Powerpoint Templates and Google slides for Cybersecurity Work Home
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
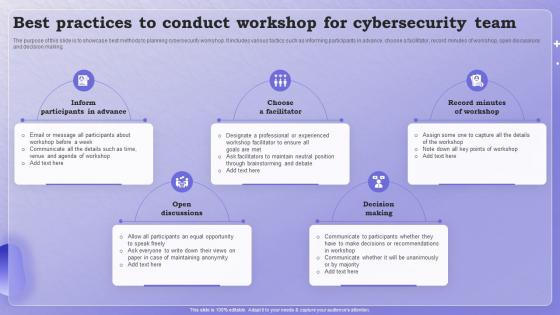 Best Practices To Conduct Workshop For Cybersecurity Team
Best Practices To Conduct Workshop For Cybersecurity TeamThe purpose of this slide is to showcase best methods to planning cybersecurity workshop. It includes various tactics such as informing participants in advance, choose a facilitator, record minutes of workshop, open discussions and decision making. Presenting our set of slides with Best Practices To Conduct Workshop For Cybersecurity Team. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Open Discussions, Decision Making.
-
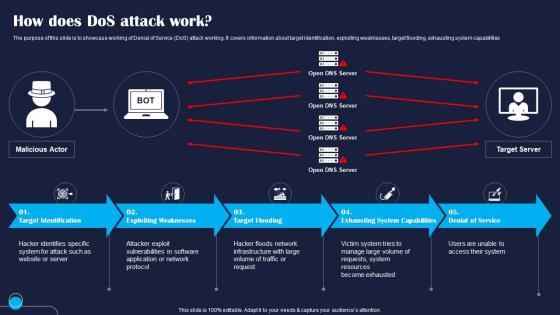 How Does Dos Attack Work Improving IoT Device Cybersecurity IoT SS
How Does Dos Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase working of Denial of Service DoS attack working. It covers information about target identification, exploiting weaknesses, target flooding, exhausting system capabilities Introducing How Does Dos Attack Work Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Target, Exploiting, Flooding, using this template. Grab it now to reap its full benefits.
-
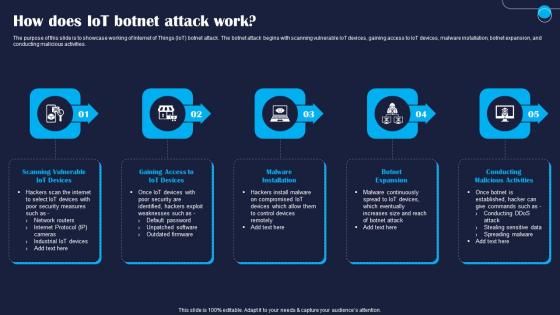 How Does IoT Botnet Attack Work Improving IoT Device Cybersecurity IoT SS
How Does IoT Botnet Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase working of Internet of Things IoT botnet attack. The botnet attack begins with scanning vulnerable IoT devices, gaining access to IoT devices, malware installation, botnet expansion, and conducting malicious activities. Increase audience engagement and knowledge by dispensing information using How Does IoT Botnet Attack Work Improving IoT Device Cybersecurity IoT SS. This template helps you present information on five stages. You can also present information on Devices, Gaining, Installation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
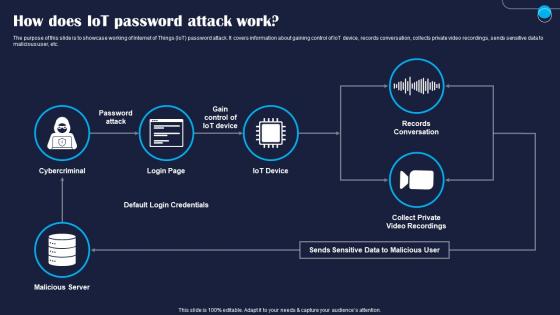 How Does IoT Password Attack Work Improving IoT Device Cybersecurity IoT SS
How Does IoT Password Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase working of Internet of Things IoT password attack. It covers information about gaining control of IoT device, records conversation, collects private video recordings, sends sensitive data to malicious user, etc. Present the topic in a bit more detail with this How Does IoT Password Attack Work Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Cybercriminal, Server, Default. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
