Powerpoint Templates and Google slides for Five Secured Unsecured
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
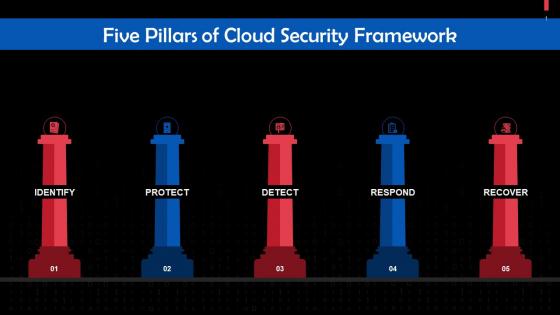 Five Pillars Of Cloud Security Framework Training Ppt
Five Pillars Of Cloud Security Framework Training PptPresenting Five Pillars of Cloud Security Framework. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Five Steps To Create An Operational Security Plan Training Ppt
Five Steps To Create An Operational Security Plan Training PptPresenting Five Steps to Create an Operational Security Plan. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Five Secured Unsecured In Powerpoint And Google Slides Cpb
Five Secured Unsecured In Powerpoint And Google Slides CpbPresenting our Five Secured Unsecured In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Five Secured Unsecured This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Comprehensive Guide To Understand Five Best Practices To Secure Bitcoin Fin SS
Comprehensive Guide To Understand Five Best Practices To Secure Bitcoin Fin SSThis slide shows details about best practices which can be adopted by Bitcoin holders to secure accounts against frauds. These tips includes hardware wallets, two factor authentication, strong passwords, etc. Introducing Comprehensive Guide To Understand Five Best Practices To Secure Bitcoin Fin SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Hardware Wallet, Two Factor Authentication, Strong Passwords, Update Software, using this template. Grab it now to reap its full benefits.
-
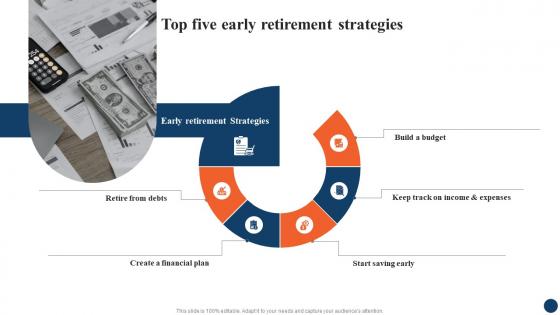 Top Five Early Retirement Strategic Retirement Planning To Build Secure Future Fin SS
Top Five Early Retirement Strategic Retirement Planning To Build Secure Future Fin SSIntroducing Top Five Early Retirement Strategic Retirement Planning To Build Secure Future Fin SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Retirement Strategies, Financial Plan, Budget, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Devsecops Transformation Phase Five Execute On Devsecops
Devsecops Best Practices For Secure Devsecops Transformation Phase Five Execute On DevsecopsThis slide discusses the fifth phase of DevSecOps transformation. The purpose of this slide is to explain the phase executed on DevSecOps, including phased execution in DevSecOps transformation and the advantages of starting with the new project. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Devsecops Transformation Phase Five Execute On Devsecops. Dispense information and present a thorough explanation of Phased Execution In Devsecops Transformation, Advantages Of Starting With New Projects, Facilitates Alignment Of Expectations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ethical Hacking And Network Security Five Phases Of Ethical Hacking
Ethical Hacking And Network Security Five Phases Of Ethical HackingThis slide represents the five phases of ethical hacking such as reconnaissance, scanning, gaining access, maintaining access, and clearing the track of system hacking. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Five Phases Of Ethical Hacking. This template helps you present information on five stages. You can also present information on Reconnaissance, Scanning, Maintaining Access, Clearing Track using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
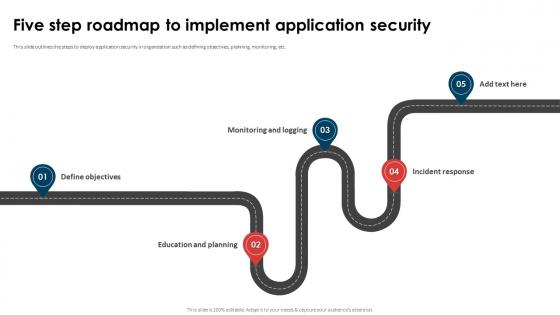 Application Security Implementation Plan Five Step Roadmap To Implement Application Security
Application Security Implementation Plan Five Step Roadmap To Implement Application SecurityThis slide outlines the steps to deploy application security in organization such as defining objectives, planning, monitoring, etc. Introducing Application Security Implementation Plan Five Step Roadmap To Implement Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Monitoring And Logging, Incident Response, Education And Planning, Application Security, using this template. Grab it now to reap its full benefits.
