Powerpoint Templates and Google slides for Vulnerability Cyber Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
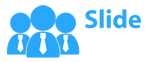
 Threat Identification And Vulnerability Assessment Formulating Cybersecurity Plan
Threat Identification And Vulnerability Assessment Formulating Cybersecurity PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Present the topic in a bit more detail with this Threat Identification And Vulnerability Assessment Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Vulnerability Severity, Threat Source, Likelihood. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Rating For Risk Identification Formulating Cybersecurity Plan
Vulnerability Rating For Risk Identification Formulating Cybersecurity PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. It shows information about severity, vulnerability score and description. Introducing Vulnerability Rating For Risk Identification Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Score, Risk Identification, using this template. Grab it now to reap its full benefits.
-
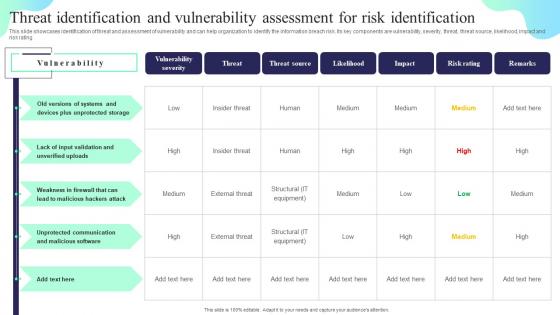
 Addressing The Cyber Incident Logging Process Cybersecurity Incident And Vulnerability
Addressing The Cyber Incident Logging Process Cybersecurity Incident And VulnerabilityThis slide displays logging process for a cyber incident logging. It covers information about process ID, procedure, its description and owner details. Present the topic in a bit more detail with this Addressing The Cyber Incident Logging Process Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on Create New Incident, Complete Incident Details, Category And Priority. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing The Roles And Responsibilities Of Incident Response Cybersecurity Incident And Vulnerability
Addressing The Roles And Responsibilities Of Incident Response Cybersecurity Incident And VulnerabilityThis slide provides information about various roles and responsibilities of incident response team to effectively identify, report and take accurate measures against any cyber incident. Introducing Addressing The Roles And Responsibilities Of Incident Response Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Incident First Response Team, Steering Committee, Cyber Incident Response Team, using this template. Grab it now to reap its full benefits.
-
 Addressing The Various Security Incidents And Attacks Cybersecurity Incident And Vulnerability
Addressing The Various Security Incidents And Attacks Cybersecurity Incident And VulnerabilityPurpose of this slide is to educate team members about different security incidents and attacks. It includes information about traditional security incidents, cyber security attacks and common techniques. Increase audience engagement and knowledge by dispensing information using Addressing The Various Security Incidents And Attacks Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Traditional IT Security Incidents, Cyber Security Attacks, Common Techniques using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
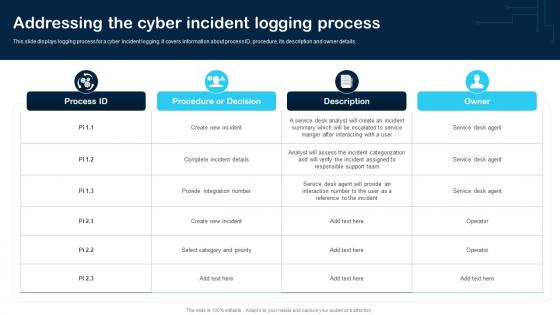
 Asset Criticality Of Identified System Components Cybersecurity Incident And Vulnerability
Asset Criticality Of Identified System Components Cybersecurity Incident And VulnerabilityMentioned slide demonstrates the asset criticality of identified system components. It includes information of system name, component used, impact rating, criticality rating and failure cost. Deliver an outstanding presentation on the topic using this Asset Criticality Of Identified System Components Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Host Computers, SCADA Software, Field Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
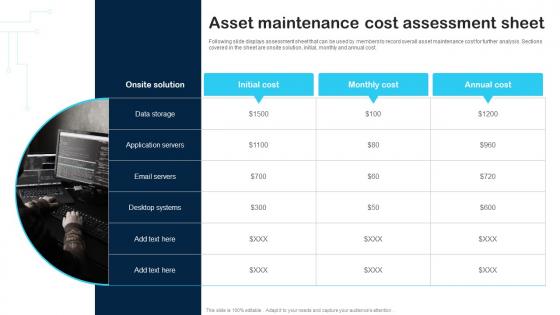 Asset Maintenance Cost Assessment Sheet Cybersecurity Incident And Vulnerability
Asset Maintenance Cost Assessment Sheet Cybersecurity Incident And VulnerabilityFollowing slide displays assessment sheet that can be used by members to record overall asset maintenance cost for further analysis. Sections covered in the sheet are onsite solution, initial, monthly and annual cost. Introducing Asset Maintenance Cost Assessment Sheet Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Data Storage, Application Servers, Email Servers, using this template. Grab it now to reap its full benefits.