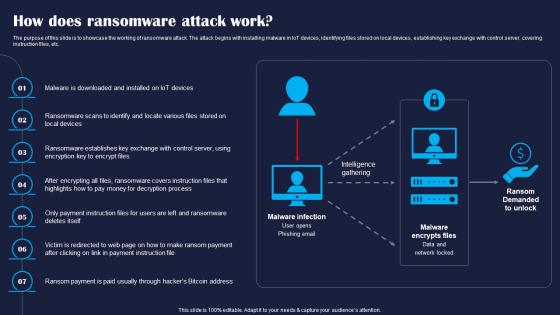 How Does Ransomware Attack Work Improving IoT Device Cybersecurity IoT SS
How Does Ransomware Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase the working of ransomware attack. The attack begins with installing malware in IoT devices, identifying files stored on local devices, establishing key exchange with control server, covering instruction files, etc. Increase audience engagement and knowledge by dispensing information using How Does Ransomware Attack Work Improving IoT Device Cybersecurity IoT SS. This template helps you present information on seven stages. You can also present information on Devices, Exchange, Covers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
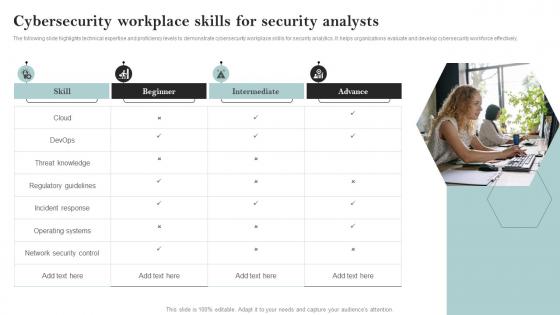 Cybersecurity Workplace Skills For Security Analysts
Cybersecurity Workplace Skills For Security AnalystsThe following slide highlights technical expertise and proficiency levels to demonstrate cybersecurity workplace skills for security analytics. It helps organizations evaluate and develop cybersecurity workforce effectively. Presenting our set of slides with Cybersecurity Workplace Skills For Security Analysts. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cybersecurity, Skills, Security.
-
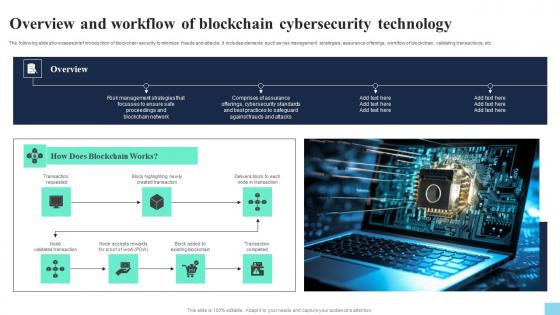 Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V
Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS VThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Increase audience engagement and knowledge by dispensing information using Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V. This template helps you present information on seven stages. You can also present information on Transaction Requested, Created Transaction, Existing Blockchain using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
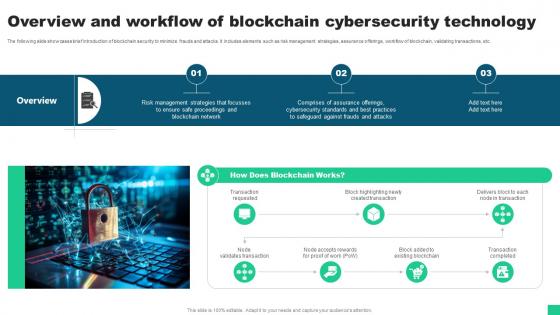 Overview And Workflow Of Blockchain Cybersecurity Technology Guide For Blockchain BCT SS V
Overview And Workflow Of Blockchain Cybersecurity Technology Guide For Blockchain BCT SS VThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Introducing Overview And Workflow Of Blockchain Cybersecurity Technology Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Blockchain Works, Transaction Completed using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Overview And Workflow Of Blockchain Cybersecurity Technology BCT SS V
