Powerpoint Templates and Google slides for Threats
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 KPIs To Evaluate Cyber Security Risk Management Implementing Strategies To Mitigate Cyber Security Threats
KPIs To Evaluate Cyber Security Risk Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights some key performance indicators to measure the impact of cyber security risk administration to assess its effectiveness and take improved decisions. It includes elements such as level of preparedness, mean time to detect, success rating etc. Present the topic in a bit more detail with this KPIs To Evaluate Cyber Security Risk Management Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Level Of Preparedness, Mean Time To Detect, Mean Time To Resolve This template is free to edit as deemed fit for your organization. Therefore download it now.
-
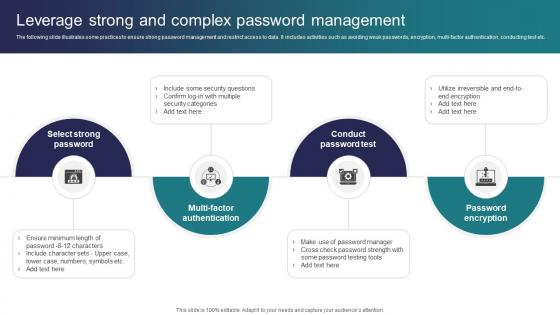 Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security Threats
Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates some practices to ensure strong password management and restrict access to data. It includes activities such as avoiding weak passwords, encryption, multi factor authentication, conducting test etc. Introducing Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Conduct Password Test, Password Encryption, Multi Factor Authentication using this template. Grab it now to reap its full benefits.
-
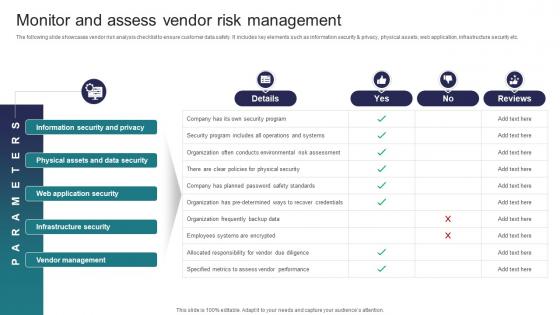 Monitor And Assess Vendor Risk Management Implementing Strategies To Mitigate Cyber Security Threats
Monitor And Assess Vendor Risk Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Present the topic in a bit more detail with this Monitor And Assess Vendor Risk Management Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Information Security And Privacy, Physical Assets And Data Security, Web Application Security This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Organize Cyber Security Training For Employees Implementing Strategies To Mitigate Cyber Security Threats
Organize Cyber Security Training For Employees Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the staff cyber security training plan to educate them regarding technology threats and practices. It mainly includes elements such as topics to be covered, target audience, trainer name, mode, proposed date, timings etc. Deliver an outstanding presentation on the topic using this Organize Cyber Security Training For Employees Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Document Management, Target Audience, Proposed Date using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
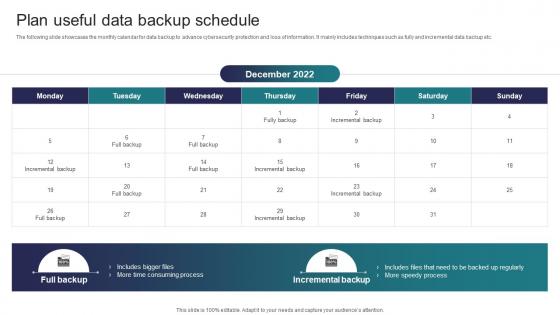 Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats
Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Increase audience engagement and knowledge by dispensing information using Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Time Consuming Process, Speedy Process, Incremental Backup using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Run Penetration Testing To Review Risk Implementing Strategies To Mitigate Cyber Security Threats
Run Penetration Testing To Review Risk Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases various methods to review cyber risks to determine probability and impact of risks. It includes elements such as penetration, red team and risk based testing along with objectives, features, cost, outcomes, duration etc. Present the topic in a bit more detail with this Run Penetration Testing To Review Risk Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Objectives, Features, Duration This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats
Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the best cybersecurity training courses to educate employees and minimize the possibility of cyber attacks. It includes cloud, disaster recovery, hardware, information security programs, duration, mode and cost Deliver an outstanding presentation on the topic using this Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Cloud Security, Information Security, Disaster Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Select Tools To Reduce Cyber Security Failure Implementing Strategies To Mitigate Cyber Security Threats
Select Tools To Reduce Cyber Security Failure Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Present the topic in a bit more detail with this Select Tools To Reduce Cyber Security Failure Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Features, Free Trial, Cost This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Implementing Strategies To Mitigate Cyber Security Threats
Table Of Contents Implementing Strategies To Mitigate Cyber Security ThreatsIncrease audience engagement and knowledge by dispensing information using Table Of Contents Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Industry Overview, Current Scenario Analysis, Cyber Security Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
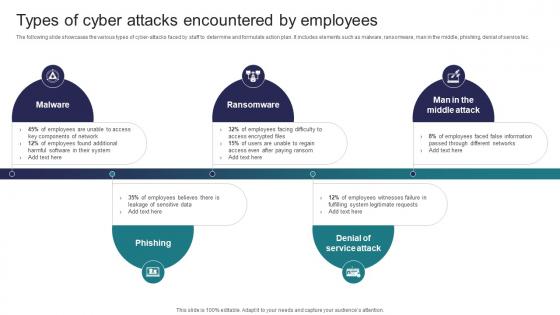 Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats
Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the various types of cyber attacks faced by staff to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service tec. Introducing Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Ransomware, Phishing using this template. Grab it now to reap its full benefits.
