems Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Digital Ecosystems, Communication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age It
Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the various misconceptions and mistakes of organization while integrating cryptographic solutions into cloud. These include dependence on low-level encryption, reliance on cloud service providers for data protection, poor key management, etc. Introducing Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Data Protection, Poor Key Management, Software Engineers, using this template. Grab it now to reap its full benefits.
-
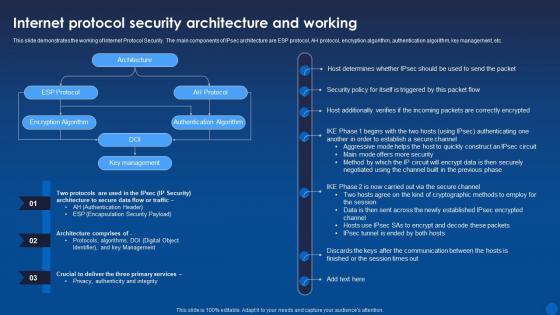 Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It
Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age ItThis slide demonstrates the working of Internet Protocol Security. The main components of IPsec architecture are ESP protocol, AH protocol, encryption algorithm, authentication algorithm, key management, etc. Present the topic in a bit more detail with this Internet Protocol Security Architecture And Working Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Protocol Security, Architecture, Encryption Algorithm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
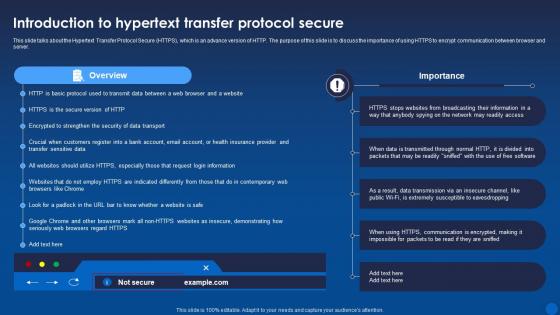 Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide talks about the Hypertext Transfer Protocol Secure HTTPS, which is an advance version of HTTP. The purpose of this slide is to discuss the importance of using HTTPS to encrypt communication between browser and server. Present the topic in a bit more detail with this Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Introduction, Overview, Protocol Secure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
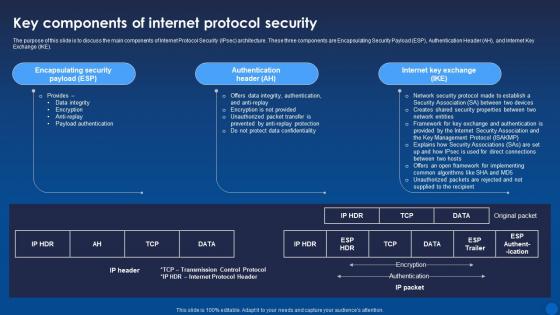 Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss the main components of Internet Protocol Security IPsec architecture. These three components are Encapsulating Security Payload ESP, Authentication Header AH, and Internet Key Exchange IKE. Deliver an outstanding presentation on the topic using this Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Authentication Header, Internet Key Exchange, Encapsulating Security Payload using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age It
Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age ItThis slide talks about the challenges of Hypertext Transfer Protocol Secure HTTPS and their possible solutions. These challenges are lack of end-to-end encryption, certificate authority vulnerabilities, difficulty in detecting malicious content, and complexity and cost of certificate management. Present the topic in a bit more detail with this Limitations Transfer Protocol Secure And Solutions Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Limitations, Solutions, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
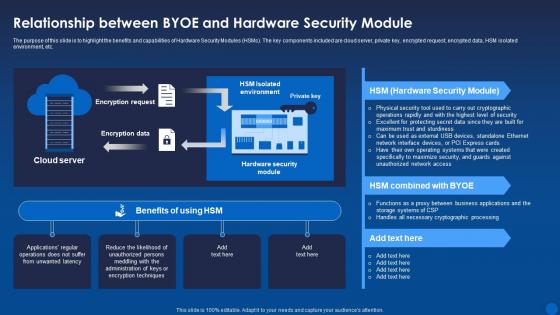 Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It
Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to highlight the benefits and capabilities of Hardware Security Modules HSMs. The key components included are cloud server, private key, encrypted request, encrypted data, HSM isolated environment, etc. Deliver an outstanding presentation on the topic using this Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Relationship, Hardware, Cryptographic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
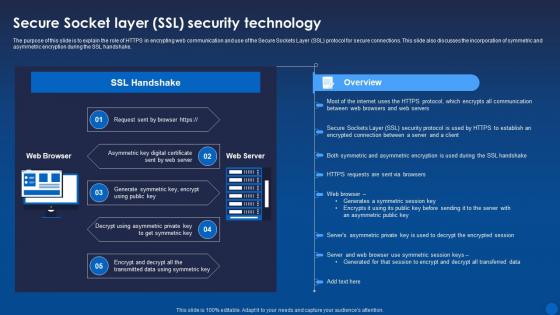 Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age It
Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role of HTTPS in encrypting web communication and use of the Secure Sockets Layer SSL protocol for secure connections. This slide also discusses the incorporation of symmetric and asymmetric encryption during the SSL handshake. Deliver an outstanding presentation on the topic using this Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Technology, Asymmetric, Symmetric using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
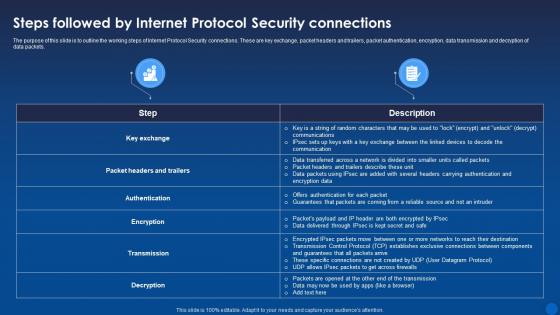 Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It
Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the working steps of Internet Protocol Security connections. These are key exchange, packet headers and trailers, packet authentication, encryption, data transmission and decryption of data packets. Deliver an outstanding presentation on the topic using this Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Connections, Protocol Security, Data Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
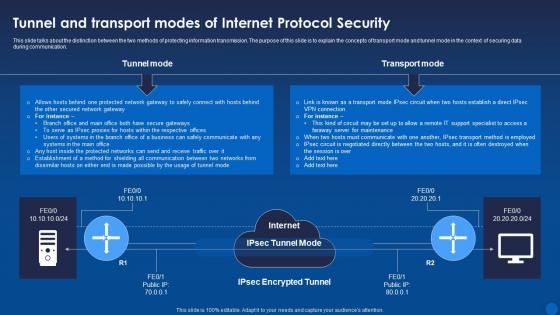 Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide talks about the distinction between the two methods of protecting information transmission. The purpose of this slide is to explain the concepts of transport mode and tunnel mode in the context of securing data during communication. Present the topic in a bit more detail with this Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Transport Mode, Protocol Security, Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
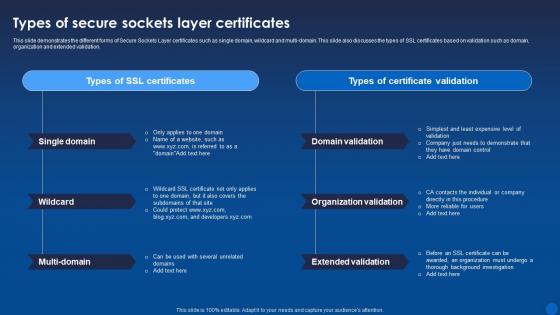 Types Of Secure Sockets Layer Certificates Encryption For Data Privacy In Digital Age It
Types Of Secure Sockets Layer Certificates Encryption For Data Privacy In Digital Age ItThis slide demonstrates the different forms of Secure Sockets Layer certificates such as single domain, wildcard and multi-domain. This slide also discusses the types of SSL certificates based on validation such as domain, organization and extended validation. Deliver an outstanding presentation on the topic using this Types Of Secure Sockets Layer Certificates Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Domain Validation, Organization Validation, Extended Validation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
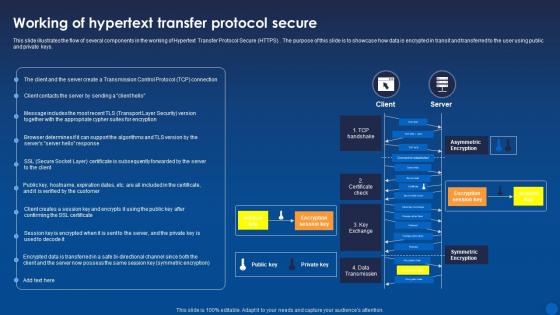 Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide illustrates the flow of several components in the working of Hypertext Transfer Protocol Secure HTTPS. The purpose of this slide is to showcase how data is encrypted in transit and transferred to the user using public and private keys. Present the topic in a bit more detail with this Working Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Asymmetric Encryption, Symmetric Encryption, Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
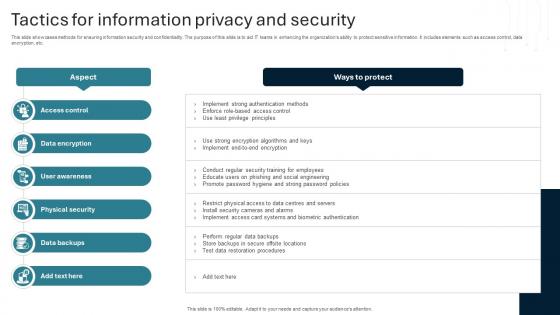 Tactics For Information Privacy And Security
Tactics For Information Privacy And SecurityThis slide showcases methods for ensuring information security and confidentiality. The purpose of this slide is to aid IT teams in enhancing the organizations ability to protect sensitive information. It includes elements such as access control, data encryption, etc. Introducing our premium set of slides with Tactics For Information Privacy And Security. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strong Password Policies, Test Data Restoration Procedures. So download instantly and tailor it with your information.
