Powerpoint Templates and Google slides for Security Technology Roadmap
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
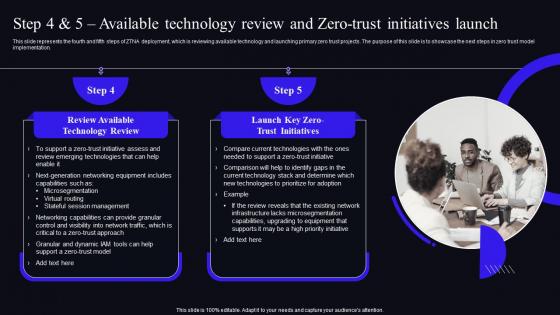 Zero Trust Security Model Step 4 And 5 Available Technology Review And Zero Trust Initiatives Launch
Zero Trust Security Model Step 4 And 5 Available Technology Review And Zero Trust Initiatives LaunchThis slide represents the fourth and fifth steps of ZTNA deployment, which is reviewing available technology and launching primary zero trust projects. The purpose of this slide is to showcase the next steps in zero trust model implementation. Present the topic in a bit more detail with this Zero Trust Security Model Step 4 And 5 Available Technology Review And Zero Trust Initiatives Launch. Use it as a tool for discussion and navigation on Technology, Equipment, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Future Of Secure Web Gateway Technology Network Security Using Secure Web Gateway
Future Of Secure Web Gateway Technology Network Security Using Secure Web GatewayThis slide talks about the future of Secure Web Gateway security technology. The purpose of this slide is to explain how SWG can lead the cyber security market in future as more businesses are migrating to the cloud. Increase audience engagement and knowledge by dispensing information using Future Of Secure Web Gateway Technology Network Security Using Secure Web Gateway. This template helps you present information on five stages. You can also present information on Predicted, Investment, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Introduction To Secure Web Gateway Technology Network Security Using Secure Web Gateway
Introduction To Secure Web Gateway Technology Network Security Using Secure Web GatewayThis slide talks about the network security solution called Secure Web Gateway. The purpose of this slide is to outline the various benefits of SWG. This slide also represents different working components of SWG such as traffic inspection, malware protection, etc. Deliver an outstanding presentation on the topic using this Introduction To Secure Web Gateway Technology Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Introduction, Technology, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations
Cyber Security Risk Assessment And Technology Deployment Plan To Improve OrganizationsThis slide represents the assessment of vulnerability and consequences of the cyber security incidents on the operations of the company. It includes details related to threat, vulnerability, consequences, risk and solution Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations. Dispense information and present a thorough explanation of Consequences, Vulnerability, Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations
Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve OrganizationsThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Introducing Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing, Malware, Application, using this template. Grab it now to reap its full benefits.
-
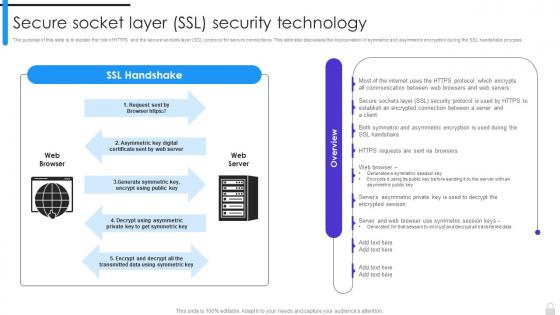 Encryption Implementation Strategies Secure Socket Layer SSL Security Technology
Encryption Implementation Strategies Secure Socket Layer SSL Security TechnologyThe purpose of this slide is to explain the role of HTTPS and the secure sockets layer SSL protocol for secure connections. This slide also discusses the incorporation of symmetric and asymmetric encryption during the SSL handshake process. Present the topic in a bit more detail with this Encryption Implementation Strategies Secure Socket Layer SSL Security Technology. Use it as a tool for discussion and navigation on Secure Socket Layer, Security Technology, Symmetric And Asymmetric Encryption, Protocol For Secure Connections. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
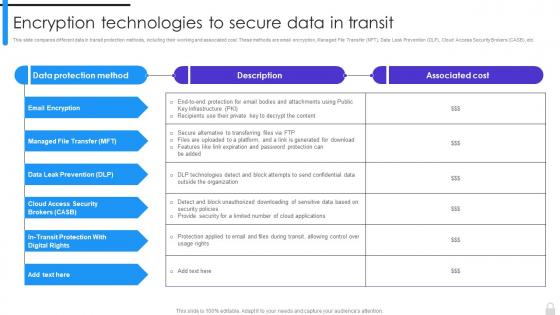 Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies
Encryption Technologies To Secure Data In Transit Encryption Implementation StrategiesThis slide compares different data in transit protection methods, including their working and associated cost. These methods are email encryption, Managed File Transfer MFT, Data Leak Prevention DLP, Cloud Access Security Brokers CASB, etc. Deliver an outstanding presentation on the topic using this Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Managed File Transfer, Cloud Access Security Brokers, Email Encryption, Encryption Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
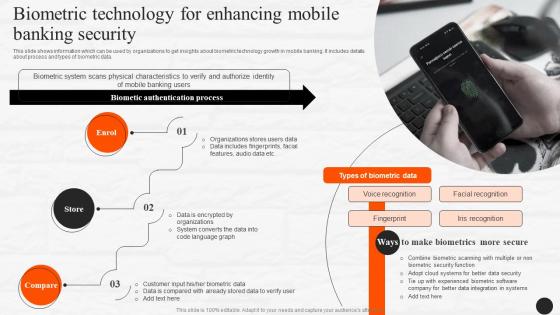 Biometric Technology For Enhancing Mobile Banking Security E Wallets As Emerging Payment Method Fin SS V