-
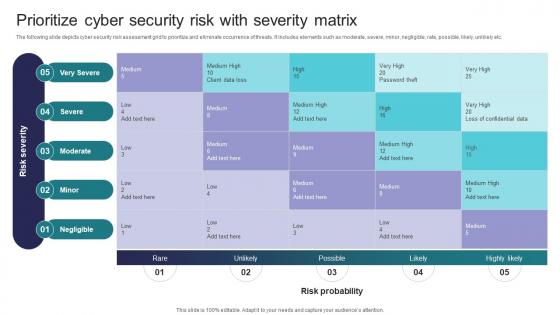 Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix
Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity MatrixThe following slide depicts cyber security risk assessment grid to prioritize and eliminate occurrence of threats. It includes elements such as moderate, severe, minor, negligible, rate, possible, likely, unlikely etc. Introducing Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Very Severe, Severe, Moderate using this template. Grab it now to reap its full benefits.
-
 Threats To Cybersecurity Infrastructure In Education
Threats To Cybersecurity Infrastructure In EducationThis slide depicts the threats to cybersecurity infrastructure in education. The purpose of this slide is to help the business ensure the organization is able to prevent attacks such insider threats, phishing, ransomware, etc. Presenting our set of slides with Threats To Cybersecurity Infrastructure In Education. This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Insider Threats, Malware, Phishing, Ransomware
-
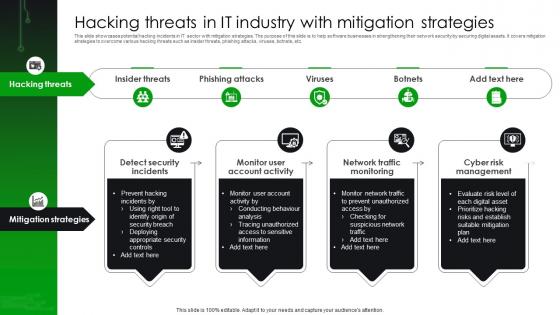 Hacking Threats In IT Industry With Mitigation Strategies
Hacking Threats In IT Industry With Mitigation StrategiesThis slide showcases potential hacking incidents in IT sector with mitigation strategies. The purpose of this slide is to help software businesses in strengthening their network security by securing digital assets. It covers mitigation strategies to overcome various hacking threats such as insider threats, phishing attacks, viruses, botnets, etc. Introducing our premium set of slides with Hacking Threats In IT Industry With Mitigation Strategies Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Insider Threats, Monitor Account Activity, Network Traffic Monitoring. So download instantly and tailor it with your information.
-
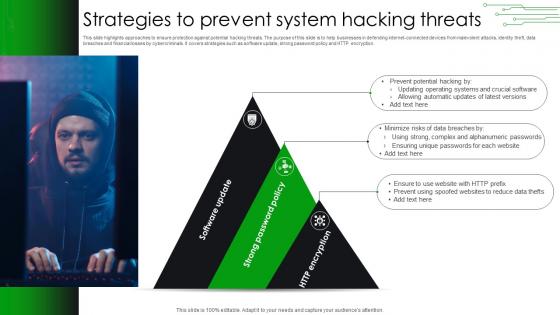 Strategies To Prevent System Hacking Threats
Strategies To Prevent System Hacking ThreatsThis slide highlights approaches to ensure protection against potential hacking threats. The purpose of this slide is to help businesses in defending internet connected devices from malevolent attacks, identity theft, data breaches and financial losses by cybercriminals. It covers strategies such as software update, strong password policy and HTTP encryption. Presenting our well structured Strategies To Prevent System Hacking Threats The topics discussed in this slide are Alphanumeric Passwords, Ensuring Unique Passwords, Updating Operating. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Primary Types Of Mobile Security Threats
Primary Types Of Mobile Security ThreatsThis slide discusses the various types of mobile security threats which include phishing, malware and ransomware, crypto jacking and outdated operating system. Introducing our premium set of slides with name Primary Types Of Mobile Security Threats. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Phishing, Malware And Ransomware, Outdated Operating Systems, Crypto Jacking. So download instantly and tailor it with your information.
-
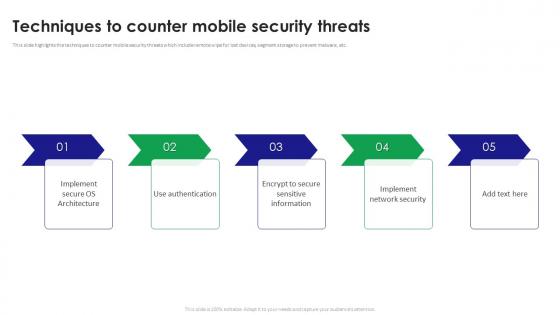 Techniques To Counter Mobile Security Threats
Techniques To Counter Mobile Security ThreatsThis slide highlights the techniques to counter mobile security threats which include remote wipe for lost devices, segment storage to prevent malware, etc. Presenting our set of slides with name Techniques To Counter Mobile Security Threats. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implement Network Security, Techniques To Counter, Mobile Security Threats.