-
 Data Privacy Training Icon For Securing Information
Data Privacy Training Icon For Securing InformationIntroducing our premium set of slides with Data Privacy Training Icon For Securing Information. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Privacy Training, Securing Information. So download instantly and tailor it with your information.
-
 Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SS
Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SSThis slide covers essential guidance on safeguarding blockchain data to ensure integrity and confidentiality such as keeping private key confidential, utilizing VPN, use of link checker, opting for trusted crypto wallets. Introducing Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SS to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Private Key Confidential, Security, Blockchain, Prevent Phishing Attacks, using this template. Grab it now to reap its full benefits.
-
 Additional Privacy And Security Techniques Comprehensive Approach To Privacy BCT SS
Additional Privacy And Security Techniques Comprehensive Approach To Privacy BCT SSThis slide covers methodologies to safeguard confidential information within blockchain system through techniques such as mixing, group signature, attribute based encryption, secure multi-party computation, etc with applications. Present the topic in a bit more detail with this Additional Privacy And Security Techniques Comprehensive Approach To Privacy BCT SS. Use it as a tool for discussion and navigation on Group Signature, Mixing, Attribute-Based Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
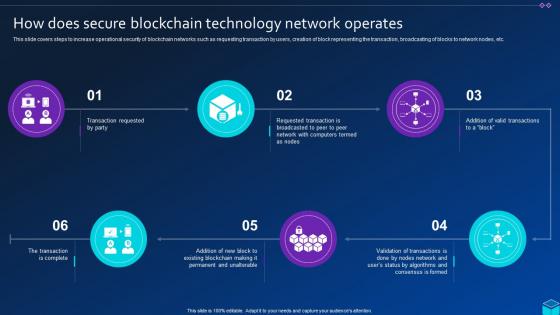 How Does Secure Blockchain Technology Comprehensive Approach To Privacy BCT SS
How Does Secure Blockchain Technology Comprehensive Approach To Privacy BCT SSThis slide covers steps to increase operational security of blockchain networks such as requesting transaction by users, creation of block representing the transaction, broadcasting of blocks to network nodes, etc. Introducing How Does Secure Blockchain Technology Comprehensive Approach To Privacy BCT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Blockchain Technology, Network Operates, using this template. Grab it now to reap its full benefits.
-
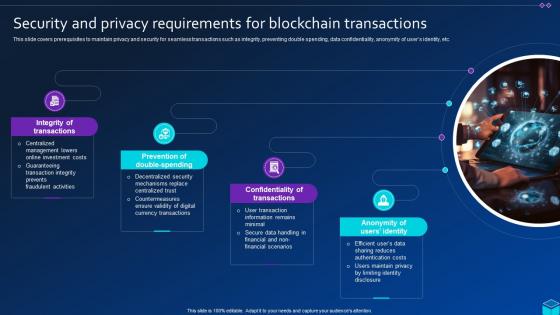 Security And Privacy Requirements For Blockchain Comprehensive Approach To Privacy BCT SS
Security And Privacy Requirements For Blockchain Comprehensive Approach To Privacy BCT SSThis slide covers prerequisites to maintain privacy and security for seamless transactions such as integrity, preventing double spending, data confidentiality, anonymity of users identity, etc. Increase audience engagement and knowledge by dispensing information using Security And Privacy Requirements For Blockchain Comprehensive Approach To Privacy BCT SS. This template helps you present information on four stages. You can also present information on Prevention Of Double-Spending, Confidentiality Of Transactions, Anonymity Of Users Identity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security Management Icon For Consumer Data Privacy
Information Security Management Icon For Consumer Data PrivacyIntroducing our premium set of slides with Information Security Management Icon For Consumer Data Privacy. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Security Management Icon, Consumer Data Privacy. So download instantly and tailor it with your information.
