Powerpoint Templates and Google slides for Social Engineering
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
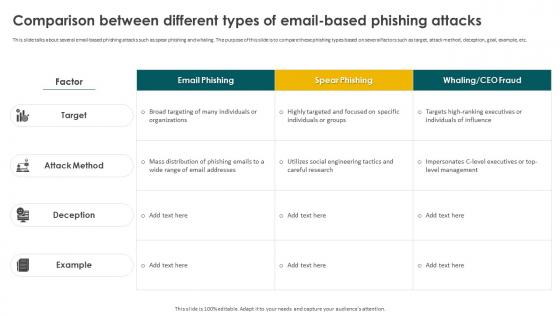 Social Engineering Methods And Mitigation Comparison Between Different Types Of Email Based Phishing
Social Engineering Methods And Mitigation Comparison Between Different Types Of Email Based PhishingThis slide talks about several email-based phishing attacks such as spear phishing and whaling. The purpose of this slide is to compare these phishing types based on several factors such as target, attack method, deception, goal, example, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Comparison Between Different Types Of Email Based Phishing. Dispense information and present a thorough explanation of Email Based Phishing Attacks, Goal, Target, Spear Phishing And Whaling using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation Defensive Strategies Against Tailgating Attacks
Social Engineering Methods And Mitigation Defensive Strategies Against Tailgating AttacksThis slide highlights the best practices to avoid tailgating social engineering attacks. These include beware of surroundings, implement biometric scanners, issue smart badges or cards with RFID technology, install AI-based video surveillance, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Defensive Strategies Against Tailgating Attacks. Use it as a tool for discussion and navigation on Implement Biometric Scanners, Be Aware Of Surroundings, Unique Physical Features. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
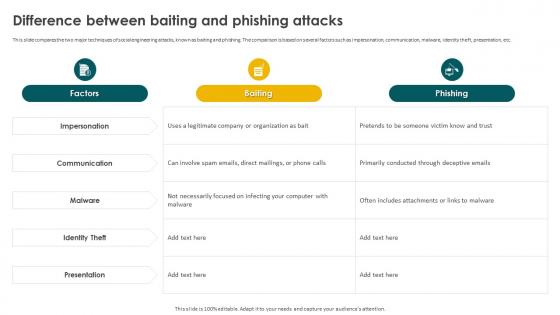 Social Engineering Methods And Mitigation Difference Between Baiting And Phishing Attacks
Social Engineering Methods And Mitigation Difference Between Baiting And Phishing AttacksThis slide compares the two major techniques of social engineering attacks, known as baiting and phishing. The comparison is based on several factors such as impersonation, communication, malware, identity theft, presentation, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Difference Between Baiting And Phishing Attacks. Dispense information and present a thorough explanation of Impersonation, Communication, Identity Theft, Presentation, Malware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
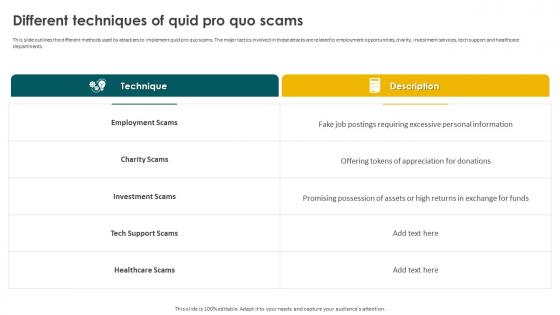 Social Engineering Methods And Mitigation Different Techniques Of Quid Pro Quo Scams
Social Engineering Methods And Mitigation Different Techniques Of Quid Pro Quo ScamsThis slide outlines the different methods used by attackers to implement quid pro quo scams. The major tactics involved in these attacks are related to employment opportunities, charity, investment services, tech support and healthcare departments. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Different Techniques Of Quid Pro Quo Scams. Use it as a tool for discussion and navigation on Employment Scams, Charity Scams, Investment Scams, Tech Support Scams, Healthcare Scams. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation Different Types Of Vishing Cyber Attacks
