Powerpoint Templates and Google slides for Security Strategy
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Building organizational security strategy plan powerpoint presentation slides
Building organizational security strategy plan powerpoint presentation slidesDeliver an informational PPT on various topics by using this Building Organizational Security Strategy Plan Powerpoint Powerpoint Presentation. This deck focuses and implements best industry practices, thus providing a birds-eye view of the topic. Encompassed with eighty two slides, designed using high-quality visuals and graphics, this deck is a complete package to use and download. All the slides offered in this deck are subjective to innumerable alterations, thus making you a pro at delivering and educating. You can modify the color of the graphics, background, or anything else as per your needs and requirements. It suits every business vertical because of its adaptable layout.
-
 Strategic Plan To Secure IT Infrastructure Powerpoint Presentation Slides Strategy CD V
Strategic Plan To Secure IT Infrastructure Powerpoint Presentation Slides Strategy CD VDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Strategic Plan To Secure IT Infrastructure Powerpoint Presentation Slides Strategy CD V is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the seventy seven slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Delivering ICT Services For Enhanced Business Security Powerpoint Presentation Slides Strategy CD V
Delivering ICT Services For Enhanced Business Security Powerpoint Presentation Slides Strategy CD VDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Delivering ICT Services For Enhanced Business Security Powerpoint Presentation Slides Strategy CD V is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the sixty nine slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Implementing Strategies To Mitigate Cyber Security Threats Powerpoint Presentation Slides
Implementing Strategies To Mitigate Cyber Security Threats Powerpoint Presentation SlidesDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Implementing Strategies To Mitigate Cyber Security Threats Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the sixty slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Cyber Security Strategy Powerpoint Ppt Template Bundles
Cyber Security Strategy Powerpoint Ppt Template BundlesIf you require a professional template with great design, then this Cyber Security Strategy Powerpoint Ppt Template Bundles is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using twenty three slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 How Amazon Is Securing Competitive Edge Across Globe Powerpoint Ppt Template Bundles Strategy MD
How Amazon Is Securing Competitive Edge Across Globe Powerpoint Ppt Template Bundles Strategy MDIntroduce your topic and host expert discussion sessions with this How Amazon Is Securing Competitive Edge Across Globe Powerpoint Ppt Template Bundles Strategy MD. This template is designed using high-quality visuals, images, graphics, etc, that can be used to showcase your expertise. Different topics can be tackled using the seventeen slides included in this template. You can present each topic on a different slide to help your audience interpret the information more effectively. Apart from this, this PPT slideshow is available in two screen sizes, standard and widescreen making its delivery more impactful. This will not only help in presenting a birds-eye view of the topic but also keep your audience engaged. Since this PPT slideshow utilizes well-researched content, it induces strategic thinking and helps you convey your message in the best possible manner. The biggest feature of this design is that it comes with a host of editable features like color, font, background, etc. So, grab it now to deliver a unique presentation every time.
-
 Eight stage infographic analysis profitability cyber security social media strategy
Eight stage infographic analysis profitability cyber security social media strategyIf you require a professional template with great design, then this Eight Stage Infographic Analysis Profitability Cyber Security Social Media Strategy is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using twelve slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Security Management Plan Measures Strategy Framework Symbol Assessment Improving
Security Management Plan Measures Strategy Framework Symbol Assessment ImprovingEngage buyer personas and boost brand awareness by pitching yourself using this prefabricated set. This Security Management Plan Measures Strategy Framework Symbol Assessment Improving is a great tool to connect with your audience as it contains high-quality content and graphics. This helps in conveying your thoughts in a well-structured manner. It also helps you attain a competitive advantage because of its unique design and aesthetics. In addition to this, you can use this PPT design to portray information and educate your audience on various topics. With twelve slides, this is a great design to use for your upcoming presentations. Not only is it cost-effective but also easily pliable depending on your needs and requirements. As such color, font, or any other design component can be altered. It is also available for immediate download in different formats such as PNG, JPG, etc. So, without any further ado, download it now.
