Powerpoint Templates and Google slides for Data Breachs
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
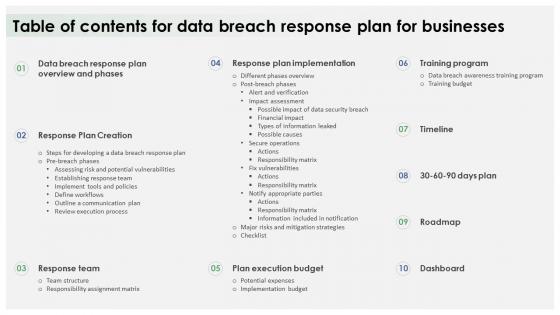 Table Of Contents For Data Breach Response Plan For Businesses
Table Of Contents For Data Breach Response Plan For BusinessesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Data Breach Response Plan For Businesses. This template helps you present information on ten stages. You can also present information on Response Plan Creation, Response Team, Plan Execution Budget, Training Program, Response Plan Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
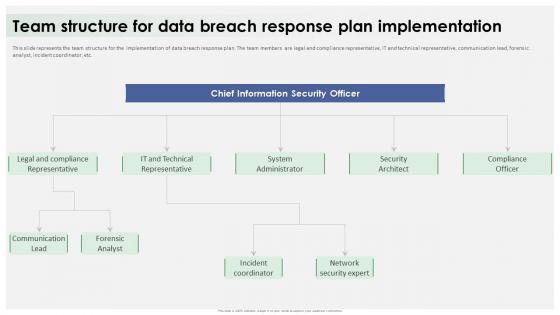 Team Structure For Data Breach Response Plan Implementation
Team Structure For Data Breach Response Plan ImplementationThis slide represents the team structure for the implementation of data breach response plan. The team members are legal and compliance representative, IT and technical representative, communication lead, forensic analyst, incident coordinator, etc. Introducing Team Structure For Data Breach Response Plan Implementation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Team Structure, Data Breach Response Plan, Legal And Compliance Representative, Forensic Analyst, using this template. Grab it now to reap its full benefits.
-
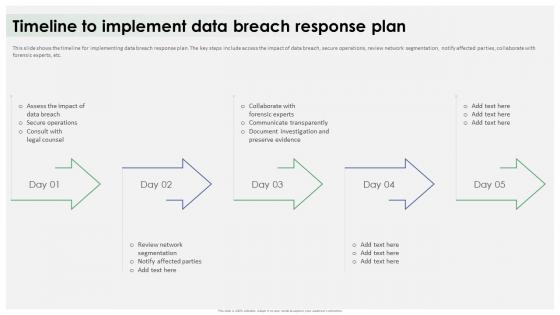 Timeline To Implement Data Breach Response Plan Ppt Icon Graphic Images
Timeline To Implement Data Breach Response Plan Ppt Icon Graphic ImagesThis slide shows the timeline for implementing data breach response plan. The key steps include access the impact of data breach, secure operations, review network segmentation, notify affected parties, collaborate with forensic experts, etc. Increase audience engagement and knowledge by dispensing information using Timeline To Implement Data Breach Response Plan Ppt Icon Graphic Images. This template helps you present information on five stages. You can also present information on Data Breach Response Plan, Secure Operations, Review Network Segmentation, Collaborate With Forensic Experts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Icon For Insurancing Data Breaches
Cyber Security Icon For Insurancing Data BreachesPresenting our set of slides with Cyber Security Icon For Insurancing Data Breaches. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Icon, Insurancing Data Breaches.
-
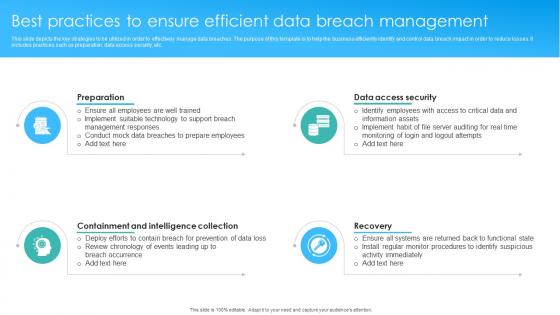 Best Practices To Ensure Efficient Data Breach Management
Best Practices To Ensure Efficient Data Breach ManagementThis slide depicts the key strategies to be utilized in order to effectively manage data breaches. The purpose of this template is to help the business efficiently identify and control data breach impact in order to reduce losses. It includes practices such as preparation, data access security, etc. Presenting our set of slides with Best Practices To Ensure Efficient Data Breach Management. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify Employees With Access, Ensure All Employees, Conduct Mock Data Breaches.
-
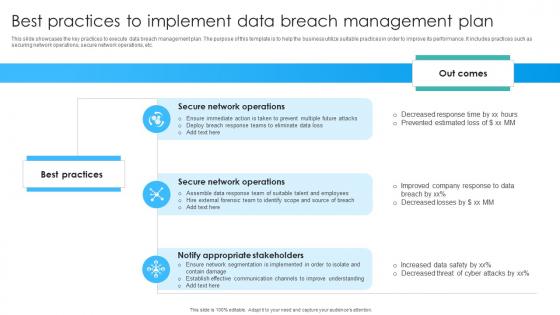 Best Practices To Implement Data Breach Management Plan
Best Practices To Implement Data Breach Management PlanThis slide showcases the key practices to execute data breach management plan. The purpose of this template is to help the business utilize suitable practices in order to improve its performance. It includes practices such as securing network operations, secure network operations, etc. Introducing our premium set of slides with Best Practices To Implement Data Breach Management Plan. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Secure Network Operations, Secure Network Operations, Notify Appropriate Stakeholders. So download instantly and tailor it with your information.