Social Engineering Methods And Mitigation Different Types Of Vishing Cyber AttacksThis slide talks about the various types of vishing cyber attacks. The purpose of this slide is to briefly explain different techniques of vishing scams used by the attackers to scam users. These are caller ID spoofing, dumpster diving, wardialing, etc. Introducing Social Engineering Methods And Mitigation Different Types Of Vishing Cyber Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vishing Cyber Attacks, Dumpster Diving, Wardialing, Techniques Of Vishing Scams, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Execution Of Man In The Middle Cyber Attacks
Social Engineering Methods And Mitigation Execution Of Man In The Middle Cyber AttacksThis slide illustrates the process of executing man-in-the-middle cyber attacks. The purpose of this slide is to outline the two stages of execution of MITM scams. These stages are interception and decryption. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Execution Of Man In The Middle Cyber Attacks. Dispense information and present a thorough explanation of Cyber Attacks, Intercepting User Traffic, Malicious Wi Fi Hotspots using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation Guidelines To Stay Safe From Phishing Scams
Social Engineering Methods And Mitigation Guidelines To Stay Safe From Phishing ScamsThis slide outlines the various preventive measures to stay safe from phishing attacks. These include know how to spot phishing scams, avoid clicking that link, install free anti-phishing extensions, change passwords regularly, install firewalls, never miss updates, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Guidelines To Stay Safe From Phishing Scams. This template helps you present information on seven stages. You can also present information on Install Firewalls, Change Passwords Regularly, Avoid Clicking That Link, Stay Safe From Phishing Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Methods And Mitigation How To Protect Users From Vishing Attacks
Social Engineering Methods And Mitigation How To Protect Users From Vishing AttacksThis slide talks about the ways to protect users from vishing attacks. These include avoid calls from robots, never respond to audio-automated calls, verify the identity of the caller, never share personal information over the call, use multi-factor authentication, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Guidelines To Stay Safe From Phishing Scams. Use it as a tool for discussion and navigation on Facto Authentication, Government Organizations, Identity Of The Caller, Avoid Calls From Robots. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
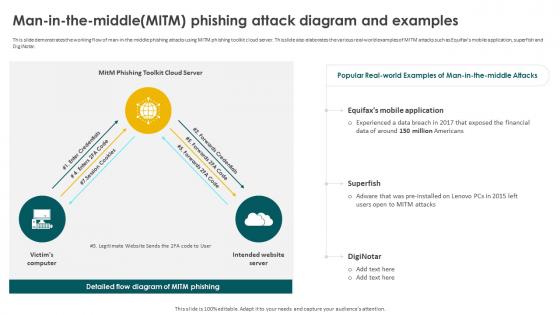 Social Engineering Methods And Mitigation Man In The Middlemitm Phishing Attack Diagram
