Powerpoint Templates and Google slides for Access And Availability
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
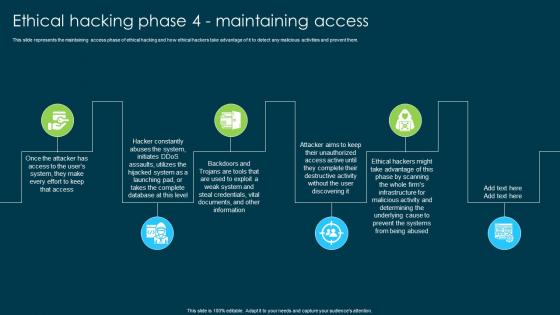 Ethical Hacking And Network Security Ethical Hacking Phase 4 Maintaining Access
Ethical Hacking And Network Security Ethical Hacking Phase 4 Maintaining AccessThis slide represents the maintaining access phase of ethical hacking and how ethical hackers take advantage of it to detect any malicious activities and prevent them. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Ethical Hacking Phase 4 Maintaining Access. This template helps you present information on six stages. You can also present information on Whole Firms Infrastructure, Malicious Activity, Prevent The Systems, Ethical Hacking using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mandatory Access Control In Powerpoint And Google Slides Cpb
Mandatory Access Control In Powerpoint And Google Slides CpbPresenting our Mandatory Access Control In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Mandatory Access Control This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
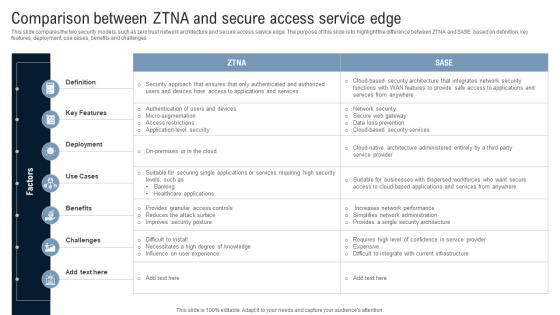 Comparison Between ZTNA And Secure Access Service Edge Identity Defined Networking
Comparison Between ZTNA And Secure Access Service Edge Identity Defined NetworkingThis slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges. Present the topic in a bit more detail with this Comparison Between ZTNA And Secure Access Service Edge Identity Defined Networking Use it as a tool for discussion and navigation on Key Features, Deployment, Benefits, Challenges This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Access Control Password Management Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Access Control Password Management Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a great visual aid for representing folder password protection. It is a modern and vibrant design that will add a professional touch to any presentation. The icon is easy to use and can be used to quickly and effectively communicate the importance of password security.
-
 Access Control Password Management Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Access Control Password Management Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Folder Password is a simple yet effective way to protect your confidential data. It is easy to use and provides a secure encryption for your files. It is an ideal solution for those who want to keep their documents safe and secure.
-
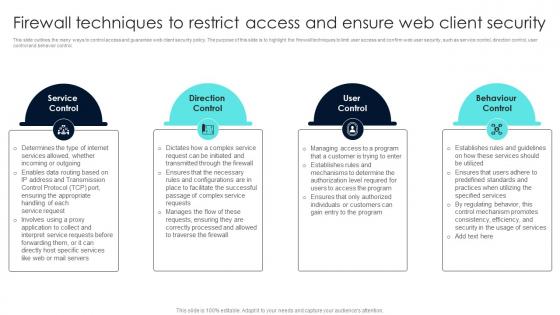 Firewall Network Security Firewall Techniques To Restrict Access And Ensure Web Client Security
Firewall Network Security Firewall Techniques To Restrict Access And Ensure Web Client SecurityThis slide outlines the many ways to control access and guarantee web client security policy. The purpose of this slide is to highlight the firewall techniques to limit user access and confirm web user security, such as service control, direction control, user control and behavior control. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Firewall Techniques To Restrict Access And Ensure Web Client Security This template helps you present information on Four stages. You can also present information on Market By Deployment, Market By Solution using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker And Encryption Next Generation CASB
Cloud Access Security Broker And Encryption Next Generation CASBThis slide describes the improved encryption with CASB version 2.0. The purpose of this slide is to showcase the various encryption features of cloud access security broker version 2.0, including security that follows the data, content access that can be revoked at any time, and multi-platform compatibility. Present the topic in a bit more detail with this Cloud Access Security Broker And Encryption Next Generation CASB Use it as a tool for discussion and navigation on Security That Tracks Data, Terminated Moment, Content Access This template is free to edit as deemed fit for your organization. Therefore download it now.
