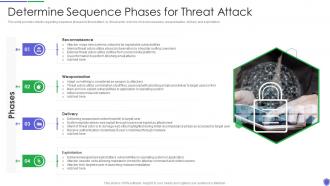
Managing critical threat vulnerabilities and security threats determine sequence phases
This slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation.
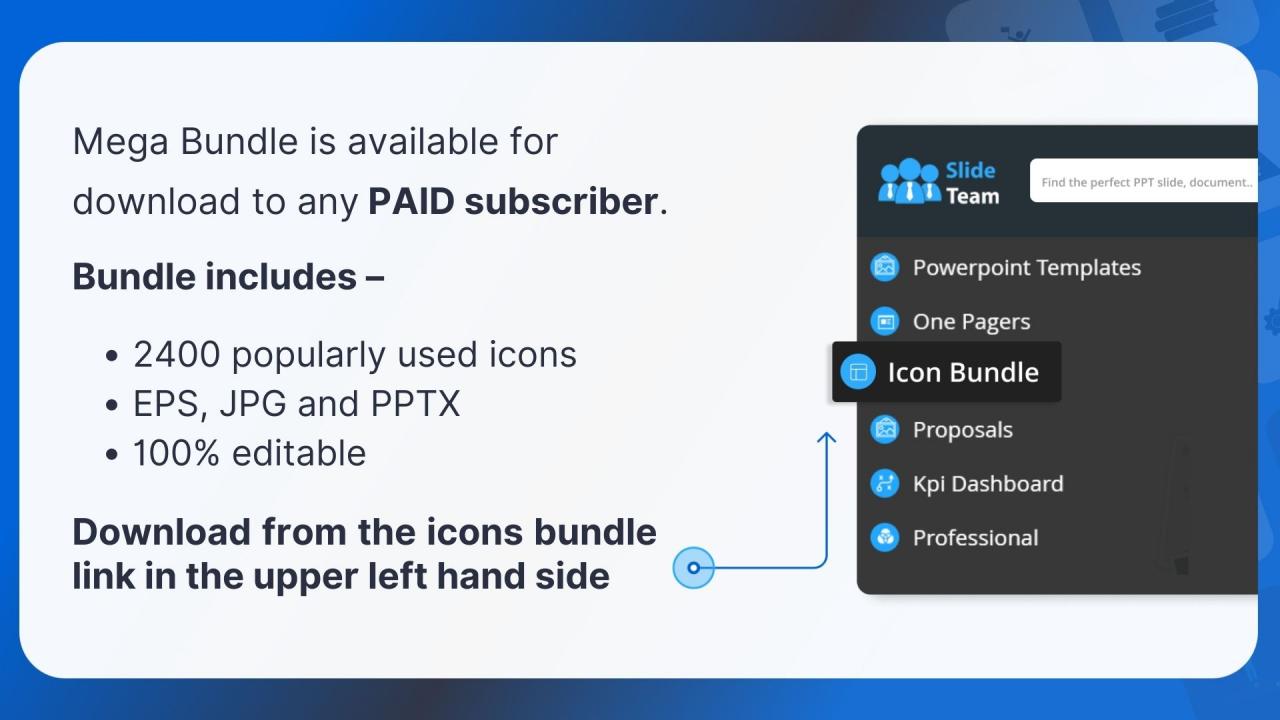
You must be logged in to download this presentation.
