Powerpoint Templates and Google slides for Social Engineering
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Social engineering with hacker and danger symbol
Social engineering with hacker and danger symbolPresenting this set of slides with name - Social Engineering With Hacker And Danger Symbol. This is a three stage process. The stages in this process are Social Engineering, Information Security, Psychological Manipulation.
-
 Social engineering with hacker and spam message
Social engineering with hacker and spam messagePresenting this set of slides with name - Social Engineering With Hacker And Spam Message. This is a five stage process. The stages in this process are Social Engineering, Information Security, Psychological Manipulation.
-
 Social engineering with hand tied up
Social engineering with hand tied upPresenting this set of slides with name - Social Engineering With Hand Tied Up. This is a four stage process. The stages in this process are Social Engineering, Information Security, Psychological Manipulation.
-
 Social engineering with launch attacks and reporting
Social engineering with launch attacks and reportingPresenting this set of slides with name - Social Engineering With Launch Attacks And Reporting. This is a six stage process. The stages in this process are Social Engineering, Information Security, Psychological Manipulation.
-
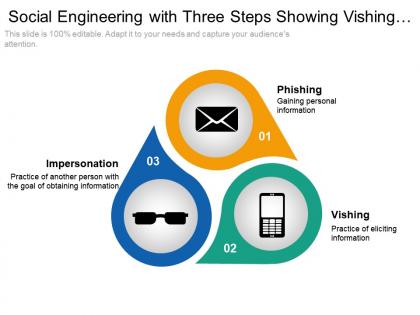 Social engineering with three steps showing vishing phishing and impersonation
Social engineering with three steps showing vishing phishing and impersonationPresenting this set of slides with name - Social Engineering With Three Steps Showing Vishing Phishing And Impersonation. This is a three stage process. The stages in this process are Social Engineering, Information Security, Psychological Manipulation.
-
 Search engine marketing social media strategy threat analysis cpb
Search engine marketing social media strategy threat analysis cpbPresenting this set of slides with name - Search Engine Marketing Social Media Strategy Threat Analysis Cpb. This is an editable five graphic that deals with topics like Search Engine Marketing, Social Media Strategy, Threat Analysis to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
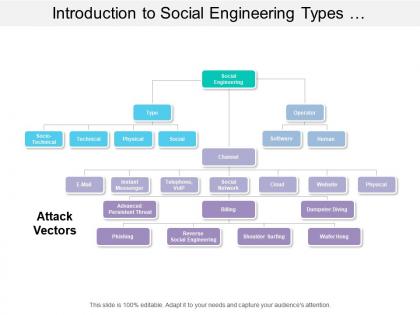 Introduction to social engineering types operator channels
Introduction to social engineering types operator channelsPresenting this set of slides with name - Introduction To Social Engineering Types Operator Channels. This is a three stage process. The stages in this process are Social Engineering, Social Network, Technology.
-
 Social engineering attack icon for malicious activities
Social engineering attack icon for malicious activitiesPresenting this set of slides with name - Social Engineering Attack Icon For Malicious Activities. This is a three stage process. The stages in this process are Social Engineering, Social Network, Technology.
-
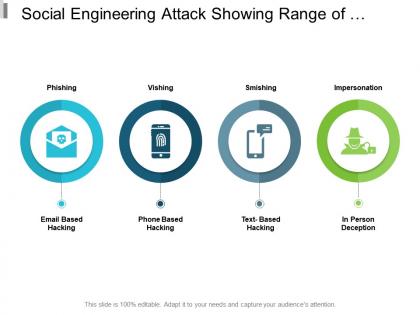 Social engineering attack showing range of malicious activities
Social engineering attack showing range of malicious activitiesPresenting this set of slides with name - Social Engineering Attack Showing Range Of Malicious Activities. This is a four stage process. The stages in this process are Social Engineering, Social Network, Technology.
-
 Social engineering icon of information security
Social engineering icon of information securityPresenting this set of slides with name - Social Engineering Icon Of Information Security. This is a three stage process. The stages in this process are Social Engineering, Social Network, Technology.
-
 Social engineering icon showing malicious activities
Social engineering icon showing malicious activitiesPresenting this set of slides with name - Social Engineering Icon Showing Malicious Activities. This is a three stage process. The stages in this process are Social Engineering, Social Network, Technology.