-
 Analyze And Rank Impact Of Cyber Threat Cyber Risk Assessment
Analyze And Rank Impact Of Cyber Threat Cyber Risk AssessmentThe following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Present the topic in a bit more detail with this Analyze And Rank Impact Of Cyber Threat Cyber Risk Assessment Use it as a tool for discussion and navigation on Framework, Appropriate Structure, Internet Access This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determine Cyber Security Risks And Threats Cyber Risk Assessment
Determine Cyber Security Risks And Threats Cyber Risk AssessmentThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Increase audience engagement and knowledge by dispensing information using Determine Cyber Security Risks And Threats Cyber Risk Assessment This template helps you present information on three stages. You can also present information on Malware, Phishing, Ransomware, Weak Credentials using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
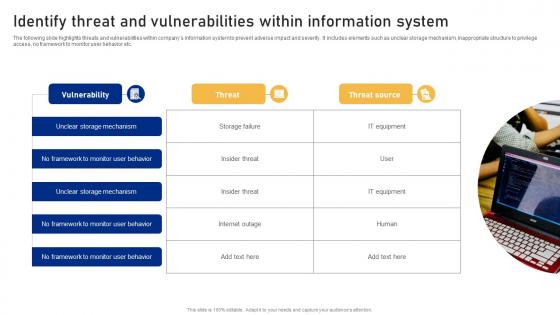 Identify Threat And Vulnerabilities Within Information System Cyber Risk Assessment
Identify Threat And Vulnerabilities Within Information System Cyber Risk AssessmentThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Introducing Identify Threat And Vulnerabilities Within Information System Cyber Risk Assessment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on No Framework, Monitor User Behavior, Vulnerability using this template. Grab it now to reap its full benefits.
-
 Environmental Threats Examples In Powerpoint And Google Slides Cpb
Environmental Threats Examples In Powerpoint And Google Slides CpbPresenting Environmental Threats Examples In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Environmental Threats Examples This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Internal Validity Threats In Powerpoint And Google Slides Cpb
Internal Validity Threats In Powerpoint And Google Slides CpbPresenting Internal Validity Threats In Powerpoint And Google Slides Cpb. slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Internal Validity Threats. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Agenda For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Agenda For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VIntroducing Agenda For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Intelligence, Vulnerability, Assessment, using this template. Grab it now to reap its full benefits.
-
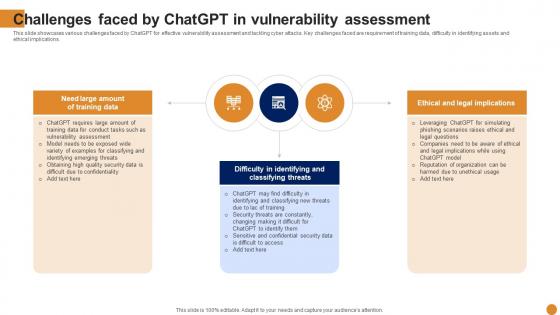 Challenges Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Challenges Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various challenges faced by ChatGPT for effective vulnerability assessment and tackling cyber attacks. Key challenges faced are requirement of training data, difficulty in identifying assets and ethical implications. Increase audience engagement and knowledge by dispensing information using Challenges Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Vulnerability, Assessment, Implications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Chatgpt For Streamlining And Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Chatgpt For Streamlining And Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases overview of ChatGPT for streamlining and optimizing the security operations in organizations. Its key elements are cybersecurity training, enhanced communication during attack, developing policies and reporting after attack Introducing Chatgpt For Streamlining And Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Training, Reporting After Attack, Developing Policies, using this template. Grab it now to reap its full benefits.
-
 Chatgpt Opportunities For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Chatgpt Opportunities For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various ChatGPT opportunities for vulnerability assessment which can help to tackle cyber attack. Its key elements are automation of security tasks, improved efficiency and identification of new vulnerabilities. Increase audience engagement and knowledge by dispensing information using Chatgpt Opportunities For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Opportunities, Vulnerability, Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Chatgpt Organization Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Chatgpt Organization Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VIntroducing Chatgpt Organization Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Organization, Cybersecurity, Threat Intelligence, using this template. Grab it now to reap its full benefits.