Social Engineering Methods And Mitigation Man In The Middlemitm Phishing Attack DiagramThis slide demonstrates the working flow of man-in-the-middle phishing attacks using MITM phishing toolkit cloud server. This slide also elaborates the various real-world examples of MITM attacks such as Equifaxs mobile application, superfish and DigiNotar. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Man In The Middlemitm Phishing Attack Diagram. Dispense information and present a thorough explanation of Equifaxs Mobile Application, Superfish, Phishing Attack Diagram, Financial Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
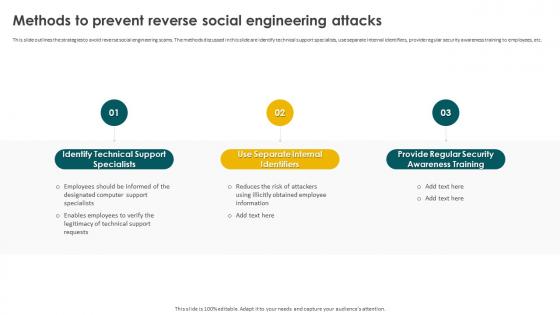 Social Engineering Methods And Mitigation Methods To Prevent Reverse Social Engineering Attacks
Social Engineering Methods And Mitigation Methods To Prevent Reverse Social Engineering AttacksThis slide outlines the strategies to avoid reverse social engineering scams. The methods discussed in this slide are identify technical support specialists, use separate internal identifiers, provide regular security awareness training to employees, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Methods To Prevent Reverse Social Engineering Attacks. This template helps you present information on three stages. You can also present information on Identify Technical Support Specialists, Use Separate Internal Identifiers, Provide Regular Security Awareness Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
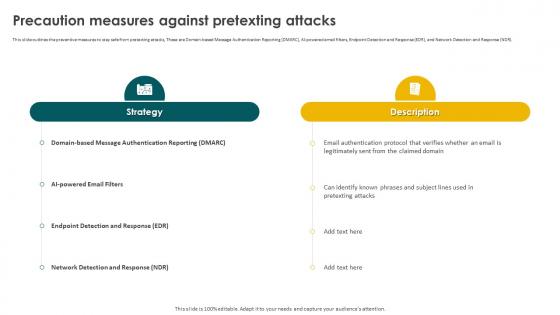 Social Engineering Methods And Mitigation Precaution Measures Against Pretexting Attacks
Social Engineering Methods And Mitigation Precaution Measures Against Pretexting AttacksThis slide outlines the preventive measures to stay safe from pretexting attacks, These are Domain-based Message Authentication Reporting DMARC, AI-powered email filters, Endpoint Detection and Response EDR, and Network Detection and Response NDR. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Precaution Measures Against Pretexting Attacks. Use it as a tool for discussion and navigation on Endpoint Detection And Response, Network Detection And Response, Pretexting Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
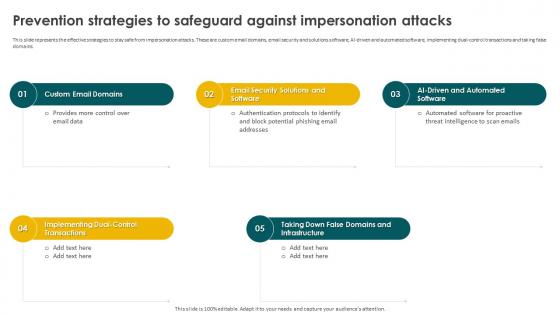 Social Engineering Methods And Mitigation Prevention Strategies To Safeguard Against Impersonation
Social Engineering Methods And Mitigation Prevention Strategies To Safeguard Against ImpersonationThis slide represents the effective strategies to stay safe from impersonation attacks. These are custom email domains, email security and solutions software, AI-driven and automated software, implementing dual-control transactions and taking false domains. Introducing Social Engineering Methods And Mitigation Prevention Strategies To Safeguard Against Impersonation to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Custom Email Domains, Taking Down False Domains, Dual Control Transactions, using this template. Grab it now to reap its full benefits.
