Powerpoint Templates and Google slides for Threat Of Substitutes
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
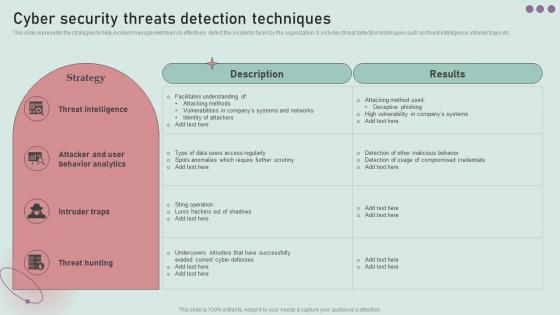 Cyber Security Threats Detection Techniques Development And Implementation Of Security Incident Management
Cyber Security Threats Detection Techniques Development And Implementation Of Security Incident ManagementThis slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc. Present the topic in a bit more detail with this Cyber Security Threats Detection Techniques Development And Implementation Of Security Incident Management. Use it as a tool for discussion and navigation on Intruder Traps, Attacker And User Behavior Analytics, Threat Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Management Capabilities Managing It Threats At Workplace Overview Technological Assessment Of Firm Current
Management Capabilities Managing It Threats At Workplace Overview Technological Assessment Of Firm CurrentThis slide provides details regarding present management capabilities assessment based on several parameters such as incidents and service requests handling rate, service failure rate, customer satisfaction score, etc. Present the topic in a bit more detail with this Management Capabilities Managing It Threats At Workplace Overview Technological Assessment Of Firm Current. Use it as a tool for discussion and navigation on Management, Capabilities, Technological. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Managing It Threats At Workplace Overview
Table Of Contents Managing It Threats At Workplace OverviewIntroducing Table Of Contents Managing It Threats At Workplace Overview to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Threat, Leveraging, Budget, using this template. Grab it now to reap its full benefits.
-
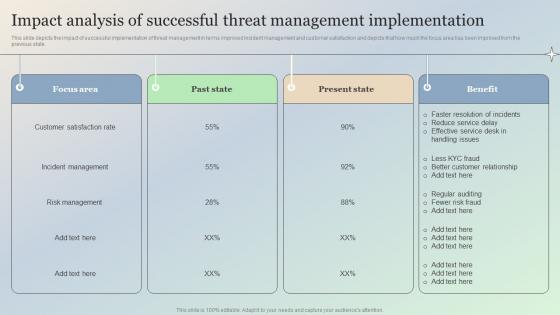 Impact Analysis Of Successful Threat Management Implementation Managing IT Threats At Workplace Overview
Impact Analysis Of Successful Threat Management Implementation Managing IT Threats At Workplace OverviewThis slide depicts the impact of successful implementation of threat management in terms improved incident management and customer satisfaction and depicts that how much the focus area has been improved from the previous state. Introducing Impact Analysis Of Successful Threat Management Implementation Managing IT Threats At Workplace Overview to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management, Incident, Satisfaction, using this template. Grab it now to reap its full benefits.
-
 Major Types Of E Banking Security Threats Digital Banking System To Optimize Financial
Major Types Of E Banking Security Threats Digital Banking System To Optimize FinancialThis slide represents types of e banking security threats. It includes brute force, phishing, pharming, cross site scripting and trojan horse. Present the topic in a bit more detail with this Major Types Of E Banking Security Threats Digital Banking System To Optimize Financial. Use it as a tool for discussion and navigation on Phishing, Pharming, Security Threats, Software For Protection . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Various Types Of Workplace Violence And Threats Handling Pivotal Assets Associated With Firm
Various Types Of Workplace Violence And Threats Handling Pivotal Assets Associated With FirmThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Increase audience engagement and knowledge by dispensing information using Various Types Of Workplace Violence And Threats Handling Pivotal Assets Associated With Firm. This template helps you present information on six stages. You can also present information on Harassment Or Intimidation, Property Damage, Physical Assault using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
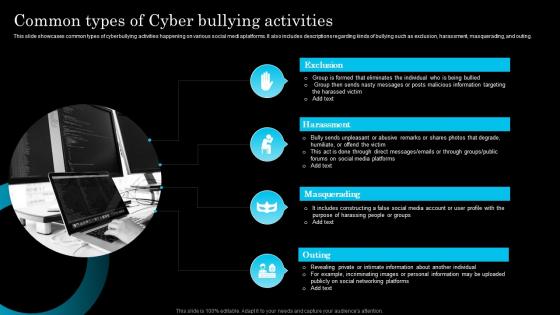 Common Types Of Cyber Bullying Activities
Common Types Of Cyber Bullying ActivitiesThis slide showcases common types of cyberbullying activities happening on various social media platforms. It also includes descriptions regarding kinds of bullying such as exclusion, harassment, masquerading, and outing. Presenting our set of slides with Common Types Of Cyber Bullying Activities. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Exclusion, Harassment, Masquerading.