-
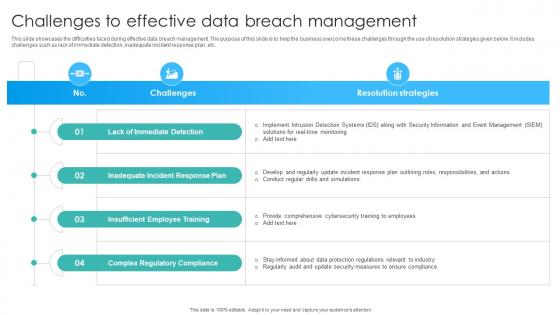 Challenges To Effective Data Breach Management
Challenges To Effective Data Breach ManagementThis slide showcases the difficulties faced during effective data breach management. The purpose of this slide is to help the business overcome these challenges through the use of resolution strategies given below. It includes challenges such as lack of immediate detection, inadequate incident response plan, etc. Introducing our Challenges To Effective Data Breach Management set of slides. The topics discussed in these slides are Lack Of Immediate Detection, Inadequate Incident Response Plan, Insufficient Employee Training. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
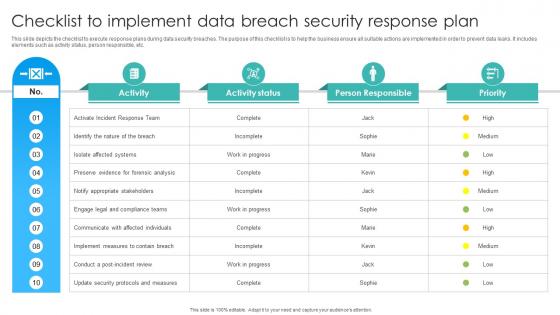 Checklist To Implement Data Breach Security Response Plan
Checklist To Implement Data Breach Security Response PlanThis slide depicts the checklist to execute response plans during data security breaches. The purpose of this checklist is to help the business ensure all suitable actions are implemented in order to prevent data leaks. It includes elements such as activity status, person responsible, etc. Presenting our well structured Checklist To Implement Data Breach Security Response Plan. The topics discussed in this slide are Isolate Affected Systems, Notify Appropriate Stakeholders, Identify The Nature. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
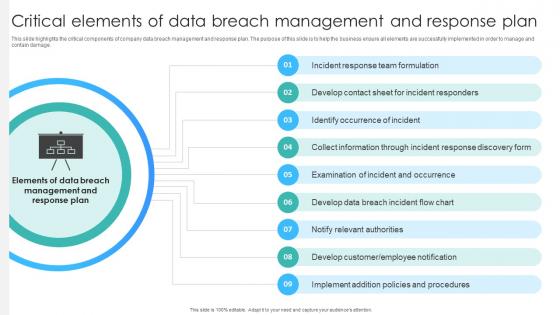 Critical Elements Of Data Breach Management And Response Plan
Critical Elements Of Data Breach Management And Response PlanThis slide highlights the critical components of company data breach management and response plan. The purpose of this slide is to help the business ensure all elements are successfully implemented in order to manage and contain damage. Presenting our set of slides with Critical Elements Of Data Breach Management And Response Plan. This exhibits information on nine stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Incident Response Team Formulation, Identify Occurrence Of Incident, Notify Relevant Authorities .
-
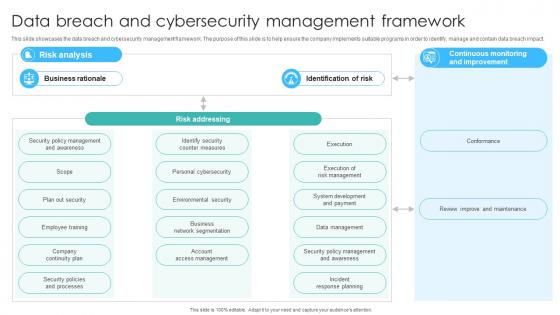 Data Breach And Cybersecurity Management Framework
Data Breach And Cybersecurity Management FrameworkThis slide showcases the data breach and cybersecurity management framework. The purpose of this slide is to help ensure the company implements suitable programs in order to identify, manage and contain data breach impact. Introducing our Data Breach And Cybersecurity Management Framework set of slides. The topics discussed in these slides are Personal Cybersecurity, Environmental Security, Execution Of Risk Management . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data Breach Management And Recovery Icon
Data Breach Management And Recovery IconIntroducing our premium set of slides with Data Breach Management And Recovery Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Breach, Management, Recovery Icon. So download instantly and tailor it with your information.
-
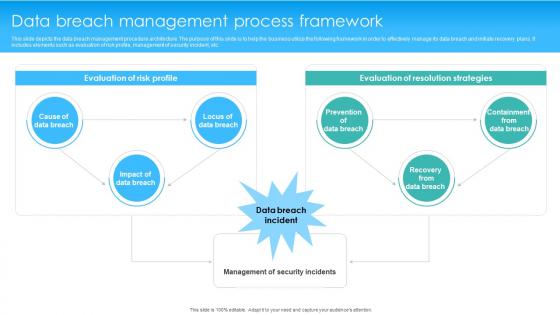 Data Breach Management Process Framework
Data Breach Management Process FrameworkThis slide depicts the data breach management procedure architecture. The purpose of this slide is to help the business utilize the following framework in order to effectively manage its data breach and initiate recovery plans. It includes elements such as evaluation of risk profile, management of security incident, etc. Introducing our Data Breach Management Process Framework set of slides. The topics discussed in these slides are Data Breach Management, Evaluation Of Risk Profile, Evaluation Of Resolution Strategies. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
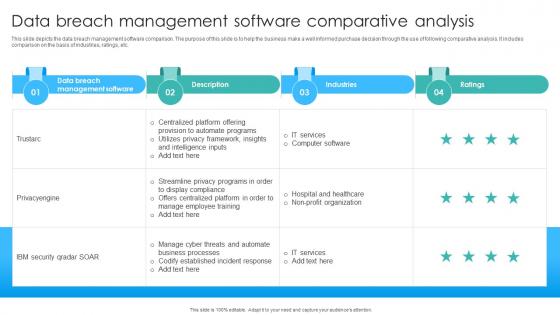 Data Breach Management Software Comparative Analysis
Data Breach Management Software Comparative AnalysisThis slide depicts the data breach management software comparison. The purpose of this slide is to help the business make a well informed purchase decision through the use of following comparative analysis. It includes comparison on the basis of industries, ratings, etc. Presenting our well structured Data Breach Management Software Comparative Analysis. The topics discussed in this slide are Hospital And Healthcare, Non Profit Organization, Utilizes Privacy Framework. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
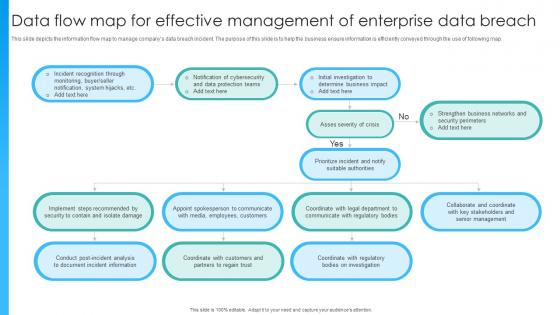 Data Flow Map For Effective Management Of Enterprise Data Breach
Data Flow Map For Effective Management Of Enterprise Data BreachThis slide depicts the information flow map to manage companys data breach incident. The purpose of this slide is to help the business ensure information is efficiently conveyed through the use of following map. Presenting our set of slides with Data Flow Map For Effective Management Of Enterprise Data Breach. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Determine Business Impact, Notification Of Cybersecurity, Incident Recognition Through.