-
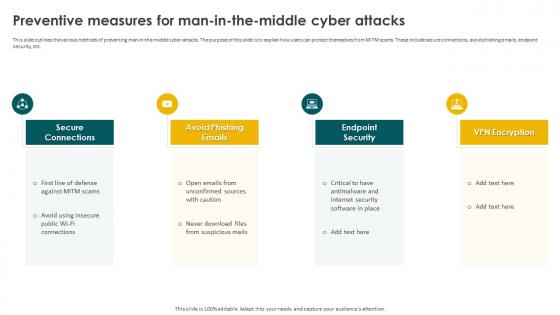 Social Engineering Methods And Mitigation Preventive Measures For Man In The Middle Cyber Attacks
Social Engineering Methods And Mitigation Preventive Measures For Man In The Middle Cyber AttacksThis slide outlines the various methods of preventing man-in-the-middle cyber attacks. The purpose of this slide is to explain how users can protect themselves from MITM scams. These include secure connections, avoid phishing emails, endpoint security, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Preventive Measures For Man In The Middle Cyber Attacks. This template helps you present information on four stages. You can also present information on Secure Connections, Avoid Phishing Emails, Endpoint Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
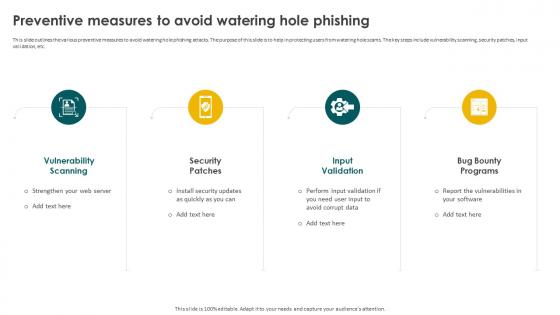 Social Engineering Methods And Mitigation Preventive Measures To Avoid Watering Hole Phishing
Social Engineering Methods And Mitigation Preventive Measures To Avoid Watering Hole PhishingThis slide outlines the various preventive measures to avoid watering hole phishing attacks. The purpose of this slide is to help in protecting users from watering hole scams. The key steps include vulnerability scanning, security patches, input validation, etc. Introducing Social Engineering Methods And Mitigation Preventive Measures To Avoid Watering Hole Phishing to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Scanning, Security Patches, Input Vulnerability, Bug Bounty Programs, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Preventive Strategies For Baiting Cyber Attacks
Social Engineering Methods And Mitigation Preventive Strategies For Baiting Cyber AttacksThis slide outlines the methods to prevent baiting attacks. These are employee training, dont follow links blindly, use anti-virus and anti-malware software, avoid use of external devices without scanning and hold organized simulated attacks. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Preventive Strategies For Baiting Cyber Attacks. Dispense information and present a thorough explanation of Vulnerability Scanning, Security Patches, Input Vulnerability, Bug Bounty Programs using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
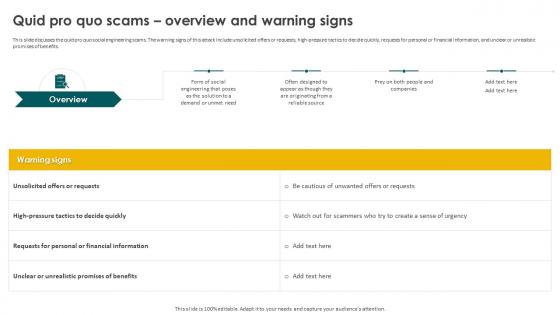 Social Engineering Methods And Mitigation Quid Pro Quo Scams Overview And Warning Signs
Social Engineering Methods And Mitigation Quid Pro Quo Scams Overview And Warning SignsThis slide discusses the quid pro quo social engineering scams. The warning signs of this attack include unsolicited offers or requests, high-pressure tactics to decide quickly, requests for personal or financial information, and unclear or unrealistic promises of benefits. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Quid Pro Quo Scams Overview And Warning Signs. This template helps you present information on four stages. You can also present information on Quid Pro Quo Scams, Unrealistic Promises Of Benefits, Financial Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
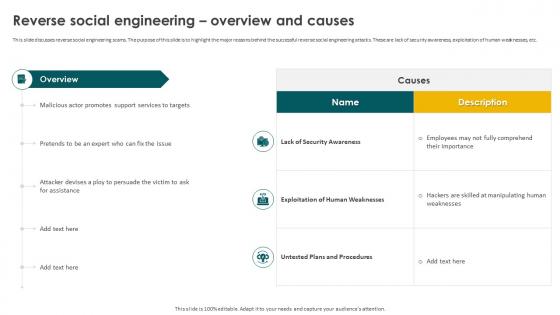 Social Engineering Methods And Mitigation Reverse Social Engineering Overview And Causes
