Powerpoint Templates and Google slides for Vulnerability
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
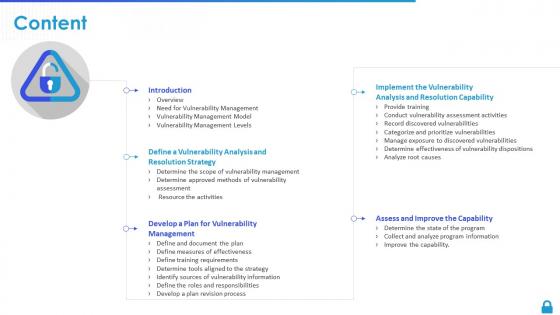 Enterprise vulnerability management content
Enterprise vulnerability management contentPresent the topic in a bit more detail with this Enterprise Vulnerability Management Content Use it as a tool for discussion and navigation on Introduction, Resolution Strategy, Vulnerability Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
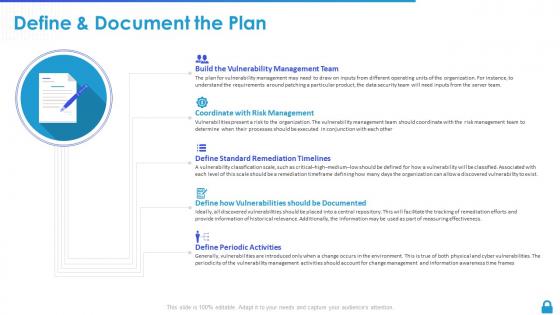 Enterprise vulnerability management define and document the plan
Enterprise vulnerability management define and document the planIntroducing Enterprise Vulnerability Management Define And Document The Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Coordinate With Risk Management, Standard Remediation Timelines, Vulnerabilities Should, using this template. Grab it now to reap its full benefits.
-
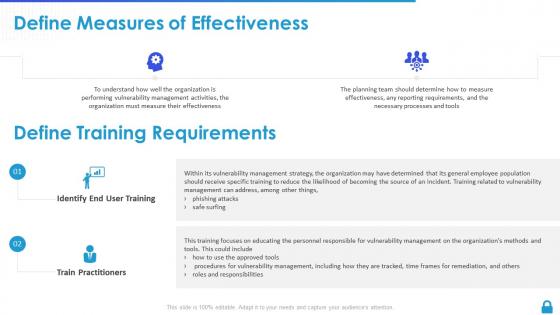 Enterprise vulnerability management define measures of effectiveness
Enterprise vulnerability management define measures of effectivenessIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Define Measures Of Effectiveness. This template helps you present information on two stages. You can also present information on Identify End User Training, Train Practitioners, Define Training Requirements using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
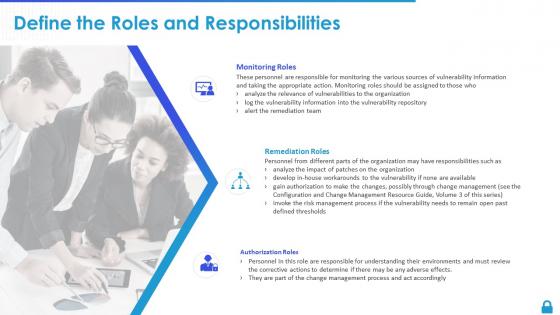 Enterprise vulnerability management define the roles and responsibilities
Enterprise vulnerability management define the roles and responsibilitiesIntroducing Enterprise Vulnerability Management Define The Roles And Responsibilities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Monitoring Roles, Remediation Roles, Authorization Roles, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management determine approved methods of vulnerability assessment
Enterprise vulnerability management determine approved methods of vulnerability assessmentIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Determine Approved Methods Of Vulnerability Assessment. This template helps you present information on four stages. You can also present information on Required By Regulation, Operational Requirements, Determine The Legal Implications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management determine effectiveness of vulnerability dispositions
Enterprise vulnerability management determine effectiveness of vulnerability dispositionsIntroducing Enterprise Vulnerability Management Determine Effectiveness Of Vulnerability Dispositions to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Evaluate Disposition Efforts, Update Vulnerability Repository, Repeat Disposition, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management determine the scope of vulnerability management
Enterprise vulnerability management determine the scope of vulnerability managementIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Determine The Scope Of Vulnerability Management. This template helps you present information on two stages. You can also present information on Document The Candidate, Determine The Operational, Analysis And Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management determine the state of the program
Enterprise vulnerability management determine the state of the programIntroducing Enterprise Vulnerability Management Determine The State Of The Program to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Relevant Stakeholders, Appropriate Work Products, Process Provides, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management determine tools aligned to the strategy
