Powerpoint Templates and Google slides for Protection Cyber Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Mdr Cybersecurity Icon For Multi Cloud Data Protection
Mdr Cybersecurity Icon For Multi Cloud Data ProtectionIntroducing our Mdr Cybersecurity Icon For Multi Cloud Data Protection set of slides. The topics discussed in these slides are Cybersecurity, Data Protection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Mdr Icon To Enhance Cybersecurity For Information Protection
Mdr Icon To Enhance Cybersecurity For Information ProtectionIntroducing our Mdr Icon To Enhance Cybersecurity For Information Protection set of slides. The topics discussed in these slides are Cybersecurity, Information, Protection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 BCP Icon For Enhancing Data Protection And Cybersecurity
BCP Icon For Enhancing Data Protection And CybersecurityPresenting our set of slides with BCP Icon For Enhancing Data Protection And Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on BCP Icon For Enhancing, Data Protection, Cybersecurity
-
 Best Practices To Improve Cybersecurity In BCP For Data Protection
Best Practices To Improve Cybersecurity In BCP For Data ProtectionThis slide represents various best practices that helps businesses in improving cybersecurity against online data threats affecting business continuity. It includes practices such as using VPN, Training employees, backing up companies data, etc. Presenting our set of slides with Best Practices To Improve Cybersecurity In BCP For Data Protection This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Continuity Software, Backup Company, Train Employees
-
 Implementing Cybersecurity In BCP For Enhancing Risk Protection
Implementing Cybersecurity In BCP For Enhancing Risk ProtectionThis slide represents process to implement cybersecurity in business continuity planning BCP for improving company data protection from cyber risks. It includes steps such as conducting business impact analysis, developing risk assessment, maintaining total vison, etc. Presenting our set of slides with Implementing Cybersecurity In BCP For Enhancing Risk Protection This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Maintain Total Vision, Risk Management, Implement Controls
-
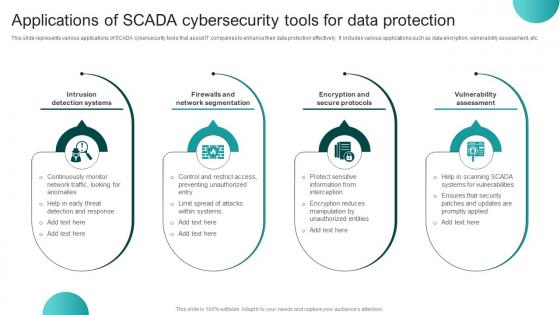 Applications Of SCADA Cybersecurity Tools For Data Protection
Applications Of SCADA Cybersecurity Tools For Data ProtectionThis slide represents various applications of SCADA cybersecurity tools that assist IT companies to enhance their data protection effectively. It includes various applications such as data encryption, vulnerability assessment, etc. Introducing our premium set of slides with Applications Of SCADA Cybersecurity Tools For Data Protection Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Intrusion Detection Systems, Firewalls And Network Segmentation, Encryption And Secure Protocols. So download instantly and tailor it with your information.
-
 SCADA Cybersecurity Icon For Network Breach Protection
SCADA Cybersecurity Icon For Network Breach ProtectionIntroducing our SCADA Cybersecurity Icon For Network Breach Protection set of slides. The topics discussed in these slides are SCADA Cybersecurity Icon, Network Breach Protection This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Working Model Of SCADA Cybersecurity For Data Protection
Working Model Of SCADA Cybersecurity For Data ProtectionThis slide represents working model of SCADA cybersecurity that assists IT companies to secure their data from vulnerable attacks. It includes various components such as impact analysis, mitigation strategies, etc. Presenting our well structured Working Model Of SCADA Cybersecurity For Data Protection The topics discussed in this slide are Remedial, Prevention, Decision Making. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Triage Cyber Security For System Protection Icon
Triage Cyber Security For System Protection IconPresenting our set of slides with name Triage Cyber Security For System Protection Icon This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Triage Cyber Security, System Protection Icon
-
 Cybersecurity Incident Response Icon For Data Protection
Cybersecurity Incident Response Icon For Data ProtectionIntroducing our premium set of slides with name Cybersecurity Incident Response Icon For Data Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybersecurity Incident, Response Icon, Data Protection. So download instantly and tailor it with your information.