 Impress your
Impress your audience
Editable
of Time
PowerPoint presentation slides
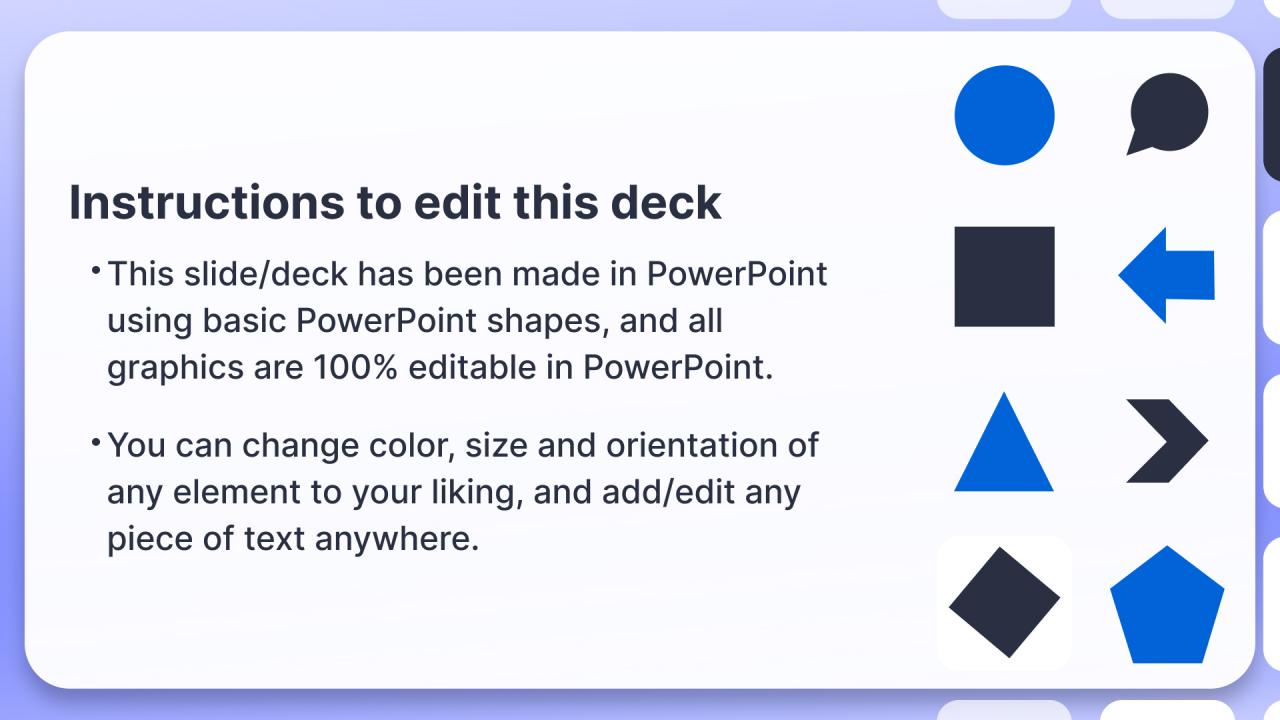
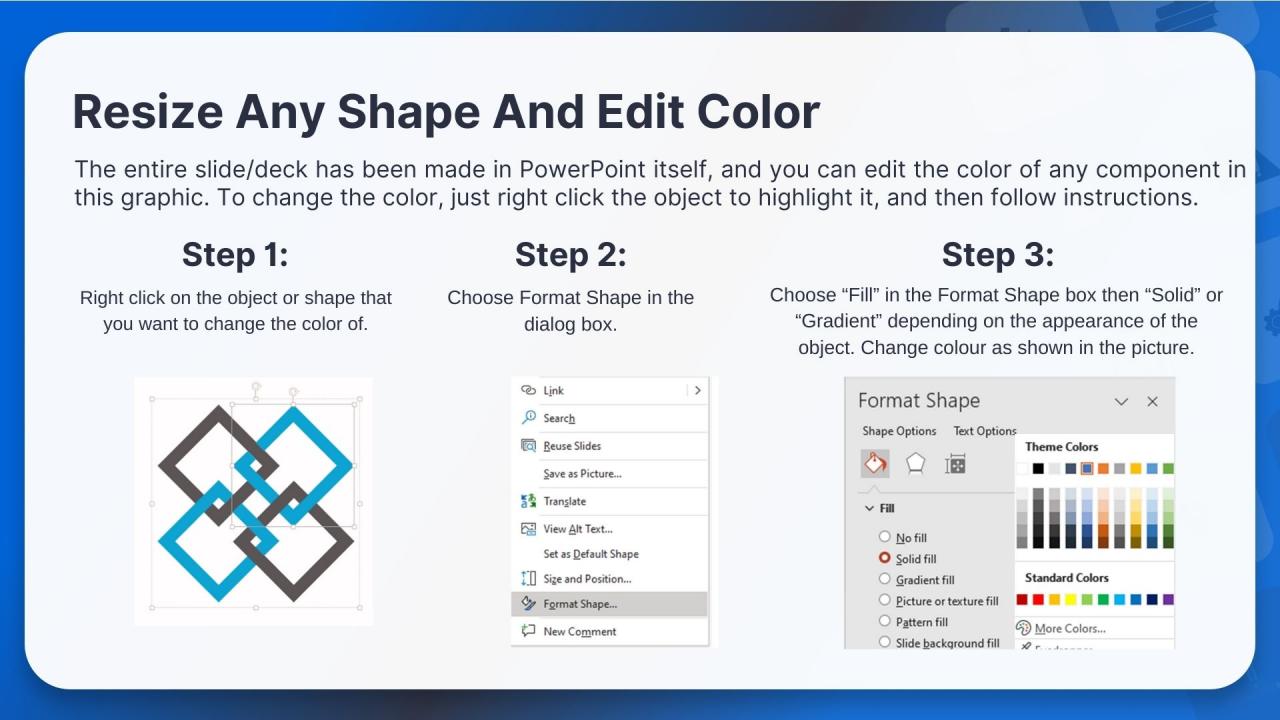
This slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Introducing Managing Critical Threat Vulnerabilities And Security Threats Determine Sequence Phases to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reconnaissance, Weaponization, Delivery, Exploitation, using this template. Grab it now to reap its full benefits.