-
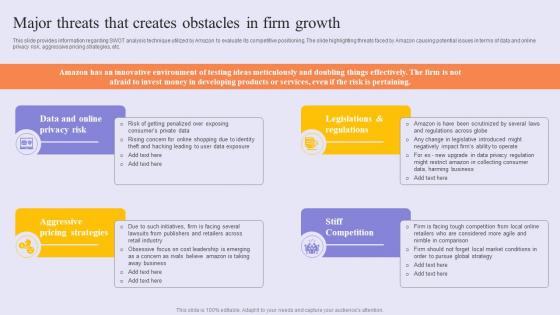 Major Threats That Creates Success Story Of Amazon To Emerge As Pioneer Strategy SS V
Major Threats That Creates Success Story Of Amazon To Emerge As Pioneer Strategy SS VThis slide provides information regarding SWOT analysis technique utilized by Amazon to evaluate its competitive positioning. The slide highlighting threats faced by Amazon causing potential issues in terms of data and online privacy risk, aggressive pricing strategies, etc. Increase audience engagement and knowledge by dispensing information using Major Threats That Creates Success Story Of Amazon To Emerge As Pioneer Strategy SS V. This template helps you present information on four stages. You can also present information on Online Privacy Risk, Aggressive Pricing Strategies, Stiff Competition using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Attributes And Motivation Drivers Of Cyber Security Threat Actors
Attributes And Motivation Drivers Of Cyber Security Threat ActorsThis slide illustrates major features and motivation drivers of cyber security hijackers who attack with an intention to gain from such activities. The major cyber security risk actors are nation states, cyber criminals, terrorist groups and insider threats Introducing our Attributes And Motivation Drivers Of Cyber Security Threat Actors set of slides. The topics discussed in these slides are Nation States, Cybercriminals . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
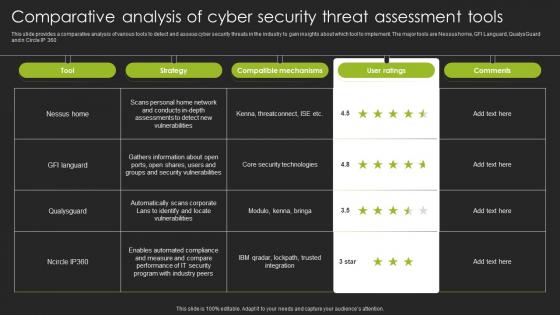 Comparative Analysis Of Cyber Security Threat Assessment Tools
Comparative Analysis Of Cyber Security Threat Assessment ToolsThis slide provides a comparative analysis of various tools to detect and assess cyber security threats in the industry to gain insights about which tool to implement. The major tools are Nessus home, GFI Languard, QualysGuard and n Circle IP 360 Presenting our well structured Comparative Analysis Of Cyber Security Threat Assessment Tools. The topics discussed in this slide are Nessus Home, Compatible Mechanisms. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Major Target Areas Of Cyber Security Threats
Major Target Areas Of Cyber Security ThreatsThe following slide consists of major target points of cyber security attacks aimed at accessing, changing, or destroying sensitive information extorting money from users or interrupting normal business processes. The major targets are electronic devices, critical information, financial resources and public opinion Presenting our set of slides with Major Target Areas Of Cyber Security Threats. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Critical Information, Financial Resources.
-
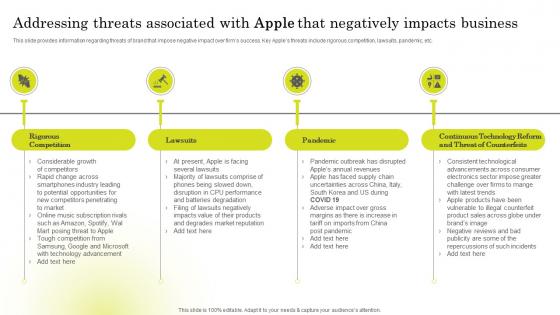 Addressing Threats Associated Brand Strategy Of Apple To Emerge Branding SS V
Addressing Threats Associated Brand Strategy Of Apple To Emerge Branding SS VThis slide provides information regarding threats of brand that impose negative impact over firms success. Key Apples threats include rigorous competition, lawsuits, pandemic, etc. Introducing Addressing Threats Associated Brand Strategy Of Apple To Emerge Branding SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Pandemic, Lawsuits, Rigorous Competition, using this template. Grab it now to reap its full benefits.