-
 Social engineering methodology showing six process steps
Social engineering methodology showing six process stepsPresenting this set of slides with name - Social Engineering Methodology Showing Six Process Steps. This is a six stage process. The stages in this process are Social Engineering, Social Network, Technology.
-
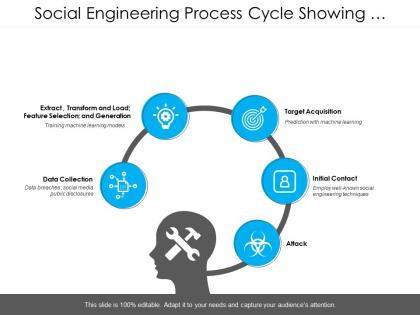 Social engineering process cycle showing five steps
Social engineering process cycle showing five stepsPresenting this set of slides with name - Social Engineering Process Cycle Showing Five Steps. This is a five stage process. The stages in this process are Social Engineering, Social Network, Technology.
-
 Search engine optimization social media ppt powerpoint presentation summary rules cpb
Search engine optimization social media ppt powerpoint presentation summary rules cpbPresenting this set of slides with name Search Engine Optimization Social Media Ppt Powerpoint Presentation Summary Rules Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Search Engine Optimization Social Media to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Search engine ranking social media marketing ppt powerpoint presentation file graphics cpb
Search engine ranking social media marketing ppt powerpoint presentation file graphics cpbPresenting this set of slides with name Search Engine Ranking Social Media Marketing Ppt Powerpoint Presentation File Graphics Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Search Engine Ranking Social Media Marketing to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
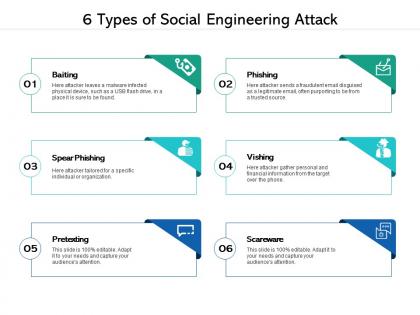 6 types of social engineering attack
6 types of social engineering attackPresenting this set of slides with name 6 Types Of Social Engineering Attack. This is a six process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Different ways to prevent social engineering attacks
Different ways to prevent social engineering attacksPresenting this set of slides with name Different Ways To Prevent Social Engineering Attacks. This is a four process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon of social engineering with two man
Icon of social engineering with two manPresenting this set of slides with name Icon Of Social Engineering With Two Man. This is a one process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
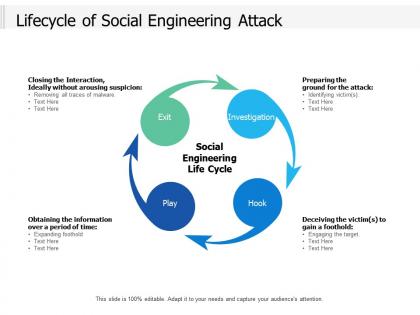 Lifecycle of social engineering attack
Lifecycle of social engineering attackPresenting this set of slides with name Lifecycle Of Social Engineering Attack. This is a four process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Social engineering attack lifecycle with investigation and play
Social engineering attack lifecycle with investigation and playPresenting this set of slides with name Social Engineering Attack Lifecycle With Investigation And Play. This is a four process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
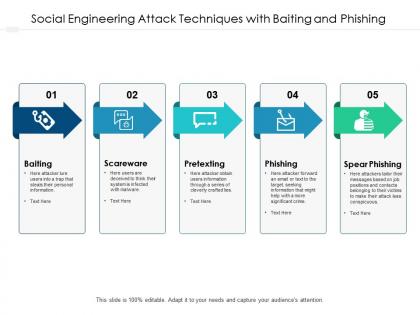 Social engineering attack techniques with baiting and phishing
Social engineering attack techniques with baiting and phishingPresenting this set of slides with name Social Engineering Attack Techniques With Baiting And Phishing. This is a five process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Social engineering icon with man inside circle
Social engineering icon with man inside circlePresenting this set of slides with name Social Engineering Icon With Man Inside Circle. This is a four process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
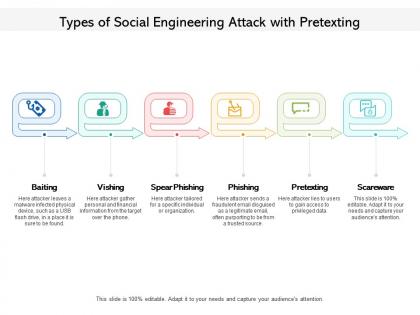 Types of social engineering attack with pretexting
Types of social engineering attack with pretextingPresenting this set of slides with name Types Of Social Engineering Attack With Pretexting. This is a six process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
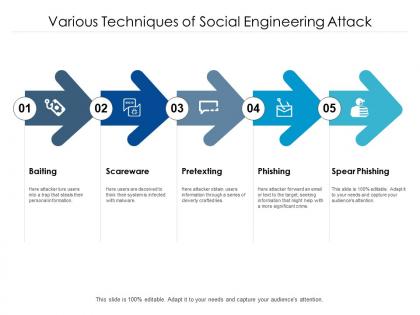 Various techniques of social engineering attack
Various techniques of social engineering attackPresenting this set of slides with name Various Techniques Of Social Engineering Attack. This is a five process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Search engine optimization seo social ppt powerpoint presentation show
Search engine optimization seo social ppt powerpoint presentation showPresenting this set of slides with name Search Engine Optimization Seo Social Ppt Powerpoint Presentation Show. The topics discussed in these slides are Marketing, Business, Management, Planning, Strategy. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
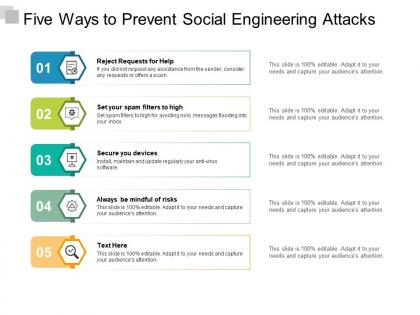 Five ways to prevent social engineering attacks