-
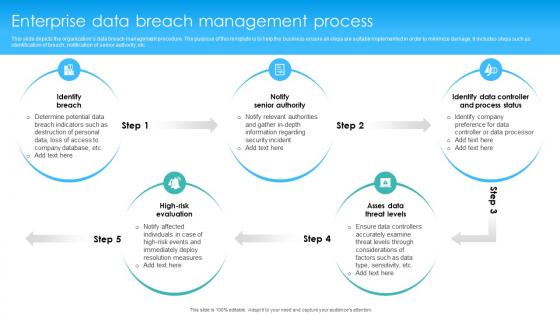 Enterprise Data Breach Management Process
Enterprise Data Breach Management ProcessThis slide depicts the organizations data breach management procedure. The purpose of this template is to help the business ensure all steps are suitably implemented in order to minimize damage. It includes steps such as identification of breach, notification of senior authority, etc. Introducing our premium set of slides with Enterprise Data Breach Management Process. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Notify Relevant Authorities, Identify Company Preference, Determine Potential Data Breach. So download instantly and tailor it with your information.
-
 Icon For Data Breach Identification And Management
Icon For Data Breach Identification And ManagementPresenting our set of slides with Icon For Data Breach Identification And Management. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon, Data Breach, Identification And Management.
-
 Icon For Effective Data Breach Management
Icon For Effective Data Breach ManagementIntroducing our premium set of slides with Icon For Effective Data Breach Management. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon For Effective, Data Breach, Management. So download instantly and tailor it with your information.
-
 Key Statistics Related To Ineffective Data Breach Management
Key Statistics Related To Ineffective Data Breach ManagementThis slide depicts the key statistics associated with ineffective data breach management. The purpose of this slide is to help the business ensure it implements suitable practices in order to improve its data protection and security. Presenting our set of slides with Key Statistics Related To Ineffective Data Breach Management. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Company Networks And Data, Data Security Breach Occur, Data Breach And Cyberattacks.
-
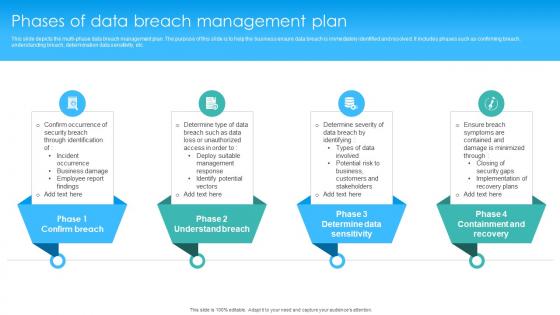 Phases Of Data Breach Management Plan
Phases Of Data Breach Management PlanThis slide depicts the multi phase data breach management plan. The purpose of this slide is to help the business ensure data breach is immediately identified and resolved. It includes phases such as confirming breach, understanding breach, determination data sensitivity, etc. Introducing our premium set of slides with Phases Of Data Breach Management Plan. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Determine Severity Of Data, Deploy Suitable Management, Identify Potential Vectors . So download instantly and tailor it with your information.
-
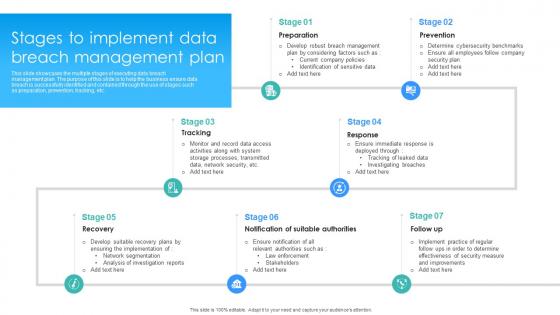 Stages To Implement Data Breach Management Plan
Stages To Implement Data Breach Management PlanThis slide showcases the multiple stages of executing data breach management plan. The purpose of this slide is to help the business ensure data breach is successfully identified and contained through the use of stages such as preparation, prevention, tracking, etc. Presenting our set of slides with Stages To Implement Data Breach Management Plan. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Determine Cybersecurity Benchmarks, Develop Suitable Recovery Plans, Monitor And Record Data.
-
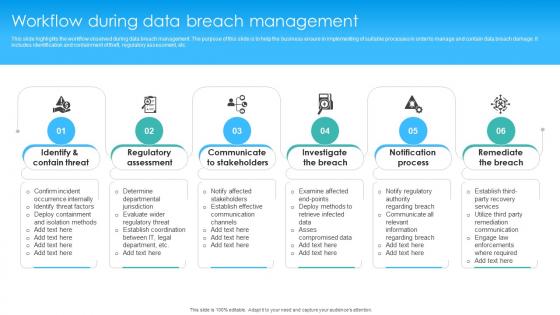 Workflow During Data Breach Management
Workflow During Data Breach ManagementThis slide highlights the workflow observed during data breach management. The purpose of this slide is to help the business ensure in implementing of suitable processes in order to manage and contain data breach damage. It includes identification and containment of theft, regulatory assessment, etc. Introducing our premium set of slides with Workflow During Data Breach Management. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Communicate To Stakeholders, Regulatory Assessment, Investigate The Breach. So download instantly and tailor it with your information.
