Powerpoint Templates and Google slides for Cyber Security Illustration
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Csirt Cyber Security Icon For Data Safety
Csirt Cyber Security Icon For Data SafetyPresenting our set of slides with Csirt Cyber Security Icon For Data Safety. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Csirt Cyber Security, Data Safety.
-
 Csirt Cyber Security Icon For Protecting Data
Csirt Cyber Security Icon For Protecting DataIntroducing our premium set of slides with Csirt Cyber Security Icon For Protecting Data. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Csirt Cyber Security, Protecting Data. So download instantly and tailor it with your information.
-
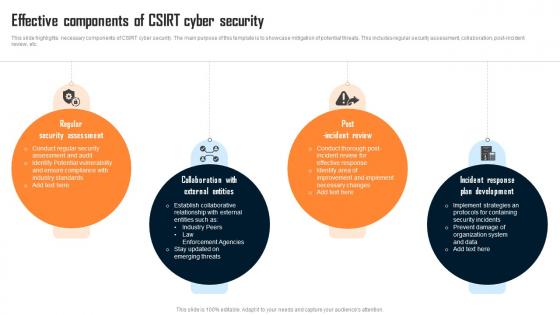 Effective Components Of Csirt Cyber Security
Effective Components Of Csirt Cyber SecurityThis slide highlights necessary components of CSIRT cyber security. The main purpose of this template is to showcase mitigation of potential threats. This includes regular security assessment, collaboration, post incident review, etc. Presenting our set of slides with Effective Components Of Csirt Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Assessment, External Entities, Incident Review.
-
 Organizational Csirt Cyber Security System
Organizational Csirt Cyber Security SystemThis slide showcases framework of CSIRT cyber security. The main purpose of this template is conflicting management and collective learning. This includes technology, CSIRT processes, CSIRT level situation, etc. Introducing our Organizational Csirt Cyber Security System set of slides. The topics discussed in these slides are Event Management, Conflict Management, Collective Learning. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
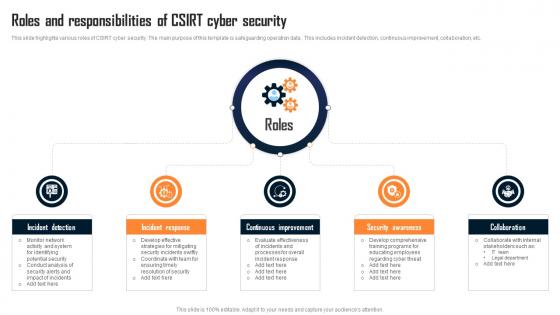 Roles And Responsibilities Of Csirt Cyber Security
Roles And Responsibilities Of Csirt Cyber SecurityThis slide highlights various roles of CSIRT cyber security. The main purpose of this template is safeguarding operation data . This includes incident detection, continuous improvement, collaboration, etc. Introducing our premium set of slides with Roles And Responsibilities Of Csirt Cyber Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Incident Detection, Incident Response, Continuous Improvement. So download instantly and tailor it with your information.
-
 Various Types Of Csirt Cyber Security
Various Types Of Csirt Cyber SecurityThis slide highlights different types of CSIRT cyber security. The main purpose of this template is showcasing various approaches of dealing with cyber security. This includes internal CSIRT, National CSIRT, Vendor CSIRT, etc. Presenting our set of slides with Various Types Of Csirt Cyber Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Maintaining Data, Cyber Threat, Cyber Security.
-
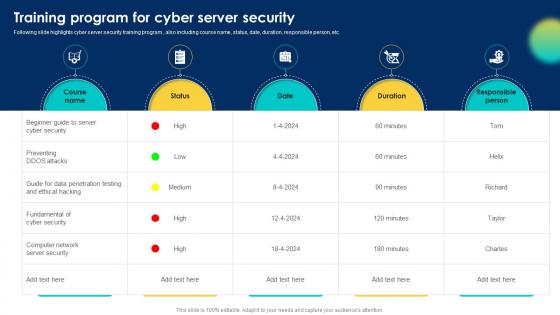 Training Program For Cyber Server Security
Training Program For Cyber Server SecurityFollowing slide highlights cyber server security training program , also including course name, status, date, duration, responsible person, etc. Presenting our well structured Training Program For Cyber Server Security. The topics discussed in this slide are Cyber Security, Server Security, Ethical Hacking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Security Trends To Mitigate Corporate Cyber Threats
Security Trends To Mitigate Corporate Cyber ThreatsThis slide represents various trends that help companies to enhance security against cyber attacks for effective data protection. It includes various trends such as firewall as a service, extended detection and response, and third-party supply chain risk management. Presenting our well structured Security Trends To Mitigate Corporate Cyber Threats. The topics discussed in this slide are Trends, Overview, Impact. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Access With Cloud Storage Solution Business Recovery Plan To Overcome Cyber Security Threat
Access With Cloud Storage Solution Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about access management with a cloud storage solution. It includes file sharing with cloud platforms and selection criteria such as storage space, privacy and security, and other benefits. Present the topic in a bit more detail with this Access With Cloud Storage Solution Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Storage Space, Privacy And Security, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda Business Recovery Plan To Overcome Cyber Security Threat
Agenda Business Recovery Plan To Overcome Cyber Security ThreatIntroducing Agenda Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Business, Financial, Operations, using this template. Grab it now to reap its full benefits.