Social Engineering Methods And Mitigation Reverse Social Engineering Overview And CausesThis slide discusses reverse social engineering scams. The purpose of this slide is to highlight the major reasons behind the successful reverse social engineering attacks. These are lack of security awareness, exploitation of human weaknesses, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Reverse Social Engineering Overview And Causes. Use it as a tool for discussion and navigation on Lack Of Security Awareness, Exploitation Of Human Weaknesses, Untested Plans And Procedures. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
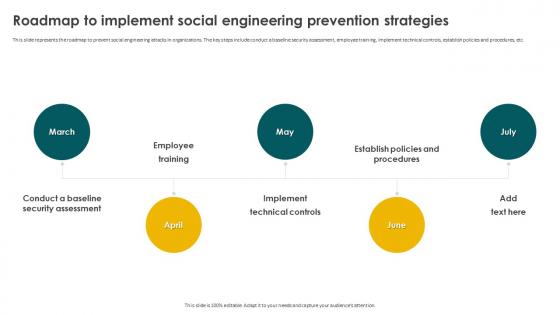 Social Engineering Methods And Mitigation Roadmap To Implement Social Engineering Prevention Strategies
Social Engineering Methods And Mitigation Roadmap To Implement Social Engineering Prevention StrategiesThis slide represents the roadmap to prevent social engineering attacks in organizations. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc. Introducing Social Engineering Methods And Mitigation Roadmap To Implement Social Engineering Prevention Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, Implement Technical Controls, Social Engineering Prevention Strategies, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Scareware Technique Overview And Warning Signs
Social Engineering Methods And Mitigation Scareware Technique Overview And Warning SignsThis slide represents the scareware technique used by scammers to attempt social engineering attacks. The purpose of this slide is to demonstrate the various warning signs of scareware attack. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Scareware Technique Overview And Warning Signs. This template helps you present information on five stages. You can also present information on Scareware Technique, Scareware Attack, Social Engineering Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
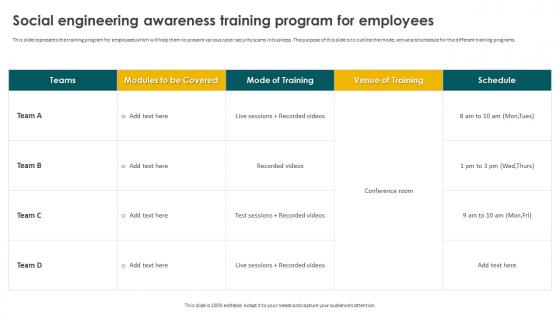 Social Engineering Methods And Mitigation Social Engineering Awareness Training Program For Employees
Social Engineering Methods And Mitigation Social Engineering Awareness Training Program For EmployeesThis slide represents the training program for employees which will help them to prevent various cyber security scams in business. The purpose of this slide is to outline the mode, venue and schedule for the different training programs. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Social Engineering Awareness Training Program For Employees. Use it as a tool for discussion and navigation on Social Engineering, Awareness Training, Program For Employees. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation Social Engineering Technique Dumpster Diving
Social Engineering Methods And Mitigation Social Engineering Technique Dumpster DivingThis slide discusses dumpster diving technique used to carry out social engineering attacks. The various types of information collected include passwords, access codes, organizational charts, calendars, credit card receipts, expense reports, phone numbers, etc. Introducing Social Engineering Methods And Mitigation Social Engineering Technique Dumpster Diving to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Organizational Charts, Network Or Application Diagrams, Dumpster Diving, Social Engineering Technique, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Steps To Identify Whaling Phishing Attacks
