Powerpoint Templates and Google slides for Security Risk
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
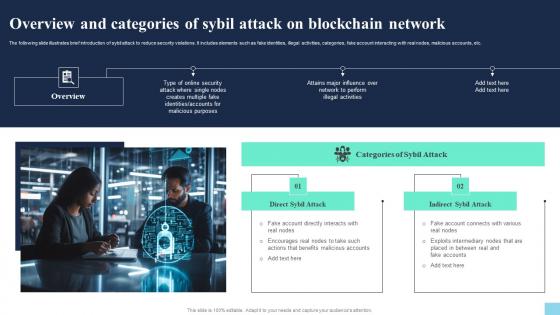 Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Introducing Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Direct Sybil Attack, Indirect Sybil Attack, using this template. Grab it now to reap its full benefits.
-
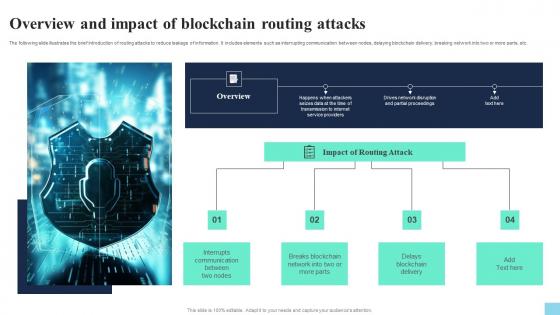 Overview And Impact Of Blockchain Routing Attacks Hands On Blockchain Security Risk BCT SS V
Overview And Impact Of Blockchain Routing Attacks Hands On Blockchain Security Risk BCT SS VThe following slide illustrates the brief introduction of routing attacks to reduce leakage of information. It includes elements such as interrupting communication between nodes, delaying blockchain delivery, breaking network into two or more parts, etc. Increase audience engagement and knowledge by dispensing information using Overview And Impact Of Blockchain Routing Attacks Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Interrupts Communication, Breaks Blockchain, Delays Blockchain Delivery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
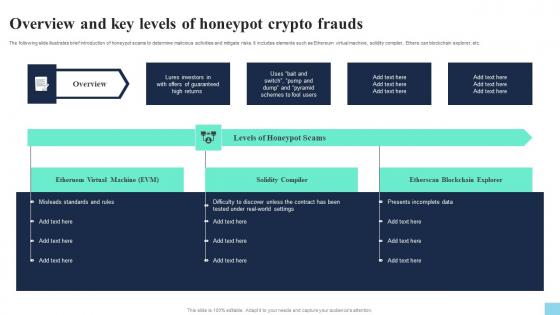 Overview And Key Levels Of Honeypot Crypto Frauds Hands On Blockchain Security Risk BCT SS V
Overview And Key Levels Of Honeypot Crypto Frauds Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of honeypot scams to determine malicious activities and mitigate risks. It includes elements such as Ethereum virtual machine, solidity compiler, Ethers can blockchain explorer, etc. Introducing Overview And Key Levels Of Honeypot Crypto Frauds Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Virtual Machine, Solidity Compiler, Etherscan Blockchain Explorer, using this template. Grab it now to reap its full benefits.
-
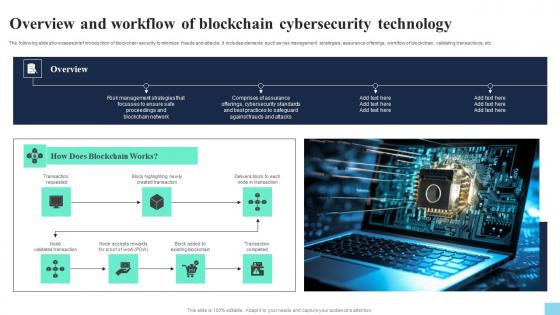 Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V
Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS VThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Increase audience engagement and knowledge by dispensing information using Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V. This template helps you present information on seven stages. You can also present information on Transaction Requested, Created Transaction, Existing Blockchain using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
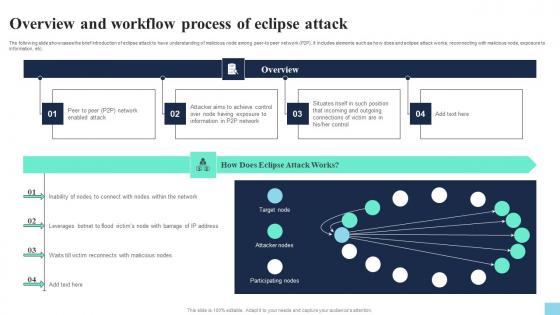 Overview And Workflow Process Of Eclipse Attack Hands On Blockchain Security Risk BCT SS V
Overview And Workflow Process Of Eclipse Attack Hands On Blockchain Security Risk BCT SS VThe following slide showcases the brief introduction of eclipse attack to have understanding of malicious node among peer-to peer network P2P. It includes elements such as how does and eclipse attack works, reconnecting with malicious node, exposure to information, etc. Introducing Overview And Workflow Process Of Eclipse Attack Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Enabled Attack, Achieve Control, Incoming And Outgoing, using this template. Grab it now to reap its full benefits.
-
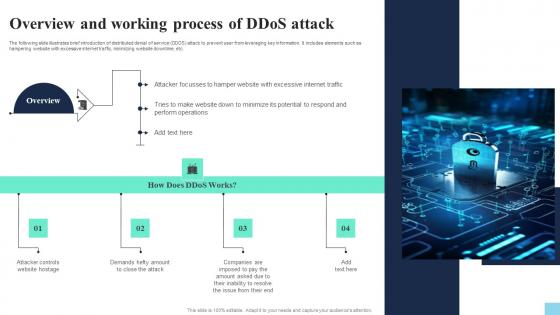 Overview And Working Process Of Ddos Attack Hands On Blockchain Security Risk BCT SS V
Overview And Working Process Of Ddos Attack Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of distributed denial of service DDOS attack to prevent user from leveraging key information. It includes elements such as hampering website with excessive internet traffic, minimizing website downtime, etc. Increase audience engagement and knowledge by dispensing information using Overview And Working Process Of Ddos Attack Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Website Hostage, Close The Attack, Inability To Resolve using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
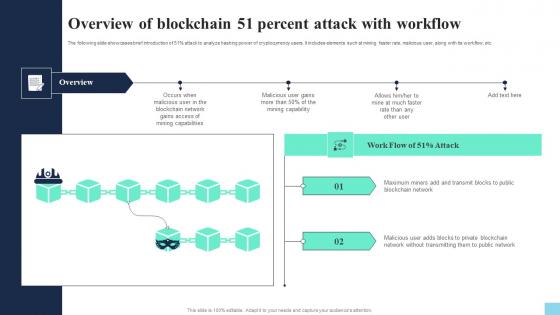 Overview Of Blockchain 51 Percent Attack With Workflow Hands On Blockchain Security Risk BCT SS V
Overview Of Blockchain 51 Percent Attack With Workflow Hands On Blockchain Security Risk BCT SS VThe following slide showcases brief introduction of 51percentage attack to analyze hashing power of cryptocurrency users. It includes elements such at mining faster rate, malicious user, along with its workflow, etc. Introducing Overview Of Blockchain 51 Percent Attack With Workflow Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain Network, Public Network, using this template. Grab it now to reap its full benefits.