-
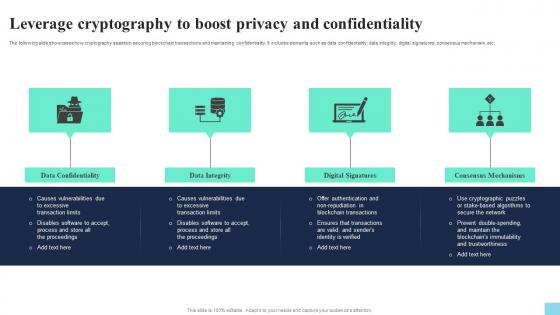 Leverage Cryptography To Boost Privacy And Confidentiality Hands On Blockchain Security Risk BCT SS V
Leverage Cryptography To Boost Privacy And Confidentiality Hands On Blockchain Security Risk BCT SS VThe following slide showcases how cryptography assists in securing blockchain transactions and maintaining confidentiality. It includes elements such as data confidentiality, data integrity, digital signatures, consensus mechanism, etc. Introducing Leverage Cryptography To Boost Privacy And Confidentiality Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Confidentiality, Data Integrity, Digital Signatures, using this template. Grab it now to reap its full benefits.
-
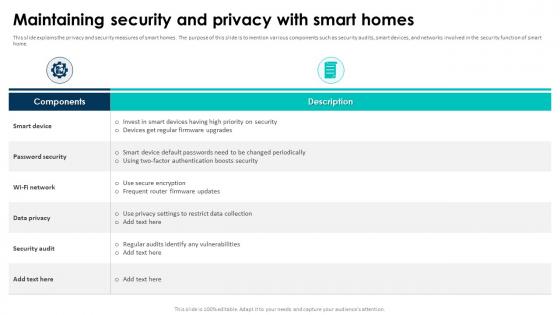 Elevating Living Spaces With Smart Maintaining Security And Privacy With Smart Homes
Elevating Living Spaces With Smart Maintaining Security And Privacy With Smart HomesThis slide explains the privacy and security measures of smart homes. The purpose of this slide is to mention various components such as security audits, smart devices, and networks involved in the security function of smart home. Deliver an outstanding presentation on the topic using this Elevating Living Spaces With Smart Maintaining Security And Privacy With Smart Homes. Dispense information and present a thorough explanation of Password Security, Data Privacy, Security Audit, High Priority On Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Security And Privacy Challenges Faced Transforming Future Of Gaming IoT SS
Impact Of Security And Privacy Challenges Faced Transforming Future Of Gaming IoT SSThe following slide showcases consequences of various security and privacy challenges faced by gaming companies. The slide covers information about misuse of personal information, data leakage, privacy violations, data theft, and access to unauthorized data. Introducing Impact Of Security And Privacy Challenges Faced Transforming Future Of Gaming IoT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Violations, Location Data, Data Theft, using this template. Grab it now to reap its full benefits.
-
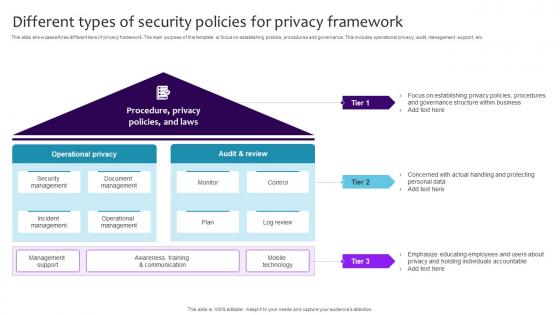 Different Types Of Security Policies For Privacy Framework
Different Types Of Security Policies For Privacy FrameworkThis slide showcases three different tiers of privacy framework. The main purpose of this template is focus on establishing policies, procedures and governance. This includes operational privacy, audit, management support, etc.Introducing our premium set of slides with Different Types Of Security Policies For Privacy Framework. Ellicudate the one stage and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Management, Incident Management, Operational Management. So download instantly and tailor it with your information.
-
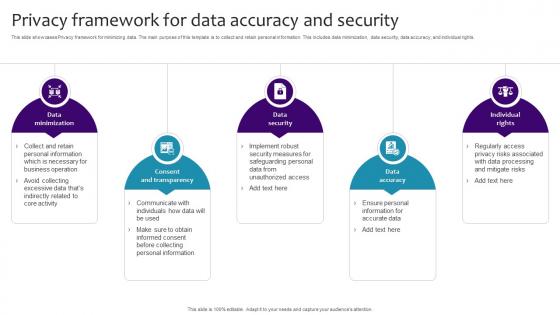 Privacy Framework For Data Accuracy And Security
Privacy Framework For Data Accuracy And SecurityThis slide showcases Privacy framework for minimizing data. The main purpose of this template is to collect and retain personal information. This includes data minimization, data security, data accuracy, and individual rights.Introducing our premium set of slides with Privacy Framework For Data Accuracy And Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Minimization, Consent Transparency, Data Accuracy. So download instantly and tailor it with your information.
-
 Privacy Framework Icon For Securing Business Data
Privacy Framework Icon For Securing Business DataPresenting our well structured Privacy Framework Icon For Securing Business Data. The topics discussed in this slide are Privacy Framework Icon, Securing Business Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.


