Powerpoint Templates and Google slides for Security Strategy
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
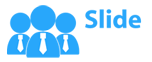
 Implementing Effective Tokenization Steps To Implement Security Tokenization Strategy
Implementing Effective Tokenization Steps To Implement Security Tokenization StrategyThis slide represents the different phases of deploying security tokenization which include identifying sensitive data, implementing tokenization, etc. Increase audience engagement and knowledge by dispensing information using Implementing Effective Tokenization Steps To Implement Security Tokenization Strategy. This template helps you present information on seven stages. You can also present information on Implement Security Tokenization, Identify Sensitive Data, Secure Storage Of Tokens using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
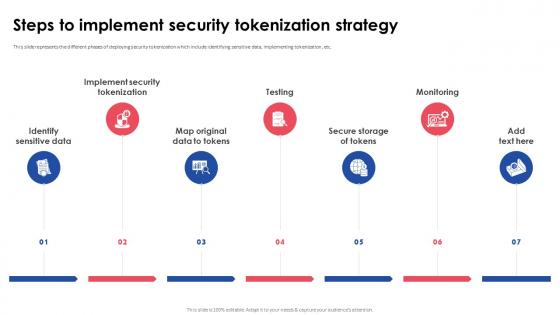
 Strategies For Implementing AI Powered Global Technology In Cyber Security
Strategies For Implementing AI Powered Global Technology In Cyber SecurityThis slide shows strategic approaches for implementing AI in cyber security. The purpose of this slide is to strengthen organizations defence against potential cyber attacks to maximize effectiveness of global technological solutions. It covers strategies such as resource allocation, training data, internal processes, etc. Presenting our set of slides with Strategies For Implementing AI Powered Global Technology In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Resource Allocation, Training Data, Internal Processes.
-
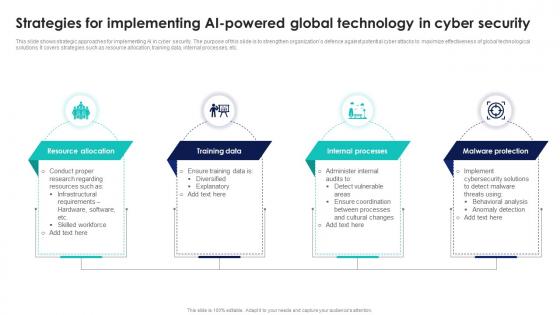
 Strategies For Identifying Security Gap In Network
Strategies For Identifying Security Gap In NetworkThe following slide represents identifying tactics of gaps in security network for improving data structure. It further covers run network audit, analyse system log data and audit IT supply chain. Introducing our Strategies For Identifying Security Gap In Network set of slides. The topics discussed in these slides are Run Network Audit, Analyse System Log Data, Audit IT Supply Chain. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Food Security Mitigation Strategies For Secure Facility
Food Security Mitigation Strategies For Secure FacilityThe purpose of this slide is to safeguard facilities and prevent unauthorized access, contamination, and theft including strategies such as physical secruity systems, emergency response plan, etc. Introducing our Food Security Mitigation Strategies For Secure Facility set of slides. The topics discussed in these slides are Employee Training Program, Physical Security Systems, Emergency Response Plan, Visitor Management System. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Steps To Create Security Strategy For Industrial Facility
Steps To Create Security Strategy For Industrial FacilityThe purpose of this slide is to develop a comprehensive security strategy for an industrial facility to safeguard personnel, assets, and operations through assessing facility vulnerabilities, developing contingency plan, etc. Introducing our premium set of slides with name Steps To Create Security Strategy For Industrial Facility. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Establish Robust Security Protocols, Regular Updates And Maintenance, Develop Contingency Plan. So download instantly and tailor it with your information.
-
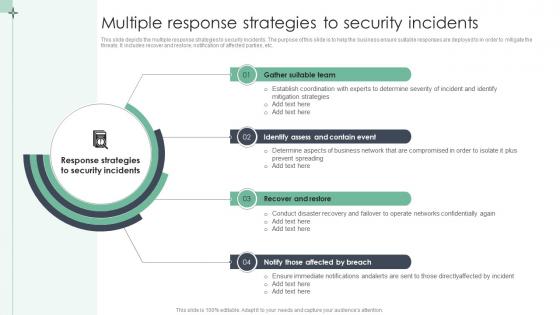 Multiple Response Strategies To Security Incidents
Multiple Response Strategies To Security IncidentsThis slide depicts the multiple response strategies to security incidents. The purpose of this slide is to help the business ensure suitable responses are deployed to in order to mitigate the threats. It includes recover and restore, notification of affected parties, etc. Introducing our premium set of slides with Multiple Response Strategies To Security Incidents. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Gather Suitable Team, Contain Event, Recover And Restore. So download instantly and tailor it with your information.
-
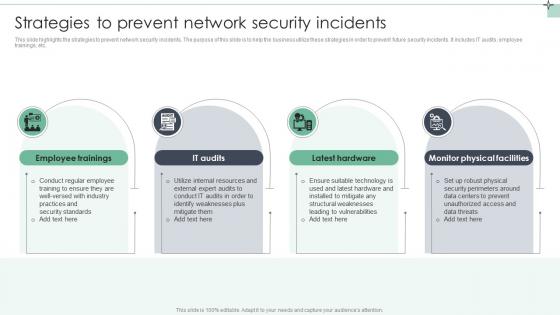 Strategies To Prevent Network Security Incidents
Strategies To Prevent Network Security IncidentsThis slide highlights the strategies to prevent network security incidents. The purpose of this slide is to help the business utilize these strategies in order to prevent future security incidents. It includes IT audits, employee trainings, etc. Introducing our premium set of slides with Strategies To Prevent Network Security Incidents. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Lack Of Preparedness, Insufficient Resources, Limited Visibility. So download instantly and tailor it with your information.
