Powerpoint Templates and Google slides for Cyber Attack Protection
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
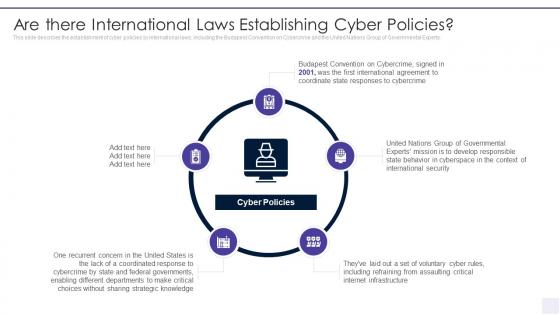 Wiper Malware Attack Are There International Laws Establishing Cyber Policies
Wiper Malware Attack Are There International Laws Establishing Cyber PoliciesThis slide describes the establishment of cyber policies by international laws, including the Budapest Convention on Cybercrime and the United Nations Group of Governmental Experts. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Are There International Laws Establishing Cyber Policies. This template helps you present information on five stages. You can also present information on Agreement, Coordinate, Responses, Convention, Security, Responsible using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Wiper Malware Attack Banks On Alert For Russian Reprisal Cyber Attacks On Swift
Wiper Malware Attack Banks On Alert For Russian Reprisal Cyber Attacks On SwiftThis slide represents that banks are on alert for Russian reprisal cyber attacks on Society for Worldwide Interbank Financial Telecommunication Swift. Introducing Wiper Malware Attack Banks On Alert For Russian Reprisal Cyber Attacks On Swift to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Transaction, Payment, Targeted, Payments, Institutions, using this template. Grab it now to reap its full benefits.
-
 Wiper Malware Attack Cyber Attacks On Ukraine Are Conspicuous
Wiper Malware Attack Cyber Attacks On Ukraine Are ConspicuousThis slide represents the conspicuous Russian cyber attacks on Ukraine, including the attacks on government and banking websites, hacking of the countrys railway computer networks, etc. Introducing Wiper Malware Attack Cyber Attacks On Ukraine Are Conspicuous to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Public Relations, Discovered, Momentarily, Network, Conflict, using this template. Grab it now to reap its full benefits.
-
 Wiper Malware Attack Cyber Officials Urge Agencies To Armor
Wiper Malware Attack Cyber Officials Urge Agencies To ArmorThis slide represents that officials from the Department of Homeland Security have urged agencies to prepare for possible Russian cyberattacks, and CISA has amended its shields up guidelines. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Cyber Officials Urge Agencies To Armor. This template helps you present information on five stages. You can also present information on Cybersecurity, Corporations, Cyberattacks, Managers, Enterprises using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
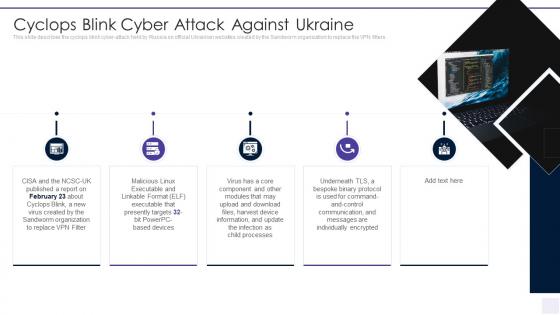 Wiper Malware Attack Cyclops Blink Cyber Attack Against Ukraine
Wiper Malware Attack Cyclops Blink Cyber Attack Against UkraineThis slide describes the cyclops blink cyber attack held by Russia on official Ukrainian websites created by the Sandworm organization to replace the VPN filters. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Cyclops Blink Cyber Attack Against Ukraine. This template helps you present information on five stages. You can also present information on Cyclops Blink Cyber Attack Against Ukraine using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Wiper Malware Attack Does Ukraine And Russia Cyber Warfare Kill People
Wiper Malware Attack Does Ukraine And Russia Cyber Warfare Kill PeopleThis slide describes if Ukraine and Russia cyber warfare is killing people and German cybersecurity expert Matthias Schulze said people have died due to misinformation efforts in earlier conflicts. Deliver an outstanding presentation on the topic using this Wiper Malware Attack Does Ukraine And Russia Cyber Warfare Kill People. Dispense information and present a thorough explanation of Cybersecurity, Traditional, Information, Misinformation, Susceptible using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
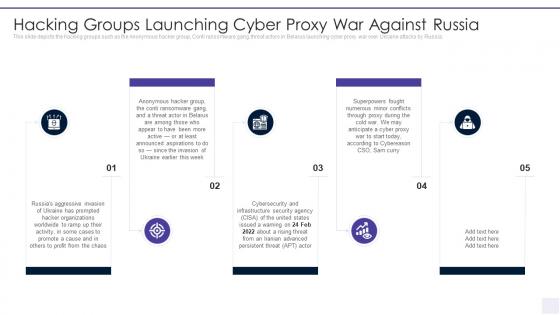 Wiper Malware Attack Hacking Groups Launching Cyber Proxy
Wiper Malware Attack Hacking Groups Launching Cyber ProxyThis slide depicts the hacking groups such as the Anonymous hacker group, Conti ransomware gang, threat actors in Belarus launching cyber proxy war over Ukraine attacks by Russia. Introducing Wiper Malware Attack Hacking Groups Launching Cyber Proxy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Aggressive, Organizations, Promote, Invasion, Ransomware, using this template. Grab it now to reap its full benefits.
