Powerpoint Templates and Google slides for Threat Of Substitutes
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
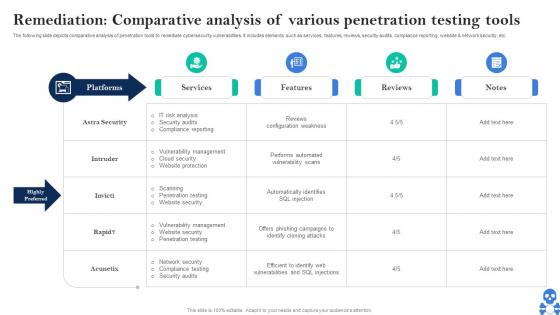 Cyber Threats In Blockchain Remediation Comparative Analysis Of Various Penetration Testing Tools BCT SS V
Cyber Threats In Blockchain Remediation Comparative Analysis Of Various Penetration Testing Tools BCT SS VThe following slide depicts comparative analysis of penetration tools to remediate cybersecurity vulnerabilities. It includes elements such as services, features, reviews, security audits, compliance reporting, website and network security, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Remediation Comparative Analysis Of Various Penetration Testing Tools BCT SS V Dispense information and present a thorough explanation of Services, Features, Reviews using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
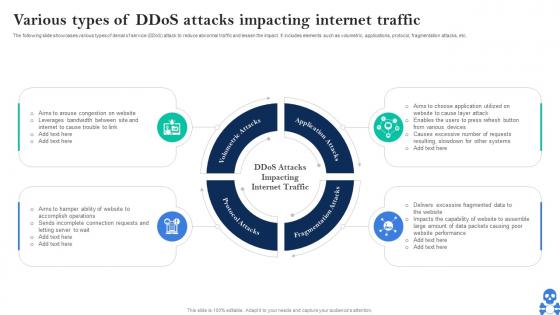 Cyber Threats In Blockchain Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS V
Cyber Threats In Blockchain Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS VThe following slide showcases various types of denial of service DDoS attack to reduce abnormal traffic and lessen the impact. It includes elements such as volumetric, applications, protocol, fragmentation attacks, etc. Introducing Cyber Threats In Blockchain Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Volumetric Attacks, Application Attacks, Fragmentation Attacks using this template. Grab it now to reap its full benefits.
-
 Table Of Contents Cyber Threats In Blockchain World Best Practices BCT SS V
Table Of Contents Cyber Threats In Blockchain World Best Practices BCT SS VIncrease audience engagement and knowledge by dispensing information using Table Of Contents Cyber Threats In Blockchain World Best Practices BCT SS V This template helps you present information on One stages. You can also present information on Industry Overview, Cybersecurity Scams using this PPT design. This layout is completely editable so personaize it now
-
 Table Of Contents For Cyber Threats In Blockchain World Best Practices BCT SS V
Table Of Contents For Cyber Threats In Blockchain World Best Practices BCT SS VIntroducing Table Of Contents For Cyber Threats In Blockchain World Best Practices BCT SS V to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain Cybersecurity, Workflow Model using this template. Grab it now to reap its full benefits.
-
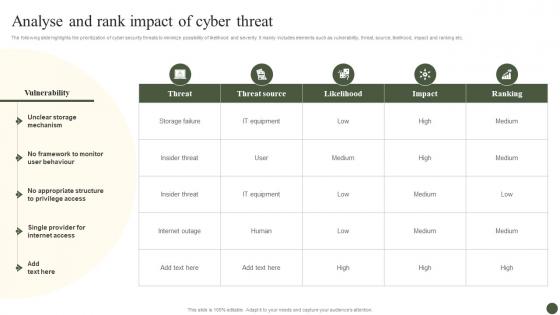 Analyse And Rank Impact Of Cyber Threat Implementing Cyber Risk Management Process
Analyse And Rank Impact Of Cyber Threat Implementing Cyber Risk Management ProcessThe following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Deliver an outstanding presentation on the topic using this Analyse And Rank Impact Of Cyber Threat Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Threat, Threat Source, Likelihood using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Analysis Of Cyber Security Threats In Automotive Industry
Impact Analysis Of Cyber Security Threats In Automotive IndustryThis slide highlights influence assessment cyber security risks in automobile industry. The purpose of this slide is to aid businesses in evaluating potential consequences of digital factors. It includes elements such as data privacy, supply chain disruption, etc. Introducing our premium set of slides with Impact Analysis Of Cyber Security Threats In Automotive Industry Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Privacy, Intellectual Property, Supply Chain Disruption So download instantly and tailor it with your information.
-
 Comparison Of Cybersecurity Apps For Threat Detection
Comparison Of Cybersecurity Apps For Threat DetectionThis slide represents comparison table for cybersecurity applications for online risk mitigation including Wireshark, Metasploit, and Entersoft apps. Introducing our premium set of slides with Comparison Of Cybersecurity Apps For Threat Detection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Protocol Analysis, Security Assessment, Infrastructure Security Analysis. So download instantly and tailor it with your information.
-
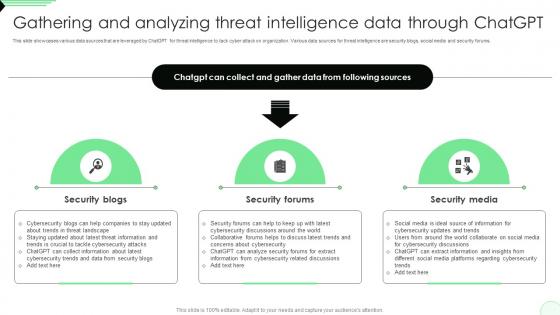 Gathering And Analyzing Threat Intelligence Opportunities And Risks Of ChatGPT AI SS V
Gathering And Analyzing Threat Intelligence Opportunities And Risks Of ChatGPT AI SS VThis slide showcases various data sources that are leveraged by ChatGPT for threat intelligence to tack cyber attack on organization. Various data sources for threat intelligence are security blogs, social media and security forums. Introducing Gathering And Analyzing Threat Intelligence Opportunities And Risks Of ChatGPT AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Blogs, Security Forums, Security Media, using this template. Grab it now to reap its full benefits.