Five ways to prevent social engineering attacksPresenting this set of slides with name Five Ways To Prevent Social Engineering Attacks. This is a five process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Social engineering solutions ppt powerpoint presentation model cpb
Social engineering solutions ppt powerpoint presentation model cpbPresenting this set of slides with name Social Engineering Solutions Ppt Powerpoint Presentation Model Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Social Engineering Solutions to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Social engineering example ppt powerpoint presentation ideas cpb
Social engineering example ppt powerpoint presentation ideas cpbPresenting this set of slides with name Social Engineering Example Ppt Powerpoint Presentation Ideas Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Social Engineering Example to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Social engineering statistics ppt powerpoint presentation pictures designs cpb
Social engineering statistics ppt powerpoint presentation pictures designs cpbPresenting this set of slides with name Social Engineering Statistics Ppt Powerpoint Presentation Pictures Designs Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Social Engineering Statistics to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security social engineering ppt powerpoint presentation summary styles cpb
Information security social engineering ppt powerpoint presentation summary styles cpbPresenting this set of slides with name Information Security Social Engineering Ppt Powerpoint Presentation Summary Styles Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Information Security Social Engineering to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Social engineering systems ppt powerpoint presentation professional samples cpb
Social engineering systems ppt powerpoint presentation professional samples cpbPresenting this set of slides with name Social Engineering Systems Ppt Powerpoint Presentation Professional Samples Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Social Engineering Systems to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Social engineering training ppt powerpoint presentation styles visuals cpb
Social engineering training ppt powerpoint presentation styles visuals cpbPresenting this set of slides with name Social Engineering Training Ppt Powerpoint Presentation Styles Visuals Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Social Engineering Training to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Common social engineering tactics ppt infographic template graphics pictures cpb
Common social engineering tactics ppt infographic template graphics pictures cpbPresenting this set of slides with name Common Social Engineering Tactics Ppt Infographic Template Graphics Pictures Cpb. This is an editable Powerpoint seven stages graphic that deals with topics like Common Social Engineering Tactics to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Social engineering tactics ppt powerpoint presentation summary tips cpb
Social engineering tactics ppt powerpoint presentation summary tips cpbPresenting this set of slides with name Social Engineering Tactics Ppt Powerpoint Presentation Summary Tips Cpb. This is an editable Powerpoint seven stages graphic that deals with topics like Social Engineering Tactics to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Primary countermeasure social engineering ppt powerpoint presentation infographics mockup cpb
Primary countermeasure social engineering ppt powerpoint presentation infographics mockup cpbPresenting Primary Countermeasure Social Engineering Ppt Powerpoint Presentation Infographics Mockup Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Primary Countermeasure Social Engineering. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Social engineering techniques ppt powerpoint presentation slides example introduction cpb
Social engineering techniques ppt powerpoint presentation slides example introduction cpbPresenting Social Engineering Techniques Ppt Powerpoint Presentation Slides Example Introduction Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Social Engineering Techniques. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Phishing social engineering cybercrime ppt powerpoint presentation professional visuals cpb
Phishing social engineering cybercrime ppt powerpoint presentation professional visuals cpbPresenting our innovatively designed set of slides titled Phishing Social Engineering Cybercrime Ppt Powerpoint Presentation Professional Visuals Cpb. This completely editable PowerPoint graphic exhibits Phishing Social Engineering Cybercrime that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design.
