Powerpoint Templates and Google slides for Improving Cyber Resilience
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Improving IoT Device Cybersecurity To Prevent Data Breaches Powerpoint Presentation Slides IoT CD
Improving IoT Device Cybersecurity To Prevent Data Breaches Powerpoint Presentation Slides IoT CDDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Improving IoT Device Cybersecurity To Prevent Data Breaches Powerpoint Presentation Slides IoT CD is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the one hundred fifteen slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Improving Cyber Security Risks Management Process Powerpoint PPT Template Bundles DK MD
Improving Cyber Security Risks Management Process Powerpoint PPT Template Bundles DK MDIf you require a professional template with great design, then this Improving Cyber Security Risks Management Process Powerpoint PPT Template Bundles DK MD is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using twenty one slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
 Big Data For Improved Cyber Security In The Banking Training Ppt
Big Data For Improved Cyber Security In The Banking Training PptPresenting Implementing Big Data for improved cyber security in the Banking Industry. This slide is well crafted and designed by our PowerPoint specialists. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. You can add or delete the content as per your need.
-
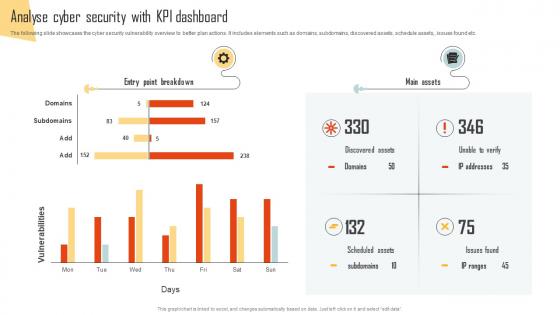 Analyse Cyber Security With KPI Dashboard Improving Cyber Security Risks Management
Analyse Cyber Security With KPI Dashboard Improving Cyber Security Risks ManagementThe following slide showcases the cyber security vulnerability overview to better plan actions. It includes elements such as domains, subdomains, discovered assets, schedule assets, , issues found etc. Present the topic in a bit more detail with this Analyse Cyber Security With KPI Dashboard Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Entry Point Breakdown, Scheduled Assets, Discovered Assets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
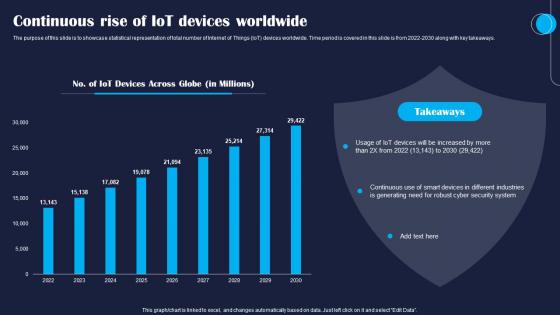 Continuous Rise Of IoT Devices Worldwide Improving IoT Device Cybersecurity IoT SS
Continuous Rise Of IoT Devices Worldwide Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase statistical representation of total number of Internet of Things IoT devices worldwide. Time period is covered in this slide is from 2022 2030 along with key takeaways. Present the topic in a bit more detail with this Continuous Rise Of IoT Devices Worldwide Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Continuous, Devices, Worldwide. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
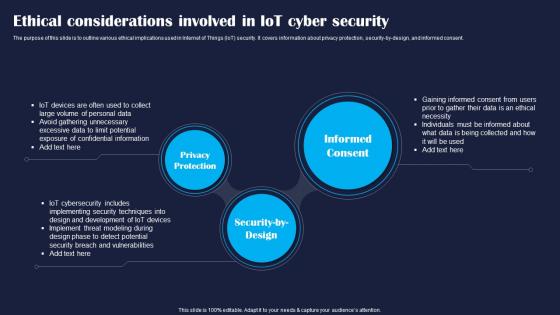 Ethical Considerations Involved In Improving IoT Device Cybersecurity IoT SS
Ethical Considerations Involved In Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline various ethical implications used in Internet of Things IoT security. It covers information about privacy protection, security by design, and informed consent. Introducing Ethical Considerations Involved In Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Devices, Development, Security, using this template. Grab it now to reap its full benefits.
-
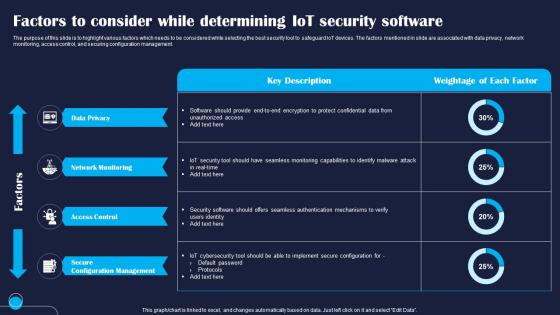 Factors To Consider While Determining IoT Improving IoT Device Cybersecurity IoT SS
Factors To Consider While Determining IoT Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight various factors which needs to be considered while selecting the best security tool to safeguard IoT devices. The factors mentioned in slide are associated with data privacy, network monitoring, access control, and securing configuration management. Deliver an outstanding presentation on the topic using this Factors To Consider While Determining IoT Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Data, Network, Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
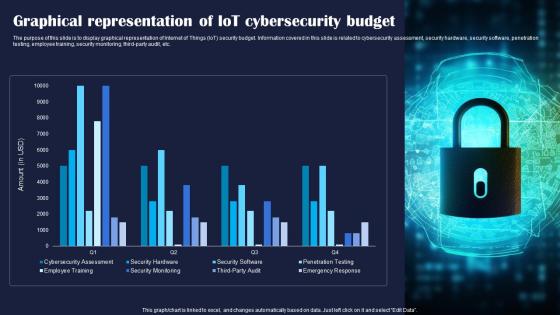 Graphical Representation Of Improving IoT Device Cybersecurity IoT SS
Graphical Representation Of Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display graphical representation of Internet of Things IoT security budget. Information covered in this slide is related to cybersecurity assessment, security hardware, security software, penetration testing, employee training, security monitoring, third party audit, etc. Present the topic in a bit more detail with this Graphical Representation Of Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Graphical, Cybersecurity, Budget. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