-
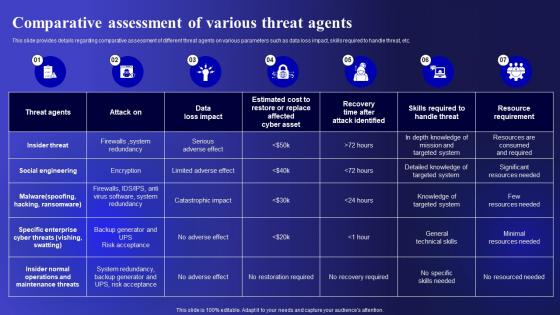 Comparative Assessment Of Various Cyber Threats Management To Enable Digital Assets Security
Comparative Assessment Of Various Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Deliver an outstanding presentation on the topic using this Comparative Assessment Of Various Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Comparative, Assessment, Parameters using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Different Kinds Of Insider Digital Threats Cyber Threats Management To Enable Digital Assets Security
Different Kinds Of Insider Digital Threats Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Present the topic in a bit more detail with this Different Kinds Of Insider Digital Threats Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Malicious Insider, Negligent Or Careless Insider, Third Party Insider . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Cyber Threats Management To Enable Digital Assets Security
Table Of Contents Cyber Threats Management To Enable Digital Assets SecurityPresent the topic in a bit more detail with this Table Of Contents Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Categorizing, Associated, Determine Sequence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Macro Analysis Of Threats Checklist Icon
Macro Analysis Of Threats Checklist IconPresenting our set of slides with Macro Analysis Of Threats Checklist Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Macro Analysis, Threats Checklist Icon.
-
 Threat Of Substitute Products Or Microsoft Strategy For Continuous Business Growth Strategy Ss
Threat Of Substitute Products Or Microsoft Strategy For Continuous Business Growth Strategy SsThis slide shows details regarding substitute products and services which may or may not become a threat for microsoft in the coming years. It covers information about the low performance of substitute or competitive products. Deliver an outstanding presentation on the topic using this Threat Of Substitute Products Or Microsoft Strategy For Continuous Business Growth Strategy Ss. Dispense information and present a thorough explanation of Products, Services, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
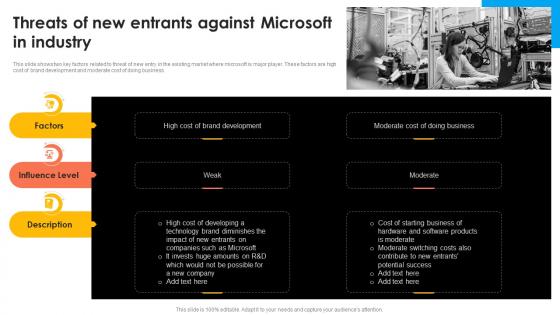 Threats Of New Entrants Against Microsoft Strategy For Continuous Business Growth Strategy Ss
Threats Of New Entrants Against Microsoft Strategy For Continuous Business Growth Strategy SsThis slide shows two key factors related to threat of new entry in the existing market where microsoft is major player. These factors are high cost of brand development and moderate cost of doing business. Present the topic in a bit more detail with this Threats Of New Entrants Against Microsoft Strategy For Continuous Business Growth Strategy Ss. Use it as a tool for discussion and navigation on Business, Brand Development, Microsoft. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Electronic Banking Management Major Types Of E Banking Security Threats
Electronic Banking Management Major Types Of E Banking Security ThreatsThis slide represents types of e banking security threats. It includes brute force, phishing, pharming, cross site scripting and trojan horse. Deliver an outstanding presentation on the topic using this Electronic Banking Management Major Types Of E Banking Security Threats. Dispense information and present a thorough explanation of Brute Force, Phishing, Pharming, Cross Site Scripting, Security Software Over System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Threat Of Alternative Products Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Of Alternative Products Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts the threat of substitutes and is perfect for use in presentations and documents. It is a high-quality vector image with bright, vivid colours that will stand out and make your content more engaging. It is easy to resize and customize to fit your needs.
