Powerpoint Templates and Google slides for Cybersecurity Attacks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Overview Of Active And Passive Attacks In Cybersecurity Training PPT
Overview Of Active And Passive Attacks In Cybersecurity Training PPTPresenting Active and Passive Attacks in Cybersecurity. These slides are 100 percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
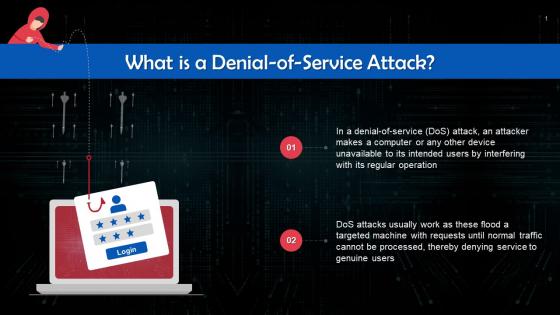 Denial Of Service Attack In Cybersecurity Training Ppt
Denial Of Service Attack In Cybersecurity Training PptPresenting Denial of Service Attack in Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Man In The Middle Attacks In Cybersecurity Training Ppt
Man In The Middle Attacks In Cybersecurity Training PptPresenting Man in the Middle Attacks in Cybersecurity. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
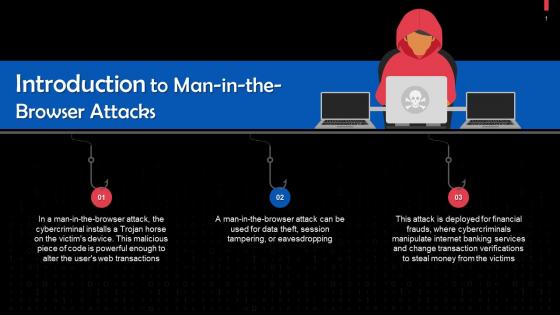 Man In The Browser Attacks In Cybersecurity Training Ppt
Man In The Browser Attacks In Cybersecurity Training PptPresenting Man in the Browser Attacks in Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Spyware Cyber Attack In Cybersecurity Training Ppt
Spyware Cyber Attack In Cybersecurity Training PptPresenting Spyware Cyber Attack in Cybersecurity. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Social Engineering Attacks In Cybersecurity Training Ppt
Social Engineering Attacks In Cybersecurity Training PptPresenting Social Engineering Attacks in Cybersecurity. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Ransomware Attacks In Cybersecurity Training Ppt
Ransomware Attacks In Cybersecurity Training PptPresenting Ransomware Attacks in Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Malvertising Cyber Attacks In Cybersecurity Training Ppt
Malvertising Cyber Attacks In Cybersecurity Training PptPresenting Malvertising Cyber Attacks in Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
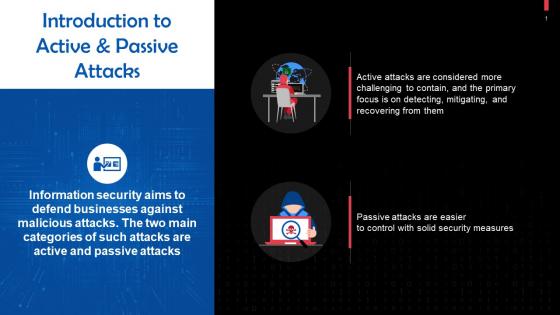 Active And Passive Attacks In Cybersecurity Training Ppt
Active And Passive Attacks In Cybersecurity Training PptPresenting Active and Passive Attacks in Cybersecurity This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Cyber Attack In Cybersecurity Training Ppt
Cyber Attack In Cybersecurity Training PptPresenting Cyber Attack in Cybersecurity. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Password Spraying Attacks In Cybersecurity Training Ppt
Password Spraying Attacks In Cybersecurity Training PptPresenting Password Spraying Attacks in Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SS
IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight Internet of Things IoT password attack prevention measures. The techniques outlined in slide are limit public information, verifying the source, and no sharing of password. Deliver an outstanding presentation on the topic using this IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Information, Verify, Password using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
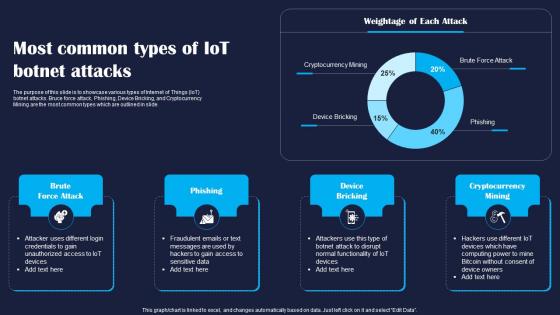 Most Common Types Of IoT Botnet Attacks Improving IoT Device Cybersecurity IoT SS