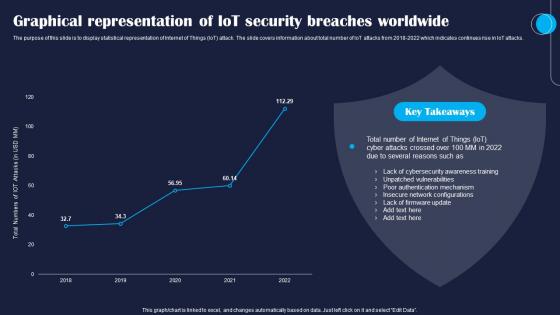 Graphical Representation Of IoT Improving IoT Device Cybersecurity IoT SS
Graphical Representation Of IoT Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display statistical representation of Internet of Things IoT attack. The slide covers information about total number of IoT attacks from 2018 2022 which indicates continues rise in IoT attacks. Deliver an outstanding presentation on the topic using this Graphical Representation Of IoT Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Graphical, Security, Worldwide using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
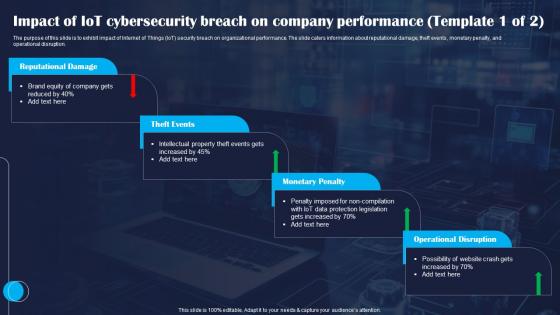 Impact Of IoT Cybersecurity Breach On Improving IoT Device Cybersecurity IoT SS
Impact Of IoT Cybersecurity Breach On Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit impact of Internet of Things IoT security breach on organizational performance. The slide caters information about reputational damage, theft events, monetary penalty, and operational disruption. Deliver an outstanding presentation on the topic using this Impact Of IoT Cybersecurity Breach On Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Reputational, Events, Penalty using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
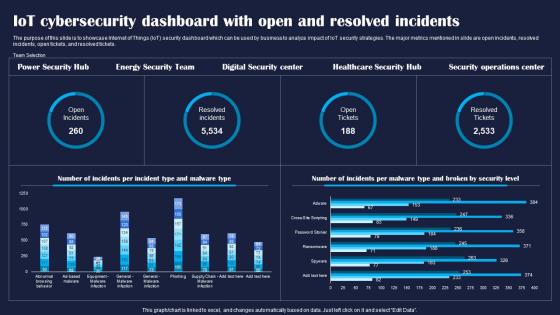 IoT Cybersecurity Dashboard With Open And Improving IoT Device Cybersecurity IoT SS
IoT Cybersecurity Dashboard With Open And Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase Internet of Things IoT security dashboard which can be used by business to analyze impact of IoT security strategies. The major metrics mentioned in slide are open incidents, resolved incidents, open tickets, and resolved tickets. Deliver an outstanding presentation on the topic using this IoT Cybersecurity Dashboard With Open And Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Cybersecurity, Resolved, Incidents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
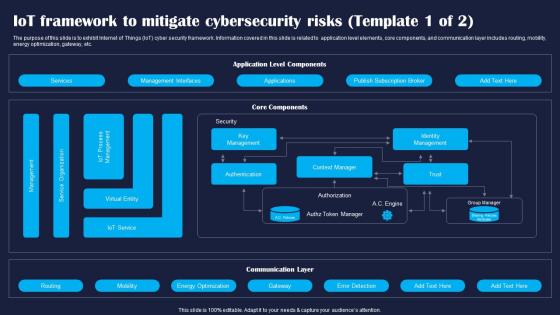 IoT Framework To Mitigate Cybersecurity Improving IoT Device Cybersecurity IoT SS
IoT Framework To Mitigate Cybersecurity Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit Internet of Things IoT cyber security framework. Information covered in this slide is related to application level elements, core components, and communication layer includes routing, mobility, energy optimization, gateway, etc. Present the topic in a bit more detail with this IoT Framework To Mitigate Cybersecurity Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Services, Management, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SS
IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight Internet of Things IoT password attack prevention measures. The techniques outlined in slide are limit public information, verifying the source, and no sharing of password. Deliver an outstanding presentation on the topic using this IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Information, Verify, Password using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IoT Security Dashboard With User Improving IoT Device Cybersecurity IoT SS
IoT Security Dashboard With User Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline key performance indicator KPI metrics dashboard of IoT security. The major metrics mentioned in slide are alert severity, alert breakdown, entity breakdown, user notification, reset password, authentications request, etc. Present the topic in a bit more detail with this IoT Security Dashboard With User Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Security, Notifications, Notification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
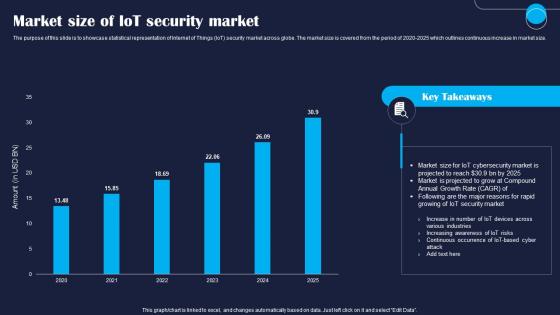 Market Size Of IoT Security Market Improving IoT Device Cybersecurity IoT SS
Market Size Of IoT Security Market Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase statistical representation of Internet of Things IoT security market across globe. The market size is covered from the period of 2020 2025 which outlines continuous increase in market size. Present the topic in a bit more detail with this Market Size Of IoT Security Market Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Market, Security, Market. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
