Powerpoint Templates and Google slides for Threat Identification
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Automating threat identification powerpoint presentation slides
Automating threat identification powerpoint presentation slidesEnthrall your audience with this Automating Threat Identification Powerpoint Presentation Slides. Increase your presentation threshold by deploying this well-crafted template. It acts as a great communication tool due to its well-researched content. It also contains stylized icons, graphics, visuals etc, which make it an immediate attention-grabber. Comprising sixty four slides, this complete deck is all you need to get noticed. All the slides and their content can be altered to suit your unique business setting. Not only that, other components and graphics can also be modified to add personal touches to this prefabricated set.
-
 Identifying Threats As A Step For Cybersecurity Risk Identification Training Ppt
Identifying Threats As A Step For Cybersecurity Risk Identification Training PptPresenting Identifying Threats as a Step for Cybersecurity Risk Identification. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Ultimate Guide For Blockchain Performing Threat Assessment For Cause Identification BCT SS
Ultimate Guide For Blockchain Performing Threat Assessment For Cause Identification BCT SSThe following slide depicts the amount of loss incurred due to blockchain frauds and scams to securely encrypt financial transactions. It includes elements such as loss amount, number of incidents along with key insights, etc. Deliver an outstanding presentation on the topic using this Ultimate Guide For Blockchain Performing Threat Assessment For Cause Identification BCT SS Dispense information and present a thorough explanation of Double Spending, Mining Threats, Wallet Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managed Detection And Response Icon For Early Threat Identification
Managed Detection And Response Icon For Early Threat IdentificationPresenting our set of slides with Managed Detection And Response Icon For Early Threat Identification. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Managed, Identification, Response.
-
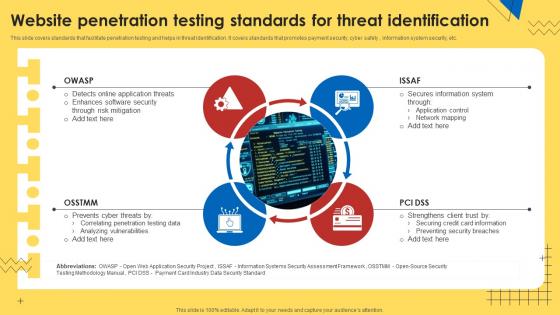 Website Penetration Testing Standards For Threat Identification
Website Penetration Testing Standards For Threat IdentificationThis slide covers standards that facilitate penetration testing and helps in threat identification. It covers standards that promotes payment security, cyber safety , information system security, etc. Presenting our set of slides with Website Penetration Testing Standards For Threat Identification. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information System, Application Control, Network Mapping.
-
 Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS V
Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting Blockchain to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Performing Threat Assessment For Cause Identification Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Threats, Attack Vectors, Causes, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Icon For Threat Identification
Cyber Security Icon For Threat IdentificationIntroducing our premium set of slides with Cyber Security Icon For Threat Identification. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Icon, Threat Identification. So download instantly and tailor it with your information.
-
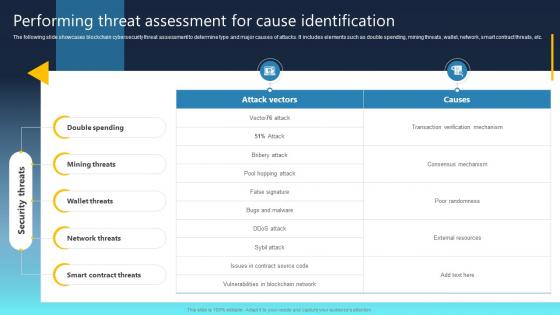
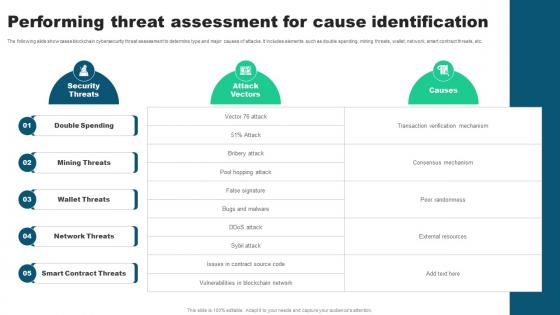 Performing Threat Assessment For Cause Identification Guide For Blockchain BCT SS V
Performing Threat Assessment For Cause Identification Guide For Blockchain BCT SS VThe following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Present the topic in a bit more detail with this Performing Threat Assessment For Cause Identification Guide For Blockchain BCT SS V Use it as a tool for discussion and navigation on Double Spending, Mining Threats, Wallet Threats, Network Threats This template is free to edit as deemed fit for your organization. Therefore download it now.
-
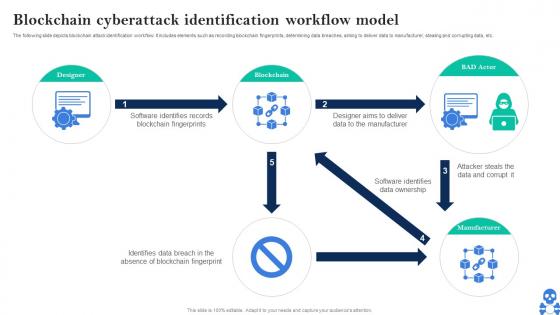 Cyber Threats In Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS V
Cyber Threats In Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS V Use it as a tool for discussion and navigation on Designer, Blockchain, BAD Actor This template is free to edit as deemed fit for your organization. Therefore download it now.