People who downloaded this PowerPoint presentation also viewed the following :
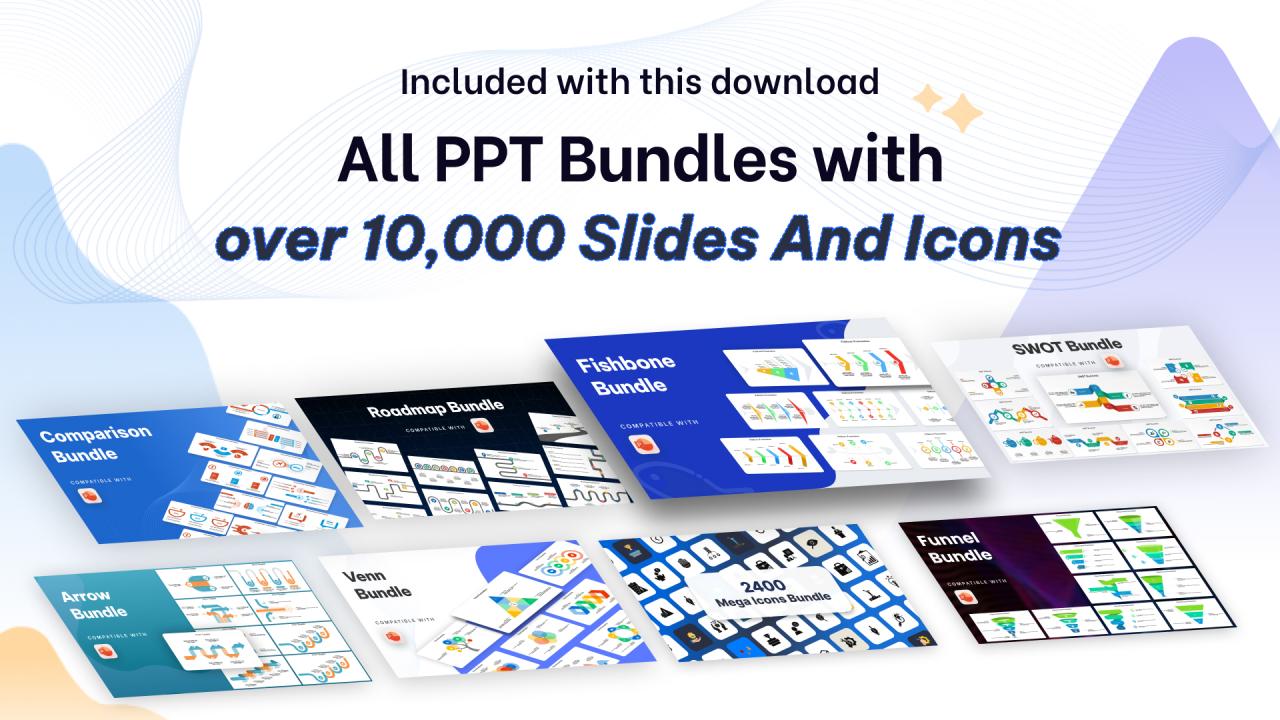
Managing critical threat vulnerabilities and security threats determine sequence phases with all 6 slides:
Use our Managing Critical Threat Vulnerabilities And Security Threats Determine Sequence Phases to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
Best Representation of topics, really appreciable.
-
Great product with highly impressive and engaging designs.