-
 Implement ATP Cyber Security Strategies In Organisation
Implement ATP Cyber Security Strategies In OrganisationThis slide depicts the strategies for cyber security ATP. Its objective is to help formulate advanced strategies for threat protection. This slide includes broad test repository, benign software behaviour, analysis of data, etc. Presenting our set of slides with name Implement ATP Cyber Security Strategies In Organisation. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Broad Test Repository, Benign Software Behaviour, Analysis Of Data.
-
 Exit Strategy Smart Farming Technology Pitch Deck For Food Security
Exit Strategy Smart Farming Technology Pitch Deck For Food SecurityFollowing slide represents major exit strategies of company to be used during financial crisis. It includes strategies such as acquisitions, mergers and initial public offerings. Introducing Exit Strategy Smart Farming Technology Pitch Deck For Food Security to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Acquisitions and Mergers, Initial Public Offerings using this template. Grab it now to reap its full benefits.
-
 Securing strategy implementation ppt examples slides
Securing strategy implementation ppt examples slidesQuick and simple download without any hassles. Modify text anywhere as per the context. Insert your own company logo, tagline, trademark, brand name etc. Absolutely modifiable PPT infographics- change color and contrast as required. No change in resolution of PPT images after editing. Fully alterable size and orientation of presentation icons.The stages in this process are human resource management, strategy, structure, lateral links, rewards systems.
-
 National security strategy ppt images gallery
National security strategy ppt images galleryQuick and simple to download without any hassles. Unchanged original resolution of PPT images after editing. Modify text anywhere to complement the graphics. Absolutely modifiable PPT infographics- change color scheme and contrast. Fully modifiable size and orientation of PPT icons. Add this slide anywhere within your own presentation to maximize impact.The stages in this process are national security strategy, homeland security review, critical infrastructure and climate, execute order.
-
 Securing strategy implementation powerpoint ideas
Securing strategy implementation powerpoint ideasPresenting securing strategy implementation powerpoint ideas. This is a securing strategy implementation powerpoint ideas. This is a five stage process. The stages in this process are strategy, structure, lateral links, reward systems, human resource management.
-
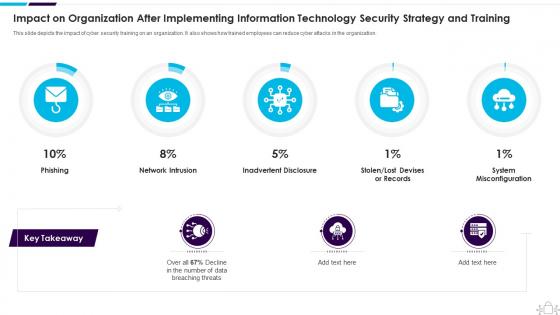 Information Technology Security Impact Organization After Implementing Strategy Training
Information Technology Security Impact Organization After Implementing Strategy TrainingThis slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Present the topic in a bit more detail with this Information Technology Security Impact Organization After Implementing Strategy Training. Use it as a tool for discussion and navigation on Organization, Implementing, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
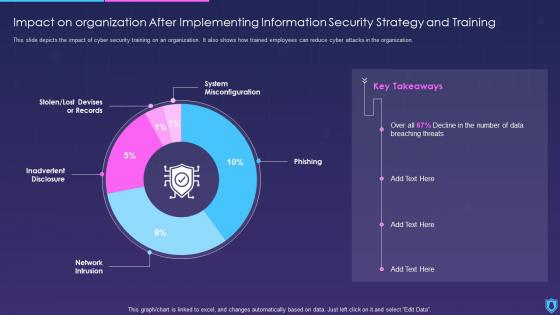 Information Security Impact On Organization After Implementing Information Strategy Training
Information Security Impact On Organization After Implementing Information Strategy TrainingThis slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Present the topic in a bit more detail with this Information Security Impact On Organization After Implementing Information Strategy Training. Use it as a tool for discussion and navigation on Implementing, Information, Strategy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security information and event management successful siem strategies for audit compliance
Security information and event management successful siem strategies for audit complianceThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Present the topic in a bit more detail with this Security Information And Event Management Successful Siem Strategies For Audit Compliance. Use it as a tool for discussion and navigation on Information, Management, Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Building organizational security strategy plan current potential challenges faced by firm
Building organizational security strategy plan current potential challenges faced by firmThis slide provides information about the various potential challenges faced by firm in terms of reported financial losses due to increase in security threats and increase in data breaches and record exposed. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Current Potential Challenges Faced By Firm. Use it as a tool for discussion and navigation on Current Potential Challenges Faced By Firm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
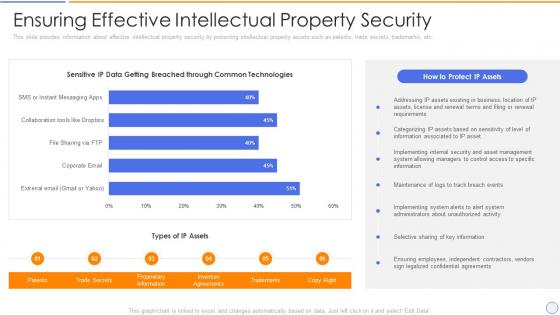 Building organizational security strategy plan ensuring effective intellectual property security
Building organizational security strategy plan ensuring effective intellectual property securityThis slide provides information about effective intellectual property security by protecting intellectual property assets such as patents, trade secrets, trademarks, etc. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Ensuring Effective Intellectual Property Security. Use it as a tool for discussion and navigation on Information, Intellectual, Trademarks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Building organizational security strategy plan impact of critical security concerns issues on overall
Building organizational security strategy plan impact of critical security concerns issues on overallThis slide provides information about the several situations that will result in increase of potential security threats in the organization and addressing various major security concerns at workplace. Introducing Building Organizational Security Strategy Plan Impact Of Critical Security Concerns Issues On Overall to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Performance, Dissatisfaction, Reputation, using this template. Grab it now to reap its full benefits.