-
 Cybersecurity Incident Investigation Icon To Enhance Data Protection
Cybersecurity Incident Investigation Icon To Enhance Data ProtectionIncrease audience engagement and knowledge by dispensing information using Cybersecurity Incident Investigation Icon To Enhance Data Protection. This template helps you present information on four stages. You can also present information on Cybersecurity Incident Investigation Icon, Enhance Data Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Security Icon Protecting From Cyber Threats
Firewall Security Icon Protecting From Cyber ThreatsIntroducing our Firewall Security Icon Protecting From Cyber Threats set of slides. The topics discussed in these slides are Firewall Security, Protecting. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Csirt Cyber Security Icon For Protecting Data
Csirt Cyber Security Icon For Protecting DataIntroducing our premium set of slides with Csirt Cyber Security Icon For Protecting Data. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Csirt Cyber Security, Protecting Data. So download instantly and tailor it with your information.
-
 Building Cybersecurity Icon For Data Protection
Building Cybersecurity Icon For Data ProtectionPresenting our set of slides with Building Cybersecurity Icon For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Building Cybersecurity,Icon,Data Protection.
-
 Cybersecurity Trends Enhancing Corporate Data Protection
Cybersecurity Trends Enhancing Corporate Data ProtectionThis slide represents various strategies assisting companies to mitigate emerging cybersecurity trends of data breaches enhancing information protection management. It includes trends such as remote working risks, rise of ransomware, and social engineering attacks. Introducing our Cybersecurity Trends Enhancing Corporate Data Protection set of slides. The topics discussed in these slides are Trends, Mitigation Strategies, Details. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cybersecurity Trends To Enhance Cloud Data Protection
Cybersecurity Trends To Enhance Cloud Data ProtectionThis slide represents various cybersecurity trends that help business security teams enhance cloud data protection effectively. It includes trends such as cybersecurity mesh, zero trust, multi-cloud environment, hybrid environment, and DevSecOps. Introducing our premium set of slides with Cybersecurity Trends To Enhance Cloud Data Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybersecurity Mesh, Zero Trust, Devsecops. So download instantly and tailor it with your information.
-
 E Commerce Cybersecurity Trends For Customer Data Protection
E Commerce Cybersecurity Trends For Customer Data ProtectionThis slide represents various cybersecurity trends that helps ecommerce companies to enhance data protection improving customer satisfaction. It includes trends such as new payment options, AI adoption, blockchain systems, etc. Presenting our set of slides with E Commerce Cybersecurity Trends For Customer Data Protection. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on New Payment Options, AI Adoption, Blockchain Systems.
-
 Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security Threat
Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information leveraging multifactor authentication to increase cyber security. It includes key points such as failed login, geographic location, time of login, operating system, IP address, etc. Deliver an outstanding presentation on the topic using this Multi Factor A For Business Data Protection Business Recovery Plan To Overcome Cyber Security Threat. Dispense information and present a thorough explanation of Time Of Login Attempt, Operating System, Source Of IP Address using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 OT Security Icon For Cyber Threat Protection
OT Security Icon For Cyber Threat ProtectionIntroducing our premium set of slides with OT Security Icon For Cyber Threat Protection Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like OT Security Icon, Cyber Threat Protection So download instantly and tailor it with your information.
-
 Cybersecurity Policy Icon Showcasing Threat Protection
Cybersecurity Policy Icon Showcasing Threat ProtectionIntroducing our Cybersecurity Policy Icon Showcasing Threat Protection set of slides. The topics discussed in these slides are Cybersecurity Policy Icon Showcasing Threat ProtectionThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data Protection Information Cybersecurity Illustration
Data Protection Information Cybersecurity IllustrationThis coloured PowerPoint icon is the perfect visual aid for presentations on safeguarding businesses with data loss prevention. Its eye-catching design and vibrant colours will capture the attention of your audience, while effectively representing the importance of protecting sensitive data in the workplace. Add it to your slides for a professional and impactful touch.