-
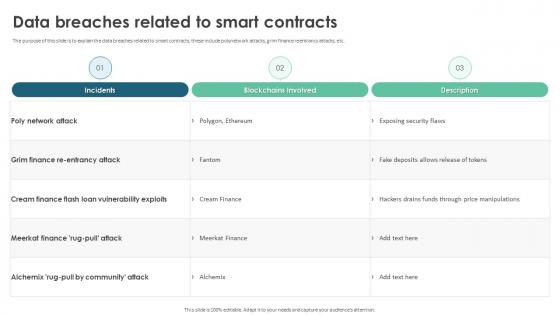 Data Breaches Related To Smart Contracts Ppt Styles Graphics Example
Data Breaches Related To Smart Contracts Ppt Styles Graphics ExampleThe purpose of this slide is to explain the data breaches related to smart contracts these include polynetwork attacks, grim finance reentrancy attacks, etc. Deliver an outstanding presentation on the topic using this Data Breaches Related To Smart Contracts Ppt Styles Graphics Example. Dispense information and present a thorough explanation of Poly Network Attack, Grim Finance Re Entrancy Attack, Cream Finance Flash Loan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Contingency Risk Icon For Data Breaches
Contingency Risk Icon For Data BreachesIntroducing our Contingency Risk Icon For Data Breaches set of slides. The topics discussed in these slides are Contingency Risk Icon For Data Breaches. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Privacy Project For Data Breach And Incident Response
Privacy Project For Data Breach And Incident ResponseThe purpose of this slide is to highlight how privacy project for data breach and incident response strengthens cybersecurity by proactively addressing, swiftly detecting, and effectively responding to potential data breaches and incidents. Introducing our Privacy Project For Data Breach And Incident Response set of slides. The topics discussed in these slides are Date Of Discovery, Response Actions, Impact Assessment, Quantified Data. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Digital Forensic Tools For Data Breach Incident Investigation
Digital Forensic Tools For Data Breach Incident InvestigationThis slide represents various tools that assist IT companies in conducting digital forensics to analyze and investigate data breach incidents effectively. It includes various tools such as Cellebrite, magnet axiom, and velociraptor. Present the topic in a bit more detail with this Digital Forensic Tools For Data Breach Incident Investigation. Use it as a tool for discussion and navigation on Magnet Axiom, Velociraptor, Cellebrite. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
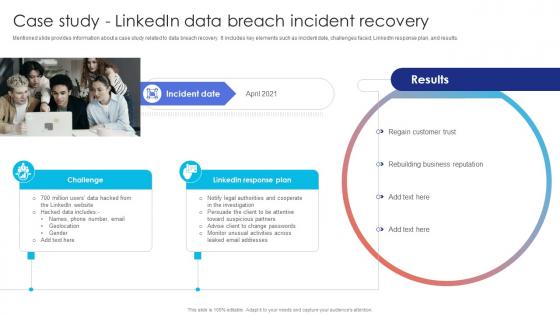 Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security Threat
Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about a case study related to data breach recovery. It includes key elements such as incident date, challenges faced, LinkedIn response plan, and results. Deliver an outstanding presentation on the topic using this Case Study Data Breach Incident Recovery Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Regain Customer Trust, Rebuilding Business Reputation, Linkedin Response using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
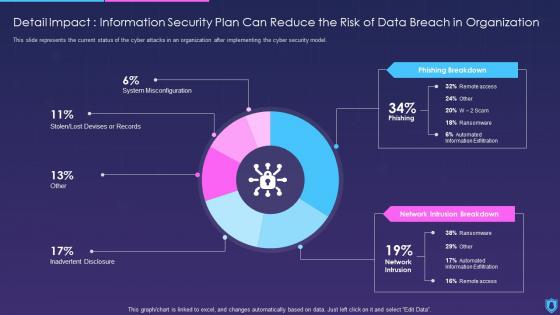 Information Security Detail Impact Information Security Can Reduce Risk Data Breach Organization
Information Security Detail Impact Information Security Can Reduce Risk Data Breach OrganizationThis slide represents the current status of the cyber attacks in an organization after implementing the cyber security model. Deliver an outstanding presentation on the topic using this Information Security Detail Impact Information Security Can Reduce Risk Data Breach Organization. Dispense information and present a thorough explanation of Organization, Information, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
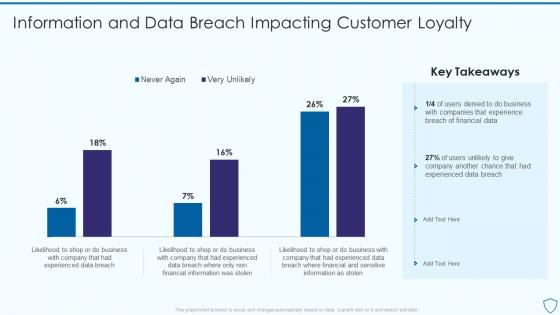 Risk Assessment And Management Plan For Information Security Information And Data Breach Impacting
Risk Assessment And Management Plan For Information Security Information And Data Breach ImpactingDeliver an outstanding presentation on the topic using this Risk Assessment And Management Plan For Information Security Information And Data Breach Impacting. Dispense information and present a thorough explanation of Information, Business, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
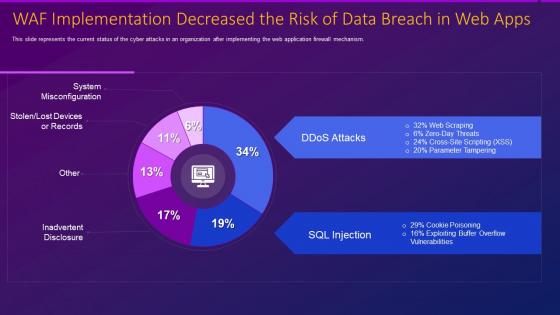 Web application firewall waf it implementation decreased risk data breach in web apps