-
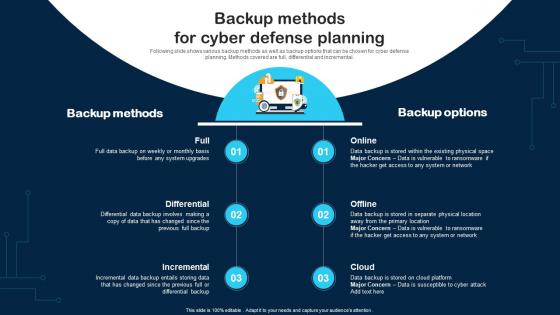 Backup Methods For Cyber Defense Planning Cybersecurity Incident And Vulnerability
Backup Methods For Cyber Defense Planning Cybersecurity Incident And VulnerabilityFollowing slide shows various backup methods as well as backup options that can be chosen for cyber defense planning. Methods covered are full, differential and incremental. Increase audience engagement and knowledge by dispensing information using Backup Methods For Cyber Defense Planning Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Backup Methods, Backup Options, Incremental using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Work From Home Data Security Practices Cybersecurity Incident And Vulnerability
Best Work From Home Data Security Practices Cybersecurity Incident And VulnerabilityPurpose of this slide is to provide information about the best data security practices that can be followed by employees who are working from home. Practices covered are configure WIFI encryption, avoid external devices, system update etc. Introducing Best Work From Home Data Security Practices Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Configure WIFI Encryption, Avoid Using External Devices, System Update, using this template. Grab it now to reap its full benefits.
-
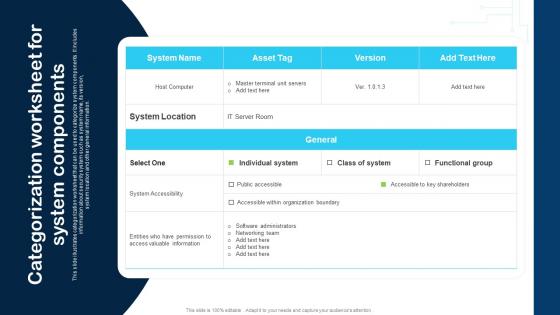 Categorization Worksheet For System Components Cybersecurity Incident And Vulnerability
Categorization Worksheet For System Components Cybersecurity Incident And VulnerabilityThis slide illustrates categorization worksheet that can be used to categorize system components. It includes information about security system such as system name, its version, system location and other general information. Present the topic in a bit more detail with this Categorization Worksheet For System Components Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on System Location, System Accessibility, IT Server Room. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
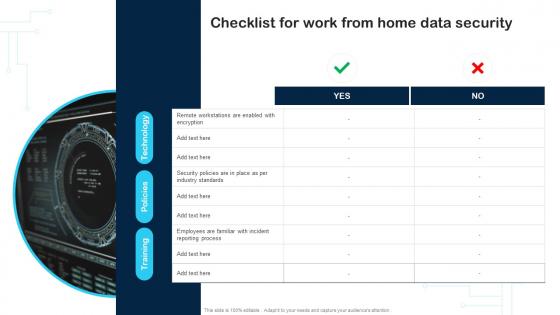 Checklist For Work From Home Data Security Cybersecurity Incident And Vulnerability
Checklist For Work From Home Data Security Cybersecurity Incident And VulnerabilityDeliver an outstanding presentation on the topic using this Checklist For Work From Home Data Security Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Data Security, Reporting Process, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability
Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And VulnerabilityFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Email, Mobile Devices, using this template. Grab it now to reap its full benefits.