-
 Wiper Malware Attack Hermetic Wiper Cyber Attack Against Ukraine
Wiper Malware Attack Hermetic Wiper Cyber Attack Against UkraineThis slide depicts the hermetic wiper attack on Ukrainian corporations, detected by a threat intelligence agency on February 23rd, and it damaged the master boot record through Ease US Partition Master. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Hermetic Wiper Cyber Attack Against Ukraine. This template helps you present information on seven stages. You can also present information on Corporations, Malware, Agency, Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
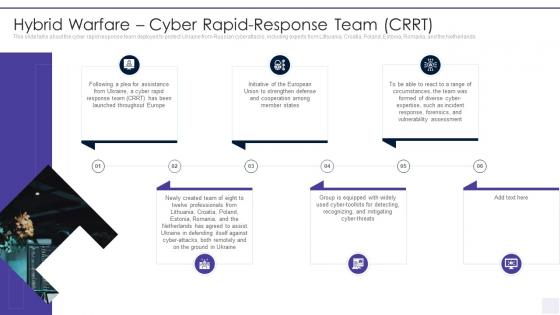 Wiper Malware Attack Hybrid Warfare Cyber Rapid Response Team Crrt
Wiper Malware Attack Hybrid Warfare Cyber Rapid Response Team CrrtThis slide talks about the cyber rapid response team deployed to protect Ukraine from Russian cyberattacks, including experts from Lithuania, Croatia, Poland, Estonia, Romania, and the Netherlands. Introducing Wiper Malware Attack Hybrid Warfare Cyber Rapid Response Team Crrt to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Strengthen, Cooperation, Vulnerability, Response, Assessment, using this template. Grab it now to reap its full benefits.
-
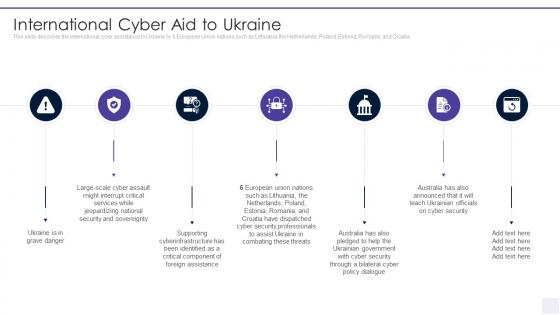 Wiper Malware Attack International Cyber Aid To Ukraine
Wiper Malware Attack International Cyber Aid To UkraineThis slide describes the international cyber assistance to Ukraine by 6 European Union nations such as Lithuania, the Netherlands, Poland, Estonia, Romania, and Croatia. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack International Cyber Aid To Ukraine. This template helps you present information on seven stages. You can also present information on Interrupt, Assault, Jeopardizing, Sovereignty, Cyberinfrastructure using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
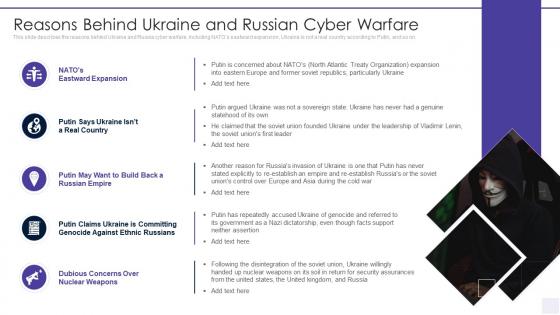 Wiper Malware Attack Reasons Behind Ukraine And Russian Cyber Warfare
Wiper Malware Attack Reasons Behind Ukraine And Russian Cyber WarfareThis slide describes the reasons behind Ukraine and Russia cyber warfare, including NATOs eastward expansion, Ukraine is not a real country according to Putin, and so on. Deliver an outstanding presentation on the topic using this Wiper Malware Attack Reasons Behind Ukraine And Russian Cyber Warfare. Dispense information and present a thorough explanation of Reasons Behind Ukraine And Russian Cyber Warfare using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
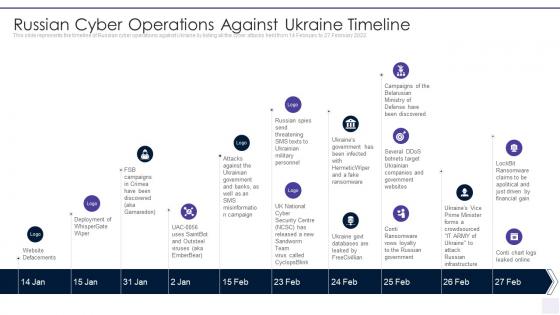 Wiper Malware Attack Russian Cyber Operations Against Ukraine Timeline
Wiper Malware Attack Russian Cyber Operations Against Ukraine TimelineThis slide represents the timeline of Russian cyber operations against Ukraine by listing all the cyber attacks held from 14 February to 27 February 2022. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Russian Cyber Operations Against Ukraine Timeline. This template helps you present information on ten stages. You can also present information on Russian Cyber Operations Against Ukraine Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Wiper Malware Attack Shuckworm Continues Cyber Espionage Attacks
Wiper Malware Attack Shuckworm Continues Cyber Espionage AttacksThis slide represents the continuous cyber espionage attacks held by the Shuckworm group against Ukraine. Most of these attacks were phishing emails to spread the malware among devices that could control remotely. Increase audience engagement and knowledge by dispensing information using Wiper Malware Attack Shuckworm Continues Cyber Espionage Attacks. This template helps you present information on five stages. You can also present information on Shuckworm Continues Cyber Espionage Attacks Against Ukraine using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Wiper Malware Attack Ukraine And Russia Cyber Warfare Impact On Western Countries