-
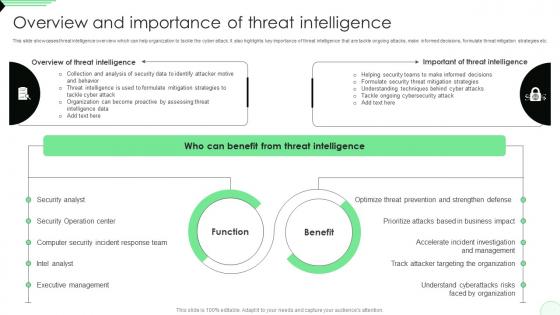 Overview And Importance Of Threat Intelligence Opportunities And Risks Of ChatGPT AI SS V
Overview And Importance Of Threat Intelligence Opportunities And Risks Of ChatGPT AI SS VThis slide showcases threat intelligence overview which can help organization to tackle the cyber attack. It also highlights key importance of threat intelligence that are tackle ongoing attacks, make informed decisions, formulate threat mitigation strategies etc. Present the topic in a bit more detail with this Overview And Importance Of Threat Intelligence Opportunities And Risks Of ChatGPT AI SS V. Use it as a tool for discussion and navigation on Security Operation Center, Security Analyst, Computer Security Incident Response Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
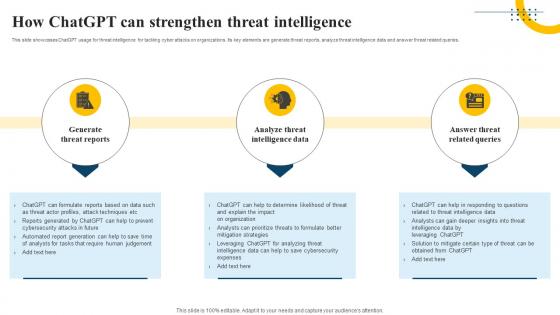 How ChatGPT Can Strengthen Threat Intelligence Impact Of Generative AI SS V
How ChatGPT Can Strengthen Threat Intelligence Impact Of Generative AI SS VThis slide showcases ChatGPT usage for threat intelligence for tackling cyber attacks on organizations. Its key elements are generate threat reports, analyze threat intelligence data and answer threat related queries. Introducing How ChatGPT Can Strengthen Threat Intelligence Impact Of Generative AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Generate Threat Reports, Intelligence Data, Related Queries, using this template. Grab it now to reap its full benefits.
-
 Overview And Importance Of Threat Intelligence Impact Of Generative AI SS V
Overview And Importance Of Threat Intelligence Impact Of Generative AI SS VThis slide showcases threat intelligence overview which can help organization to tackle the cyber attack. It also highlights key importance of threat intelligence that are tackle ongoing attacks, make informed decisions, formulate threat mitigation strategies etc. Introducing Overview And Importance Of Threat Intelligence Impact Of Generative AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Motive And Behavior, Tackle Cyber Attack, Intelligence Data, using this template. Grab it now to reap its full benefits.
-
 Impact Analysis Of Cybersecurity Threats In Retail Industry
Impact Analysis Of Cybersecurity Threats In Retail IndustryThis slide highlights impact assessment of cyber safety concerns in retail sector. The purpose of this template is to aid businesses in assessing potential consequences for protecting against threats with highest impact in timely manner. It includes elements such as payment data breach, supply chain disruption, etc. Introducing our Impact Analysis Of Cybersecurity Threats In Retail Industry set of slides. The topics discussed in these slides are Payment Data Breach, Supply Chain, Customer Data Compromise This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Management of aggression in workplace ppt presentation slides
Management of aggression in workplace ppt presentation slidesPresenting management of aggression in workplace ppt presentation slides. This is a management of aggression in workplace ppt presentation slides. This is a three stage process. The stages in this process are root causes, aggression, issues.
-
 Management of aggression in workplace powerpoint slide show
Management of aggression in workplace powerpoint slide showPresenting management of aggression in workplace powerpoint slide show. This is a management of aggression in workplace powerpoint slide show. This is a three stage process. The stages in this process are root causes, aggression, issues.
-
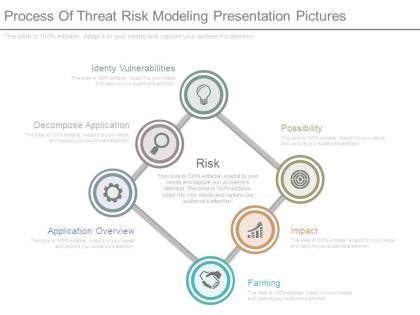 Process of threat risk modeling presentation pictures
Process of threat risk modeling presentation picturesPresenting process of threat risk modeling presentation pictures. This is a process of threat risk modeling presentation pictures. This is a six stage process. The stages in this process are identify vulnerabilities, decompose application, risk, application overview, possibility, impact, farming.
-
 Threat of substitution diagram ppt slides examples
Threat of substitution diagram ppt slides examplesPresenting threat of substitution diagram ppt slides examples. This is a threat of substitution diagram ppt slides examples. This is five stage process. The stages in this process are resource nationalism, threat of substitute, combine, adapt, eliminate.
-
 Process of threat risk modeling diagram powerpoint images
Process of threat risk modeling diagram powerpoint imagesPresenting process of threat risk modeling diagram powerpoint images. This is a process of threat risk modeling diagram powerpoint images. This is a five stage process. The stages in this process are risk, impact, degree of mitigating, exploitability, damage potential, possibility, identify vulnerabilities, application overview, identify threats, decompose application.
-
 Threat of new competitors powerpoint ideas
Threat of new competitors powerpoint ideasPresenting threat of new competitors powerpoint ideas. This is a threat of new competitors powerpoint ideas. This is a four stage process. The stages in this process are threat of new competitors, existing competitive rivalry, threat of substitution, supplier power.
-
 Threat of new competitors powerpoint presentation
Threat of new competitors powerpoint presentationPresenting threat of new competitors powerpoint presentation. This is a threat of new competitors powerpoint presentation. This is a four stage process. The stages in this process are supplier power, threat of new competitors, existing competitive rivalry, threat of substitution.
-
 Threat profiling sample of ppt presentation
Threat profiling sample of ppt presentationPresenting threat profiling sample of ppt presentation. This is a threat profiling sample of ppt presentation. This is a four stage process. The stages in this process are threat name, related incident, threat alias, threat type.