Biometric Technology For Enhancing Mobile Banking Security E Wallets As Emerging Payment Method Fin SS VThis slide shows information which can be used by organizations to get insights about biometric technology growth in mobile banking. It includes details about process and types of biometric data. Present the topic in a bit more detail with this Biometric Technology For Enhancing Mobile Banking Security E Wallets As Emerging Payment Method Fin SS V. Use it as a tool for discussion and navigation on Biometric, Technology, Iris Recognition. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
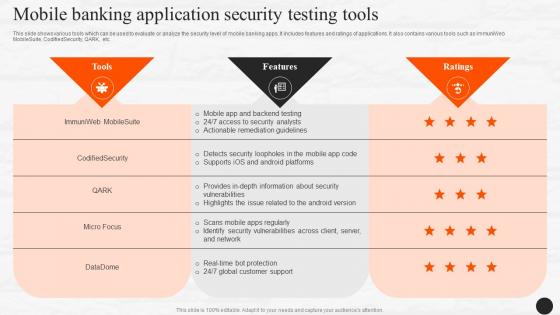 Mobile Banking Application Security Testing Tools E Wallets As Emerging Payment Method Fin SS V
Mobile Banking Application Security Testing Tools E Wallets As Emerging Payment Method Fin SS VThis slide shows various tools which can be used to evaluate or analyze the security level of mobile banking apps. It includes features and ratings of applications. It also contains various tools such as ImmuniWeb MobileSuite, CodifiedSecurity, QARK, etc. Present the topic in a bit more detail with this Mobile Banking Application Security Testing Tools E Wallets As Emerging Payment Method Fin SS V. Use it as a tool for discussion and navigation on Application, Evaluate, Analyze. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Emerging Technologies Cyber Security Technology Market Overview
Emerging Technologies Cyber Security Technology Market OverviewThis slide explains Cyber security technology market overview with top players in the year 2021. It also predicts market growth and compound annual growth rate from year 2021 till 2028. Deliver an outstanding presentation on the topic using this Emerging Technologies Cyber Security Technology Market Overview. Dispense information and present a thorough explanation of Overview Of Cyber Security, False Sense Of Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
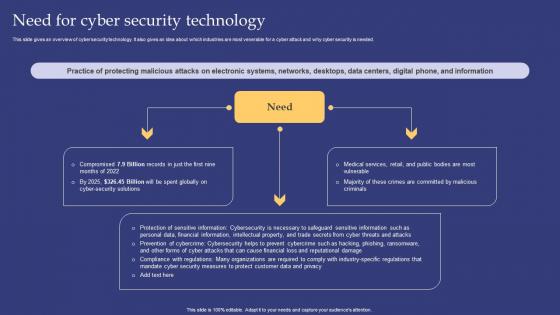 Emerging Technologies Need For Cyber Security Technology
Emerging Technologies Need For Cyber Security TechnologyThis slide gives an overview of cyber security technology. It also gives an idea about which industries are most venerable for a cyber attack and why cyber security is needed. Deliver an outstanding presentation on the topic using this Emerging Technologies Need For Cyber Security Technology. Dispense information and present a thorough explanation of Protection, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Emerging Technologies Objectives Of Cyber Security Technology
Emerging Technologies Objectives Of Cyber Security TechnologyThis slide explains the objectives of cyber security technology such as confidentiality, integrity and availability. It also talks about the three goals and how they collectively ensures the data protection. Introducing Emerging Technologies Objectives Of Cyber Security Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, using this template. Grab it now to reap its full benefits.
-
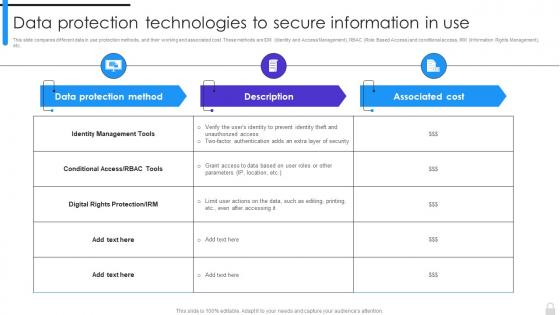 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
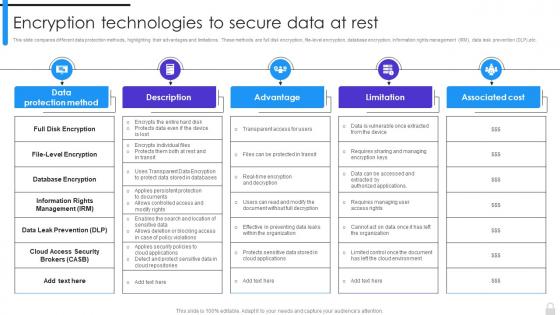 Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest
Encryption Implementation Strategies Encryption Technologies To Secure Data At RestThis slide compares different data protection methods, highlighting their advantages and limitations. These methods are full disk encryption, file-level encryption, database encryption, information rights management IRM, data leak prevention DLP,etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Full Disk Encryption, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secured Automated Lending Technology In Powerpoint And Google Slides Cpb
Secured Automated Lending Technology In Powerpoint And Google Slides CpbPresenting Secured Automated Lending Technology In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Secured Automated Lending Technology. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Edge Computing Technology Key Edge AI Security Strategies AI SS
Edge Computing Technology Key Edge AI Security Strategies AI SSThis slide showcases 5 major edge AI security strategies so that developers can build and deploy their models in secured way. It provides details about secured perimeter, secured applications, early detection, automated patch, etc. Introducing Edge Computing Technology Key Edge AI Security Strategies AI SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Creating A Secure Perimeter, Securing Applications, Early Detection, Creating Automated Patch, using this template. Grab it now to reap its full benefits.