Enterprise vulnerability management determine tools aligned to the strategyIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Determine Tools Aligned To The Strategy. This template helps you present information on five stages. You can also present information on Publish Authorized, Exception Process, Conduct Periodic Reviews using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management develop a plan revision process
Enterprise vulnerability management develop a plan revision processIntroducing Enterprise Vulnerability Management Develop A Plan Revision Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Review The Changes, Vulnerability Information, Update Toolset If Necessary, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management icons slide
Enterprise vulnerability management icons slideIntroducing our well researched set of slides titled Enterprise Vulnerability Management Icons Slide. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
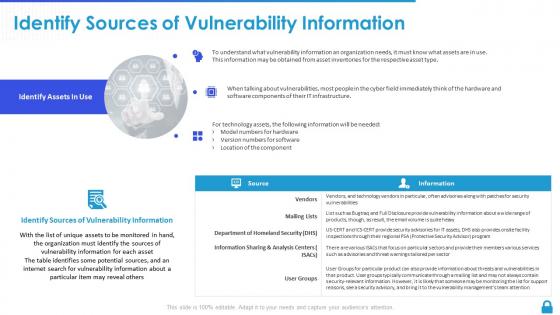 Enterprise vulnerability management identify sources of vulnerability information
Enterprise vulnerability management identify sources of vulnerability informationDeliver an outstanding presentation on the topic using this Enterprise Vulnerability Management Identify Sources Of Vulnerability Information. Dispense information and present a thorough explanation of Location Of The Component, Vulnerability Information, Vulnerability Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
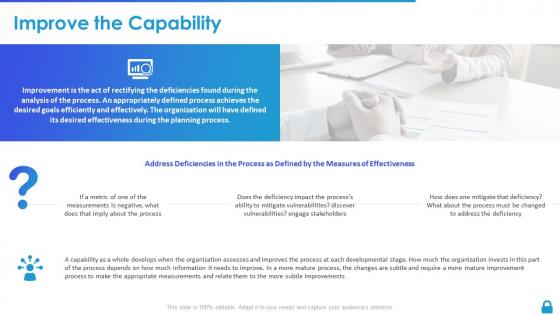 Enterprise vulnerability management improve the capability
Enterprise vulnerability management improve the capabilityIntroducing Enterprise Vulnerability Management Improve The Capability to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Deficiencies In The Pro, Measures Of Effectiveness, Measurements Is Negative, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management manage exposure to discovered vulnerabilities
Enterprise vulnerability management manage exposure to discovered vulnerabilitiesIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Manage Exposure To Discovered Vulnerabilities This template helps you present information on four stages. You can also present information on Test Disposition, Deploy Disposition Method, Track To Resolution using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management need for vulnerability management
Enterprise vulnerability management need for vulnerability managementIntroducing Enterprise Vulnerability Management Need For Vulnerability Management to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Detective And Responsive, Responsive Controls, Preventative Approaches, using this template. Grab it now to reap its full benefits.
-
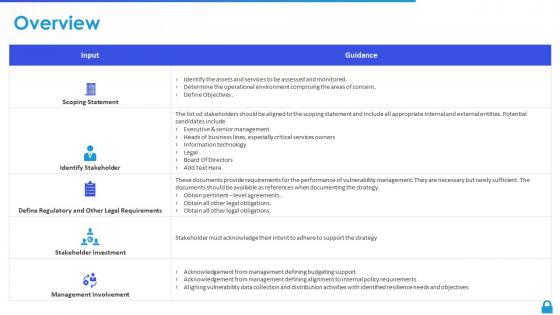 Enterprise vulnerability management overview assets
Enterprise vulnerability management overview assetsIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Overview Assets This template helps you present information on five stages. You can also present information on Identify Stakeholder, Scoping Statement, Management Involvement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management overview list
Enterprise vulnerability management overview listIntroducing Enterprise Vulnerability Management Overview List to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management Support, Vulnerability Management, Vulnerability Management Strategy, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management provide training
Enterprise vulnerability management provide trainingIntroducing Enterprise Vulnerability Management Provide Training to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Personnel On The Process, Train Personnel, Perform Them According, using this template. Grab it now to reap its full benefits.