-
 Social engineering vs phishing ppt powerpoint presentation slides influencers cpb
Social engineering vs phishing ppt powerpoint presentation slides influencers cpbPresenting Social Engineering Vs Phishing Ppt Powerpoint Presentation Slides Influencers Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Social Engineering Vs Phishing. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Social engineering ppt powerpoint presentation summary introduction cpb
Social engineering ppt powerpoint presentation summary introduction cpbPresenting Social Engineering Ppt Powerpoint Presentation Summary Introduction Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the colour, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Profits Interests. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Social engineering attack ppt powerpoint presentation infographics ideas cpb
Social engineering attack ppt powerpoint presentation infographics ideas cpbPresenting Social Engineering Attack Ppt Powerpoint Presentation Infographics Ideas Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Social Engineering Attack. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Social engineering attack example ppt powerpoint presentation file introduction cpb
Social engineering attack example ppt powerpoint presentation file introduction cpbPresenting Social Engineering Attack Example Ppt Powerpoint Presentation File Introduction Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Social Engineering Attack Example. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Social engineering attacks ppt powerpoint presentation model inspiration cpb
Social engineering attacks ppt powerpoint presentation model inspiration cpbPresenting Social Engineering Attacks Ppt Powerpoint Presentation Model Inspiration Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Social Engineering Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
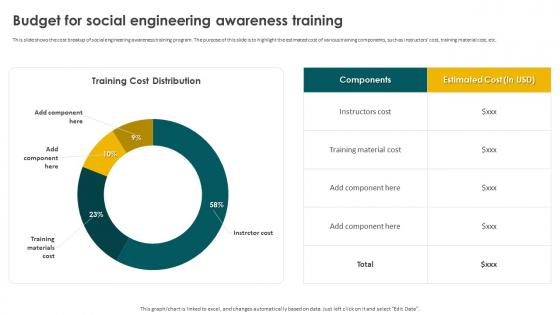 Social Engineering Methods And Mitigation Budget For Social Engineering Awareness Training
Social Engineering Methods And Mitigation Budget For Social Engineering Awareness TrainingThis slide shows the cost breakup of social engineering awareness training program. The purpose of this slide is to highlight the estimated cost of various training components, such as instructors cost, training material cost, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Budget For Social Engineering Awareness Training. Use it as a tool for discussion and navigation on Budget For Social Engineering, Awareness Training, Training Components, Training Material Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation Social Engineering Attacks Tracking Dashboard
Social Engineering Methods And Mitigation Social Engineering Attacks Tracking DashboardThis slide represents the dashboard to track social engineering attacks. The purpose of this slide is to provide a graphical representation of cyber attacks occurred in a specific time span. It also depicts the overview of different types of attacks. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Social Engineering Attacks Tracking Dashboard. Dispense information and present a thorough explanation of Social Engineering Attacks, Tracking Dashboard, Unique Suspicious Emails using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda For Social Engineering Methods And Mitigation Strategies
Agenda For Social Engineering Methods And Mitigation StrategiesIntroducing Agenda For Social Engineering Methods And Mitigation Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Impersonation, Tailgating, Pretexting, Scareware, Mitigation Strategies, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Social Engineering Methods And Mitigation Strategies