Wiper Malware Attack Ukraine And Russia Cyber Warfare Impact On Western CountriesThis slide represents the Ukraine and Russia cyber warfare impact on western countries such as the United States, United Kingdom, and Estonia. Introducing Wiper Malware Attack Ukraine And Russia Cyber Warfare Impact On Western Countries to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Businesses, Pondering, Confrontation, Significant, Cybersecurity, using this template. Grab it now to reap its full benefits.
-
 Wiper Malware Attack Ukraine And Russia Cyber Warfare Russian Vigilante Hacker
Wiper Malware Attack Ukraine And Russia Cyber Warfare Russian Vigilante HackerThis slide depicts the Russian vigilante hacker who was able to bring down some official Ukrainian websites and one military website along with his group of 6 hackers. Present the topic in a bit more detail with this Wiper Malware Attack Ukraine And Russia Cyber Warfare Russian Vigilante Hacker. Use it as a tool for discussion and navigation on Ukraine And Russia Cyber Warfare Russian Vigilante Hacker. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Wiper Malware Attack Weaknesses Of Russian Cyber Cell
Wiper Malware Attack Weaknesses Of Russian Cyber CellThis slide represents the weaknesses of Russian cyber cells, which are expected as in other countries, such as lack of skilled professionals and corrupted officials. Deliver an outstanding presentation on the topic using this Wiper Malware Attack Weaknesses Of Russian Cyber Cell. Dispense information and present a thorough explanation of Skilled Professionals, Corruption, Outsource, Opportunities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
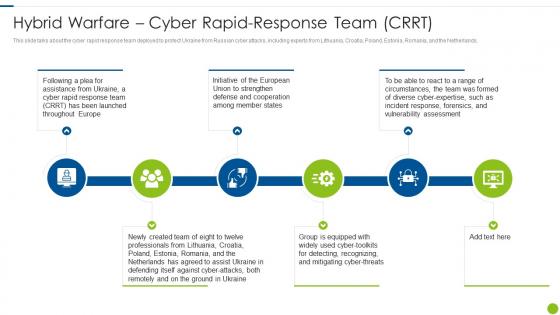 Cyber Attacks On Ukraine Hybrid Warfare Cyber Rapid Response Team Crrt
Cyber Attacks On Ukraine Hybrid Warfare Cyber Rapid Response Team CrrtThis slide talks about the cyber rapid response team deployed to protect Ukraine from Russian cyber attacks, including experts from Lithuania, Croatia, Poland, Estonia, Romania, and the Netherlands. Introducing Cyber Attacks On Ukraine Hybrid Warfare Cyber Rapid Response Team Crrt to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Hybrid Warfare Cyber Rapid Response Team Crrt, using this template. Grab it now to reap its full benefits.
-
 Global Cyber Terrorism Attacks Icon
Global Cyber Terrorism Attacks IconPresenting our set of slides with name Global Cyber Terrorism Attacks Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Global Cyber Terrorism Attacks Icon.
-
 Survey Insights On Cyber Terrorism Attacks Icons
Survey Insights On Cyber Terrorism Attacks IconsIntroducing our premium set of slides with name Survey Insights On Cyber Terrorism Attacks Icons. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Survey Insights On Cyber Terrorism Attacks Icons. So download instantly and tailor it with your information.
-
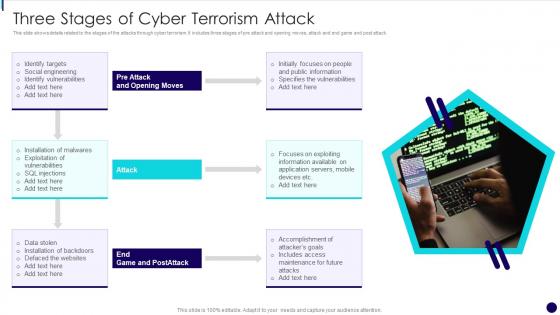 Three Stages Of Cyber Terrorism Attack
Three Stages Of Cyber Terrorism AttackThis slide shows details related to the stages of the attacks through cyber terrorism. It includes three stages of pre attack and opening moves, attack and end game and post attack. Presenting our set of slides with name Three Stages Of Cyber Terrorism Attack. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Social Engineering, Identify Vulnerabilities, Exploitation Of Vulnerabilities, Data Stolen.