-
 Data security it impact on organization after implementing data security strategy
Data security it impact on organization after implementing data security strategyThis slide depicts the impact of data security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Deliver an outstanding presentation on the topic using this Data Security IT Impact On Organization After Implementing Data Security Strategy. Dispense information and present a thorough explanation of Phishing, Network Intrusion, Inadvertent Disclosure, System Misconfiguration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ict Business Security Kpi Dashboard Comprehensive Guide For Deployment Strategy SS V
Ict Business Security Kpi Dashboard Comprehensive Guide For Deployment Strategy SS VThis slide represents ICT Information and Communication Technology business security dashboard to track threats and incidents It covers details regarding issues by control type, risk categories, etc Deliver an outstanding presentation on the topic using this Ict Business Security Kpi Dashboard Comprehensive Guide For Deployment Strategy SS V Dispense information and present a thorough explanation of Risk Categories, Control Review Status, Standard Control Issues using the slides given This template can be altered and personalized to fit your needs It is also available for immediate download So grab it now
-
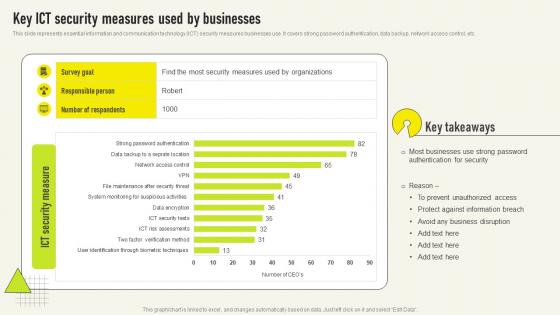 Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V
Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use It covers strong password authentication, data backup, network access control, etc Presenting our well structured Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V The topics discussed in this slide are Authentication Security, Most Businesses, Protect Against This is an instantly available PowerPoint presentation that can be edited conveniently Download it right away and captivate your audience
-
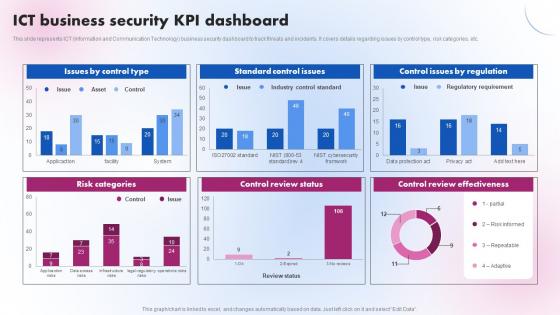 ICT Business Security KPI Dashboard Delivering ICT Services For Enhanced Business Strategy SS V
ICT Business Security KPI Dashboard Delivering ICT Services For Enhanced Business Strategy SS VThis slide represents ICT Information and Communication Technology business security dashboard to track threats and incidents. It covers details regarding issues by control type, risk categories, etc. Present the topic in a bit more detail with this ICT Business Security KPI Dashboard Delivering ICT Services For Enhanced Business Strategy SS V. Use it as a tool for discussion and navigation on Standard Control Issues, Control Review Status. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
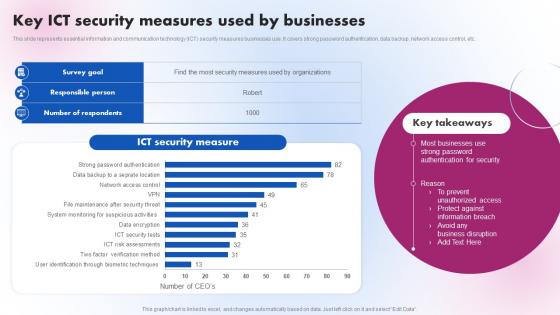 Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS V
Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Present the topic in a bit more detail with this Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS V. Use it as a tool for discussion and navigation on Security Measure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
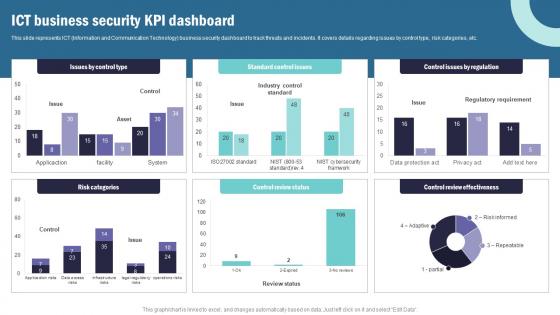 Strategic Plan To Implement Ict Business Security Kpi Dashboard Strategy SS V
Strategic Plan To Implement Ict Business Security Kpi Dashboard Strategy SS VThis slide represents ICT Information and Communication Technology business security dashboard to track threats and incidents. It covers details regarding issues by control type, risk categories, etc. Present the topic in a bit more detail with this Strategic Plan To Implement Ict Business Security Kpi Dashboard Strategy SS V Use it as a tool for discussion and navigation on Organisational Capability Framework, Performance Appraisal, Feedback System This template is free to edit as deemed fit for your organization. Therefore download it now.
-
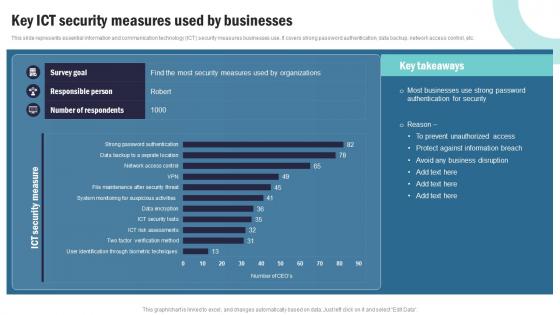 Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS V
Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Present the topic in a bit more detail with this Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS V Use it as a tool for discussion and navigation on Data Sets And Compliance, IT Service Planning This template is free to edit as deemed fit for your organization. Therefore download it now.