Icons Slide For Social Engineering Methods And Mitigation StrategiesIntroducing our well researched set of slides titled Icons Slide For Social Engineering Methods And Mitigation Strategies. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
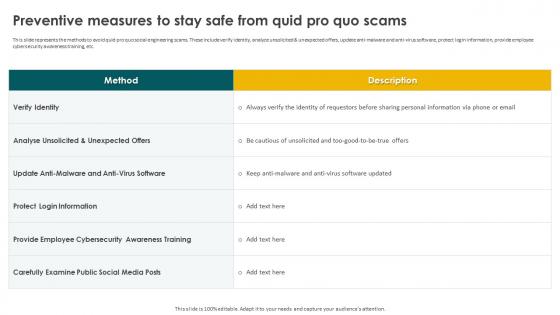 Preventive Measures To Stay Safe From Quid Pro Quo Scams Social Engineering Methods And Mitigation
Preventive Measures To Stay Safe From Quid Pro Quo Scams Social Engineering Methods And MitigationThis slide represents the methods to avoid quid pro quo social engineering scams. These include verify identity, analyze unsolicited and unexpected offers, update anti-malware and anti-virus software, protect login information, provide employee cybersecurity awareness training, etc. Present the topic in a bit more detail with this Preventive Measures To Stay Safe From Quid Pro Quo Scams Social Engineering Methods And Mitigation. Use it as a tool for discussion and navigation on Protect Login Information, Anti Virus Software, Quid Pro Quo Scams. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation 30 60 90 Days Plan To Implement Social Engineering Prevention
Social Engineering Methods And Mitigation 30 60 90 Days Plan To Implement Social Engineering PreventionThis slide represents 30-60-90 plan to protect companies and their employees from social engineering attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Introducing Social Engineering Methods And Mitigation 30 60 90 Days Plan To Implement Social Engineering Prevention to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering, Prevention Strategies, Protect Companies, Social Engineering Attacks, using this template. Grab it now to reap its full benefits.
-
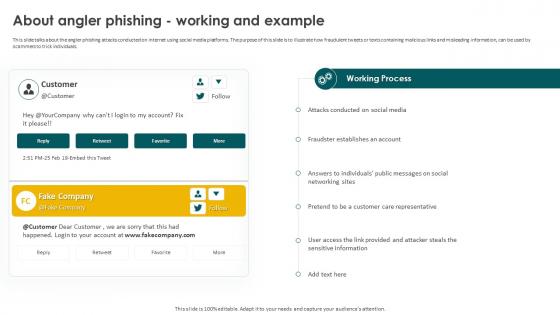 Social Engineering Methods And Mitigation About Angler Phishing Working And Example
Social Engineering Methods And Mitigation About Angler Phishing Working And ExampleThis slide talks about the angler phishing attacks conducted on internet using social media platforms. The purpose of this slide is to illustrate how fraudulent tweets or texts containing malicious links and misleading information, can be used by scammers to trick individuals. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation About Angler Phishing Working And Example. Dispense information and present a thorough explanation of Angler Phishing Attacks, Social Media Platforms, Fraudulent Tweets, Texts Containing Malicious using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
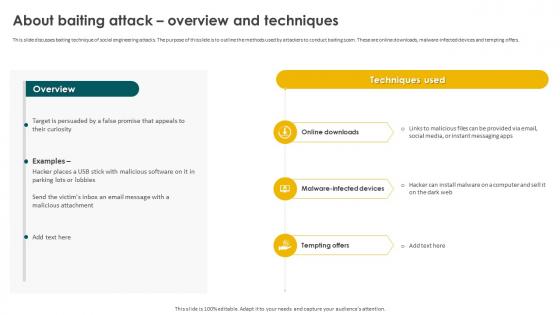 Social Engineering Methods And Mitigation About Baiting Attack Overview And Techniques
Social Engineering Methods And Mitigation About Baiting Attack Overview And TechniquesThis slide discusses baiting technique of social engineering attacks. The purpose of this slide is to outline the methods used by attackers to conduct baiting scam. These are online downloads, malware-infected devices and tempting offers. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation About Baiting Attack Overview And Techniques. Use it as a tool for discussion and navigation on Online Downloads, Malware Infected Devices, Baiting Attack, Malicious Attachment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
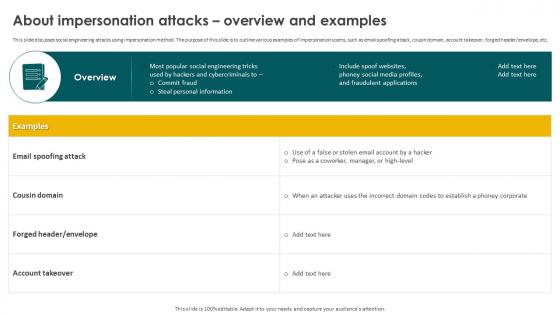 Social Engineering Methods And Mitigation About Impersonation Attacks Overview And Examples