-
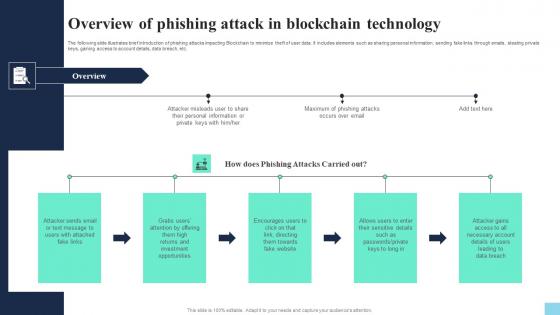 Overview Of Phishing Attack In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Overview Of Phishing Attack In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting Blockchain to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Increase audience engagement and knowledge by dispensing information using Overview Of Phishing Attack In Blockchain Technology Hands On Blockchain Security Risk BCT SS V. This template helps you present information on five stages. You can also present information on Fake Links, Investment Opportunities, Towards Fake Website using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS V
Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting Blockchain to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Threats, Attack Vectors, Causes, using this template. Grab it now to reap its full benefits.
-
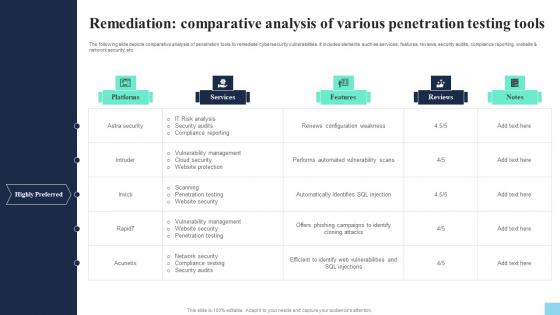 Remediation Comparative Analysis Of Various Penetration Hands On Blockchain Security Risk BCT SS V
Remediation Comparative Analysis Of Various Penetration Hands On Blockchain Security Risk BCT SS VThe following slide depicts comparative analysis of penetration tools to remediate cybersecurity vulnerabilities. It includes elements such as services, features, reviews, security audits, compliance reporting, website and network security, etc. Deliver an outstanding presentation on the topic using this Remediation Comparative Analysis Of Various Penetration Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Platforms, Services, Features using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
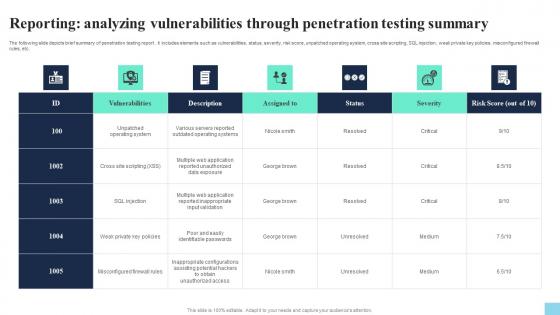 Reporting Analyzing Vulnerabilities Through Penetration Hands On Blockchain Security Risk BCT SS V
Reporting Analyzing Vulnerabilities Through Penetration Hands On Blockchain Security Risk BCT SS VThe following slide depicts brief summary of penetration testing report. it includes elements such as vulnerabilities, status, severity, risk score, unpatched operating system, cross site scripting, SQL injection, weak private key policies, misconfigured firewall rules, etc. Present the topic in a bit more detail with this Reporting Analyzing Vulnerabilities Through Penetration Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Vulnerabilities, Description, Status. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Reviewing Consensus Mechanism To Manage Hands On Blockchain Security Risk BCT SS V
Reviewing Consensus Mechanism To Manage Hands On Blockchain Security Risk BCT SS VThe following slide showcases some tips for consensus mechanism to ensure record of legitimate transactions. It includes elements such as proof of work pow, proof of stake pos, delegated pos, resolving complicated puzzles, verifying transactions, sharing monetary risks, etc. Introducing Reviewing Consensus Mechanism To Manage Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Proof Of Work, Proof Of Stake, Delegated Pos, using this template. Grab it now to reap its full benefits.
-
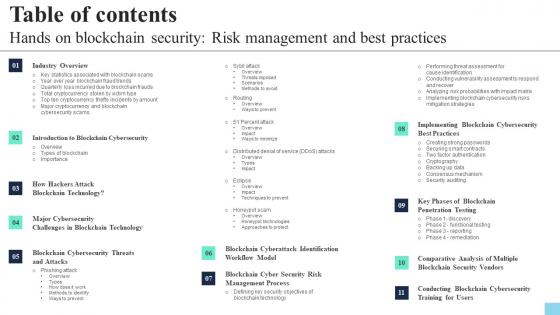 Table Of Contents Hands On Blockchain Security Risk Management And Best Practices BCT SS V
Table Of Contents Hands On Blockchain Security Risk Management And Best Practices BCT SS VIncrease audience engagement and knowledge by dispensing information using Table Of Contents Hands On Blockchain Security Risk Management And Best Practices BCT SS V. This template helps you present information on one stages. You can also present information on Industry Overview, Blockchain Cybersecurity, Blockchain Cyber Security Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
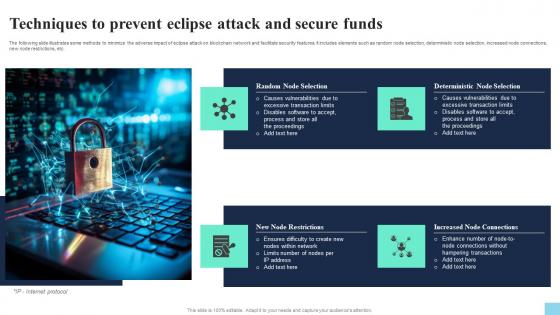 Techniques To Prevent Eclipse Attack And Secure Funds Hands On Blockchain Security Risk BCT SS V
Techniques To Prevent Eclipse Attack And Secure Funds Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Introducing Techniques To Prevent Eclipse Attack And Secure Funds Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Random Node Selection, Deterministic Node Selection, New Node Restrictions, using this template. Grab it now to reap its full benefits.
