Powerpoint Templates and Google slides for Stages Of Cyber Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
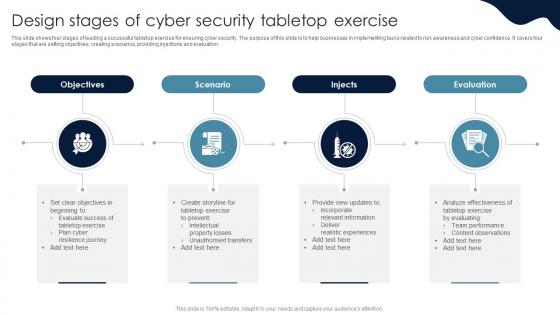 Design Stages Of Cyber Security Tabletop Exercise
Design Stages Of Cyber Security Tabletop ExerciseThis slide shows four stages of leading a successful tabletop exercise for ensuring cyber security. The purpose of this slide is to help businesses in implementing tasks related to risk awareness and cyber confidence. It covers four stages that are setting objectives, creating scenarios, providing injections and evaluation. Introducing our premium set of slides with Design Stages Of Cyber Security Tabletop Exercise. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Provide New Updates, Analyze Effectiveness, Team Performance. So download instantly and tailor it with your information.
-
 Stages Of Cyber Security And Compliance Automation
Stages Of Cyber Security And Compliance AutomationThis slide represents stages of cyber security and compliance automation which assists in cyber risk and policy adherence. It includes stages of cyber security and compliance automation such as initial, developing, define, etc. Presenting our set of slides with name Stages Of Cyber Security And Compliance Automation. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Stages Of Cyber Security, Compliance Automation, Developing, Risk And Policy Adherence.
-
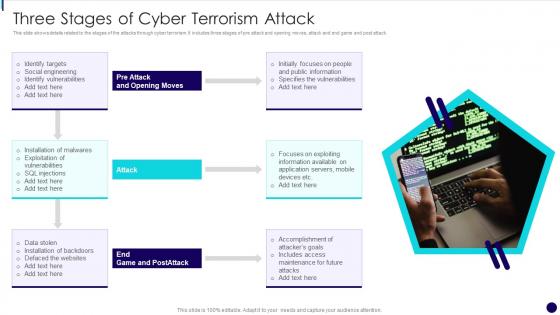 Three Stages Of Cyber Terrorism Attack
Three Stages Of Cyber Terrorism AttackThis slide shows details related to the stages of the attacks through cyber terrorism. It includes three stages of pre attack and opening moves, attack and end game and post attack. Presenting our set of slides with name Three Stages Of Cyber Terrorism Attack. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Social Engineering, Identify Vulnerabilities, Exploitation Of Vulnerabilities, Data Stolen.
-
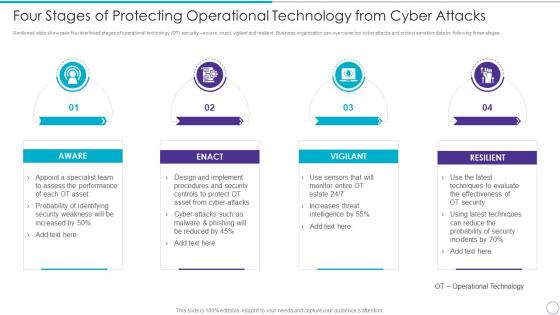 Four Stages Of Protecting Operational Technology From Cyber Attacks
Four Stages Of Protecting Operational Technology From Cyber AttacksMentioned slide showcase four interlinked stages of operational technology OT security aware, enact, vigilant and resilient. Business organization can overcome top cyber attacks and protect sensitive data by following these stages. Increase audience engagement and knowledge by dispensing information using four Stages Of Protecting Operational Technology From Cyber Attacks. This template helps you present information on four stages. You can also present information on Aware, Enact, Vigilant, Resilient using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Stages Of Botnet Malware Cybercriminal Attacks
Stages Of Botnet Malware Cybercriminal AttacksThis slide illustrates how to create a bot and orchestrating a botnet attack. It includes stages such as expose, infect and grow, activate, etc. Introducing our premium set of slides with Stages Of Botnet Malware Cybercriminal Attacks. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Expose, Infect And Grow, Activate. So download instantly and tailor it with your information.