-
 Alternative For Managing Cyber Threats Business Recovery Plan To Overcome Cyber Security Threat
Alternative For Managing Cyber Threats Business Recovery Plan To Overcome Cyber Security ThreatIncrease audience engagement and knowledge by dispensing information using Alternative For Managing Cyber Threats Business Recovery Plan To Overcome Cyber Security Threat. This template helps you present information on five stages. You can also present information on Staff Training, End Point Protection, Wifi Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
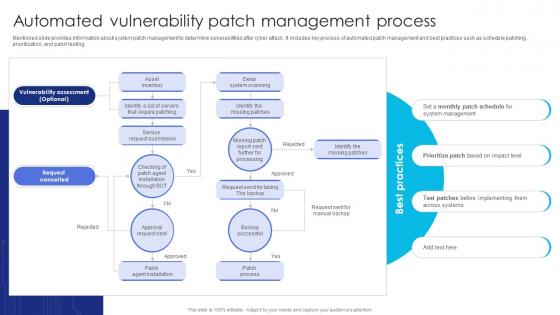 Automated Patch Management Process Business Recovery Plan To Overcome Cyber Security Threat
Automated Patch Management Process Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about system patch management to determine vulnerabilities after cyber attack. It includes key process of automated patch management and best practices such as schedule patching, prioritization, and patch testing. Deliver an outstanding presentation on the topic using this Automated Patch Management Process Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Management, Process, Vulnerability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Business Goals Achievement Duration Business Recovery Plan To Overcome Cyber Security Threat
Business Goals Achievement Duration Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about time-based goals achieved for cyber attack management. It includes goals such as mean time to detect incidents, containment time, resolution time, and recovery time. Present the topic in a bit more detail with this Business Goals Achievement Duration Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Mean Time To Recover, Mean Time To Resolve, Mean Time To Contain. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
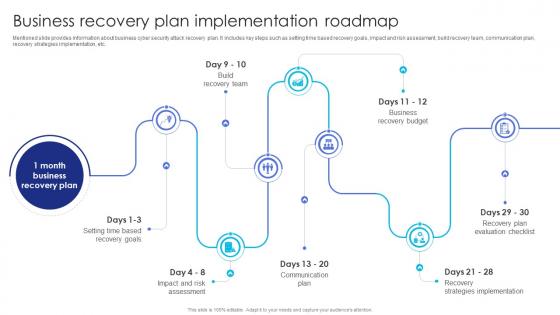 Business Plan Implementation Roadmap Business Recovery Plan To Overcome Cyber Security Threat
Business Plan Implementation Roadmap Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about business cyber security attack recovery plan. It includes key steps such as setting time based recovery goals, impact and risk assessment, build recovery team, communication plan, recovery strategies implementation, etc. Introducing Business Plan Implementation Roadmap Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Assessment, Communication Plan, Recovery Strategies Implementation, using this template. Grab it now to reap its full benefits.
-
 Business Plan To Overcome Cyber Security Threat Table Of Contents
Business Plan To Overcome Cyber Security Threat Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Business Plan To Overcome Cyber Security Threat Table Of Contents. This template helps you present information on one stages. You can also present information on Business, Communication, External Stakeholders using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
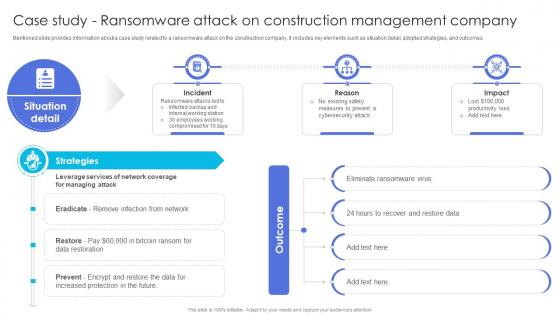 Case Study Construction Management Company Business Recovery To Overcome Cyber Security Threat