-
 Cyber Security Protection In Industry 4 0 Icon
Cyber Security Protection In Industry 4 0 IconIntroducing our premium set of slides with Cyber Security Protection In Industry 4 0 Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Protection, Industry 4 0, Icon. So download instantly and tailor it with your information.
-
 NIDS Cyber Security Icon For Sensitive Data Protection
NIDS Cyber Security Icon For Sensitive Data ProtectionIntroducing our premium set of slides with NIDS Cyber Security Icon For Sensitive Data Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Protection, Sensitive, Cyber Security. So download instantly and tailor it with your information.
-
 NIDS Cyber Security Icon To Enhance Network Protection
NIDS Cyber Security Icon To Enhance Network ProtectionPresenting our set of slides with NIDS Cyber Security Icon To Enhance Network Protection. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Protection, NIDS Cyber Security.
-
 Ethical Standards To Enhance Cybersecurity For Data Protection
Ethical Standards To Enhance Cybersecurity For Data ProtectionThis slide represents various ethical standards that assist companies to enhance their cybersecurity for effect data protection. It includes various ethical standards such as integrity, professionalism, and credibility. Introducing our premium set of slides with Ethical Standards To Enhance Cybersecurity For Data Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ethical Standards, Cyber Security, Integrity. So download instantly and tailor it with your information.
-
 Types Of Cybersecurity Ethical Issues Affecting Data Protection
Types Of Cybersecurity Ethical Issues Affecting Data ProtectionThis slide represents various actions to mitigate multiple cybersecurity ethical issues assisting companies to enhance corporate and customer data protection. It includes issues such as harm to privacy, harm to property, transparency, etc. Presenting our well structured Types Of Cybersecurity Ethical Issues Affecting Data Protection. The topics discussed in this slide are Details, Actions By Professional, Priority. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Email Protection Against Cyber Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Email Protection Against Cyber Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps FormatProtect your emails from cyber threats with our Email Security PowerPoint icon. This vibrant and eye-catching icon features a shield with a lock symbol, representing the strong defense against potential attacks. Use it to educate your audience on the importance of email security in todays digital world.
-
 Email Protection Against Cyber Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Email Protection Against Cyber Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is the perfect visual aid for presentations on Email security and defense against cyber threats. With its simple yet impactful design, it effectively conveys the importance of protecting email communications from potential cyber attacks. Add this icon to your slides to enhance your message and engage your audience.
-
 Pam Framework For Optimizing Cyber Security And Data Protection
Pam Framework For Optimizing Cyber Security And Data ProtectionThis slide represents framework that assists companies to implement PAM cybersecurity to enhance their data protection and risk management. It includes various components such as use cases, defining requirements, architecture development, etc. Presenting our well structured Pam Framework For Optimizing Cyber Security And Data Protection. The topics discussed in this slide are Determine Use Cases, Define Requirements, Develop Architecture. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Role Of Cyber Deception Technology In Protecting Businesses
Role Of Cyber Deception Technology In Protecting BusinessesThe purpose of this slide is to explore the role of cyber deception technology in safeguarding businesses from cyber threats by faster threat detection, leveraging reliable alerts and attack data. Introducing our premium set of slides with Role Of Cyber Deception Technology In Protecting Businesses. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Faster Threat Detection, Reliable Alerting, Attack Data And Metrics. So download instantly and tailor it with your information.