-
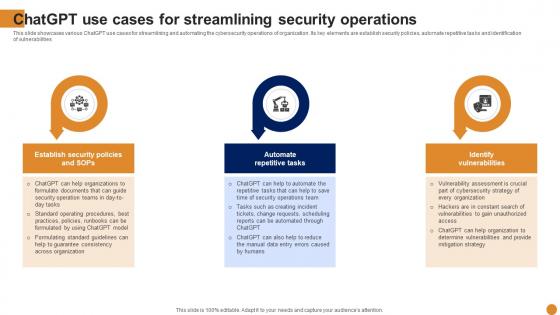 Chatgpt Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Chatgpt Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various ChatGPT use cases for streamlining and automating the cybersecurity operations of organization. Its key elements are establish security policies, automate repetitive tasks and identification of vulnerabilities Increase audience engagement and knowledge by dispensing information using Chatgpt Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Streamlining, Operations, Identify Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
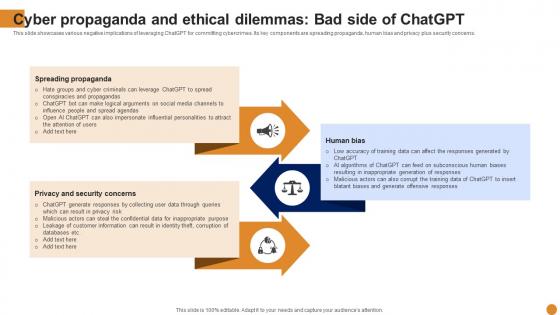 Cyber Propaganda And Ethical Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Cyber Propaganda And Ethical Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various negative implications of leveraging ChatGPT for committing cybercrimes. Its key components are spreading propaganda, human bias and privacy plus security concerns. Introducing Cyber Propaganda And Ethical Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Spreading Propaganda, Privacy And Security Concerns, Propaganda, using this template. Grab it now to reap its full benefits.
-
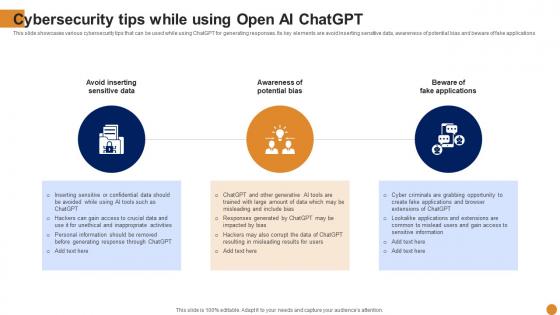 Cybersecurity Tips While Using Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Cybersecurity Tips While Using Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various cybersecurity tips that can be used while using ChatGPT for generating responses. Its key elements are avoid inserting sensitive data, awareness of potential bias and beware of fake applications Increase audience engagement and knowledge by dispensing information using Cybersecurity Tips While Using Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Avoid Inserting Sensitive Data, Awareness Of Potential Bias, Beware Of Fake Applications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Gathering And Analyzing Threat Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Gathering And Analyzing Threat Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various data sources that are leveraged by ChatGPT for threat intelligence to tack cyber attack on organization. Various data sources for threat intelligence are security blogs, social media and security forums. Introducing Gathering And Analyzing Threat Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Blogs, Security Forums, Social Media, using this template. Grab it now to reap its full benefits.
-
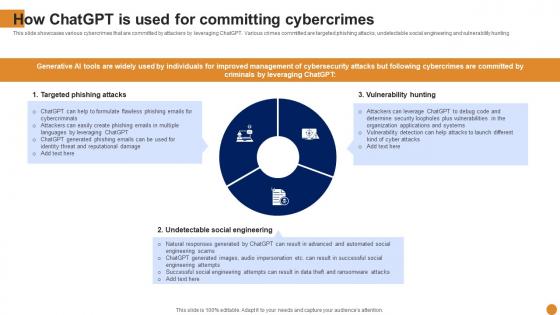 How Committing Cybercrimes Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
How Committing Cybercrimes Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various cybercrimes that are committed by attackers by leveraging ChatGPT. Various crimes committed are targeted phishing attacks, undetectable social engineering and vulnerability hunting Present the topic in a bit more detail with this How Committing Cybercrimes Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Use it as a tool for discussion and navigation on Targeted Phishing Attacks, Undetectable Social Engineering, Vulnerability Hunting. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
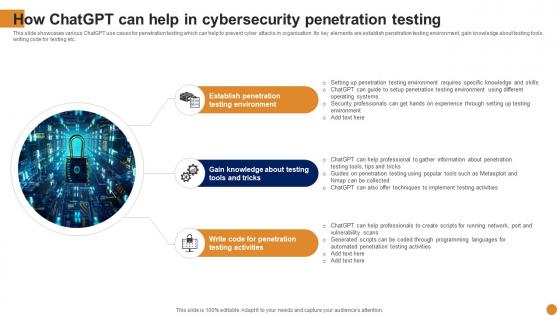 How In Cybersecurity Penetration Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
How In Cybersecurity Penetration Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various ChatGPT use cases for penetration testing which can help to prevent cyber attacks in organization. Its key elements are establish penetration testing environment, gain knowledge about testing tools, writing code for testing etc. Introducing How In Cybersecurity Penetration Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Penetration, Testing Environment, Penetration, using this template. Grab it now to reap its full benefits.
-
 How Incident Management Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
How Incident Management Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various ChatGPT use cases that can help organization in incident management and tackling cyber attacks. Its key elements are explore cyber attacks, decision support and post incident analysis Increase audience engagement and knowledge by dispensing information using How Incident Management Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Explore Cyber Attacks, Decision Support, Post Incident Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How Threat Intelligence Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
How Threat Intelligence Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases ChatGPT usage for threat intelligence for tackling cyber attacks on organizations. Its key elements are generate threat reports, analyze threat intelligence data and answer threat related queries. Introducing How Threat Intelligence Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Generate Threat Reports, Analyze Threat Intelligence Data, Answer Threat Related Queries, using this template. Grab it now to reap its full benefits.