Cyber Threats In Blockchain Overview And Workflow Of Blockchain Cybersecurity Technology BCT SS VThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Overview And Workflow Of Blockchain Cybersecurity Technology BCT SS V This template helps you present information on One stages. You can also present information on Node Validates Transaction, Existing Blockchain, Transaction Completed using this PPT design. This layout is completely editable so personaize it now
-
 Working Model Of SCADA Cybersecurity For Data Protection
Working Model Of SCADA Cybersecurity For Data ProtectionThis slide represents working model of SCADA cybersecurity that assists IT companies to secure their data from vulnerable attacks. It includes various components such as impact analysis, mitigation strategies, etc. Presenting our well structured Working Model Of SCADA Cybersecurity For Data Protection The topics discussed in this slide are Remedial, Prevention, Decision Making. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
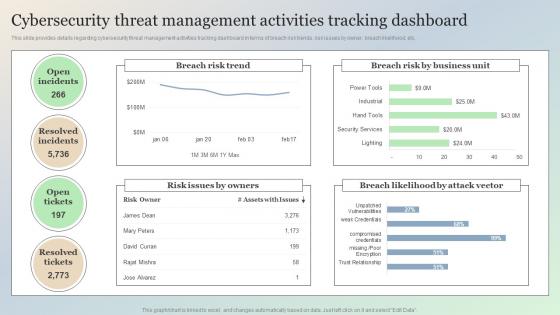 Cybersecurity Threat Management Activities Tracking Dashboard Managing IT Threats At Workplace Overview
Cybersecurity Threat Management Activities Tracking Dashboard Managing IT Threats At Workplace OverviewThis slide provides details regarding cybersecurity threat management activities tracking dashboard in terms of breach risk trends, risk issues by owner, breach likelihood, etc. Present the topic in a bit more detail with this Cybersecurity Threat Management Activities Tracking Dashboard Managing IT Threats At Workplace Overview. Use it as a tool for discussion and navigation on Cybersecurity, Management, Tracking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
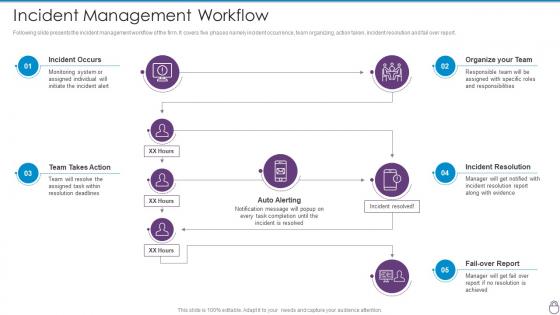 Cybersecurity Risk Management Framework Incident Management Workflow
Cybersecurity Risk Management Framework Incident Management WorkflowFollowing slide presents the incident management workflow of the firm. It covers five phases namely incident occurrence, team organizing, action taken, incident resolution and fail over report. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Incident Management Workflow. Dispense information and present a thorough explanation of Incident Occurs, Organize Team, Team Action, Incident Resolution, Fail Over Report using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
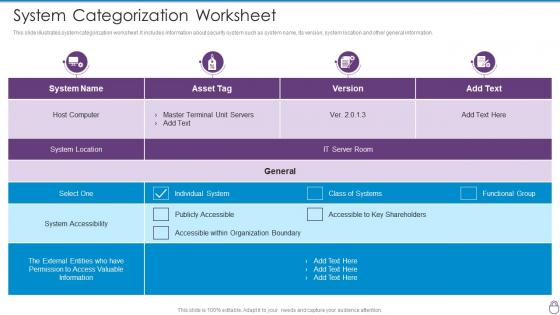 Cybersecurity Risk Management Framework System Categorization Worksheet