-
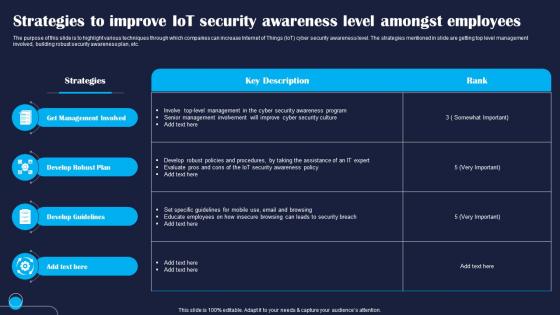 Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SS
Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight various techniques through which companies can increase Internet of Things IoT cyber security awareness level. The strategies mentioned in slide are getting top level management involved, building robust security awareness plan, etc. Present the topic in a bit more detail with this Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Management, Develop, Guidelines. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
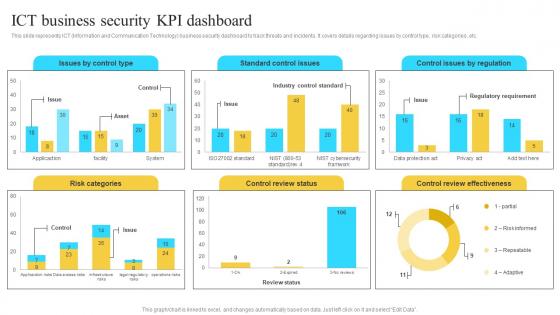 Implementation Of Information Ict Business Security Kpi Dashboard Strategy SS V
Implementation Of Information Ict Business Security Kpi Dashboard Strategy SS VThis slide represents ICT Information and Communication Technology business security dashboard to track threats and incidents. It covers details regarding issues by control type, risk categories, etc. Present the topic in a bit more detail with this Implementation Of Information Ict Business Security Kpi Dashboard Strategy SS V. Use it as a tool for discussion and navigation on Issues By Control Type, Standard Control Issues. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
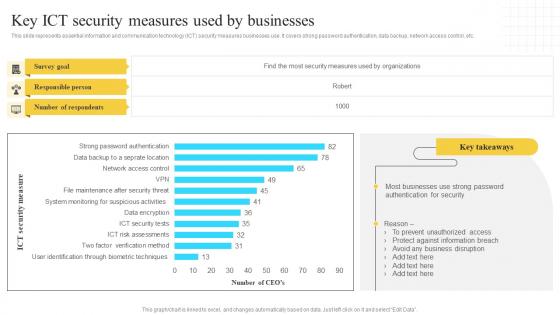 Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS V
Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Deliver an outstanding presentation on the topic using this Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS V. Dispense information and present a thorough explanation of Survey Goal, Responsible Person using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
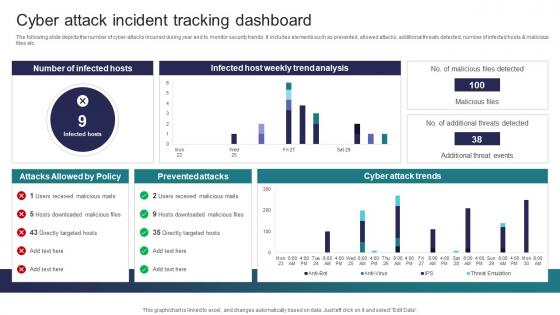 Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security Threats
Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the number of cyber attacks incurred during year end to monitor security trends. It includes elements such as prevented, allowed attacks, additional threats detected, number of infected hosts and malicious files etc. Present the topic in a bit more detail with this Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Prevented Attacks, Cyber Attack Trends This template is free to edit as deemed fit for your organization. Therefore download it now.
-
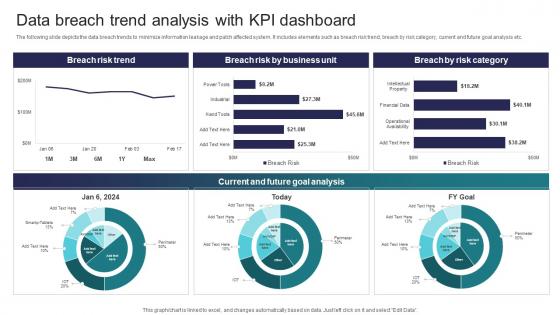 Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security Threats
Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the data breach trends to minimize information leakage and patch affected system. It includes elements such as breach risk trend, breach by risk category, current and future goal analysis etc. Present the topic in a bit more detail with this Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Current And Future Goal Analysis, Breach Risk Trend This template is free to edit as deemed fit for your organization. Therefore download it now.
-
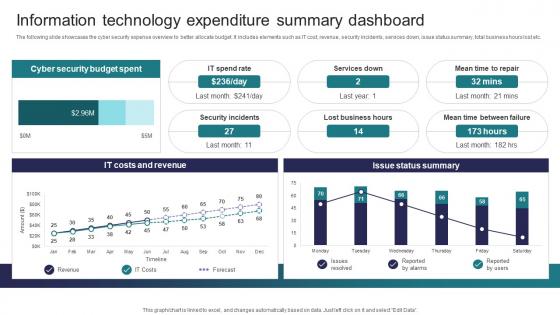 Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security Threats
Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the cyber security expense overview to better allocate budget. It includes elements such as IT cost, revenue, security incidents, services down, issue status summary, total business hours lost etc. Deliver an outstanding presentation on the topic using this Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Cyber Security Budget Spent, It Costs And Revenue, Issue Status Summary using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
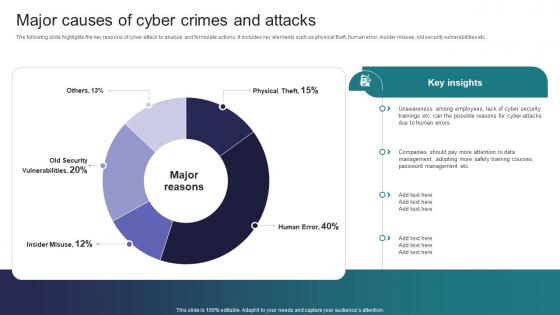 Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security Threats
Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights the key reasons of cyber attack to analyze and formulate actions. It includes key elements such as physical theft, human error, insider misuse, old security vulnerabilities etc. Deliver an outstanding presentation on the topic using this Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Employees, Management, Training Courses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