Most Common Types Of IoT Botnet Attacks Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase various types of Internet of Things IoT botnet attacks. Bruce force attack, Phishing, Device Bricking, and Cryptocurrency Mining are the most common types which are outlined in slide. Present the topic in a bit more detail with this Most Common Types Of IoT Botnet Attacks Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Phishing, Bricking, Mining. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
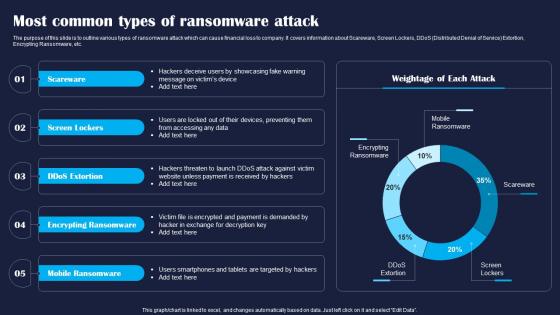 Most Common Types Of Ransomware Attack Improving IoT Device Cybersecurity IoT SS
Most Common Types Of Ransomware Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline various types of ransomware attack which can cause financial loss to company. It covers information about Scareware, Screen Lockers, DDoS Distributed Denial of Service Extortion, Encrypting Ransomware, etc. Deliver an outstanding presentation on the topic using this Most Common Types Of Ransomware Attack Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Scareware, Lockers, Mobile using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
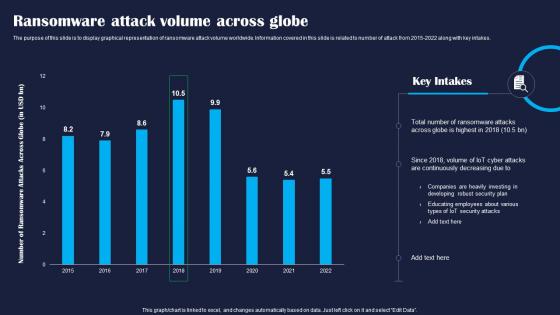 Ransomware Attack Volume Across Globe Improving IoT Device Cybersecurity IoT SS
Ransomware Attack Volume Across Globe Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display graphical representation of ransomware attack volume worldwide. Information covered in this slide is related to number of attack from 2015 2022 along with key intakes. Deliver an outstanding presentation on the topic using this Ransomware Attack Volume Across Globe Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Globe, Attacks, Developing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
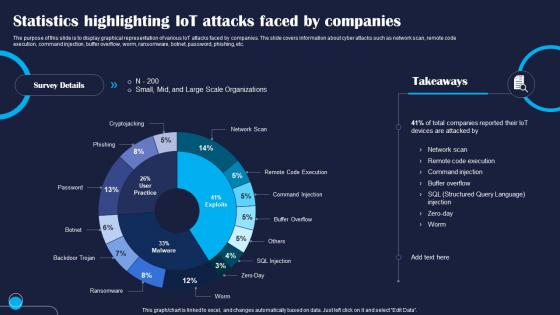 Statistics Highlighting IoT Attacks Faced Improving IoT Device Cybersecurity IoT SS
Statistics Highlighting IoT Attacks Faced Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display graphical representation of various IoT attacks faced by companies. The slide covers information about cyber attacks such as network scan, remote code execution, command injection, buffer overflow, worm, ransomware, botnet, password, phishing, etc. Present the topic in a bit more detail with this Statistics Highlighting IoT Attacks Faced Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Statistics, Injection, Execution. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
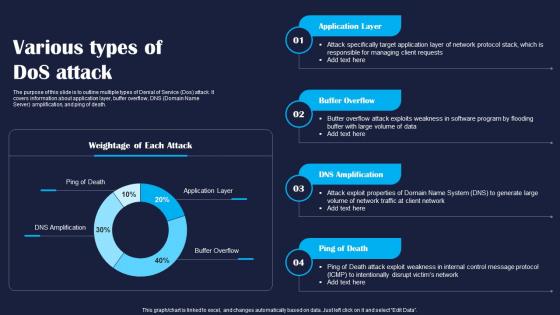 Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SS
Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline multiple types of Denial of Service Dos attack. It covers information about application layer, buffer overflow, DNS Domain Name Server amplification, and ping of death. Deliver an outstanding presentation on the topic using this Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Application, Layer, Death using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
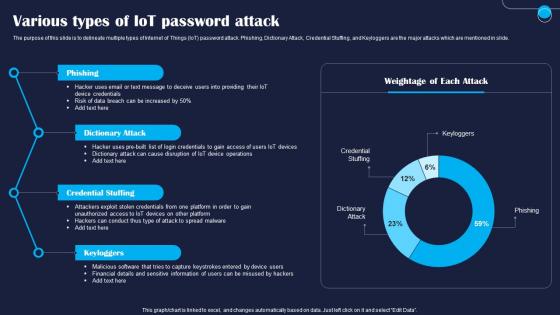 Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS
Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to delineate multiple types of Internet of Things IoT password attack. Phishing, Dictionary Attack, Credential Stuffing, and Keyloggers are the major attacks which are mentioned in slide. Present the topic in a bit more detail with this Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Phishing, Dictionary, Credential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