-
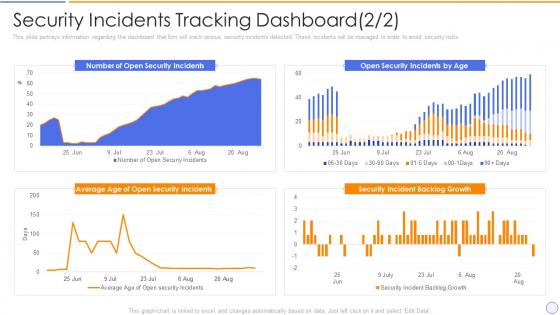 Building organizational security strategy plan security incidents tracking dashboard
Building organizational security strategy plan security incidents tracking dashboardThis slide portrays information regarding the dashboard that firm will track various security incidents detected. These incidents will be managed in order to avoid security risks. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Security Incidents Tracking Dashboard. Use it as a tool for discussion and navigation on Security Incidents Tracking Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
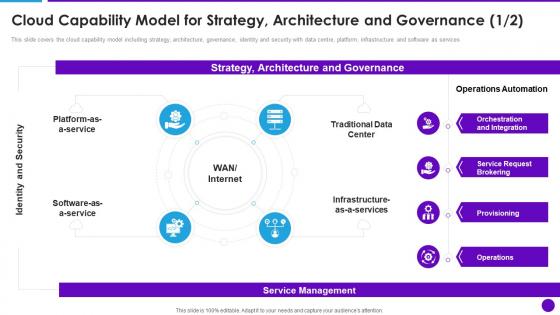 Cloud Architecture And Security Review Cloud Capability Model For Strategy Architecture And Governance
Cloud Architecture And Security Review Cloud Capability Model For Strategy Architecture And GovernanceThis slide covers the cloud capability model including strategy, architecture, governance, identity and security with data centre, platform, infrastructure and software as services. Increase audience engagement and knowledge by dispensing information using Cloud Architecture And Security Review Cloud Capability Model For Strategy Architecture And Governance. This template helps you present information on four stages. You can also present information on Traditional Data Center, Orchestration And Integration, Service Request Brokering using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
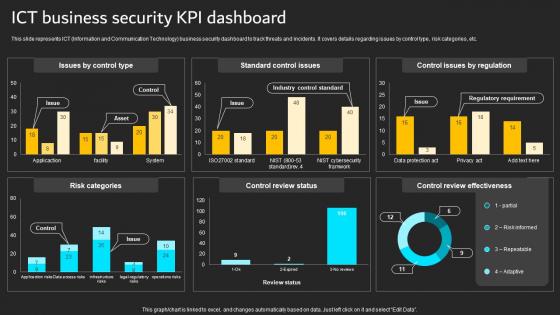 ICT Business Security KPI Dashboard Implementation Of ICT Strategic Plan Strategy SS
ICT Business Security KPI Dashboard Implementation Of ICT Strategic Plan Strategy SSThis slide represents ICT Information and Communication Technology business security dashboard to track threats and incidents. It covers details regarding issues by control type, risk categories, etc.Present the topic in a bit more detail with this ICT Business Security KPI Dashboard Implementation Of ICT Strategic Plan Strategy SS. Use it as a tool for discussion and navigation on Risk Categories, Control Review, Control Review Effectiveness. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
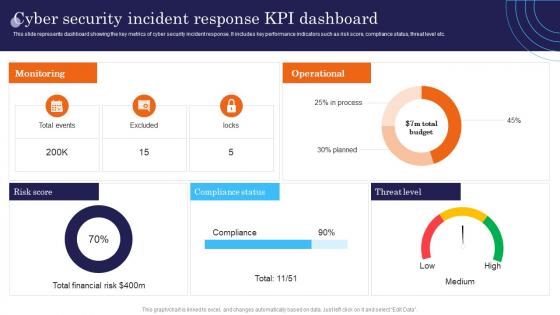 Cyber Security Incident Response KPI Dashboard Incident Response Strategies Deployment
Cyber Security Incident Response KPI Dashboard Incident Response Strategies DeploymentThis slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Deliver an outstanding presentation on the topic using this Cyber Security Incident Response KPI Dashboard Incident Response Strategies Deployment. Dispense information and present a thorough explanation of Monitoring, Operational, Score using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
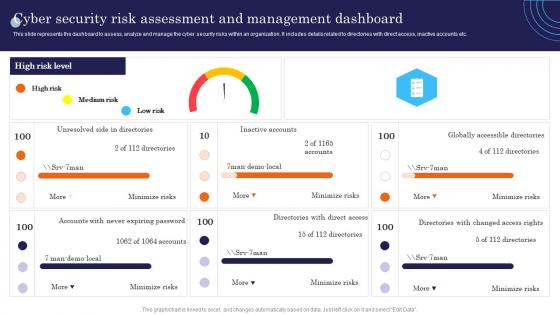 Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment
Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies DeploymentThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Present the topic in a bit more detail with this Cyber Security Risk Assessment And Management Dashboard Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Accounts, Globally, Unresolved. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
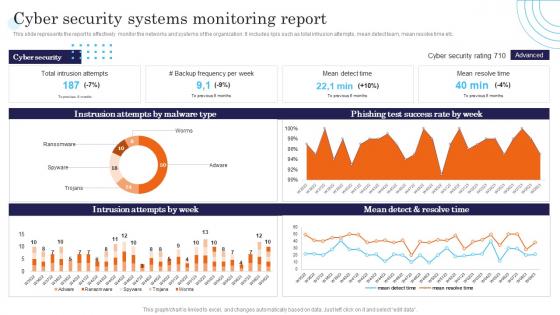 Cyber Security Systems Monitoring Report Incident Response Strategies Deployment
Cyber Security Systems Monitoring Report Incident Response Strategies DeploymentThis slide represents the report to effectively monitor the networks and systems of the organization. It includes kpis such as total intrusion attempts, mean detect team, mean resolve time etc. Present the topic in a bit more detail with this Cyber Security Systems Monitoring Report Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Success, Resolve, Intrusion. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
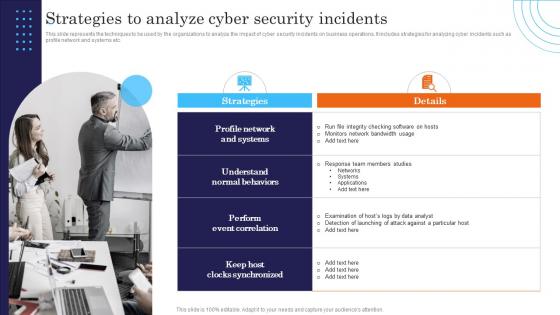 Strategies To Analyze Cyber Security Incidents Response Strategies Deployment
Strategies To Analyze Cyber Security Incidents Response Strategies DeploymentThis slide represents the techniques to be used by the organizations to analyze the impact of cyber security incidents on business operations. It includes strategies for analyzing cyber incidents such as profile network and systems etc. Introducing Strategies To Analyze Cyber Security Incidents Response Strategies Deployment to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Details, Strategies, Correlation, using this template. Grab it now to reap its full benefits.