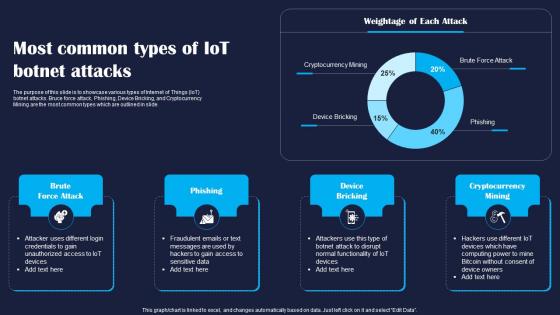 Most Common Types Of IoT Botnet Attacks Improving IoT Device Cybersecurity IoT SS
Most Common Types Of IoT Botnet Attacks Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase various types of Internet of Things IoT botnet attacks. Bruce force attack, Phishing, Device Bricking, and Cryptocurrency Mining are the most common types which are outlined in slide. Present the topic in a bit more detail with this Most Common Types Of IoT Botnet Attacks Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Phishing, Bricking, Mining. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
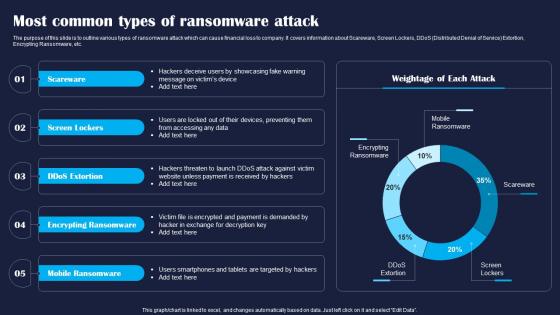 Most Common Types Of Ransomware Attack Improving IoT Device Cybersecurity IoT SS
Most Common Types Of Ransomware Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline various types of ransomware attack which can cause financial loss to company. It covers information about Scareware, Screen Lockers, DDoS Distributed Denial of Service Extortion, Encrypting Ransomware, etc. Deliver an outstanding presentation on the topic using this Most Common Types Of Ransomware Attack Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Scareware, Lockers, Mobile using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
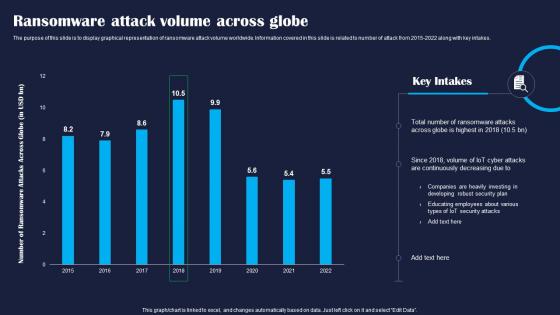 Ransomware Attack Volume Across Globe Improving IoT Device Cybersecurity IoT SS
Ransomware Attack Volume Across Globe Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display graphical representation of ransomware attack volume worldwide. Information covered in this slide is related to number of attack from 2015 2022 along with key intakes. Deliver an outstanding presentation on the topic using this Ransomware Attack Volume Across Globe Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Globe, Attacks, Developing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
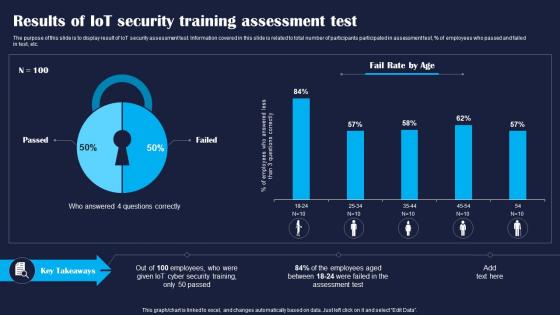 Results Of IoT Security Training Improving IoT Device Cybersecurity IoT SS
Results Of IoT Security Training Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display result of IoT security assessment test. Information covered in this slide is related to total number of participants participated in assessment test, percentage of employees who passed and failed in test, etc. Present the topic in a bit more detail with this Results Of IoT Security Training Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Assessment, Training, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
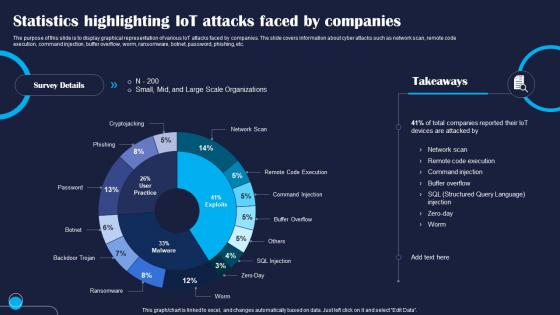 Statistics Highlighting IoT Attacks Faced Improving IoT Device Cybersecurity IoT SS
Statistics Highlighting IoT Attacks Faced Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display graphical representation of various IoT attacks faced by companies. The slide covers information about cyber attacks such as network scan, remote code execution, command injection, buffer overflow, worm, ransomware, botnet, password, phishing, etc. Present the topic in a bit more detail with this Statistics Highlighting IoT Attacks Faced Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Statistics, Injection, Execution. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
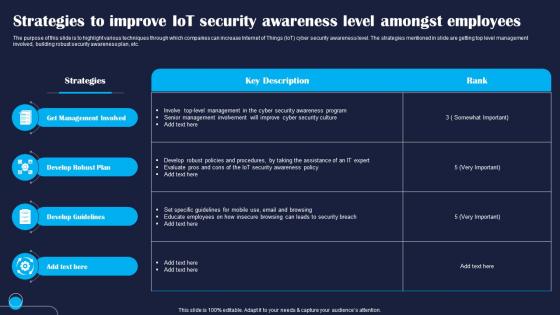 Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SS
Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight various techniques through which companies can increase Internet of Things IoT cyber security awareness level. The strategies mentioned in slide are getting top level management involved, building robust security awareness plan, etc. Present the topic in a bit more detail with this Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Management, Develop, Guidelines. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS
Table Of Contents Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS. This template helps you present information on six stages. You can also present information on Security, Strategies, Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
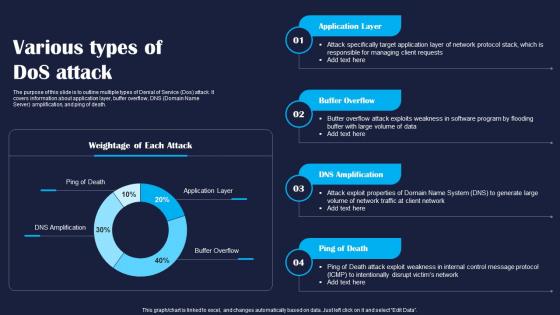 Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SS
Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline multiple types of Denial of Service Dos attack. It covers information about application layer, buffer overflow, DNS Domain Name Server amplification, and ping of death. Deliver an outstanding presentation on the topic using this Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Application, Layer, Death using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