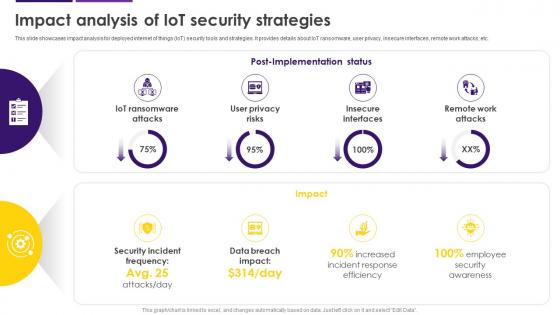 Impact Analysis Of IoT Security Strategies Internet Of Things IoT Security Cybersecurity SS
Impact Analysis Of IoT Security Strategies Internet Of Things IoT Security Cybersecurity SSThis slide showcases impact analysis for deployed internet of things IoT security tools and strategies. It provides details about IoT ransomware, user privacy, insecure interfaces, remote work attacks, etc. Present the topic in a bit more detail with this Impact Analysis Of IoT Security Strategies Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on Internet Of Things, Security Tools And Strategies, IoT Ransomware, Remote Work Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
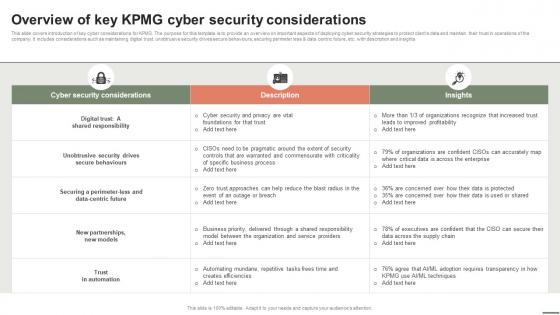 Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS V
Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS VThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less and data centric future, etc. with description and insights Present the topic in a bit more detail with this Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS V. Use it as a tool for discussion and navigation on Cyber Security Considerations, Description, Insights. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
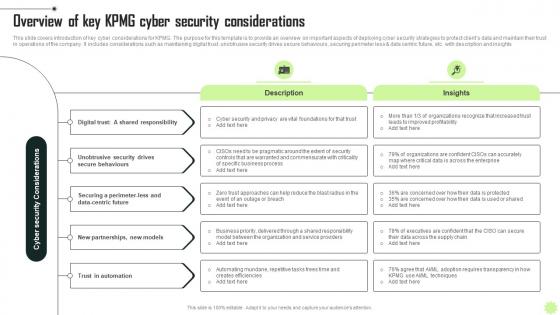 Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V
Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS VThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less and data centric future, etc. with description and insights Increase audience engagement and knowledge by dispensing information using Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V. This template helps you present information on five stages. You can also present information on Digital, Security, Automation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
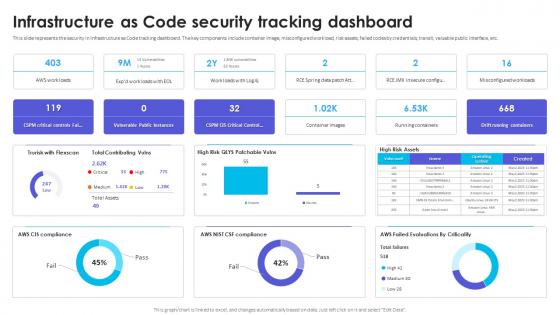 Infrastructure As Code Security Tracking Dashboard Infrastructure As Code Adoption Strategy
Infrastructure As Code Security Tracking Dashboard Infrastructure As Code Adoption StrategyThis slide represents the security in Infrastructure as Code tracking dashboard. The key components include container image, misconfigured workload, risk assets, failed codes by credentials, transit, valuable public interface, etc. Deliver an outstanding presentation on the topic using this Infrastructure As Code Security Tracking Dashboard Infrastructure As Code Adoption Strategy. Dispense information and present a thorough explanation of Security In Infrastructure, Code Tracking Dashboard, Misconfigured Workload, Risk Assets, Valuable Public Interface using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Circle With 4 Quadrants Organization Security Allowance Business Operational Marketing Strategies
Circle With 4 Quadrants Organization Security Allowance Business Operational Marketing StrategiesThis complete presentation has PPT slides on wide range of topics highlighting the core areas of your business needs. It has professionally designed templates with relevant visuals and subject driven content. This presentation deck has total of ten slides. Get access to the customizable templates. Our designers have created editable templates for your convenience. You can edit the colour, text and font size as per your need. You can add or delete the content if required. You are just a click to away to have this ready-made presentation. Click the download button now.
-
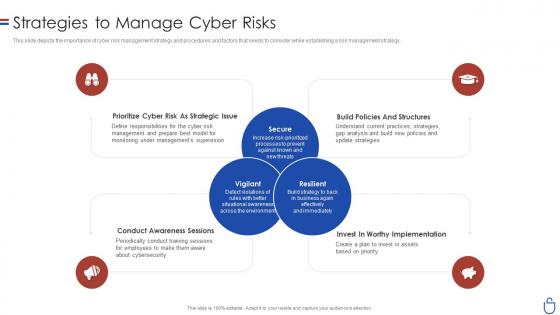 Data security it strategies to manage cyber risks ppt slides clipart images
Data security it strategies to manage cyber risks ppt slides clipart imagesThis slide depicts the importance of cyber risk management strategy and procedures and factors that needs to consider while establishing a risk management strategy. Introducing Data Security IT Strategies To Manage Cyber Risks Ppt Slides Clipart Images to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prioritize Cyber Risk As Strategic Issue, Conduct Awareness Sessions, Invest Worthy Implementation, Build Policies And Structures, using this template. Grab it now to reap its full benefits.