-
 Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V
Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding effective IT cost optimization strategies for IT executives such as revamping technology procurement, DevOps deployment, enabling business process reengineering, etc. Increase audience engagement and knowledge by dispensing information using Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V. This template helps you present information on four stages. You can also present information on Revamping Technology Procurement, Enabling Business Process Reengineering, Optimization Initiatives using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
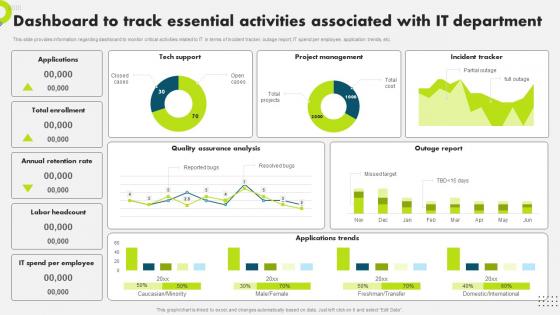 F1471 Dashboard To Track Essential Activities Strategic Plan To Secure It Infrastructure Strategy SS V
F1471 Dashboard To Track Essential Activities Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding dashboard to monitor critical activities related to IT in terms of incident tracker, outage report, IT spend per employee, application trends, etc. Present the topic in a bit more detail with this F1471 Dashboard To Track Essential Activities Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Dashboard, Associated, Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It Performance Dashboard To Track Customer Strategic Plan To Secure It Infrastructure Strategy SS V
It Performance Dashboard To Track Customer Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the dashboard to monitor overall IT performance. The dashboard tracks occupancy rate, net promoter score, avg. first contact resolution rate, etc. Present the topic in a bit more detail with this It Performance Dashboard To Track Customer Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Performance, Dashboard, Satisfaction. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
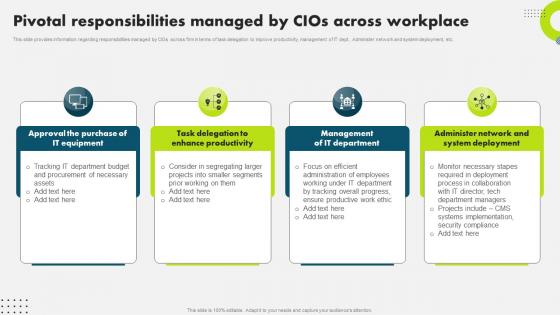 Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS V
Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding responsibilities managed by CIOs across firm in terms of task delegation to improve productivity, management of IT dept., Administer network and system deployment, etc. Present the topic in a bit more detail with this Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Responsibilities, Management, Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
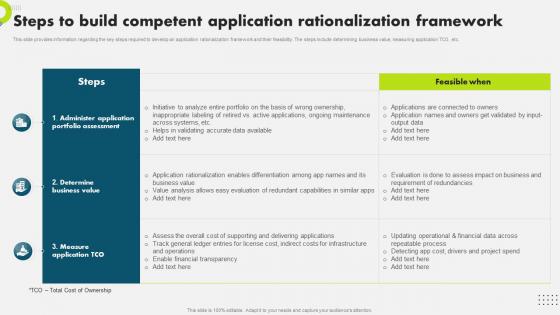 Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V
Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the key steps required to develop an application rationalization framework and their feasibility. The steps include determining business value, measuring application TCO, etc. Present the topic in a bit more detail with this Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Application, Rationalization, Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps To Develop Targeted Marketing Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V
Steps To Develop Targeted Marketing Initiatives Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information various steps required to develop target marketing initiatives for IT department. The initiatives include detect target market, conduct market research, develop objectives and goals, etc. Introducing Steps To Develop Targeted Marketing Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Marketing, Initiatives, Department, using this template. Grab it now to reap its full benefits.