-
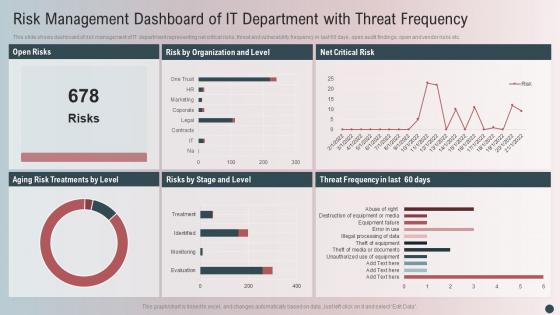 Risk Management Dashboard Of It Department With Threat Frequency
Risk Management Dashboard Of It Department With Threat FrequencyThis slide shows dashboard of risk management of IT department representing net critical risks, threat and vulnerability frequency in last 60 days, open audit findings, open and vendor risks etc. Presenting our well-structured Risk Management Dashboard Of It Department With Threat Frequency. The topics discussed in this slide are Open Risks, Risk Organization Level, Net Critical Risk. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Impact Of Insider Threat On Business Operations
Impact Of Insider Threat On Business OperationsThis slide shows impact of insider threat on business operations. It contains information about operational disruption, damaging brand image, loss of sensitive information, market value, etc. Introducing our Impact Of Insider Threat On Business Operations set of slides. The topics discussed in these slides are Operational Disruption, Brand Damage, Loss Critical Data. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
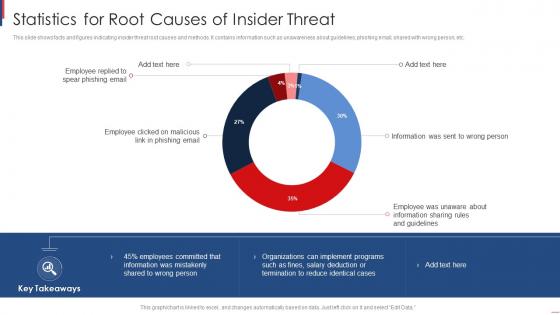 Statistics For Root Causes Of Insider Threat
Statistics For Root Causes Of Insider ThreatThis slide shows facts and figures indicating insider threat root causes and methods. It contains information such as unawareness about guidelines, phishing email, shared with wrong person, etc. Introducing our Statistics For Root Causes Of Insider Threat set of slides. The topics discussed in these slides are Statistics Root, Causes Insider Threat. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
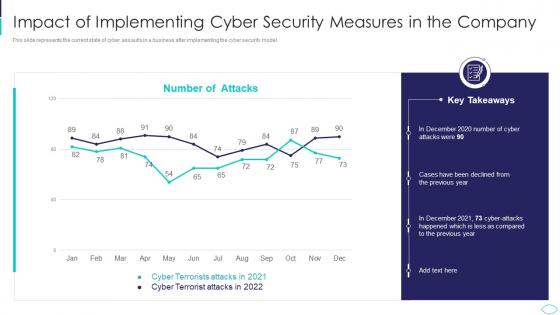 Cyber Terrorism Attacks Impact Of Implementing Cyber Security
Cyber Terrorism Attacks Impact Of Implementing Cyber SecurityThis slide represents the current state of cyber assaults in a business after implementing the cyber security model. Deliver an outstanding presentation on the topic using this Cyber Terrorism Attacks Impact Of Implementing Cyber Security. Dispense information and present a thorough explanation of Impact Of Implementing Cyber Security Measures In The Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
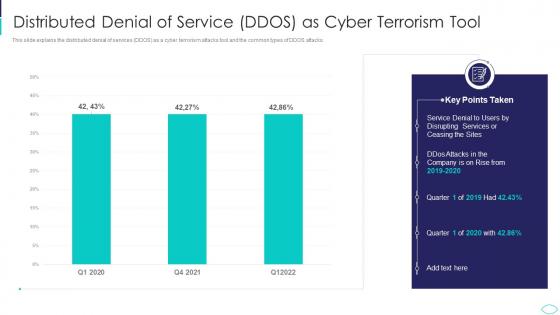 Distributed Denial Of Service DDOS Cyber Terrorism Attacks
Distributed Denial Of Service DDOS Cyber Terrorism AttacksThis slide explains the distributed denial of services DDOS as a cyber terrorism attacks tool and the common types of DDOS attacks. Present the topic in a bit more detail with this Distributed Denial Of Service DDOS Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Distributed Denial Of Service Ddos As Cyber Terrorism Tool. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
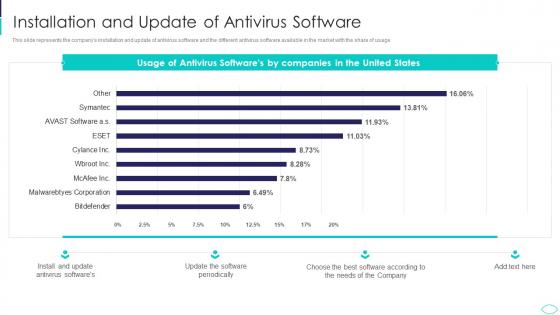 Installation And Update Of Antivirus Software Cyber Terrorism Attacks
Installation And Update Of Antivirus Software Cyber Terrorism AttacksThis slide represents the companys installation and update of antivirus software and the different antivirus software available in the market with the share of usage. Deliver an outstanding presentation on the topic using this Installation And Update Of Antivirus Software Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Installation And Update Of Antivirus Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
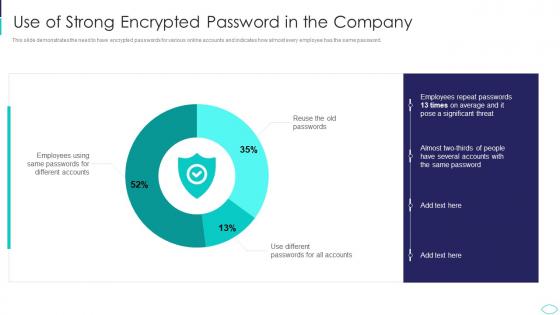 Use Of Strong Encrypted Password In The Company Cyber Terrorism Attacks
Use Of Strong Encrypted Password In The Company Cyber Terrorism AttacksThis slide demonstrates the need to have encrypted passwords for various online accounts and indicates how almost every employee has the same password. Present the topic in a bit more detail with this Use Of Strong Encrypted Password In The Company Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Use Of Strong Encrypted Password In The Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