-
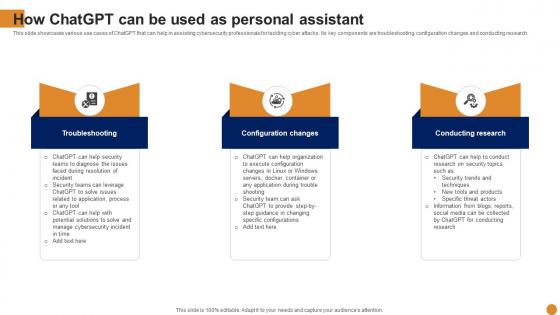 How Used As Personal Assistant Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
How Used As Personal Assistant Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various use cases of ChatGPT that can help in assisting cybersecurity professionals for tackling cyber attacks. Its key components are troubleshooting, configuration changes and conducting research. Increase audience engagement and knowledge by dispensing information using How Used As Personal Assistant Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Troubleshooting, Configuration Change, Conducting Research using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Icons Slide For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VDeliver an outstanding presentation on the topic using this Icons Slide For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Dispense information and present a thorough explanation of Icons using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
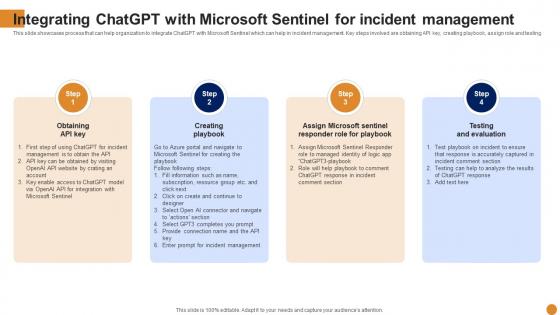 Integrating Chatgpt With Microsoft Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Integrating Chatgpt With Microsoft Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases process that can help organization to integrate ChatGPT with Microsoft Sentinel which can help in incident management. Key steps involved are obtaining API key, creating playbook, assign role and testing Introducing Integrating Chatgpt With Microsoft Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Obtaining API Key, Creating Playbook, Testing And Evaluation, using this template. Grab it now to reap its full benefits.
-
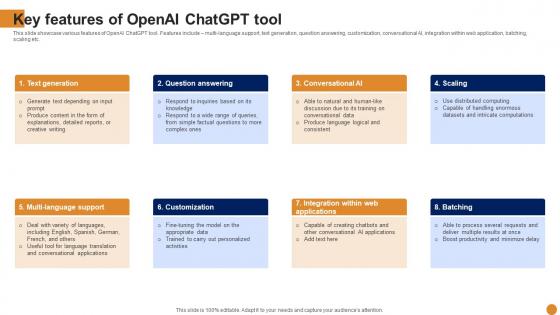 Key Features Of Openai Chatgpt Tool Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Key Features Of Openai Chatgpt Tool Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcase various features of OpenAI ChatGPT tool. Features include multi-language support, text generation, question answering, customization, conversational AI, integration within web application, batching, scaling etc. Increase audience engagement and knowledge by dispensing information using Key Features Of Openai Chatgpt Tool Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on eight stages. You can also present information on Text Generation, Question Answering, Customization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Importance Of Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Key Importance Of Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various statistics that highlights the importance of cybersecurity in organization. It highlights stats related to malware attacks, DDos attacks, cybersecurity spending, ransomware attacks, malicious mining software etc. Present the topic in a bit more detail with this Key Importance Of Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Use it as a tool for discussion and navigation on Cybersecurity, Statistics, Importance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
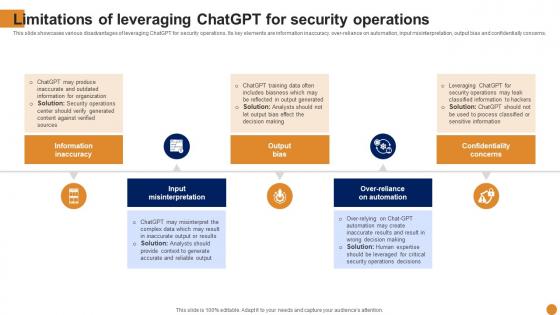 Limitations Of Leveraging Chatgpt Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Limitations Of Leveraging Chatgpt Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various disadvantages of leveraging ChatGPT for security operations. Its key elements are information inaccuracy, over-reliance on automation, input misinterpretation, output bias and confidentially concerns. Introducing Limitations Of Leveraging Chatgpt Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information Inaccuracy, Input Misinterpretation, Confidentiality Concerns, using this template. Grab it now to reap its full benefits.