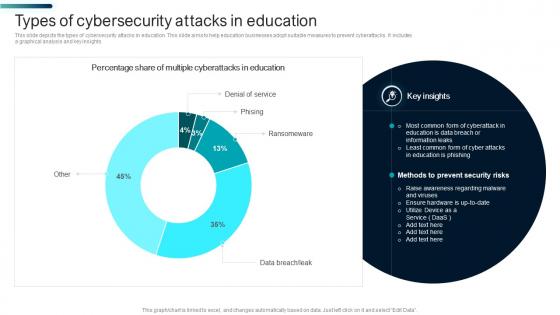 Types Of Cybersecurity Attacks In Education
Types Of Cybersecurity Attacks In EducationThis slide depicts the types of cybersecurity attacks in education. This slide aims to help education businesses adopt suitable measures to prevent cyberattacks. It includes a graphical analysis and key insights Introducing our Types Of Cybersecurity Attacks In Education set of slides. The topics discussed in these slides are Cyberattacks In Education, Education Is Phishing. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Healthcare Cybersecurity Icon For Protection Against Phishing Attacks
Healthcare Cybersecurity Icon For Protection Against Phishing AttacksIntroducing our Healthcare Cybersecurity Icon For Protection Against Phishing Attacks set of slides. The topics discussed in these slides are Healthcare Cybersecurity Icon, Protection Against Phishing Attacks. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
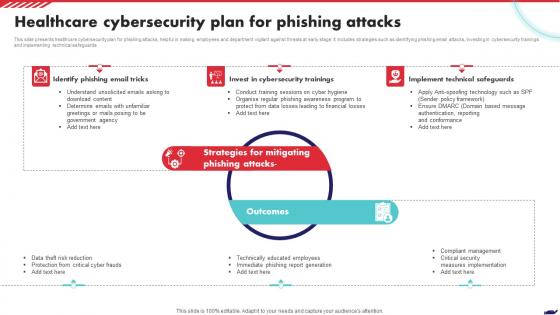 Healthcare Cybersecurity Plan For Phishing Attacks
Healthcare Cybersecurity Plan For Phishing AttacksThis slide presents healthcare cybersecurity plan for phishing attacks, helpful in making employees and department vigilant against threats at early stage. It includes strategies such as identifying phishing email attacks, investing in cybersecurity trainings and implementing technical safeguards Presenting our set of slides with Healthcare Cybersecurity Plan For Phishing Attacks. This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Email Tricks, Cybersecurity Trainings, Technical Safeguards.
-
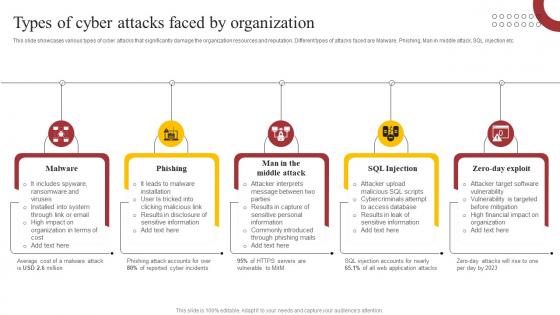 Types Of Cyber Attacks Faced By How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS
Types Of Cyber Attacks Faced By How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SSThis slide showcases various types of cyber attacks that significantly damage the organization resources and reputation. Different types of attacks faced are Malware, Phishing, Man in middle attack, SQL injection etc. Introducing Types Of Cyber Attacks Faced By How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Software, Financial, Results, using this template. Grab it now to reap its full benefits.
-
 Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management
Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks ManagementThe following slide showcases the various types of cyber-attacks faced by employees to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service etc. Introducing Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Spear Phishing, Advanced Persistent Threats, Ransomware, Phishing, using this template. Grab it now to reap its full benefits.
-
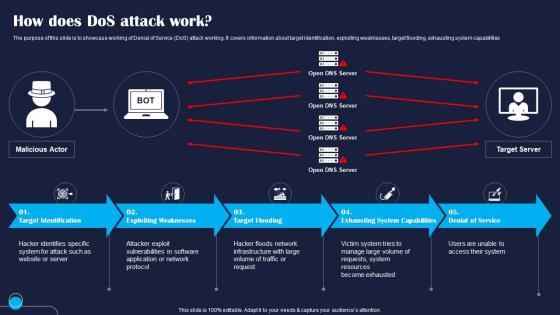 How Does Dos Attack Work Improving IoT Device Cybersecurity IoT SS
How Does Dos Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase working of Denial of Service DoS attack working. It covers information about target identification, exploiting weaknesses, target flooding, exhausting system capabilities Introducing How Does Dos Attack Work Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Target, Exploiting, Flooding, using this template. Grab it now to reap its full benefits.