-
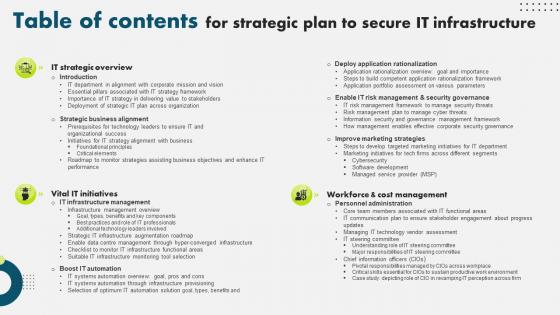 Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS V
Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS VPresent the topic in a bit more detail with this Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Strategic Business Alignment, Workforce And Cost Management, Deploy Application Rationalization . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Competitive Analysis Of Major How Amazon Is Securing Competitive Edge Across Globe Strategy SS
Competitive Analysis Of Major How Amazon Is Securing Competitive Edge Across Globe Strategy SSThis slide provides information regarding comparative analysis of potential players existing across marketplace. The points of differentiation include financial parameters, critical success factors such as product variety, customer services, email marketing, etc. Present the topic in a bit more detail with this Competitive Analysis Of Major How Amazon Is Securing Competitive Edge Across Globe Strategy SS. Use it as a tool for discussion and navigation on Ecommerce Market Share, Ecommerce Ecosystem, Dynamics. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
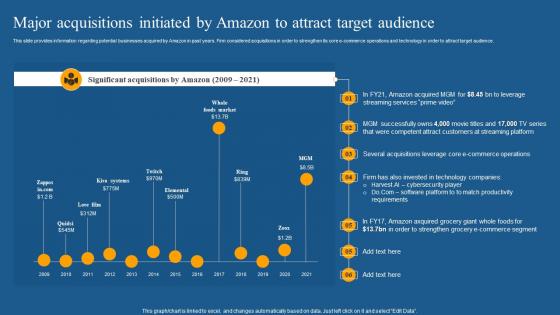 Major Acquisitions Initiated How Amazon Is Securing Competitive Edge Across Globe Strategy SS
Major Acquisitions Initiated How Amazon Is Securing Competitive Edge Across Globe Strategy SSThis slide provides information regarding potential businesses acquired by Amazon in past years. Firm considered acquisitions in order to strengthen its core e commerce operations and technology in order to attract target audience. Present the topic in a bit more detail with this Major Acquisitions Initiated How Amazon Is Securing Competitive Edge Across Globe Strategy SS. Use it as a tool for discussion and navigation on E Commerce Operations, Technology, Cybersecurity Player. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
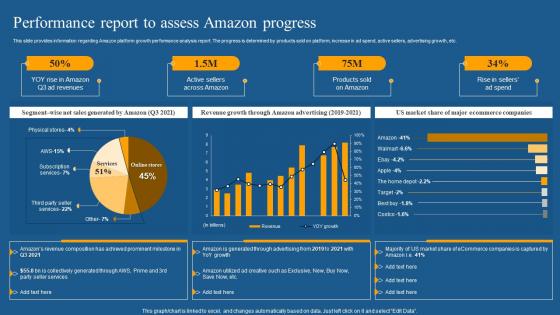 Performance Report To Assess How Amazon Is Securing Competitive Edge Across Globe Strategy SS
Performance Report To Assess How Amazon Is Securing Competitive Edge Across Globe Strategy SSThis slide provides information regarding Amazon platform growth performance analysis report. The progress is determined by products sold on platform, increase in ad spend, active sellers, advertising growth, etc. Deliver an outstanding presentation on the topic using this Performance Report To Assess How Amazon Is Securing Competitive Edge Across Globe Strategy SS. Dispense information and present a thorough explanation of Revenue Growth, Amazon Advertising, Market Share using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Significant Business Research How Amazon Is Securing Competitive Edge Across Globe Strategy SS
Significant Business Research How Amazon Is Securing Competitive Edge Across Globe Strategy SSThis slide provides information regarding potential business and research collaboration initiated by Amazon. The focus of Amazon is to cooperate with credible, knowledgeable, innovative industry partners who share similar vision such as microsoft, ford, etc. Introducing Significant Business Research How Amazon Is Securing Competitive Edge Across Globe Strategy SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Implemented, Security Systems, Capability, using this template. Grab it now to reap its full benefits.
-
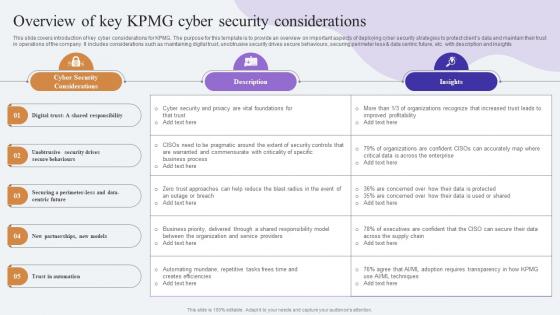 Overview Of Key KPMG Cyber Security Comprehensive Guide To KPMG Strategy SS
Overview Of Key KPMG Cyber Security Comprehensive Guide To KPMG Strategy SSThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less data centric future, etc. with description and insights.Present the topic in a bit more detail with this Overview Of Key KPMG Cyber Security Comprehensive Guide To KPMG Strategy SS. Use it as a tool for discussion and navigation on Security Considerations, Warranted Commensurate, Automating Mundane. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
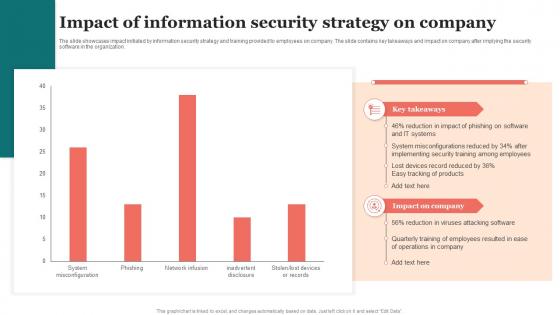 Impact Of Information Security Strategy On Company
Impact Of Information Security Strategy On CompanyThe slide showcases impact initiated by information security strategy and training provided to employees on company. The slide contains key takeaways and impact on company after implying the security software in the organization. Presenting our well structured Impact Of Information Security Strategy On Company. The topics discussed in this slide are Impact Of Information, Security, Strategy On Company. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
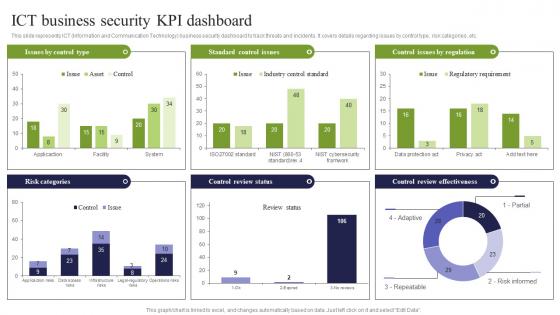 ICT Business Security KPI Dashboard ICT Strategic Framework Strategy SS V
ICT Business Security KPI Dashboard ICT Strategic Framework Strategy SS VThis slide represents ICT Information and Communication Technology business security dashboard to track threats and incidents. It covers details regarding issues by control type, risk categories, etc. Present the topic in a bit more detail with this ICT Business Security KPI Dashboard ICT Strategic Framework Strategy SS V. Use it as a tool for discussion and navigation on Standard Control Issues, Control Issues By Regulation, Risk Categories. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
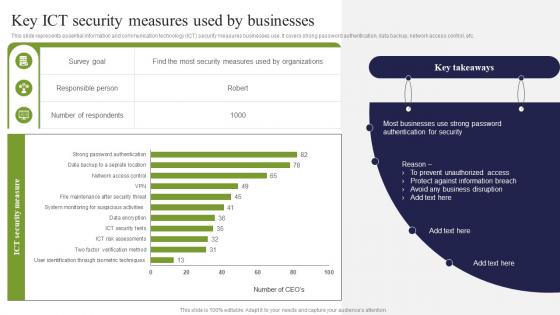 Key ICT Security Measures Used By Businesses ICT Strategic Framework Strategy SS V
Key ICT Security Measures Used By Businesses ICT Strategic Framework Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Present the topic in a bit more detail with this Key ICT Security Measures Used By Businesses ICT Strategic Framework Strategy SS V. Use it as a tool for discussion and navigation on Responsible Person, Number Of Respondents, Businesses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber threat strategies for security protection
Cyber threat strategies for security protectionThis slide highlights the cyber threat strategies that include risk assessment, phishing program, software protocols and end point protection. Presenting our set of slides with Cyber Threat Strategies For Security Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Program, Software Protocols, End Point Protection.