Case Study Construction Management Company Business Recovery To Overcome Cyber Security ThreatMentioned slide provides information about a case study related to a ransomware attack on the construction company. It includes key elements such as situation detail, adopted strategies, and outcomes. Deliver an outstanding presentation on the topic using this Case Study Construction Management Company Business Recovery To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Construction, Management, Ransomware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
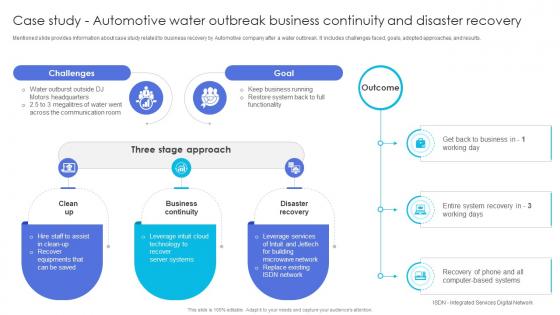 Case Study Continuity Disaster Recovery Business Recovery Plan To Overcome Cyber Security Threat
Case Study Continuity Disaster Recovery Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about case study related to business recovery by Automotive company after a water outbreak. It includes challenges faced, goals, adopted approaches, and results. Present the topic in a bit more detail with this Case Study Continuity Disaster Recovery Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Business Continuity, Disaster Recovery, Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
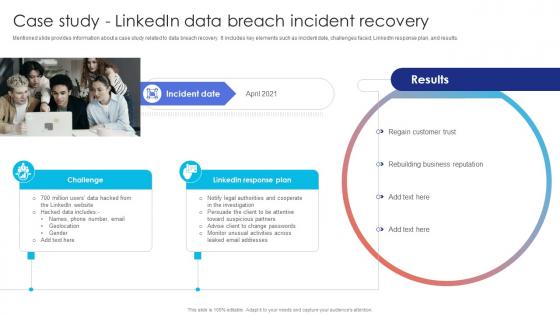 Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security Threat
Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about a case study related to data breach recovery. It includes key elements such as incident date, challenges faced, LinkedIn response plan, and results. Deliver an outstanding presentation on the topic using this Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Regain Customer Trust, Rebuilding Business Reputation, Linkedin Response using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
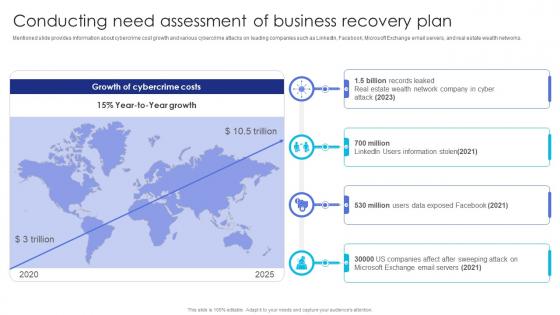 Conducting Of Business Recovery Plan Business Recovery Plan To Overcome Cyber Security Threat
Conducting Of Business Recovery Plan Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about cybercrime cost growth and various cybercrime attacks on leading companies such as LinkedIn, Facebook, Microsoft Exchange email servers, and real estate wealth networks. Present the topic in a bit more detail with this Conducting Of Business Recovery Plan Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Assessment, Business, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
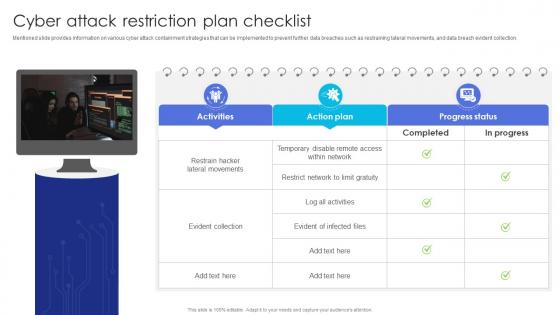 Cyber Attack Restriction Plan Checklist Business Recovery Plan To Overcome Cyber Security Threat
Cyber Attack Restriction Plan Checklist Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information on various cyber attack containment strategies that can be implemented to prevent further data breaches such as restraining lateral movements, and data breach evident collection. Deliver an outstanding presentation on the topic using this Cyber Attack Restriction Plan Checklist Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Containment, Strategies, Implemented using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Communication Different Stakeholders Business Recovery Plan To Overcome Cyber Security Threat
Cyber Communication Different Stakeholders Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about various stakeholders to be taken care of during and after the business recovery periods such as customers, internal stakeholders, external agencies, and recovery team. Introducing Cyber Communication Different Stakeholders Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Customer, Government, Recovery Team, using this template. Grab it now to reap its full benefits.