-
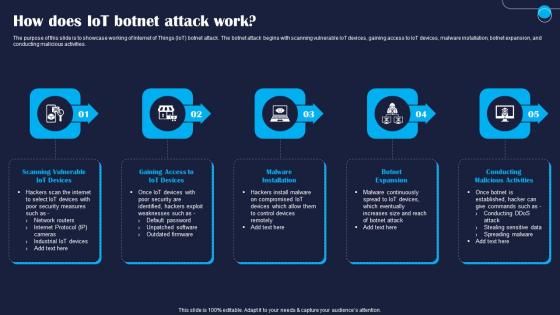 How Does IoT Botnet Attack Work Improving IoT Device Cybersecurity IoT SS
How Does IoT Botnet Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase working of Internet of Things IoT botnet attack. The botnet attack begins with scanning vulnerable IoT devices, gaining access to IoT devices, malware installation, botnet expansion, and conducting malicious activities. Increase audience engagement and knowledge by dispensing information using How Does IoT Botnet Attack Work Improving IoT Device Cybersecurity IoT SS. This template helps you present information on five stages. You can also present information on Devices, Gaining, Installation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
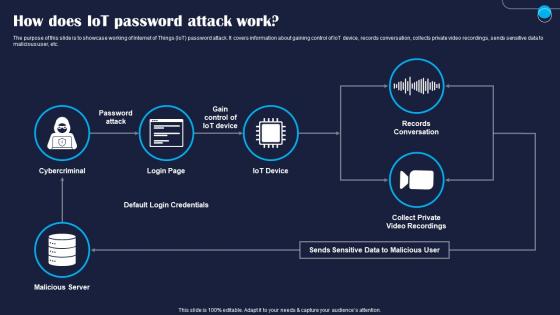 How Does IoT Password Attack Work Improving IoT Device Cybersecurity IoT SS
How Does IoT Password Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase working of Internet of Things IoT password attack. It covers information about gaining control of IoT device, records conversation, collects private video recordings, sends sensitive data to malicious user, etc. Present the topic in a bit more detail with this How Does IoT Password Attack Work Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Cybercriminal, Server, Default. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
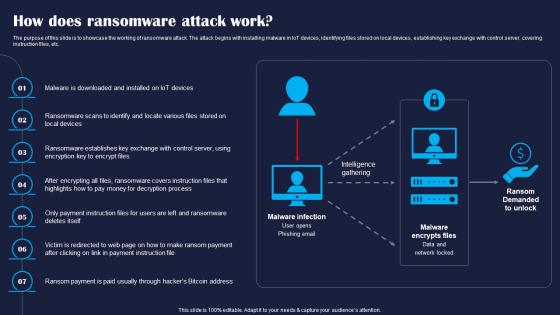 How Does Ransomware Attack Work Improving IoT Device Cybersecurity IoT SS
How Does Ransomware Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase the working of ransomware attack. The attack begins with installing malware in IoT devices, identifying files stored on local devices, establishing key exchange with control server, covering instruction files, etc. Increase audience engagement and knowledge by dispensing information using How Does Ransomware Attack Work Improving IoT Device Cybersecurity IoT SS. This template helps you present information on seven stages. You can also present information on Devices, Exchange, Covers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
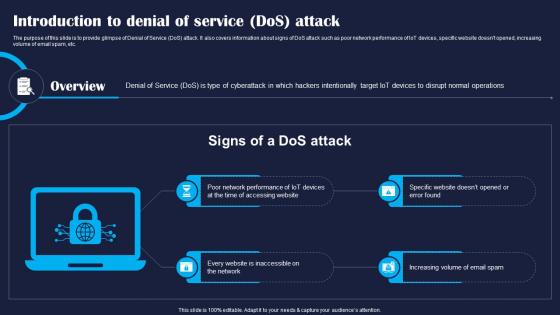 Introduction To Denial Of Service Dos Attack Improving IoT Device Cybersecurity IoT SS
Introduction To Denial Of Service Dos Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to provide glimpse of Denial of Service DoS attack. It also covers information about signs of DoS attack such as poor network performance of IoT devices, specific website doesnt opened, increasing volume of email spam, etc. Increase audience engagement and knowledge by dispensing information using Introduction To Denial Of Service Dos Attack Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Accessing, Website, Increasing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
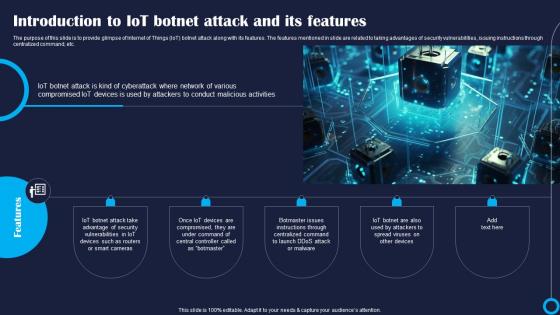 Introduction To IoT Botnet Attack And Its Improving IoT Device Cybersecurity IoT SS
Introduction To IoT Botnet Attack And Its Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to provide glimpse of Internet of Things IoT botnet attack along with its features. The features mentioned in slide are related to taking advantages of security vulnerabilities, issuing instructions through centralized command, etc. Increase audience engagement and knowledge by dispensing information using Introduction To IoT Botnet Attack And Its Improving IoT Device Cybersecurity IoT SS. This template helps you present information on five stages. You can also present information on Vulnerabilities, Compromised, Centralized using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
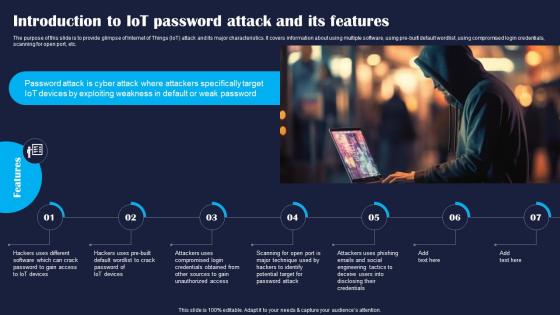 Introduction To IoT Password Attack And Improving IoT Device Cybersecurity IoT SS