-
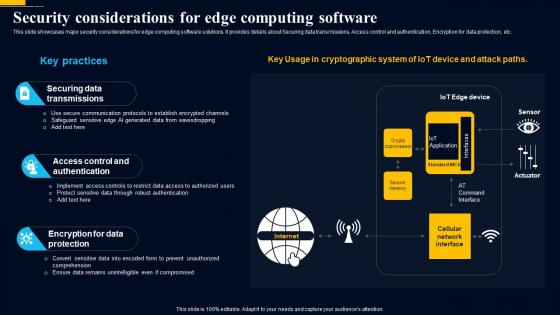 Edge Computing Technology Security Considerations For Edge Computing Software AI SS
Edge Computing Technology Security Considerations For Edge Computing Software AI SSThis slide showcases major security considerations for edge computing software solutions. It provides details about Securing data transmissions, Access control and authentication, Encryption for data protection, etc. Present the topic in a bit more detail with this Edge Computing Technology Security Considerations For Edge Computing Software AI SS. Use it as a tool for discussion and navigation on Securing Data Transmissions, Access Control And Authentication, Encryption For Data Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Best Tools For Security Operations Secops V2 Ppt Infographic Template Files
Best Tools For Security Operations Secops V2 Ppt Infographic Template FilesThis slide represents the best security operations tools for the year 2023. The purpose of this slide is to showcase the various prominent tools for SecOps, including Grafana, StackStorm, GRR Rapid Response, Chef Inspec, and Alerta. Deliver an outstanding presentation on the topic using this Best Tools For Security Operations Secops V2 Ppt Infographic Template Files. Dispense information and present a thorough explanation of Needs Comprehensive Knowledge, Complex Version Management, Incident Response Framework using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
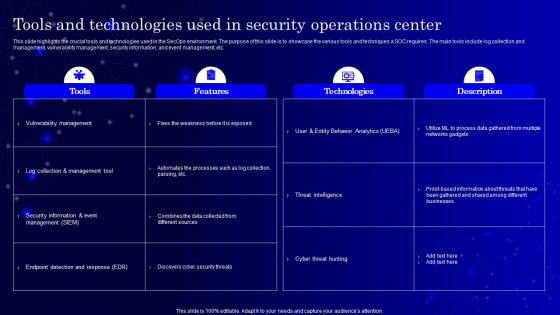 Secops V2 Tools And Technologies Used In Security Operations Center
Secops V2 Tools And Technologies Used In Security Operations CenterThis slide highlights the crucial tools and technologies used in the SecOps environment. The purpose of this slide is to showcase the various tools and techniques a SOC requires. The main tools include log collection and management, vulnerability management, security information, and event management, etc. Deliver an outstanding presentation on the topic using this Secops V2 Tools And Technologies Used In Security Operations Center. Dispense information and present a thorough explanation of Vulnerability Management, Log Collection And Management Tool, Security Information And Event Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
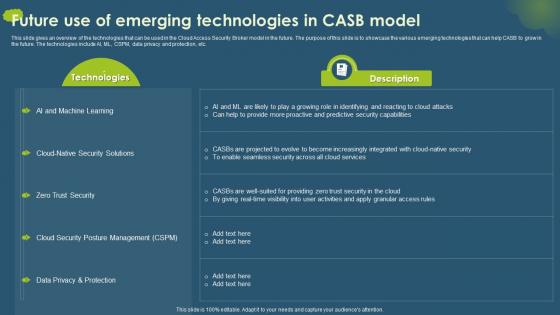 Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB Model
Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB ModelThis slide gives an overview of the technologies that can be used in the Cloud Access Security Broker model in the future. The purpose of this slide is to showcase the various emerging technologies that can help CASB to grow in the future. The technologies include AI, ML, CSPM, data privacy and protection, etc. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB Model. Dispense information and present a thorough explanation of Cloud Security Posture Management, Data Privacy And Protection, Zero Trust Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Lorawan Lorawan Technology Security Session Keys Ppt Show Inspiration
Lorawan Lorawan Technology Security Session Keys Ppt Show InspirationThis slide explains LoRaWAN security session keys which are used to ensure secure communication between LoRaWAN devices and network servers. Purpose of this slide is to define two types of session keys the application session key AppSKey and the network session key NwkSKey. Deliver an outstanding presentation on the topic using this Lorawan Lorawan Technology Security Session Keys Ppt Show Inspiration. Dispense information and present a thorough explanation of Overview, Technology, Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
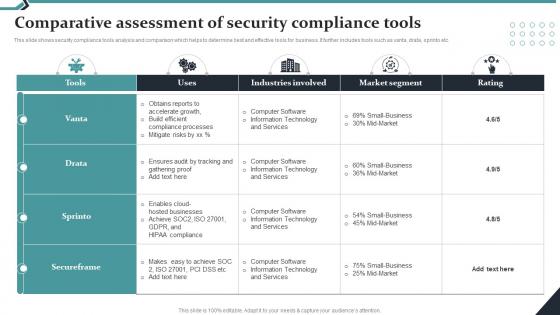 Comparative Assessment Of Security Compliance Tools
Comparative Assessment Of Security Compliance ToolsThis slide shows security compliance tools analysis and comparison which helps to determine best and effective tools for business. It further includes tools such as vanta, drata, sprinto etc. Presenting our well structured Comparative Assessment Of Security Compliance Tools. The topics discussed in this slide are Industries Involved, Market Segment.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Secure Computer Technology Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Secure Computer Technology Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a visual representation of secure computer. It is a modern, vibrant and eye catching icon that will help to create an impactful presentation. It is a great way to emphasize the importance of data security and safety.
-
 Secure Computer Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Secure Computer Technology Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for presentations on secure computer systems. It features a black and white design depicting a computer with a padlock, symbolizing the safety of your data. Use this icon to emphasize the importance of secure computing.
-
 Secure Financial Technology Services AI Image PowerPoint Presentation PPT ECS
Secure Financial Technology Services AI Image PowerPoint Presentation PPT ECSIntroducing a Visual PPT on Secure Financial Technology Services. Our Presentation Specialists have taken great care in designing each slide in this PowerPoint. Feel free to tailor the content. The PPT Template fits well with any screen size, and its also compatible with Google Slides. Download the PPT, and present it confidently.
-
 IoT Cyber Security Technologies For Data Improving IoT Device Cybersecurity IoT SS
IoT Cyber Security Technologies For Data Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase various types of Internet of Things IoT security technologies which can assist companies in safeguarding customer data. Blockchain, IoT security analytics, Zero Trust Architecture, and Edge Computing are the most trending technologies which are outlined in slide. Increase audience engagement and knowledge by dispensing information using IoT Cyber Security Technologies For Data Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Devices, Architecture, Computing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
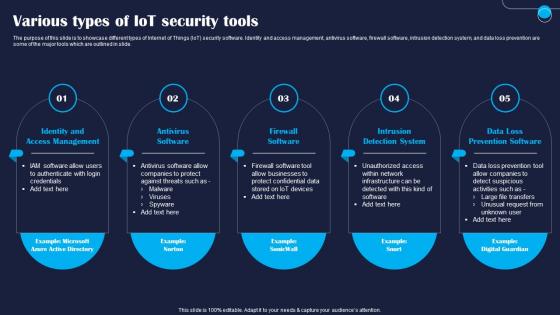 Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SS
Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase different types of Internet of Things IoT security software. Identity and access management, antivirus software, firewall software, intrusion detection system, and data loss prevention are some of the major tools which are outlined in slide. Introducing Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Management, Software, System, using this template. Grab it now to reap its full benefits.