-
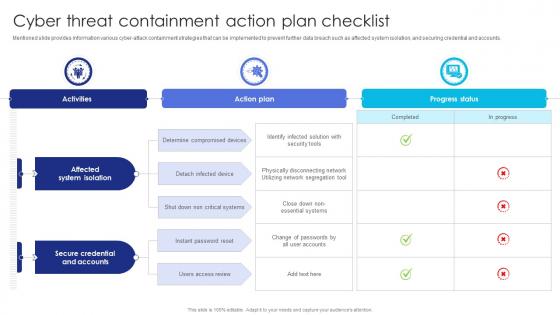 Cyber Containment Action Plan Checklist Business Recovery Plan To Overcome Cyber Security Threat
Cyber Containment Action Plan Checklist Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information various cyber-attack containment strategies that can be implemented to prevent further data breach such as affected system isolation, and securing credential and accounts. Deliver an outstanding presentation on the topic using this Cyber Containment Action Plan Checklist Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Affected System Isolation, Secure Credential And Accounts, Determine Compromised Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Impact And Risk Assessment Matrix Business Recovery Plan To Overcome Cyber Security Threat
Cyber Impact And Risk Assessment Matrix Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about the cyber security attack risk assessment matrix which can be leveraged to determine the severity of cyber threats, the likelihood of occurrence, and future action plan. Present the topic in a bit more detail with this Cyber Impact And Risk Assessment Matrix Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Assessment Matrix, Occurrence, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
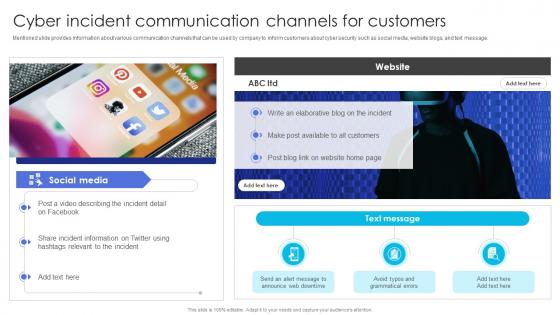 Cyber Incident Channels For Customers Business Recovery Plan To Overcome Cyber Security Threat
Cyber Incident Channels For Customers Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about various communication channels that can be used by company to inform customers about cyber security such as social media, website blogs, and text message. Present the topic in a bit more detail with this Cyber Incident Channels For Customers Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Communication, Incident Information, Grammatical. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
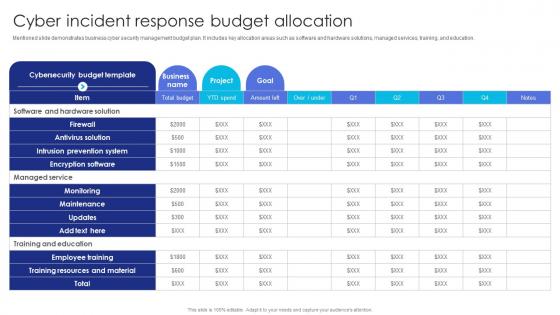 Cyber Incident Response Budget Allocation Business Recovery Plan To Overcome Cyber Security Threat
Cyber Incident Response Budget Allocation Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide demonstrates business cyber security management budget plan. It includes key allocation areas such as software and hardware solutions, managed services, training, and education. Deliver an outstanding presentation on the topic using this Cyber Incident Response Budget Allocation Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Antivirus Solution, Intrusion Prevention System, Encryption Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Meeting With Recovery Team Business Recovery Plan To Overcome Cyber Security Threat
Cyber Meeting With Recovery Team Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about communication plan for the recovery team. It includes key elements such as meeting agenda, meeting coordinator, things to communicate, meeting mode, and target audience. Present the topic in a bit more detail with this Cyber Meeting With Recovery Team Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Incident Details, Impact Assessment, Recovery Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Designated Business Recovery Team Structure Business Recovery Plan To Overcome Cyber Security Threat
Designated Business Recovery Team Structure Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about recovery team structure and number of members across different team for business recovery. It includes teams such as executive, communication, crisis management, impact assessment, etc. Present the topic in a bit more detail with this Designated Business Recovery Team Structure Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Business Continuity Expert, Assessment, Communication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
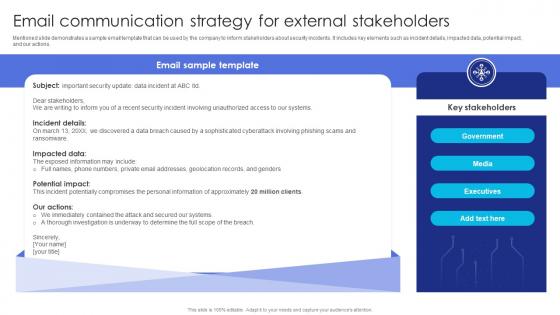 Email Strategy For External Stakeholders Business Recovery Plan To Overcome Cyber Security Threat
Email Strategy For External Stakeholders Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide demonstrates a sample email template that can be used by the company to inform stakeholders about security incidents. It includes key elements such as incident details, impacted data, potential impact, and our actions. Present the topic in a bit more detail with this Email Strategy For External Stakeholders Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Government, Executives, Stakeholders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
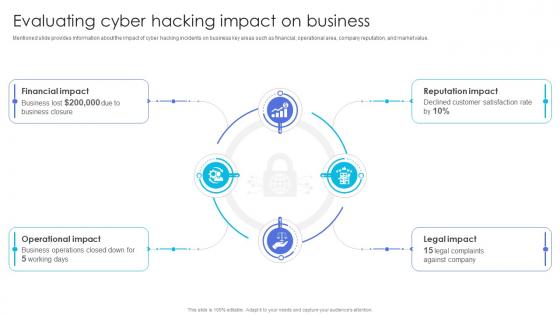 Evaluating Hacking Impact On Business Business Recovery Plan To Overcome Cyber Security Threat
Evaluating Hacking Impact On Business Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about the impact of cyber hacking incidents on business key areas such as financial, operational area, company reputation, and market value. Introducing Evaluating Hacking Impact On Business Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Financial Impact, Operational Impact, Legal Impact, using this template. Grab it now to reap its full benefits.