Social Engineering Methods And Mitigation Steps To Identify Whaling Phishing AttacksThis slide talks about the various methods of identifying whale phishing cyber attacks. The purpose of this slide is to help users identify CEO phishing scams. These include flag emails received from external domains, cross-verify sensitive requests, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Steps To Identify Whaling Phishing Attacks. This template helps you present information on six stages. You can also present information on Phishing Cyber Attacks, Phishing Scams, External Domains, Cross Verify Sensitive Requests using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
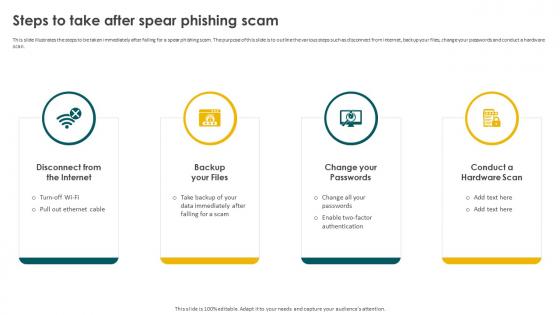 Social Engineering Methods And Mitigation Steps To Take After Spear Phishing Scam
Social Engineering Methods And Mitigation Steps To Take After Spear Phishing ScamThis slide illustrates the steps to be taken immediately after falling for a spear phishing scam. The purpose of this slide is to outline the various steps such as disconnect from internet, backup your files, change your passwords and conduct a hardware scan. Introducing Social Engineering Methods And Mitigation Steps To Take After Spear Phishing Scam to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Disconnect From The Internet, Change Your Passwords, Conduct A Hardware Scan, Backup Your Files, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Strategies Techniques Table Of Contents
Social Engineering Methods And Mitigation Strategies Techniques Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Strategies Techniques Table Of Contents. This template helps you present information on one stages. You can also present information on Overview And Warning Signs, Common Tactics Used, Working Process, Tools And Best Practices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
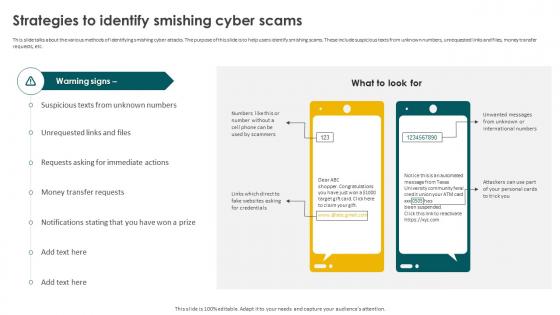 Social Engineering Methods And Mitigation Strategies To Identify Smishing Cyber Scams
Social Engineering Methods And Mitigation Strategies To Identify Smishing Cyber ScamsThis slide talks about the various methods of identifying smishing cyber attacks. The purpose of this slide is to help users identify smishing scams. These include suspicious texts from unknown numbers, unrequested links and files, money transfer requests, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Strategies To Identify Smishing Cyber Scams. Dispense information and present a thorough explanation of Smishing Cyber Scams, Money Transfer Requests, Unrequested Links And Files using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
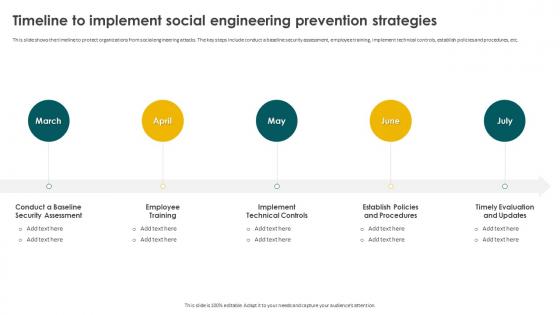 Social Engineering Methods And Mitigation Timeline To Implement Social Engineering Prevention Strategies
Social Engineering Methods And Mitigation Timeline To Implement Social Engineering Prevention StrategiesThis slide shows the timeline to protect organizations from social engineering attacks. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc. Introducing Social Engineering Methods And Mitigation Timeline To Implement Social Engineering Prevention Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, Implement Technical Controls, Establish Policies And Procedures, Timely Evaluation And Updates, using this template. Grab it now to reap its full benefits.