-
 6 Stage Process For Implementation Of Risk Management In Cyber Security Project
6 Stage Process For Implementation Of Risk Management In Cyber Security ProjectThis This slide signifies the six step process for successful implementation of risk assessment in cyber security project. It covers information about stages like identify, analyse, evaluate, prioritize, treat and monitor. Presenting our set of slides with name 6 Stage Process For Implementation Of Risk Management In Cyber Security Project. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Analyse, Evaluate, Prioritize, Treat.
-
 Four Stage Cyclic Process Of Building Cyber Security
Four Stage Cyclic Process Of Building Cyber SecurityThis slide showcases four cyclic stages of cyber security process of creating and maintaining a secure . It includes security assess , detecting , identifying , recording attacks , bringing safety measures , strengthening protection etc. Introducing our premium set of slides with Four Stage Cyclic Process Of Building Cyber Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Safe State, Strengthen Protection, Remediation. So download instantly and tailor it with your information.
-
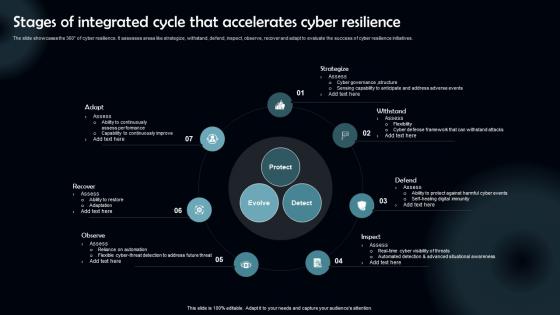 Stages Of Integrated Cycle That Accelerates Cyber Resilience
Stages Of Integrated Cycle That Accelerates Cyber ResilienceThe slide showcases the 360 of cyber resilience. It assesses areas like strategize, withstand, defend, inspect, observe, recover and adapt to evaluate the success of cyber resilience initiatives. Introducing our premium set of slides with Stages Of Integrated Cycle That Accelerates Cyber Resilience Ellicudate the Seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strategize, Withstand, Defend. So download instantly and tailor it with your information.
-
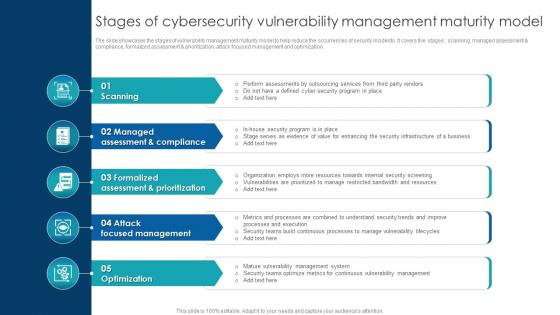 Stages Of Cybersecurity Vulnerability Management Maturity Model
Stages Of Cybersecurity Vulnerability Management Maturity ModelThe slide showcases the stages of vulnerability management maturity model to help reduce the occurrences of security incidents. It covers five stages scanning, managed assessment compliance, formalized assessment prioritization, attack focused management and optimization.Presenting our set of slides with Stages Of Cybersecurity Vulnerability Management Maturity Model. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Initiatives, Assess Current Inventory, Record Desired Security.