Cybersecurity Risk Management Framework System Categorization WorksheetThis slide illustrates system categorization worksheet. It includes information about security system such as system name, its version, system location and other general information. Present the topic in a bit more detail with this Cybersecurity Risk Management Framework System Categorization Worksheet. Use it as a tool for discussion and navigation on Host Computer, System Location, System Accessibility, Asset Tag. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
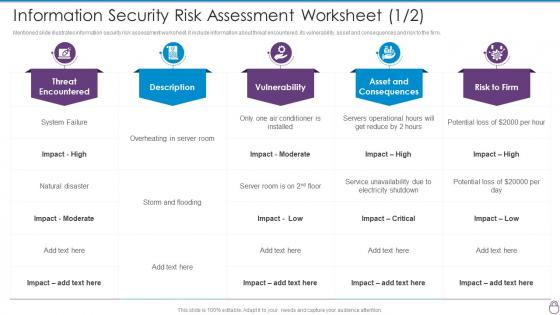 Information Security Risk Assessment Worksheet Cybersecurity Risk Management Framework
Information Security Risk Assessment Worksheet Cybersecurity Risk Management FrameworkMentioned slide illustrates information security risk assessment worksheet. It include information about threat encountered, its vulnerability, asset and consequences and risk to the firm. Present the topic in a bit more detail with this Information Security Risk Assessment Worksheet Cybersecurity Risk Management Framework. Use it as a tool for discussion and navigation on Threat Encountered, Vulnerability, Asset And Consequences, Risk To Firm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
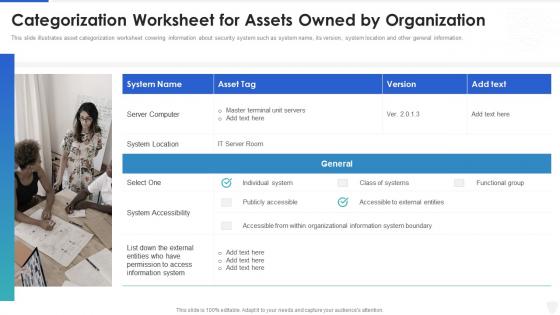 Cybersecurity and digital business risk management categorization worksheet for assets
Cybersecurity and digital business risk management categorization worksheet for assetsThis slide illustrates asset categorization worksheet covering information about security system such as system name, its version, system location and other general information. Increase audience engagement and knowledge by dispensing information using Cybersecurity And Digital Business Risk Management Categorization Worksheet For Assets. This template helps you present information on one stages. You can also present information on Organization, Information, Location using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
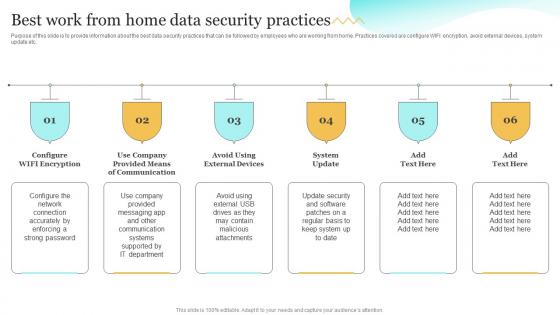 Best Work From Home Data Security Practices Upgrading Cybersecurity With Incident Response Playbook
Best Work From Home Data Security Practices Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to provide information about the best data security practices that can be followed by employees who are working from home. Practices covered are configure WIFI encryption, avoid external devices, system update etc. Introducing Best Work From Home Data Security Practices Upgrading Cybersecurity With Incident Response Playbook to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Communication, Attachments, Department, using this template. Grab it now to reap its full benefits.
