Powerpoint Templates and Google slides for Vulnerabilities Mitigate
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data Breach Prevention And Mitigation Data Breach Response Plan Fix Vulnerabilities
Data Breach Prevention And Mitigation Data Breach Response Plan Fix VulnerabilitiesThis slide represents actions to be taken, the responsible team, the deadline, and tasks for fixing vulnerabilities after a data breach. The action items include assessing Service Providers access privileges, reviewing network segmentation, monitoring, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Data Breach Response Plan Fix Vulnerabilities. Dispense information and present a thorough explanation of Collaborate With Forensics Experts, Review Network Segmentation, Communicate Transparently using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats
Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts some major assets that are more prone to cyber attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Sales Record, Customer Database, Product Database This template is free to edit as deemed fit for your organization. Therefore download it now.
-
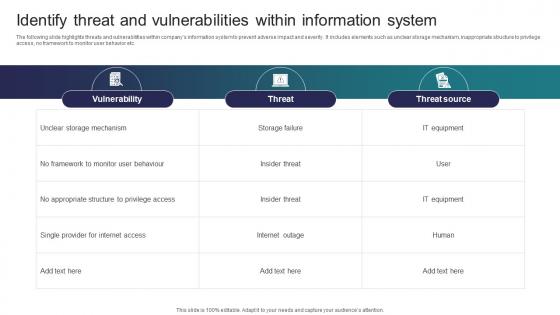 Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security
Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber SecurityThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security Dispense information and present a thorough explanation of Vulnerability, Threat, Threat Source using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Patch Management Icon To Mitigate Software Vulnerability
Patch Management Icon To Mitigate Software VulnerabilityPresenting our set of slides with name Patch Management Icon To Mitigate Software Vulnerability. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Patch Management Icon, Mitigate Software Vulnerability.
-
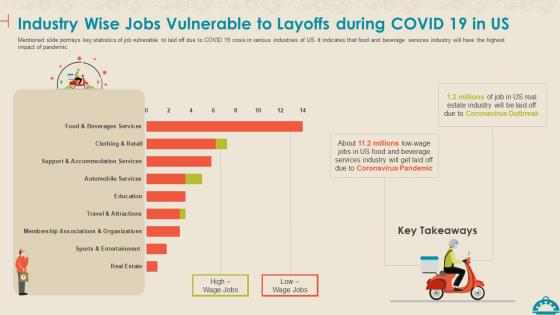 Coronavirus Mitigation Strategies Food Service Industry Jobs Vulnerable Layoffs During Covid 19
Coronavirus Mitigation Strategies Food Service Industry Jobs Vulnerable Layoffs During Covid 19Mentioned slide portrays key statistics of job vulnerable to laid off due to COVID 19 crisis in various industries of US. It indicates that food and beverage services industry will have the highest impact of pandemic. Present the topic in a bit more detail with this Coronavirus Mitigation Strategies Food Service Industry Jobs Vulnerable Layoffs During Covid 19. Use it as a tool for discussion and navigation on Industry Wise Jobs Vulnerable To Layoffs During COVID 19 In US. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat Vulnerability And Risk Mitigation Table
Threat Vulnerability And Risk Mitigation TableThis slide covers the risks assessment of companys information security to improve the clients safety and anticipate data vulnerability. It also includes threats, risks, assets and consequences with solutions. Introducing our Threat Vulnerability And Risk Mitigation Table set of slides. The topics discussed in these slides are Threat, Vulnerability, Risk, Solution. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Food Fraud Mitigation Plan Development To Remove Vulnerability
Food Fraud Mitigation Plan Development To Remove VulnerabilityThis slide provide information about procedure to formulate food fraud mitigation plan to remove vulnerability. It includes elements such as pre-screening, vulnerability assessment, impact assessment, overall risk assessment etc. Presenting our set of slides with Food Fraud Mitigation Plan Development To Remove Vulnerability. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Pre Screening, Vulnerability Assessment, Impact Assessment, Overall Risk Assessment.
-
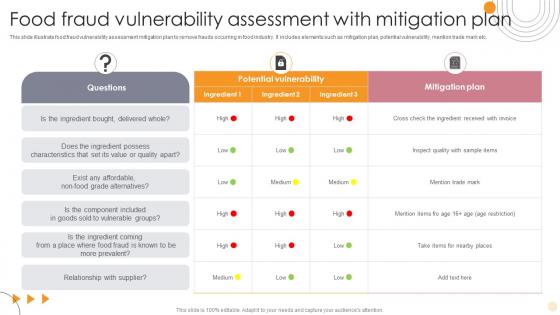 Food Fraud Vulnerability Assessment With Mitigation Plan
Food Fraud Vulnerability Assessment With Mitigation PlanThis slide illustrate food fraud vulnerability assessment mitigation plan to remove frauds occurring in food industry. It includes elements such as mitigation plan, potential vulnerability, mention trade mark etc. Introducing our Food Fraud Vulnerability Assessment With Mitigation Plan set of slides. The topics discussed in these slides are Potential Vulnerability, Mitigation Plan, Ingredient Bought. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
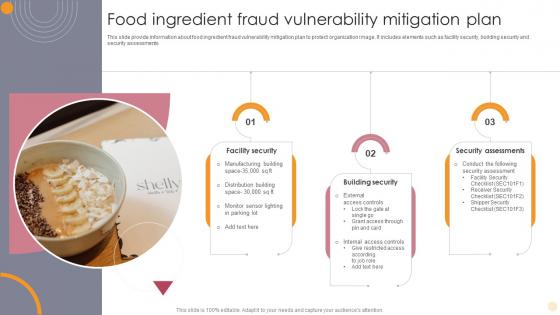 Food Ingredient Fraud Vulnerability Mitigation Plan
Food Ingredient Fraud Vulnerability Mitigation PlanThis slide provide information about food ingredient fraud vulnerability mitigation plan to protect organization image. It includes elements such as facility security, building security and security assessments. Presenting our well structured Food Ingredient Fraud Vulnerability Mitigation Plan. The topics discussed in this slide are Facility Security, Building Security, Security Assessments. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
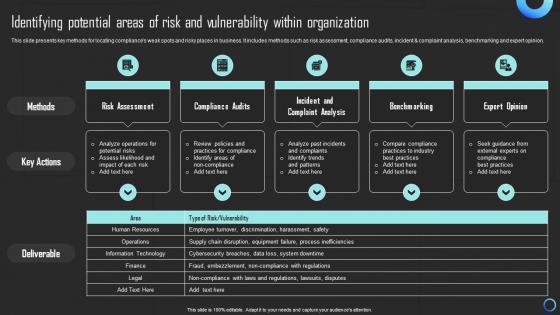 Identifying Potential Areas Of Risk And Vulnerability Mitigating Risks And Building Trust Strategy SS
Identifying Potential Areas Of Risk And Vulnerability Mitigating Risks And Building Trust Strategy SSThis slide presents key methods for locating compliances weak spots and risky places in business. It includes methods such as risk assessment, compliance audits, incident and complaint analysis, benchmarking and expert opinion. Deliver an outstanding presentation on the topic using this Identifying Potential Areas Of Risk And Vulnerability Mitigating Risks And Building Trust Strategy SS. Dispense information and present a thorough explanation of Risk Assessment, Compliance Audits, Benchmarking using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability management identify analyze mitigate manage
Vulnerability management identify analyze mitigate managePresenting this set of slides with name - Vulnerability Management Identify Analyze Mitigate Manage. This is a four stage process. The stages in this process are Vulnerability Management, Risk Management, Vulnerability Planning.