-
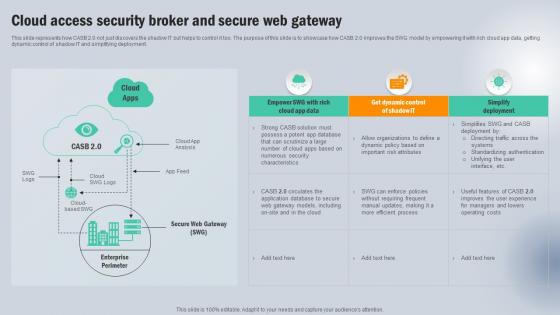 Cloud Access Security Broker And Secure Web Gateway Next Generation CASB
Cloud Access Security Broker And Secure Web Gateway Next Generation CASBThis slide represents how CASB 2.0 not just discovers the shadow IT but helps to control it too. The purpose of this slide is to showcase how CASB 2.0 improves the SWG model by empowering it with rich cloud app data, getting dynamic control of shadow IT and simplifying deployment. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker And Secure Web Gateway Next Generation CASB Dispense information and present a thorough explanation of Cloud App Data, Get Dynamic Control, Simplify Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
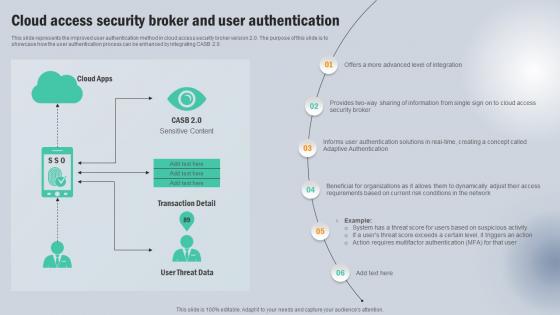 Cloud Access Security Broker And User Authentication Next Generation CASB
Cloud Access Security Broker And User Authentication Next Generation CASBThis slide represents the improved user authentication method in cloud access security broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Present the topic in a bit more detail with this Cloud Access Security Broker And User Authentication Next Generation CASB Use it as a tool for discussion and navigation on Cloud Apps, Transaction Detail, User Threat Data This template is free to edit as deemed fit for your organization. Therefore download it now.
-
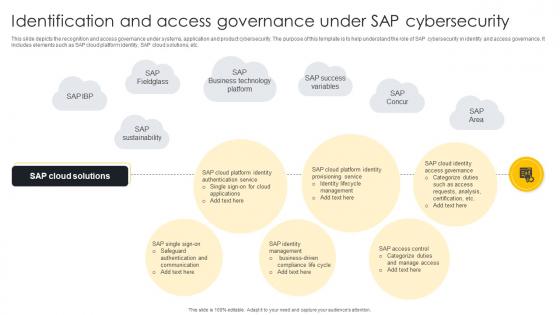 Identification And Access Governance Under SAP Cybersecurity
Identification And Access Governance Under SAP CybersecurityThis slide depicts the recognition and access governance under systems, application and product cybersecurity. The purpose of this template is to help understand the role of SAP cybersecurity in identity and access governance. It includes elements such as SAP cloud platform identity, SAP cloud solutions, etc. Introducing our Identification And Access Governance Under SAP Cybersecurity set of slides. The topics discussed in these slides are SAP Fieldglass, Identity Lifecycle Management, SAP Success Variables. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Access Control Data Privacy Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Access Control Data Privacy Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon features a visual representation of data classification for information security. It is designed to enhance presentations and documents related to data protection and security measures. The icon is easy to use and adds a professional touch to any visual aid or document.
-
 Access Control Data Privacy Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Access Control Data Privacy Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is perfect for presentations on data classification in information security. With a sleek and simple design, it effectively conveys the importance of organizing and protecting sensitive information. Use it to enhance your slides and educate your audience on the crucial topic of data classification.
-
 Access Entrance Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Access Entrance Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon features a keyhole design, perfect for adding a touch of creativity to your presentations. The vibrant colors and detailed design make it eye-catching and easy to spot. Use it to represent security, access, or any other relevant concept in your slides.
-
 Access Entrance Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Access Entrance Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon on door Key Hole is the perfect addition to any presentation. Its sleek design and simple yet eye-catching image will make your presentation stand out. With its high-quality resolution, it is sure to impress your audience and add a professional touch to your slides.