-
 Threat Of Alternative Products Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Of Alternative Products Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon represents the threat of substitutes in the market. It is a simple and effective visual representation of the impact of substitutes on a business and its products. This icon is perfect for any presentation to help explain the concept of substitutes in a clear and concise way.
-
 Threat Of Substitutes Cloth Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Of Substitutes Cloth Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts the threat of substitutes and is perfect for use in presentations and documents. It is a high-quality vector image with bright, vivid colours that will stand out and make your content more engaging. It is easy to resize and customize to fit your needs.
-
 Threat Of Substitutes Cloth Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Of Substitutes Cloth Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon represents the threat of substitutes in the market. It is a simple and effective visual representation of the impact of substitutes on a business and its products. This icon is perfect for any presentation to help explain the concept of substitutes in a clear and concise way.
-
 Threat Of Substitutes Device Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Of Substitutes Device Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts the threat of substitutes and is perfect for use in presentations and documents. It is a high-quality vector image with bright, vivid colours that will stand out and make your content more engaging. It is easy to resize and customize to fit your needs.
-
 Threat Of Substitutes Device Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Of Substitutes Device Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon represents the threat of substitutes in the market. It is a simple and effective visual representation of the impact of substitutes on a business and its products. This icon is perfect for any presentation to help explain the concept of substitutes in a clear and concise way.
-
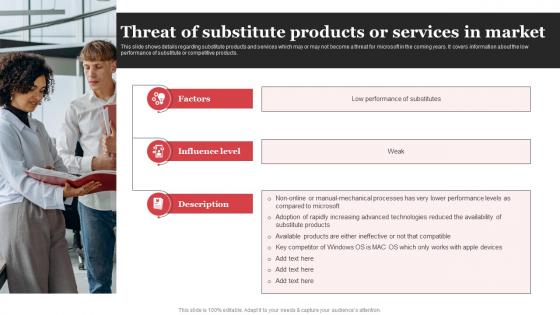 Threat Of Substitute Products Or Services In Market Microsoft Strategic Plan Strategy SS V
Threat Of Substitute Products Or Services In Market Microsoft Strategic Plan Strategy SS VThis slide shows details regarding substitute products and services which may or may not become a threat for microsoft in the coming years. It covers information about the low performance of substitute or competitive products. Increase audience engagement and knowledge by dispensing information using Threat Of Substitute Products Or Services In Market Microsoft Strategic Plan Strategy SS V This template helps you present information on three stages. You can also present information on Factors, Influence Level using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
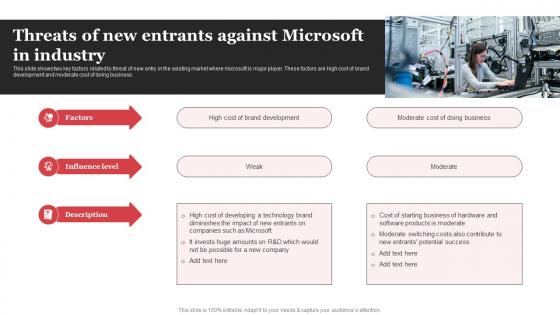 Threats Of New Entrants Against Microsoft In Industry Microsoft Strategic Plan Strategy SS V
Threats Of New Entrants Against Microsoft In Industry Microsoft Strategic Plan Strategy SS VThis slide shows two key factors related to threat of new entry in the existing market where microsoft is major player. These factors are high cost of brand development and moderate cost of doing business. Introducing Threats Of New Entrants Against Microsoft In Industry Microsoft Strategic Plan Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Brand Development, Moderate Cost using this template. Grab it now to reap its full benefits.
-
 Comprehensive Guide For Successful Types Of Website Security Threats And Vulnerabilities
Comprehensive Guide For Successful Types Of Website Security Threats And VulnerabilitiesFollowing slide exhibits types of security threats that negatively affect website operational efficiency and goodwill. It include types such as malware, viruses, spam links, DDoS with examples, impact and mitigation tools. Increase audience engagement and knowledge by dispensing information using Comprehensive Guide For Successful Types Of Website Security Threats And Vulnerabilities. This template helps you present information on three stages. You can also present information on Malware And Viruses, Spam Links, Denial Of Service Attacks, Website Security Threats, Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Alternative Threat Of Substitutes Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Alternative Threat Of Substitutes Colored Icon In Powerpoint Pptx Png And Editable Eps FormatA coloured PowerPoint icon depicting the threat of substitutes in a market. Illustrates the competitive pressure on companies from other products and services that can be used as an alternative. Perfect for presentations on market analysis and business strategy.