-
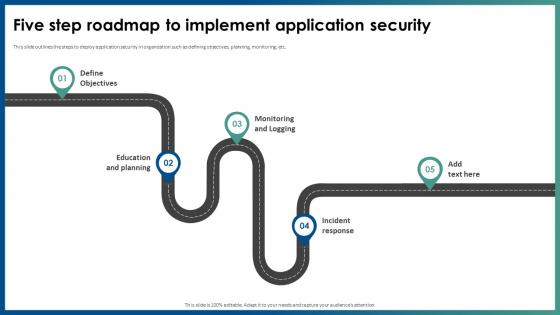 Five Step Roadmap To Implement Application Security
Five Step Roadmap To Implement Application SecurityThis slide outlines the steps to deploy application security in organization such as defining objectives, planning, monitoring, etc. Introducing Five Step Roadmap To Implement Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Monitoring And Logging, Education And Planning, Five Step Roadmap, Application Security, using this template. Grab it now to reap its full benefits.
-
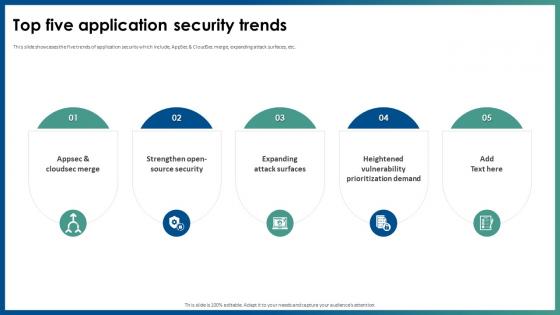 Top Five Application Security Trends Ppt File Example Introduction
Top Five Application Security Trends Ppt File Example IntroductionThis slide showcases the five trends of application security which include, AppSec and CloudSec merge, expanding attack surfaces, etc. Increase audience engagement and knowledge by dispensing information using Top Five Application Security Trends Ppt File Example Introduction. This template helps you present information on five stages. You can also present information on Heightened Vulnerability, Prioritization Demand, Expanding Attack Surfaces, Appsec And Cloudsec Merge using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
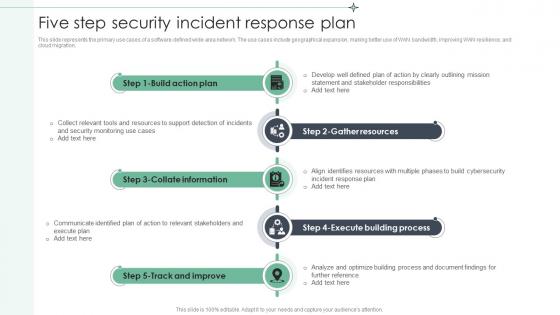 Five Step Security Incident Response Plan
Five Step Security Incident Response PlanThis slide represents the primary use cases of a software defined wide area network. The use cases include geographical expansion, making better use of WAN bandwidth, improving WAN resilience, and cloud migration. Introducing our premium set of slides with Five Step Security Incident Response Plan. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Build Action Plan, Collate Information, Gather Resources. So download instantly and tailor it with your information.
-
 Five Key Consideration For Hotel Safety And Security
Five Key Consideration For Hotel Safety And SecurityThis slide highlights five strategies to ensure safety and security in hotels. It involves strategies such as installation of proper lighting, CCTV security cameras, fire alarms, emergency power and manual. Presenting our set of slides with name Five Key Consideration For Hotel Safety And Security. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Cameras, Emergency, Consideration.
-
 Ai Transformation Playbook Stage Five Security Breach Readiness Checklist
Ai Transformation Playbook Stage Five Security Breach Readiness ChecklistPurpose of this slide is to illustrate readiness checklist that will assist businesses in countering any security breach in advance. Readiness level will be evaluated based on different questions.Present the topic in a bit more detail with this Ai Transformation Playbook Stage Five Security Breach Readiness Checklist Use it as a tool for discussion and navigation on Proper Risk Management, Each Organizational, Governance Procedures This template is free to edit as deemed fit for your organization. Therefore download it now.
-
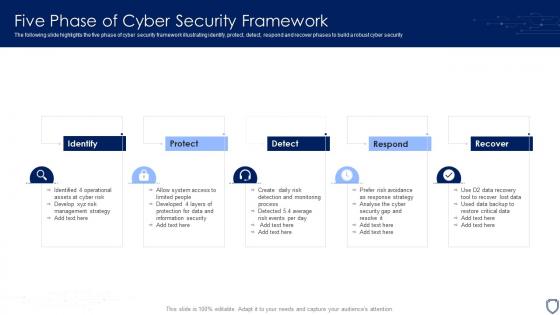 Five Phase Of Cyber Security Framework
Five Phase Of Cyber Security FrameworkThe following slide highlights the five phase of cyber security framework illustrating identify, protect, detect, respond and recover phases to build a robust cyber security. Introducing our premium set of slides with name Five Phase Of Cyber Security Framework. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify, Protect, Detect, Respond, Recover. So download instantly and tailor it with your information.