-
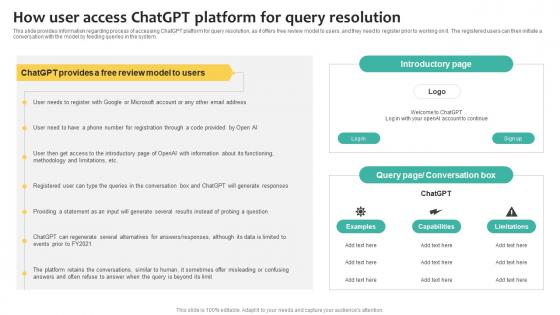 How User Access Chatgpt what Is Chatgpt And GPT 4 Everything You Need Chatgpt SS V
How User Access Chatgpt what Is Chatgpt And GPT 4 Everything You Need Chatgpt SS VThis slide provides information regarding process of accessing ChatGPT platform for query resolution, as it offers free review model to users, and they need to register prior to working on it. The registered users can then initiate a conversation with the model by feeding queries in the system. Present the topic in a bit more detail with this How User Access Chatgpt what Is Chatgpt And GPT 4 Everything You Need Chatgpt SS V. Use it as a tool for discussion and navigation on Review Model, Introductory Page, Conversation Box. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IAM Process For Effective Access About Directory Services And Aggregation Of IAM
IAM Process For Effective Access About Directory Services And Aggregation Of IAMThis slide discusses the directory services and aggregation of identity management. The purpose of this slide is to explain the identity stores stored in organizational stores and aggregation that involves discovering, selecting, and determining authority sources. Present the topic in a bit more detail with this IAM Process For Effective Access About Directory Services And Aggregation Of IAM. Use it as a tool for discussion and navigation on Integration And Synchronization Techniques, Determining Authoritative Sources, Aggregation And Synchronization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
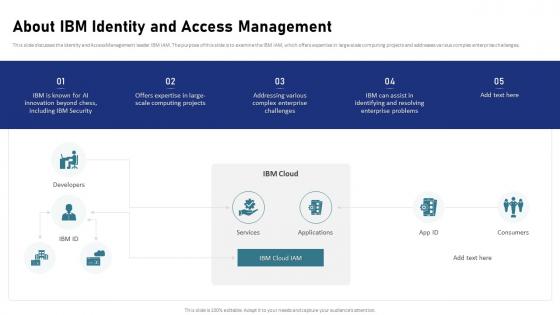 IAM Process For Effective Access About IBM Identity And Access Management
IAM Process For Effective Access About IBM Identity And Access ManagementThis slide discusses the Identity and Access Management leader IBM IAM. The purpose of this slide is to examine the IBM IAM, which offers expertise in large-scale computing projects and addresses various complex enterprise challenges. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access About IBM Identity And Access Management. Dispense information and present a thorough explanation of Identity And Access Management, Complex Enterprise Challenges, Large Scale Computing Projects using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
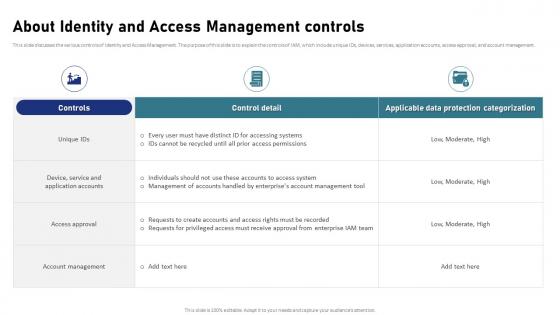 IAM Process For Effective Access About Identity And Access Management Controls
IAM Process For Effective Access About Identity And Access Management ControlsThis slide discusses the various controls of Identity and Access Management. The purpose of this slide is to explain the controls of IAM, which include unique IDs, devices, services, application accounts, access approval, and account management. Present the topic in a bit more detail with this IAM Process For Effective Access About Identity And Access Management Controls. Use it as a tool for discussion and navigation on Service And Application Accounts, Account Management, Applicable Data Protection Categorization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
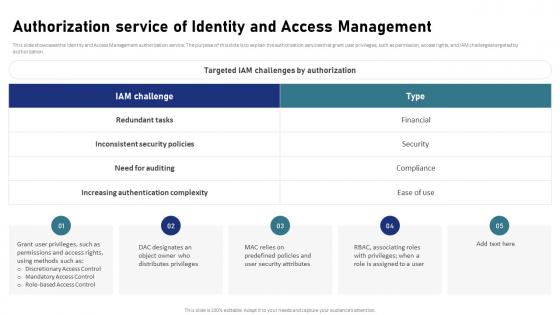 IAM Process For Effective Access Authorization Service Of Identity And Access Management
IAM Process For Effective Access Authorization Service Of Identity And Access ManagementThis slide showcases the Identity and Access Management authorization service. The purpose of this slide is to explain the authorization services that grant user privileges, such as permission, access rights, and IAM challenges targeted by authorization. Introducing IAM Process For Effective Access Authorization Service Of Identity And Access Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Discretionary Access Control, Mandatory Access Control, Role Based Access Control, using this template. Grab it now to reap its full benefits.