-
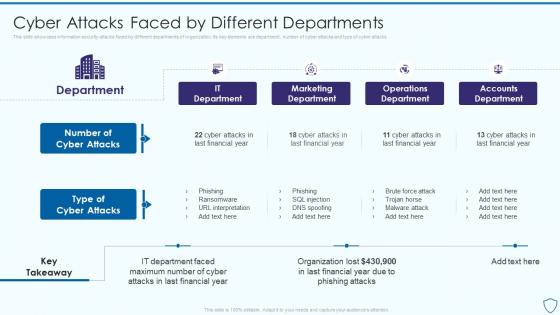 Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By Different
Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By DifferentThis slide showcase information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks Deliver an outstanding presentation on the topic using this Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By Different. Dispense information and present a thorough explanation of Marketing Department, Operations Department, Accounts Department using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber attacks on ukraine are conspicuous by their absence ukraine and russia cyber warfare it
Cyber attacks on ukraine are conspicuous by their absence ukraine and russia cyber warfare itThis slide represents the conspicuous Russian cyber attacks on Ukraine, including the attacks on government and banking websites, hacking of the countrys railway computer networks, etc. Increase audience engagement and knowledge by dispensing information using Cyber Attacks On Ukraine Are Conspicuous By Their Absence Ukraine And Russia Cyber Warfare It. This template helps you present information on six stages. You can also present information on Government, Operations, Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ukraine and russia cyber warfare it banks on alert for russian reprisal cyber attacks on swift
Ukraine and russia cyber warfare it banks on alert for russian reprisal cyber attacks on swiftThis slide represents that banks are on alert for Russian reprisal cyber attacks on Society for Worldwide Interbank Financial Telecommunication Swift. Deliver an outstanding presentation on the topic using this Ukraine And Russia Cyber Warfare It Banks On Alert For Russian Reprisal Cyber Attacks On Swift. Dispense information and present a thorough explanation of Banks On Alert For Russian Reprisal Cyber Attacks On Swift using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ukraine and russia cyber warfare it cyclops blink cyber attack against ukraine
Ukraine and russia cyber warfare it cyclops blink cyber attack against ukraineThis slide describes the cyclops blink cyber attack held by Russia on official Ukrainian websites created by the Sandworm organization to replace the VPN filters. Increase audience engagement and knowledge by dispensing information using Ukraine And Russia Cyber Warfare It Cyclops Blink Cyber Attack Against Ukraine. This template helps you present information on five stages. You can also present information on Cyclops Blink Cyber Attack Against Ukraine using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ukraine and russia cyber warfare it hermetic wiper cyber attack against ukraine
Ukraine and russia cyber warfare it hermetic wiper cyber attack against ukraineThis slide depicts the hermeticwiper attack on Ukrainian corporations, detected by a threat intelligence agency on February 23rd, and it damaged the master boot record through EaseUS Partition Master. Deliver an outstanding presentation on the topic using this Ukraine And Russia Cyber Warfare It Hermetic Wiper Cyber Attack Against Ukraine. Dispense information and present a thorough explanation of Hermetic Wiper Cyber Attack Against Ukraine using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ukraine and russia cyber warfare it how to protect yourself from ongoing cybersecurity attacks
Ukraine and russia cyber warfare it how to protect yourself from ongoing cybersecurity attacksThis slide talks about how to protect yourself from ongoing Russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Introducing Ukraine And Russia Cyber Warfare It How To Protect Yourself From Ongoing Cybersecurity Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Resources, Antivirus, Software, using this template. Grab it now to reap its full benefits.
-
 Ukraine and russia cyber warfare it impact of defacement attacks and fake news
Ukraine and russia cyber warfare it impact of defacement attacks and fake newsThis slide shows the impact of defacement attacks and fake news on the public, and Meta has banned Russian media on its platforms, and Russia has restricted access to Facebook. Introducing Ukraine And Russia Cyber Warfare It Impact Of Defacement Attacks And Fake News to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Information, Platforms, Restricted, using this template. Grab it now to reap its full benefits.
-
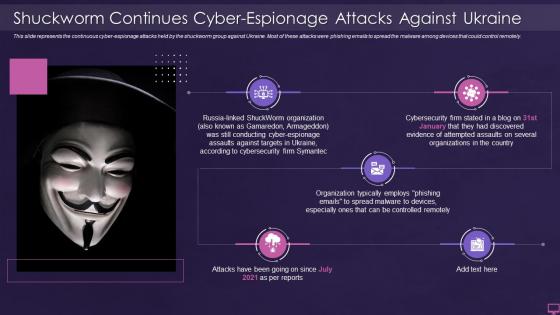 Ukraine and russia cyber warfare it shuckworm continues cyber espionage attacks against ukraine
Ukraine and russia cyber warfare it shuckworm continues cyber espionage attacks against ukraineThis slide represents the continuous cyber espionage attacks held by the shuckworm group against Ukraine. Most of these attacks were phishing emails to spread the malware among devices that could control remotely. Introducing Ukraine And Russia Cyber Warfare It Shuckworm Continues Cyber Espionage Attacks Against Ukraine to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Organization, Cybersecurity, Shuckworm, using this template. Grab it now to reap its full benefits.