-
 Deploying Edr For Advanced Threat Protection Building Next Generation Endpoint Security Cybersecurity SS
Deploying Edr For Advanced Threat Protection Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases deploying endpoint detection and response EDR for advanced threat protection. It provides details about alert triage, containment, incident data search, etc.Deliver an outstanding presentation on the topic using this Deploying Edr For Advanced Threat Protection Building Next Generation Endpoint Security Cybersecurity SS. Dispense information and present a thorough explanation of Advanced Threat Detection, Incident Data Search, Alert Triage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Mitigation Plan For Malicious Code Protection Building Next Generation Endpoint Security Cybersecurity SS
Mitigation Plan For Malicious Code Protection Building Next Generation Endpoint Security Cybersecurity SSThis slide showcases mitigation plan for protection against malicious code. It can help detect malware, adware, etc. and plan action items accordingly.Present the topic in a bit more detail with this Mitigation Plan For Malicious Code Protection Building Next Generation Endpoint Security Cybersecurity SS. Use it as a tool for discussion and navigation on Malware Infection, Unauthorized Access, Adware Intrusion, Phishing Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
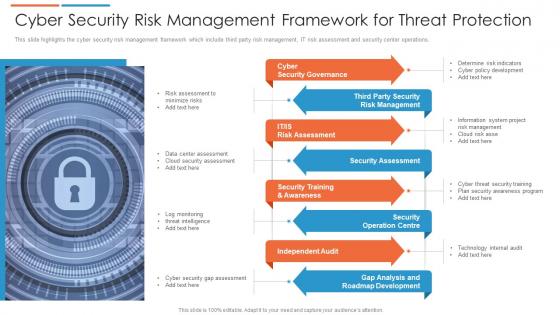 Cyber security risk management framework for threat protection
Cyber security risk management framework for threat protectionThis slide highlights the cyber security risk management framework which include third party risk management, IT risk assessment and security center operations. Presenting our set of slides with Cyber Security Risk Management Framework For Threat Protection. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Governance, Security Assessment, Independent Audit.
-
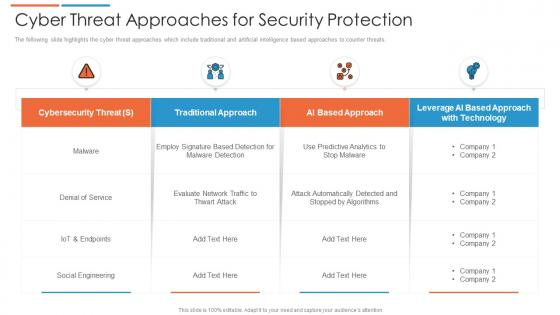 Cyber threat approaches for security protection
Cyber threat approaches for security protectionThe following slide highlights the cyber threat approaches which include traditional and artificial intelligence based approaches to counter threats. Presenting our well structured Cyber Threat Approaches For Security Protection. The topics discussed in this slide are Cybersecurity Threat, Social Engineering, Traditional Approach. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
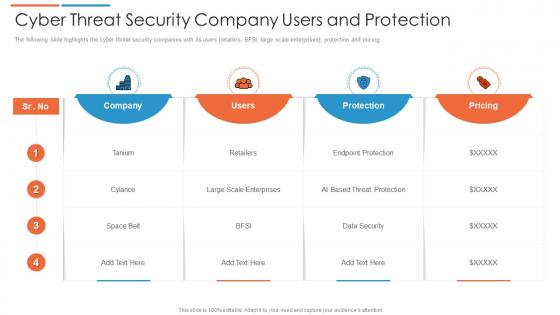 Cyber threat security company users and protection
Cyber threat security company users and protectionThe following slide highlights the cyber threat security companies with its users retailers, BFSI, large scale enterprises, protection and pricing. Introducing our Cyber Threat Security Company Users And Protection set of slides. The topics discussed in these slides are Pricing, Company, Users. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
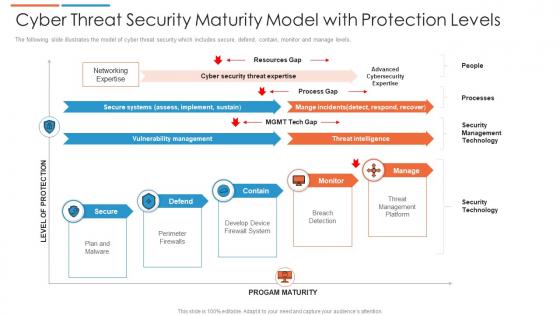 Cyber threat security maturity model with protection levels
Cyber threat security maturity model with protection levelsThe following slide illustrates the model of cyber threat security which includes secure, defend, contain, monitor and manage levels. Presenting our well structured Cyber Threat Security Maturity Model With Protection Levels. The topics discussed in this slide are Security Management Technology, Threat Management Platform, Threat Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber threat strategies for security protection
Cyber threat strategies for security protectionThis slide highlights the cyber threat strategies that include risk assessment, phishing program, software protocols and end point protection. Presenting our set of slides with Cyber Threat Strategies For Security Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Program, Software Protocols, End Point Protection.