Introduction To IoT Password Attack And Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to provide glimpse of Internet of Things IoT attack and its major characteristics. It covers information about using multiple software, using pre built default wordlist, using compromised login credentials, scanning for open port, etc. Increase audience engagement and knowledge by dispensing information using Introduction To IoT Password Attack And Improving IoT Device Cybersecurity IoT SS. This template helps you present information on seven stages. You can also present information on Software, Credentials, Technique using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Introduction To Ransomware Attack And Improving IoT Device Cybersecurity IoT SS
Introduction To Ransomware Attack And Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to provide glimpse of ransomware attack which can cause deny user to access to files on their system. It also covers information abut ransomware attack features such as focusing on industrial control system, smart home devices, etc. Present the topic in a bit more detail with this Introduction To Ransomware Attack And Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Industrial, Software, Functionalities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT Access Points To Malicious Attackers Improving IoT Device Cybersecurity IoT SS
IoT Access Points To Malicious Attackers Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to delineate various Internet of Things IoT access points that can be accessed by hackers. The slide covers information about edge computing, communication network, and cloud computing. Increase audience engagement and knowledge by dispensing information using IoT Access Points To Malicious Attackers Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Devices, Hardware, Commonly using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
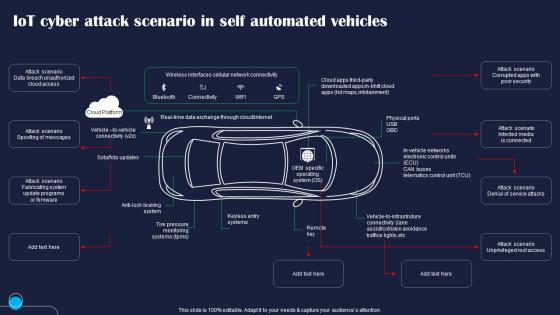 IoT Cyber Attack Scenario In Self Automated Improving IoT Device Cybersecurity IoT SS
IoT Cyber Attack Scenario In Self Automated Improving IoT Device Cybersecurity IoT SSPresent the topic in a bit more detail with this IoT Cyber Attack Scenario In Self Automated Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Systems, Updates, Connectivity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
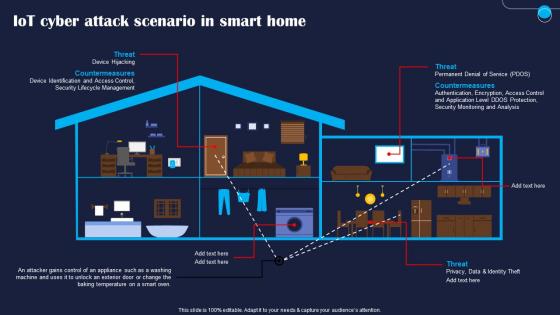 IoT Cyber Attack Scenario In Smart Home Improving IoT Device Cybersecurity IoT SS
IoT Cyber Attack Scenario In Smart Home Improving IoT Device Cybersecurity IoT SSDeliver an outstanding presentation on the topic using this IoT Cyber Attack Scenario In Smart Home Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Identification, Temperature, Identity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
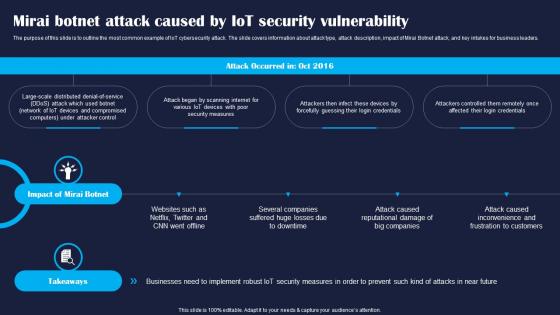 Mirai Botnet Attack Caused By IoT Improving IoT Device Cybersecurity IoT SS
Mirai Botnet Attack Caused By IoT Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline the most common example of IoT cybersecurity attack. The slide covers information about attack type, attack description, impact of Mirai Botnet attack, and key intakes for business leaders. Introducing Mirai Botnet Attack Caused By IoT Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Distributed, Various, Credentials, using this template. Grab it now to reap its full benefits.
-
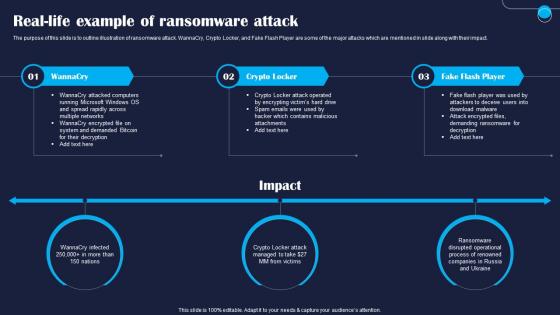 Real Life Example Of Ransomware Attack Improving IoT Device Cybersecurity IoT SS
Real Life Example Of Ransomware Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline illustration of ransomware attack. WannaCry, Crypto Locker, and Fake Flash Player are some of the major attacks which are mentioned in slide along with their impact. Introducing Real Life Example Of Ransomware Attack Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Running, Locker, Player, using this template. Grab it now to reap its full benefits.