-
 Forecasted Cyber Business Performance Business Recovery Plan To Overcome Cyber Security Threat
Forecasted Cyber Business Performance Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about the impact of cyber response plan applications on business performance. It includes key areas of impact such as reputation, operations, and market value of company Increase audience engagement and knowledge by dispensing information using Forecasted Cyber Business Performance Business Recovery Plan To Overcome Cyber Security Threat. This template helps you present information on three stages. You can also present information on Operational Impact, Reputation Impact, Legal Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Business Recovery Plan To Overcome Cyber Security Threat
Icons Slide For Business Recovery Plan To Overcome Cyber Security ThreatDeliver an outstanding presentation on the topic using this Icons Slide For Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Icons using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Elements Security Response Plan Business Recovery Plan To Overcome Cyber Security Threat
Key Elements Security Response Plan Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about the key components of cyber security threat response plan. It includes key elements such as identify attack source, limit damage, damage scope assessment, consulting, clean up system, and future action plan. Increase audience engagement and knowledge by dispensing information using Key Elements Security Response Plan Business Recovery Plan To Overcome Cyber Security Threat. This template helps you present information on six stages. You can also present information on Identify The Attack Source, Limit Additional Damage, Damage Scope Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Incident Details Related To It Failure Business Recovery Plan To Overcome Cyber Security Threat
Major Incident Details Related To It Failure Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about cyber attack incidents. It includes information about incident date, impact, and incident information comprising loss of customer name, address, phone number, birth date, etc. Increase audience engagement and knowledge by dispensing information using Major Incident Details Related To It Failure Business Recovery Plan To Overcome Cyber Security Threat. This template helps you present information on three stages. You can also present information on Ransomware, Information, Cyber Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security Threat
Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information leveraging multifactor authentication to increase cyber security. It includes key points such as failed login, geographic location, time of login, operating system, IP address, etc. Deliver an outstanding presentation on the topic using this Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Time Of Login Attempt, Operating System, Source Of IP Address using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
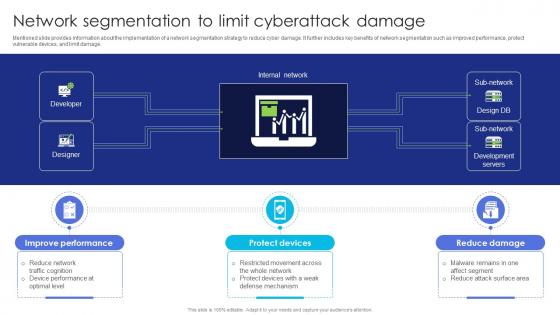 Network To Limit Cyberattack Damage Business Recovery Plan To Overcome Cyber Security Threat
Network To Limit Cyberattack Damage Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about the implementation of a network segmentation strategy to reduce cyber damage. It further includes key benefits of network segmentation such as improved performance, protect vulnerable devices, and limit damage. Present the topic in a bit more detail with this Network To Limit Cyberattack Damage Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Improve Performance, Protect Devices, Reduce Damage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Potential Consistent Cyber Security Attacks Business Recovery Plan To Overcome Cyber Security Threat
Potential Consistent Cyber Security Attacks Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about various solutions that can be adopted for business cyber-attack management. It includes key solutions such as staff training, collaboration with experts, and develop business recovery plan. Deliver an outstanding presentation on the topic using this Potential Consistent Cyber Security Attacks Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Solution Scope, Solution Duration, Requisites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
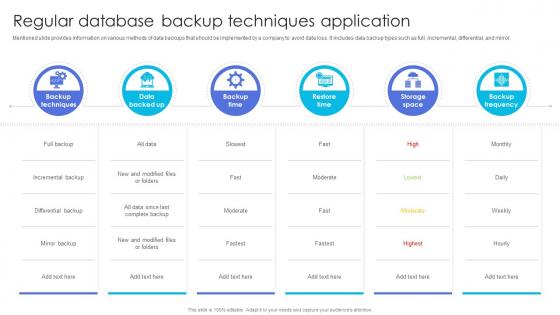 Regular Backup Techniques Application Business Recovery Plan To Overcome Cyber Security Threat
Regular Backup Techniques Application Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information on various methods of data backups that should be implemented by a company to avoid data loss. It includes data backup types such as full, incremental, differential, and mirror. Present the topic in a bit more detail with this Regular Backup Techniques Application Business Recovery Plan To Overcome Cyber Security Threat. Use it as a tool for discussion and navigation on Techniques, Application, Incremental. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Setting Goals For Cyber Attack Management Business Recovery Plan To Overcome Cyber Security Threat
Setting Goals For Cyber Attack Management Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about time-based goals set for cyber attack management. It includes goals such as mean time to detect incidents, containment time, resolution time, and recovery time. Introducing Setting Goals For Cyber Attack Management Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Mean Time To Contain, Mean Time To Resolve, Mean Time To Recover, using this template. Grab it now to reap its full benefits.