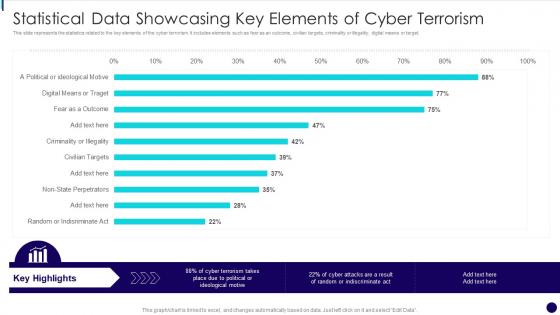 Statistical Data Showcasing Key Elements Of Cyber Terrorism
Statistical Data Showcasing Key Elements Of Cyber TerrorismThis slide represents the statistics related to the key elements of the cyber terrorism. It includes elements such as fear as an outcome, civilian targets, criminality or illegality, digital means or target. Presenting our well structured Statistical Data Showcasing Key Elements Of Cyber Terrorism. The topics discussed in this slide are Statistical Data Showcasing Key Elements Of Cyber Terrorism. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
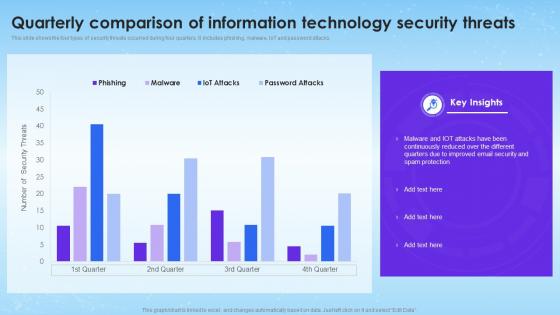 Quarterly Comparison Of Information Technology Security Threats
Quarterly Comparison Of Information Technology Security ThreatsThis slide shows the four types of security threats occurred during four quarters. It includes phishing, malware, IoT and password attacks. Introducing our Quarterly Comparison Of Information Technology Security Threats set of slides. The topics discussed in these slides are Quarterly Comparison, Information Technology, Security Threats. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
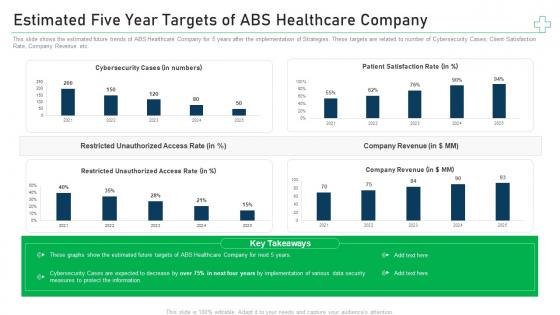 Estimated five year targets of company minimize cybersecurity threats in healthcare company
Estimated five year targets of company minimize cybersecurity threats in healthcare companyThis slide shows the estimated future trends of ABS Healthcare Company for 5 years after the implementation of Strategies. These targets are related to number of Cybersecurity Cases, Client Satisfaction Rate, Company Revenue etc. Present the topic in a bit more detail with this Estimated Five Year Targets Of Company Minimize Cybersecurity Threats In Healthcare Company. Use it as a tool for discussion and navigation on Cybersecurity Cases, Patient Satisfaction Rate, Company Revenue. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
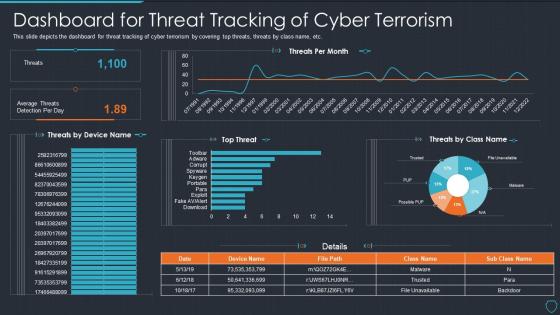 Cyberterrorism it dashboard for threat tracking of cyber terrorism
Cyberterrorism it dashboard for threat tracking of cyber terrorismThis slide depicts the dashboard for threat tracking of cyber terrorism by covering top threats, threats by class name, etc. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Dashboard For Threat Tracking Of Cyber Terrorism. Dispense information and present a thorough explanation of Threats Per Month, Top Threat, Average Threats Detection Per Day using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
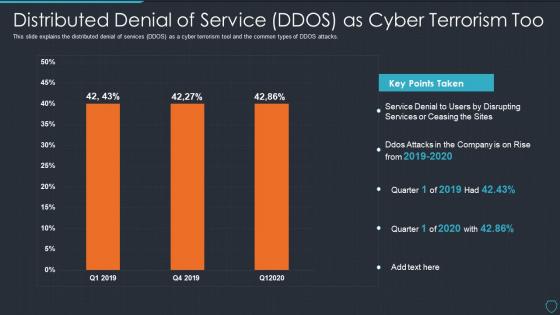 Cyberterrorism it distributed denial of service ddos as cyber terrorism too
Cyberterrorism it distributed denial of service ddos as cyber terrorism tooThis slide explains the distributed denial of services DDOS as a cyber terrorism tool and the common types of DDOS attacks. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Distributed Denial Of Service DDOS As Cyber Terrorism Too. Dispense information and present a thorough explanation of Service Denial, Disrupting Services, Ceasing Sites, 2019 To 2020 using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
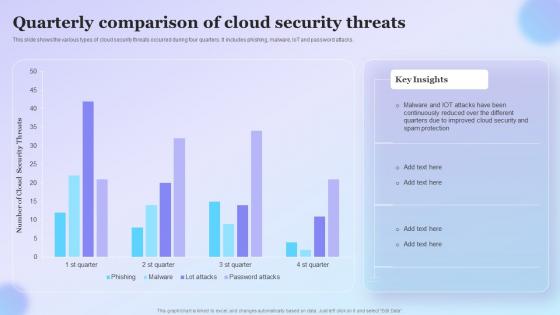 Quarterly Comparison Of Cloud Security Threats
Quarterly Comparison Of Cloud Security ThreatsThis slide shows the various types of cloud security threats occurred during four quarters. It includes phishing, malware, IoT and password attacks. Presenting our well structured Quarterly Comparison Of Cloud Security Threats. The topics discussed in this slide are Quarterly, Comparison Of Cloud Security, Threats. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