Social Engineering Methods And Mitigation About Impersonation Attacks Overview And ExamplesThis slide discusses social engineering attacks using impersonation method. The purpose of this slide is to outline various examples of impersonation scams, such as email spoofing attack, cousin domain, account takeover, forged header or envelope, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation About Impersonation Attacks Overview And Examples. Dispense information and present a thorough explanation of Email Spoofing Attack, Cousin Domain, Fraudulent Applications, Impersonation Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
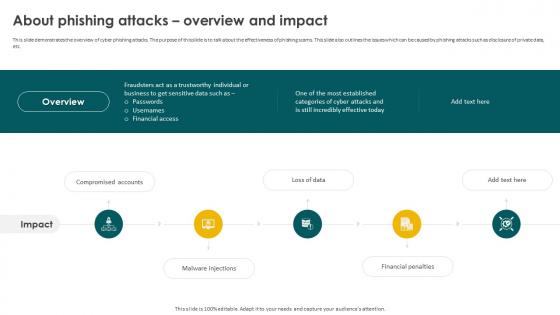 Social Engineering Methods And Mitigation About Phishing Attacks Overview And Impact
Social Engineering Methods And Mitigation About Phishing Attacks Overview And ImpactThis slide demonstrates the overview of cyber phishing attacks. The purpose of this slide is to talk about the effectiveness of phishing scams. This slide also outlines the issues which can be caused by phishing attacks such as disclosure of private data, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation About Phishing Attacks Overview And Impact. This template helps you present information on five stages. You can also present information on Compromised Accounts, Malware Injections, Financial Penalties, Financial Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
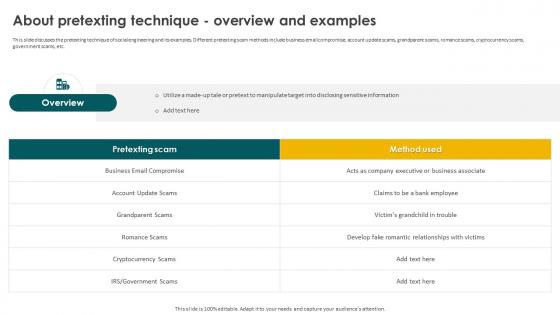 Social Engineering Methods And Mitigation About Pretexting Technique Overview And Examples
Social Engineering Methods And Mitigation About Pretexting Technique Overview And ExamplesThis slide discusses the pretexting technique of social engineering and its examples. Different pretexting scam methods include business email compromise, account update scams, grandparent scams, romance scams, cryptocurrency scams, government scams, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation About Pretexting Technique Overview And Examples. Use it as a tool for discussion and navigation on Business Email Compromise, Grandparent Scams, Cryptocurrency Scams, Pretexting Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation About Smishing Attacks Overview And Types
Social Engineering Methods And Mitigation About Smishing Attacks Overview And TypesThis slide talks about the smishing cyber attacks conducted by sending text messages to the targets. The purpose of this slide is to illustrate how fraudulent texts are sent to the users which contains malicious links and other mis-leading information. Introducing Social Engineering Methods And Mitigation About Smishing Attacks Overview And Types to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Smishing Scams, Financial Services Smishing, Gift Smishing, Customer Support Smishing, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation About Tailgating Attacks Overview And Techniques
Social Engineering Methods And Mitigation About Tailgating Attacks Overview And TechniquesThis slide demonstrates the procedure of tailgating attack with the help of an illustrative example. The purpose of this slide is to provide the overview of tailgating social engineering attack and the techniques used to implement it in organizations. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation About Tailgating Attacks Overview And Techniques. Dispense information and present a thorough explanation of Procedure Of Tailgating Attack, Tailgating Social Engineering Attack, Subcontractors Identity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation About Vishing Attacks Overview And Identification