-
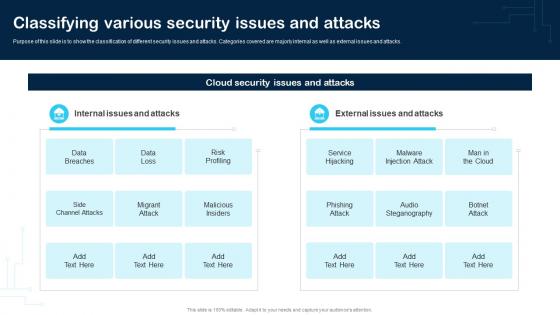 Classifying Various Security Issues And Attacks Cybersecurity Incident And Vulnerability
Classifying Various Security Issues And Attacks Cybersecurity Incident And VulnerabilityPurpose of this slide is to show the classification of different security issues and attacks. Categories covered are majorly internal as well as external issues and attacks. Present the topic in a bit more detail with this Classifying Various Security Issues And Attacks Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on Data Breaches, Data Loss, Risk Profiling. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Communication Plan For Effective Incident Management Cybersecurity Incident And Vulnerability
Communication Plan For Effective Incident Management Cybersecurity Incident And VulnerabilityThis slide portrays communication plan for successfully managing cyber incidents. Sections covered are deliverable info, recipient, delivery method, schedule and responsible person. Introducing Communication Plan For Effective Incident Management Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Delivery Method, Incident Information, Team Meetings, using this template. Grab it now to reap its full benefits.
-
 Comparison Cybersecurity Incident And Vulnerability Response Playbook
Comparison Cybersecurity Incident And Vulnerability Response PlaybookIncrease audience engagement and knowledge by dispensing information using Comparison Cybersecurity Incident And Vulnerability Response Playbook. This template helps you present information on two stages. You can also present information on Comparison using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Awareness Training Program Cybersecurity Incident And Vulnerability
Cyber Security Awareness Training Program Cybersecurity Incident And VulnerabilityPurpose of this slide is to provide information about the cyber security awareness training program to be conducted for in house team. It also provides the details about training types, content types and audience. Present the topic in a bit more detail with this Cyber Security Awareness Training Program Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on Policy Based, Industry Specific Content, Generic Security Awareness. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
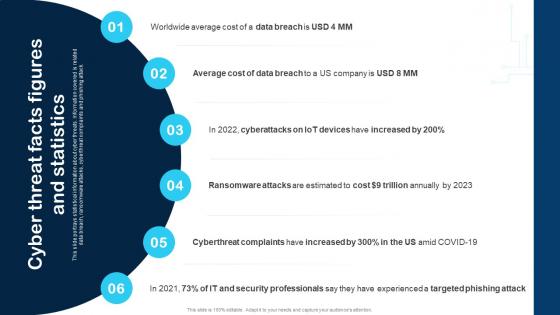 Cyber Threat Facts Figures And Statistics Cybersecurity Incident And Vulnerability
Cyber Threat Facts Figures And Statistics Cybersecurity Incident And VulnerabilityThis slide portrays statistical information about cyber threats. Information covered is related data breach, ransomware attacks, cyberthreat complaints and phishing attack. Increase audience engagement and knowledge by dispensing information using Cyber Threat Facts Figures And Statistics Cybersecurity Incident And Vulnerability. This template helps you present information on six stages. You can also present information on Data Breach, Cost, Security Professionals using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cybersecurity Incident and Vulnerability Response Playbook Table Of Contents
Cybersecurity Incident and Vulnerability Response Playbook Table Of ContentsDeliver an outstanding presentation on the topic using this Cybersecurity Incident and Vulnerability Response Playbook Table Of Contents. Dispense information and present a thorough explanation of Response Approach, Response Team, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