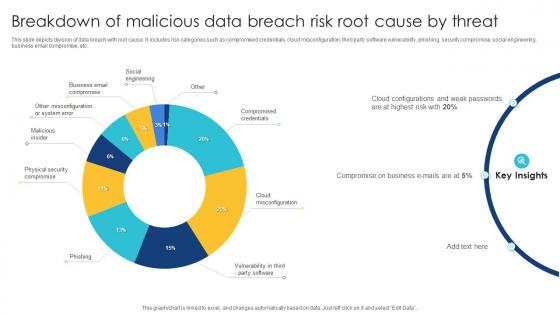 Breakdown Of Malicious Data Breach Risk Root Cause By Threat
Breakdown Of Malicious Data Breach Risk Root Cause By ThreatThis slide depicts division of data breach with root cause. It includes risk categories such as compromised credentials, cloud misconfiguration, third party software vulnerability, phishing, security compromise, social engineering, business email compromise, etc. Introducing our Breakdown Of Malicious Data Breach Risk Root Cause By Threat set of slides. The topics discussed in these slides are Social Engineering, Business Email Compromise, Malicious Insider. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
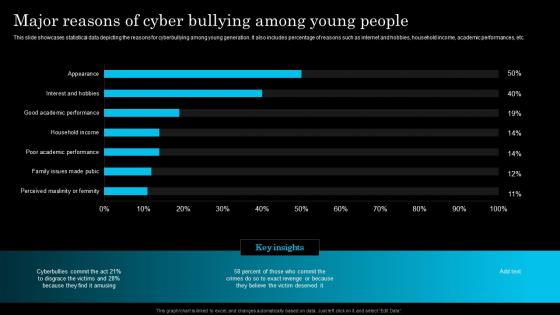 Major Reasons Of Cyber Bullying Among Young People
Major Reasons Of Cyber Bullying Among Young PeopleThis slide showcases statistical data depicting the harmful impact of cyberbullying on individuals. It also includes proportion depicting various impacts such as social anxiety, suicidal thoughts, eating disorder, etc. Introducing our Major Reasons Of Cyber Bullying Among Young People set of slides. The topics discussed in these slides are Percent, Online, Target. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
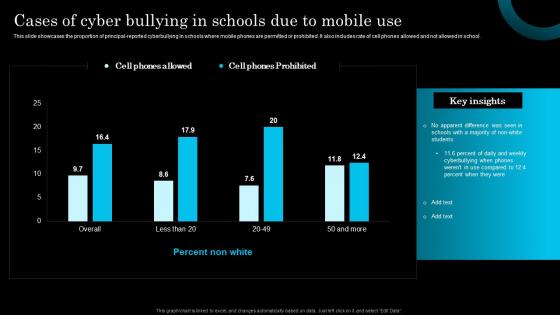 Cases Of Cyber Bullying In Schools Due To Mobile Use
Cases Of Cyber Bullying In Schools Due To Mobile UseThis slide showcases the proportion of principal reported cyberbullying in schools where mobile phones are permitted or prohibited. It also includes rate of cell phones allowed and not allowed in school .Introducing our Cases Of Cyber Bullying In Schools Due To Mobile Use set of slides. The topics discussed in these slides are Apparent, Difference, Cyberbullying. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
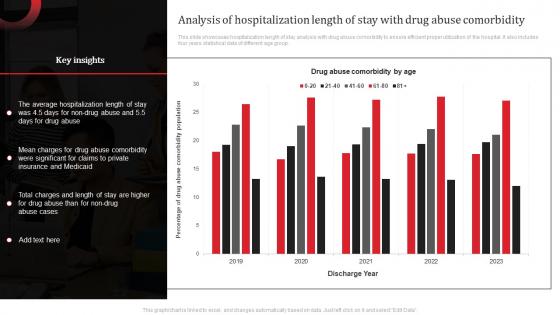 Analysis Of Hospitalization Length Of Stay With Drug Abuse Comorbidity
Analysis Of Hospitalization Length Of Stay With Drug Abuse ComorbidityThis slide showcases hospitalization length of stay analysis with drug abuse comorbidity to ensure efficient proper utilization of the hospital. It also includes four years statistical data of different age group . Introducing our Analysis Of Hospitalization Length Of Stay With Drug Abuse Comorbidity set of slides. The topics discussed in these slides are Medicaid, Comorbidity, Insurance. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
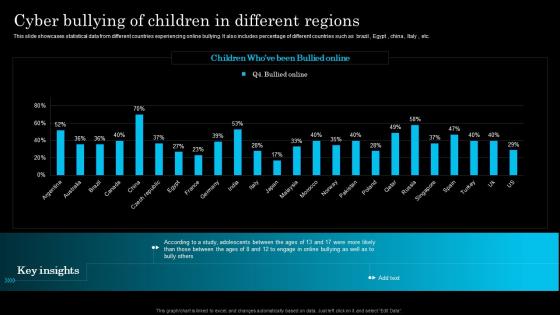 Cyber Bullying Of Children In Different Regions
Cyber Bullying Of Children In Different RegionsThis slide showcases statistical data from different countries experiencing online bullying. It also includes percentage of different countries such as brazil, Egypt, china, Italy, etc. Introducing our Cyber Bullying Of Children In Different Regions set of slides. The topics discussed in these slides are Adolescents, Between, Bullying. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
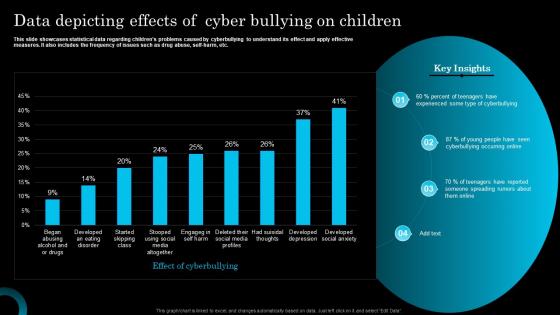 Data Depicting Effects Of Cyber Bullying On Children
Data Depicting Effects Of Cyber Bullying On ChildrenThis slide showcases statistical data regarding childrens problems caused by cyberbullying to understand its effect and apply effective measures. It also includes the frequency of issues such as drug abuse, self harm, etc. Introducing our Data Depicting Effects Of Cyber Bullying On Children set of slides. The topics discussed in these slides are Experienced, Cyberbullying, Spreading. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
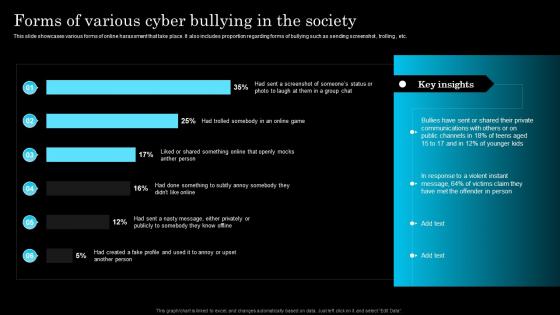 Forms Of Various Cyber Bullying In The Society