Social Engineering Methods And Mitigation About Vishing Attacks Overview And IdentificationThis slide talks about the vishing cyber attacks. The purpose of this slide is to explain the vishing technique used by phishers to scam victims. This slide also outlines the signs of vishing attack such as call from unknown number, act as an authority, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation About Vishing Attacks Overview And Identification. Use it as a tool for discussion and navigation on Vishing Cyber Attacks, Vishing Technique, Phishers To Scam Victims, Internal Revenue Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
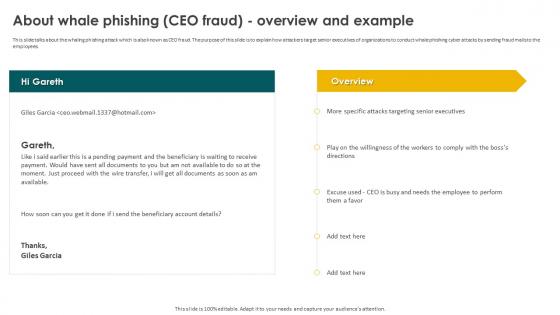 Social Engineering Methods And Mitigation About Whale Phishing CEO Fraud Overview And Example
Social Engineering Methods And Mitigation About Whale Phishing CEO Fraud Overview And ExampleThis slide talks about the whaling phishing attack which is also known as CEO fraud. The purpose of this slide is to explain how attackers target senior executives of organizations to conduct whale phishing cyber attacks by sending fraud mails to the employees. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation About Whale Phishing CEO Fraud Overview And Example. Dispense information and present a thorough explanation of Whaling Phishing Attack, Attackers Target Senior Executives, Phishing Cyber Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
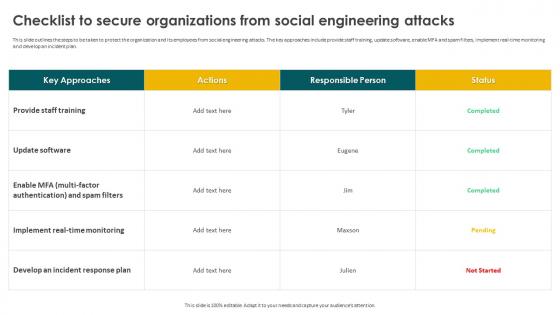 Social Engineering Methods And Mitigation Checklist To Secure Organizations From Social Engineering
Social Engineering Methods And Mitigation Checklist To Secure Organizations From Social EngineeringThis slide outlines the steps to be taken to protect the organization and its employees from social engineering attacks. The key approaches include provide staff training, update software, enable MFA and spam filters, implement real-time monitoring and develop an incident plan. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Checklist To Secure Organizations From Social Engineering. Dispense information and present a thorough explanation of Social Engineering Attacks, Real Time Monitoring, Develop An Incident Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation Classification Of Different Social Engineering Attacks
Social Engineering Methods And Mitigation Classification Of Different Social Engineering AttacksThis slide represents the different types of social engineering attacks based on technology and human interaction. These include impersonation, tailgating, baiting, pretexting, scareware, quid pro quo, reverse social engineering, phishing, email phishing, spear phishing, whaling, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Classification Of Different Social Engineering Attacks. This template helps you present information on two stages. You can also present information on Human Based Attacks, Social Engineering Attacks, Technology Based Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
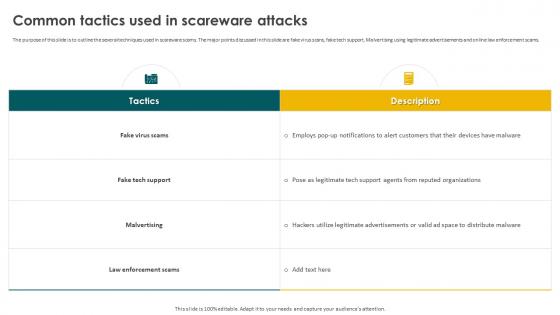 Social Engineering Methods And Mitigation Common Tactics Used In Scareware Attacks
Social Engineering Methods And Mitigation Common Tactics Used In Scareware AttacksThe purpose of this slide is to outline the several techniques used in scareware scams. The major points discussed in this slide are fake virus scans, fake tech support, Malvertising using legitimate advertisements and online law enforcement scams. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Common Tactics Used In Scareware Attacks. Use it as a tool for discussion and navigation on Fake Virus Scams, Malvertising, Law Enforcement Scams, Fake Tech Support. This template is free to edit as deemed fit for your organization. Therefore download it now.