-
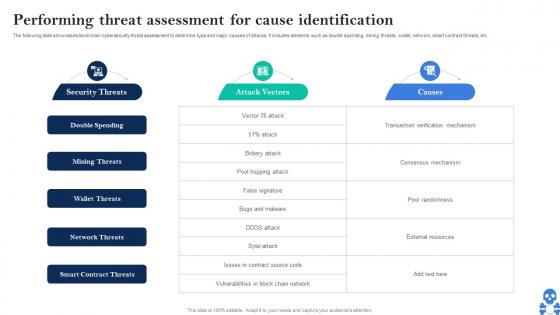 Cyber Threats In Blockchain Performing Threat Assessment For Cause Identification BCT SS V
Cyber Threats In Blockchain Performing Threat Assessment For Cause Identification BCT SS VThe following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Major Cybersecurity Challenges In Blockchain Technology BCT SS V Dispense information and present a thorough explanation of Double Spending, Mining Threats, Wallet Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
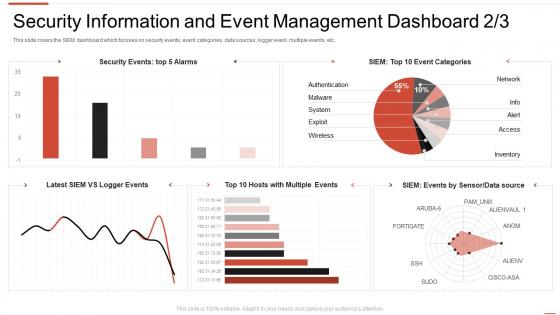 Automating threat identification event management dashboard sanpshot
Automating threat identification event management dashboard sanpshotThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an outstanding presentation on the topic using this Automating Threat Identification Event Management Dashboard Snapshot. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
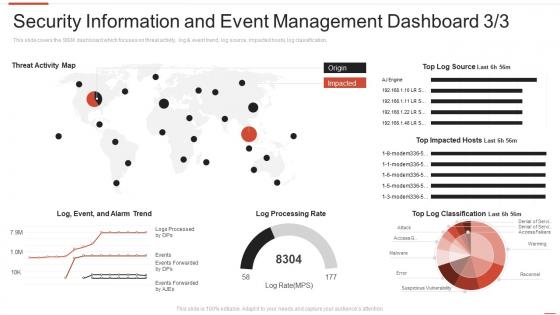 Automating threat identification information and event management dashboard
Automating threat identification information and event management dashboardThis slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification, Deliver an outstanding presentation on the topic using this Automating Threat Identification Information And Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
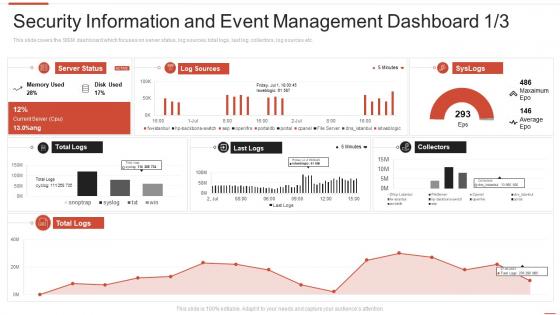 Information and event management dashboard automating threat identification
Information and event management dashboard automating threat identificationThis slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Present the topic in a bit more detail with this Information And Event Management Dashboard Automating Threat Identification. Use it as a tool for discussion and navigation on Information, Management, Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
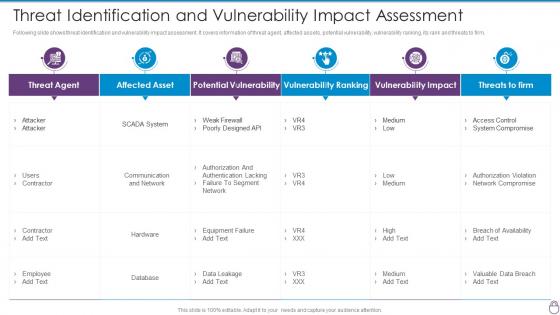 Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact
Cybersecurity Risk Management Framework Threat Identification And Vulnerability ImpactFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact. Dispense information and present a thorough explanation of Threat Agent, Affected Asset, Potential Vulnerability, Vulnerability Ranking, Vulnerability Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Insider Threat Identification Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Insider Threat Identification Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Insider threat identification colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Insider Threat Identification Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Insider Threat Identification Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Insider threat identification monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
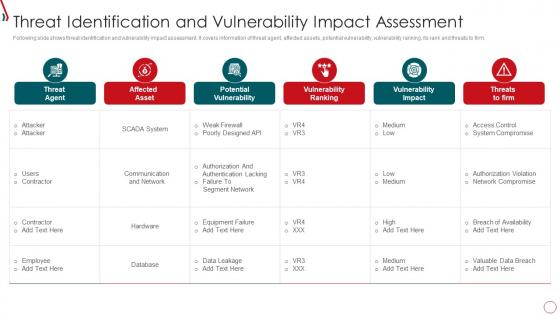 Risk Management Framework For Information Security Threat Identification And Vulnerability