-
 Software Updation To Avoid Security Breach Business Recovery Plan To Overcome Cyber Security Threat
Software Updation To Avoid Security Breach Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information software updation best practices to follow. It includes key practices such as updation operating system, uninstall unnecessary software, and leverage patch systems. Increase audience engagement and knowledge by dispensing information using Software Updation To Avoid Security Breach Business Recovery Plan To Overcome Cyber Security Threat. This template helps you present information on three stages. You can also present information on Leverage Patching System, Uninstall Unnecessary Software, Update Operating System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Business Recovery Plan To Overcome Cyber Security Threat
Table Of Contents Business Recovery Plan To Overcome Cyber Security ThreatIntroducing Table Of Contents Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Current Scenario, Potential Solutions, Business Recovery Plan , using this template. Grab it now to reap its full benefits.
-
 Ai Technology Implementation Icon For Robust OT Cyber Security
Ai Technology Implementation Icon For Robust OT Cyber SecurityPresenting our set of slides with Ai Technology Implementation Icon For Robust OT Cyber Security This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on AI Technology Implementation Icon, Robust OT Cyber Security
-
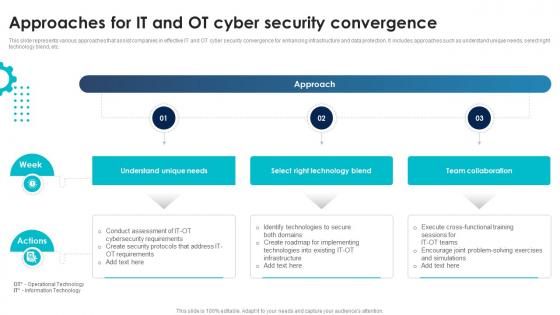 Approaches For IT And OT Cyber Security Convergence
Approaches For IT And OT Cyber Security ConvergenceIntroducing our premium set of slides with Approaches For IT And OT Cyber Security Convergence Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Understand Unique Needs, Select Right Technology Blend, Team Collaboration So download instantly and tailor it with your information.
-
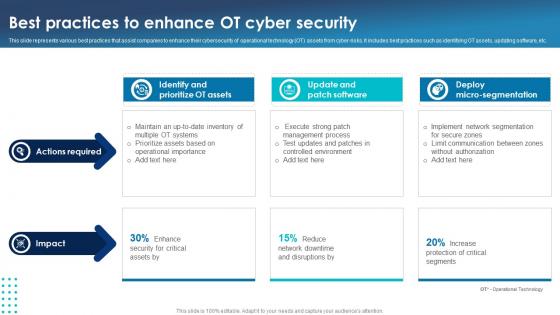 Best Practices To Enhance OT Cyber Security
Best Practices To Enhance OT Cyber SecurityThis slide represents various best practices that assist companies to enhance their cybersecurity of operational technology OT assets from cyber-risks. It includes best practices such as identifying OT assets, updating software, etc. Presenting our set of slides with Best Practices To Enhance OT Cyber Security This exhibits information on Two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify And Prioritize OT Assets, Update And Patch Software
-
 Checklist To Enhance OT Security From Cyber Risks
Checklist To Enhance OT Security From Cyber RisksThis slide represents checklist that assist companies to optimize their OT security against multiple cyber threats efficiently. It includes various steps such as separate IT and OT assets, Restrict industrial security, document all communication, etc. Introducing our Checklist To Enhance OT Security From Cyber Risks set of slides. The topics discussed in these slides are Checklist, Status, PhaseThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
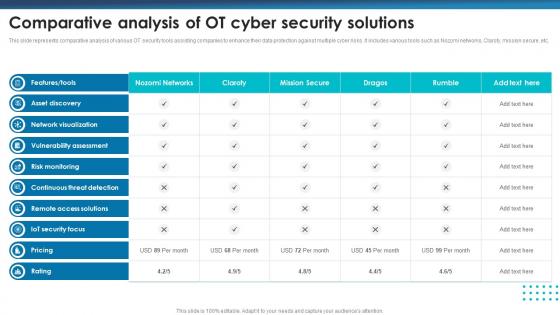 Comparative Analysis Of OT Cyber Security Solutions
Comparative Analysis Of OT Cyber Security SolutionsThis slide represents comparative analysis of various OT security tools assisting companies to enhance their data protection against multiple cyber risks. It includes various tools such as Nozomi networks, Claroty, mission secure, etc. Presenting our well structured Comparative Analysis Of OT Cyber Security Solutions The topics discussed in this slide are Network Visualization, Vulnerability Assessment, Risk MonitoringThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
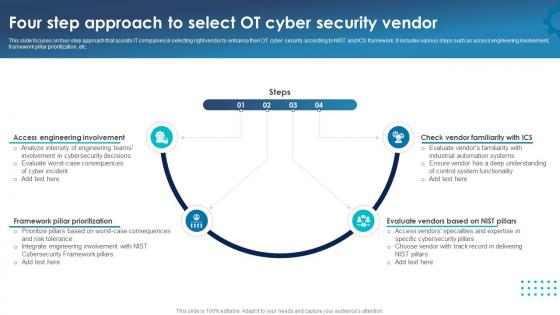 Four Step Approach To Select OT Cyber Security Vendor
Four Step Approach To Select OT Cyber Security VendorThis slide focuses on four-step approach that assists IT companies in selecting right vendor to enhance their OT cyber security according to NIST and ICS framework. It includes various steps such as access engineering involvement, framework pillar prioritization, etc. Introducing our premium set of slides with Four Step Approach To Select OT Cyber Security Vendor Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Engineering Involvement, Framework Pillar Prioritization So download instantly and tailor it with your information.