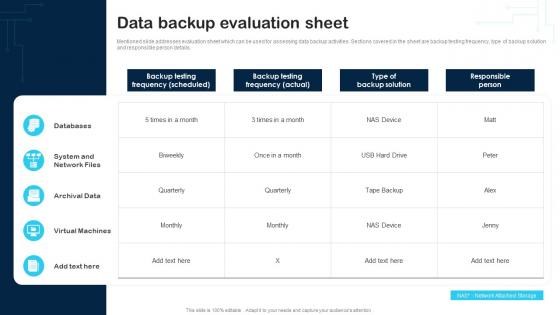 Data Backup Evaluation Sheet Cybersecurity Incident And Vulnerability Response Playbook
Data Backup Evaluation Sheet Cybersecurity Incident And Vulnerability Response PlaybookMentioned slide addresses evaluation sheet which can be used for assessing data backup activities. Sections covered in the sheet are backup testing frequency, type of backup solution and responsible person details. Present the topic in a bit more detail with this Data Backup Evaluation Sheet Cybersecurity Incident And Vulnerability Response Playbook. Use it as a tool for discussion and navigation on Databases, System And Network Files, Archival Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Financial Cybersecurity Incident And Vulnerability Response Playbook
Financial Cybersecurity Incident And Vulnerability Response PlaybookIntroducing Financial Cybersecurity Incident And Vulnerability Response Playbook to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Financial, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Cybersecurity Incident And Vulnerability Response Playbook
Icons Slide For Cybersecurity Incident And Vulnerability Response PlaybookPresent the topic in a bit more detail with this Icons Slide For Cybersecurity Incident And Vulnerability Response Playbook. Use it as a tool for discussion and navigation on Icons Slide. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Idea Generation Cybersecurity Incident And Vulnerability Response Playbook
Idea Generation Cybersecurity Incident And Vulnerability Response PlaybookIncrease audience engagement and knowledge by dispensing information using Idea Generation Cybersecurity Incident And Vulnerability Response Playbook. This template helps you present information on five stages. You can also present information on Idea Generation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
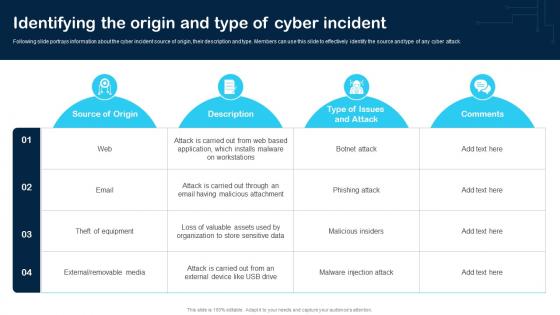 Identifying The Origin And Type Of Cyber Incident Cybersecurity Incident And Vulnerability
Identifying The Origin And Type Of Cyber Incident Cybersecurity Incident And VulnerabilityFollowing slide portrays information about the cyber incident source of origin, their description and type. Members can use this slide to effectively identify the source and type of any cyber attack. Deliver an outstanding presentation on the topic using this Identifying The Origin And Type Of Cyber Incident Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Web, Email, Removable Media using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
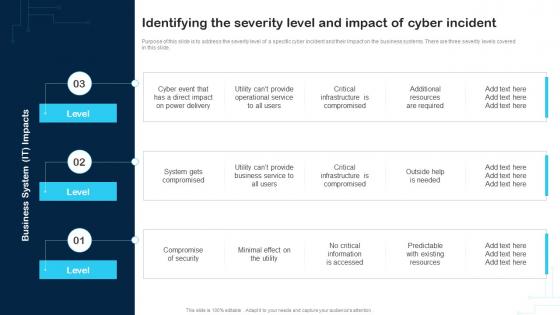 Identifying The Severity Level And Impact Of Cyber Incident Cybersecurity Incident And Vulnerability
Identifying The Severity Level And Impact Of Cyber Incident Cybersecurity Incident And VulnerabilityPurpose of this slide is to address the severity level of a specific cyber incident and their impact on the business systems. There are three severity levels covered in this slide. Introducing Identifying The Severity Level And Impact Of Cyber Incident Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Compromise Of Security, Service, Business System, using this template. Grab it now to reap its full benefits.