Risk Management Framework For Information Security Threat Identification And VulnerabilityFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Threat Identification And Vulnerability. Dispense information and present a thorough explanation of Communication And Network, Database, Failure To Segment Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat Identification And Vulnerability Assessment For Risk Identification
Threat Identification And Vulnerability Assessment For Risk IdentificationThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating Present the topic in a bit more detail with this Threat Identification And Vulnerability Assessment For Risk Identification. Use it as a tool for discussion and navigation on Identification, Vulnerability, Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
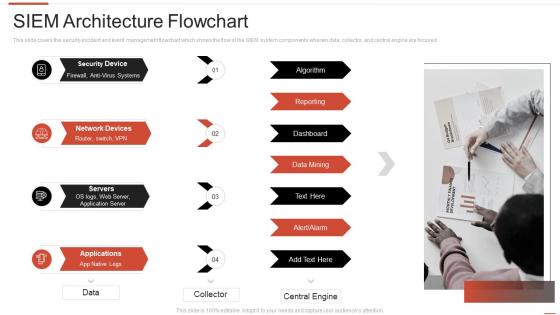 Architecture flowchart automating threat identification
Architecture flowchart automating threat identificationThis slide covers the security incident and event management flowchart which shows the flow of the SIEM system components wherein data, collector, and central engine are focused. Introducing Architecture Flowchart Automating Threat Identification to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Architecture, Flowchart, Servers , using this template. Grab it now to reap its full benefits.
-
 Automating threat identification 30 60 90 days plan
Automating threat identification 30 60 90 days planIncrease audience engagement and knowledge by dispensing information using Automating Threat Identification 30 60 90 Days Plan. This template helps you present information on three stages. You can also present information on 30 60 90 Days Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
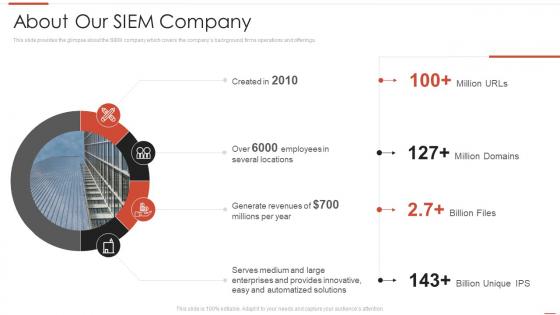 Automating threat identification about our siem company
Automating threat identification about our siem companyThis slide provides the glimpse about the SIEM company which covers the companys background, firms operations and offerings. Present the topic in a bit more detail with this Automating Threat Identification About Our Siem Company. Use it as a tool for discussion and navigation on About Our Siem Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
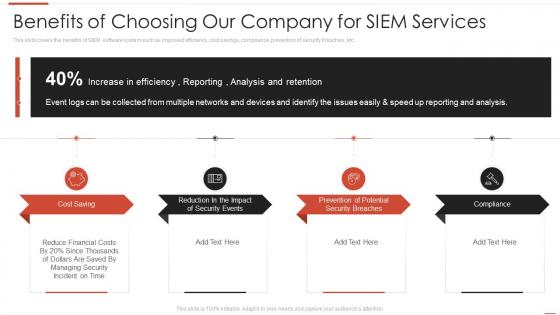 Automating threat identification benefits of choosing our company for siem services
Automating threat identification benefits of choosing our company for siem servicesThis slide covers the benefits of SIEM software system such as improved efficiency, cost savings, compliance, prevention of security breaches, etc. Introducing Automating Threat Identification Benefits Of Choosing Our Company For Siem Services to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Services, Potential, Compliance, using this template. Grab it now to reap its full benefits.