-
 Five Phase Of Risk Based Cyber Security
Five Phase Of Risk Based Cyber SecurityThe following slide highlights the five phase of risk based cyber security which includes business impact analysis, risk assessment, controls, report and monitor, it provides activity, value and outcome for each phase which helps company to develop a consistent incident response process. Presenting our set of slides with name Five Phase Of Risk Based Cyber Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Business Impact Analysis, Risk Assessment, Monitor.
-
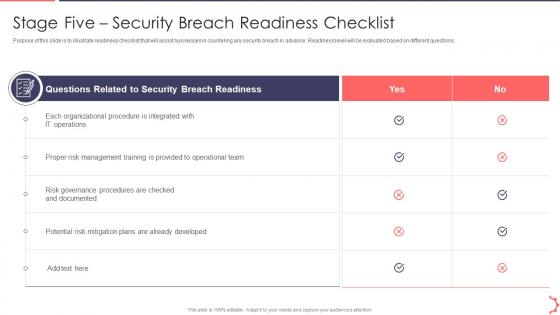 Stage Five Security Breach Readiness AI Playbook Accelerate Digital Transformation
Stage Five Security Breach Readiness AI Playbook Accelerate Digital TransformationPurpose of this slide is to illustrate readiness checklist that will assist businesses in countering any security breach in advance. Readiness level will be evaluated based on different questions.Present the topic in a bit more detail with this Stage Five Security Breach Readiness AI Playbook Accelerate Digital Transformation . Use it as a tool for discussion and navigation on Stage Five Security Breach Readiness Checklist . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
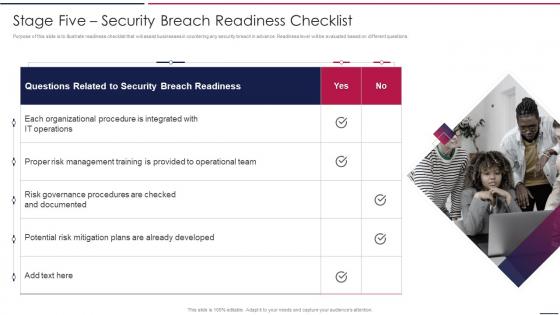 AIOps Playbook Stage Five Security Breach Readiness Checklist Ppt Topics
AIOps Playbook Stage Five Security Breach Readiness Checklist Ppt TopicsPurpose of this slide is to illustrate readiness checklist that will assist businesses in countering any security breach in advance. Readiness level will be evaluated based on different questions. Introducing AIOps Playbook Stage Five Security Breach Readiness Checklist Ppt Topics to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Stage Five Security Breach Readiness Checklist, using this template. Grab it now to reap its full benefits.
-
 Five Levels Cloud Security Maturity Model
Five Levels Cloud Security Maturity ModelThis slide shows maturity model which can be used by IT managers in cloud security. These five levels are no automation, simple automation, manually executed scripts, guardrails and automation everywhere. Presenting our set of slides with Five Levels Cloud Security Maturity Model. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on No Automation, Simple Automation, Manually Executed Scripts.
-
 Five Step Process Of Safety And Security
Five Step Process Of Safety And SecurityThis slide shows the five stages process of safety and security. These stages are audit, plan, execute, monitor and repeat. Introducing our premium set of slides with Five Step Process Of Safety And Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Audit, Cyber Security Training, Quarterly Plan Review. So download instantly and tailor it with your information.
-
 Five Elements Of Cloud Computing Security
Five Elements Of Cloud Computing SecurityThis slide includes elements of cloud computing security to assure network protection and efficient management. It contains five elements architecture, security, due diligence, authentication, monitor and visibility.Presenting our set of slides with Five Elements Of Cloud Computing Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Compliance, Monitor Visibility, Authentication.