-
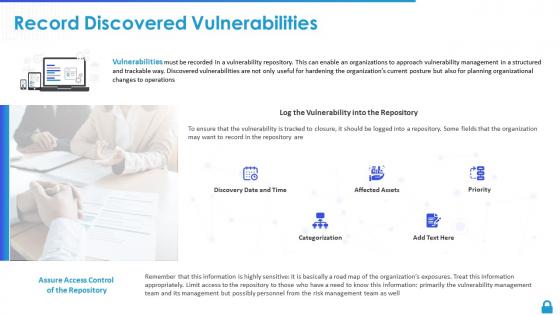 Enterprise vulnerability management record discovered vulnerabilities
Enterprise vulnerability management record discovered vulnerabilitiesIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Record Discovered Vulnerabilities. This template helps you present information on five stages. You can also present information on Management Should Understand, Perform Them According, Personnel Need To Understand using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
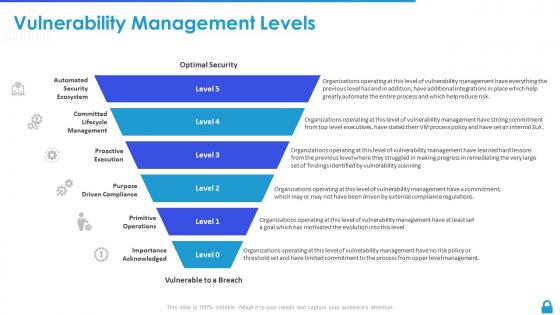 Enterprise vulnerability management vulnerability management levels
Enterprise vulnerability management vulnerability management levelsIntroducing Enterprise Vulnerability Management Vulnerability Management Levels to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Categorization, Affected Assets, Discovery Date And Time, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management vulnerability management model
Enterprise vulnerability management vulnerability management modelIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Vulnerability Management Model. This template helps you present information on five stages. You can also present information on Proactive Execution, Purpose Driven Compliance, Primitive Operations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
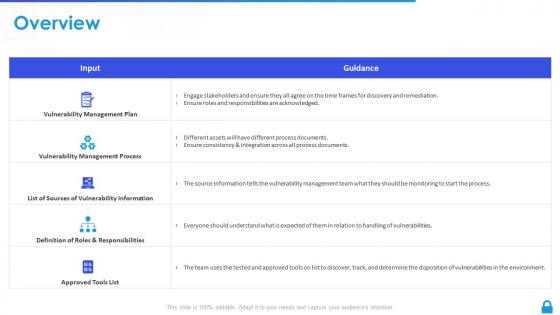 Enterprise vulnerability management overview plan
Enterprise vulnerability management overview planIntroducing Enterprise Vulnerability Management Overview Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Management, Vulnerability Information, Definition Of Roles And Responsibilities, using this template. Grab it now to reap its full benefits.
-
 Enterprise vulnerability management overview program
Enterprise vulnerability management overview programIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Overview Program. This template helps you present information on four stages. You can also present information on Identified Stakeholders, Vulnerability Management, Established Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Overview enterprise vulnerability management
Overview enterprise vulnerability managementIntroducing Overview Enterprise Vulnerability Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Thousands Of Vulnerabilities, Vulnerability Mana, Elements Connected, using this template. Grab it now to reap its full benefits.