-
 Openai Chatgpt Usage In Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Openai Chatgpt Usage In Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various use cases of ChatGPT for cybersecurity in organization. Various use cases are incident management, penetration testing, security operations, threat intelligence, vulnerability assessment and security training. Increase audience engagement and knowledge by dispensing information using Openai Chatgpt Usage In Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on six stages. You can also present information on Security Operations, Threat Intelligence, Vulnerability Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Overview And Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview And Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases cybersecurity overview that can help organization to safeguard data from different types of cyber attacks. It also highlights various benefits of cybersecurity such as safeguard data, timely incident response, reduce monetary damage etc. Deliver an outstanding presentation on the topic using this Overview And Cybersecurity Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Dispense information and present a thorough explanation of Organization, Cybersecurity, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
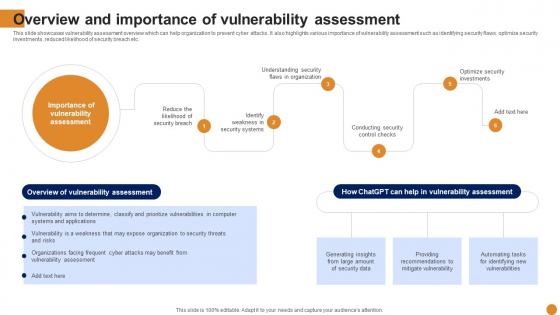 Overview And Importance Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview And Importance Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases vulnerability assessment overview which can help organization to prevent cyber attacks. It also highlights various importance of vulnerability assessment such as identifying security flaws, optimize security investments, reduced likelihood of security breach etc. Present the topic in a bit more detail with this Overview And Importance Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Use it as a tool for discussion and navigation on Vulnerability, Assessment, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
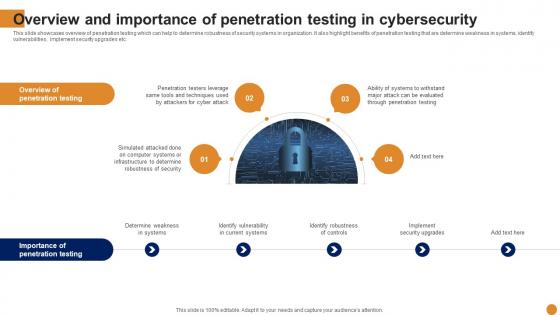 Overview And Importance Of Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview And Importance Of Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases overview of penetration testing which can help to determine robustness of security systems in organization. It also highlight benefits of penetration testing that are determine weakness in systems, identify vulnerabilities, implement security upgrades etc. Increase audience engagement and knowledge by dispensing information using Overview And Importance Of Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on four stages. You can also present information on Overview, Penetration, Cybersecurity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
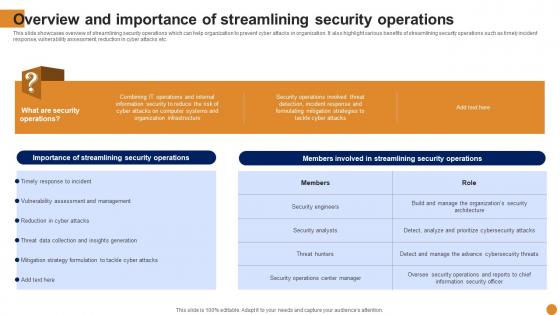 Overview And Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview And Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases overview of streamlining security operations which can help organization to prevent cyber attacks in organization. It also highlight various benefits of streamlining security operations such as timely incident response, vulnerability assessment, reduction in cyber attacks etc. Deliver an outstanding presentation on the topic using this Overview And Security Operations Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Dispense information and present a thorough explanation of Overview, Streamlining, Operations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Overview Cybersecurity Incident Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview Cybersecurity Incident Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases overview of incident management that can help organization in tackling cyber attacks. It also highlights various importance of incident management that are reduction in cyber attacks, decrease in system downtime, improved incident response etc. Present the topic in a bit more detail with this Overview Cybersecurity Incident Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Use it as a tool for discussion and navigation on Management, Overview, Cybersecurity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
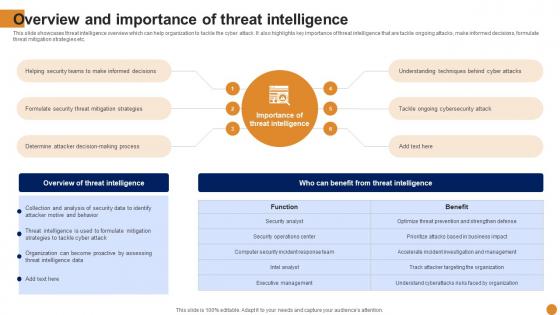 Overview Intelligence Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview Intelligence Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases threat intelligence overview which can help organization to tackle the cyber attack. It also highlights key importance of threat intelligence that are tackle ongoing attacks, make informed decisions, formulate threat mitigation strategies etc. Deliver an outstanding presentation on the topic using this Overview Intelligence Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Dispense information and present a thorough explanation of Overview, Intelligence, Strategies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
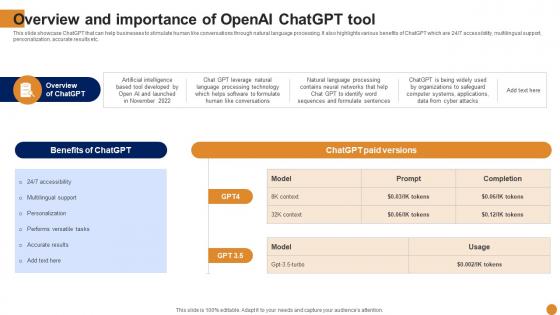 Overview Of Openai Chatgpt Tool Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Overview Of Openai Chatgpt Tool Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcase ChatGPT that can help businesses to stimulate human like conversations through natural language processing. It also highlights various benefits of ChatGPT which are 24 or 7 accessibility, multilingual support, personalization, accurate results etc. Present the topic in a bit more detail with this Overview Of Openai Chatgpt Tool Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Use it as a tool for discussion and navigation on Overview, Organizations, Conversations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
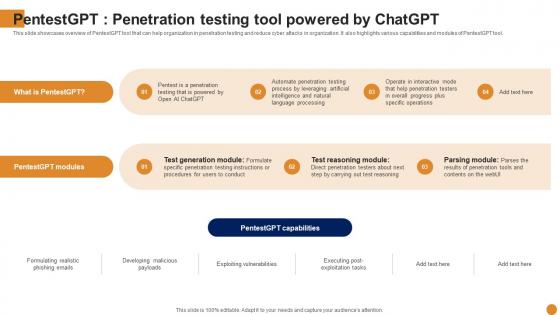 Pentestgpt Penetration Testing Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Pentestgpt Penetration Testing Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases overview of PentestGPT tool that can help organization in penetration testing and reduce cyber attacks in organization. It also highlights various capabilities and modules of PentestGPT tool. Introducing Pentestgpt Penetration Testing Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Penetration, Capabilities, Exploitation, using this template. Grab it now to reap its full benefits.