-
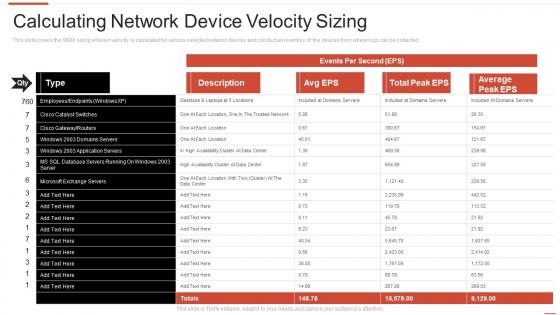 Automating threat identification calculating network device velocity sizing
Automating threat identification calculating network device velocity sizingThis slide covers the SIEM sizing wherein velocity is calculated for various selected network devices and conduct an inventory of the devices from where logs can be collected. Deliver an outstanding presentation on the topic using this Automating Threat Identification Calculating Network Device Velocity Sizing. Dispense information and present a thorough explanation of Calculating Network Device Velocity Sizing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
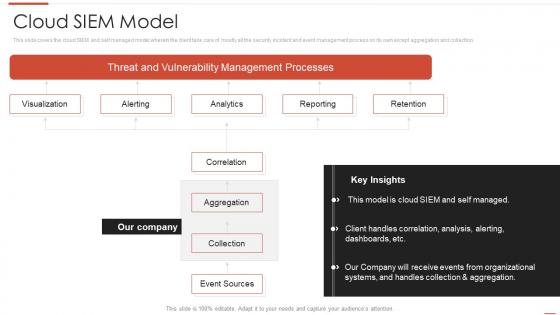 Automating threat identification cloud siem model
Automating threat identification cloud siem modelThis slide covers the cloud SIEM and self managed model wherein the client take care of mostly all the security incident and event management process on its own except aggregation and collection. Present the topic in a bit more detail with this Automating Threat Identification Cloud Siem Model. Use it as a tool for discussion and navigation on Vulnerability, Management, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Automating threat identification companys enhanced features and capabilities
Automating threat identification companys enhanced features and capabilitiesThis slide provides the details about the companys main features and additional features such as threat detection, investigation, security monitoring, normalization, etc. Increase audience engagement and knowledge by dispensing information using Automating Threat Identification Companys Enhanced Features And Capabilities. This template helps you present information on two stages. You can also present information on Threat Detection, Investigation, Time To Respond using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Automating threat identification competitive advantage
Automating threat identification competitive advantageThis slide covers the competitive advantage scoring for security information and event management based on different factors such as value, deployment, ease of use, support, etc. Present the topic in a bit more detail with this Automating Threat Identification Competitive Advantage. Use it as a tool for discussion and navigation on Siem Competitive Advantage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
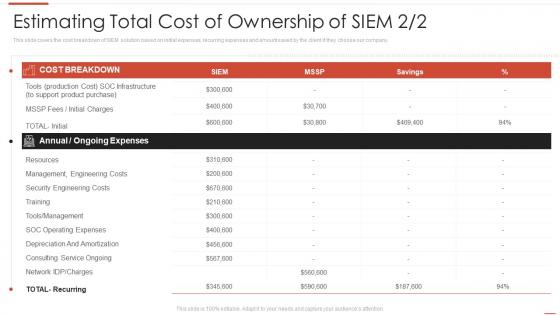 Automating threat identification estimating total cost of ownership of siem
Automating threat identification estimating total cost of ownership of siemThis slide covers the cost breakdown of SIEM solution based on initial expenses, recurring expenses and amount saved by the client if they choose our company. Present the topic in a bit more detail with this Automating Threat Identification Estimating Total Cost Of Ownership Of Siem. Use it as a tool for discussion and navigation on Estimating Total Cost Of Ownership Of SIEM. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
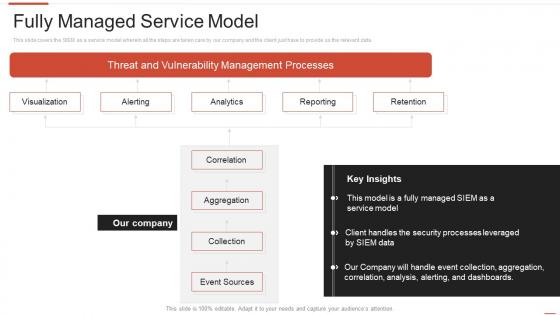 Automating threat identification fully managed service model
Automating threat identification fully managed service modelThis slide covers the SIEM as a service model wherein all the steps are taken care by our company and the client just have to provide us the relevant data. Present the topic in a bit more detail with this Automating Threat Identification Fully Managed Service Model. Use it as a tool for discussion and navigation on Vulnerability, Management, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
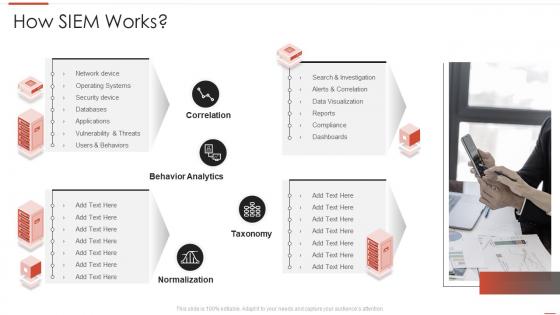 Automating threat identification how siem works
Automating threat identification how siem worksDeliver an outstanding presentation on the topic using this Automating Threat Identification How Siem Works. Dispense information and present a thorough explanation of Behavior Analytics, Taxonomy, Normalization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
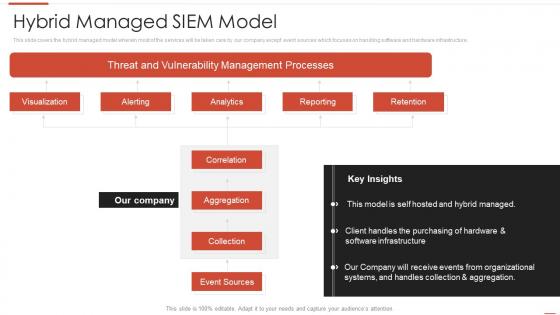 Automating threat identification hybrid managed siem model
Automating threat identification hybrid managed siem modelThis slide covers the hybrid managed model wherein most of the services will be taken care by our company except event sources which focuses on handling software and hardware infrastructure. Present the topic in a bit more detail with this Automating Threat Identification Hybrid Managed Siem Model. Use it as a tool for discussion and navigation on Vulnerability, Management, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Automating threat identification integrations
Automating threat identification integrationsIncrease audience engagement and knowledge by dispensing information using Automating Threat Identification Integrations. This template helps you present information on four stages. You can also present information on Security Events, Network Logs, Applications And Device using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Automating threat identification intelligence services
Automating threat identification intelligence servicesThis slide covers the security intelligence services such as cyber threat intelligence, incident and response management, cyber analytics, vulnerability management, etc. Present the topic in a bit more detail with this Automating Threat Identification Intelligence Services. Use it as a tool for discussion and navigation on Management, Analytics, Infrastructure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Automating threat identification key features of siem software
Automating threat identification key features of siem softwareThis slide provides the details about our companys SIEM key features such as automated reports, log collection and classification, high scalability, security automation, etc. Introducing Automating Threat Identification Key Features Of Siem Softwa to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Comprehensive, Classification, Enrichment, using this template. Grab it now to reap its full benefits.