-
 Ukraine and russia cyber warfare it website defacements ddos attacks and website clones
Ukraine and russia cyber warfare it website defacements ddos attacks and website clonesThis slide represents the other attacks carried out by Russia on Ukraine, such as website defacement, distributed denial of service attacks, and website clones. Introducing Ukraine And Russia Cyber Warfare It Website Defacements Ddos Attacks And Website Clones to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Government, Institutions, Defacements, using this template. Grab it now to reap its full benefits.
-
 Ukraine and russia cyber warfare it whispergate attack on ukrainian organizations
Ukraine and russia cyber warfare it whispergate attack on ukrainian organizationsThis slide represents Russias whispergate attack on Ukrainian organizations, consists of three stages, and is designed to turn off the systems defenses, delete data, and format itself. Increase audience engagement and knowledge by dispensing information using Ukraine And Russia Cyber Warfare It Whispergate Attack On Ukrainian Organizations. This template helps you present information on five stages. You can also present information on Whispergate Attack On Ukrainian Organizations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it cyber terrorist attacks experienced by company in previous financial year
Cyberterrorism it cyber terrorist attacks experienced by company in previous financial yearThis slide describes the number of cyber-terrorist attacks experienced by the company in the previous financial year 2020. Present the topic in a bit more detail with this Cyberterrorism IT Cyber Terrorist Attacks Experienced By Company In Previous Financial Year. Use it as a tool for discussion and navigation on Cyber Crime, Lowest Cyber Crimes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
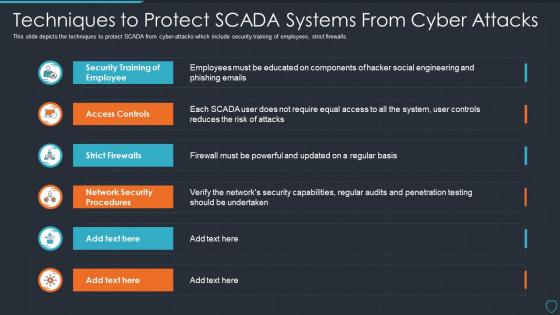 Cyberterrorism it techniques to protect scada systems from cyber attacks
Cyberterrorism it techniques to protect scada systems from cyber attacksThis slide depicts the techniques to protect SCADA from cyber-attacks which include security training of employees, strict firewalls. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Techniques To Protect SCADA Systems From Cyber Attacks. Dispense information and present a thorough explanation of Security Training, Employee, Access Controls, Strict Firewalls, Network Security Procedures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Website cyber attacks ppt powerpoint presentation outline designs cpb
Website cyber attacks ppt powerpoint presentation outline designs cpbPresenting our Website Cyber Attacks Ppt Powerpoint Presentation Outline Designs Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Website Cyber Attacks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
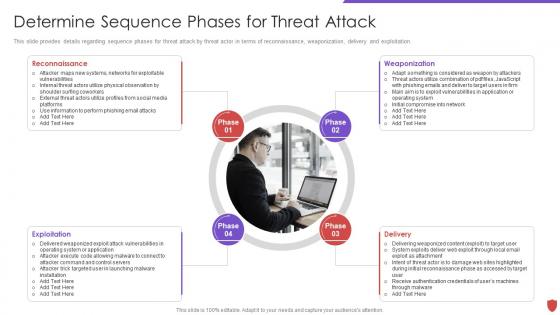 Cyber security risk management determine sequence phases for threat attack
Cyber security risk management determine sequence phases for threat attackThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Increase audience engagement and knowledge by dispensing information using Cyber Security Risk Management Determine Sequence Phases For Threat Attack. This template helps you present information on four stages. You can also present information on Reconnaissance, Weaponization, Exploitation, Delivery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
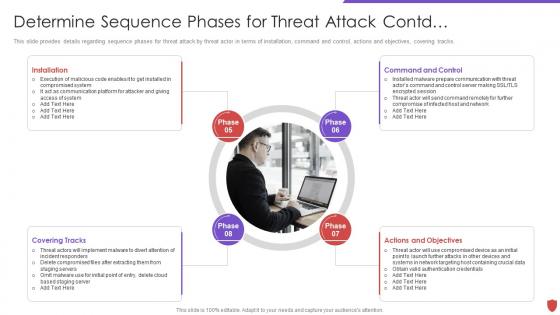 Determine sequence phases for threat attack contd cyber security risk management
Determine sequence phases for threat attack contd cyber security risk managementThis slide provides details regarding sequence phases for threat attack by threat actor in terms of installation, command and control, actions and objectives, covering tracks. Introducing Determine Sequence Phases For Threat Attack Contd Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Installation, Command And Control, Actions And Objectives, Covering Tracks, using this template. Grab it now to reap its full benefits.