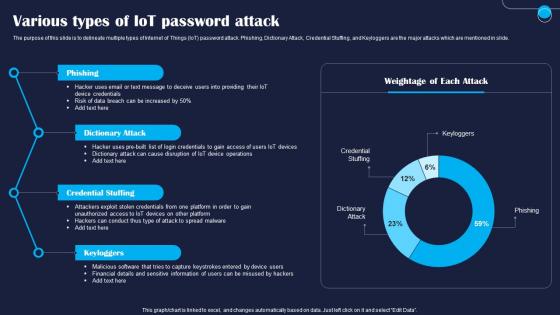 Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS
Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to delineate multiple types of Internet of Things IoT password attack. Phishing, Dictionary Attack, Credential Stuffing, and Keyloggers are the major attacks which are mentioned in slide. Present the topic in a bit more detail with this Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Phishing, Dictionary, Credential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Incident Tracking Dashboard For Improving Cyber Resilence
Incident Tracking Dashboard For Improving Cyber ResilenceThis slide showcases incident tracking KPI dashboard for prioritizing resolution to ensure optimal functioning of data and security. It includes metrics such as total incidents, open incidents, average resolution time, unassigned tickets, past due issues, past due incidents, etc. Presenting our well structured Incident Tracking Dashboard For Facilitating Trend Analysis. The topics discussed in this slide are Incident Tracking, Improving Cyber Resilience, Average Resolution Time. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
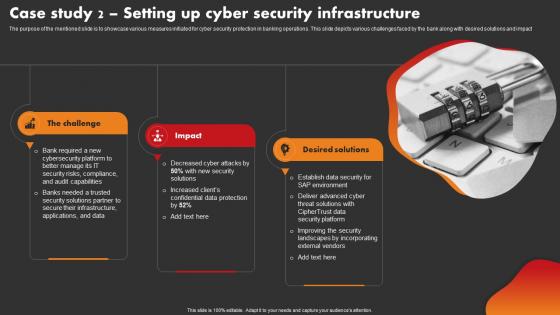 Case Study 2 Setting Up Cyber Security Infrastructure Strategic Improvement In Banking Operations
Case Study 2 Setting Up Cyber Security Infrastructure Strategic Improvement In Banking OperationsThe purpose of the mentioned slide is to showcase various measures initiated for cyber security protection in banking operations. This slide depicts various challenges faced by the bank along with desired solutions and impact Introducing Case Study 2 Setting Up Cyber Security Infrastructure Strategic Improvement In Banking Operations to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Infrastructure, Desired Solutions, Environment, using this template. Grab it now to reap its full benefits.
-
 ChatGPT For Streamlining And Improving How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS
ChatGPT For Streamlining And Improving How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SSThis slide showcases overview of ChatGPT for streamlining and optimizing the security operations in organizations. Its key elements are cybersecurity training, enhanced communication during attack, developing policies and reporting after attack Introducing ChatGPT For Streamlining And Improving How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Training, Communication, Reporting, using this template. Grab it now to reap its full benefits.
-
 Analyse And Rank Impact Of Cyber Threat Improving Cyber Security Risks Management
Analyse And Rank Impact Of Cyber Threat Improving Cyber Security Risks ManagementThe following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Present the topic in a bit more detail with this Analyse And Rank Impact Of Cyber Threat Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Vulnerability, Threat Source, Appropriate Structure, Privilege Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
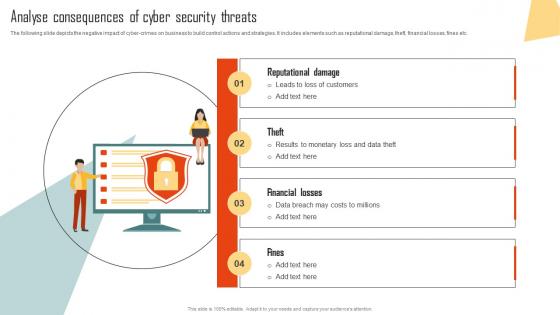 Analyse Consequences Of Cyber Security Threats Improving Cyber Security Risks Management
Analyse Consequences Of Cyber Security Threats Improving Cyber Security Risks ManagementThe following slide depicts the negative impact of cyber-crimes on business to build control actions and strategies. It includes elements such as reputational damage, theft, financial losses, fines etc. Introducing Analyse Consequences Of Cyber Security Threats Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reputational Damage, Financial Losses, Security Threats, using this template. Grab it now to reap its full benefits.
-
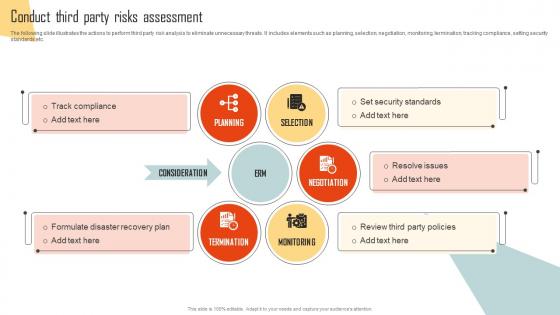 Conduct Third Party Risks Assessment Improving Cyber Security Risks Management
Conduct Third Party Risks Assessment Improving Cyber Security Risks ManagementThe following slide illustrates the actions to perform third party risk analysis to eliminate unnecessary threats. It includes elements such as planning, selection, negotiation, monitoring, termination, tracking compliance, setting security standards etc. Introducing Conduct Third Party Risks Assessment Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Planning, Selection, Negotiation, Monitoring, Termination, using this template. Grab it now to reap its full benefits.