-
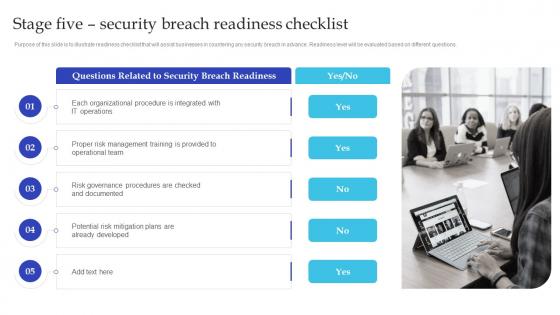 Stage Five Security Breach Readiness Checklist Artificial Intelligence Playbook For Business
Stage Five Security Breach Readiness Checklist Artificial Intelligence Playbook For BusinessPurpose of this slide is to illustrate readiness checklist that will assist businesses in countering any security breach in advance. Readiness level will be evaluated based on different questions. Introducing Stage Five Security Breach Readiness Checklist Artificial Intelligence Playbook For Business to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Organizational Procedure, IT Operations, Operational Team, using this template. Grab it now to reap its full benefits.
-
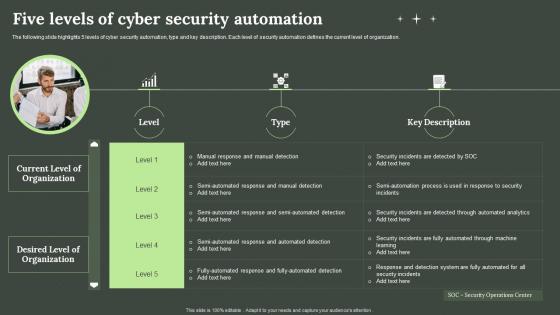 Five Levels Of Cyber Security Automation
Five Levels Of Cyber Security AutomationThe following slide highlights 5 levels of cyber security automation, type and key description. Each level of security automation defines the current level of organization. Presenting our well-structured Five Levels Of Cyber Security Automation. The topics discussed in this slide are Five Levels, Cyber Security Automation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Five Steps For Cyber Security Risk Analysis
Five Steps For Cyber Security Risk AnalysisThis slide covers the steps for analysis of risk occurring in cyber security to reduce errors and system hacks so that the information of clients remain safe. It includes finding assets, identifying consequences, threats and assessing risk. Presenting our set of slides with Five Steps For Cyber Security Risk Analysis. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Find Valuable Assets, Assess Risk, Identify Potential Consequences.
-
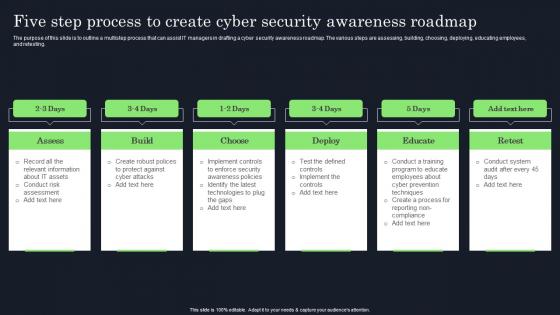 Five Step Process To Create Cyber Security Raising Cyber Security Awareness In Organizations
Five Step Process To Create Cyber Security Raising Cyber Security Awareness In OrganizationsThe purpose of this slide is to outline a multistep process that can assist IT managers in drafting a cyber security awareness roadmap. The various steps are assessing, building, choosing, deploying, educating employees and retesting. Increase audience engagement and knowledge by dispensing information using Five Step Process To Create Cyber Security Raising Cyber Security Awareness In Organizations. This template helps you present information on six stages. You can also present information on Assess, Build, Choose, Deploy, Educate, Retest using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
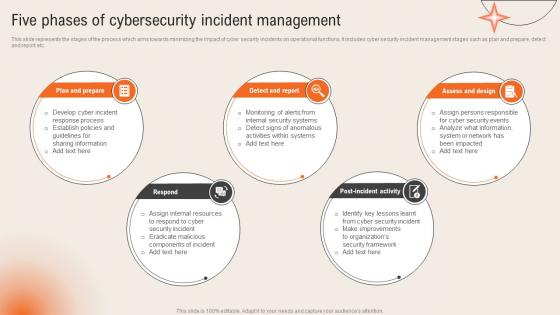 Five Phases Of Cybersecurity Incident Management Deploying Computer Security Incident Management
Five Phases Of Cybersecurity Incident Management Deploying Computer Security Incident ManagementThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc.Introducing Five Phases Of Cybersecurity Incident Management Deploying Computer Security Incident Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Sharing Information, Establish Policies, Response Process, using this template. Grab it now to reap its full benefits.
-
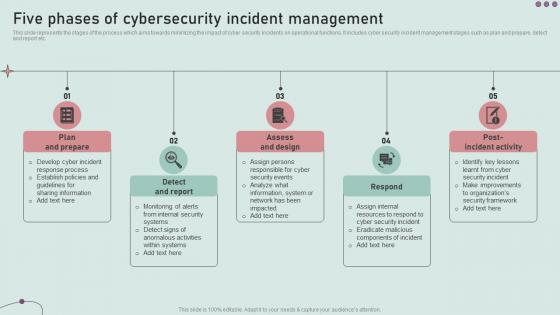 Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident
Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security IncidentThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Introducing Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assess And Design, Detect And Report, Plan And Prepare, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Attacks Response Plan Five Phases Of Cybersecurity Incident Management
Cyber Security Attacks Response Plan Five Phases Of Cybersecurity Incident ManagementThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Introducing Cyber Security Attacks Response Plan Five Phases Of Cybersecurity Incident Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Plan And Prepare, Post Incident Activity, Assess And Design, Incident Management, using this template. Grab it now to reap its full benefits.