-
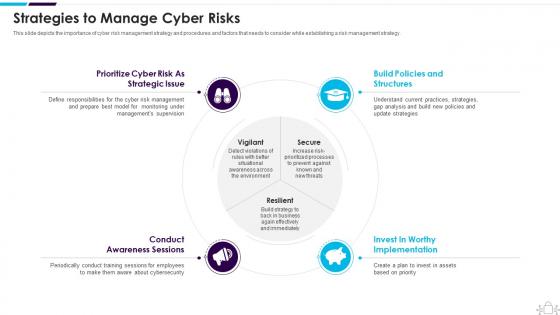 Information Technology Security Strategies To Manage Cyber Risks
Information Technology Security Strategies To Manage Cyber RisksThis slide depicts the importance of cyber risk management strategy and procedures and factors that needs to consider while establishing a risk management strategy. Increase audience engagement and knowledge by dispensing information using Information Technology Security Strategies To Manage Cyber Risks. This template helps you present information on four stages. You can also present information on Strategic, Structures, Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
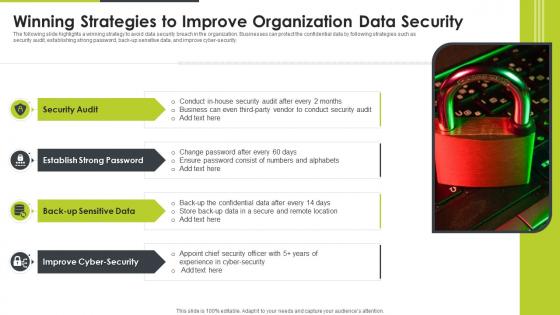 Winning Strategies To Improve Organization Data Security
Winning Strategies To Improve Organization Data SecurityThe following slide highlights a winning strategy to avoid data security breach in the organization. Businesses can protect the confidential data by following strategies such as security audit, establishing strong password, back up sensitive data, and improve cyber-security. Introducing our premium set of slides with Winning Strategies To Improve Organization Data Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Audit, Improve Cyber Security, Back Up Sensitive Data. So download instantly and tailor it with your information.
-
 Strategies For Safety And Security In Hotel Industry
Strategies For Safety And Security In Hotel IndustryThis slide outlines measures to ensure safety and security in hospitality sectors. It highlights four basic ways i.e. cyber security, add intelligence to video surveillance, internal theft and fraud and establish evergreen background screening protocol. Introducing our Strategies For Safety And Security In Hotel Industry set of slides. The topics discussed in these slides are Strategies, Intelligence, Surveillance. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
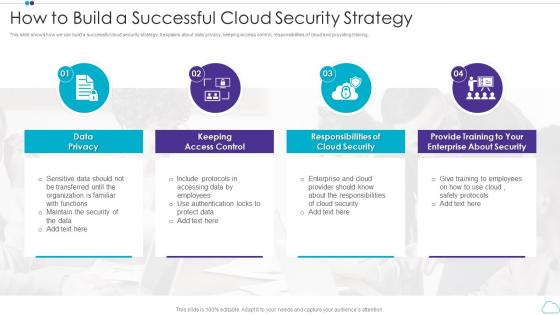 How To Build A Successful Cloud Security Strategy
How To Build A Successful Cloud Security StrategyThis slide shows how we can build a successful cloud security strategy. It explains about data privacy, keeping access control, responsibilities of cloud and providing training. Introducing our premium set of slides with How To Build A Successful Cloud Security Strategy. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Privacy, Keeping Access Control, Responsibilities Of Cloud Security, Provide Training To Your Enterprise About Security. So download instantly and tailor it with your information.