-
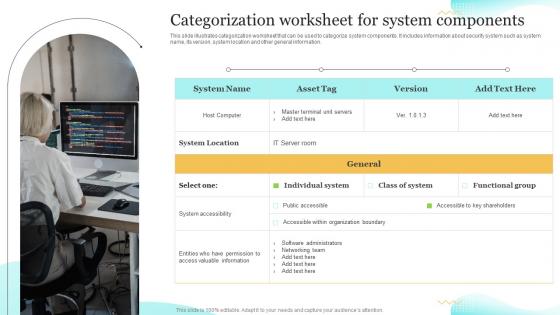 Categorization Worksheet For System Components Upgrading Cybersecurity With Incident Response Playbook
Categorization Worksheet For System Components Upgrading Cybersecurity With Incident Response PlaybookThis slide illustrates categorization worksheet that can be used to categorize system components. It includes information about security system such as system name, its version, system location and other general information. Present the topic in a bit more detail with this Categorization Worksheet For System Components Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Categorization, Components, Worksheet. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
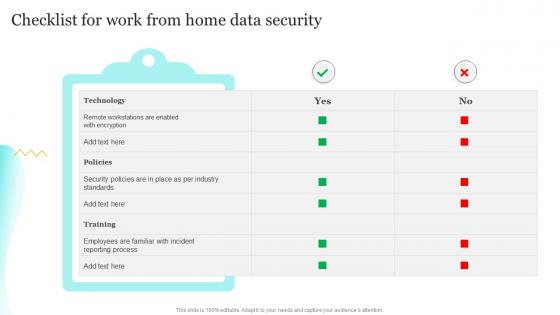 Checklist For Work From Home Data Security Upgrading Cybersecurity With Incident Response Playbook
Checklist For Work From Home Data Security Upgrading Cybersecurity With Incident Response PlaybookDeliver an outstanding presentation on the topic using this Checklist For Work From Home Data Security Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Process, Technology, Standards using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
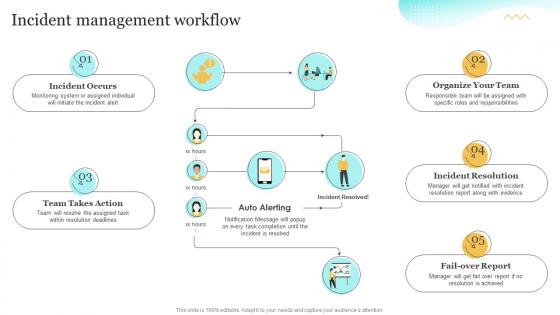 Incident Management Workflow Upgrading Cybersecurity With Incident Response Playbook
Incident Management Workflow Upgrading Cybersecurity With Incident Response PlaybookDeliver an outstanding presentation on the topic using this Incident Management Workflow Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Management Workflow, Incident Resolution, Organize Your Team using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Work From Home Data Security Practices Cybersecurity Incident And Vulnerability
Best Work From Home Data Security Practices Cybersecurity Incident And VulnerabilityPurpose of this slide is to provide information about the best data security practices that can be followed by employees who are working from home. Practices covered are configure WIFI encryption, avoid external devices, system update etc. Introducing Best Work From Home Data Security Practices Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Configure WIFI Encryption, Avoid Using External Devices, System Update, using this template. Grab it now to reap its full benefits.
-
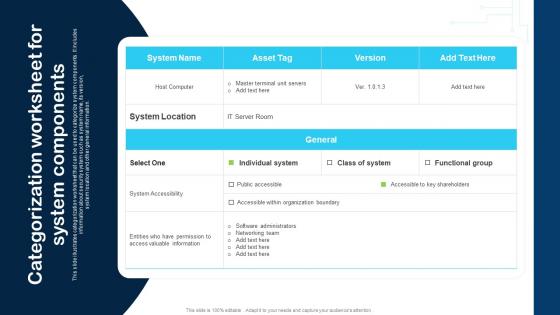 Categorization Worksheet For System Components Cybersecurity Incident And Vulnerability
Categorization Worksheet For System Components Cybersecurity Incident And VulnerabilityThis slide illustrates categorization worksheet that can be used to categorize system components. It includes information about security system such as system name, its version, system location and other general information. Present the topic in a bit more detail with this Categorization Worksheet For System Components Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on System Location, System Accessibility, IT Server Room. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
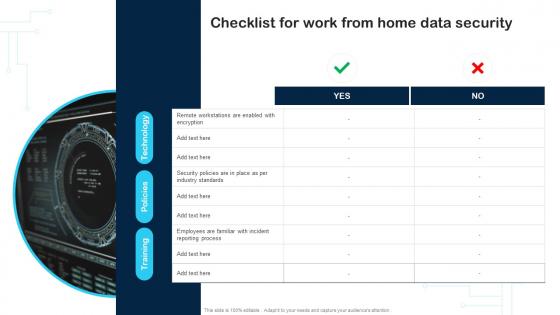 Checklist For Work From Home Data Security Cybersecurity Incident And Vulnerability
Checklist For Work From Home Data Security Cybersecurity Incident And VulnerabilityDeliver an outstanding presentation on the topic using this Checklist For Work From Home Data Security Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Data Security, Reporting Process, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Incident Management Workflow Cybersecurity Incident And Vulnerability Response Playbook