-
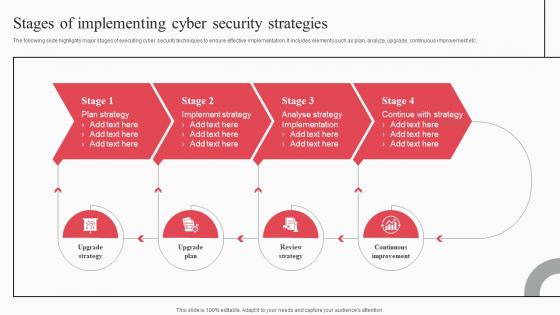 Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation
Stages Of Implementing Cyber Security Strategies Cyber Attack Risks MitigationThe following slide highlights major stages of executing cyber security techniques to ensure effective implementation. It includes elements such as plan, analyze, upgrade, continuous improvement etc. Increase audience engagement and knowledge by dispensing information using Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Plan Strategy, Implement Strategy, Analyse Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
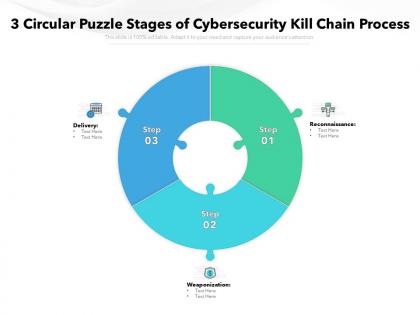 3 circular puzzle stages of cybersecurity kill chain process
3 circular puzzle stages of cybersecurity kill chain processPresenting this set of slides with name 3 Circular Puzzle Stages Of Cybersecurity Kill Chain Process. This is a three stage process. The stages in this process are Delivery, Reconnaissance, Weaponization. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 4 circular puzzle stages of cybersecurity kill chain process
4 circular puzzle stages of cybersecurity kill chain processPresenting this set of slides with name 4 Circular Puzzle Stages Of Cybersecurity Kill Chain Process. This is a four stage process. The stages in this process are Delivery, Reconnaissance, Weaponization. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 5 circular puzzle stages of cybersecurity kill chain process
5 circular puzzle stages of cybersecurity kill chain processPresenting this set of slides with name 5 Circular Puzzle Stages Of Cybersecurity Kill Chain Process. This is a five stage process. The stages in this process are Delivery, Reconnaissance, Weaponization. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
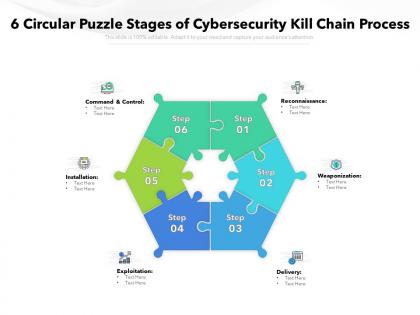 6 circular puzzle stages of cybersecurity kill chain process
6 circular puzzle stages of cybersecurity kill chain processPresenting this set of slides with name 6 Circular Puzzle Stages Of Cybersecurity Kill Chain Process. This is a six stage process. The stages in this process are Delivery, Reconnaissance, Weaponization. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
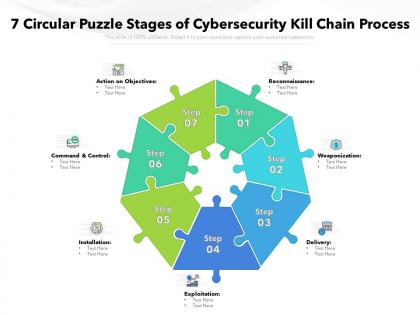 7 circular puzzle stages of cybersecurity kill chain process
7 circular puzzle stages of cybersecurity kill chain processPresenting this set of slides with name 7 Circular Puzzle Stages Of Cybersecurity Kill Chain Process. This is a seven stage process. The stages in this process are Delivery, Reconnaissance, Weaponization. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 8 circular puzzle stages of cybersecurity kill chain process
8 circular puzzle stages of cybersecurity kill chain processPresenting this set of slides with name 8 Circular Puzzle Stages Of Cybersecurity Kill Chain Process. This is a eight stage process. The stages in this process are Delivery, Reconnaissance, Weaponization. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 9 circular puzzle stages of cybersecurity kill chain process
9 circular puzzle stages of cybersecurity kill chain processPresenting this set of slides with name 9 Circular Puzzle Stages Of Cybersecurity Kill Chain Process. This is a nine stage process. The stages in this process are Delivery, Reconnaissance, Weaponization. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Free four stages funnel visual of cyber deception infographic template
Free four stages funnel visual of cyber deception infographic templateThis is our Free Four Stages Funnel Visual Of Cyber Deception Infographic Template designed in PowerPoint, however, you can also access it in Google Slides. It comes in two aspect ratios standard and widescreen, with fully editable visual content.