-
 Alternative Threat Of Substitutes Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Alternative Threat Of Substitutes Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is an essential visual aid for any presentation on the threat of substitutes. It is a simple yet effective illustration of the concept, providing a clear and concise representation of the concept. It is a great way to effectively communicate the concept to an audience.
-
 Person Threat Of Substitutes Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Person Threat Of Substitutes Colored Icon In Powerpoint Pptx Png And Editable Eps FormatA coloured PowerPoint icon depicting the threat of substitutes in a market. Illustrates the competitive pressure on companies from other products and services that can be used as an alternative. Perfect for presentations on market analysis and business strategy.
-
 Person Threat Of Substitutes Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Person Threat Of Substitutes Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is an essential visual aid for any presentation on the threat of substitutes. It is a simple yet effective illustration of the concept, providing a clear and concise representation of the concept. It is a great way to effectively communicate the concept to an audience.
-
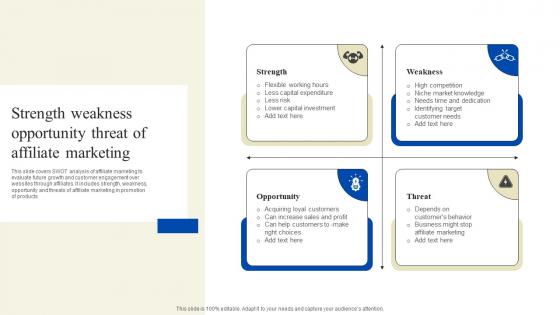 Strength Weakness Opportunity Threat Of Affiliate Marketing
Strength Weakness Opportunity Threat Of Affiliate MarketingThis slide covers SWOT analysis of affiliate marketing to evaluate future growth and customer engagement over websites through affiliates. It includes strength, weakness, opportunity and threats of affiliate marketing in promotion of products Introducing our Strength Weakness Opportunity Threat Of Affiliate Marketing set of slides. The topics discussed in these slides are Threat, Opportunity, Strength. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
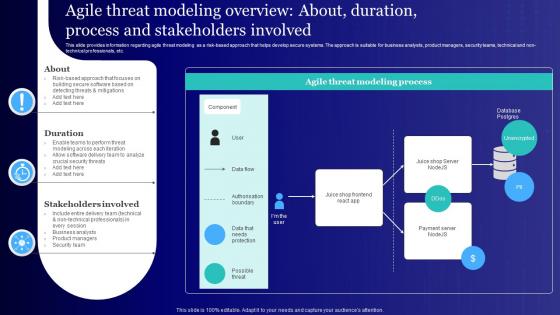 Agile Threat Modeling Overview About Usage Of Technology Ethically
Agile Threat Modeling Overview About Usage Of Technology EthicallyThis slide provides information regarding agile threat modeling as a risk based approach that helps develop secure systems. The approach is suitable for business analysts, product managers, security teams, technical and non technical professionals, etc.Present the topic in a bit more detail with this Agile Threat Modeling Overview About Usage Of Technology Ethically. Use it as a tool for discussion and navigation on Modeling Across, Building Secure, Crucial Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
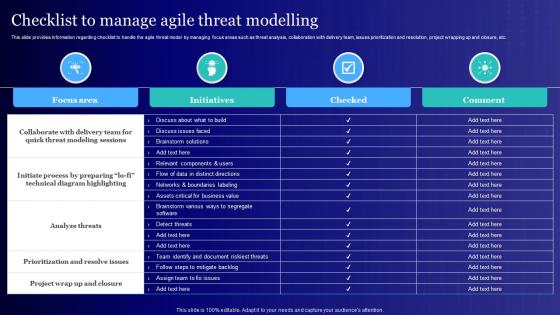 Checklist To Manage Agile Threat Modelling Usage Of Technology Ethically
Checklist To Manage Agile Threat Modelling Usage Of Technology EthicallyThis slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc.Deliver an outstanding presentation on the topic using this Checklist To Manage Agile Threat Modelling Usage Of Technology Ethically. Dispense information and present a thorough explanation of Prioritization Resolve Issues, Analyze Threats, Modeling Sessions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
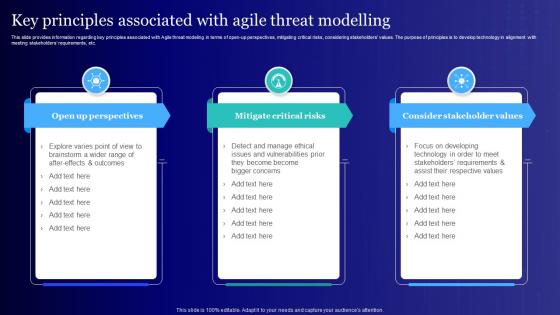 Key Principles Associated With Agile Threat Usage Of Technology Ethically
Key Principles Associated With Agile Threat Usage Of Technology EthicallyThis slide provides information regarding key principles associated with Agile threat modeling in terms of open up perspectives, mitigating critical risks, considering stakeholders values. The purpose of principles is to develop technology in alignment with meeting stakeholders requirements, etc.Increase audience engagement and knowledge by dispensing information using Key Principles Associated With Agile Threat Usage Of Technology Ethically. This template helps you present information on four stages. You can also present information on Unintended Consequences, Associated Product, Participants Represent using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Reasons of cyber threats powerpoint slide deck samples
Reasons of cyber threats powerpoint slide deck samplesPresenting reasons of cyber threats powerpoint slide deck samples. This is a reasons of cyber threats powerpoint slide deck samples. This is a two stage process. The stages in this process are no it department, less likely to follow internet best practices, simple networks and systems, use encryption, back up data, get cyber insurance, using the cloud, message recipient, big data, threats ads malware and cybercrime.