-
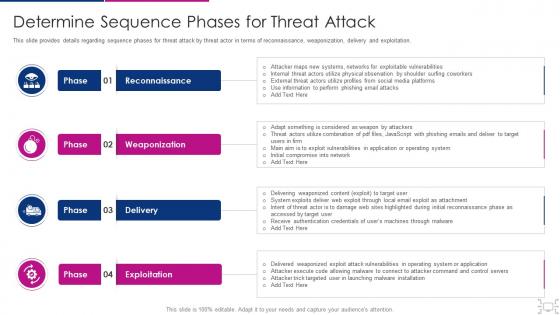 Cyber threat management workplace determine sequence phases for attack
Cyber threat management workplace determine sequence phases for attackThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Increase audience engagement and knowledge by dispensing information using Cyber Threat Management Workplace Determine Sequence Phases For Attack. This template helps you present information on four stages. You can also present information on Reconnaissance, Weaponization, Delivery, Exploitation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
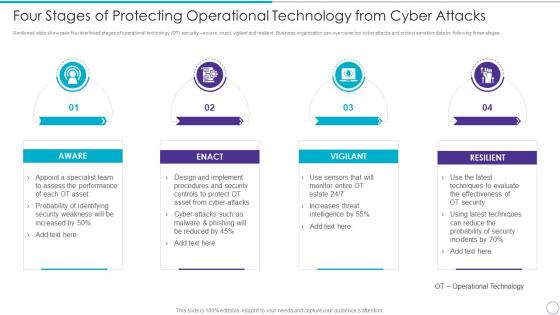 Four Stages Of Protecting Operational Technology From Cyber Attacks
Four Stages Of Protecting Operational Technology From Cyber AttacksMentioned slide showcase four interlinked stages of operational technology OT security aware, enact, vigilant and resilient. Business organization can overcome top cyber attacks and protect sensitive data by following these stages. Increase audience engagement and knowledge by dispensing information using four Stages Of Protecting Operational Technology From Cyber Attacks. This template helps you present information on four stages. You can also present information on Aware, Enact, Vigilant, Resilient using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
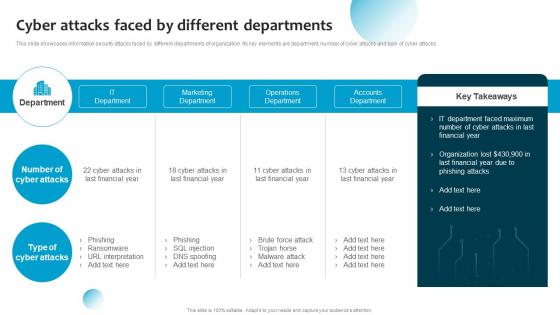 Cyber Attacks Faced By Different Departments Information System Security And Risk Administration Plan
Cyber Attacks Faced By Different Departments Information System Security And Risk Administration PlanThis slide showcases information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks. Present the topic in a bit more detail with this Cyber Attacks Faced By Different Departments Information System Security And Risk Administration Plan. Use it as a tool for discussion and navigation on It Department, Marketing Department, Operations Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Protect Cyber Attacks In Powerpoint And Google Slides Cpb
Protect Cyber Attacks In Powerpoint And Google Slides CpbPresenting Protect Cyber Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Protect Cyber Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Energy Cyber Attacks In Powerpoint And Google Slides Cpb
Energy Cyber Attacks In Powerpoint And Google Slides CpbPresenting Energy Cyber Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Energy Cyber Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
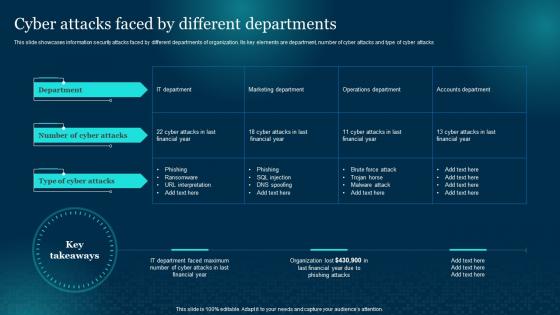 Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different Departments
Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different DepartmentsThis slide showcases information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks Present the topic in a bit more detail with this Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different Departments. Use it as a tool for discussion and navigation on Departments, Information, Cyber Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Attack Mitigation Strategies In Powerpoint And Google Slides Cpb
Cyber Attack Mitigation Strategies In Powerpoint And Google Slides CpbPresenting our er Attack Mitigation Strategies In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Attack Mitigation Strategies This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Attacks Faced By Different Departments Formulating Cybersecurity Plan
Cyber Attacks Faced By Different Departments Formulating Cybersecurity PlanThis slide showcase information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks. Present the topic in a bit more detail with this Cyber Attacks Faced By Different Departments Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Marketing Department, Operations Department, Accounts Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Cyber Attacks In Powerpoint And Google Slides Cpb
Impact Cyber Attacks In Powerpoint And Google Slides CpbPresenting Impact Cyber Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Impact Cyber Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Agenda For Implementing Security Awareness Training To Prevent Cyber Attacks
Agenda For Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing Agenda For Implementing Security Awareness Training To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Awareness Campaign, Cyber Security, Awareness Training, using this template. Grab it now to reap its full benefits.