-
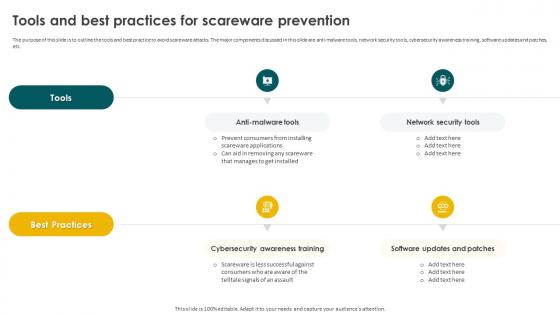 Social Engineering Methods And Mitigation Tools And Best Practices For Scareware Prevention
Social Engineering Methods And Mitigation Tools And Best Practices For Scareware PreventionThe purpose of this slide is to outline the tools and best practice to avoid scareware attacks. The major components discussed in this slide are anti-malware tools, network security tools, cybersecurity awareness training, software updates and patches, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Tools And Best Practices For Scareware Prevention. Use it as a tool for discussion and navigation on Anti Malware Tools, Network Security Tools, Software Updates And Patches, Cybersecurity Awareness Training. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation Understanding The Process Of E Mail Based Phishing Attacks
Social Engineering Methods And Mitigation Understanding The Process Of E Mail Based Phishing AttacksThis slide demonstrates the procedure of email-based phishing attacks. The purpose of this slide is to explain how fake websites are used by attackers to get the sensitive data of the users. The key components include database, fake website, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Understanding The Process Of E Mail Based Phishing Attacks. Dispense information and present a thorough explanation of Phishing Attacks, Fake Website, Email Based Phishing Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation Understanding The Working Process Of Scareware Scam
Social Engineering Methods And Mitigation Understanding The Working Process Of Scareware ScamThis slide represents the various steps involved in fake antivirus scareware campaign process. The major components are victim, bank, fake anti-virus website, payment processor, affiliates, settlement systems, credit card company, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Understanding The Working Process Of Scareware Scam. Use it as a tool for discussion and navigation on Understanding The Working Process, Scareware Scam, Payment Processor, Affiliates, Settlement Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation Working Of Watering Hole Phishing Attack
Social Engineering Methods And Mitigation Working Of Watering Hole Phishing AttackThis slide represents the working process of watering hole phishing attacks. The purpose of this slide is to illustrate the flow diagram of watering hole phishing scams. The key points include research and identification, analysis, preparation and execution. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Working Of Watering Hole Phishing Attack. This template helps you present information on four stages. You can also present information on Research And Identification, Analysis, Preparation, Domain And Subdomain Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
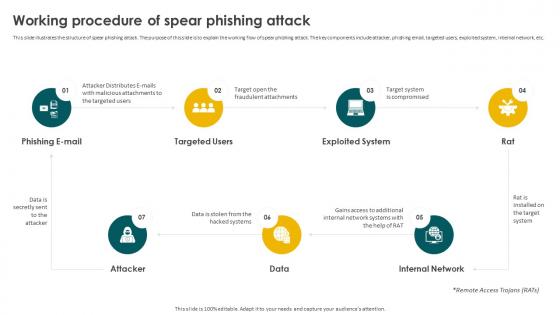 Social Engineering Methods And Mitigation Working Procedure Of Spear Phishing Attack
Social Engineering Methods And Mitigation Working Procedure Of Spear Phishing AttackThis slide illustrates the structure of spear phishing attack. The purpose of this slide is to explain the working flow of spear phishing attack. The key components include attacker, phishing email, targeted users, exploited system, internal network, etc. Introducing Social Engineering Methods And Mitigation Working Procedure Of Spear Phishing Attack to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Email, Targeted Users, Exploited System, Internal Network, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Social Engineering Methods And Mitigation Strategies
Table Of Contents For Social Engineering Methods And Mitigation StrategiesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Social Engineering Methods And Mitigation Strategies. This template helps you present information on five stages. You can also present information on Social Engineering Attacks, Mitigation Strategies, Training And Budget, Tracking Dashboard using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