-
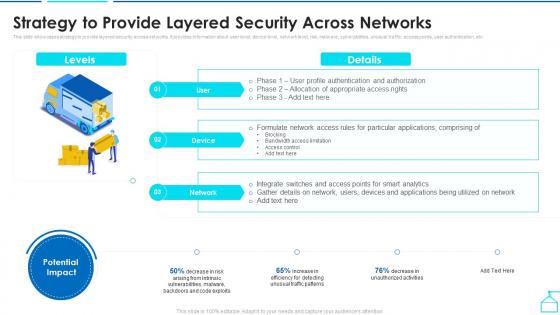 Strategy To Provide Layered Security Across Networks Enabling Smart Shipping And Logistics Through Iot
Strategy To Provide Layered Security Across Networks Enabling Smart Shipping And Logistics Through IotThis slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Deliver an outstanding presentation on the topic using this Strategy To Provide Layered Security Across Networks Enabling Smart Shipping And Logistics Through Iot. Dispense information and present a thorough explanation of Applications, Bandwidth Access Limitation, Strategy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 F267 Strategies To Enhance Retail Store Security Retail Store Operations Performance Assessment
F267 Strategies To Enhance Retail Store Security Retail Store Operations Performance AssessmentThis slide provides information regarding the strategies to enhance retail store security such as integrate access control technology, deploy video surveillance, utilizes electronic article surveillance, install monitored alarms. Increase audience engagement and knowledge by dispensing information using F267 Strategies To Enhance Retail Store Security Retail Store Operations Performance Assessment. This template helps you present information on four stages. You can also present information on Technology, Surveillance, Strategies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
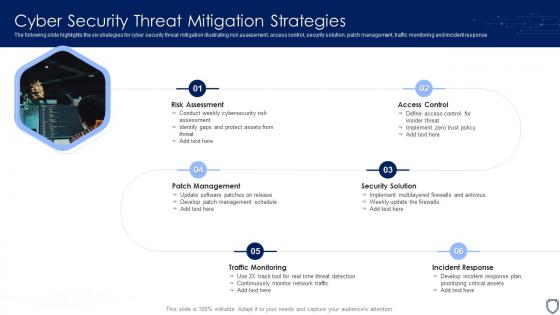 Cyber Security Threat Mitigation Strategies
Cyber Security Threat Mitigation StrategiesThe following slide highlights the six strategies for cyber security threat mitigation illustrating risk assessment, access control, security solution, patch management, traffic monitoring and incident response. Presenting our set of slides with name Cyber Security Threat Mitigation Strategies. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Risk Assessment, Patch Management, Traffic Monitoring.
-
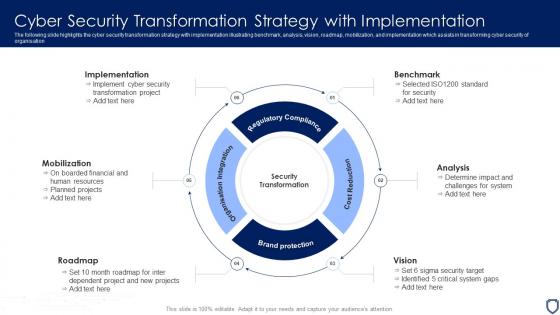 Cyber Security Transformation Strategy With Implementation
Cyber Security Transformation Strategy With ImplementationThe following slide highlights the cyber security transformation strategy with implementation illustrating benchmark, analysis, vision, roadmap, mobilization, and implementation which assists in transforming cyber security of organisation. Introducing our premium set of slides with name Cyber Security Transformation Strategy With Implementation. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Implementation, Mobilization, Vision, Analysis. So download instantly and tailor it with your information.
-
 Business Development Strategy Wireless Home Security Systems Company Profile
Business Development Strategy Wireless Home Security Systems Company ProfileThis slide highlights the security company channel expansion strategy which showcases strategies for retail, multifamily and professional channels including instore lead generation and robust product offerings. Increase audience engagement and knowledge by dispensing information using Business Development Strategy Wireless Home Security Systems Company Profile. This template helps you present information on three stages. You can also present information on Retail, Multifamily, Professional Channels using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
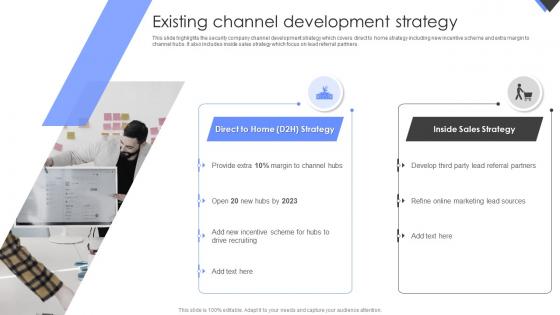 Existing Channel Development Strategy Wireless Home Security Systems Company Profile
Existing Channel Development Strategy Wireless Home Security Systems Company ProfileThis slide highlights the security company channel development strategy which covers direct to home strategy including new incentive scheme and extra margin to channel hubs. It also includes inside sales strategy which focus on lead referral partners. Introducing Existing Channel Development Strategy Wireless Home Security Systems Company Profile to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispense information on Direct To Home Strategy, Inside Sales Strategy, using this template. Grab it now to reap its full benefits.
-
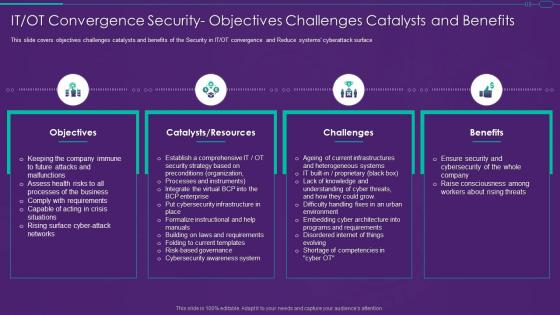 It Ot Convergence Strategy Security Objectives Challenges Catalysts And Benefits
It Ot Convergence Strategy Security Objectives Challenges Catalysts And BenefitsThis slide covers objectives challenges catalysts and benefits of the Security in IT or OT convergence and Reduce systems cyberattack surface Present the topic in a bit more detail with this It Ot Convergence Strategy Security Objectives Challenges Catalysts And Benefits. Use it as a tool for discussion and navigation on Objectives, Catalysts Resources, Challenges. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
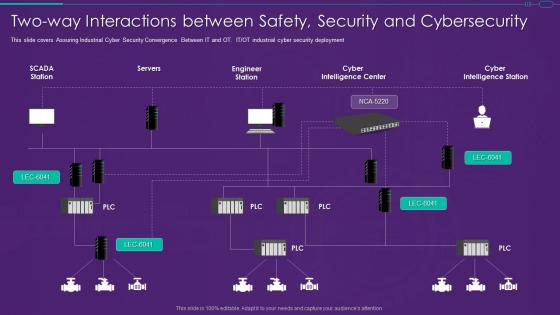 It Ot Convergence Strategy Two Way Interactions Between Safety Security And Cybersecurity
It Ot Convergence Strategy Two Way Interactions Between Safety Security And CybersecurityThis slide covers Assuring Industrial Cyber Security Convergence Between IT and OT. IT or OT industrial cyber security deployment Present the topic in a bit more detail with this It Ot Convergence Strategy Two Way Interactions Between Safety Security And Cybersecurity. Use it as a tool for discussion and navigation on Interactions, Security, Cybersecurity This template is free to edit as deemed fit for your organization. Therefore download it now.