-
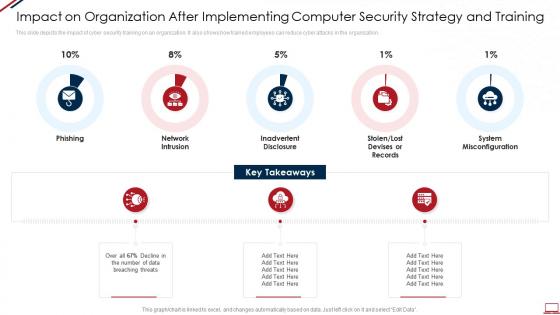 Computer system security impact on organization after implementing computer security strategy and training
Computer system security impact on organization after implementing computer security strategy and trainingThis slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Increase audience engagement and knowledge by dispensing information using Computer System Security Impact On Organization After Implementing Computer Security Strategy And Training. This template helps you present information on five stages. You can also present information on Phishing, Network Intrusion, Inadvertent Disclosure, Stolen Or Lost Devises Or Records, System Misconfiguration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
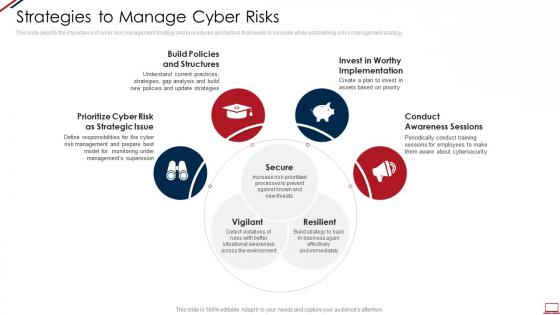 Computer system security strategies to manage cyber risks
Computer system security strategies to manage cyber risksThis slide depicts the importance of cyber risk management strategy and procedures and factors that needs to consider while establishing a risk management strategy. Introducing Computer System Security Strategies To Manage Cyber Risks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Secure, Vigilant, Resilient, Implementation, Awareness, using this template. Grab it now to reap its full benefits.
-
 Information security strategy ppt powerpoint presentation icon example cpb
Information security strategy ppt powerpoint presentation icon example cpbPresenting Information Security Strategy Ppt Powerpoint Presentation Icon Example Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Information Security Strategy. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
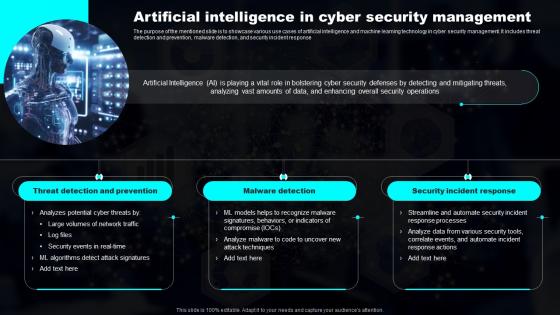 Artificial Intelligence In Cyber Security Transforming Industries With AI ML And NLP Strategy
Artificial Intelligence In Cyber Security Transforming Industries With AI ML And NLP StrategyThe purpose of the mentioned slide is to showcase various use cases of artificial intelligence and machine learning technology in cyber security management. It includes threat detection and prevention, malware detection, and security incident response Increase audience engagement and knowledge by dispensing information using Artificial Intelligence In Cyber Security Transforming Industries With AI ML And NLP Strategy. This template helps you present information on three stages. You can also present information on Prevention, Detection, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Budget Securing Tips For Public Relations Brand Positioning Strategies To Boost Online MKT SS V
Budget Securing Tips For Public Relations Brand Positioning Strategies To Boost Online MKT SS VThis slide shows various tips which can be used by organizations to while developing marketing budget. It includes aligning marketing outcome with organizational goals, strategic insights and highlight impacts. Increase audience engagement and knowledge by dispensing information using Budget Securing Tips For Public Relations Brand Positioning Strategies To Boost Online MKT SS V. This template helps you present information on three stages. You can also present information on Company, Strategic, Impacts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 4 Steps For Building Digital Security Strategy
4 Steps For Building Digital Security StrategyThis slide showcase developing and implementation of cyber security strategy for streamline the data security and organization vision and mission. It includes cyber threat landscape, assess cybersecurity maturity, determine security program and document cybersecurity strategy Presenting our set of slides with 4 Steps For Building Digital Security Strategy. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Building, Digital, Security.
-
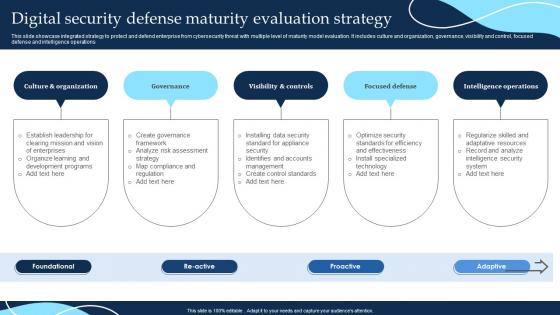 Digital Security Defense Maturity Evaluation Strategy
Digital Security Defense Maturity Evaluation StrategyThis slide showcase integrated strategy to protect and defend enterprise from cybersecurity threat with multiple level of maturity model evaluation. It includes culture and organization, governance, visibility and control, focused defense and intelligence operations Introducing our premium set of slides with Digital Security Defense Maturity Evaluation Strategy. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Organization, Governance, Visibility. So download instantly and tailor it with your information.