-
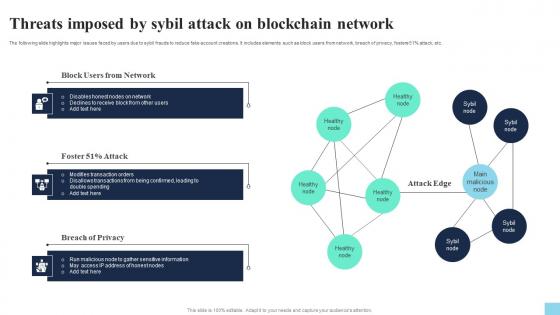 Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide highlights major issues faced by users due to sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percentage attack, etc. Increase audience engagement and knowledge by dispensing information using Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V. This template helps you present information on three stages. You can also present information on Block Users From Network, Attack, Breach Of Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
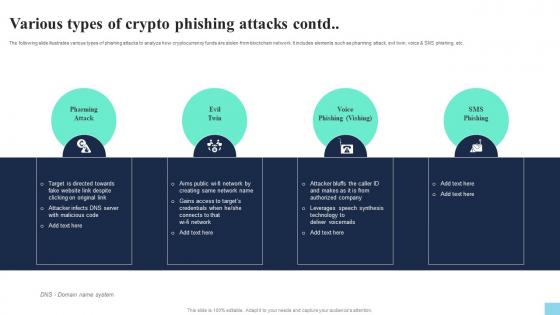 Various Types Of Crypto Phishing Attacks Contd Hands On Blockchain Security Risk BCT SS V
Various Types Of Crypto Phishing Attacks Contd Hands On Blockchain Security Risk BCT SS VThe following slide illustrates various types of phishing attacks to analyze how cryptocurrency funds are stolen from blockchain network. It includes elements such as pharming attack, evil twin, voice and SMS phishing, etc. Introducing Various Types Of Crypto Phishing Attacks Contd Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Pharming Attack, Evil Twin, Sms Phishing, using this template. Grab it now to reap its full benefits.
-
 Various Types Of Crypto Phishing Attacks Hands On Blockchain Security Risk BCT SS V
Various Types Of Crypto Phishing Attacks Hands On Blockchain Security Risk BCT SS VThe following slide illustrates various types of phishing attacks to analyze how cryptocurrency funds are stolen from blockchain network. It includes elements such as spear, whaling, clone, spoof emails, accessibility to personal details, replacing original link with fake one, etc. Increase audience engagement and knowledge by dispensing information using Various Types Of Crypto Phishing Attacks Hands On Blockchain Security Risk BCT SS V. This template helps you present information on three stages. You can also present information on Spear Phishing, Whaling Phishing, Clone Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
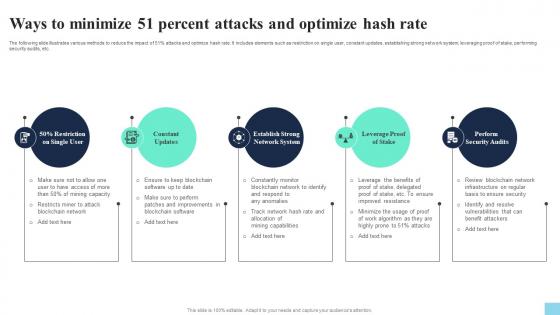 Ways To Minimize 51 Percent Attacks And Optimize Hash Rate Hands On Blockchain Security Risk BCT SS V
Ways To Minimize 51 Percent Attacks And Optimize Hash Rate Hands On Blockchain Security Risk BCT SS VThe following slide illustrates various methods to reduce the impact of 51percentage attacks and optimize hash rate. It includes elements such as restriction on single user, constant updates, establishing strong network system, leveraging proof of stake, performing security audits, etc. Introducing Ways To Minimize 51 Percent Attacks And Optimize Hash Rate Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Constant Updates, Leverage Proof Of Stake, Perform Security Audits, using this template. Grab it now to reap its full benefits.
-
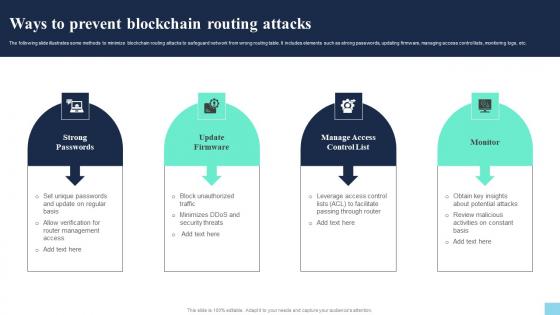 Ways To Prevent Blockchain Routing Attacks Hands On Blockchain Security Risk BCT SS V
Ways To Prevent Blockchain Routing Attacks Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some methods to minimize blockchain routing attacks to safeguard network from wrong routing table. It includes elements such as strong passwords, updating firmware, managing access control lists, monitoring logs, etc. Increase audience engagement and knowledge by dispensing information using Ways To Prevent Blockchain Routing Attacks Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Strong Passwords, Update Firmware, Monitor using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
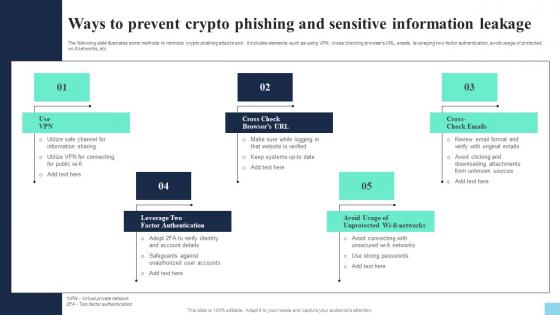 Ways To Prevent Crypto Phishing And Sensitive Hands On Blockchain Security Risk BCT SS V
Ways To Prevent Crypto Phishing And Sensitive Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some methods to minimize crypto phishing attacks and. it includes elements such as using VPN, cross checking browsers URL, emails, leveraging two factor authentication, avoid usage of protected wi-fi networks, etc. Introducing Ways To Prevent Crypto Phishing And Sensitive Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Factor Authentication, Avoid Usage, Cross Check Emails, using this template. Grab it now to reap its full benefits.