-
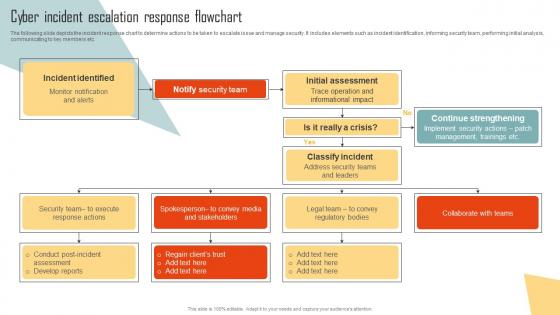 Cyber Incident Escalation Response Flowchart Improving Cyber Security Risks Management
Cyber Incident Escalation Response Flowchart Improving Cyber Security Risks ManagementThe following slide depicts the incident response chart to determine actions to be taken to escalate issue and manage security. It includes elements such as incident identification, informing security team, performing initial analysis, communicating to key members etc. Present the topic in a bit more detail with this Cyber Incident Escalation Response Flowchart Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Incident Identified, Notify Security Team, Initial Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
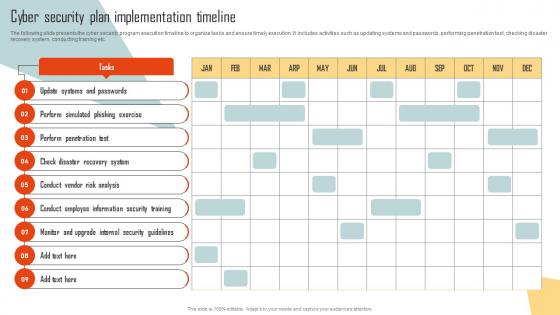 Cyber Security Plan Implementation Timeline Improving Cyber Security Risks Management
Cyber Security Plan Implementation Timeline Improving Cyber Security Risks ManagementThe following slide presents the cyber security program execution timeline to organize tasks and ensure timely execution. It includes activities such as updating systems and passwords, performing penetration test, checking disaster recovery system, conducting training etc. Introducing Cyber Security Plan Implementation Timeline Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Systems And Passwords, Perform Simulated, Phishing Exercise, using this template. Grab it now to reap its full benefits.
-
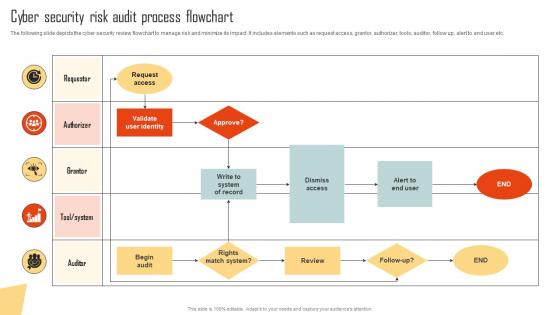 Cyber Security Risk Audit Process Flowchart Improving Cyber Security Risks Management
Cyber Security Risk Audit Process Flowchart Improving Cyber Security Risks ManagementThe following slide depicts the cyber security review flowchart to manage risk and minimize its impact. It includes elements such as request access, grantor, authorizer, tools, auditor, follow up, alert to end user etc. Present the topic in a bit more detail with this Cyber Security Risk Audit Process Flowchart Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Request Access, Validate User Identity, Dismiss Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Deploy Tools To Minimize Impact Of Cyber Security Risks Improving Cyber Security Risks Management
Deploy Tools To Minimize Impact Of Cyber Security Risks Improving Cyber Security Risks ManagementThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool name, features, trial period, cost and reviews etc. Deliver an outstanding presentation on the topic using this Deploy Tools To Minimize Impact Of Cyber Security Risks Improving Cyber Security Risks Management. Dispense information and present a thorough explanation of Determines Suspicious, Features, Cyber Security Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
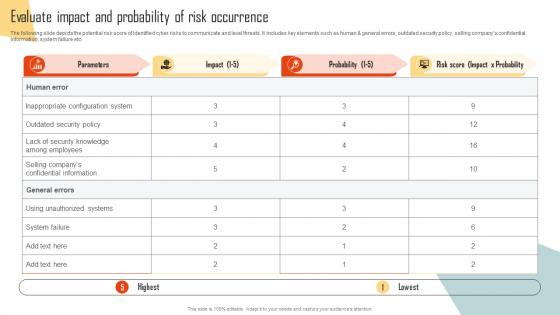 Evaluate Impact And Probability Of Risk Occurrence Improving Cyber Security Risks Management
Evaluate Impact And Probability Of Risk Occurrence Improving Cyber Security Risks ManagementThe following slide depicts the potential risk score of identified cyber risks to communicate and level threats. It includes key elements such as human and general errors, outdated security policy, selling companys confidential information, system failure etc. Present the topic in a bit more detail with this Evaluate Impact And Probability Of Risk Occurrence Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Parameters, Inappropriate Configuration System, Unauthorized Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
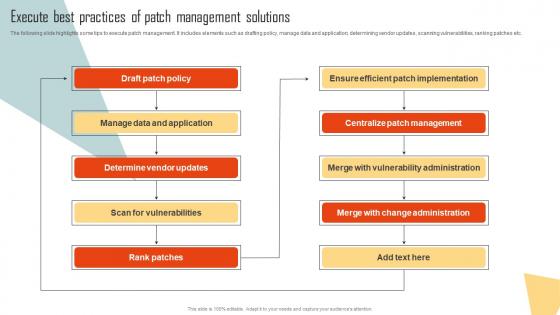 Execute Best Practices Of Patch Management Solutions Improving Cyber Security Risks Management
Execute Best Practices Of Patch Management Solutions Improving Cyber Security Risks ManagementThe following slide highlights some tips to execute patch management. It includes elements such as drafting policy, manage data and application, determining vendor updates, scanning vulnerabilities, ranking patches etc. Deliver an outstanding presentation on the topic using this Execute Best Practices Of Patch Management Solutions Improving Cyber Security Risks Management. Dispense information and present a thorough explanation of Draft Patch Policy, Manage Data And Application, Determine Vendor Updates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management
Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks ManagementThe following slide showcases the various types of cyber-attacks faced by employees to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service etc. Introducing Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Spear Phishing, Advanced Persistent Threats, Ransomware, Phishing, using this template. Grab it now to reap its full benefits.