-
 Risk threat vulnerability matrix ppt powerpoint presentation icon aids cpb
Risk threat vulnerability matrix ppt powerpoint presentation icon aids cpbPresenting Risk Threat Vulnerability Matrix Ppt Powerpoint Presentation Icon Aids Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Risk Threat Vulnerability Matrix. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
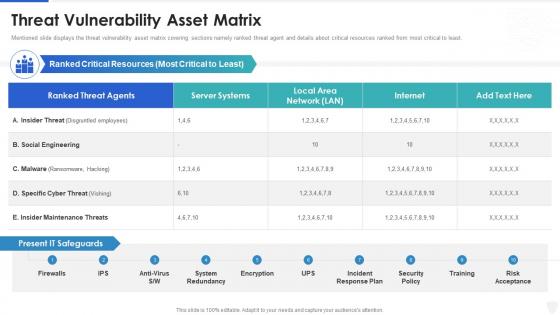 Cybersecurity and digital business risk management threat vulnerability asset matrix
Cybersecurity and digital business risk management threat vulnerability asset matrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Cybersecurity And Digital Business Risk Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
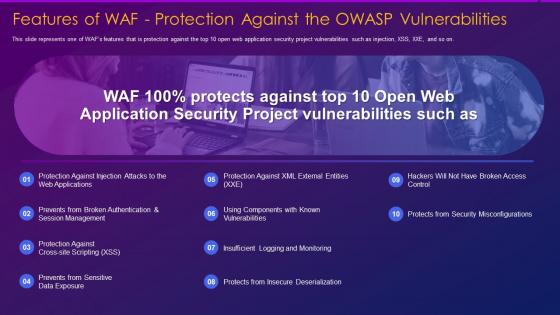 Web application firewall features waf protection against owasp vulnerabilities
Web application firewall features waf protection against owasp vulnerabilitiesThis slide represents one of WAFs features that is protection against the top 10 open web application security project vulnerabilities such as injection, XSS, XXE, and so on. Introducing Web Application Firewall Features Waf Protection Against Owasp Vulnerabilities to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerabilities, Management, Deserialization, using this template. Grab it now to reap its full benefits.
-
 Prioritizing vulnerability remediation ppt powerpoint presentation summary objects cpb
Prioritizing vulnerability remediation ppt powerpoint presentation summary objects cpbPresenting Prioritizing Vulnerability Remediation Ppt Powerpoint Presentation Summary Objects Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Paid Social Manager Salary. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Managing threats vulnerabilities ppt powerpoint presentation layouts elements cpb
Managing threats vulnerabilities ppt powerpoint presentation layouts elements cpbPresenting our Managing Threats Vulnerabilities Ppt Powerpoint Presentation Layouts Elements Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Managing Threats Vulnerabilities This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
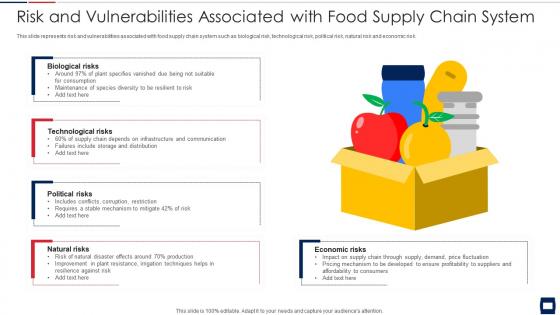 Risk and vulnerabilities associated with food supply chain system
Risk and vulnerabilities associated with food supply chain systemIntroducing our Risk And Vulnerabilities Associated With Food Supply Chain System set of slides. The topics discussed in these slides are Biological Risks, Technological Risks, Political Risks. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan
Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Vulnerability Severity, Threat Source, Risk Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Rating For Risk Identification Information System Security And Risk Administration Plan
Vulnerability Rating For Risk Identification Information System Security And Risk Administration PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. Its shows information about severity, vulnerability score and description. Increase audience engagement and knowledge by dispensing information using Vulnerability Rating For Risk Identification Information System Security And Risk Administration Plan. This template helps you present information on one stages. You can also present information on Severity, Vulnerability Score, Vulnerability Rating using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