-
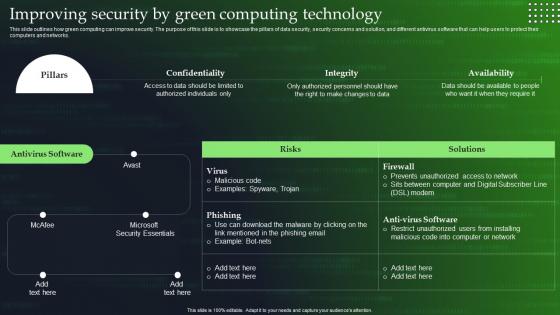 Green Cloud Computing V2 Improving Security By Green Computing Technology
Green Cloud Computing V2 Improving Security By Green Computing TechnologyThis slide outlines how green computing can improve security. The purpose of this slide is to showcase the pillars of data security, security concerns and solution, and different antivirus software that can help users to protect their computers and networks. Present the topic in a bit more detail with this Green Cloud Computing V2 Improving Security By Green Computing Technology. Use it as a tool for discussion and navigation on Green Computing, Data Security, Security Concerns And Solution, Computers And Networks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
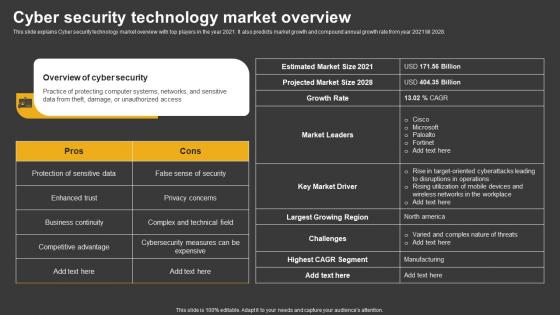 Trending Technologies Cyber Security Technology Market Overview
Trending Technologies Cyber Security Technology Market OverviewThis slide explains Cyber security technology market overview with top players in the year 2021. It also predicts market growth and compound annual growth rate from year 2021 till 2028. Deliver an outstanding presentation on the topic using this Trending Technologies Cyber Security Technology Market Overview. Dispense information and present a thorough explanation of Pros, Cons using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
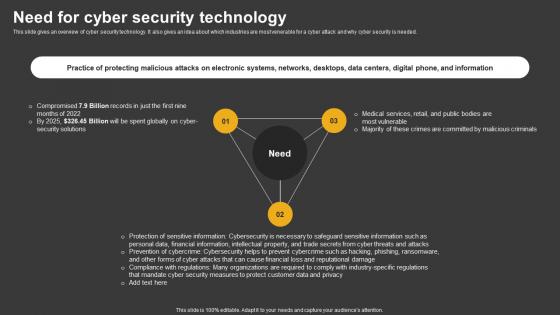 Trending Technologies Need For Cyber Security Technology
Trending Technologies Need For Cyber Security TechnologyThis slide gives an overview of cyber security technology. It also gives an idea about which industries are most venerable for a cyber attack and why cyber security is needed. Increase audience engagement and knowledge by dispensing information using Trending Technologies Need For Cyber Security Technology. This template helps you present information on three stages. You can also present information on Cyber Security Solutions, Malicious Criminals, Data And Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Trending Technologies Objectives Of Cyber Security Technology
Trending Technologies Objectives Of Cyber Security TechnologyThis slide explains the objectives of cyber security technology such as confidentiality, integrity and availability. It also talks about the three goals and how they collectively ensures the data protection. Introducing Trending Technologies Objectives Of Cyber Security Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, Availability, using this template. Grab it now to reap its full benefits.
-
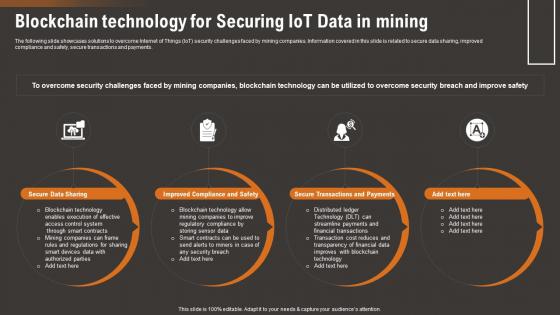 Blockchain Technology For Securing IoT Data How IoT Technology Is Transforming IoT SS
Blockchain Technology For Securing IoT Data How IoT Technology Is Transforming IoT SSThe following slide showcases solutions to overcome Internet of Things IoT security challenges faced by mining companies. Information covered in this slide is related to secure data sharing, improved compliance and safety, secure transactions and payments.Introducing Blockchain Technology For Securing IoT Data How IoT Technology Is Transforming IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Secure Data Sharing, Blockchain Technology, Enables Execution, using this template. Grab it now to reap its full benefits.
-
 Consequences Of Security Challenge On Mining How IoT Technology Is Transforming IoT SS
Consequences Of Security Challenge On Mining How IoT Technology Is Transforming IoT SSThe following slide showcases impact of Internet of Things IoT security challenges on mining companies. The slide covers information about unsafe working conditions, lost data, higher downtime, data leak, cost associated with security incident, loss of productivity, etc.Increase audience engagement and knowledge by dispensing information using Consequences Of Security Challenge On Mining How IoT Technology Is Transforming IoT SS. This template helps you present information on five stages. You can also present information on Compromised Smart, Working Conditions, Higher Downtime using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
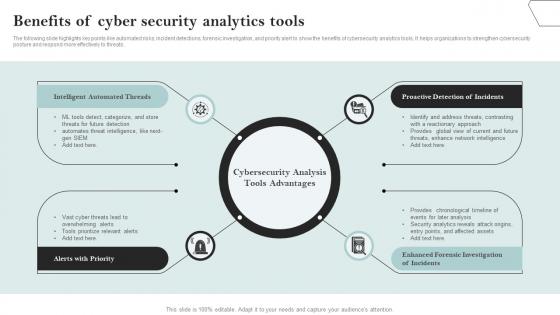 Benefits Of Cyber Security Analytics Tools
Benefits Of Cyber Security Analytics ToolsThe following slide highlights key points like automated risks, incident detections, forensic investigation, and priority alert to show the benefits of cybersecurity analytics tools. It helps organizations to strengthen cybersecurity posture and respond more effectively to threats. Presenting our set of slides with Benefits Of Cyber Security Analytics Tools. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Automated, Priority, Investigation.