-
 Five Important Supply Chain Security Concerns
Five Important Supply Chain Security ConcernsThe following slide highlights concerns associated with supply chain security to safeguard integrity of products and services being delivered. It includes concerns such as data protection, data locality, fraud prevention, third-party risks and data visibility and governance. Introducing our premium set of slides with Five Important Supply Chain Security Concerns Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Protection, Data Locality, Fraud Prevention. So download instantly and tailor it with your information.
-
 Five Stage Security Policy Management Lifecycle
Five Stage Security Policy Management LifecycleFollowing slide includes five stage process for security policy management which can be used by businesses to improve communication across departments. It includes stages such as discover and visualize, plan and assess, migrate and deploy, maintain, and decommission. Introducing our premium set of slides with Five Stage Security Policy Management Lifecycle. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Discover And Visualize, Plan And Access, Migrate And Deploy. So download instantly and tailor it with your information.
-
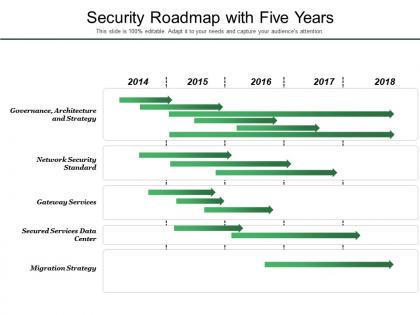 Security roadmap with five years
Security roadmap with five yearsPresenting this set of slides with name - Security Roadmap With Five Years. This is a five stage process. The stages in this process are Security Roadmap, Security Timeline, Safer Roadmap.
-
 Access rights key with five security access
Access rights key with five security accessPresenting this set of slides with name - Access Rights Key With Five Security Access. This is a one stage process. The stages in this process are Access Rights, Permission, Logins.
-
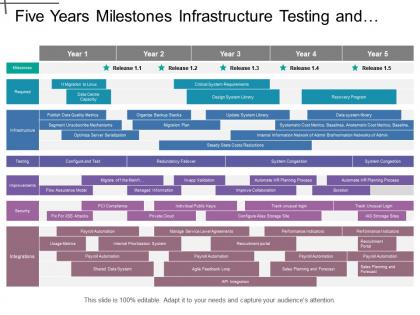 Five years milestones infrastructure testing and security it timeline
Five years milestones infrastructure testing and security it timelinePresenting this set of slides with name - Five Years Milestones Infrastructure Testing And Security It Timeline. This is a five stage process. The stages in this process are It Timeline, It Roadmap, Information Technology Timeline.
-
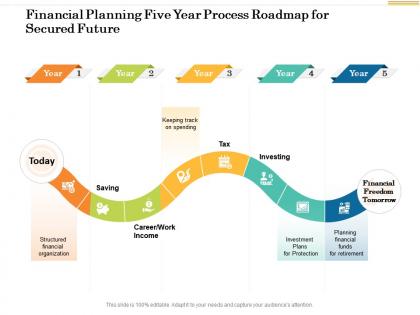 Financial planning five year process roadmap for secured future
Financial planning five year process roadmap for secured futurePresenting Financial Planning Five Year Process Roadmap For Secured Future PowerPoint Template. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements.
-
 Cyber security strategy process management five year roadmap
Cyber security strategy process management five year roadmapPresenting Cyber Security Strategy Process Management Five Year Roadmap PowerPoint Template. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements.