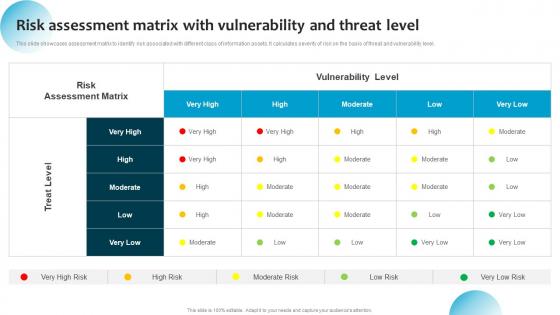 Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat Level
Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat LevelThis slide showcases assessment matrix to identify risk associated with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level. Present the topic in a bit more detail with this Information System Security And Risk Administration Risk Assessment Matrix With Vulnerability And Threat Level. Use it as a tool for discussion and navigation on Treat Level, Vulnerability Level, Risk Assessment Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerable Populations Examples In Powerpoint And Google Slides Cpb
Vulnerable Populations Examples In Powerpoint And Google Slides CpbPresenting our Vulnerable Populations Examples In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Vulnerable Populations Examples. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cybersecurity Risk Analysis And Management Plan Risk Assessment Matrix With Vulnerability And Threat
Cybersecurity Risk Analysis And Management Plan Risk Assessment Matrix With Vulnerability And ThreatThis slide showcases assessment matrix to identify risk associated with different class of information assets. It calculates severity of risk on the basis of threat and vulnerability level Deliver an outstanding presentation on the topic using this Cybersecurity Risk Analysis And Management Plan Risk Assessment Matrix With Vulnerability And Threat. Dispense information and present a thorough explanation of Assessment, Vulnerability, Threat Level using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
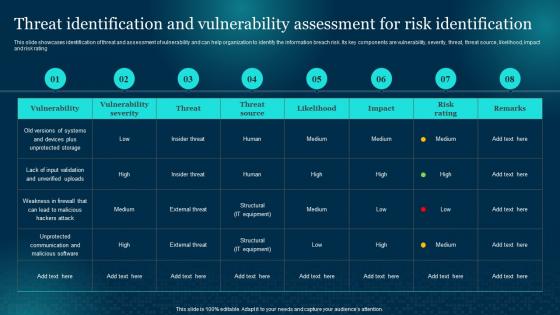 Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management Plan
Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Identification, Assessment, Vulnerability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
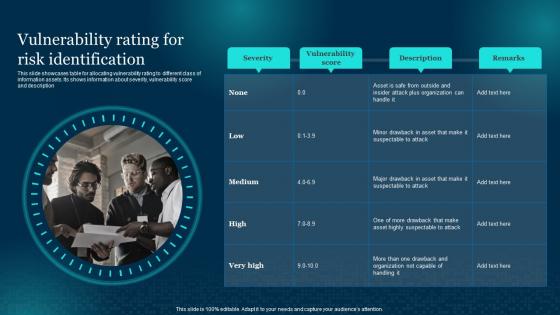 Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management Plan
Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. Its shows information about severity, vulnerability score and description Deliver an outstanding presentation on the topic using this Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Vulnerability, Identification, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Environment Vulnerability Assessment In Powerpoint And Google Slides Cpb
Cyber Security Environment Vulnerability Assessment In Powerpoint And Google Slides CpbPresenting our Cyber Security Environment Vulnerability Assessment In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases eight stages. It is useful to share insightful information on Cyber Security Environment Vulnerability Assessment. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
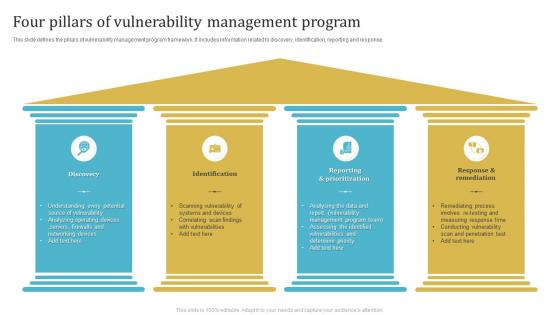 Four Pillars Of Vulnerability Management Program
Four Pillars Of Vulnerability Management ProgramThis slide defines the pillars of vulnerability management program framework. It includes information related to discovery, identification, reporting and response. Presenting our set of slides with Four Pillars Of Vulnerability Management Program. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identification, Reporting And Prioritization, Response And Remediation.