-
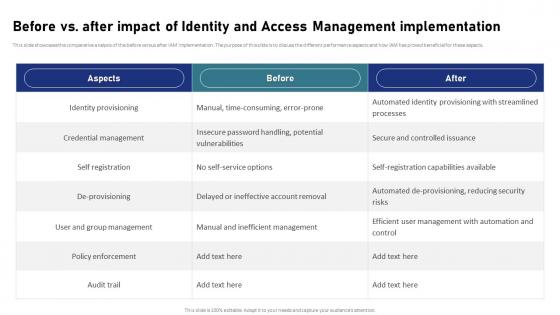 IAM Process For Effective Access Before Vs After Impact Of Identity And Access Management Implementation
IAM Process For Effective Access Before Vs After Impact Of Identity And Access Management ImplementationThis slide showcases the comparative analysis of the before versus after IAM implementation. The purpose of this slide is to discuss the different performance aspects and how IAM has proved beneficial for these aspects. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access Before Vs After Impact Of Identity And Access Management Implementation. Dispense information and present a thorough explanation of Credential Management, Identity Provisioning, Policy Enforcement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
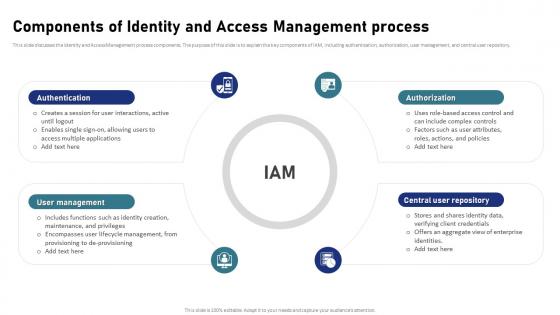 IAM Process For Effective Access Components Of Identity And Access Management Process
IAM Process For Effective Access Components Of Identity And Access Management ProcessThis slide discusses the Identity and Access Management process components. The purpose of this slide is to explain the key components of IAM, including authentication, authorization, user management, and central user repository. Increase audience engagement and knowledge by dispensing information using IAM Process For Effective Access Components Of Identity And Access Management Process. This template helps you present information on four stages. You can also present information on Authentication, User Management, Central User Repository, Authorization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 IAM Process For Effective Access Covid 19 Impact On Identity And Access Management
IAM Process For Effective Access Covid 19 Impact On Identity And Access ManagementThis slide highlights the various impacts of the COVID-19 pandemic on Identity and Access Management. The purpose of this slide is to discuss the effects of the pandemic that disrupted global cyber security, causing a surge in cyber attacks. Introducing IAM Process For Effective Access Covid 19 Impact On Identity And Access Management to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Global Cyber Security, Flexibility And Cost Effectiveness, Organizations Susceptible, Cloud Environments, using this template. Grab it now to reap its full benefits.