-
 Integrating Artificial Intelligence For Optimizing OT Cyber Security
Integrating Artificial Intelligence For Optimizing OT Cyber SecurityThis slide represents various applications of artificial intelligence that assist companies to enhance their OT cyber security and protect from potential cyber threats. It includes various applications such as rapid analysis, task prioritization, etc. Introducing our premium set of slides with Integrating Artificial Intelligence For Optimizing OT Cyber Security Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Threat Detection Capabilities, Routine Task Automation So download instantly and tailor it with your information.
-
 Key Pillars Of Robust OT Cyber Security
Key Pillars Of Robust OT Cyber SecurityThis slide represents key pillars that assist companies to implement robust OT cyber security strategies to enhance infrastructure protection. It includes various pillars such as business continuity, strategy, resiliency, finance, and culture. Presenting our set of slides with Key Pillars Of Robust OT Cyber Security This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Business Continuity, Strategy, Resiliency
-
 Maturity Model To Monitor OT Cyber Security Adoption
Maturity Model To Monitor OT Cyber Security AdoptionThis slide represents maturity model that assist companies to monitor and track cyber security adoption for enhancing OT protection. It includes various phases such as secure, defend, contain, monitor and manage phase. Presenting our well structured Maturity Model To Monitor OT Cyber Security Adoption The topics discussed in this slide are Secure, Defend, Contain, MonitorThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
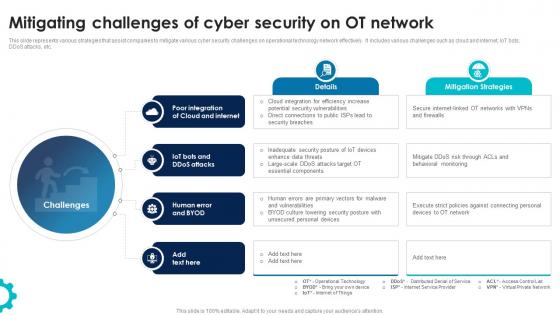 Mitigating Challenges Of Cyber Security On OT Network
Mitigating Challenges Of Cyber Security On OT NetworkThis slide represents various strategies that assist companies to mitigate various cyber security challenges on operational technology network effectively. It includes various challenges such as cloud and internet, IoT bots, DDoS attacks, etc. Introducing our premium set of slides with Mitigating Challenges Of Cyber Security On OT Network Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud And Internet, Ddos Attacks, Human Error And BYOD So download instantly and tailor it with your information.
-
 OT Cyber Security Icon To Prevent Unauthorized Access
OT Cyber Security Icon To Prevent Unauthorized AccessIntroducing our premium set of slides with OT Cyber Security Icon To Prevent Unauthorized Access Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like OT Cyber Security Icon To Prevent, Unauthorized Access So download instantly and tailor it with your information.
-
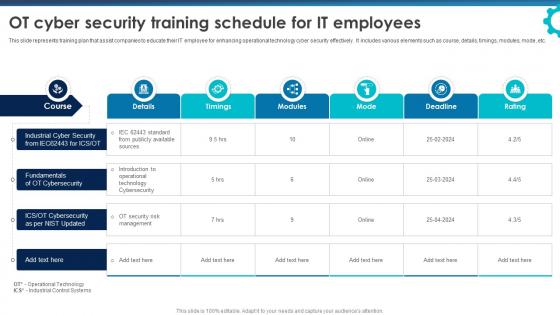 OT Cyber Security Training Schedule For It Employees
OT Cyber Security Training Schedule For It EmployeesThis slide represents training plan that assist companies to educate their IT employee for enhancing operational technology cyber security effectively. It includes various elements such as course, details, timings, modules, mode, etc. Introducing our OT Cyber Security Training Schedule For It Employees set of slides. The topics discussed in these slides are Details, Timings, ModulesThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 OT Security Icon For Cyber Threat Protection
OT Security Icon For Cyber Threat ProtectionIntroducing our premium set of slides with OT Security Icon For Cyber Threat Protection Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like OT Security Icon, Cyber Threat Protection So download instantly and tailor it with your information.