Incident Management Workflow Cybersecurity Incident And Vulnerability Response PlaybookPresent the topic in a bit more detail with this Incident Management Workflow Cybersecurity Incident And Vulnerability Response Playbook. Use it as a tool for discussion and navigation on Incident Occurs, Team Takes Action, Organize Your Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
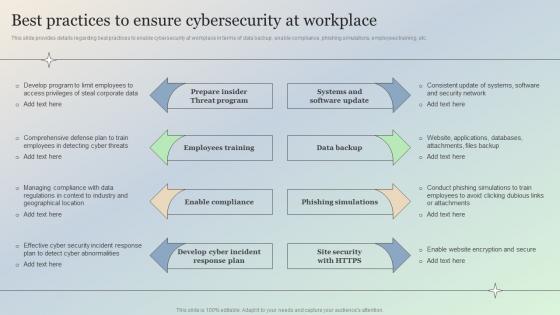 Best Practices To Ensure Cybersecurity At Workplace Managing IT Threats At Workplace Overview
Best Practices To Ensure Cybersecurity At Workplace Managing IT Threats At Workplace OverviewThis slide provides details regarding best practices to enable cybersecurity at workplace in terms of data backup, enable compliance, phishing simulations, employees training, etc. Introducing Best Practices To Ensure Cybersecurity At Workplace Managing IT Threats At Workplace Overview to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Develop, Security, using this template. Grab it now to reap its full benefits.
-
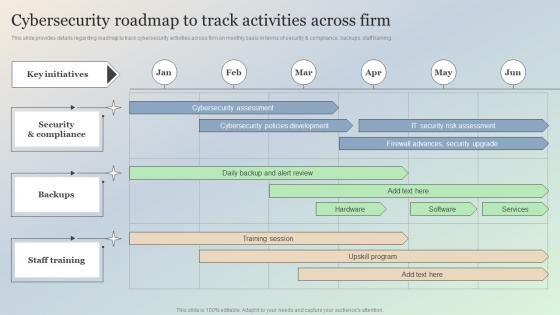 Cybersecurity Roadmap To Track Activities Across Firm Managing IT Threats At Workplace Overview
Cybersecurity Roadmap To Track Activities Across Firm Managing IT Threats At Workplace OverviewThis slide provides details regarding roadmap to track cybersecurity activities across firm on monthly basis in terms of security and compliance, backups, staff training. Deliver an outstanding presentation on the topic using this Cybersecurity Roadmap To Track Activities Across Firm Managing IT Threats At Workplace Overview. Dispense information and present a thorough explanation of Security, Backups, Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enable Cybersecurity Compliance At Organization Managing IT Threats At Workplace Overview
Enable Cybersecurity Compliance At Organization Managing IT Threats At Workplace OverviewThis slide provides details regarding role of cybersecurity compliance at workplace. The importance of the security compliance include management of user trust, enhance business efficiency, secure brand reputation, etc. Increase audience engagement and knowledge by dispensing information using Enable Cybersecurity Compliance At Organization Managing IT Threats At Workplace Overview. This template helps you present information on eight stages. You can also present information on Cybersecurity, Confidentiality, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Highlighting Ongoing Cybersecurity Trends Across Globe Managing IT Threats At Workplace Overview
Highlighting Ongoing Cybersecurity Trends Across Globe Managing IT Threats At Workplace OverviewThis slide provides details regarding cybersecurity trends existing across globe in terms of rise in automotive hacking, IoT with 5G, cloud platform as potential vulnerable, etc. Introducing Highlighting Ongoing Cybersecurity Trends Across Globe Managing IT Threats At Workplace Overview to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Automotive, Artificial, Potential, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Work Home In Powerpoint And Google Slides Cpb
Cybersecurity Work Home In Powerpoint And Google Slides CpbPresenting our Cybersecurity Work Home In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Cybersecurity Work Home This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cybersecurity Incident Action Plan Workflow
Cybersecurity Incident Action Plan WorkflowThis slide presents workflow for cybersecurity incident action plan, helpful in determining basic streams of work involved in crisis management. It includes detection, containment, eradication and lessons learned. Presenting our set of slides with Cybersecurity Incident Action Plan Workflow. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detection, Containment, Eradication.