-
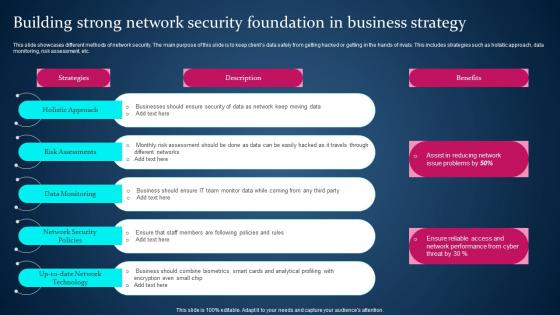 Building Strong Network Security Foundation In Business Strategy
Building Strong Network Security Foundation In Business StrategyThis slide showcases different methods of network security. The main purpose of this slide is to keep clients data safely from getting hacked or getting in the hands of rivals. This includes strategies such as holistic approach, data monitoring, risk assessment, etc. Presenting our set of slides with Building Strong Network Security Foundation In Business Strategy. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Holistic Approach, Risk Assessments.
-
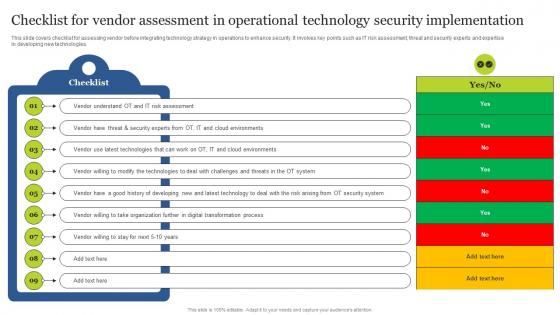 Checklist For Vendor Assessment In Operational Technology Security Guide For Integrating Technology Strategy SS V
Checklist For Vendor Assessment In Operational Technology Security Guide For Integrating Technology Strategy SS VThis slide covers checklist for assessing vendor before integrating technology strategy in operations to enhance security. It involves key points such as IT risk assessment, threat and security experts and expertise in developing new technologies. Deliver an outstanding presentation on the topic using this Checklist For Vendor Assessment In Operational Technology Security Guide For Integrating Technology Strategy SS V. Dispense information and present a thorough explanation of Cloud Environments, Risk Arising, Digital Transformation Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Operational Technology Security Controls To Enhance Safety Guide For Integrating Technology Strategy SS V
Operational Technology Security Controls To Enhance Safety Guide For Integrating Technology Strategy SS VThis slide covers operational technology security controls to improve IT safety. It involves five kinds of security controls such as update asset inventory, training, ,manage portable media and secure configuration. Introducing Operational Technology Security Controls To Enhance Safety Guide For Integrating Technology Strategy SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Update Asset Inventory, Portable Media, Backup And Restore, using this template. Grab it now to reap its full benefits.
-
 Social Security Claiming Strategy Calculator In Powerpoint And Google Slides Cpb
Social Security Claiming Strategy Calculator In Powerpoint And Google Slides CpbPresenting our Social Security Claiming Strategy Calculator In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Social Security Claiming Strategy Calculator This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Strategies Information Security In Powerpoint And Google Slides Cpb
Strategies Information Security In Powerpoint And Google Slides CpbPresenting our Strategies Information Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Strategies Information Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
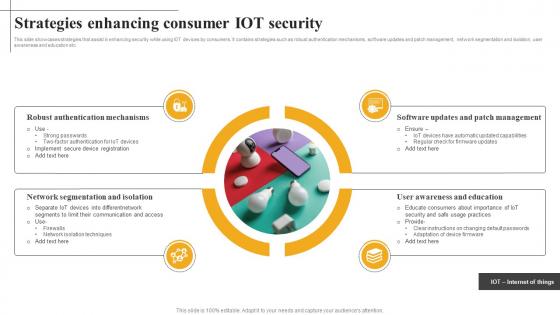 Strategies Enhancing Consumer Iot Security
Strategies Enhancing Consumer Iot SecurityThis slide showcases strategies that assist in enhancing security while using IOT devices by consumers. It contains strategies such as robust authentication mechanisms, software updates and patch management, network segmentation and isolation, user awareness and education etc. Introducing our premium set of slides with Strategies Enhancing Consumer Iot Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Robust Authentication, Network Segmentation, Software Updates. So download instantly and tailor it with your information.