-
 G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks
G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing G33 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Current Assessment, Organization, Cyber Security, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Implementing Security Awareness Training To Prevent Cyber Attacks
Icons Slide For Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing our well researched set of slides titled Icons Slide For Implementing Security Awareness Training To Prevent Cyber Attacks. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Critical Infrastructure Cyber Attacks In Powerpoint And Google Slides Cpb
Critical Infrastructure Cyber Attacks In Powerpoint And Google Slides CpbPresenting our Critical Infrastructure Cyber Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Critical Infrastructure Cyber Attacks. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
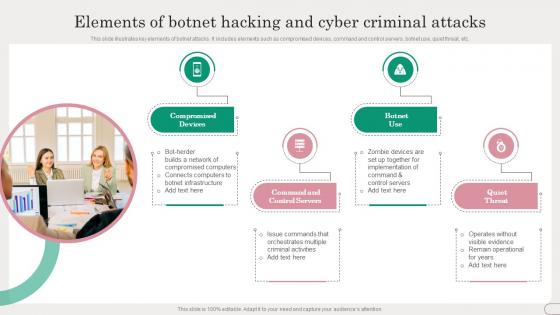 Elements Of Botnet Hacking And Cyber Criminal Attacks
Elements Of Botnet Hacking And Cyber Criminal AttacksThis slide illustrates key elements of botnet attacks. It includes elements such as compromised devices, command and control servers, botnet use, quiet threat, etc. Introducing our premium set of slides with Elements Of Botnet Hacking And Cyber Criminal Attacks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Command and Control Servers. So download instantly and tailor it with your information.
-
 Annual Statistical Trends In Cyber Attack
Annual Statistical Trends In Cyber AttackThe following slide depicts some key trends in cyber threats happening across the globe. It includes some facts and figures related to the malware attack, data breach records, annual losses etc. Presenting our set of slides with Annual Statistical Trends In Cyber Attack. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Facts And Figures.
-
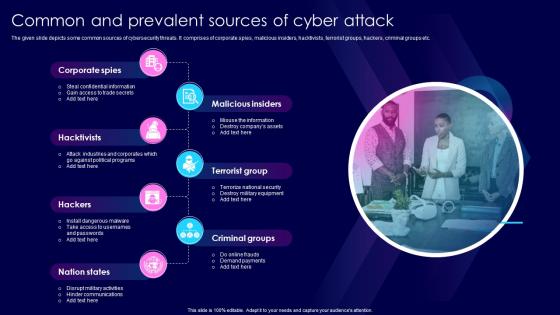 Common And Prevalent Sources Of Cyber Attack
Common And Prevalent Sources Of Cyber AttackThe given slide depicts some common sources of cybersecurity threats. It comprises of corporate spies, malicious insiders, hacktivists, terrorist groups, hackers, criminal groups etc. Introducing our premium set of slides with Common And Prevalent Sources Of Cyber Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Malicious Insiders, Corporate Spies. So download instantly and tailor it with your information.
-
 Cyber Attack Alert Icon With Desktop Screen
Cyber Attack Alert Icon With Desktop ScreenPresenting our set of slides with Cyber Attack Alert Icon With Desktop Screen. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Attack Alert Icon, Desktop Screen.
-
 Cyber Attack Icon With Man In Black Hood
Cyber Attack Icon With Man In Black HoodPresenting our set of slides with Cyber Attack Icon With Man In Black Hood. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Attack Icon, Man Black Hood.
-
 Cyber Security Checklist To Mitigate Threats Of Attack
Cyber Security Checklist To Mitigate Threats Of AttackThe given slide provides the key activities to be done to alleviate the effects of cyber threats. It includes managing social media profiles, backing up the data, crosschecking privacy and security settings etc. Introducing our premium set of slides with Cyber Security Checklist To Mitigate Threats Of Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Checklist, Mitigate Threats Attack. So download instantly and tailor it with your information.