-
 Icon For Vulnerability Management Software Program
Icon For Vulnerability Management Software ProgramIntroducing our premium set of slides with Icon For Vulnerability Management Software Program. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon For Vulnerability, Management Software Program. So download instantly and tailor it with your information.
-
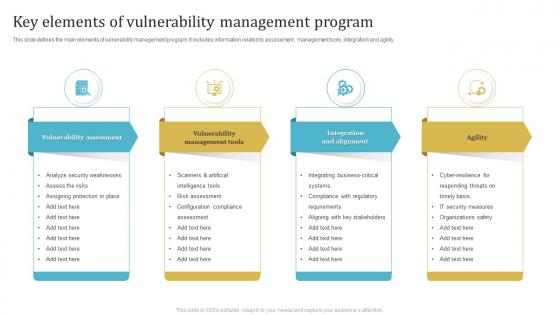 Key Elements Of Vulnerability Management Program
Key Elements Of Vulnerability Management ProgramThis slide defines the main elements of vulnerability management program. It includes information related to assessment, management tools, integration and agility. Presenting our set of slides with Key Elements Of Vulnerability Management Program. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerability Assessment, Vulnerability Management Tools, Integration And Alignment .
-
 Planning Vulnerability Management Program Icon
Planning Vulnerability Management Program IconIntroducing our premium set of slides with Planning Vulnerability Management Program Icon. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Planning Vulnerability, Management Program Icon. So download instantly and tailor it with your information.
-
 Technological Components For Vulnerability Management Program
Technological Components For Vulnerability Management ProgramThis slide defines the technological components used for creating vulnerability management programs. It includes information related to assessment, process, software development, automation and reporting. Presenting our set of slides with Technological Components For Vulnerability Management Program. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerability Assessment, Reporting, Systematic Process.
-
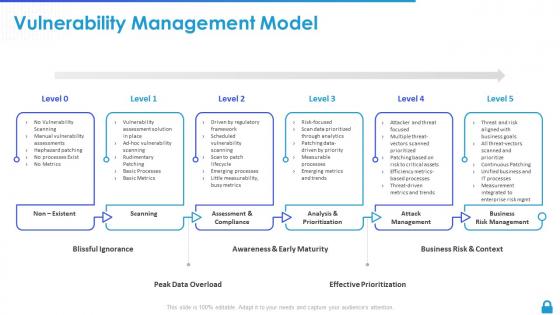
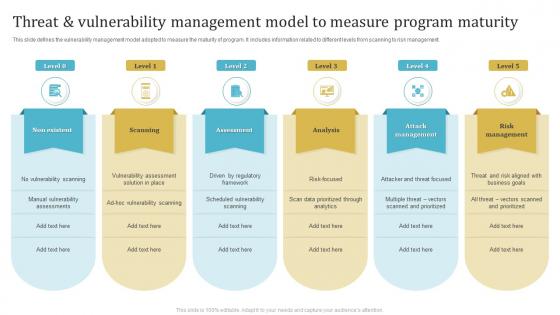 Threat And Vulnerability Management Model To Measure Program Maturity
Threat And Vulnerability Management Model To Measure Program MaturityThis slide defines the vulnerability management model adopted to measure the maturity of program. It includes information related to different levels from scanning to risk management. Introducing our premium set of slides with Threat And Vulnerability Management Model To Measure Program Maturity. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Non Existent, Scanning, Assessment. So download instantly and tailor it with your information.
-
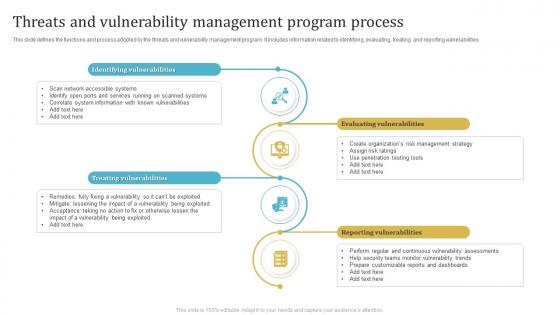 Threats And Vulnerability Management Program Process
Threats And Vulnerability Management Program ProcessThis slide defines the functions and process adopted by the threats and vulnerability management program. It includes information related to identifying, evaluating, treating and reporting vulnerabilities. Presenting our set of slides with Threats And Vulnerability Management Program Process. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identifying Vulnerabilities, Treating Vulnerabilities, Evaluating Vulnerabilities.