-
 Opportunities and threats framework sample of ppt presentation
Opportunities and threats framework sample of ppt presentationPresenting opportunities and threats framework sample of PPT presentation.PPT template can be utilized by sales and marketing teams and business managers. Instantly downloadable slide and supports formats like JPEG and PDF. Adjust colors, text, and fonts as per your business requirements. This PPT layout is compatible with Google Slides. It offers easy to put in the company logo, trademark or name; accommodate words to support the key points. Images do no blur out even when they are projected on big screens.
-
 Bomb threat girl standing in front of explosion
Bomb threat girl standing in front of explosionPresenting this set of slides with name - Bomb Threat Girl Standing In Front Of Explosion. This is a one stage process. The stages in this process are Bomb Threat, Bomb Scare, Explosive Device.
-
 Bomb threat statue of liberty explosion cloud
Bomb threat statue of liberty explosion cloudPresenting this set of slides with name - Bomb Threat Statue Of Liberty Explosion Cloud. This is a one stage process. The stages in this process are Bomb Threat, Bomb Scare, Explosive Device.
-
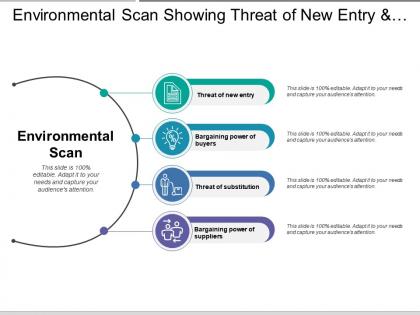 Environmental scan showing threat of new entry and substitutes
Environmental scan showing threat of new entry and substitutesPresenting this set of slides with name - Environmental Scan Showing Threat Of New Entry And Substitutes. This is a four stage process. The stages in this process are Environmental Scan, Environmental Study, Environmental Examine.
-
 List of business opportunities and threats with icons
List of business opportunities and threats with iconsPresenting this set of slides with name - List Of Business Opportunities And Threats With Icons. This is a two stage process. The stages in this process are Opportunities And Threats, Issues And Solutions, Problem And Challenges.
-
 Swot icons covering different icons for each category of strength weakness threat and opportunities
Swot icons covering different icons for each category of strength weakness threat and opportunitiesPresenting this set of slides with name - Swot Icons Covering Different Icons For Each Category Of Strength Weakness Threat And Opportunities. This is a four stage process. The stages in this process are Swot Icons, Swot Analysis Icon, Swot Matrix Icon.
-
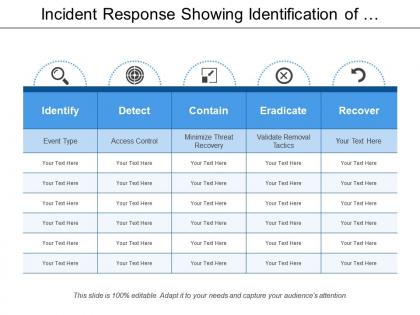 Incident response showing identification of threats and recovery
Incident response showing identification of threats and recoveryPresenting this set of slides with name - Incident Response Showing Identification Of Threats And Recovery. This is a five stage process. The stages in this process are Incident Response, Incident Reaction, Incident Reply.