-
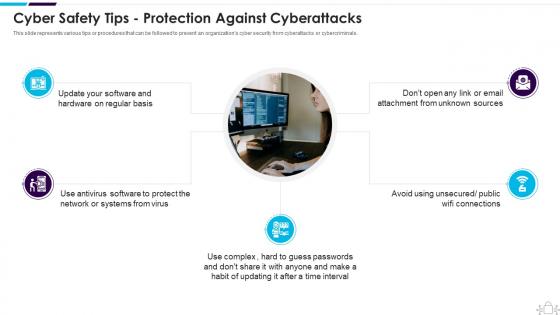 Information Technology Security Safety Tips Protection Against Cyberattacks
Information Technology Security Safety Tips Protection Against CyberattacksThis slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. Increase audience engagement and knowledge by dispensing information using Information Technology Security Safety Tips Protection Against Cyberattacks. This template helps you present information on five stages. You can also present information on Cyber Safety Tips Protection Against Cyberattacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
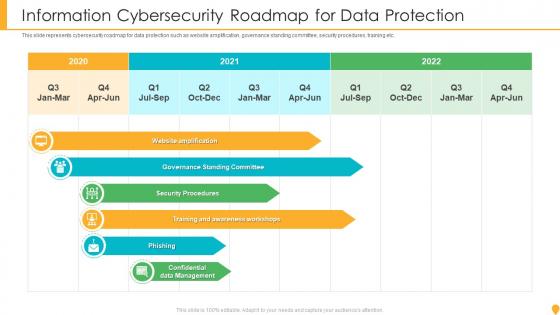 Information Cybersecurity Roadmap For Data Protection
Information Cybersecurity Roadmap For Data ProtectionThis slide represents cybersecurity roadmap for data protection such as website amplification, governance standing committee, security procedures, training etc. Introducing our premium set of slides with Information Cybersecurity Roadmap For Data Protection. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Website Amplification, Governance Standing Committee, Security Procedures, Phishing. So download instantly and tailor it with your information.
-
 Cybersecurity Framework With Protection Lock Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cybersecurity Framework With Protection Lock Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cybersecurity framework with protection lock colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cybersecurity Framework With Protection Lock Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cybersecurity Framework With Protection Lock Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cybersecurity framework with protection lock monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Cyber Protection Team Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Protection Team Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cyber protection team colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cyber Protection Team Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Protection Team Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cyber protection team monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
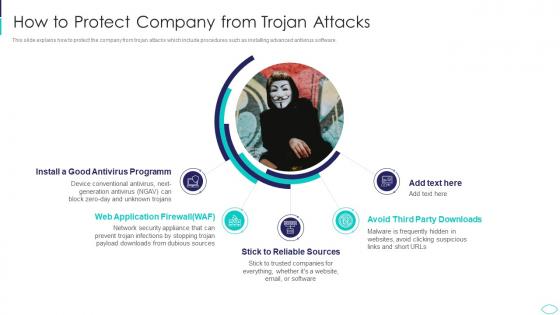 How To Protect Company From Trojan Attacks Cyber Terrorism Attacks
How To Protect Company From Trojan Attacks Cyber Terrorism AttacksThis slide explains how to protect the company from trojan attacks which include procedures such as installing advanced antivirus software. Increase audience engagement and knowledge by dispensing information using How To Protect Company From Trojan Attacks Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Antivirus Programm, Application Firewall, Reliable Sources, Avoid Third Party Downloads using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Techniques To Protect SCADA Systems From Cyber Terrorism Attacks
Techniques To Protect SCADA Systems From Cyber Terrorism AttacksThis slide depicts the techniques to protect SCADA from cyber attacks which include security training of employees, strict firewalls. Increase audience engagement and knowledge by dispensing information using Techniques To Protect SCADA Systems From Cyber Terrorism Attacks. This template helps you present information on six stages. You can also present information on Security Training, Access Controls, Strict Firewalls, Security Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Business Cyber Security Protection Icon
Business Cyber Security Protection IconIntroducing our Business Cyber Security Protection Icon set of slides. The topics discussed in these slides are Business Cyber Security, Protection Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security With Virus Protection Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Security With Virus Protection Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cyber security with virus protection colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cyber Security With Virus Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Security With Virus Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cyber security with virus protection monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 3 Step Cyber Security Plan For Data Protection
3 Step Cyber Security Plan For Data ProtectionThis slide signifies the three stage cyber security program to improve data protection. It covers information about steps like prevention, response and remediation. Presenting our set of slides with 3 Step Cyber Security Plan For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prevention, Response, Remediation.