-
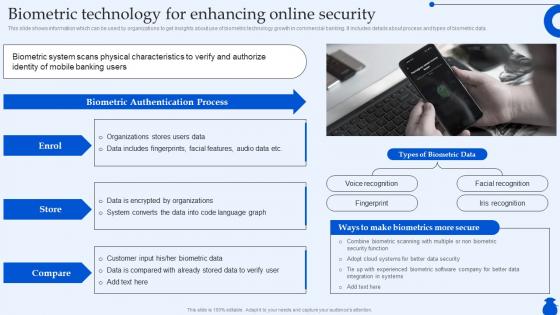 Biometric Technology For Enhancing Online Security Ultimate Guide To Commercial Fin SS
Biometric Technology For Enhancing Online Security Ultimate Guide To Commercial Fin SSThis slide shows information which can be used by organizations to get insights about use of biometric technology growth in commercial banking. It includes details about process and types of biometric data. Present the topic in a bit more detail with this Biometric Technology For Enhancing Online Security Ultimate Guide To Commercial Fin SS. Use it as a tool for discussion and navigation on Biometric Authentication Process, Make Biometrics More Secure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
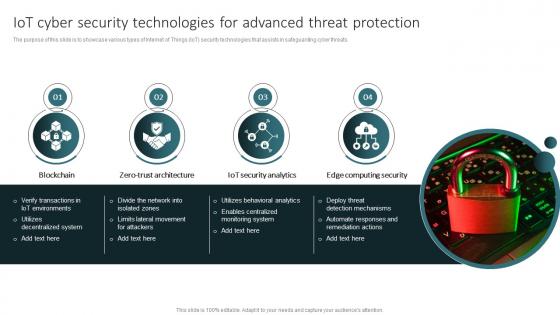 IoT Cyber Security Technologies For Advanced Threat Protection
IoT Cyber Security Technologies For Advanced Threat ProtectionThe purpose of this slide is to showcase various types of Internet of Things IoT security technologies that assists in safeguarding cyber threats. Introducing our premium set of slides with IoT Cyber Security Technologies For Advanced Threat Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Architecture, Security, Computing. So download instantly and tailor it with your information.
-
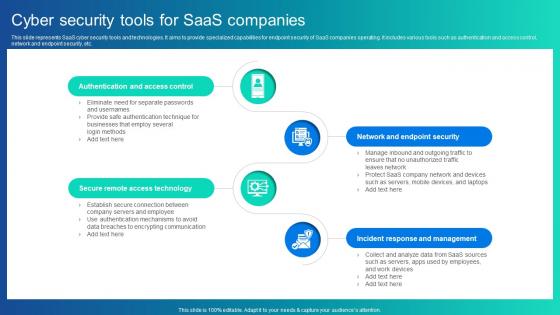 Cyber Security Tools For Saas Companies
Cyber Security Tools For Saas CompaniesThis slide represents SaaS cyber security tools and technologies. It aims to provide specialized capabilities for endpoint security of SaaS companies operating. It includes various tools such as authentication and access control, network and endpoint security, etc. Introducing our premium set of slides with Cyber Security Tools For Saas Companies Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Authentication And Access Control, Secure Remote Access Technology, Network And Endpoint Security. So download instantly and tailor it with your information.
-
 Smart Automation Robotics Autonomous Robotics Technologies For Surveillance And Security RB SS
Smart Automation Robotics Autonomous Robotics Technologies For Surveillance And Security RB SSThis slide showcases various types of robots that collectively contribute to a comprehensive security framework, ensuring enhanced surveillance capabilities across different domains. It includes types such as unmanned ground vehicles, patrol robots, drone surveillance, and underwater surveillance robots. Increase audience engagement and knowledge by dispensing information using Smart Automation Robotics Autonomous Robotics Technologies For Surveillance And Security RB SS This template helps you present information on Four stages. You can also present information on Unmanned Ground Vehicles, Patrol Robots, Underwater Surveillance Robots using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
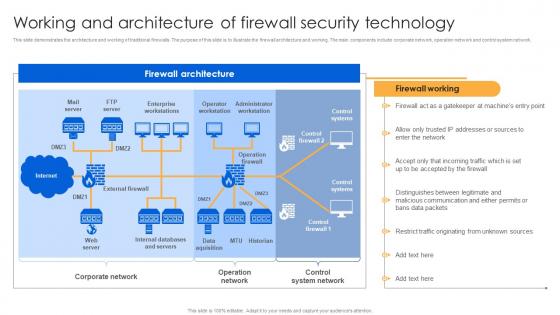 Working And Architecture Of Firewall Security Technology Firewall Virtualization
Working And Architecture Of Firewall Security Technology Firewall VirtualizationThis slide demonstrates the architecture and working of traditional firewalls. The purpose of this slide is to illustrate the firewall architecture and working. The main components include corporate network, operation network and control system network. Deliver an outstanding presentation on the topic using this Working And Architecture Of Firewall Security Technology Firewall Virtualization. Dispense information and present a thorough explanation of Firewall Architecture, Corporate Network, Control System Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
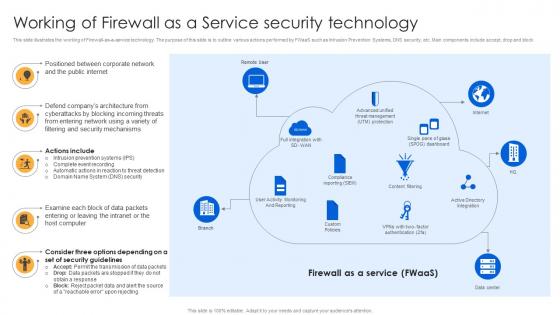 Working Of Firewall As A Service Security Technology Firewall Virtualization
Working Of Firewall As A Service Security Technology Firewall VirtualizationThis slide illustrates the working of Firewall-as-a-service technology. The purpose of this slide is to outline various actions performed by FWaaS such as Intrusion Prevention Systems, DNS security, etc. Main components include accept, drop and block. Increase audience engagement and knowledge by dispensing information using Working Of Firewall As A Service Security Technology Firewall Virtualization. This template helps you present information on five stages. You can also present information on Public Internet, Corporate Network, Companys Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Select Tools To Reduce Cyber Security Failure Implementing Strategies To Mitigate Cyber Security Threats
Select Tools To Reduce Cyber Security Failure Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Present the topic in a bit more detail with this Select Tools To Reduce Cyber Security Failure Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Features, Free Trial, Cost This template is free to edit as deemed fit for your organization. Therefore download it now.