-
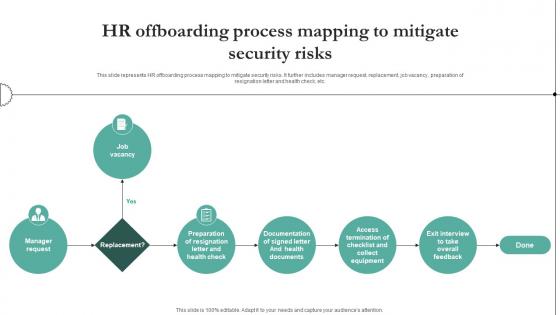 HR Offboarding Process Mapping To Mitigate Security Risks
HR Offboarding Process Mapping To Mitigate Security RisksThis slide represents HR offboarding process mapping to mitigate security risks. It further includes manager request, replacement, job vacancy, preparation of resignation letter and health check, etc. Presenting our well structured HR Offboarding Process Mapping To Mitigate Security Risks. The topics discussed in this slide are Resignation, Documentation, Termination. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
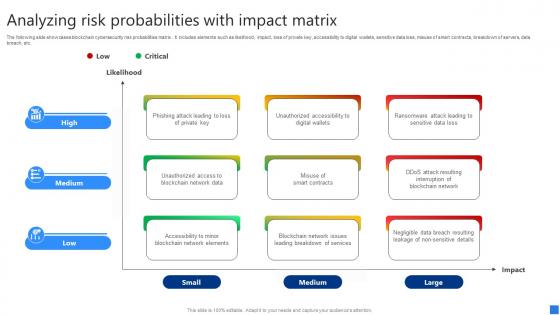 Analyzing Risk Probabilities Securing Blockchain Transactions A Beginners Guide BCT SS V
Analyzing Risk Probabilities Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity risk probabilities matrix . It includes elements such as likelihood, impact, loss of private key, accessibility to digital wallets, sensitive data loss, misuse of smart contracts, breakdown of servers, data breach, etc. Deliver an outstanding presentation on the topic using this Analyzing Risk Probabilities Securing Blockchain Transactions A Beginners Guide BCT SS V. Dispense information and present a thorough explanation of Phishing Attack Leading, Unauthorized Accessibility, Ransomware Attack Leading using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
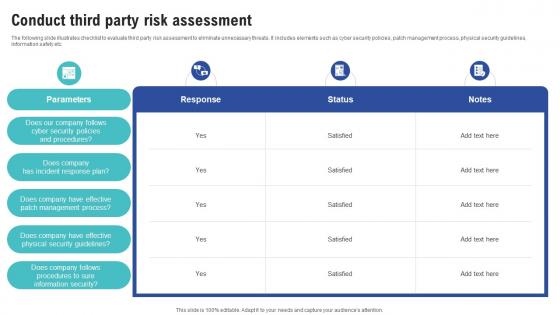 Conduct Third Party Risk Assessment Creating Cyber Security Awareness
Conduct Third Party Risk Assessment Creating Cyber Security AwarenessThe following slide illustrates checklist to evaluate third party risk assessment to eliminate unnecessary threats. It includes elements such as cyber security policies, patch management process, physical security guidelines, information safety etc. Deliver an outstanding presentation on the topic using this Conduct Third Party Risk Assessment Creating Cyber Security Awareness Dispense information and present a thorough explanation of Response, Status, Notes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Determine Cyber Security Risks And Threats Creating Cyber Security Awareness
Determine Cyber Security Risks And Threats Creating Cyber Security AwarenessThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Present the topic in a bit more detail with this Determine Cyber Security Risks And Threats Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Human Errors, Factor Authentication This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Evaluate Impact And Probability Of Risk Occurrence Creating Cyber Security Awareness
Evaluate Impact And Probability Of Risk Occurrence Creating Cyber Security AwarenessThe following slide depicts the potential risk score of identified cyber risks to communicate and level threats. It includes key elements such as human and general errors, outdated security policy, selling companys confidential information, system failure etc. Deliver an outstanding presentation on the topic using this Evaluate Impact And Probability Of Risk Occurrence Creating Cyber Security Awareness Dispense information and present a thorough explanation of Data Backup Methods, Network Attached Storage, Cloud Storage Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
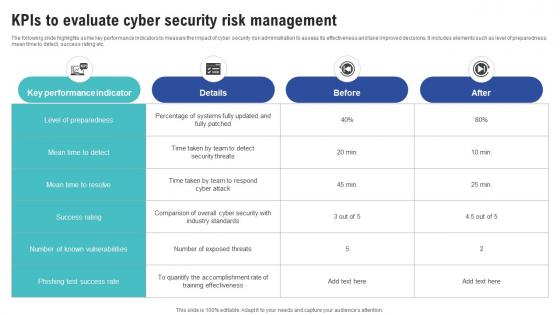 Kpis To Evaluate Cyber Security Risk Management Creating Cyber Security Awareness
Kpis To Evaluate Cyber Security Risk Management Creating Cyber Security AwarenessThe following slide highlights some key performance indicators to measure the impact of cyber security risk administration to assess its effectiveness and take improved decisions. It includes elements such as level of preparedness, mean time to detect, success rating etc. Present the topic in a bit more detail with this Kpis To Evaluate Cyber Security Risk Management Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Minimizes Malware Infection, Security Requirements, Internal Risks This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Monitor And Assess Vendor Risk Management Creating Cyber Security Awareness
Monitor And Assess Vendor Risk Management Creating Cyber Security AwarenessThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Deliver an outstanding presentation on the topic using this Monitor And Assess Vendor Risk Management Creating Cyber Security Awareness Dispense information and present a thorough explanation of Select Strong Password, Conduct Password Test, Password Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