-
 Threats And Vulnerability Management Program Requirement Icon
Threats And Vulnerability Management Program Requirement IconIntroducing our premium set of slides with Threats And Vulnerability Management Program Requirement Icon. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Threats And Vulnerability Management, Program Requirement Icon. So download instantly and tailor it with your information.
-
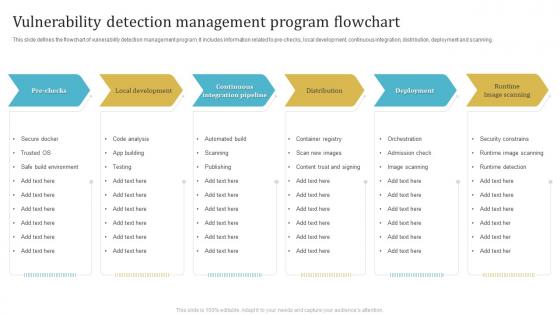 Vulnerability Detection Management Program Flowchart
Vulnerability Detection Management Program FlowchartThis slide defines the flowchart of vulnerability detection management program. It includes information related to pre checks, local development, continuous integration, distribution, deployment and scanning. Presenting our set of slides with Vulnerability Detection Management Program Flowchart. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Local Development, Continuous Integration Pipeline, Runtime Image Scanning.
-
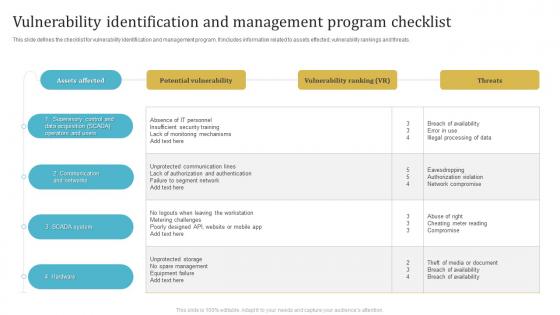 Vulnerability Identification And Management Program Checklist
Vulnerability Identification And Management Program ChecklistThis slide defines the checklist for vulnerability identification and management program. It includes information related to assets effected, vulnerability rankings and threats. Introducing our Vulnerability Identification And Management Program Checklist set of slides. The topics discussed in these slides are Potential Vulnerability, Vulnerability Ranking, Threats. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Vulnerability Management Program And Process For Organization
Vulnerability Management Program And Process For OrganizationThis slide defines the vulnerability management program and process adopted by the organization. It includes information related to identifying and addressing vulnerabilities on continuous basis. Introducing our premium set of slides with Vulnerability Management Program And Process For Organization. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Discover, Prioritize, Remediate. So download instantly and tailor it with your information.
-
 Vulnerability Management Program And Security Services
Vulnerability Management Program And Security ServicesThis slide defines the vulnerability management program and security services based on risk. It includes information related to integrating, assessment planning, analysis and sustainability. Presenting our set of slides with Vulnerability Management Program And Security Services. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Assessment Planning, Analysis And Reporting, Sustainability.