-
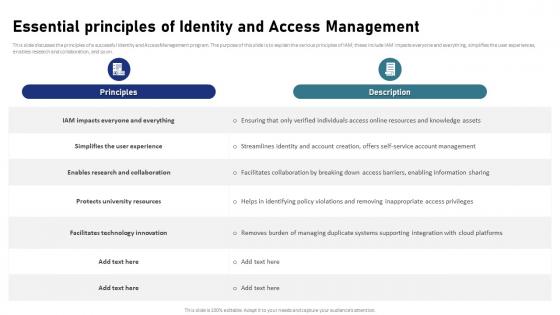 IAM Process For Effective Access Essential Principles Of Identity And Access Management
IAM Process For Effective Access Essential Principles Of Identity And Access ManagementThis slide discusses the principles of a successful Identity and Access Management program. The purpose of this slide is to explain the various principles of IAM these include IAM impacts everyone and everything, simplifies the user experiences, enables research and collaboration, and so on. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access Essential Principles Of Identity And Access Management. Dispense information and present a thorough explanation of Simplifies The User Experience, Facilitates Technology Innovation, Protects University Resources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
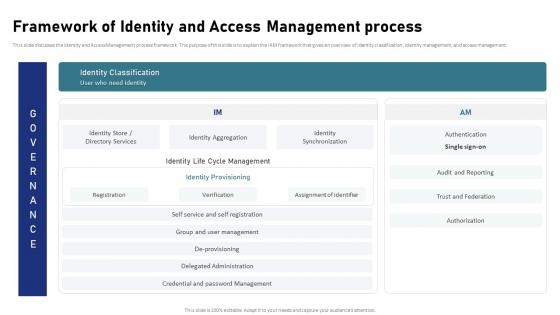 IAM Process For Effective Access Framework Of Identity And Access Management Process
IAM Process For Effective Access Framework Of Identity And Access Management ProcessThis slide discusses the Identity and Access Management process framework. The purpose of this slide is to explain the IAM framework that gives an overview of identity classification, identity management, and access management. Present the topic in a bit more detail with this IAM Process For Effective Access Framework Of Identity And Access Management Process. Use it as a tool for discussion and navigation on Audit And Reporting, Trust And Federation, Access Management Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
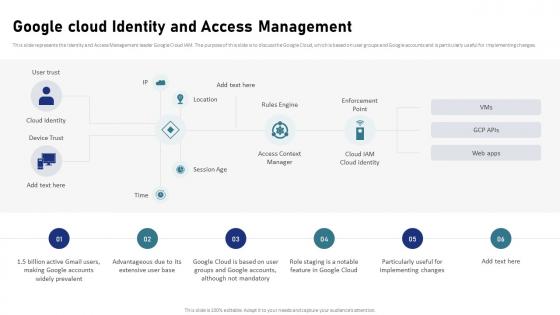 IAM Process For Effective Access Google Cloud Identity And Access Management
IAM Process For Effective Access Google Cloud Identity And Access ManagementThis slide represents the Identity and Access Management leader Google Cloud IAM. The purpose of this slide is to discuss the Google Cloud, which is based on user groups and Google accounts and is particularly useful for implementing changes. Increase audience engagement and knowledge by dispensing information using IAM Process For Effective Access Google Cloud Identity And Access Management. This template helps you present information on six stages. You can also present information on Google Cloud Identity, Access Management, Google Accounts Widely Prevalent using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
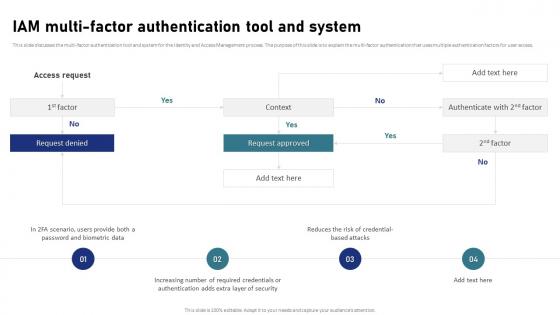 IAM Process For Effective Access IAM Multi Factor Authentication Tool And System
IAM Process For Effective Access IAM Multi Factor Authentication Tool And SystemThis slide discusses the multi-factor authentication tool and system for the Identity and Access Management process. The purpose of this slide is to explain the multi-factor authentication that uses multiple authentication factors for user access. Introducing IAM Process For Effective Access IAM Multi Factor Authentication Tool And System to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Multi Factor Authentication Tool, Access Management Process, Risk Of Credential Based Attacks, using this template. Grab it now to reap its full benefits.