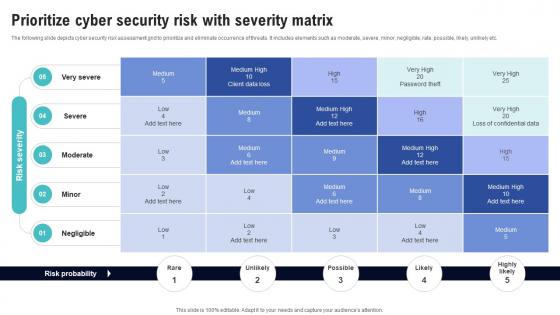 Prioritize Cyber Security Risk With Severity Matrix Creating Cyber Security Awareness
Prioritize Cyber Security Risk With Severity Matrix Creating Cyber Security AwarenessThe following slide depicts cyber security risk assessment grid to prioritize and eliminate occurrence of threats. It includes elements such as moderate, severe, minor, negligible, rate, possible, likely, unlikely etc. Present the topic in a bit more detail with this Prioritize Cyber Security Risk With Severity Matrix Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Target Audience, Document Management This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Run Penetration Testing To Review Risk Creating Cyber Security Awareness
Run Penetration Testing To Review Risk Creating Cyber Security AwarenessThe following slide showcases various methods to review cyber risks to determine probability and impact of risks. It includes elements such as penetration, red team and risk based testing along with objectives, features, cost, outcomes, duration etc. Deliver an outstanding presentation on the topic using this Run Penetration Testing To Review Risk Creating Cyber Security Awareness Dispense information and present a thorough explanation of Minimizes Data Breaches, Controls User Access, Improves Tracking Visibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
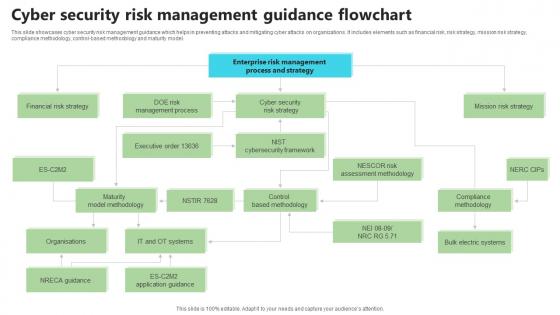 Cyber Security Risk Management Guidance Flowchart
Cyber Security Risk Management Guidance FlowchartThis slide showcases cyber security risk management guidance which helps in preventing attacks and mitigating cyber attacks on organizations. It includes elements such as financial risk, risk strategy, mission risk strategy, compliance methodology, control-based methodology and maturity model. Introducing our Cyber Security Risk Management Guidance Flowchart set of slides. The topics discussed in these slides are Financial Risk Strategy, Compliance Methodology, Mission Risk Strategy. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Opsec Cyber Security To Eliminate Business Risks
Opsec Cyber Security To Eliminate Business RisksThis slide showcases the multiple threats eliminated by opsec cybersecurity measures. This slide aims to help the business understand the importance of opsec security measures. It includes elements such as third party risks, social engineering, etc. Introducing our premium set of slides with Opsec Cyber Security To Eliminate Business Risks. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Social Engineering,Patch Management,Malware And Ransomware. So download instantly and tailor it with your information.
-
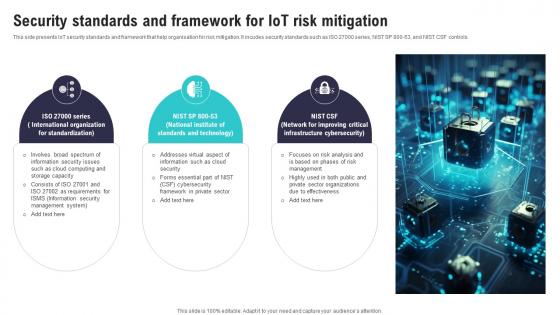 Security Standards And Framework For IoT Risk Mitigation IoT Security And Privacy Safeguarding IoT SS
Security Standards And Framework For IoT Risk Mitigation IoT Security And Privacy Safeguarding IoT SSThis side presents IoT security standards and framework that help organisation for risk mitigation. It incudes security standards such as ISO 27000 series, NIST SP 800 53, and NIST CSF controls. Introducing Security Standards And Framework For IoT Risk Mitigation IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on International Organization, Information Security Issues, Management System, using this template. Grab it now to reap its full benefits.
-
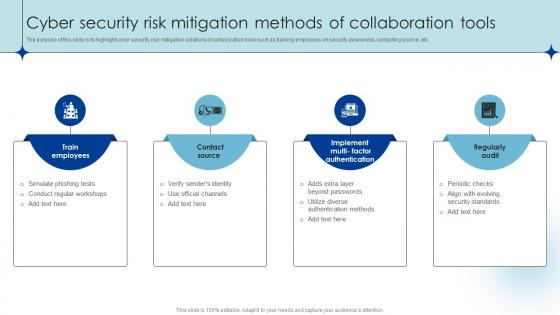 Cyber Security Risk Mitigation Methods Of Collaboration Tools
Cyber Security Risk Mitigation Methods Of Collaboration ToolsThe purpose of this slide is to highlight cyber security risk mitigation solutions of collaboration tools such as training employees on security awareness, contacting source, etc. Introducing our premium set of slides with Cyber Security Risk Mitigation Methods Of Collaboration Tools. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Simulate Phishing Tests, Verify Senders Identity, Use Official Channels . So download instantly and tailor it with your information.
-
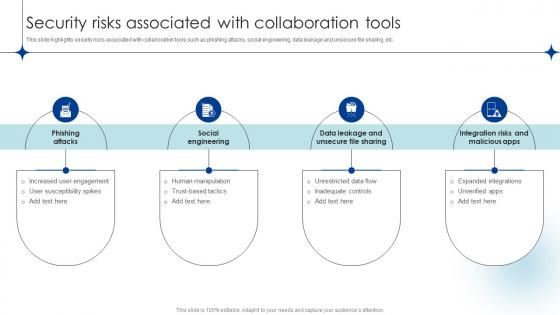 Security Risks Associated With Collaboration Tools
Security Risks Associated With Collaboration ToolsThis slide highlights security risks associated with collaboration tools such as phishing attacks, social engineering, data leakage and unsecure file sharing, etc. Presenting our set of slides with Security Risks Associated With Collaboration Tools. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Attacks, Social Engineering, Unrestricted Data Flow, Human Manipulation .