-
 Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks Management
Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks ManagementThe following slide illustrates some best practices to execute preventive actions for cyber attacks. It includes elements such as train employees, updating systems and software, developing incident response plan, backing up data, maintaining compliance etc. Increase audience engagement and knowledge by dispensing information using Implement Best Practices To Prevent Cyber Attacks Improving Cyber Security Risks Management. This template helps you present information on six stages. You can also present information on Train Employees, Maintain Compliance, Develop Incident Response Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Plan Useful Data Backup Schedule Improving Cyber Security Risks Management
Plan Useful Data Backup Schedule Improving Cyber Security Risks ManagementThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Present the topic in a bit more detail with this Plan Useful Data Backup Schedule Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Incremental Backup, Plan Useful, Data Backup Schedule. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Prioritize Cyber Security Risks With Matrix Improving Cyber Security Risks Management
Prioritize Cyber Security Risks With Matrix Improving Cyber Security Risks ManagementThe following slide presents cyber security risks exposure grid to determine and plan mitigation actions. It includes elements such as restricting permissions, remediating constantly, postponing remediation, tracking risk escalation etc. Introducing Prioritize Cyber Security Risks With Matrix Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Restrict Permissions, Postpone Remediation, Track Risk Escalation, using this template. Grab it now to reap its full benefits.
-
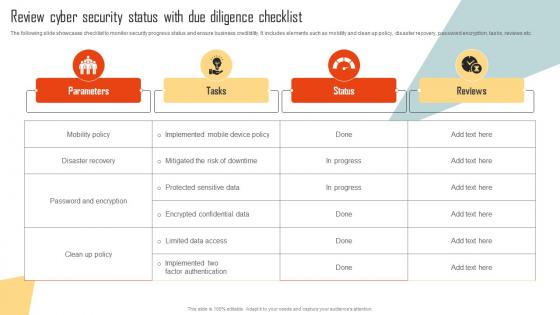 Review Cyber Security Status With Due Diligence Checklist Improving Cyber Security Risks Management
Review Cyber Security Status With Due Diligence Checklist Improving Cyber Security Risks ManagementThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Present the topic in a bit more detail with this Review Cyber Security Status With Due Diligence Checklist Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Disaster Recovery, Password And Encryption, Parameters. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
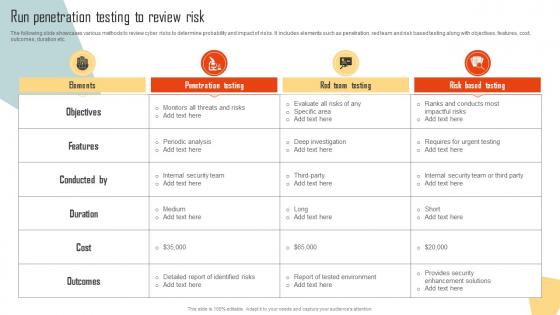 Run Penetration Testing To Review Risk Improving Cyber Security Risks Management
Run Penetration Testing To Review Risk Improving Cyber Security Risks ManagementThe following slide showcases various methods to review cyber risks to determine probability and impact of risks. It includes elements such as penetration, red team and risk based testing along with objectives, features, cost, outcomes, duration etc. Deliver an outstanding presentation on the topic using this Run Penetration Testing To Review Risk Improving Cyber Security Risks Management. Dispense information and present a thorough explanation of Objectives, Features, Conducted, Duration, Outcomes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Select Cybersecurity Training Program Courses Improving Cyber Security Risks Management
Select Cybersecurity Training Program Courses Improving Cyber Security Risks ManagementThe following slide showcases the best cybersecurity training courses to educate employees and minimize the possibility of cyber-attacks. It includes cloud, disaster recovery, hardware, information security programs, duration, mode and cost. Present the topic in a bit more detail with this Select Cybersecurity Training Program Courses Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Cloud Security, Information Security, Cybersecurity Fundamentals. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents For Improving Cyber Security Risk Management Process
Table Of Contents For Improving Cyber Security Risk Management ProcessIntroducing Table Of Contents For Improving Cyber Security Risk Management Process to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risks And Attacks, Management Solutions, Program Courses, using this template. Grab it now to reap its full benefits.
-
 Various Sources Of Cyber Security Incidents Improving Cyber Security Risks Management
Various Sources Of Cyber Security Incidents Improving Cyber Security Risks ManagementThe following slide depicts some multiple drivers of cyber security incidents to generate awareness about cyber crimes. It includes elements such as corporate spies, malicious insiders, criminal groups, hackers, hacktivists, terrorist groups etc. Increase audience engagement and knowledge by dispensing information using Various Sources Of Cyber Security Incidents Improving Cyber Security Risks Management. This template helps you present information on seven stages. You can also present information on Criminal Groups, Terrorist Groups, Malicious Insiders, Corporate Spies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations
Cyber Security Risk Assessment And Technology Deployment Plan To Improve OrganizationsThis slide represents the assessment of vulnerability and consequences of the cyber security incidents on the operations of the company. It includes details related to threat, vulnerability, consequences, risk and solution Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Technology Deployment Plan To Improve Organizations. Dispense information and present a thorough explanation of Consequences, Vulnerability, Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations
Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve OrganizationsThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Introducing Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing, Malware, Application, using this template. Grab it now to reap its full benefits.