Forms Of Various Cyber Bullying In The SocietyThis slide showcases various forms of online harassment that take place. It also includes proportion regarding forms of bullying such as sending screenshot, trolling , etc. Introducing our Forms Of Various Cyber Bullying In The Society set of slides. The topics discussed in these slides are Bullies, Communications, Response. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
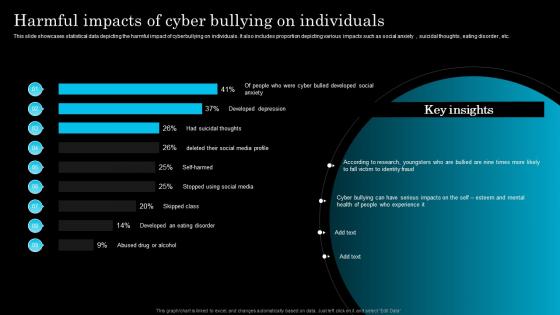 Harmful Impacts Of Cyber Bullying On Individuals
Harmful Impacts Of Cyber Bullying On IndividualsThis slide showcases statistical data depicting the harmful impact of cyberbullying on individuals. It also includes proportion depicting various impacts such as social anxiety, suicidal thoughts, eating disorder, etc. Introducing our Harmful Impacts Of Cyber Bullying On Individuals set of slides. The topics discussed in these slides are According, Cyber, Esteem. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
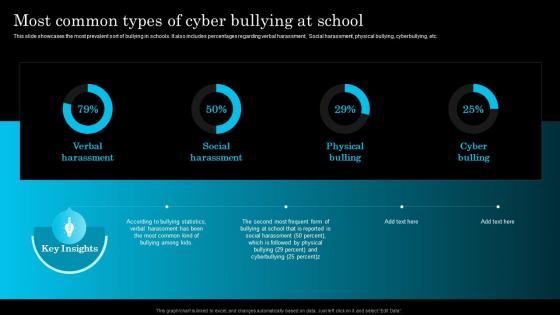 Most Common Types Of Cyber Bullying At School
Most Common Types Of Cyber Bullying At SchoolThis slide showcases the most prevalent sort of bullying in schools. It also includes percentages regarding verbal harassment, Social harassment, physical bullying, cyberbullying, etc. Introducing our Most Common Types Of Cyber Bullying At School set of slides. The topics discussed in these slides are According, Frequent, Harassment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
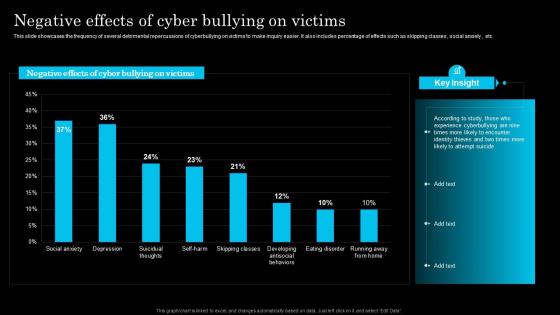 Negative Effects Of Cyber Bullying On Victims
Negative Effects Of Cyber Bullying On VictimsThis slide showcases the frequency of several detrimental repercussions of cyberbullying on victims to make inquiry easier. It also includes percentage of effects such as skipping classes, social anxiety, etc. Presenting our well structured Negative Effects Of Cyber Bullying On Victims. The topics discussed in this slide are According, Encounter, Attempt. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
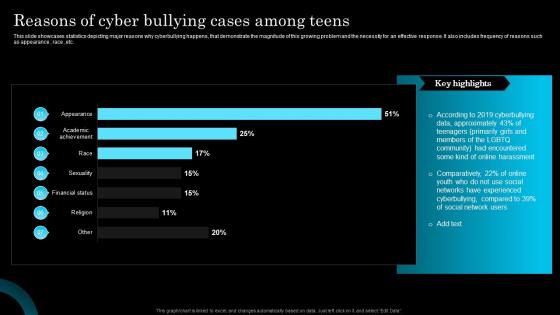 Reasons Of Cyber Bullying Cases Among Teens
Reasons Of Cyber Bullying Cases Among TeensThis slide showcases statistics depicting major reasons why cyberbullying happens, that demonstrate the magnitude of this growing problem and the necessity for an effective response. It also includes frequency of reasons such as appearance, race ,etc. Presenting our well structured Reasons Of Cyber Bullying Cases Among Teens. The topics discussed in this slide are Cyberbullying, Approximately, Members. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
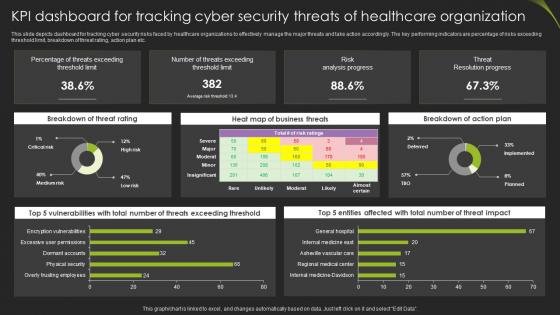 Kpi Dashboard For Tracking Cyber Security Threats Of Healthcare Organization
Kpi Dashboard For Tracking Cyber Security Threats Of Healthcare OrganizationThis slide depicts dashboard for tracking cyber security risks faced by healthcare organizations to effectively manage the major threats and take action accordingly. The key performing indicators are percentage of risks exceeding threshold limit, breakdown of threat rating, action plan etc. Introducing our Kpi Dashboard For Tracking Cyber Security Threats Of Healthcare Organization set of slides. The topics discussed in these slides are Breakdown Of Threat, Business Threats. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
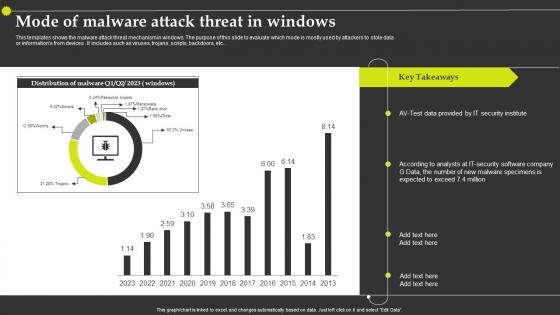 Mode Of Malware Attack Threat In Windows
Mode Of Malware Attack Threat In WindowsThis templates shows the malware attack threat mechanism in windows. The purpose of this slide to evaluate which mode is mostly used by attackers to stole data or informations from devices . It includes such as viruses, trojans, scripts, backdoors, etc.Introducing our Mode Of Malware Attack Threat In Windows set of slides. The topics discussed in these slides are Security Institute, Malware Specimens, Security Software Company. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