-
 Overlapping squares showing threats of organisational structure
Overlapping squares showing threats of organisational structurePresenting this set of slides with name - Overlapping Squares Showing Threats Of Organisational Structure. This is a four stage process. The stages in this process are Overlapping Squares, Convergence Squares, Concurrence Squares.
-
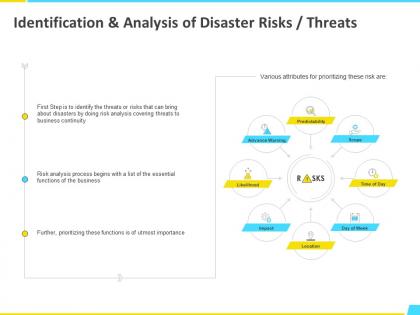 Identification and analysis of disaster risks threats process ppt powerpoint presentation file influencers
Identification and analysis of disaster risks threats process ppt powerpoint presentation file influencersPresenting this set of slides with name Identification And Analysis Of Disaster Risks Threats Process Ppt Powerpoint Presentation File Influencers. This is a eight stage process. The stages in this process are Planning, Management, Marketing, Business, Strategy. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Summary of key findings icons slide growth threat e156 ppt powerpoint presentation
Summary of key findings icons slide growth threat e156 ppt powerpoint presentationPresenting this set of slides with name Summary Of Key Findings Icons Slide Growth Threat E156 Ppt Powerpoint Presentation. The topics discussed in these slides are Threat, Our Team, Growth, Agenda, Our Goal. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Benefits of jidoka threat a425 ppt powerpoint presentation layouts topics
Benefits of jidoka threat a425 ppt powerpoint presentation layouts topicsPresenting this set of slides with name Benefits Of Jidoka Threat A425 Ppt Powerpoint Presentation Layouts Topics. This is a three stage process. The stages in this process are Business, Planning, Strategy, Marketing, Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Threat of product substitution with switching cost
Threat of product substitution with switching costPresenting this set of slides with name Threat Of Product Substitution With Switching Cost. The topics discussed in these slides are Switching Cost, Number Of Substitute Products Available, Buyer Propensity To Substitute, Relative Price Performance Of Substitute, Price Level Of Product Differentiation. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Six building blocks of digital transformation threats ppt powerpoint slides
Six building blocks of digital transformation threats ppt powerpoint slidesPresenting this set of slides with name Six Building Blocks Of Digital Transformation Threats Ppt Powerpoint Slides. This is a six stage process. The stages in this process are Mindset, Leaders, Business, Excellence, Strategy, Opportunities, Threats, Develop, Digital Business, Capabilities. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
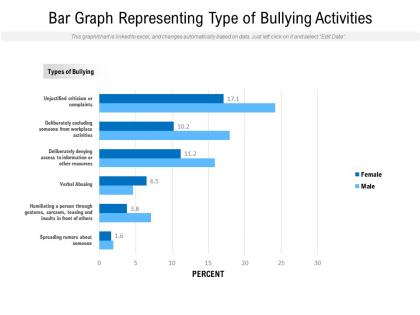 Bar graph representing type of bullying activities
Bar graph representing type of bullying activitiesPresenting this set of slides with name Bar Graph Representing Type Of Bullying Activities. The topics discussed in these slides are Resources, Gestures, Sarcasm. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
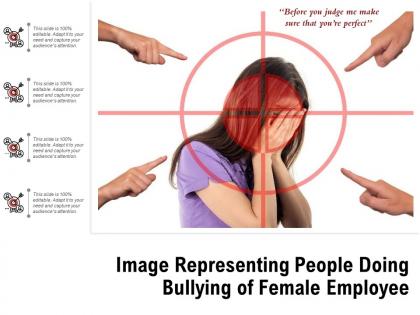 Image representing people doing bullying of female employee
Image representing people doing bullying of female employeePresenting this set of slides with name Image Representing People Doing Bullying Of Female Employee. The topics discussed in these slide is Image Representing People Doing Bullying Of Female Employee. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Powerpoint template and background with the threat of a bomb
Powerpoint template and background with the threat of a bombAre you looking for inspirational design ideas or a fully equipped template for your next presentation Then this Powerpoint Template And Background With The Threat Of A Bomb is an ideal fit for your next delivery. Portray your principal ideas and make your presentation stand out with this design. Make your audience fully aware of the concept by presenting information in an accessible way. The streamlined layout of this design will help your audience understand and retain the complicated idea thereby making it an impactful delivery. It can be used in businesses and organizations such as corporal presentations case studies reports marketing or any other academic presentation to make your message clear and distinctive. This PPT is designed as per the emerging trends in the marketplace and therefore you will face no difficulty in adapting it to your setting. The high resolution graphics and images make it free from any form of pixelation thus making your presentation delivery an absolute success.