-
 Agenda Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS
Agenda Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SSIntroducing Agenda Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Provide, Business, Common, using this template. Grab it now to reap its full benefits.
-
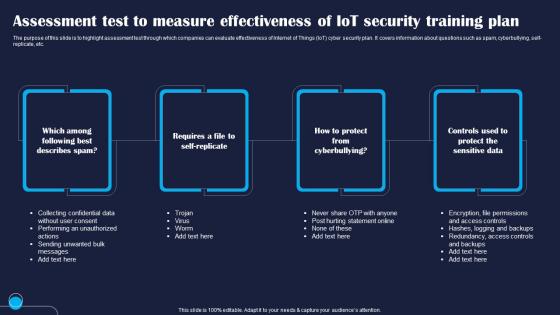 Assessment Test To Measure Effectiveness Of Improving IoT Device Cybersecurity IoT SS
Assessment Test To Measure Effectiveness Of Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight assessment test through which companies can evaluate effectiveness of Internet of Things IoT cyber security plan. It covers information about questions such as spam, cyberbullying, self replicate, etc. Increase audience engagement and knowledge by dispensing information using Assessment Test To Measure Effectiveness Of Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Describes, Requires, Cyberbullying using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
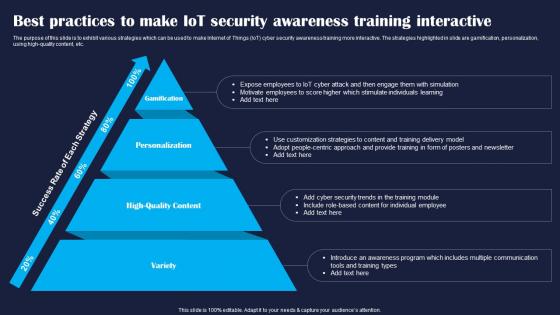 Best Practices To Make IoT Security Improving IoT Device Cybersecurity IoT SS
Best Practices To Make IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit various strategies which can be used to make Internet of Things IoT cyber security awareness training more interactive. The strategies highlighted in slide are gamification, personalization, using high quality content, etc. Introducing Best Practices To Make IoT Security Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Variety, Personalization, Gamification, using this template. Grab it now to reap its full benefits.
-
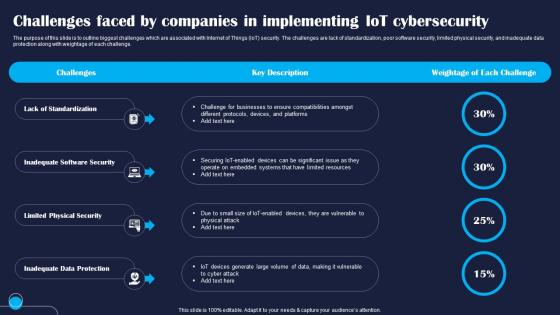 Challenges Faced By Companies In Improving IoT Device Cybersecurity IoT SS
Challenges Faced By Companies In Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline biggest challenges which are associated with Internet of Things IoT security. The challenges are lack of standardization, poor software security, limited physical security, and inadequate data protection along with weightage of each challenge. Increase audience engagement and knowledge by dispensing information using Challenges Faced By Companies In Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Standardization, Software, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
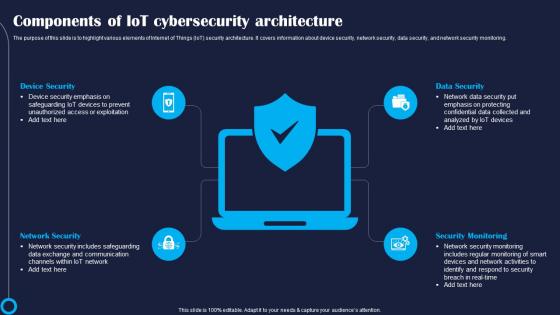 Components Of IoT Cybersecurity Improving IoT Device Cybersecurity IoT SS
Components Of IoT Cybersecurity Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight various elements of Internet of Things IoT security architecture. It covers information about device security, network security, data security, and network security monitoring. Introducing Components Of IoT Cybersecurity Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Device, Network, Monitoring, using this template. Grab it now to reap its full benefits.
-
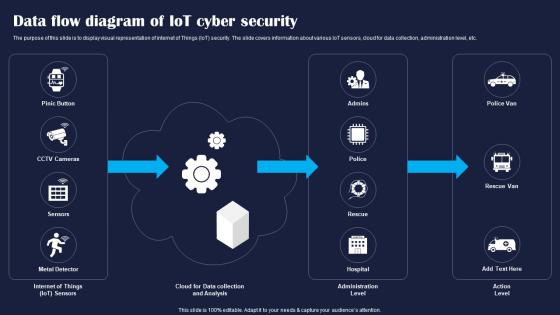 Data Flow Diagram Of IoT Cyber Security Improving IoT Device Cybersecurity IoT SS
Data Flow Diagram Of IoT Cyber Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display visual representation of internet of Things IoT security. The slide covers information about various IoT sensors, cloud for data collection, administration level, etc. Deliver an outstanding presentation on the topic using this Data Flow Diagram Of IoT Cyber Security Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Data, Security, Cyber using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
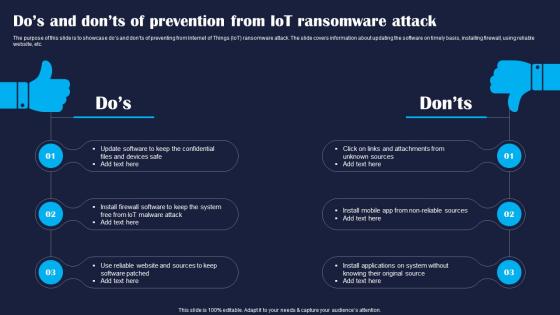 Dos And Donts Of Prevention From Improving IoT Device Cybersecurity IoT SS
Dos And Donts Of Prevention From Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase dos and donts of preventing from Internet of Things IoT ransomware attack. The slide covers information about updating the software on timely basis, installing firewall, using reliable website, etc. Present the topic in a bit more detail with this Dos And Donts Of Prevention From Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Update, Software, Patched. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
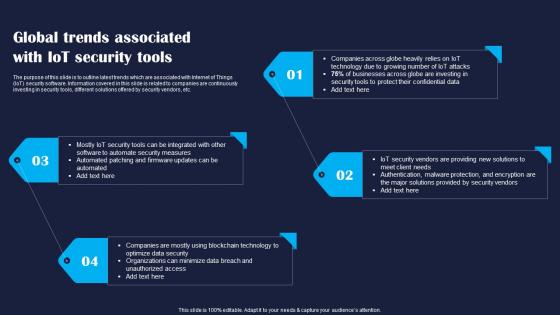 Global Trends Associated With Improving IoT Device Cybersecurity IoT SS
Global Trends Associated With Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline latest trends which are associated with Internet of Things IoT security software. Information covered in this slide is related to companies are continuously investing in security tools, different solutions offered by security vendors, etc. Introducing Global Trends Associated With Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Software, Firmware, Organizations, using this template. Grab it now to reap its full benefits.