-
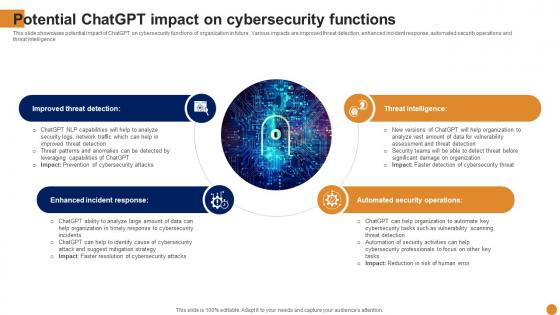 Potential Chatgpt Impact On Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Potential Chatgpt Impact On Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases potential impact of ChatGPT on cybersecurity functions of organization in future. Various impacts are improved threat detection, enhanced incident response, automated security operations and threat intelligence Increase audience engagement and knowledge by dispensing information using Potential Chatgpt Impact On Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on four stages. You can also present information on Improved Threat Detection, Enhanced Incident Response, Threat Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
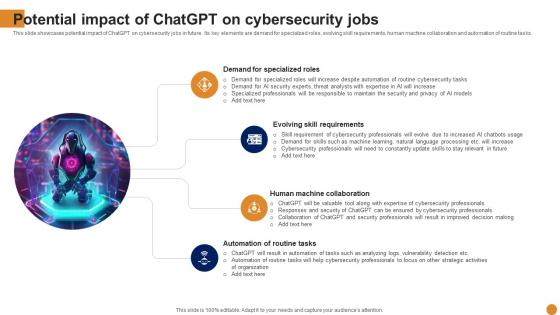 Potential Impact Of Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Potential Impact Of Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases potential impact of ChatGPT on cybersecurity jobs in future. Its key elements are demand for specialized roles, evolving skill requirements, human machine collaboration and automation of routine tasks. Introducing Potential Impact Of Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Demand For Specialized Roles, Evolving Skill Requirements, Human Machine Collaboration, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Table Of Contents Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VIncrease audience engagement and knowledge by dispensing information using Table Of Contents Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on one stages. You can also present information on Vulnerability, Assessment, Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
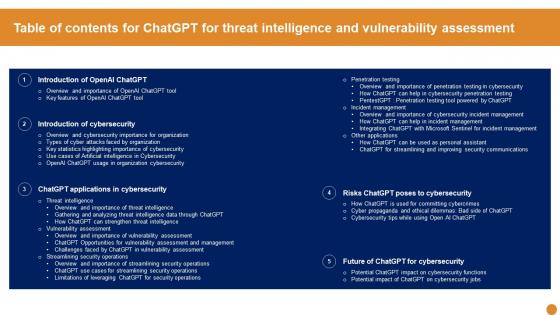 Table Of Contents For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Table Of Contents For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VDeliver an outstanding presentation on the topic using this Table Of Contents For Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Dispense information and present a thorough explanation of Introduction Of Cybersecurity, Applications In Cybersecurity, Vulnerability Assessment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various types of cyber attacks that significantly damage the organization resources and reputation. Different types of attacks faced are Malware, Phishing, Man in middle attack, SQL injection etc. Increase audience engagement and knowledge by dispensing information using Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on five stages. You can also present information on Phishing, SQL Injection, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
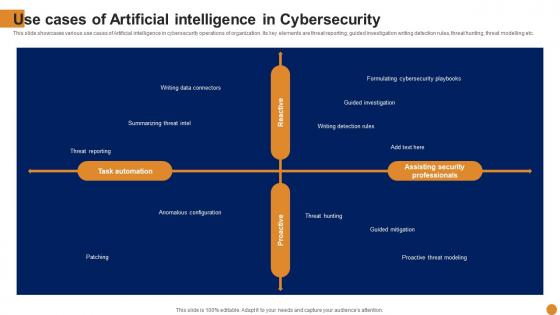 Use Cases Of Artificial Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Use Cases Of Artificial Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various use cases of Artificial intelligence in cybersecurity operations of organization. Its key elements are threat reporting, guided investigation writing detection rules, threat hunting, threat modelling etc. Present the topic in a bit more detail with this Use Cases Of Artificial Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. Use it as a tool for discussion and navigation on Summarizing Threat Intel, Writing Detection Rules, Guided Investigation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
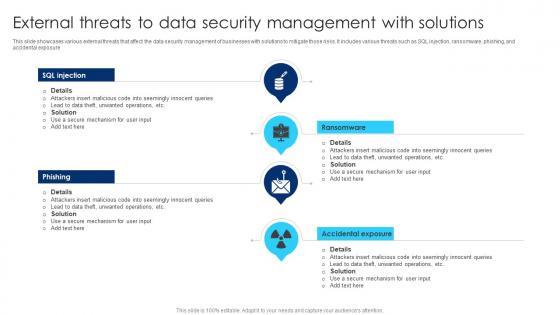 External Threats To Data Security Management With Solutions
External Threats To Data Security Management With SolutionsThis slide showcases various external threats that affect the data security management of businesses with solutions to mitigate those risks. It includes various threats such as SQL injection, ransomware, phishing, and accidental exposure. Introducing our premium set of slides with External Threats To Data Security Management With Solutions. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Accidental Exposure, Unwanted Operations, Secure Mechanism. So download instantly and tailor it with your information.