Web application firewall waf it implementation decreased risk data breach in web appsThis slide represents the current status of the cyber attacks in an organization after implementing the web application firewall mechanism. Deliver an outstanding presentation on the topic using this Web Application Firewall Waf It Implementation Decreased Risk Data Breach In Web Apps. Dispense information and present a thorough explanation of Implementation, Misconfiguration, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
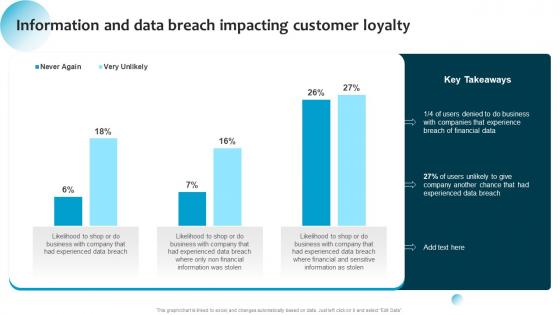 Information System Security And Risk Administration Information And Data Breach Impacting Customer Loyalty
Information System Security And Risk Administration Information And Data Breach Impacting Customer LoyaltyDeliver an outstanding presentation on the topic using this Information System Security And Risk Administration Information And Data Breach Impacting Customer Loyalty. Dispense information and present a thorough explanation of Business, Financial Data, Data Breach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity Risk Analysis And Management Plan Information And Data Breach Impacting
Cybersecurity Risk Analysis And Management Plan Information And Data Breach ImpactingPresent the topic in a bit more detail with this Cybersecurity Risk Analysis And Management Plan Information And Data Breach Impacting. Use it as a tool for discussion and navigation on Information, Customer Loyalty, Financial Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
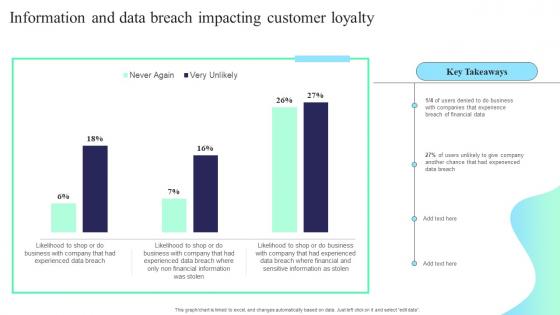 Information And Data Breach Impacting Customer Loyalty Formulating Cybersecurity Plan
Information And Data Breach Impacting Customer Loyalty Formulating Cybersecurity PlanPresent the topic in a bit more detail with this Information And Data Breach Impacting Customer Loyalty Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Information, Data Breach Impacting, Customer Loyalty. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
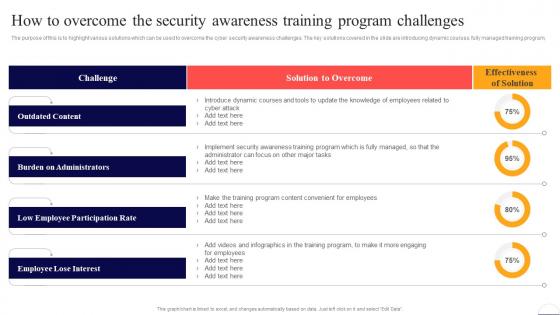 How To Overcome The Security Awareness Training Program Preventing Data Breaches Through Cyber Security
How To Overcome The Security Awareness Training Program Preventing Data Breaches Through Cyber SecurityThe purpose of this is to highlight various solutions which can be used to overcome the cyber security awareness challenges. The key solutions covered in the slide are introducing dynamic courses, fully managed training program. Deliver an outstanding presentation on the topic using this How To Overcome The Security Awareness Training Program Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Outdated Content, Burden On Administrators, Low Employee Participation Rate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
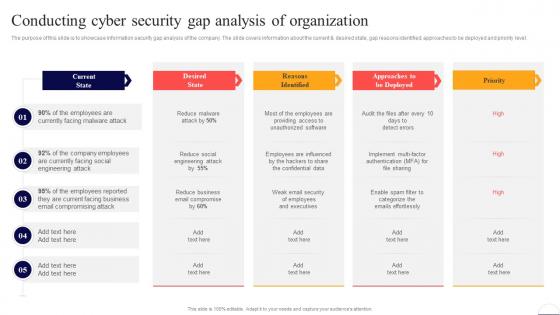 Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security
Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase information security gap analysis of the company. The slide covers information about the current and desired state, gap reasons identified, approaches to be deployed and priority level. Deliver an outstanding presentation on the topic using this Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Current State, Email, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
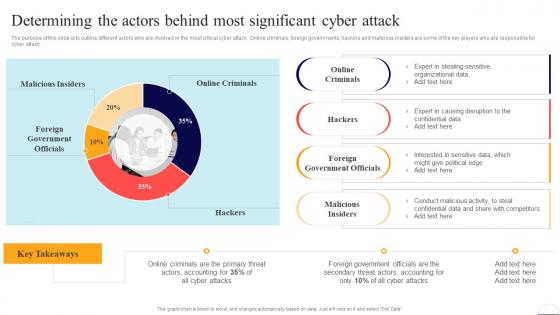 Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber Security
Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Present the topic in a bit more detail with this Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Online Criminals, Foreign Government Officials, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
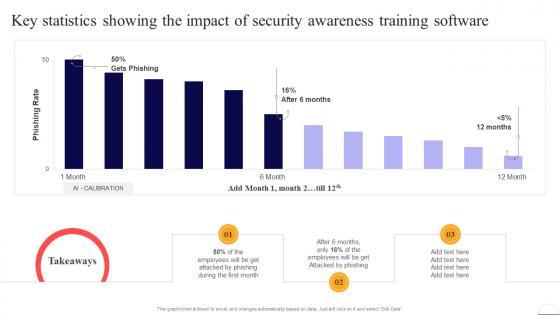 Key Statistics Showing The Impact Of Security Awarenesspreventing Data Breaches Through Cyber Security
Key Statistics Showing The Impact Of Security Awarenesspreventing Data Breaches Through Cyber SecurityPresent the topic in a bit more detail with this Key Statistics Showing The Impact Of Security Awarenesspreventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Employees, Security, Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
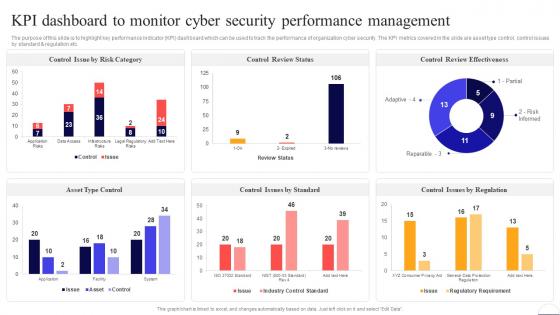 Kpi Dashboard To Monitor Cyber Security Performance Preventing Data Breaches Through Cyber Security