-
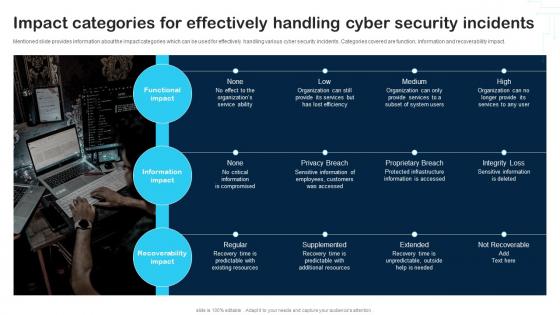 Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability
Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And VulnerabilityMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Incident Management Workflow Cybersecurity Incident And Vulnerability Response Playbook
Incident Management Workflow Cybersecurity Incident And Vulnerability Response PlaybookPresent the topic in a bit more detail with this Incident Management Workflow Cybersecurity Incident And Vulnerability Response Playbook. Use it as a tool for discussion and navigation on Incident Occurs, Team Takes Action, Organize Your Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
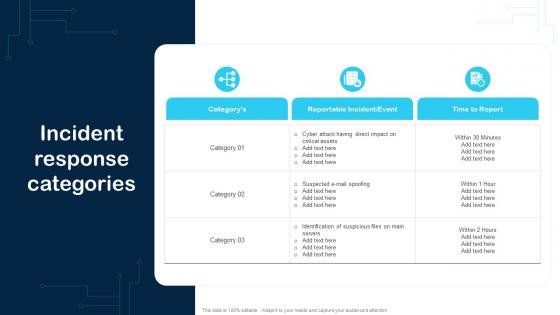 Incident Response Categories Cybersecurity Incident And Vulnerability Response Playbook
Incident Response Categories Cybersecurity Incident And Vulnerability Response PlaybookDeliver an outstanding presentation on the topic using this Incident Response Categories Cybersecurity Incident And Vulnerability Response Playbook. Dispense information and present a thorough explanation of Event, Reportable Incident, Category using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Meet Are Awesome Team Cybersecurity Incident And Vulnerability Response Playbook
Meet Are Awesome Team Cybersecurity Incident And Vulnerability Response PlaybookIntroducing Meet Are Awesome Team Cybersecurity Incident And Vulnerability Response Playbook to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Meet Are Awesome Team, using this template. Grab it now to reap its full benefits.
-
 Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And Vulnerability
Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And VulnerabilityPurpose of this slide is to address and perform various cyber training exercises in order to secure companys assets. Exercises covered are defense in depth, capture the flag etc. Deliver an outstanding presentation on the topic using this Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Capture The Flag Event, Training, System Administrator using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
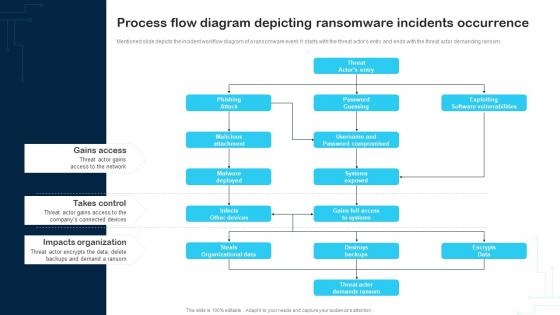 Process Flow Diagram Depicting Ransomware Incidents Occurrence Cybersecurity Incident And Vulnerability
Process Flow Diagram Depicting Ransomware Incidents Occurrence Cybersecurity Incident And VulnerabilityMentioned slide depicts the incident workflow diagram of a ransomware event. It starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Process Flow Diagram Depicting Ransomware Incidents Occurrence Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Gains Access, Takes Control, Impacts Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Purpose Of Cybersecurity Incident And Vulnerability Response Playbook
Purpose Of Cybersecurity Incident And Vulnerability Response PlaybookIntroducing Purpose Of Cybersecurity Incident And Vulnerability Response Playbook to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity, Playbook, Vulnerability Response, using this template. Grab it now to reap its full benefits.
-
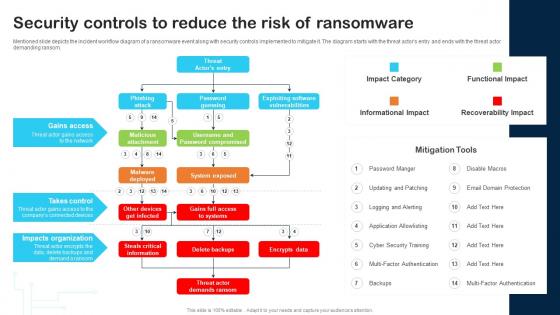 Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability
Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And VulnerabilityMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Gains Access, Takes Control, Impacts Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Swot Analysis Cybersecurity Incident And Vulnerability Response Playbook
Swot Analysis Cybersecurity Incident And Vulnerability Response PlaybookIntroducing v to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weaknesses, Opportunities, using this template. Grab it now to reap its full benefits.