-
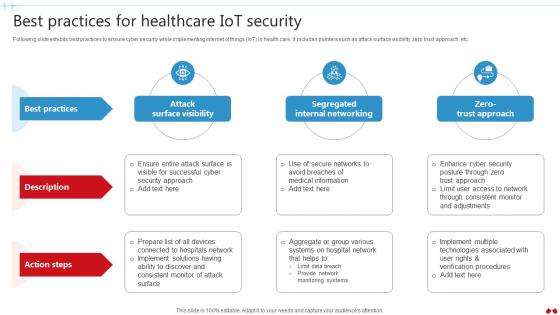 Best Practices For Healthcare IoT Security Transforming Healthcare Industry Through Technology IoT SS V
Best Practices For Healthcare IoT Security Transforming Healthcare Industry Through Technology IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Healthcare IoT Security Transforming Healthcare Industry Through Technology IoT SS V. This template helps you present information on two stages. You can also present information on Surface Visibility, Internal Networking, Trust Approach using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
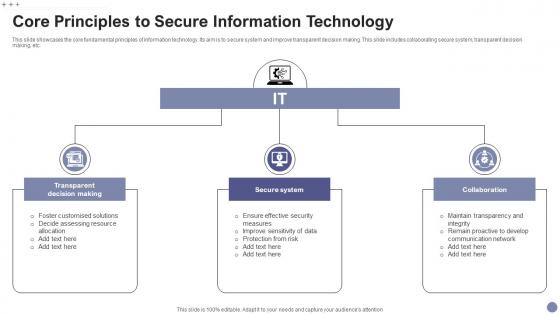 Core Principles To Secure Information Technology
Core Principles To Secure Information TechnologyThis slide showcases the core fundamental principles of information technology. Its aim is to secure system and improve transparent decision making. This slide includes collaborating secure system, transparent decision making, etc. Introducing our premium set of slides with Core Principles To Secure Information Technology. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Transparent Decision Making, Secure System, Collaboration. So download instantly and tailor it with your information.
-
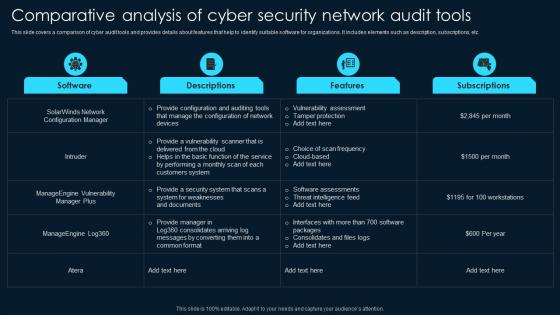 Comparative Analysis Of Cyber Security Network Audit Tools
Comparative Analysis Of Cyber Security Network Audit ToolsThis slide covers a comparison of cyber audit tools and provides details about features that help to identify suitable software for organizations. It includes elements such as description, subscriptions, etc. Introducing our Comparative Analysis Of Cyber Security Network Audit Tools set of slides. The topics discussed in these slides are Vulnerability Assessment, Tamper Protection, Cloud Based. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Network Security Audit Technology Icon
Cyber Network Security Audit Technology IconPresenting our set of slides with Cyber Network Security Audit Technology Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Network Security, Audit Technology Icon.
-
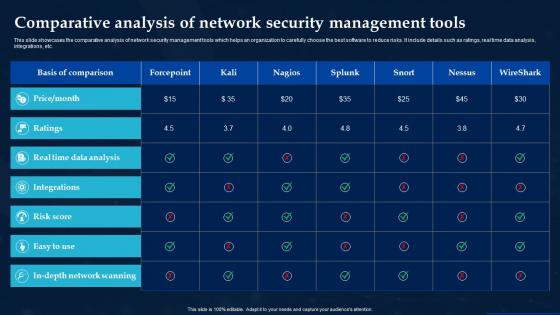 Comparative Analysis Of Network Security Management Tools
Comparative Analysis Of Network Security Management ToolsThis slide showcases the comparative analysis of network security management tools which helps an organization to carefully choose the best software to reduce risks. It include details such as ratings, real time data analysis, integrations, etc. Introducing our Comparative Analysis Of Network Security Management Tools set of slides. The topics discussed in these slides are Ratings, Integrations, Risk Score. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
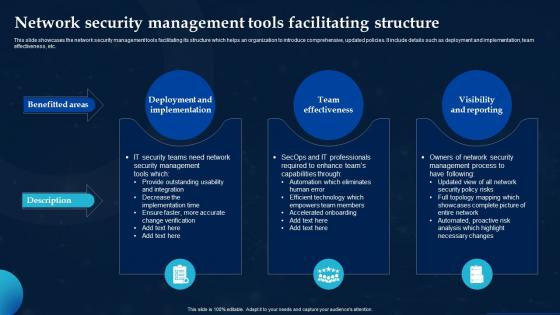 Network Security Management Tools Facilitating Structure
Network Security Management Tools Facilitating StructureThis slide showcases the network security management tools facilitating its structure which helps an organization to introduce comprehensive, updated policies. It include details such as deployment and implementation, team effectiveness, etc. Presenting our set of slides with Network Security Management Tools Facilitating Structure. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Deployment Implementation, Team Effectiveness, Visibility Reporting.