-
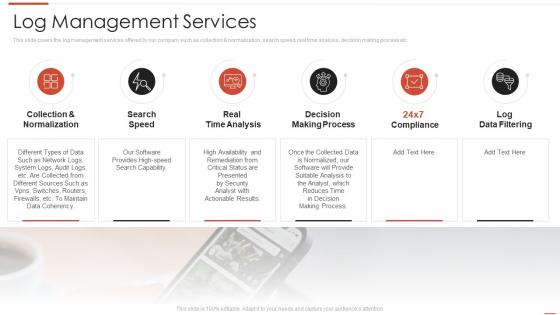 Automating threat identification log management services
Automating threat identification log management servicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Increase audience engagement and knowledge by dispensing information using Automating Threat Identification Log Management Services. This template helps you present information on six stages. You can also present information on Management, Services, Normalization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
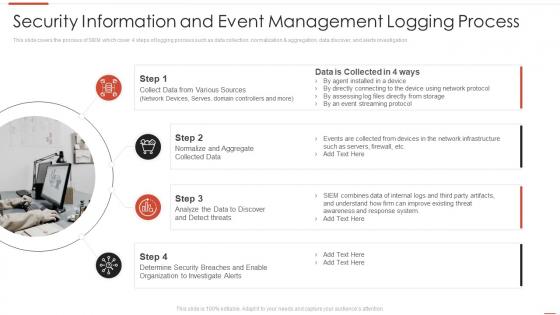 Automating threat identification management logging process
Automating threat identification management logging processThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Automating Threat Identification Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
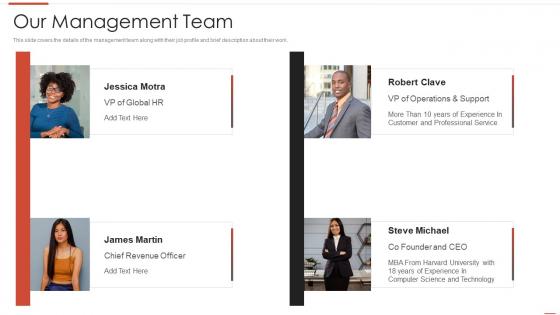 Automating threat identification management team
Automating threat identification management teamThis slide covers the details of the management team along with their job profile and brief description about their work. Increase audience engagement and knowledge by dispensing information using Automating Threat Identification Management Team. This template helps you present information on four stages. You can also present information on Our Management Team using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Automating threat identification need for siem software in your company
Automating threat identification need for siem software in your companyThis slide covers the need for the SIEM software which focuses on detecting incidents, compliance regulations, and incident management Introducing Automating Threat Identification Need For Siem Software In Your Company to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Detecting Incidents, Regulations, Management, using this template. Grab it now to reap its full benefits.
-
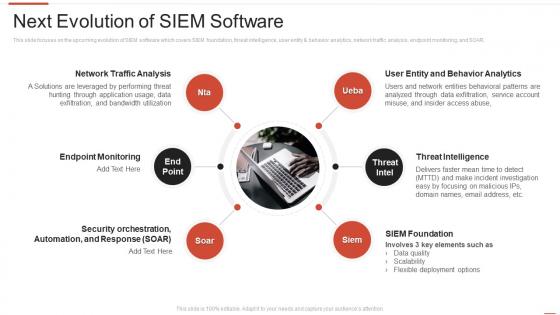 Automating threat identification next evolution of siem software
Automating threat identification next evolution of siem softwareThis slide focuses on the upcoming evolution of SIEM software which covers SIEM foundation, threat intelligence, user entity and behavior analytics, network traffic analysis, endpoint monitoring, and SOAR. Increase audience engagement and knowledge by dispensing information using Automating Threat Identification Next Evolution Of Siem Software. This template helps you present information on six stages. You can also present information on Threat Intelligence, Siem Foundation, Endpoint Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
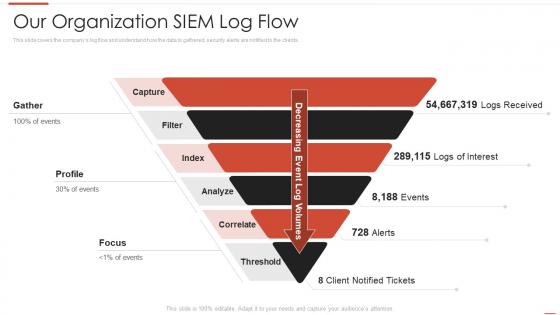 Automating threat identification organization siem log flow
Automating threat identification organization siem log flowThis slide covers the companys log flow and understand how the data is gathered, security alerts are notified to the clients. Introducing Automating Threat Identification Organization Siem Log Flow to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Our Organization Siem Log Flow, using this template. Grab it now to reap its full benefits.