-
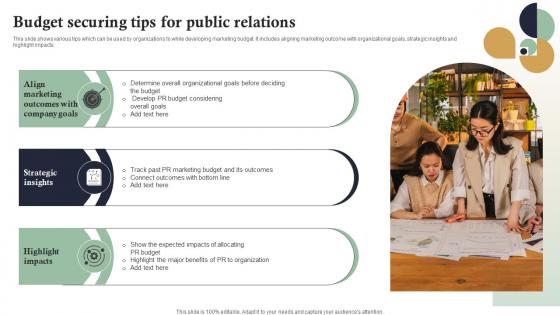 Budget Securing Tips For Public Relations Internet Marketing Strategies MKT SS V
Budget Securing Tips For Public Relations Internet Marketing Strategies MKT SS VThis slide shows various tips which can be used by organizations to while developing marketing budget. It includes aligning marketing outcome with organizational goals, strategic insights Deliver an outstanding presentation on the topic using this Budget Securing Tips For Public Relations Internet Marketing Strategies MKT SS V. Dispense information and present a thorough explanation of Budget Considering, Connect Outcomes, Impacts Allocating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
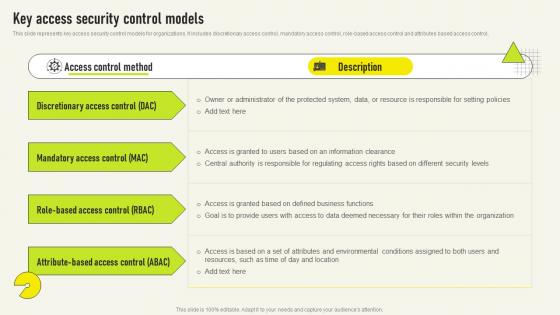 Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS V
Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS VThis slide represents key access security control models for organizations It includes discretionary access control, mandatory access control, role based access control and attributes based access control,Present the topic in a bit more detail with this Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Mandatory Access, Discretionary Access, Administrator Protected This template is free to edit as deemed fit for your organization Therefore download it now
-
 Most Commonly Types Of Ict Securities Used Comprehensive Guide For Deployment Strategy SS V
Most Commonly Types Of Ict Securities Used Comprehensive Guide For Deployment Strategy SS VThis slide represents various types of information and communication technology ICT securities used by businesses It covers network security, endpoint security, access security, and data encryption Increase audience engagement and knowledge by dispensing information using Most Commonly Types Of Ict Securities Used Comprehensive Guide For Deployment Strategy SS V This template helps you present information on four stages You can also present information on Network Security, End Point Security, Access Security using this PPT design This layout is completely editable so personaize it now to meet your audiences expectations
-
 Network Security Model To Effective Comprehensive Guide For Deployment Strategy SS V
Network Security Model To Effective Comprehensive Guide For Deployment Strategy SS VThis slide represents the network security model for effective communication in the organization It covers information regarding security threats, firewalls, virtual private networks, etc Present the topic in a bit more detail with this Network Security Model To Effective Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Protection Computer, Components Detect, Information Channel This template is free to edit as deemed fit for your organization Therefore download it now
-
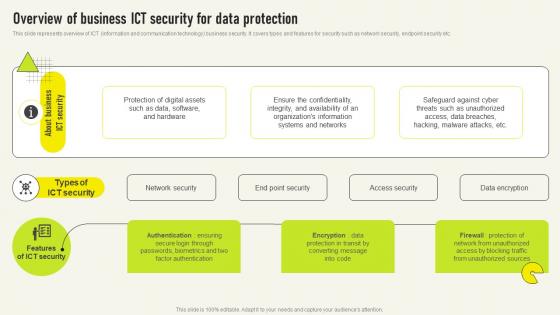 Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V
Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS VThis slide represents overview of ICT information and communication technology business security It covers types and features for security such as network security, endpoint security etc Present the topic in a bit more detail with this Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Unauthorized Sources, Factor Authentication, Organizations Information This template is free to edit as deemed fit for your organization Therefore download it now
-
 Cyber Security Offensive Defensive Strategies In Powerpoint And Google Slides Cpb
Cyber Security Offensive Defensive Strategies In Powerpoint And Google Slides CpbPresenting our Cyber Security Offensive Defensive Strategies In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Cyber Security Offensive Defensive Strategies This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Computer Security Strategies In Powerpoint And Google Slides Cpb
Computer Security Strategies In Powerpoint And Google Slides CpbPresenting our Computer Security Strategies In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Computer Security Strategies This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
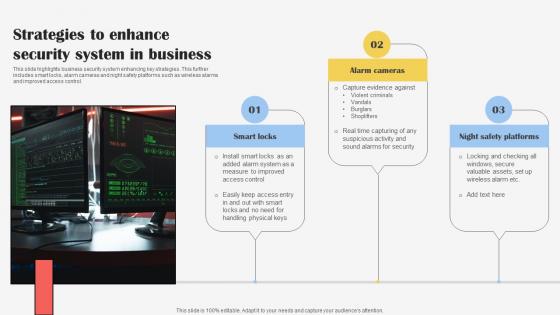 Strategies To Enhance Security System In Business
Strategies To Enhance Security System In BusinessThis slide highlights business security system enhancing key strategies. This further includes smart locks, alarm cameras and night safety platforms such as wireless alarms and improved access control. Introducing our premium set of slides with Strategies To Enhance Security System In Business. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Smart Locks, Alarm Cameras, Night Safety Platforms. So download instantly and tailor it with your information.
-
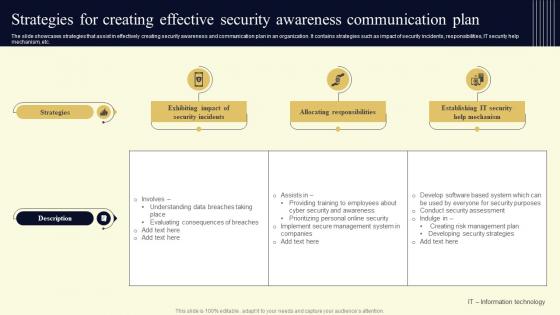 Strategies For Creating Effective Security Awareness Communication Plan
Strategies For Creating Effective Security Awareness Communication PlanThe slide showcases strategies that assist in effectively creating security awareness and communication plan in an organization. It contains strategies such as impact of security incidents, responsibilities, IT security help mechanism, etc. Introducing our Strategies For Creating Effective Security Awareness Communication Plan set of slides. The topics discussed in these slides are Strategies, Description, Incidents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Business Expansion And Data Security Strategy Icon
Business Expansion And Data Security Strategy IconIntroducing our premium set of slides with Business Expansion And Data Security Strategy Icon. Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Business Expansion, Data Security Strategy Icon. So download instantly and tailor it with your information.