-
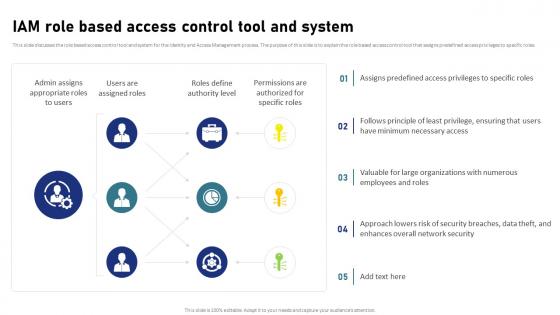 IAM Process For Effective Access IAM Role Based Access Control Tool And System
IAM Process For Effective Access IAM Role Based Access Control Tool And SystemThis slide discusses the role based access control tool and system for the Identity and Access Management process. The purpose of this slide is to explain the role based access control tool that assigns predefined access privileges to specific roles. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access IAM Role Based Access Control Tool And System. Dispense information and present a thorough explanation of Network Security, Numerous Employees And Roles, Assigns Predefined Access Privileges using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
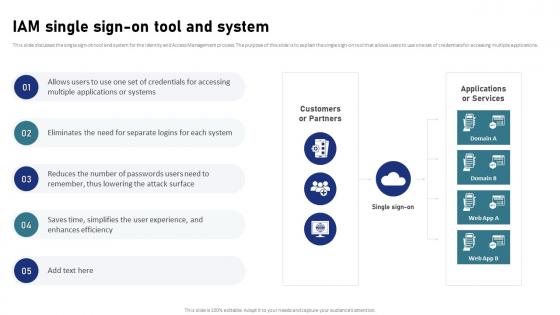 IAM Process For Effective Access IAM Single Sign On Tool And System
IAM Process For Effective Access IAM Single Sign On Tool And SystemThis slide discusses the single sign-on tool and system for the Identity and Access Management process. The purpose of this slide is to explain the single sign-on tool that allows users to use one set of credentials for accessing multiple applications. Present the topic in a bit more detail with this IAM Process For Effective Access IAM Single Sign On Tool And System. Use it as a tool for discussion and navigation on Access Management Process, Accessing Multiple Applications, User Experience. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
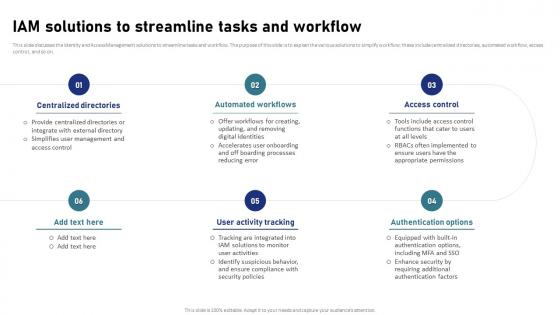 IAM Process For Effective Access IAM Solutions To Streamline Tasks And Workflow
IAM Process For Effective Access IAM Solutions To Streamline Tasks And WorkflowThis slide discusses the Identity and Access Management solutions to streamline tasks and workflow. The purpose of this slide is to explain the various solutions to simplify workflow these include centralized directories, automated workflow, access control, and so on. Increase audience engagement and knowledge by dispensing information using IAM Process For Effective Access IAM Solutions To Streamline Tasks And Workflow. This template helps you present information on six stages. You can also present information on Centralized Directories, Automated Workflows, Authentication Options using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
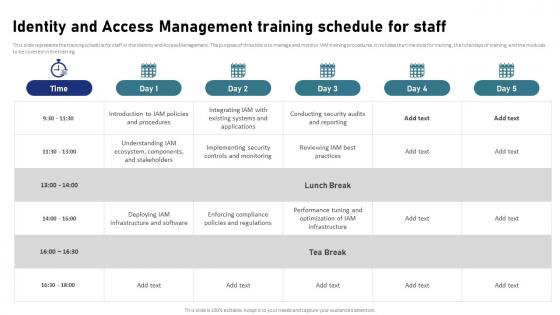 IAM Process For Effective Access Identity And Access Management Training Schedule For Staff
IAM Process For Effective Access Identity And Access Management Training Schedule For StaffThis slide represents the training schedule for staff in the Identity and Access Management. The purpose of this slide is to manage and monitor IAM training procedures. It includes the time slots for training, the total days of training, and the modules to be covered in the training. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access Identity And Access Management Training Schedule For Staff. Dispense information and present a thorough explanation of Identity And Access Management, Time Slots For Training, Enforcing Compliance Policies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
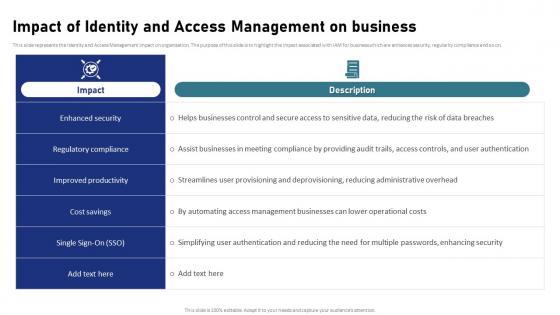 IAM Process For Effective Access Impact Of Identity And Access Management On Business