-
 Automating threat identification security information and event management
Automating threat identification security information and event managementIncrease audience engagement and knowledge by dispensing information using Automating Threat Identification Security Information And Event Management. This template helps you present information on four stages. You can also present information on Information, Management, Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
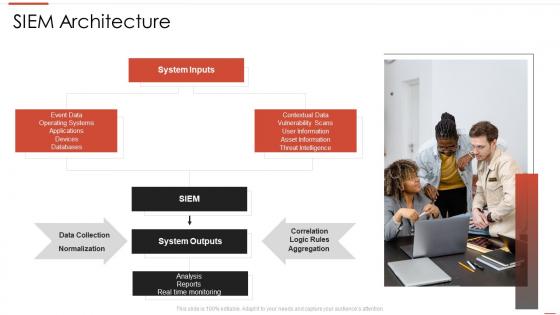 Automating threat identification siem architecture
Automating threat identification siem architecturePresent the topic in a bit more detail with this Automating Threat Identification Siem Architecture. Use it as a tool for discussion and navigation on Siem Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
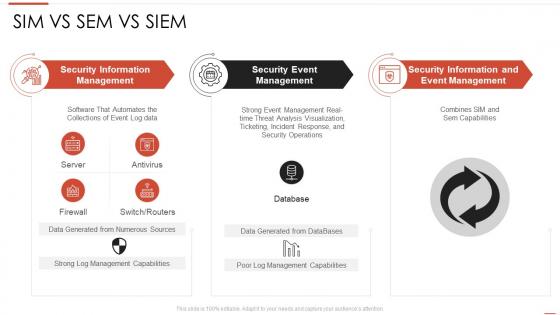 Automating threat identification sim vs sem vs siem
Automating threat identification sim vs sem vs siemDeliver an outstanding presentation on the topic using this Automating Threat Identification Sim Vs Sem Vs Siem. Dispense information and present a thorough explanation of Information, Management, Capabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
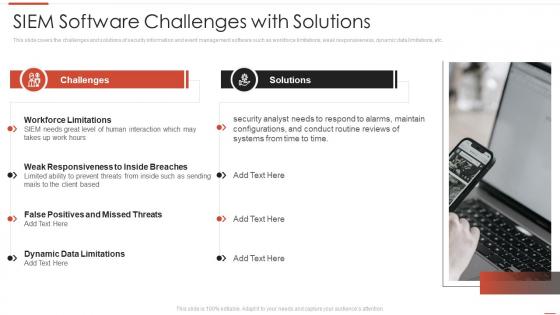 Automating threat identification software challenges with solutions
Automating threat identification software challenges with solutionsThis slide covers the challenges and solutions of security information and event management software such as workforce limitations, weak responsiveness, dynamic data limitations, etc. Present the topic in a bit more detail with this Automating Threat Identification Software Challenges With Solutions. Use it as a tool for discussion and navigation on Software, Challenges, Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Automating threat identification table of contents security information and event management
Automating threat identification table of contents security information and event managementIncrease audience engagement and knowledge by dispensing information using Automating Threat Identification Table Of Contents Security Information And Event Management. This template helps you present information on eleven stages. You can also present information on Company Overview, Management, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Automating threat identification threat intelligence services
Automating threat identification threat intelligence servicesThis slide covers the threat intelligence services such as global intelligence, local intelligence, and other effective threat detection services. Introducing Automating Threat Identification Threat Intelligence Services to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Global Intelligence, Other Services, Local Intelligence, using this template. Grab it now to reap its full benefits.