-
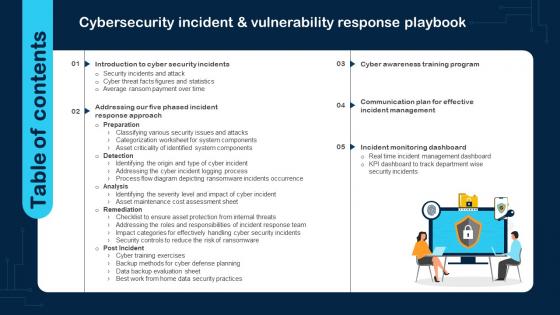 Table Of Contents Cybersecurity Incident And Vulnerability Response Playbook
Table Of Contents Cybersecurity Incident And Vulnerability Response PlaybookPresent the topic in a bit more detail with this Table Of Contents Cybersecurity Incident And Vulnerability Response Playbook. Use it as a tool for discussion and navigation on Cyber Security Incidents, Response Approach, Training Program. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Venn Diagram Cybersecurity Incident And Vulnerability Response Playbook
Venn Diagram Cybersecurity Incident And Vulnerability Response PlaybookIntroducing Venn Diagram Cybersecurity Incident And Vulnerability Response Playbook to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Venn Diagram, using this template. Grab it now to reap its full benefits.
-
 Vulnerability Cybersecurity In Powerpoint And Google Slides Cpb
Vulnerability Cybersecurity In Powerpoint And Google Slides CpbPresenting our Vulnerability Cybersecurity In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases eight stages. It is useful to share insightful information on Vulnerability Cybersecurity This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
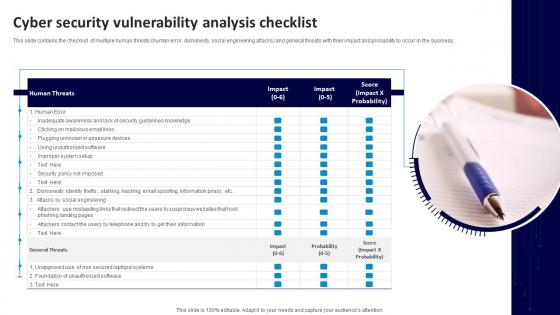 Cyber Security Vulnerability Analysis Checklist
Cyber Security Vulnerability Analysis ChecklistThis slide contains the checklist of multiple human threats human error, dishonesty, social engineering attacks and general threats with their impact and probability to occur in the business. Introducing our premium set of slides with Cyber Security Vulnerability Analysis Checklist. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Human Threats, General Threats, Unsecure Devices. So download instantly and tailor it with your information.
-
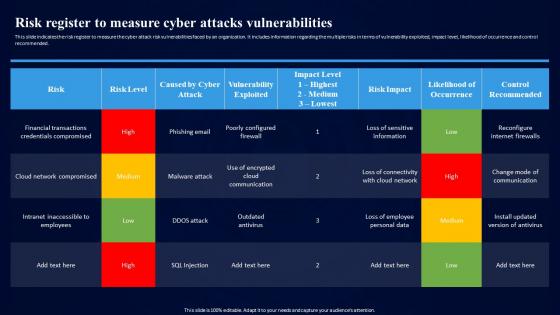 Cybersecurity Risk Assessment Program Risk Register To Measure Cyber Attacks Vulnerabilities
Cybersecurity Risk Assessment Program Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cyber Attacks, Vulnerabilities, Cloud Network Compromised, Outdated Antivirus. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Vulnerability In Powerpoint And Google Slides Cpb
Cyber Security Vulnerability In Powerpoint And Google Slides CpbPresenting our Cyber Security Vulnerability In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Security Vulnerability This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
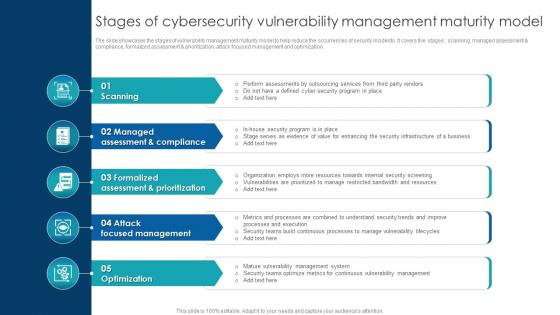 Stages Of Cybersecurity Vulnerability Management Maturity Model
Stages Of Cybersecurity Vulnerability Management Maturity ModelThe slide showcases the stages of vulnerability management maturity model to help reduce the occurrences of security incidents. It covers five stages scanning, managed assessment compliance, formalized assessment prioritization, attack focused management and optimization.Presenting our set of slides with Stages Of Cybersecurity Vulnerability Management Maturity Model. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Initiatives, Assess Current Inventory, Record Desired Security.