-
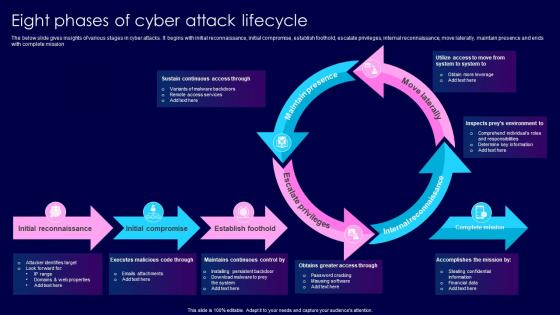 Eight Phases Of Cyber Attack Lifecycle
Eight Phases Of Cyber Attack LifecycleThe below slide gives insights of various stages in cyber attacks. It begins with initial reconnaissance, initial compromise, establish foothold, escalate privileges, internal reconnaissance, move laterally, maintain presence and ends with complete mission. Presenting our well structured Eight Phases Of Cyber Attack Lifecycle. The topics discussed in this slide are Move Laterally, Escalate Privileges, Maintain Presence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
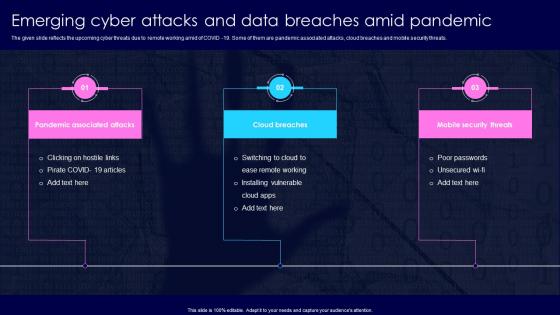 Emerging Cyber Attacks And Data Breaches Amid Pandemic
Emerging Cyber Attacks And Data Breaches Amid PandemicThe given slide reflects the upcoming cyber threats due to remote working amid of COVID 19. Some of them are pandemic associated attacks, cloud breaches and mobile security threats. Presenting our set of slides with Emerging Cyber Attacks And Data Breaches Amid Pandemic. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Breaches, Mobile Security Threats.
-
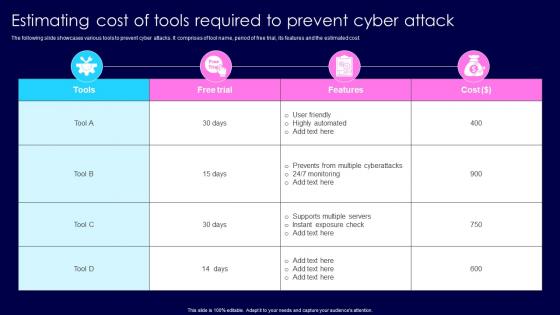 Estimating Cost Of Tools Required To Prevent Cyber Attack
Estimating Cost Of Tools Required To Prevent Cyber AttackThe following slide showcases various tools to prevent cyber attacks. It comprises of tool name, period of free trial, its features and the estimated cost. Introducing our Estimating Cost Of Tools Required To Prevent Cyber Attack set of slides. The topics discussed in these slides are Highly Automated, Supports Multiple Servers. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
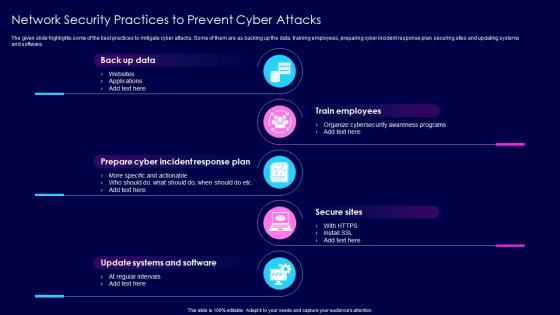 Network Security Practices To Prevent Cyber Attacks
Network Security Practices To Prevent Cyber AttacksThe given slide highlights some of the best practices to mitigate cyber attacks. Some of them are as backing up the data, training employees, preparing cyber incident response plan, securing sites and updating systems and software. Presenting our set of slides with Network Security Practices To Prevent Cyber Attacks. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Train Employees, Secure Sites.
-
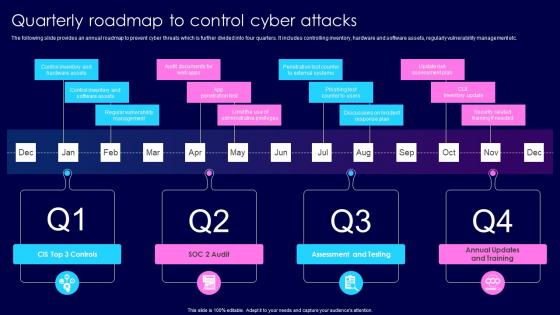 Quarterly Roadmap To Control Cyber Attacks
Quarterly Roadmap To Control Cyber AttacksThe following slide provides an annual roadmap to prevent cyber threats which is further divided into four quarters. It includes controlling inventory, hardware and software assets, regularly vulnerability management etc. Introducing our premium set of slides with Quarterly Roadmap To Control Cyber Attacks. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Assessment, Testing, Annual Updates, Training. So download instantly and tailor it with your information.
-
 Six Common Types Of Cyber Attacks
Six Common Types Of Cyber AttacksThe following slide represents the common types of cyber threats. It includes malware, phishing, password attacks, drive by downloads, man in the middle and denial of service attacks. Presenting our set of slides with Six Common Types Of Cyber Attacks. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Visiting Sites, Hacking Passwords.