-
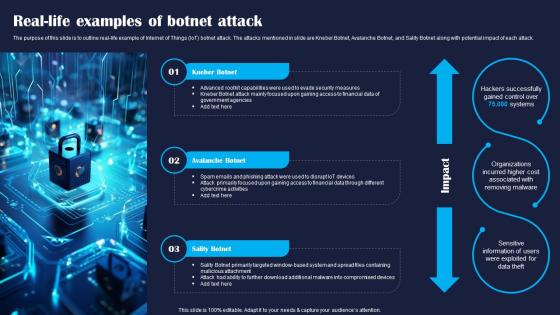 Real Life Examples Of Botnet Attack Improving IoT Device Cybersecurity IoT SS
Real Life Examples Of Botnet Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline real life example of Internet of Things IoT botnet attack. The attacks mentioned in slide are Kneber Botnet, Avalanche Botnet, and Sality Botnet along with potential impact of each attack. Increase audience engagement and knowledge by dispensing information using Real Life Examples Of Botnet Attack Improving IoT Device Cybersecurity IoT SS. This template helps you present information on three stages. You can also present information on Botnet, Avalanche, Attachment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
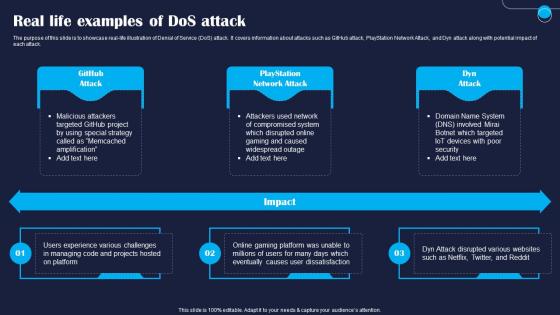 Real Life Examples Of Dos Attack Improving IoT Device Cybersecurity IoT SS
Real Life Examples Of Dos Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase real life illustration of Denial of Service DoS attack. It covers information about attacks such as GitHub attack, PlayStation Network Attack, and Dyn attack along with potential impact of each attack. Introducing Real Life Examples Of Dos Attack Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Attack, Network, Managing, using this template. Grab it now to reap its full benefits.
-
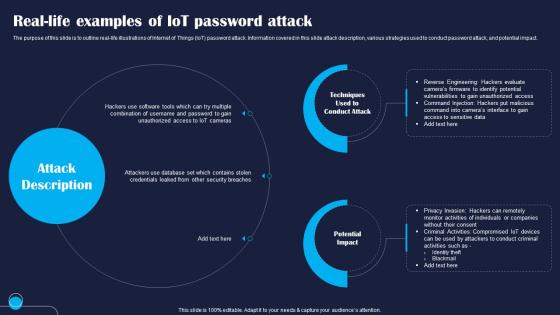 Real Life Examples Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS
Real Life Examples Of IoT Password Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline real life illustrations of Internet of Things IoT password attack. Information covered in this slide attack description, various strategies used to conduct password attack, and potential impact. Increase audience engagement and knowledge by dispensing information using Real Life Examples Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS. This template helps you present information on two stages. You can also present information on Conduct, Techniques, Potential using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Stuxnet Attack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS
Stuxnet Attack Caused By IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight overview of Stuxnet attack caused by Internet of Things IoT security vulnerability. The slide covers information about attack occurred date, its overview, impact of Stuxnet attack, and key takeaways for companies. Introducing Stuxnet Attack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Efficiency, Reduction, Damage, using this template. Grab it now to reap its full benefits.
-
 Types Of Maritime Cybersecurity Attacks On Sensitive Data
Types Of Maritime Cybersecurity Attacks On Sensitive DataThis slide showcases various types of cybersecurity attacks on sensitive data. The main purpose of this template is to highlight various types of attacks, such as phishing attacks, supply chain attacks, data theft, and IoT device exploitation. Presenting our set of slides with Types Of Maritime Cybersecurity Attacks On Sensitive Data. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on IOT Device Exploitation, Supply Chain Attacks, Phishing Attacks.
-
 CTI Cybersecurity Icon To Prevent Malware Infections And Attacks
CTI Cybersecurity Icon To Prevent Malware Infections And AttacksPresenting our set of slides with CTI Cybersecurity Icon To Prevent Malware Infections And Attacks This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on CTI Cybersecurity Icon, Prevent Malware Infections And Attacks
-
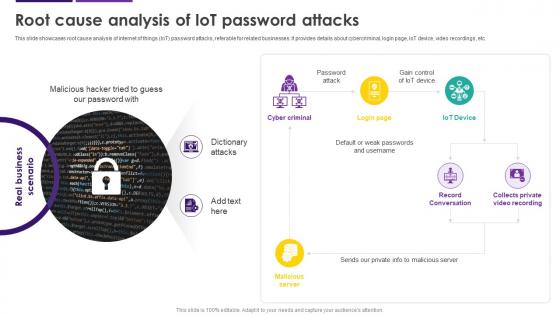 Root Cause Analysis Of IoT Password Attacks Internet Of Things IoT Security Cybersecurity SS
Root Cause Analysis Of IoT Password Attacks Internet Of Things IoT Security Cybersecurity SSThis slide showcases root cause analysis of internet of things IoT password attacks, referable for related businesses. It provides details about cybercriminal, login page, IoT device, video recordings, etc. Increase audience engagement and knowledge by dispensing information using Root Cause Analysis Of IoT Password Attacks Internet Of Things IoT Security Cybersecurity SS. This template helps you present information on two stages. You can also present information on Record Conversation, Password Attack, Cyber Criminal, Root Cause Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
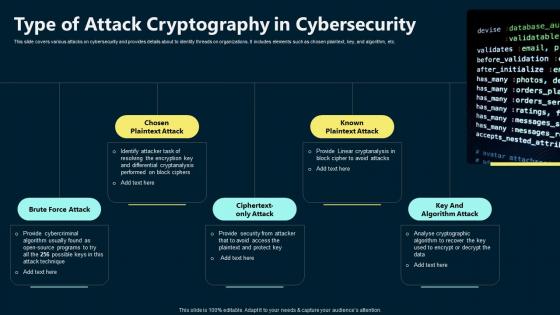 Type Of Attack Cryptography In Cybersecurity
Type Of Attack Cryptography In CybersecurityThis slide covers various attacks on cybersecurity and provides details about to identity threads on organizations. It includes elements such as chosen plaintext, key, and algorithm, etc. Presenting our set of slides with Type Of Attack Cryptography In Cybersecurity. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Brute Force Attack, Key And Algorithm Attack, Known Plaintext Attack.