-
 It security five years strategy roadmap
It security five years strategy roadmapPresenting IT Security Five Years Strategy Roadmap PowerPoint slide. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
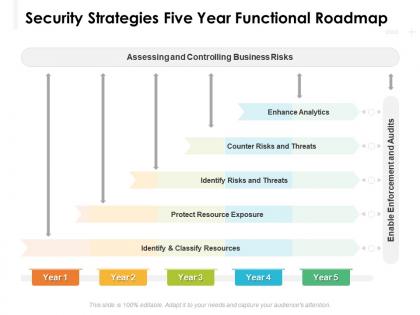 Security strategies five year functional roadmap
Security strategies five year functional roadmapPresenting Security Strategies Five Year Functional Roadmap PowerPoint slide. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
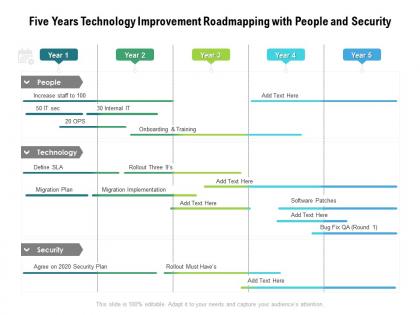 Five years technology improvement roadmapping with people and security
Five years technology improvement roadmapping with people and securityPresenting Five Years Technology Improvement Roadmapping With People And Security PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
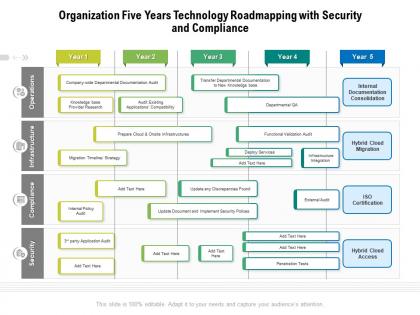 Organization five years technology roadmapping with security and compliance
Organization five years technology roadmapping with security and compliancePresenting Organization Five Years Technology Roadmapping With Security And Compliance PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Secured cryptocurrency transaction five year roadmap
Secured cryptocurrency transaction five year roadmapPresenting Secured Cryptocurrency Transaction Five Year Roadmap PowerPoint slide. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Five year company product development roadmap with advanced security
Five year company product development roadmap with advanced securityPresenting Five Year Company Product Development Roadmap With Advanced Security PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
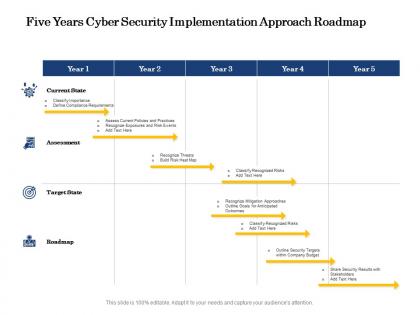 Five years cyber security implementation approach roadmap
Five years cyber security implementation approach roadmapPresenting Five Years Cyber Security Implementation Approach Roadmap PowerPoint slide. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
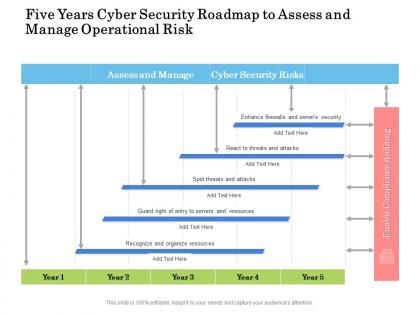 Five years cyber security roadmap to assess and manage operational risk
Five years cyber security roadmap to assess and manage operational riskPresenting Five Years Cyber Security Roadmap To Assess And Manage Operational Risk PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
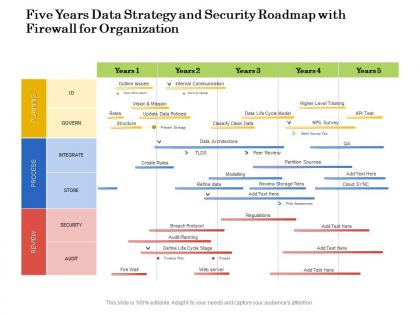 Five years data strategy and security roadmap with firewall for organization
Five years data strategy and security roadmap with firewall for organizationPresenting Five Years Data Strategy And Security Roadmap With Firewall For Organization PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
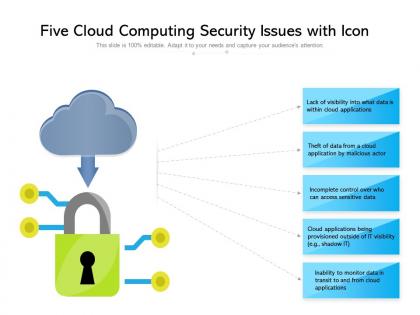 Five cloud computing security issues with icon
Five cloud computing security issues with iconPresenting this set of slides with name Five Cloud Computing Security Issues With Icon. This is a five stage process. The stages in this process are Five Cloud Computing Security Issues With Icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
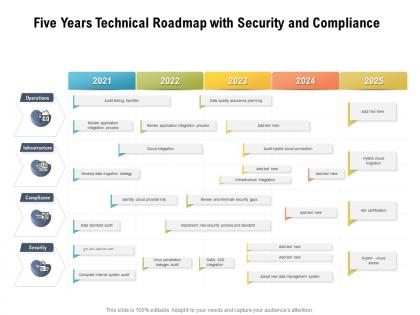 Five years technical roadmap with security and compliance
Five years technical roadmap with security and compliancePresenting Five Years Technical Roadmap With Security And Compliance PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Five yearly roadmap for securing business process management
Five yearly roadmap for securing business process managementPresenting our Five Yearly Roadmap For Securing Business Process Management PowerPoint Presentation Slide. This is a 100% editable and adaptable PPT slide. This layout allows you to modify the font, text, and image according to your unique requirements. The template can also be accessed with Google Slides. You can save it in different formats such as PDF or JPEG. High-quality graphics add to its benefits.