-
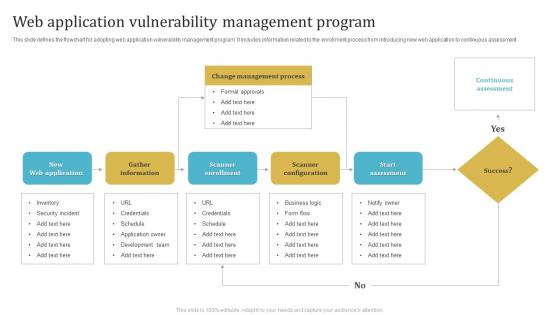 Web Application Vulnerability Management Program
Web Application Vulnerability Management ProgramThis slide defines the flowchart for adopting web application vulnerability management program. It includes information related to the enrollment process from introducing new web application to continuous assessment. Presenting our well structured Web Application Vulnerability Management Program. The topics discussed in this slide are Web Application, Gather Information, Scanner Enrollment. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
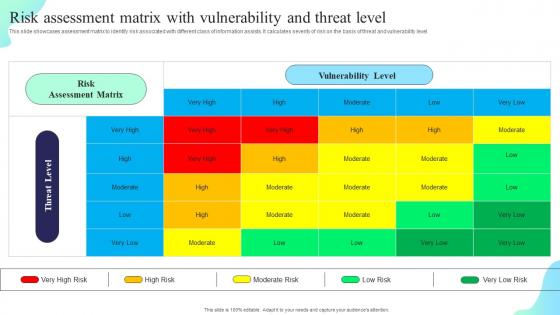 Risk Assessment Matrix With Vulnerability And Threat Level Formulating Cybersecurity Plan
Risk Assessment Matrix With Vulnerability And Threat Level Formulating Cybersecurity PlanThis slide showcases assessment matrix to identify risk associated with different class of information assists. It calculates severity of risk on the basis of threat and vulnerability level. Present the topic in a bit more detail with this Risk Assessment Matrix With Vulnerability And Threat Level Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Risk Assessment Matrix, Vulnerability Level. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
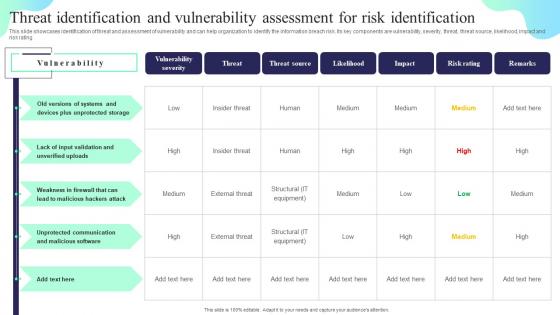 Threat Identification And Vulnerability Assessment Formulating Cybersecurity Plan
Threat Identification And Vulnerability Assessment Formulating Cybersecurity PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Present the topic in a bit more detail with this Threat Identification And Vulnerability Assessment Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Vulnerability Severity, Threat Source, Likelihood. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Rating For Risk Identification Formulating Cybersecurity Plan
Vulnerability Rating For Risk Identification Formulating Cybersecurity PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. It shows information about severity, vulnerability score and description. Introducing Vulnerability Rating For Risk Identification Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Score, Risk Identification, using this template. Grab it now to reap its full benefits.
-
 Vulnerability Example Network Security In Powerpoint And Google Slides Cpb
Vulnerability Example Network Security In Powerpoint And Google Slides CpbPresenting our Vulnerability Example Network Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Vulnerability Example Network Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 SMB Protocol Vulnerability In Powerpoint And Google Slides Cpb
SMB Protocol Vulnerability In Powerpoint And Google Slides CpbPresenting SMB Protocol Vulnerability In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like SMB Protocol Vulnerability. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Input Validation Vulnerability Attack In Powerpoint And Google Slides Cpb
Input Validation Vulnerability Attack In Powerpoint And Google Slides CpbPresenting our Input Validation Vulnerability Attack In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Input Validation Vulnerability Attack This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Hazard Exposure Vulnerability In Powerpoint And Google Slides Cpb
Hazard Exposure Vulnerability In Powerpoint And Google Slides CpbPresenting our Hazard Exposure Vulnerability In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Hazard Exposure Vulnerability This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Difference Between Hazard Vulnerability In Powerpoint And Google Slides Cpb
Difference Between Hazard Vulnerability In Powerpoint And Google Slides CpbPresenting Difference Between Hazard Vulnerability In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Difference Between Hazard Vulnerability. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Supply Chain Vulnerabilities In Powerpoint And Google Slides Cpb
Supply Chain Vulnerabilities In Powerpoint And Google Slides CpbPresenting Supply Chain Vulnerabilities In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Supply Chain Vulnerabilities. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.