-
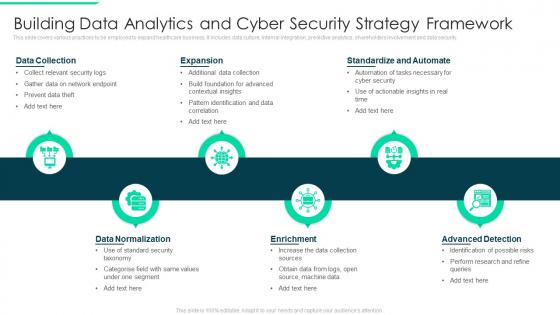 Building Data Analytics And Cyber Security Strategy Framework
Building Data Analytics And Cyber Security Strategy FrameworkThis slide covers various practices to be employed to expand healthcare business. It includes data culture, internal integration, predictive analytics, shareholders involvement and data security. Introducing our premium set of slides with Building Data Analytics And Cyber Security Strategy Framework. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Collection, Data Normalization, Expansion. So download instantly and tailor it with your information.
-
 Cyber Security Strategy Roadmap Icon With Lock Symbol
Cyber Security Strategy Roadmap Icon With Lock SymbolPresenting our set of slides with name Cyber Security Strategy Roadmap Icon With Lock Symbol. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Strategy Roadmap Icon With Lock Symbol.
-
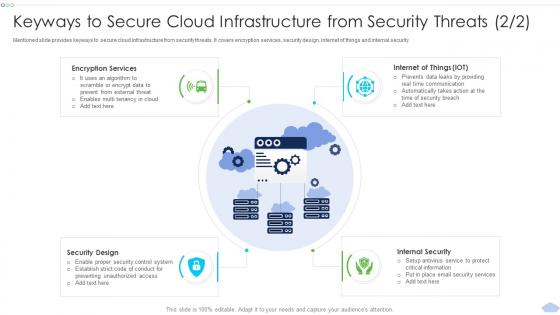 Keyways To Secure Cloud Infrastructure Strategies To Implement Cloud Computing Infrastructure
Keyways To Secure Cloud Infrastructure Strategies To Implement Cloud Computing InfrastructureMentioned slide provides keyways to secure cloud infrastructure from security threats. It covers encryption services, security design, internet of things and internal security. Introducing Keyways To Secure Cloud Infrastructure Strategies To Implement Cloud Computing Infrastructure to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Encryption Services, Internal Security, Security Design, using this template. Grab it now to reap its full benefits.
-
 Business Development Strategy Home Security Systems Company Profile
Business Development Strategy Home Security Systems Company ProfileThis slide highlights the security company channel expansion strategy which showcases strategies for retail, multifamily and professional channels including instore lead generation and robust product offerings. Increase audience engagement and knowledge by dispensing information using Business Development Strategy Home Security Systems Company Profile . This template helps you present information on three stages. You can also present information on Business, Development, Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Existing Channel Development Strategy Home Security Systems Company Profile
Existing Channel Development Strategy Home Security Systems Company ProfileThis slide highlights the security company channel development strategy which covers direct to home strategy including new incentive scheme and extra margin to channel hubs. It also includes inside sales strategy which focus on lead referral partners. Present the topic in a bit more detail with this Existing Channel Development Strategy Home Security Systems Company Profile . Use it as a tool for discussion and navigation on Development, Strategy, Sources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
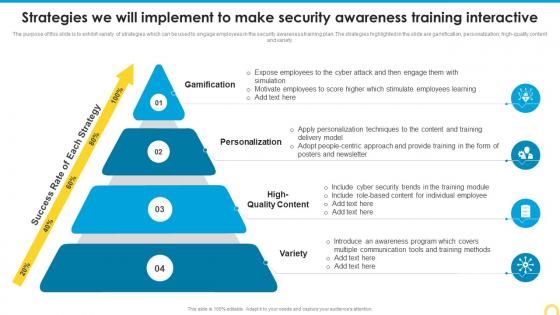 Strategies We Will Implement To Make Building A Security Awareness Program
Strategies We Will Implement To Make Building A Security Awareness ProgramThe purpose of this slide is to exhibit variety of strategies which can be used to engage employees in the security awareness training plan. The strategies highlighted in the slide are gamification, personalization, high quality content and variety. Increase audience engagement and knowledge by dispensing information using Strategies We Will Implement To Make Building A Security Awareness Program. This template helps you present information on four stages. You can also present information on Gamification, Personalization, High Quality Content using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Hacker 30 60 90 Days Plan For New Strategies Implementation Ppt Information
Security Hacker 30 60 90 Days Plan For New Strategies Implementation Ppt InformationThis slide represents the 30 60 90 days plan to implement new strategies in the company, including the tasks performed in each month interval. Increase audience engagement and knowledge by dispensing information using Security Hacker 30 60 90 Days Plan For New Strategies Implementation Ppt Information. This template helps you present information on three stages. You can also present information on 30 Days, 60 Days, 90 Days using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.