-
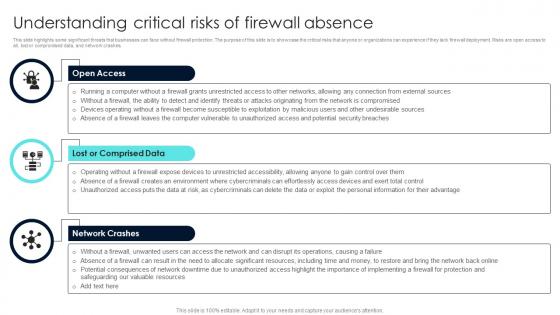 Firewall Network Security Understanding Critical Risks Of Firewall Absence
Firewall Network Security Understanding Critical Risks Of Firewall AbsenceThis slide highlights some significant threats that businesses can face without firewall protection. The purpose of this slide is to showcase the critical risks that anyone or organizations can experience if they lack firewall deployment. Risks are open access to all, lost or compromised data, and network crashes. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Understanding Critical Risks Of Firewall Absence This template helps you present information on Three stages. You can also present information on Open Access, Lost Or Comprised Data, Network Crashes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
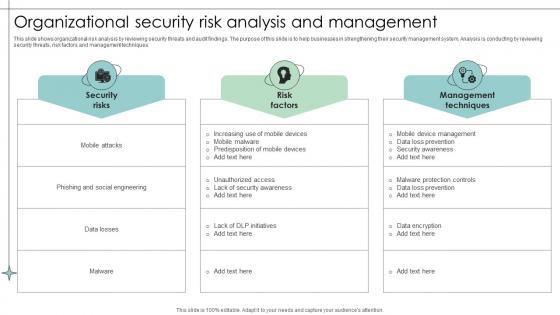 Organizational Security Risk Analysis And Management
Organizational Security Risk Analysis And ManagementThis slide shows organizational risk analysis by reviewing security threats and audit findings. The purpose of this slide is to help businesses in strengthening their security management system. Analysis is conducting by reviewing security threats, risk factors and management techniques. Presenting our well structured Organizational Security Risk Analysis And Management. The topics discussed in this slide are Security, Factors, Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Information Security And Risk Management Training Program
Information Security And Risk Management Training ProgramThis slide showcases the successful information security and risk management training outline. It include details such as threats and vulnerabilities, etc. Presenting our well structured Information Security And Risk Management Training Program. The topics discussed in this slide are Training, Vulnerabilities, Information. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Emerging Cloud Security Risks And Threats Next Generation CASB
Emerging Cloud Security Risks And Threats Next Generation CASBThis slide represents the emerging cloud security risks, and threats organizations can encounter. The purpose of this slide is to highlight the various threats that CASB deployment can help overcome, including VPNs, system misconfiguration, non-zero security permissions, and so on. Present the topic in a bit more detail with this Emerging Cloud Security Risks And Threats Next Generation CASB Use it as a tool for discussion and navigation on Virtual Private Networks, System Misconfigurations, Perimeter Security This template is free to edit as deemed fit for your organization. Therefore download it now.
-
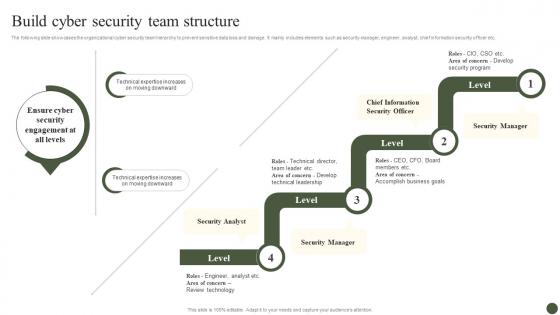 Build Cyber Security Team Structure Implementing Cyber Risk Management Process
Build Cyber Security Team Structure Implementing Cyber Risk Management ProcessThe following slide showcases the organizational cyber security team hierarchy to prevent sensitive data loss and damage. It mainly includes elements such as security manager, engineer, analyst, chief information security officer etc. Deliver an outstanding presentation on the topic using this Build Cyber Security Team Structure Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Security Analyst, Security Manager, Chief Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
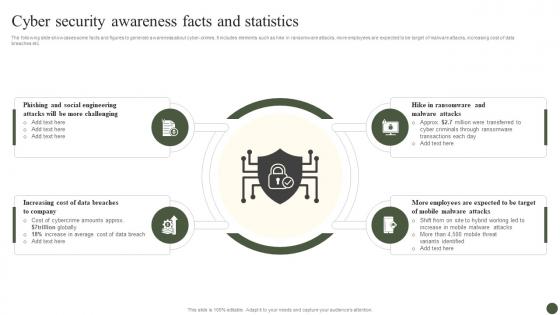 Cyber Security Awareness Facts And Statistics Implementing Cyber Risk Management Process
Cyber Security Awareness Facts And Statistics Implementing Cyber Risk Management ProcessThe following slide showcases some facts and figures to generate awareness about cyber-crimes. It includes elements such as hike in ransomware attacks, more employees are expected to be target of malware attacks, increasing cost of data breaches etc. Introducing Cyber Security Awareness Facts And Statistics Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering, Data Breaches, Mobile Malware Attacks, using this template. Grab it now to reap its full benefits.
-
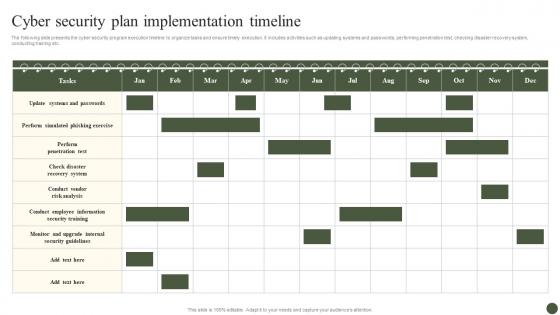 Cyber Security Plan Implementation Timeline Implementing Cyber Risk Management Process
Cyber Security Plan Implementation Timeline Implementing Cyber Risk Management ProcessThe following slide presents the cyber security program execution timeline to organize tasks and ensure timely execution. It includes activities such as updating systems and passwords, performing penetration test, checking disaster recovery system, conducting training etc. Present the topic in a bit more detail with this Cyber Security Plan Implementation Timeline Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Cyber Security Plan, Implementation Timeline. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
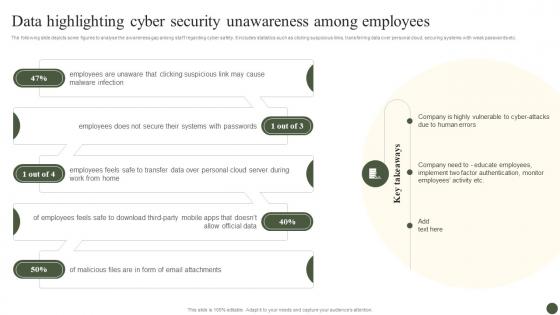 Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process
Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management ProcessThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Increase audience engagement and knowledge by dispensing information using Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process. This template helps you present information on five stages. You can also present information on Malware Infection, Systems With Passwords, Employees Feels, Allow Official Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine Cyber Security Risks And Threats Implementing Cyber Risk Management Process
Determine Cyber Security Risks And Threats Implementing Cyber Risk Management ProcessThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Present the topic in a bit more detail with this Determine Cyber Security Risks And Threats Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Details, Objectives, Issue Identifier. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
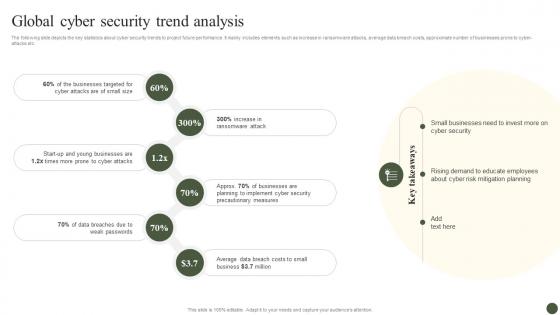 Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process
Global Cyber Security Trend Analysis Implementing Cyber Risk Management ProcessThe following slide depicts the key statistics about cyber security trends to project future performance. It mainly includes elements such as increase in ransomware attacks, average data breach costs, approximate number of businesses prone to cyber-attacks etc. Introducing Global Cyber Security Trend Analysis Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Businesses Targeted, Ransomware Attack, Cyber Attacks, using this template. Grab it now to reap its full benefits.