-
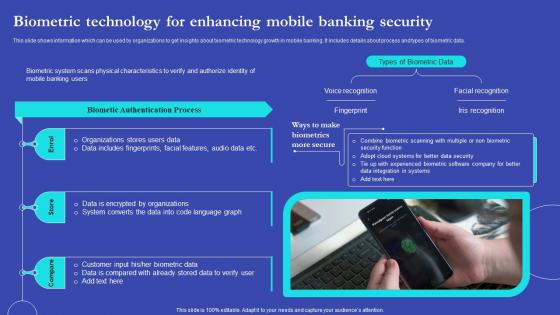 NEO Banks For Digital Funds Biometric Technology For Enhancing Mobile Banking Security Fin SS V
NEO Banks For Digital Funds Biometric Technology For Enhancing Mobile Banking Security Fin SS VThis slide shows information which can be used by organizations to get insights about biometric technology growth in mobile banking. It includes details about process and types of biometric data. Introducing NEO Banks For Digital Funds Biometric Technology For Enhancing Mobile Banking Security Fin SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Biometric Technology, Mobile Banking Security, Biometric Data, Facial Recognition, using this template. Grab it now to reap its full benefits.
-
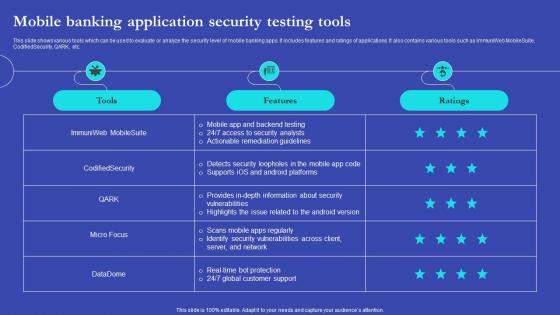 NEO Banks For Digital Funds Mobile Banking Application Security Testing Tools Fin SS V
NEO Banks For Digital Funds Mobile Banking Application Security Testing Tools Fin SS VThis slide shows various tools which can be used to evaluate or analyze the security level of mobile banking apps. It includes features and ratings of applications. It also contains various tools such as ImmuniWeb MobileSuite, CodifiedSecurity, QARK, etc. Present the topic in a bit more detail with this NEO Banks For Digital Funds Mobile Banking Application Security Testing Tools Fin SS V. Use it as a tool for discussion and navigation on Mobile Banking Application, Security Testing Tools, Ratings Of Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
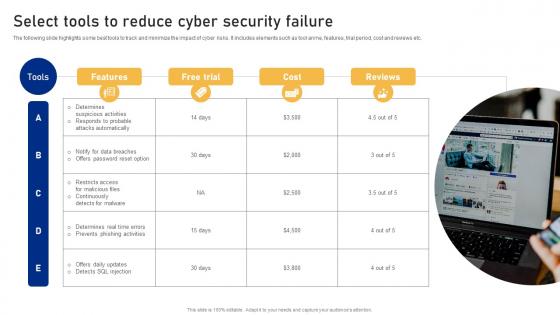 Select Tools To Reduce Cyber Security Failure Cyber Risk Assessment
Select Tools To Reduce Cyber Security Failure Cyber Risk AssessmentThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Introducing Select Tools To Reduce Cyber Security Failure Cyber Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Suspicious Activities, Select Tools, Cyber Security Failure using this template. Grab it now to reap its full benefits.
-
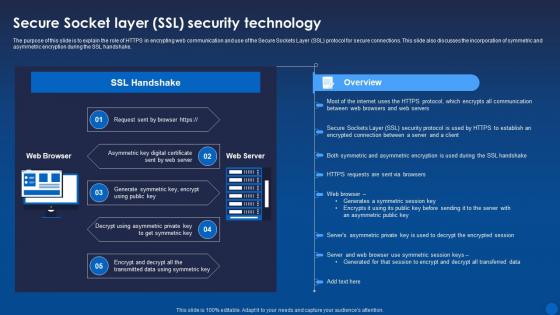 Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age It
Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role of HTTPS in encrypting web communication and use of the Secure Sockets Layer SSL protocol for secure connections. This slide also discusses the incorporation of symmetric and asymmetric encryption during the SSL handshake. Deliver an outstanding presentation on the topic using this Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Technology, Asymmetric, Symmetric using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
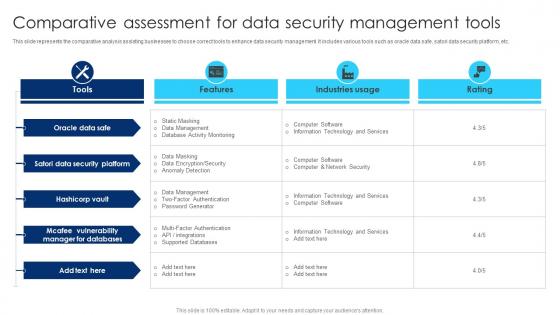 Comparative Assessment For Data Security Management Tools
Comparative Assessment For Data Security Management ToolsThis slide represents the comparative analysis assisting businesses to choose correct tools to enhance data security management. It includes various tools such as oracle data safe, satori data security platform, etc. Introducing our Comparative Assessment For Data Security Management Tools set of slides. The topics discussed in these slides are Oracle Data Safe, Data Security Platform, Manager For Databases. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
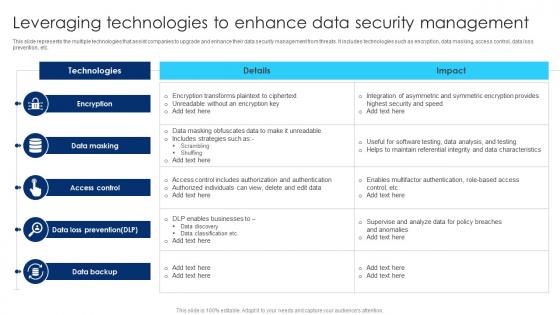 Leveraging Technologies To Enhance Data Security Management
Leveraging Technologies To Enhance Data Security ManagementThis slide represents the multiple technologies that assist companies to upgrade and enhance their data security management from threats. It includes technologies such as encryption, data masking, access control, data loss prevention, etc. Introducing our Leveraging Technologies To Enhance Data Security Management set of slides. The topics discussed in these slides are Data Loss Prevention, Access Control, Data Masking. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
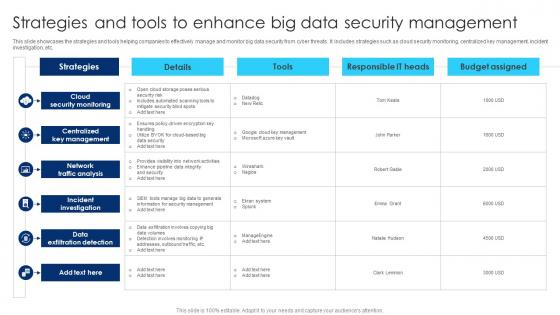 Strategies And Tools To Enhance Big Data Security Management