IAM Process For Effective Access Impact Of Identity And Access Management On BusinessThis slide represents the Identity and Access Management impact on organization. The purpose of this slide is to highlight the impact associated with IAM for business which are enhances security, regularity compliance and so on. Present the topic in a bit more detail with this IAM Process For Effective Access Impact Of Identity And Access Management On Business. Use it as a tool for discussion and navigation on Regulatory Compliance, Improved Productivity, Enhanced Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IAM Process For Effective Access Primary Identity And Access Management Software
IAM Process For Effective Access Primary Identity And Access Management SoftwareThis slide discusses the primary software used in the Identity and Access Management process. The purpose of this slide is to explain the software of IAM, which are Okta, JumpCloud, Rippling, Auth0, and OneLogin. Deliver an outstanding presentation on the topic using this IAM Process For Effective Access Primary Identity And Access Management Software. Dispense information and present a thorough explanation of Customizable Regional Settings, Access Management Software, Flawless Integration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
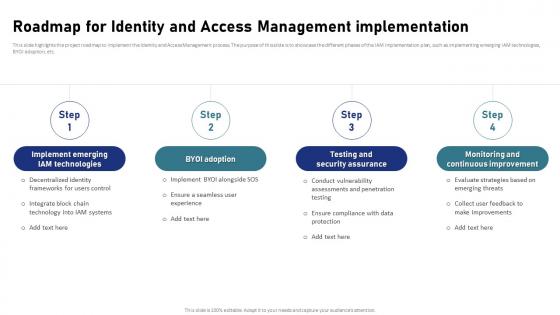 IAM Process For Effective Access Roadmap For Identity And Access Management Implementation
IAM Process For Effective Access Roadmap For Identity And Access Management ImplementationThis slide highlights the project roadmap to implement the Identity and Access Management process. The purpose of this slide is to showcase the different phases of the IAM implementation plan, such as implementing emerging IAM technologies, BYOI adoption, etc. Introducing IAM Process For Effective Access Roadmap For Identity And Access Management Implementation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Testing And Security Assurance, Monitoring And Continuous Improvement, Access Management Implementation, using this template. Grab it now to reap its full benefits.
-
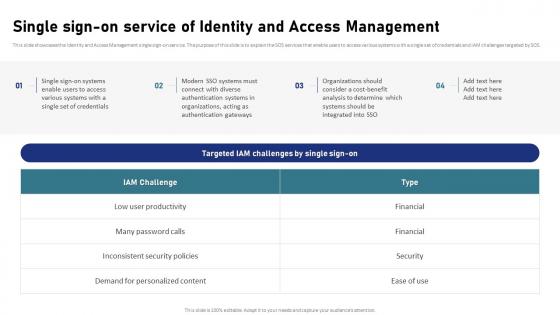 IAM Process For Effective Access Single Sign On Service Of Identity And Access Management
IAM Process For Effective Access Single Sign On Service Of Identity And Access ManagementThis slide showcases the Identity and Access Management single sign-on service. The purpose of this slide is to explain the SOS services that enable users to access various systems with a single set of credentials and IAM challenges targeted by SOS. Increase audience engagement and knowledge by dispensing information using IAM Process For Effective Access Single Sign On Service Of Identity And Access Management. This template helps you present information on four stages. You can also present information on Testing And Security Assurance, Monitoring And Continuous Improvement, Access Management Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
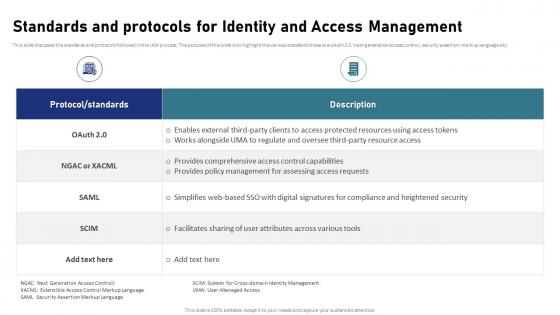 IAM Process For Effective Access Standards And Protocols For Identity And Access Management
IAM Process For Effective Access Standards And Protocols For Identity And Access ManagementThis slide discusses the standards and protocols followed in the IAM process. The purpose of this slide is to highlight the various standards these are oAuth 2.0, next-generation access control, security assertion markup language etc. Present the topic in a bit more detail with this IAM Process For Effective Access Standards And Protocols For Identity And Access Management. Use it as a tool for discussion and navigation on Next Generation Access Control, Security Assertion Markup Language, Access Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