-
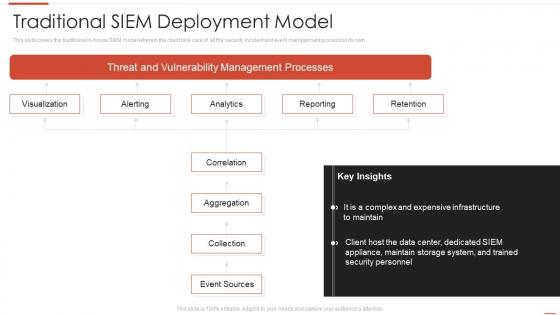 Automating threat identification traditional siem deployment model
Automating threat identification traditional siem deployment modelThis slide covers the traditional in house SIEM model wherein the client take care of all the security incident and event management process on its own. Deliver an outstanding presentation on the topic using this Automating Threat Identification Traditional Siem Deployment Model. Dispense information and present a thorough explanation of Expensive, Infrastructure, Analytics using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
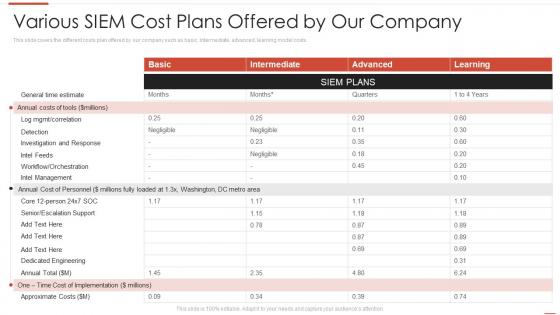 Automating threat identification various siem cost plans offered by our company
Automating threat identification various siem cost plans offered by our companyThis slide covers the different costs plan offered by our company such as basic, intermediate, advanced, learning model costs. Present the topic in a bit more detail with this Automating Threat Identification Various Siem Cost Plans Offered By Our Company. Use it as a tool for discussion and navigation on Various SIEM Cost Plans Offered By Our Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
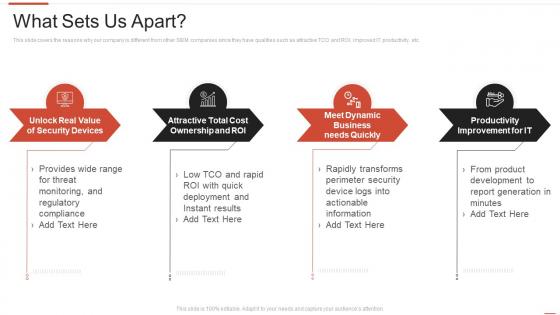 Automating threat identification what sets us apart
Automating threat identification what sets us apartThis slide covers the reasons why our company is different from other SIEM companies since they have qualities such as attractive TCO and ROI, improved IT productivity, etc. Introducing Automating Threat Identification What Sets Us Apart to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Improvement, Productivity, Ownership, using this template. Grab it now to reap its full benefits.
-
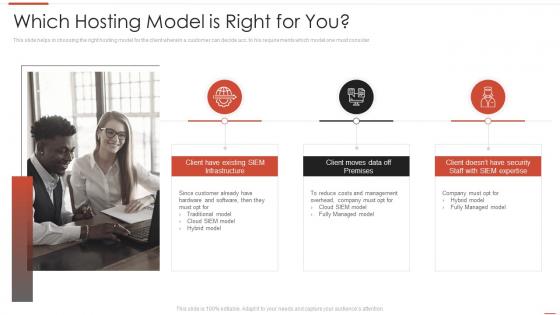 Automating threat identification which hosting model is right for you
Automating threat identification which hosting model is right for youThis slide helps in choosing the right hosting model for the client wherein a customer can decide acc. to his requirements which model one must consider. Increase audience engagement and knowledge by dispensing information using Automating Threat Identification Which Hosting Model Is Right For You. This template helps you present information on three stages. You can also present information on Infrastructure, Premises, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
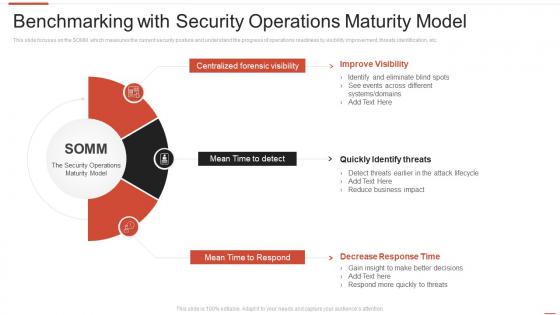 Benchmarking with security operations maturity model automating threat identification
Benchmarking with security operations maturity model automating threat identificationThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Introducing Benchmarking With Security Operations Maturity Model Automating Threat Identification to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Forensic Visibility, Mean Time To Detect, Mean Time To Respond, using this template. Grab it now to reap its full benefits.
-
 Companys mission vision and values automating threat identification
Companys mission vision and values automating threat identificationThis slide provides the details of our company mission, vision and values to provide unique services to the customers. Increase audience engagement and knowledge by dispensing information using Companys Mission Vision And Values Automating Threat Identification. This template helps you present information on three stages. You can also present information on Organization, Collaboration, Values using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
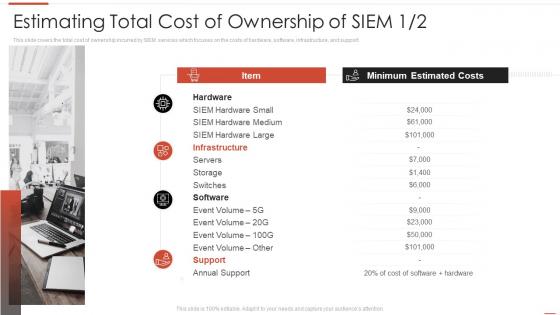 Estimating total cost of ownership of siem automating threat identification
Estimating total cost of ownership of siem automating threat identificationThis slide covers the total cost of ownership incurred by SIEM services which focuses on the costs of hardware, software, infrastructure, and support. Introducing Estimating Total Cost Of Ownership Of Siem Automating Threat Identification to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Estimating Total Cost Of Ownership Of SIEM, using this template. Grab it now to reap its full benefits.