-
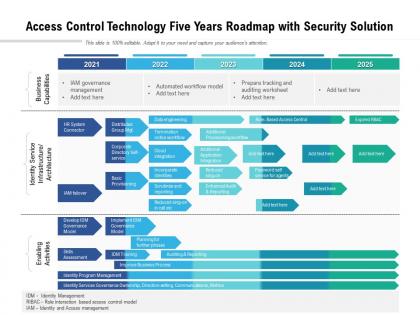 Access control technology five years roadmap with security solution
Access control technology five years roadmap with security solutionPresenting Access Control Technology Five Years Roadmap With Security Solution PowerPoint Template. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements.
-
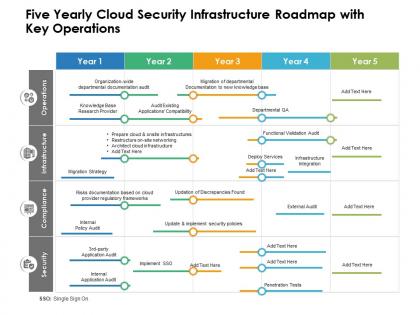 Five yearly cloud security infrastructure roadmap with key operations
Five yearly cloud security infrastructure roadmap with key operationsPresenting Five Yearly Cloud Security Infrastructure Roadmap With Key Operations PowerPoint slide. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
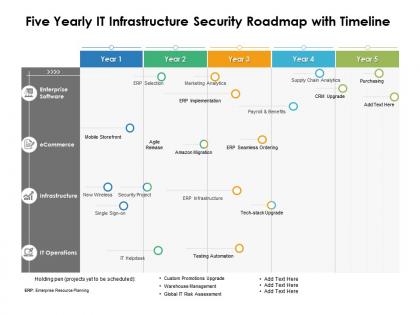 Five yearly it infrastructure security roadmap with timeline
Five yearly it infrastructure security roadmap with timelinePresenting Five Yearly IT Infrastructure Security Roadmap With Timeline PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
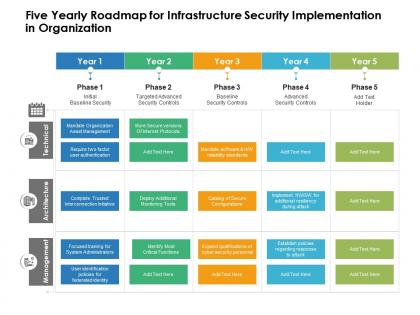 Five yearly roadmap for infrastructure security implementation in organization
Five yearly roadmap for infrastructure security implementation in organizationPresenting Five Yearly Roadmap For Infrastructure Security Implementation In Organization PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
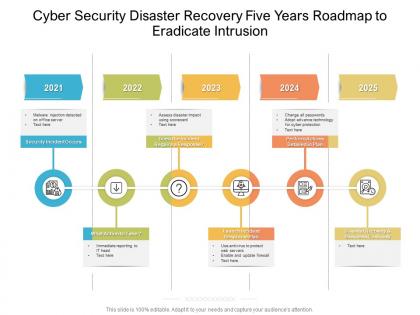 Cyber security disaster recovery five years roadmap to eradicate intrusion
Cyber security disaster recovery five years roadmap to eradicate intrusionPresenting Cyber Security Disaster Recovery Five Years Roadmap To Eradicate Intrusion PowerPoint Template. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements.
-
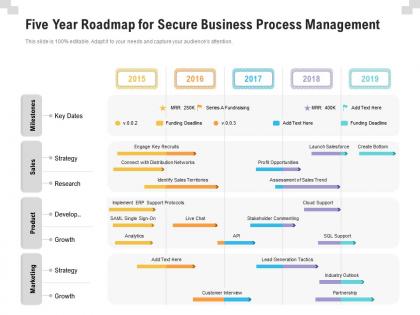 Five year roadmap for secure business process management
Five year roadmap for secure business process managementPresenting Five Year Roadmap For Secure Business Process Management PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Five hybrid cloud security issues overcome ppt powerpoint presentation model example topics cpb
Five hybrid cloud security issues overcome ppt powerpoint presentation model example topics cpbPresenting this set of slides with name Five Hybrid Cloud Security Issues Overcome Ppt Powerpoint Presentation Model Example Topics Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Five Hybrid Cloud Security Issues Overcome to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Five year cyber security roadmap for continuous threat analysis
Five year cyber security roadmap for continuous threat analysisPresenting Five Year Cyber Security Roadmap For Continuous Threat Analysis PowerPoint Template. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements.