Kpi Dashboard To Monitor Cyber Security Performance Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Deliver an outstanding presentation on the topic using this Kpi Dashboard To Monitor Cyber Security Performance Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Control Review Status, Management, Cyber Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security
Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this Kpi Metrics Dashboard To Effectively Track Cyber Threat Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Risk By Threats, Threat Report, Current Risk Status. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
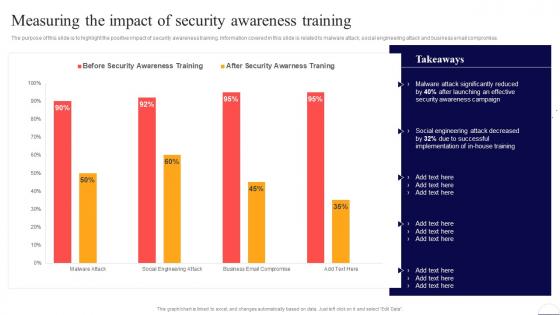 Measuring The Impact Of Security Awareness Training Preventing Data Breaches Through Cyber Security
Measuring The Impact Of Security Awareness Training Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight the positive impact of security awareness training. Information covered in this slide is related to malware attack, social engineering attack and business email compromise. Present the topic in a bit more detail with this Measuring The Impact Of Security Awareness Training Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Security Awareness, Social Engineering. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
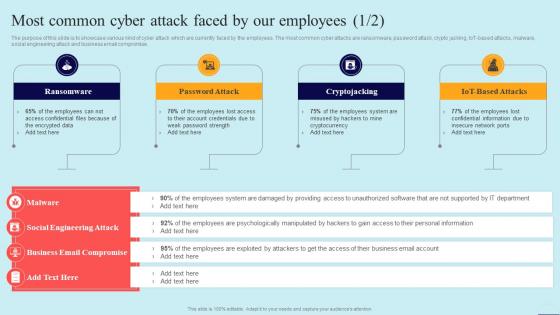 Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security
Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT-based attacks, malware, social engineering attack and business email compromise. Introducing Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Password Attack, Cryptojacking, using this template. Grab it now to reap its full benefits.
-
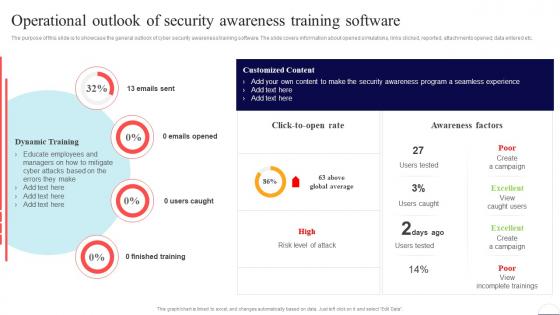 Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber Security
Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Present the topic in a bit more detail with this Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Finished Training, Awareness Factors, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Practices To Improve Security Awareness Level Amongst The Preventing Data Breaches Through Cyber Security
Practices To Improve Security Awareness Level Amongst The Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline multiple ways which can be used by the organization to improve the cyber security awareness level of employees. The key practices mentioned in the slide are involving top level management, developing robust policies, and setting guidelines. Increase audience engagement and knowledge by dispensing information using Practices To Improve Security Awareness Level Amongst The Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Get Management Involved, Develop Robust Policies, Set Guidelines using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
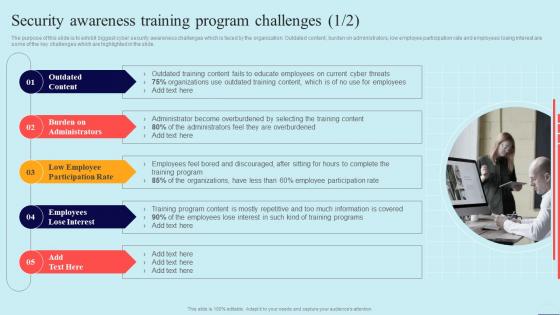 Security Awareness Training Program Challenges Preventing Data Breaches Through Cyber Security
Security Awareness Training Program Challenges Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to exhibit biggest cyber security awareness challenges which is faced by the organization. Outdated content, burden on administrators, low employee participation rate and employees losing interest are some of the key challenges which are highlighted in the slide. Increase audience engagement and knowledge by dispensing information using Security Awareness Training Program Challenges Preventing Data Breaches Through Cyber Security. This template helps you present information on five stages. You can also present information on Outdated Content, Employees Lose Interest, Burden On Administrators using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
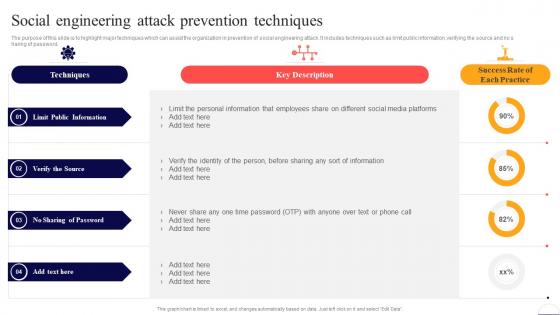 Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber Security
Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no sharing of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Limit Public Information, Verify The Source, No Sharing Of Password. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
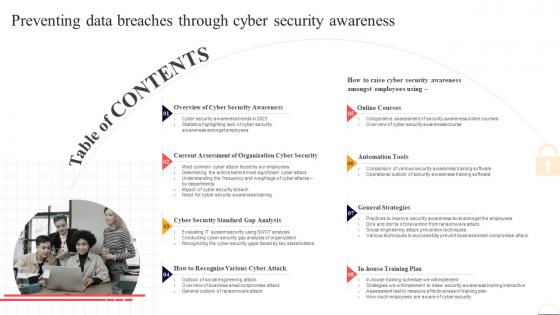 Table Of Contents For Preventing Data Breaches Through Cyber Security Awareness
Table Of Contents For Preventing Data Breaches Through Cyber Security AwarenessDeliver an outstanding presentation on the topic using this Table Of Contents For Preventing Data Breaches Through Cyber Security Awareness. Dispense information and present a thorough explanation of Cyber Security Awareness, Online Courses, Automation Tools using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