-
 Icons slide for automating threat identification
Icons slide for automating threat identificationIntroducing our well researched set of slides titled Icons Slide For Automating Threat Identification. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
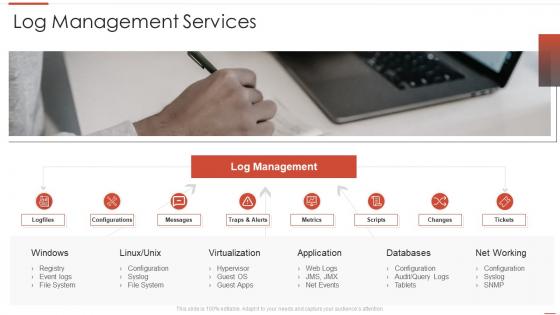 Log management services automating threat identification
Log management services automating threat identificationIntroducing Log Management Services Automating Threat Identification to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Virtualization, Application, Databases, using this template. Grab it now to reap its full benefits.
-
 Need for siem software in your company automating threat identification
Need for siem software in your company automating threat identificationThis slide covers the need for the SIEM software which focuses on detecting incidents, compliance regulations, and incident management Increase audience engagement and knowledge by dispensing information using Need For Siem Software In Your Company Automating Threat Identification. This template helps you present information on four stages. You can also present information on Security Devices, Network Devices, Applications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
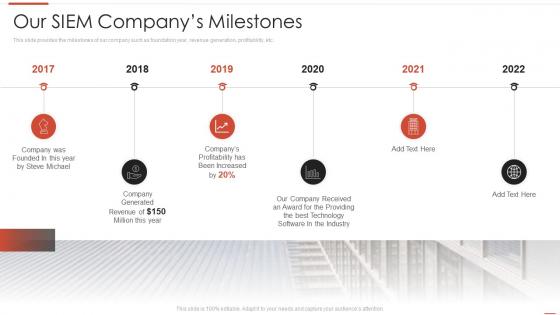 Our siem companys milestones automating threat identification
Our siem companys milestones automating threat identificationThis slide provides the milestones of our company such as foundation year, revenue generation, profitability, etc. Introducing Our Siem Companys Milestones Automating Threat Identification to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Our Siem Companys Milestones, using this template. Grab it now to reap its full benefits.
-
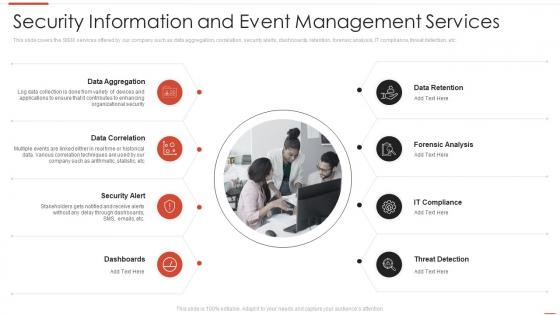 Security information and event management services automating threat identification
Security information and event management services automating threat identificationThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Increase audience engagement and knowledge by dispensing information using Security Information And Event Management Services Automating Threat Identification. This template helps you present information on eight stages. You can also present information on Data Aggregation, Data Correlation, Security Alert using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
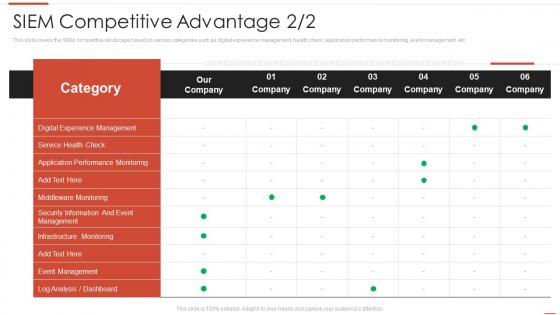 Siem competitive advantage automating threat identification
Siem competitive advantage automating threat identificationThis slide covers the SIEM competitive landscape based on various categories such as digital experience management, health check, application performance monitoring, event management, etc. Deliver an outstanding presentation on the topic using this Siem Competitive Advantage Automating Threat Identification. Dispense information and present a thorough explanation of Siem Competitive Advantage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 What our clients say about us automating threat identification
What our clients say about us automating threat identificationThis slide covers the client testimonials and what our customers have to say about our company and its services to understand the companys market reputation. Present the topic in a bit more detail with this What Our Clients Say About Us Automating Threat Identification. Use it as a tool for discussion and navigation on Procurement, Representative, Interconnect. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan
Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Vulnerability Severity, Threat Source, Risk Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.