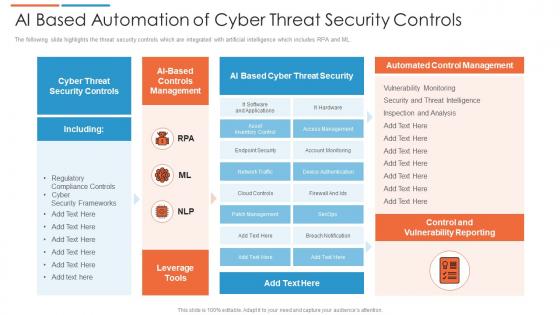 Ai based automation of cyber threat security controls
Ai based automation of cyber threat security controlsThe following slide highlights the threat security controls which are integrated with artificial intelligence which includes RPA and ML. Introducing our AI Based Automation Of Cyber Threat Security Controls set of slides. The topics discussed in these slides are Cyber Threat Security, Automated Control Management, Control And Vulnerability Reporting. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
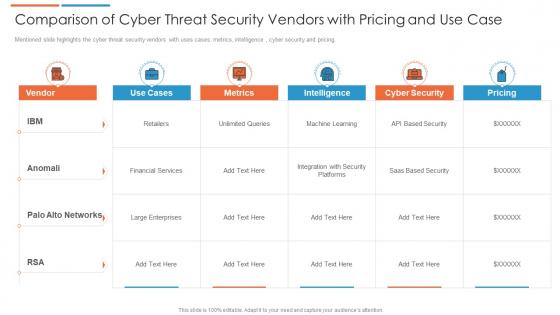 Comparison of cyber threat security vendors with pricing and use case
Comparison of cyber threat security vendors with pricing and use caseMentioned slide highlights the cyber threat security vendors with uses cases, metrics, intelligence , cyber security and pricing. Presenting our well structured Comparison Of Cyber Threat Security Vendors With Pricing And Use Case. The topics discussed in this slide are Financial Services, Cyber Security, Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
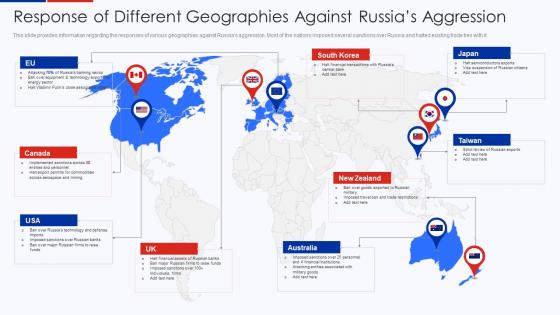 Response Of Different Geographies Against Russias Aggression Ukraine Vs Russia Analyzing Conflict
Response Of Different Geographies Against Russias Aggression Ukraine Vs Russia Analyzing ConflictThis slide provides information regarding the responses of various geographies against Russias aggression. Most of the nations imposed several sanctions over Russia and halted existing trade ties with it.Introducing Response Of Different Geographies Against Russias Aggression Ukraine Vs Russia Analyzing Conflict to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Semiconductors Exports, Suspension Of Russian, Imposed Sanctions using this template. Grab it now to reap its full benefits.
-
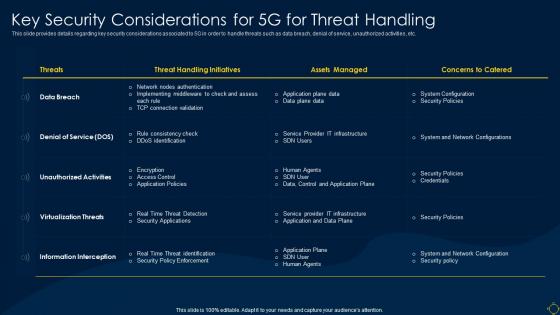 Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System
Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless SystemThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System. Use it as a tool for discussion and navigation on Considerations, Service, Unauthorized. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
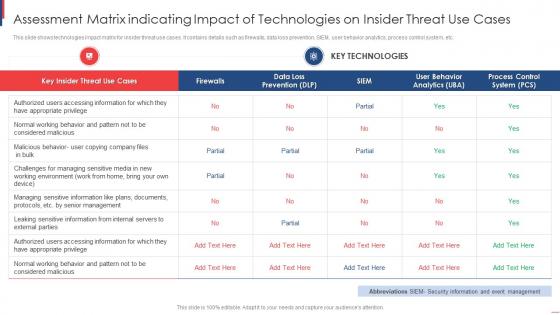 Assessment Matrix Indicating Impact Of Technologies On Insider Threat Use Cases
Assessment Matrix Indicating Impact Of Technologies On Insider Threat Use CasesThis slide shows technologies impact matrix for insider threat use cases. It contains details such as firewalls, data loss prevention, SIEM, user behavior analytics, process control system, etc. Introducing our Assessment Matrix Indicating Impact Of Technologies On Insider Threat Use Cases set of slides. The topics discussed in these slides are Assessment Matrix, Indicating Impact, Technologies On Insider, Threat Use Cases. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
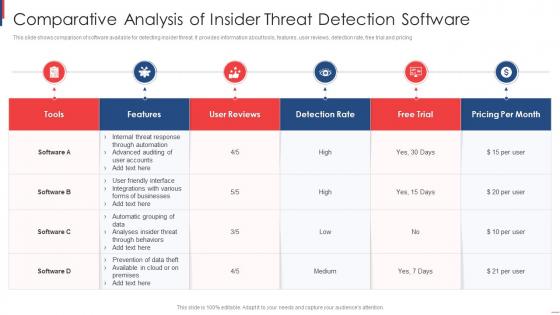 Comparative Analysis Of Insider Threat Detection Software
Comparative Analysis Of Insider Threat Detection SoftwareThis slide shows comparison of software available for detecting insider threat. It provides information about tools, features, user reviews, detection rate, free trial and pricing Introducing our Comparative Analysis Of Insider Threat Detection Software set of slides. The topics discussed in these slides are Comparative Analysis, Insider, Threat Detection Software. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
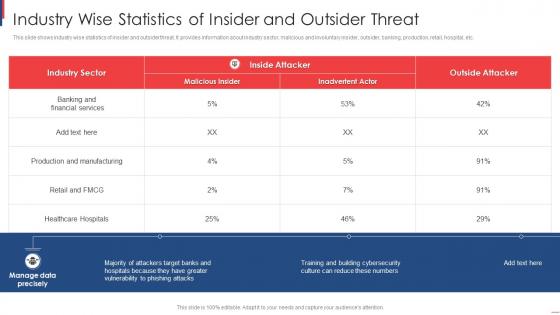 Industry Wise Statistics Of Insider And Outsider Threat