-
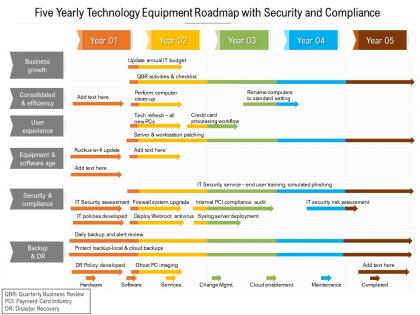 Five yearly technology equipment roadmap with security and compliance
Five yearly technology equipment roadmap with security and compliancePresenting Five Yearly Technology Equipment Roadmap With Security And Compliance PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
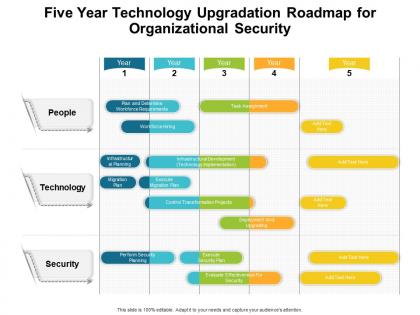 Five year technology upgradation roadmap for organizational security
Five year technology upgradation roadmap for organizational securityPresenting Five Year Technology Upgradation Roadmap For Organizational Security PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
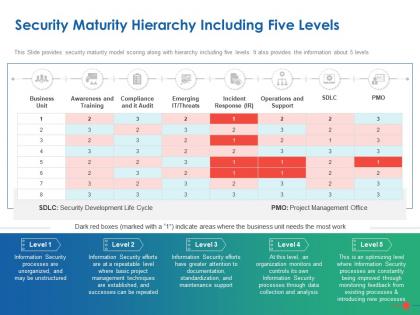 Security maturity hierarchy including five levels ppt powerpoint presentation outline
Security maturity hierarchy including five levels ppt powerpoint presentation outlineThis Slide provides security maturity model scoring along with hierarchy including five levels. It also provides the information about 5 levels. Presenting this set of slides with name Security Maturity Hierarchy Including Five Levels Ppt Powerpoint Presentation Outline. The topics discussed in these slides are Business, Awareness, Training, Processes, Security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
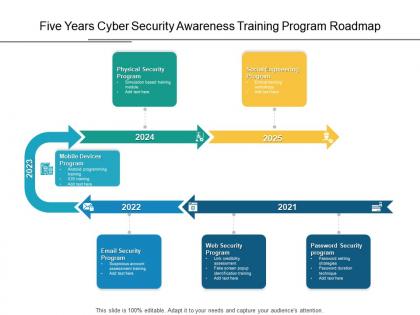 Five years cyber security awareness training program roadmap
Five years cyber security awareness training program roadmapPresenting Five Years Cyber Security Awareness Training Program Roadmap PowerPoint slide. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
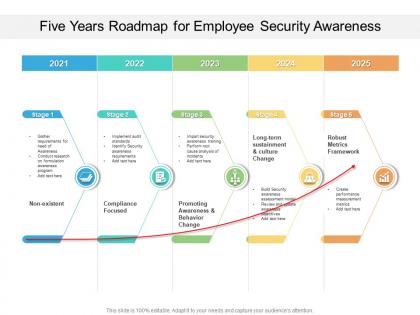 Five years roadmap for employee security awareness
Five years roadmap for employee security awarenessPresenting Five Years Roadmap For Employee Security Awareness PowerPoint slide which is 100 percent editable. You can change the color, font size, font type, and shapes of this PPT layout according to your needs. This PPT template is compatible with Google Slides and is available in both 4,3 and 16,9 aspect ratios. This ready to use PowerPoint presentation can be downloaded in various formats like PDF, JPG, and PNG.
-
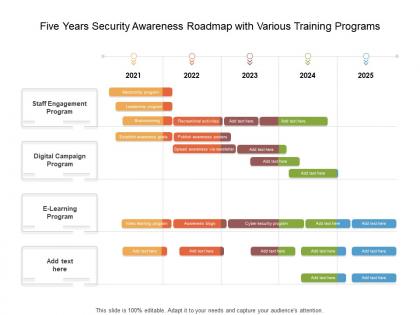 Five years security awareness roadmap with various training programs
Five years security awareness roadmap with various training programsPresenting Five Years Security Awareness Roadmap With Various Training Programs PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.