-
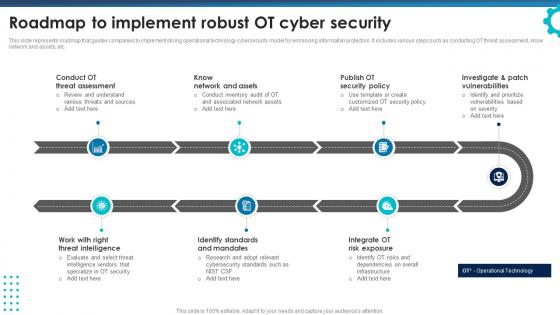 Roadmap To Implement Robust OT Cyber Security
Roadmap To Implement Robust OT Cyber SecurityThis slide represents roadmap that guides companies to implement strong operational technology cybersecurity model for enhancing information protection. It includes various steps such as conducting OT threat assessment, know network and assets, etc. Presenting our set of slides with Roadmap To Implement Robust OT Cyber Security This exhibits information on Seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Conduct OT Threat Assessment, Know Network And Assets, Publish OT Security Policy
-
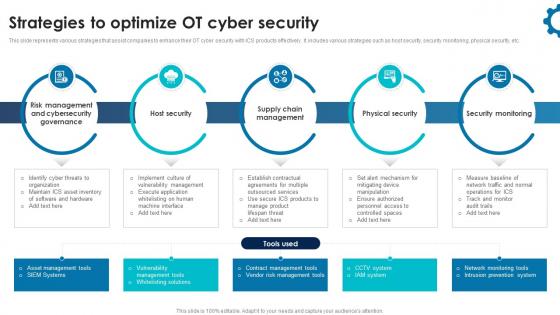 Strategies To Optimize OT Cyber Security
Strategies To Optimize OT Cyber SecurityThis slide represents various strategies that assist companies to enhance their OT cyber security with ICS products effectively. It includes various strategies such as host security, security monitoring, physical security, etc. Introducing our premium set of slides with Strategies To Optimize OT Cyber Security Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Host Security, Physical Security, Security Monitoring So download instantly and tailor it with your information.
-
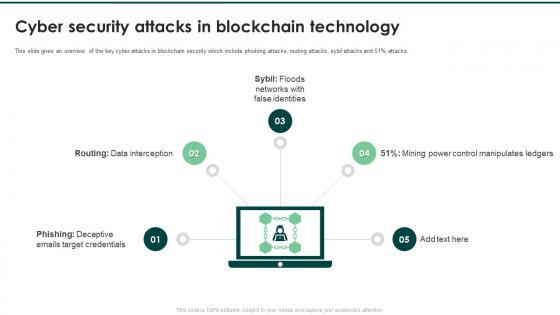 Cyber Security Attacks In Blockchain Technology
Cyber Security Attacks In Blockchain TechnologyPresenting our set of slides with Cyber Security Attacks In Blockchain Technology. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Interception, Floods Networks, False Identities.
-
 Icon For Blockchain Technology In Cyber Security
Icon For Blockchain Technology In Cyber SecurityPresenting our well structured Icon For Blockchain Technology In Cyber Security. The topics discussed in this slide are Icon, Blockchain Technology, Cyber Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
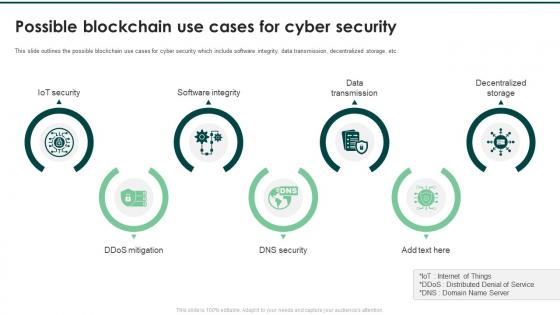 Possible Blockchain Use Cases For Cyber Security
Possible Blockchain Use Cases For Cyber SecurityPresenting our set of slides with Possible Blockchain Use Cases For Cyber Security. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Iot Security, Software Integrity, Data Transmission.
-
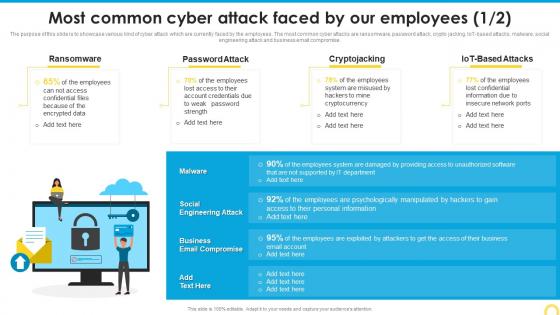 Most Common Cyber Attack Building A Security Awareness Program
Most Common Cyber Attack Building A Security Awareness ProgramThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT based attacks, malware, social engineering attack and business email compromise. Present the topic in a bit more detail with this Most Common Cyber Attack Building A Security Awareness Program. Use it as a tool for discussion and navigation on Ransomware, Password Attack, Cryptojacking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
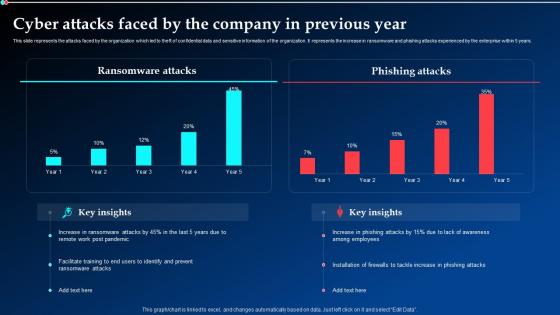 Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration
Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt DemonstrationThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks, Previous Year. This template is free to edit as deemed fit for your organization. Therefore download it now.