-
 Industry challenges threat of ransomware ppt powerpoint presentation examples
Industry challenges threat of ransomware ppt powerpoint presentation examplesUse this slide to show the major industry challenges in E-Mail Security market. Presenting this set of slides with name Industry Challenges Threat Of Ransomware Ppt Powerpoint Presentation Examples. This is a five stage process. The stages in this process are Industry Challenges, Threat, Ransomware. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Powerpoint template and background with an illustration shows a threat of global warming
Powerpoint template and background with an illustration shows a threat of global warmingBolster your presentation designs and make them impactful with our Powerpoint Template And Background With An Illustration Shows A Threat Of Global Warming. This cutting edge PPT will help you meet your audience expectations due to its interactive design. Useful content has been added to help you convey your ideas vision and principle aspects more proficiently. Throw light on what is important and take your presentation game a notch higher with this multipurpose design that comes with an assortment of features. No matter what is the purpose of your presentation conveying business ideas proposals analysis reports or any other you will find this creative design template perfect for all the scenarios. Also input any information and keep your audience hooked with this content ready template that is fully editable and customizable. Besides this you can represent large sets of complex data and information with this template design that can be adopted by any industry agency individual or group to deliver awe inspiring presentations.
-
 Icon of laptop protected with security software from cyber threat
Icon of laptop protected with security software from cyber threatPresenting this set of slides with name Icon Of Laptop Protected With Security Software From Cyber Threat. This is a three stage process. The stages in this process are Icon Of Laptop Protected With Security Software From Cyber Threat. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Role of employees in reducing threats information ppt powerpoint presentation rules
Role of employees in reducing threats information ppt powerpoint presentation rulesHere we have listed some of the organization ethic and policies that are to be followed by the employees through which internal threats to the company can be prevented. Presenting this set of slides with name Role Of Employees In Reducing Threats Information Ppt Powerpoint Presentation Rules. This is a three stage process. The stages in this process are Role Employees, Reducing Threats, Information. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
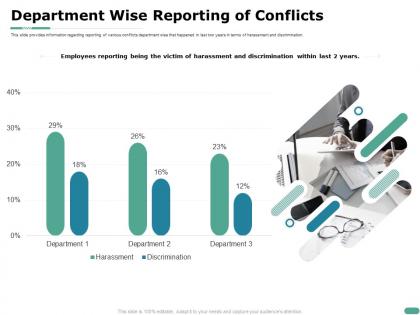 Department wise reporting of conflicts harassment ppt powerpoint presentation file model
Department wise reporting of conflicts harassment ppt powerpoint presentation file modelThis slide provides information regarding reporting of various conflicts department wise that happened in last two years in terms of harassment and discrimination. Presenting this set of slides with name Department Wise Reporting Of Conflicts Harassment Ppt Powerpoint Presentation File Model. The topics discussed in these slides are Employees, Reporting, Years. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
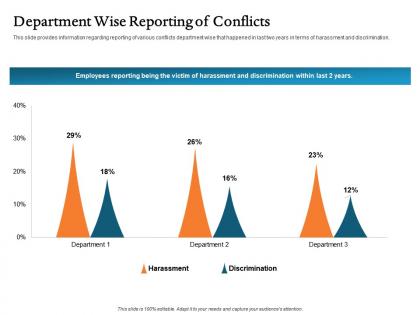 Department wise reporting of conflicts harassment ppt file aids
Department wise reporting of conflicts harassment ppt file aidsThis slide provides information regarding reporting of various conflicts department wise that happened in last two years in terms of harassment and discrimination. Presenting this set of slides with name Department Wise Reporting Of Conflicts Harassment Ppt File Aids. This is a three stage process. The stages in this process are Department Wise Reporting Of Conflicts. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Various kinds of personnel crisis sexual assaults ppt powerpoint slides
Various kinds of personnel crisis sexual assaults ppt powerpoint slidesThis slide provides information regarding the various personnel crisis that exists. It occurs when employee or individual associated with the company perform illegal or unethical misconduct. Presenting this set of slides with name Various Kinds Of Personnel Crisis Sexual Assaults Ppt Powerpoint Slides. The topics discussed in these slides are Various Kinds, Personnel Crisis, Sexual Assaults. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.