-
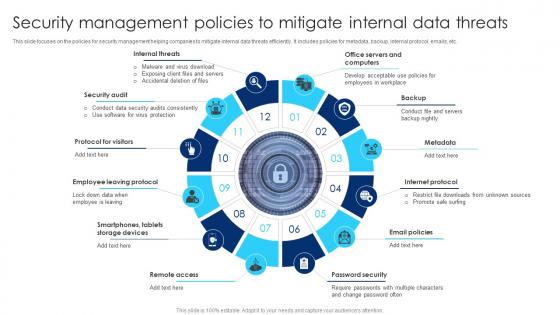 Security Management Policies To Mitigate Internal Data Threats
Security Management Policies To Mitigate Internal Data ThreatsThis slide focuses on the policies for security management helping companies to mitigate internal data threats efficiently. It includes policies for metadata, backup, internal protocol, emails, etc. Introducing our premium set of slides with Security Management Policies To Mitigate Internal Data Threats. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protocol For Visitors, Internet Protocol, Security Audit. So download instantly and tailor it with your information.
-
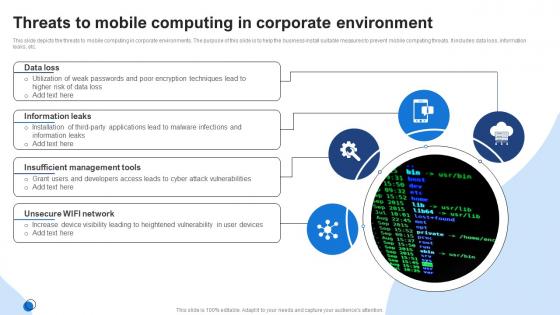 Threats To Mobile Computing In Corporate Environment
Threats To Mobile Computing In Corporate EnvironmentThis slide depicts the threats to mobile computing in corporate environments. The purpose of this slide is to help the business install suitable measures to prevent mobile computing threats. It includes data loss, information leaks, etc. Introducing our premium set of slides with Threats To Mobile Computing In Corporate Environment. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Leaks, Insufficient Management Tools, Unsecure WIFI Network. So download instantly and tailor it with your information.
-
 Impact Of Cyber Security Threats On Organisational Policy
Impact Of Cyber Security Threats On Organisational PolicyThis slide covers the negative impacts of prevalent cybersecurity threats. This template aims to highlight two key negative impacts of threats, including DNS Attacks, SQL Injection, Malware, Phishing, and Ransomware. Presenting our set of slides with Impact Of Cyber Security Threats On Organisational Policy This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware, DNS Attack, SQL Injection
-
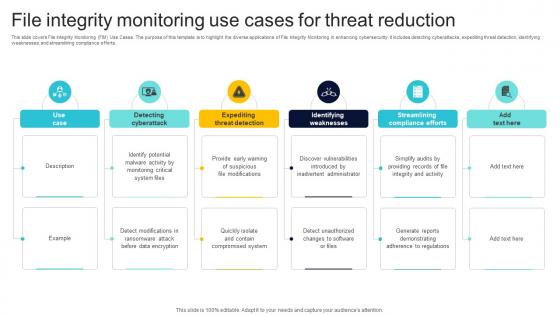 File Integrity Monitoring Use Cases For Threat Reduction
File Integrity Monitoring Use Cases For Threat ReductionThis slide covers File Integrity Monitoring FIM Use Cases. The purpose of this template is to highlight the diverse applications of File Integrity Monitoring in enhancing cybersecurity. It includes detecting cyberattacks, expediting threat detection, identifying weaknesses, and streamlining compliance efforts. Presenting our set of slides with File Integrity Monitoring Use Cases For Threat Reduction This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detecting Cyberattack, Expediting Threat Detection, Identifying Weaknesses