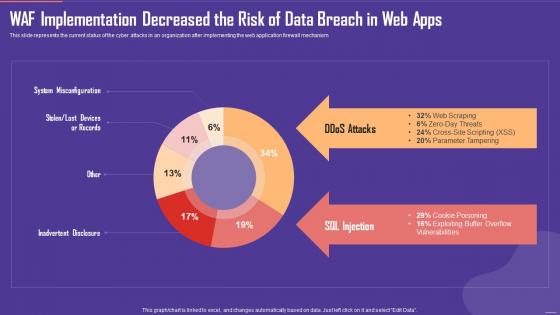 Application Firewall WAF Implementation Decreased the Risk of Data Breach in Web Apps
Application Firewall WAF Implementation Decreased the Risk of Data Breach in Web AppsThis slide represents the current status of the cyber attacks in an organization after implementing the web application firewall mechanism. Present the topic in a bit more detail with this Application Firewall WAF Implementation Decreased the Risk of Data Breach in Web Apps. Use it as a tool for discussion and navigation on SQL Injection, Ddos Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
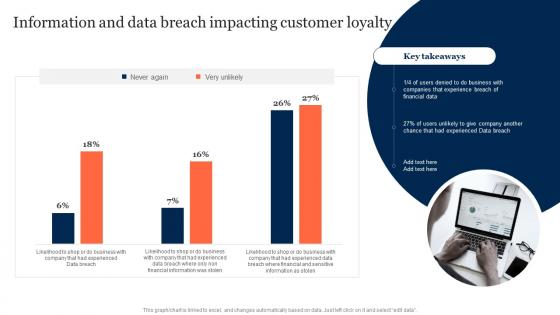 Information And Data Breach Impacting Customer Loyalty Information Security Risk Management
Information And Data Breach Impacting Customer Loyalty Information Security Risk ManagementDeliver an outstanding presentation on the topic using this Information And Data Breach Impacting Customer Loyalty Information Security Risk Management. Dispense information and present a thorough explanation of Information, Data Breach Impacting, Customer Loyalty using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Average Costing On Risk Management For Data Breach Incident
Average Costing On Risk Management For Data Breach IncidentThis slide covers total cost incurred on response of data breach incident. It includes four categories such as incident detection and escalation, notifications, post breach response, lost business cost ,etc. Presenting our well structured Average Costing On Risk Management For Data Breach Incident. The topics discussed in this slide are Average Costing On Risk, Management, Data Breach Incident. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
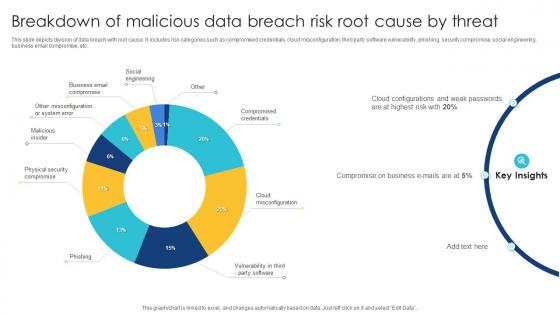 Breakdown Of Malicious Data Breach Risk Root Cause By Threat
Breakdown Of Malicious Data Breach Risk Root Cause By ThreatThis slide depicts division of data breach with root cause. It includes risk categories such as compromised credentials, cloud misconfiguration, third party software vulnerability, phishing, security compromise, social engineering, business email compromise, etc. Introducing our Breakdown Of Malicious Data Breach Risk Root Cause By Threat set of slides. The topics discussed in these slides are Social Engineering, Business Email Compromise, Malicious Insider. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
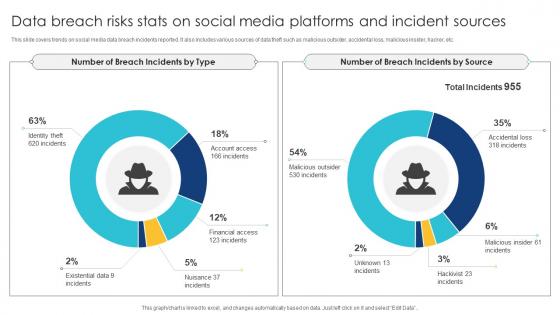 Data Breach Risks Stats On Social Media Platforms And Incident Sources
Data Breach Risks Stats On Social Media Platforms And Incident SourcesThis slide covers trends on social media data breach incidents reported. It also includes various sources of data theft such as malicious outsider, accidental loss, malicious insider, hacker, etc. Introducing our Data Breach Risks Stats On Social Media Platforms And Incident Sources set of slides. The topics discussed in these slides are Data Breach Risks, Stats On Social Media, Platforms And Incident Sources. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
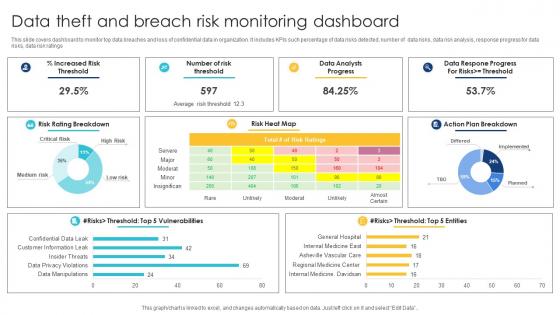 Data Theft And Breach Risk Monitoring Dashboard
Data Theft And Breach Risk Monitoring DashboardThis slide covers dashboard to monitor top data breaches and loss of confidential data in organization. It includes KPIs such percentage of data risks detected, number of data risks, data risk analysis, response progress for data risks, data risk ratings. Presenting our well structured Data Theft And Breach Risk Monitoring Dashboard. The topics discussed in this slide are Data Theft And Breach, Risk Monitoring, Dashboard. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
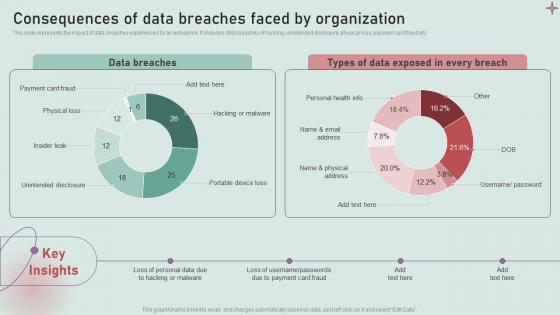
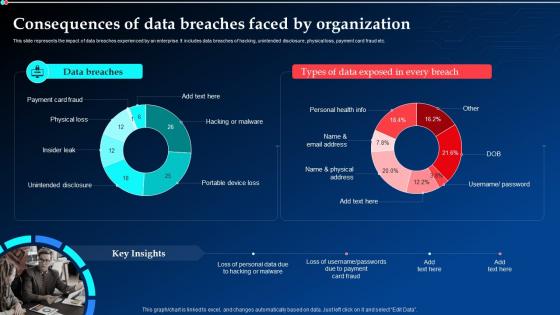 Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt Diagrams
Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt DiagramsThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Deliver an outstanding presentation on the topic using this Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt Diagrams. Dispense information and present a thorough explanation of Data Breaches, Consequences, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Consequences Of Data Breaches Faced By Organization Deploying Computer Security Incident Management