-
 Growth Opportunities In IoT Security Improving IoT Device Cybersecurity IoT SS
Growth Opportunities In IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase emerging opportunities in Internet of Things IoT cyber security market. Higher adoption of IoT devices, continuous rise in cyber attack, and cloud based security solutions are the major growth opportunities which are highlighted in slide. Increase audience engagement and knowledge by dispensing information using Growth Opportunities In IoT Security Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Devices, Cyber, Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
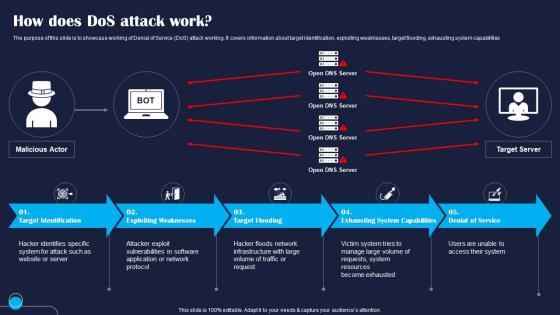 How Does Dos Attack Work Improving IoT Device Cybersecurity IoT SS
How Does Dos Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase working of Denial of Service DoS attack working. It covers information about target identification, exploiting weaknesses, target flooding, exhausting system capabilities Introducing How Does Dos Attack Work Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Target, Exploiting, Flooding, using this template. Grab it now to reap its full benefits.
-
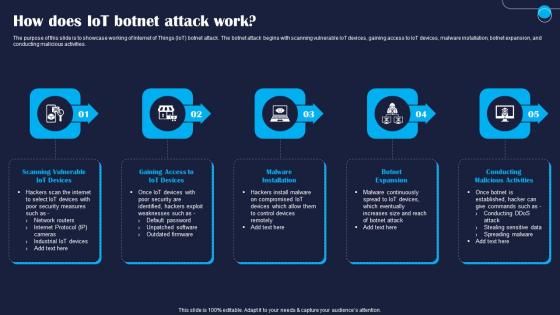 How Does IoT Botnet Attack Work Improving IoT Device Cybersecurity IoT SS
How Does IoT Botnet Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase working of Internet of Things IoT botnet attack. The botnet attack begins with scanning vulnerable IoT devices, gaining access to IoT devices, malware installation, botnet expansion, and conducting malicious activities. Increase audience engagement and knowledge by dispensing information using How Does IoT Botnet Attack Work Improving IoT Device Cybersecurity IoT SS. This template helps you present information on five stages. You can also present information on Devices, Gaining, Installation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
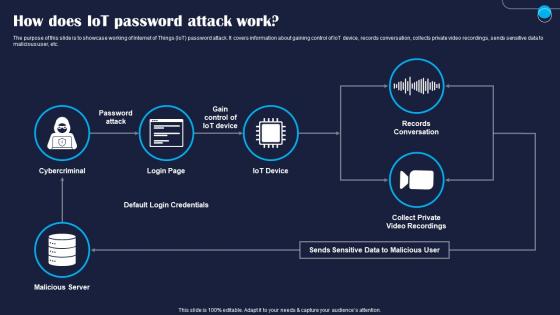 How Does IoT Password Attack Work Improving IoT Device Cybersecurity IoT SS
How Does IoT Password Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase working of Internet of Things IoT password attack. It covers information about gaining control of IoT device, records conversation, collects private video recordings, sends sensitive data to malicious user, etc. Present the topic in a bit more detail with this How Does IoT Password Attack Work Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Cybercriminal, Server, Default. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
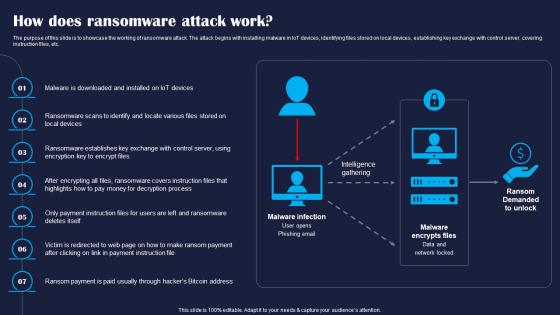 How Does Ransomware Attack Work Improving IoT Device Cybersecurity IoT SS
How Does Ransomware Attack Work Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase the working of ransomware attack. The attack begins with installing malware in IoT devices, identifying files stored on local devices, establishing key exchange with control server, covering instruction files, etc. Increase audience engagement and knowledge by dispensing information using How Does Ransomware Attack Work Improving IoT Device Cybersecurity IoT SS. This template helps you present information on seven stages. You can also present information on Devices, Exchange, Covers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