-
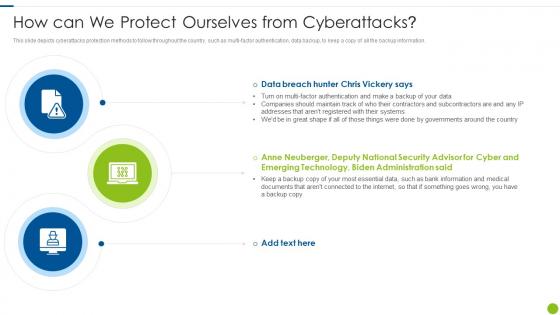 Cyber Attacks On Ukraine How Can We Protect Ourselves From Cyberattacks
Cyber Attacks On Ukraine How Can We Protect Ourselves From CyberattacksThis slide depicts cyberattacks protection methods to follow throughout the country, such as multi factor authentication, data backup, to keep a copy of all the backup information. Introducing Cyber Attacks On Ukraine How Can We Protect Ourselves From Cyberattacks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on How Can We Protect Ourselves From Cyberattacks, using this template. Grab it now to reap its full benefits.
-
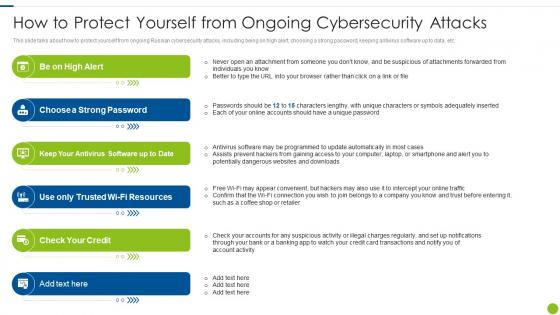 Cyber Attacks On Ukraine How To Protect Yourself From Ongoing Cybersecurity
Cyber Attacks On Ukraine How To Protect Yourself From Ongoing CybersecurityThis slide talks about how to protect yourself from ongoing Russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Increase audience engagement and knowledge by dispensing information using Cyber Attacks On Ukraine How To Protect Yourself From Ongoing Cybersecurity. This template helps you present information on six stages. You can also present information on Suspicious, Individuals, Adequately, Programmed using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security Safety Tips Protection Against Cyberattacks
Information Security Safety Tips Protection Against CyberattacksThis slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. Introducing Information Security Safety Tips Protection Against Cyberattacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Safety Tips Protection Against Cyberattacks, using this template. Grab it now to reap its full benefits.