-
 Key Strategies To Secure Business Data
Key Strategies To Secure Business DataThis slide showcase strategies that can be used for securing cyberattacks and target organizational data security and access. It includes updating devices, secure iot technology, track cloud storage, train employees and secure network access. Introducing our premium set of slides with Key Strategies To Secure Business Data. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Updated Devices, Track Cloud Storage, Train Employees. So download instantly and tailor it with your information.
-
 Implement Effective Marketing Strategies For Successful Launch Security Token Offerings BCT SS
Implement Effective Marketing Strategies For Successful Launch Security Token Offerings BCT SSThe following slide depicts various marketing techniques to ensure successful launch of security token offerings STO project. It includes elements such as public relations, social media, content, affiliate, email marketing, paid ads, etc. Introducing Implement Effective Marketing Strategies For Successful Launch Security Token Offerings BCT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Marketing Strategies, Potential Impact, Project Awareness, using this template. Grab it now to reap its full benefits.
-
 Security Company Marketing Strategy In Powerpoint And Google Slides Cpb
Security Company Marketing Strategy In Powerpoint And Google Slides CpbPresenting Security Company Marketing Strategy In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Company Marketing Strategy. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
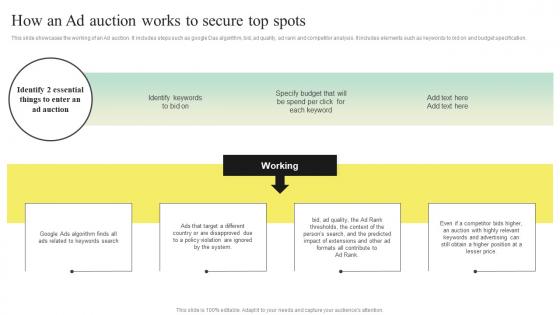 Search Engine Marketing Strategy To Enhance How An Ad Auction Works To Secure Top Spots MKT SS V
Search Engine Marketing Strategy To Enhance How An Ad Auction Works To Secure Top Spots MKT SS VThis slide showcases the working of an Ad auction. It includes steps such as google Das algorithm, bid, ad quality, ad rank and competitor analysis. It includes elements such as keywords to bid on and budget specification. Introducing Search Engine Marketing Strategy To Enhance How An Ad Auction Works To Secure Top Spots MKT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Algorithm, Violation Are Ignored, Extensions, using this template. Grab it now to reap its full benefits.
-
 Agenda Delivering ICT Services For Enhanced Business Security Strategy SS V
Agenda Delivering ICT Services For Enhanced Business Security Strategy SS VIncrease audience engagement and knowledge by dispensing information using Agenda Delivering ICT Services For Enhanced Business Security Strategy SS V. This template helps you present information on five stages. You can also present information on Process And Retention Rate, Configuration Management, Effective Business Performance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
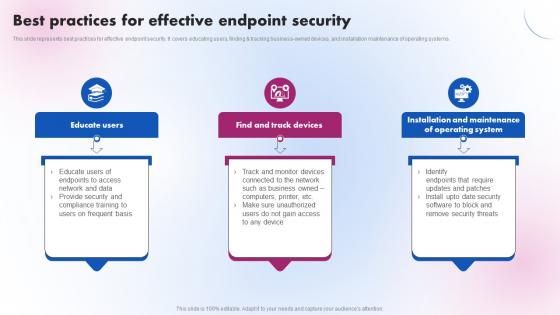 Best Practices For Effective Endpoint Security Delivering ICT Services For Enhanced Business Strategy SS V
Best Practices For Effective Endpoint Security Delivering ICT Services For Enhanced Business Strategy SS VThis slide represents best practices for effective endpoint security. It covers educating users, finding and tracking business-owned devices, and installation maintenance of operating systems. Increase audience engagement and knowledge by dispensing information using Best Practices For Effective Endpoint Security Delivering ICT Services For Enhanced Business Strategy SS V. This template helps you present information on three stages. You can also present information on Educate Users, Find And Track Devices, Operating System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Delivering ICT Services For Enhanced Business Security Table Of Contents Strategy SS V
Delivering ICT Services For Enhanced Business Security Table Of Contents Strategy SS VIncrease audience engagement and knowledge by dispensing information using Delivering ICT Services For Enhanced Business Security Table Of Contents Strategy SS V. This template helps you present information on one stages. You can also present information on ICT Technologies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide Delivering ICT Services For Enhanced Business Security Strategy SS V
Icons Slide Delivering ICT Services For Enhanced Business Security Strategy SS VIntroducing our well researched set of slides titled Icons Slide Delivering ICT Services For Enhanced Business Security Strategy SS V. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Key Access Security Control Models Delivering ICT Services For Enhanced Business Strategy SS V
Key Access Security Control Models Delivering ICT Services For Enhanced Business Strategy SS VThis slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role-based access control and attributes based access control, Deliver an outstanding presentation on the topic using this Key Access Security Control Models Delivering ICT Services For Enhanced Business Strategy SS V. Dispense information and present a thorough explanation of Access Control Method, Description using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.