Consequences Of Data Breaches Faced By Organization Deploying Computer Security Incident ManagementThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc.Present the topic in a bit more detail with this Consequences Of Data Breaches Faced By Organization Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Unintended Disclosure, Portable Device, Hacking Malware. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
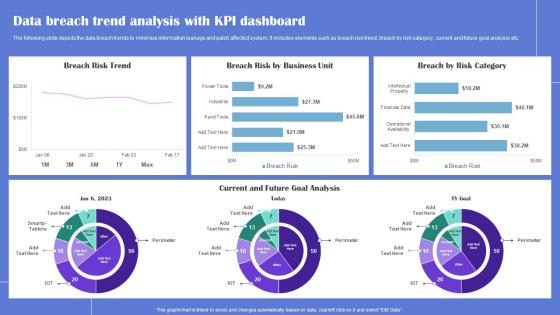 Data Breach Trend Generating Security Awareness Among Employees To Reduce
Data Breach Trend Generating Security Awareness Among Employees To ReduceThe following slide depicts the data breach trends to minimize information leakage and patch affected system. It includes elements such as breach risk trend, breach by risk category, current and future goal analysis etc. Deliver an outstanding presentation on the topic using this Data Breach Trend Generating Security Awareness Among Employees To Reduce Dispense information and present a thorough explanation of Data Breach Trend, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
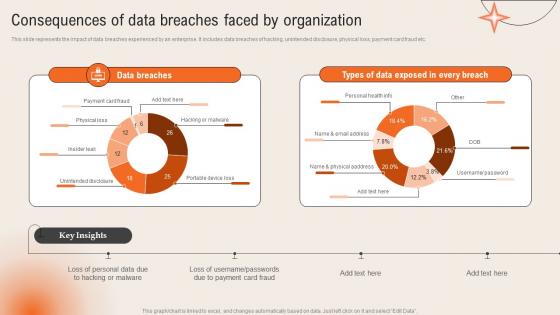
 Consequences Of Data Breaches Faced By Organization Development And Implementation Of Security
Consequences Of Data Breaches Faced By Organization Development And Implementation Of SecurityThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Deliver an outstanding presentation on the topic using this Consequences Of Data Breaches Faced By Organization Development And Implementation Of Security. Dispense information and present a thorough explanation of Payment Card Fraud, Physical Loss, Insider Leak using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
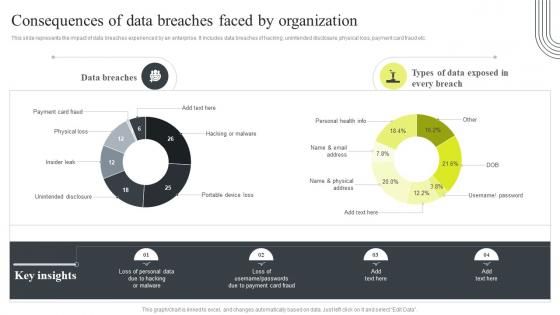 Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization
Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By OrganizationThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization. Use it as a tool for discussion and navigation on Consequences, Data Breaches, Unintended Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
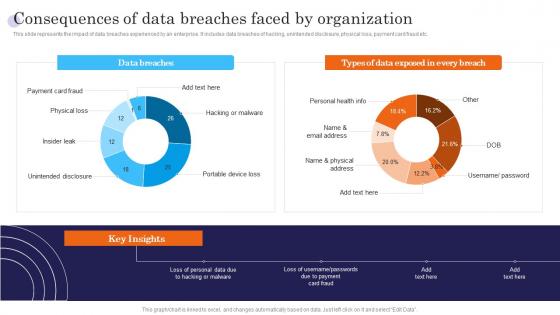 Consequences Of Data Breaches Faced By Organization Incident Response Strategies Deployment
Consequences Of Data Breaches Faced By Organization Incident Response Strategies DeploymentThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Consequences Of Data Breaches Faced By Organization Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Data, Consequences, Portable. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
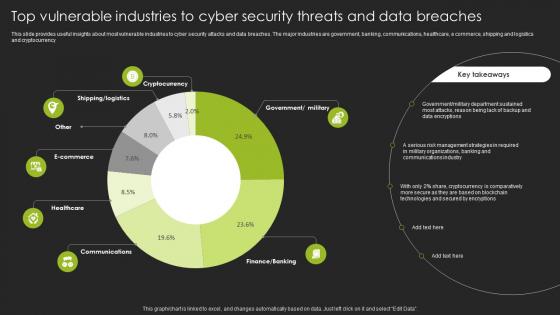 Top Vulnerable Industries To Cyber Security Threats And Data Breaches
Top Vulnerable Industries To Cyber Security Threats And Data BreachesThis slide provides useful insights about most vulnerable industries to cyber security attacks and data breaches. The major industries are government, banking, communications, healthcare, e commerce, shipping and logistics and cryptocurrency Introducing our Top Vulnerable Industries To Cyber Security Threats And Data Breaches set of slides. The topics discussed in these slides are Government, Department. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cloud Security Threats Contract Breaches With Clients Cloud Data Protection
Cloud Security Threats Contract Breaches With Clients Cloud Data ProtectionThis slide defines the contract breaches with clients and customers that could be the biggest threat to the organizational data. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Contract Breaches With Clients Cloud Data Protection. This template helps you present information on four stages. You can also present information on Business Partners, Organization, Cloud using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Data Breach Vulnerabilities In Powerpoint And Google Slides Cpb
Data Breach Vulnerabilities In Powerpoint And Google Slides CpbPresenting Data Breach Vulnerabilities In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Data Breach Vulnerabilities. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.