-
 Impact Of Cyber Safety Security Measures Implementing Cyber Risk Management Process
Impact Of Cyber Safety Security Measures Implementing Cyber Risk Management ProcessThe following slide depicts the projected consequences of implementing cyber security preventive measures. It includes data about number of cyber attracts pre and post adopting latest strategies. Present the topic in a bit more detail with this Impact Of Cyber Safety Security Measures Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Cyber Attack Type, Remarks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Cyber Security Policies And Practices Implementing Cyber Risk Management Process
Impact Of Cyber Security Policies And Practices Implementing Cyber Risk Management ProcessThe following slide focuses on drafting cyber security policies to manage data control and breach. It mainly includes elements such as impact of existing cyber safety policies, mitigation actions. Deliver an outstanding presentation on the topic using this Impact Of Cyber Security Policies And Practices Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Inadequate Security Guidelines, Inappropriate Privacy Policies, Insufficient Background Check using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
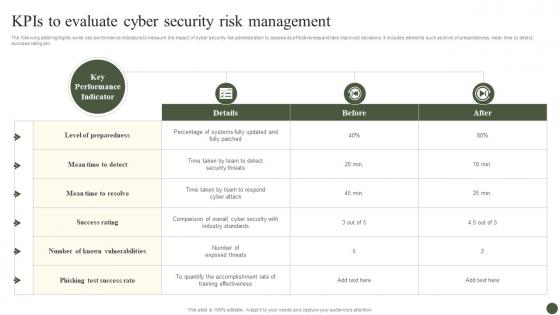 KPIs To Evaluate Cyber Security Risk Management Implementing Cyber Risk Management Process
KPIs To Evaluate Cyber Security Risk Management Implementing Cyber Risk Management ProcessThe following slide highlights some key performance indicators to measure the impact of cyber security risk administration to assess its effectiveness and take improved decisions. It includes elements such as level of preparedness, mean time to detect, success rating etc. Present the topic in a bit more detail with this KPIs To Evaluate Cyber Security Risk Management Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Details, Before, After. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
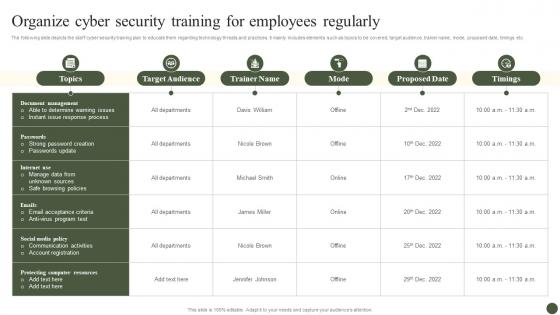 Organize Cyber Security Training For Employees Regularly Implementing Cyber Risk Management Process
Organize Cyber Security Training For Employees Regularly Implementing Cyber Risk Management ProcessThe following slide depicts the staff cyber security training plan to educate them regarding technology threats and practices. It mainly includes elements such as topics to be covered, target audience, trainer name, mode, proposed date, timings etc. Present the topic in a bit more detail with this Organize Cyber Security Training For Employees Regularly Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Target Audience, Trainer Name, Mode. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
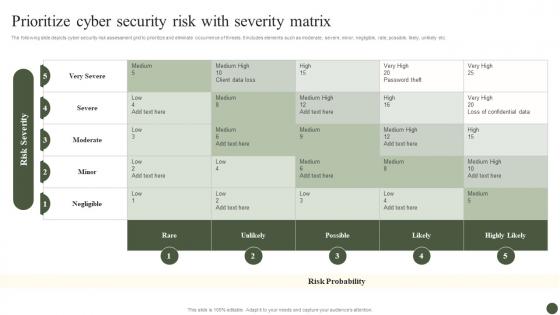 Prioritize Cyber Security Risk With Severity Matrix Implementing Cyber Risk Management Process
Prioritize Cyber Security Risk With Severity Matrix Implementing Cyber Risk Management ProcessThe following slide depicts cyber security risk assessment grid to prioritize and eliminate occurrence of threats. It includes elements such as moderate, severe, minor, negligible, rate, possible, likely, unlikely etc. Present the topic in a bit more detail with this Prioritize Cyber Security Risk With Severity Matrix Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Rare, Unlikely, Possible. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
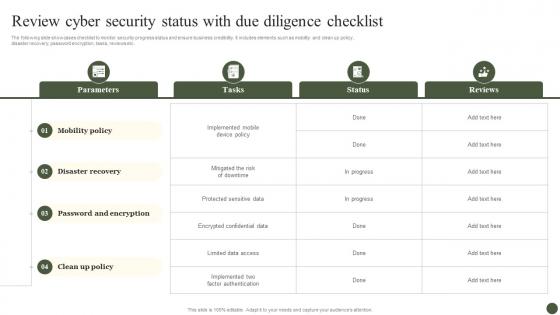 Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management Process
Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management ProcessThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Present the topic in a bit more detail with this Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Parameters, Tasks, Status, Reviews. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Select Tools To Reduce Cyber Security Failure Implementing Cyber Risk Management Process
Select Tools To Reduce Cyber Security Failure Implementing Cyber Risk Management ProcessThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Deliver an outstanding presentation on the topic using this Select Tools To Reduce Cyber Security Failure Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Features, Free Trial, Cost using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Practices In Cyber Security Risk Management
Best Practices In Cyber Security Risk ManagementThis slide exhibits cyber risk management practices which enable businesses to prioritize risks and apply the right kinds of security controls to minimize impact. It include adaptive and continuous risk management, strict security protocols, cyber security risk management strategy. Introducing our premium set of slides with Best Practices In Cyber Security Risk Management. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Know Organizations IT Environment And Assets. Impose Strict Security Protocols, Adaptive And Continuous Risk Management . So download instantly and tailor it with your information.