-
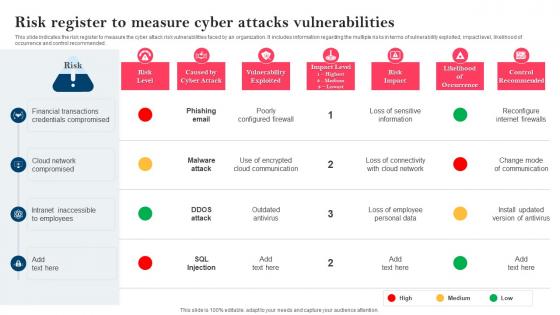 Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities
Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities. Dispense information and present a thorough explanation of Financial Transactions, Credentials Compromised, Cloud Network Compromised using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Reputational management organizational design methodology cyber vulnerability assessment cpb
Reputational management organizational design methodology cyber vulnerability assessment cpbPresenting this set of slides with name - Reputational Management Organizational Design Methodology Cyber Vulnerability Assessment Cpb. This is an editable three stages graphic that deals with topics like Reputational Management, Organizational Design Methodology, Cyber Vulnerability Assessment to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber database security issues vulnerabilities ppt powerpoint presentation outline ideas cpb
Cyber database security issues vulnerabilities ppt powerpoint presentation outline ideas cpbPresenting this set of slides with name Cyber Database Security Issues Vulnerabilities Ppt Powerpoint Presentation Outline Ideas Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Database Security Issues Vulnerabilities to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
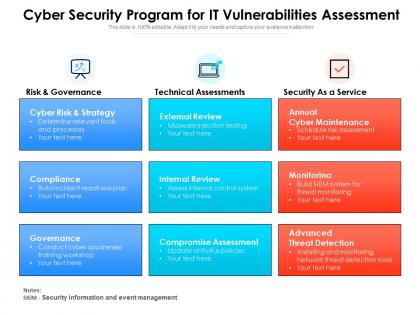 Cyber security program for it vulnerabilities assessment
Cyber security program for it vulnerabilities assessmentPresenting this set of slides with name Cyber Security Program For It Vulnerabilities Assessment. This is a three stage process. The stages in this process are Risk And Governance, Technical Assessments, Security As A Service. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Scanning system for vulnerability to cyber attack
Scanning system for vulnerability to cyber attackPresenting this set of slides with name Scanning System For Vulnerability To Cyber Attack. This is a three stage process. The stages in this process are Scanning System For Vulnerability To Cyber Attack. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 System vulnerability scanning for potential cyber attack
System vulnerability scanning for potential cyber attackPresenting this set of slides with name System Vulnerability Scanning For Potential Cyber Attack. This is a three stage process. The stages in this process are System Vulnerability Scanning For Potential Cyber Attack. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
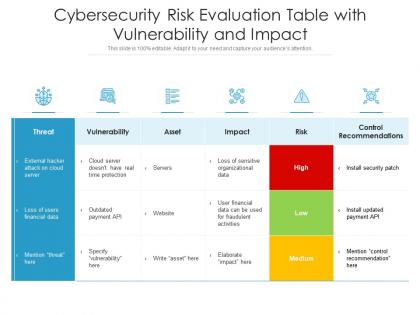 Cybersecurity risk evaluation table with vulnerability and impact
Cybersecurity risk evaluation table with vulnerability and impactPresenting our well-structured Cybersecurity Risk Evaluation Table With Vulnerability And Impact. The topics discussed in this slide are Threat, Vulnerability, Asset, Risk, Recommendations. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.