-
 5G Cybersecurity Icon For Preventing Digital Attacks
5G Cybersecurity Icon For Preventing Digital AttacksIntroducing our 5G Cybersecurity Icon For Preventing Digital Attacks set of slides. The topics discussed in these slides are Preventing, Digital, Cybersecurity. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cybersecurity Infrastructure Icon To Prevent Malware Attacks
Cybersecurity Infrastructure Icon To Prevent Malware AttacksIntroducing our premium set of slides with Cybersecurity Infrastructure Icon To Prevent Malware Attacks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybersecurity Infrastructure, Icon To Prevent, Malware Attacks So download instantly and tailor it with your information.
-
 Navigating Cybersecurity Challenges On Maritime Attacks
Navigating Cybersecurity Challenges On Maritime AttacksThis slide represents maritime cybersecurity challenges for protecting human lives, securing assets, and maintaining overall stability of industry. It includes bases such as date, victim, location, incident type, and malware. Presenting our well structured Navigating Cybersecurity Challenges On Maritime Attacks The topics discussed in this slide are Victim, Location, Incident Type This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Attacks Faced By Organization Previous Cybersecurity Risk Analysis And Management Plan
Cyber Attacks Faced By Organization Previous Cybersecurity Risk Analysis And Management PlanThis slide showcases information security attacks faced by organization in past financial year. It can help company to assess different type of cyber attacks and formulate strategies to tackle them. Deliver an outstanding presentation on the topic using this Cyber Attacks Faced By Organization Previous Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Organization, Financial Year, Experienced using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan
Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection Present the topic in a bit more detail with this Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Information, Security Attacks, Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Attacks Faced By Organization In Previous Financial Year Formulating Cybersecurity Plan
Cyber Attacks Faced By Organization In Previous Financial Year Formulating Cybersecurity PlanThis slide showcases information security attacks faced by organization in past financial year. It can help company to assess different type of cyber attacks and formulate strategies to tackle them. Deliver an outstanding presentation on the topic using this Cyber Attacks Faced By Organization In Previous Financial Year Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Cyber Attacks, Organization, Financial Year using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
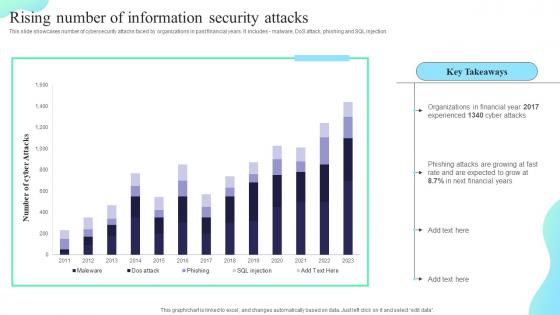 Rising Number Of Information Security Attacks Formulating Cybersecurity Plan
Rising Number Of Information Security Attacks Formulating Cybersecurity PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection. Deliver an outstanding presentation on the topic using this Rising Number Of Information Security Attacks Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Rising Number, Information Security, Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
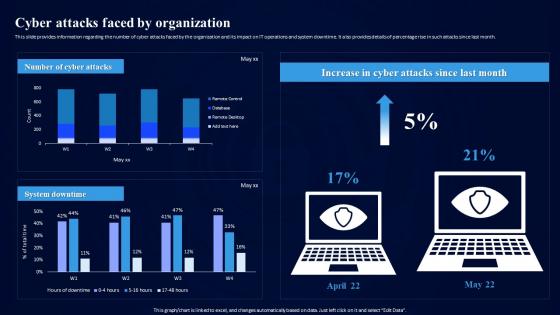 Cybersecurity Risk Assessment Program Cyber Attacks Faced By Organization
Cybersecurity Risk Assessment Program Cyber Attacks Faced By OrganizationThis slide provides information regarding the number of cyber attacks faced by the organization and its impact on IT operations and system downtime. It also provides details of percentage rise in such attacks since last month. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Cyber Attacks Faced By Organization. Use it as a tool for discussion and navigation on Cyber Attacks, IT Operations, System Downtime. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk Levels
Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk Levels. Dispense information and present a thorough explanation of Infrastructure Controls, Preventive Controls, Detective Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
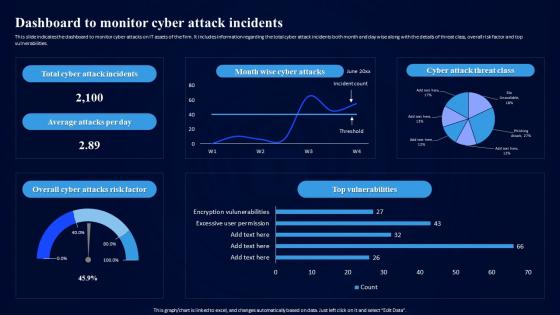 Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents
Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents. Use it as a tool for discussion and navigation on Dashboard To Monitor, Cyber Attack Incidents, Vulnerabilities, Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
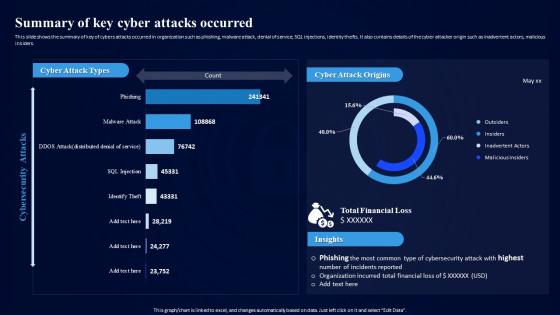 Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks Occurred
Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cyber Attacks Occurred, Financial Loss, Cyber Attack Origins. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
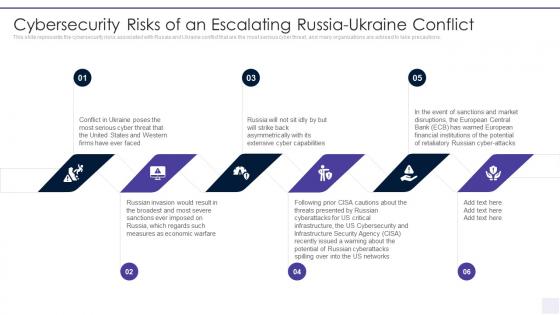
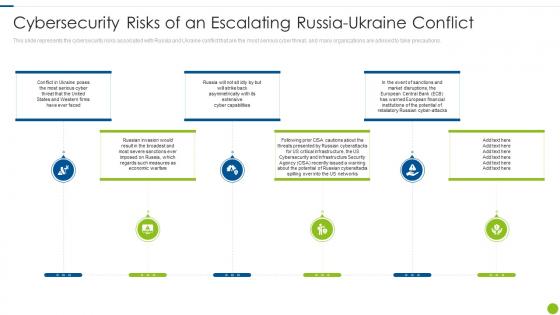 Cyber Attacks On Ukraine Cybersecurity Risks Of An Escalating Russia Ukraine Conflict
Cyber Attacks On Ukraine Cybersecurity Risks Of An Escalating Russia Ukraine ConflictThis slide represents the cybersecurity risks associated with Russia and Ukraine conflict that are the most serious cyber threat, and many organizations are advised to take precautions. Introducing Cyber Attacks On Ukraine Cybersecurity Risks Of An Escalating Russia Ukraine Conflict to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Infrastructure, Cybersecurity, Potential, Cyberattacks, Financial, using this template. Grab it now to reap its full benefits.
-
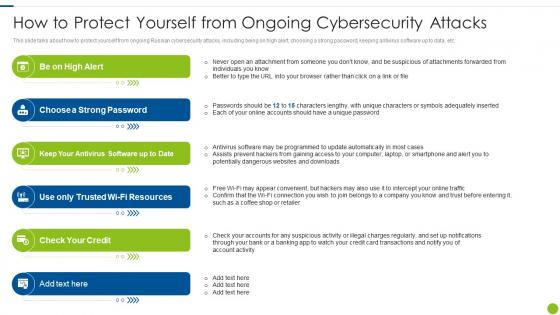 Cyber Attacks On Ukraine How To Protect Yourself From Ongoing Cybersecurity
Cyber Attacks On Ukraine How To Protect Yourself From Ongoing CybersecurityThis slide talks about how to protect yourself from ongoing Russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Increase audience engagement and knowledge by dispensing information using Cyber Attacks On Ukraine How To Protect Yourself From Ongoing Cybersecurity. This template helps you present information on six stages. You can also present information on Suspicious, Individuals, Adequately, Programmed using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Wiper Malware Attack Cybersecurity Risks Of An Escalating Russia
Wiper Malware Attack Cybersecurity Risks Of An Escalating RussiaThis slide represents the cybersecurity risks associated with Russia and Ukraine conflict that are the most serious cyber threat, and many organizations are advised to take precautions. Introducing Wiper Malware Attack Cybersecurity Risks Of An Escalating Russia to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risks Of An Escalating Russia Ukraine Conflict, using this template. Grab it now to reap its full benefits.
-
 Ukraine and russia cyber warfare it how to protect yourself from ongoing cybersecurity attacks
Ukraine and russia cyber warfare it how to protect yourself from ongoing cybersecurity attacksThis slide talks about how to protect yourself from ongoing Russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Introducing Ukraine And Russia Cyber Warfare It How To Protect Yourself From Ongoing Cybersecurity Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Resources, Antivirus, Software, using this template. Grab it now to reap its full benefits.
-
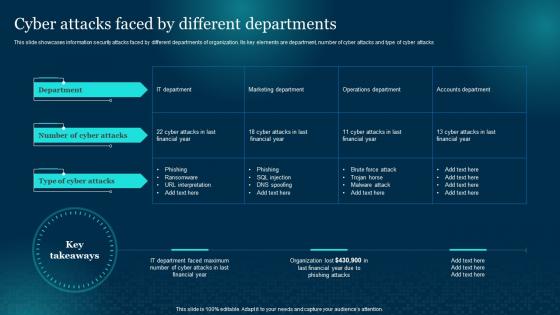 Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different Departments
Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different DepartmentsThis slide showcases information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks Present the topic in a bit more detail with this Cybersecurity Risk Analysis And Management Plan Cyber Attacks Faced By Different Departments. Use it as a tool for discussion and navigation on Departments, Information, Cyber Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.