-
 Computer Security Icon For Cyber Risk Management
Computer Security Icon For Cyber Risk ManagementPresenting our set of slides with Computer Security Icon For Cyber Risk Management. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Computer Security Icon, Cyber Risk Management.
-
 Cyber Security Risk Management Lifecycle
Cyber Security Risk Management LifecycleFollowing slide highlights risk management lifecycle of cyber security for maintaining customer trust. It further covers evaluate, analyse, implement and decision and further includes preparing cyber security policy, risk in data collection, etc. Introducing our premium set of slides with Cyber Security Risk Management Lifecycle. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Implement, Evaluate, Decision. So download instantly and tailor it with your information.
-
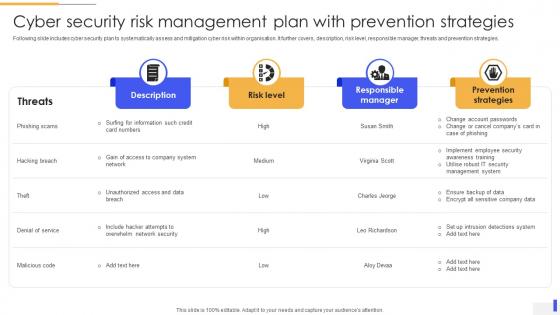 Cyber Security Risk Management Plan With Prevention Strategies
Cyber Security Risk Management Plan With Prevention StrategiesFollowing slide includes cyber security plan to systematically assess and mitigation cyber risk within organisation. It further covers, description, risk level, responsible manager, threats and prevention strategies. Introducing our Cyber Security Risk Management Plan With Prevention Strategies set of slides. The topics discussed in these slides are Risk Level, Responsible Manager, Prevention Strategies. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Supply Chain Cyber Security Risk Management Plan
Supply Chain Cyber Security Risk Management PlanThis slide includes cyber security management plan which can be used by supply chain managers to manage security threats. It includes various strategies such as upgrade minimum security baseline, assess process for further risks, and educate employees. Presenting our well structured Supply Chain Cyber Security Risk Management Plan. The topics discussed in this slide are Supervisor, Action Required, Mitigation Strategy. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
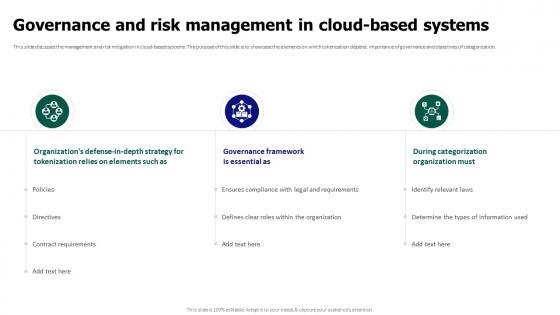 Tokenization For Improved Data Security Governance And Risk Management In Cloud Based Systems
Tokenization For Improved Data Security Governance And Risk Management In Cloud Based SystemsThis slide discusses the management and risk mitigation in cloud-based systems. The purpose of this slide is to showcase the elements on which tokenization depend, importance of governance and objectives of categorization. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Governance And Risk Management In Cloud Based Systems. Dispense information and present a thorough explanation of Governance And Risk Management, Cloud Based Systems, During Categorization Organization Must using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
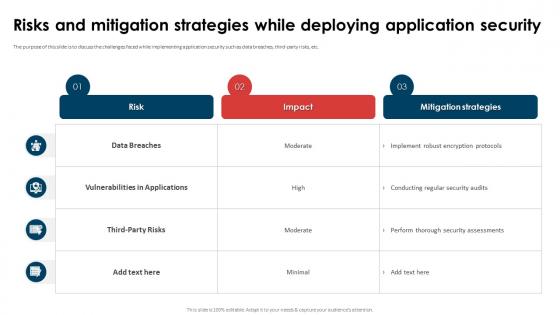 Application Security Implementation Plan Risks And Mitigation Strategies While Deploying Application Security
Application Security Implementation Plan Risks And Mitigation Strategies While Deploying Application SecurityThe purpose of this slide is to discuss the challenges faced while implementing application security such as data breaches, third-party risks, etc. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Risks And Mitigation Strategies While Deploying Application Security. Dispense information and present a thorough explanation of Vulnerabilities In Applications, Data Breaches, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
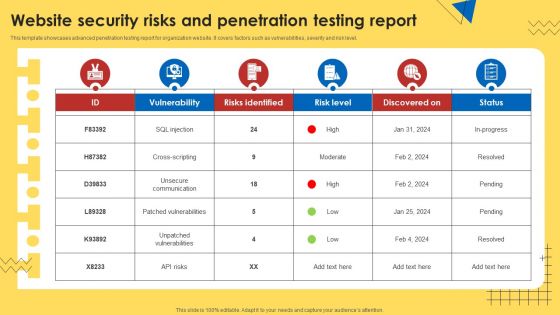 Website Security Risks And Penetration Testing Report
Website Security Risks And Penetration Testing ReportThis template showcases advanced penetration testing report for organization website. It covers factors such as vulnerabilities, severity and risk level. Presenting our well structured Website Security Risks And Penetration Testing Report. The topics discussed in this slide are Website Security Risks, Penetration Testing Report. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
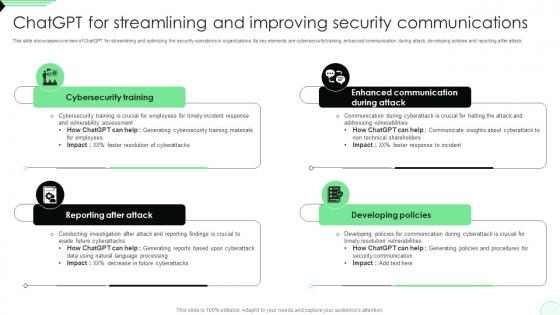 ChatGPT For Streamlining And Improving Security Opportunities And Risks Of ChatGPT AI SS V
ChatGPT For Streamlining And Improving Security Opportunities And Risks Of ChatGPT AI SS VThis slide showcases overview of ChatGPT for streamlining and optimizing the security operations in organizations. Its key elements are cybersecurity training, enhanced communication during attack, developing policies and reporting after attack. Introducing ChatGPT For Streamlining And Improving Security Opportunities And Risks Of ChatGPT AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reporting After Attack, Cybersecurity Training, Developing Policies, using this template. Grab it now to reap its full benefits.