Industry Wise Statistics Of Insider And Outsider ThreatThis slide shows industry wise statistics of insider and outsider threat. It provides information about industry sector, malicious and involuntary insider, outsider, banking, production, retail, hospital, etc. Presenting our well-structured Industry Wise Statistics Of Insider And Outsider Threat. The topics discussed in this slide are Industry Wise Statistics, Insider, Outsider Threat. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
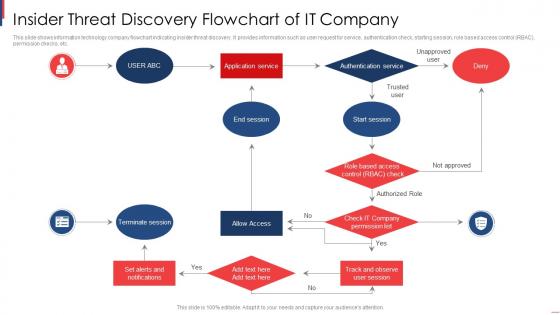 Insider Threat Discovery Flowchart Of It Company
Insider Threat Discovery Flowchart Of It CompanyThis slide shows information technology company flowchart indicating insider threat discovery. It provides information such as user request for service, authentication check, starting session, role based access control RBAC, permission checks, etc. Presenting our set of slides with name Insider Threat Discovery Flowchart Of It Company. This exhibits information on one stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Application Service, End Session, Start Session, Allow Access, Terminate Session.
-
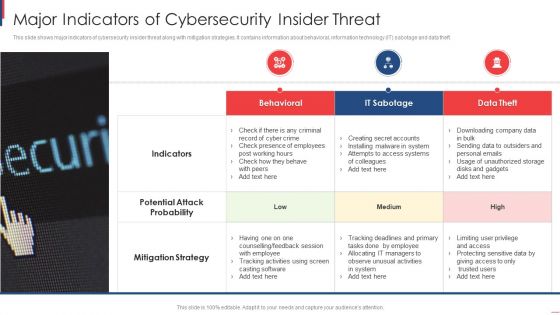 Major Indicators Of Cybersecurity Insider Threat
Major Indicators Of Cybersecurity Insider ThreatThis slide shows major indicators of cybersecurity insider threat along with mitigation strategies. It contains information about behavioral, information technology IT sabotage and data theft. Introducing our premium set of slides with Major Indicators Of Cybersecurity Insider Threat. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Indicators, Potential Attack Probability, Mitigation Strategy. So download instantly and tailor it with your information.
-
 Role Of Insider Threat Management Technologies In Banking Industry
Role Of Insider Threat Management Technologies In Banking IndustryThis slide shows role of insider threat management technologies in banking industry. It provides information about identifying user risk, protecting from data loss and accelerating threat response. Introducing our premium set of slides with Role Of Insider Threat Management Technologies In Banking Industry. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identifying User Risk, Accelerating Threat Response, Protecting Data Loss. So download instantly and tailor it with your information.
-
 Distributed Denial Of Service With Cyber Threat Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Distributed Denial Of Service With Cyber Threat Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Distributed denial of service with cyber threat colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Distributed Denial Of Service With Cyber Threat Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Distributed Denial Of Service With Cyber Threat Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Distributed denial of service with cyber threat monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
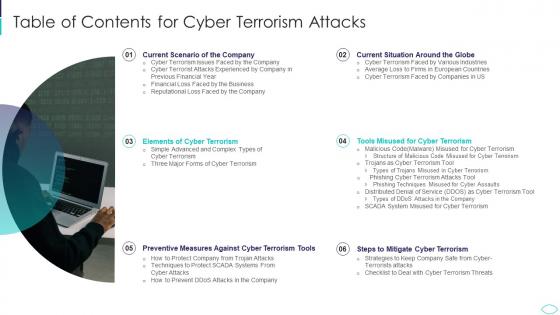 A56 Table Of Contents For Cyber Terrorism Attacks Ppt Slides Guidelines
A56 Table Of Contents For Cyber Terrorism Attacks Ppt Slides GuidelinesIntroducing A56 Table Of Contents For Cyber Terrorism Attacks Ppt Slides Guidelines to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Current Situation, Mitigate, Terrorism Tools, Cyber Terrorism, using this template. Grab it now to reap its full benefits.
-
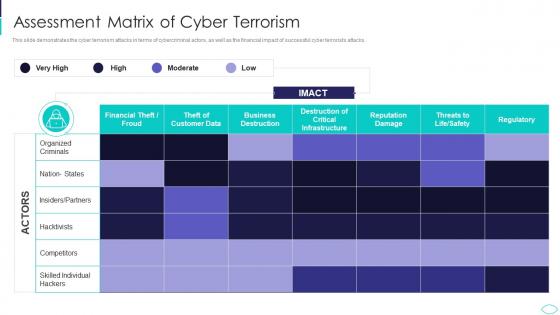 Cyber Terrorism Attacks Assessment Matrix Of Cyber Terrorism
Cyber Terrorism Attacks Assessment Matrix Of Cyber TerrorismThis slide demonstrates the cyber terrorism attacks in terms of cybercriminal actors, as well as the financial impact of successful cyber terrorists attacks. Deliver an outstanding presentation on the topic using this Cyber Terrorism Attacks Assessment Matrix Of Cyber Terrorism. Dispense information and present a thorough explanation of Assessment Matrix Of Cyber Terrorism using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