Strategies And Tools To Enhance Big Data Security ManagementThis slide showcases the strategies and tools helping companies to effectively manage and monitor big data security from cyber threats. It includes strategies such as cloud security monitoring, centralized key management, incident investigation, etc. Introducing our Strategies And Tools To Enhance Big Data Security Management set of slides. The topics discussed in these slides are Cloud Security Monitoring, Centralized Key Management, Network Traffic Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
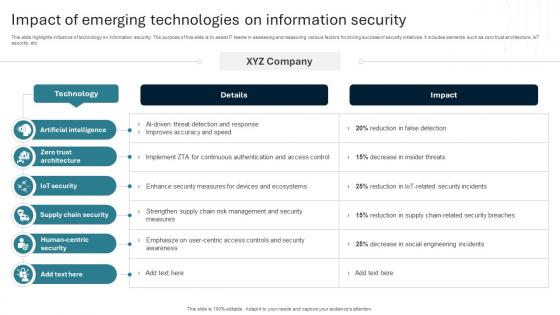 Impact Of Emerging Technologies On Information Security
Impact Of Emerging Technologies On Information SecurityThis slide highlights influence of technology on information security. The purpose of this slide is to assist IT teams in assessing and measuring various factors for driving success of security initiatives. It includes elements such as zero trust architecture, IoT security, etc.Introducing our Impact Of Emerging Technologies On Information Security set of slides. The topics discussed in these slides are Artificial Intelligence, Zero Trust Architecture, Iot Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
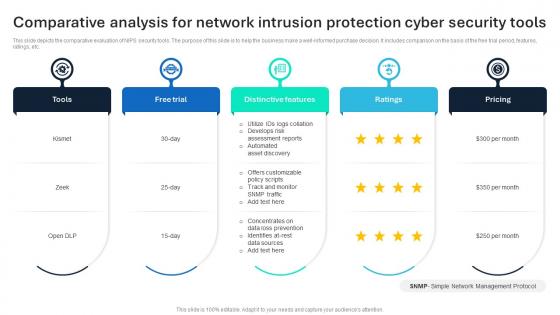 Comparative Analysis For Network Intrusion Protection Cyber Security Tools
Comparative Analysis For Network Intrusion Protection Cyber Security ToolsThis slide depicts the comparative evaluation of NIPS security tools. The purpose of this slide is to help the business make a well informed purchase decision. It includes comparison on the basis of the free trial period, features, ratings, etc. Introducing our premium set of slides with Comparative Analysis For Network Intrusion Protection Cyber Security Tools Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Distinctive Features, Free Trial, Tools So download instantly and tailor it with your information.
-
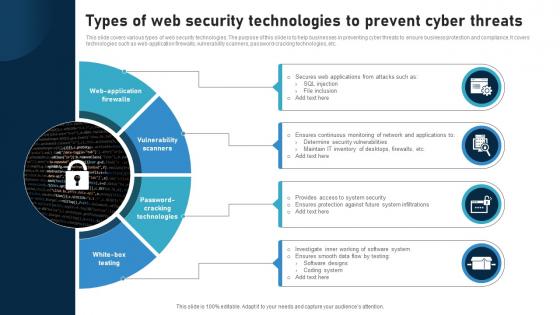 Types Of Web Security Technologies To Prevent Cyber Threats
Types Of Web Security Technologies To Prevent Cyber ThreatsThis slide covers various types of web security technologies. The purpose of this slide is to help businesses in preventing cyber threats to ensure business protection and compliance. It covers technologies such as web application firewalls, vulnerability scanners, password cracking technologies, etc. Presenting our set of slides with Types Of Web Security Technologies To Prevent Cyber Threats This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Web Application Firewalls, Vulnerability Scanners, Password Cracking Technologies
-
 Icon For Ensuring Security By Containerization Technology
Icon For Ensuring Security By Containerization TechnologyPresenting our well structured Icon For Ensuring Security By Containerization Technology. The topics discussed in this slide are Icon, Ensuring Security, Containerization Technology. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
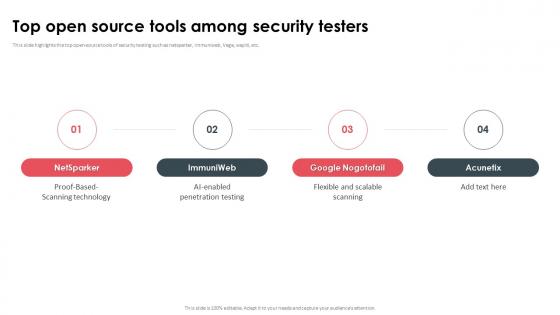 Top Open Source Tools Among Security Testers
Top Open Source Tools Among Security TestersThis slide highlights the top open-source tools of security testing such as netsparker, immuniweb, Vega, wapiti, etc. Increase audience engagement and knowledge by dispensing information using Top Open Source Tools Among Security Testers. This template helps you present information on four stages. You can also present information on Proof Based Scanning Technology, AI Enabled Penetration Testing, Flexible And Scalable Scanning using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
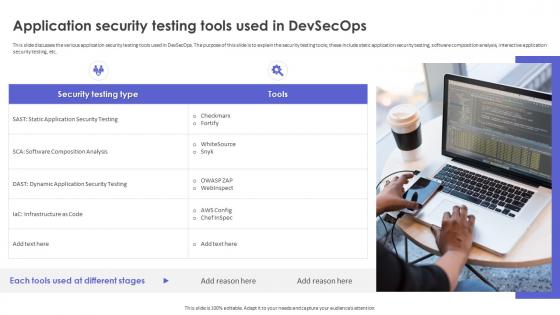 Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps
Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOpsThis slide discusses the various application security testing tools used in DevSecOps. The purpose of this slide is to explain the security testing tools these include static application security testing, software composition analysis, interactive application security testing, etc. Increase audience engagement and knowledge by dispensing information using Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps. This template helps you present information on one stages. You can also present information on Application Security Testing, Software Composition Analysis, Interactive Application Security Testing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