-
 Ultimate Guide For Blockchain Overview And Workflow Of Blockchain Cybersecurity BCT SS
Ultimate Guide For Blockchain Overview And Workflow Of Blockchain Cybersecurity BCT SSThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Present the topic in a bit more detail with this Ultimate Guide For Blockchain Overview And Workflow Of Blockchain Cybersecurity BCT SS Use it as a tool for discussion and navigation on Frauds And Attacks, Blockchain Network This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity incident response workflow system ppt powerpoint presentation infographics graphics tutorials cpb
Cybersecurity incident response workflow system ppt powerpoint presentation infographics graphics tutorials cpbPresenting this set of slides with name Cybersecurity Incident Response Workflow System Ppt Powerpoint Presentation Infographics Graphics Tutorials Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Cybersecurity Incident Response Workflow System to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
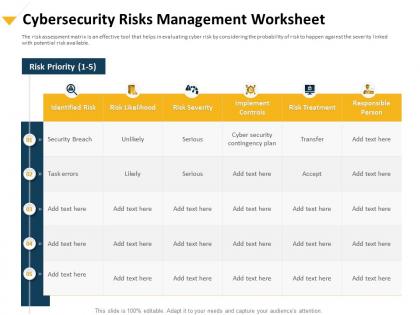 Cybersecurity risks management worksheet implement controls ppt portfolio
Cybersecurity risks management worksheet implement controls ppt portfolioThe risk assessment matrix is an effective tool that helps in evaluating cyber risk by considering the probability of risk to happen against the severity linked with potential risk available. Presenting this set of slides with name Cybersecurity Risks Management Worksheet Implement Controls Ppt Portfolio. The topics discussed in these slides are Cybersecurity Risks, Management, Worksheet, Implement Controls. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cybersecurity checklist during remote working for employees ppt powerpoint grid
Cybersecurity checklist during remote working for employees ppt powerpoint gridThis slide provides cybersecurity checklist for employees while they are doing remote working or work from home. Presenting this set of slides with name Cybersecurity Checklist During Remote Working For Employees Ppt Powerpoint Grid. This is a eleven stage process. The stages in this process are Cybersecurity Checklist During Remote Working For Employees. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
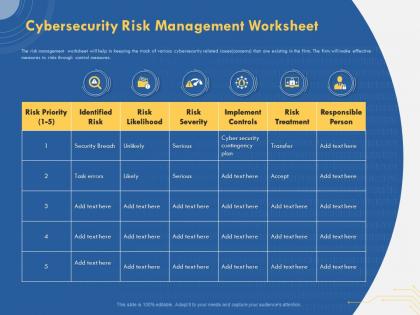 Cybersecurity risk management worksheet risk ppt powerpoint presentation template
Cybersecurity risk management worksheet risk ppt powerpoint presentation templateThe risk management worksheet will help in keeping the track of various cybersecurity related issues concerns that are existing in the firm. The firm will make effective measures to risks through control measures. Presenting this set of slides with name Cybersecurity Risk Management Worksheet Risk Ppt Powerpoint Presentation Template. The topics discussed in these slides are Cybersecurity, Risk Management, Worksheet Risk. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cybersecurity risk management worksheet security ppt file topics
Cybersecurity risk management worksheet security ppt file topicsThe risk management worksheet will help in keeping the track of various cybersecurity related issues concerns that are existing in the firm. The firm will make effective measures to risks through control measures. Presenting this set of slides with name Cybersecurity Risk Management Worksheet Security Ppt File Topics. The topics discussed in these slides are Identified Risk, Risk Likelihood, Risk Severity, Implement Controls, Risk Treatment. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cybersecurity incident response workflow ppt powerpoint presentation outline layout ideas cpb
Cybersecurity incident response workflow ppt powerpoint presentation outline layout ideas cpbPresenting our Cybersecurity Incident Response Workflow Ppt Powerpoint Presentation Outline Layout Ideas Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Cybersecurity Incident Response Workflow This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.