-
 Identity Protection Cyber Safety Ppt Powerpoint Presentation Gallery Graphic Tips Cpb
Identity Protection Cyber Safety Ppt Powerpoint Presentation Gallery Graphic Tips CpbPresenting Identity Protection Cyber Safety Ppt Powerpoint Presentation Gallery Graphic Tips Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Identity Protection Cyber Safety. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Global Cyber Security And Protection Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Global Cyber Security And Protection Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Global cyber security and protection colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Global Cyber Security And Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Global Cyber Security And Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Global cyber security and protection monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 How can we protect ourselves from cyberattacks ukraine and russia cyber warfare it
How can we protect ourselves from cyberattacks ukraine and russia cyber warfare itThis slide depicts cyberattacks protection methods to follow throughout the country, such as multi factor authentication, data backup, to keep a copy of all the backup information. Increase audience engagement and knowledge by dispensing information using How Can We Protect Ourselves From Cyberattacks Ukraine And Russia Cyber Warfare It. This template helps you present information on three stages. You can also present information on How CAN We Protect Ourselves FROM Cyberattacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ukraine and russia cyber warfare it how to protect yourself from ongoing cybersecurity attacks
Ukraine and russia cyber warfare it how to protect yourself from ongoing cybersecurity attacksThis slide talks about how to protect yourself from ongoing Russian cybersecurity attacks, including being on high alert, choosing a strong password, keeping antivirus software up to data, etc. Introducing Ukraine And Russia Cyber Warfare It How To Protect Yourself From Ongoing Cybersecurity Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Resources, Antivirus, Software, using this template. Grab it now to reap its full benefits.
-
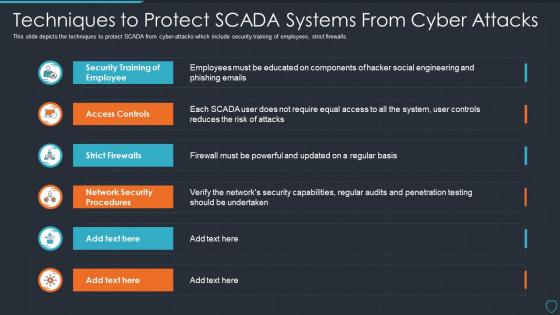 Cyberterrorism it techniques to protect scada systems from cyber attacks
Cyberterrorism it techniques to protect scada systems from cyber attacksThis slide depicts the techniques to protect SCADA from cyber-attacks which include security training of employees, strict firewalls. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Techniques To Protect SCADA Systems From Cyber Attacks. Dispense information and present a thorough explanation of Security Training, Employee, Access Controls, Strict Firewalls, Network Security Procedures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
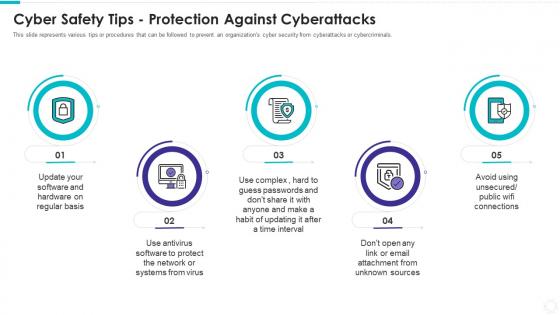 Electronic information security cyber safety tips protection against cyberattacks
Electronic information security cyber safety tips protection against cyberattacksThis slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. Introducing Electronic Information Security Cyber Safety Tips Protection Against Cyberattacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Regular Basis, Protect Network, Systems Virustime Interval, Email Attachment Unknown Sources, using this template. Grab it now to reap its full benefits.
-
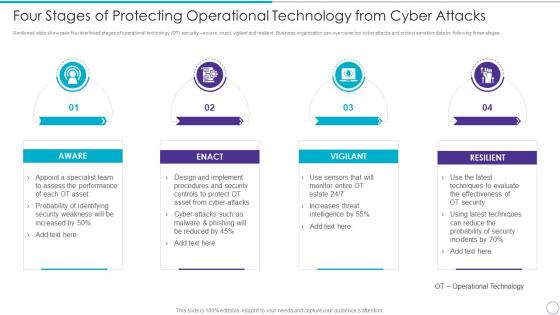 Four Stages Of Protecting Operational Technology From Cyber Attacks
Four Stages Of Protecting Operational Technology From Cyber AttacksMentioned slide showcase four interlinked stages of operational technology OT security aware, enact, vigilant and resilient. Business organization can overcome top cyber attacks and protect sensitive data by following these stages. Increase audience engagement and knowledge by dispensing information using four Stages Of Protecting Operational Technology From Cyber Attacks. This template helps you present information on four stages. You can also present information on Aware, Enact, Vigilant, Resilient using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.