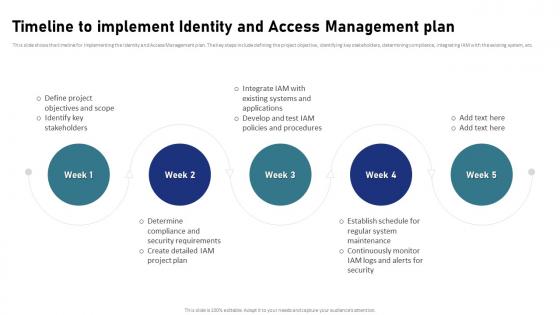 IAM Process For Effective Access Timeline To Implement Identity And Access Management Plan
IAM Process For Effective Access Timeline To Implement Identity And Access Management PlanThis slide shows the timeline for implementing the Identity and Access Management plan. The key steps include defining the project objective, identifying key stakeholders, determining compliance, integrating IAM with the existing system, etc. Introducing IAM Process For Effective Access Timeline To Implement Identity And Access Management Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Timeline To Implement Identity, Access Management Plan, Regular System Maintenance, using this template. Grab it now to reap its full benefits.
-
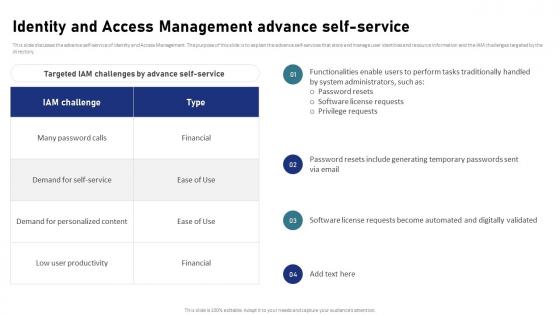 Identity And Access Management Advance Self Service IAM Process For Effective Access
Identity And Access Management Advance Self Service IAM Process For Effective AccessThis slide discusses the advance self-service of Identity and Access Management. The purpose of this slide is to explain the advance self-services that store and manage user identities and resource information and the IAM challenges targeted by the directory. Present the topic in a bit more detail with this Identity And Access Management Advance Self Service IAM Process For Effective Access. Use it as a tool for discussion and navigation on Demand For Personalized Content, Low User Productivity, Many Password Calls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identity And Access Management And Compliance Regulation IAM Process For Effective Access
Identity And Access Management And Compliance Regulation IAM Process For Effective AccessThis slide showcases the Identity and Access Management and compliance regulations. The purpose of this slide is to discuss the compliances adopting the IAM system, enhancing data security and privacy, simplifying compliance, etc. Deliver an outstanding presentation on the topic using this Identity And Access Management And Compliance Regulation IAM Process For Effective Access. Dispense information and present a thorough explanation of Adoption Of IAM Systems, Automation For Reporting Compliance, Regulatory Documentation Requirements using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
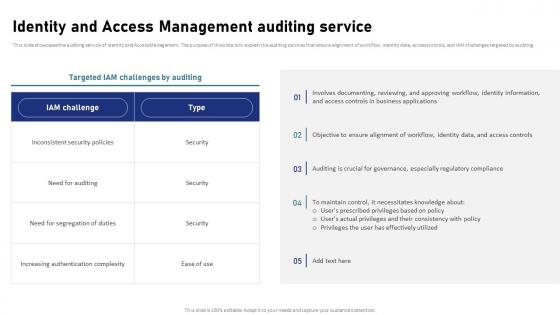 Identity And Access Management Auditing Service IAM Process For Effective Access
Identity And Access Management Auditing Service IAM Process For Effective AccessThis slide showcases the auditing service of Identity and Access Management. The purpose of this slide is to explain the auditing services that ensure alignment of workflow, identity data, access controls, and IAM challenges targeted by auditing. Present the topic in a bit more detail with this Identity And Access Management Auditing Service IAM Process For Effective Access. Use it as a tool for discussion and navigation on Need For Segregation Of Duties, Increasing Authentication Complexity, Inconsistent Security Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identity And Access Management Challenges And Solutions IAM Process For Effective Access
Identity And Access Management Challenges And Solutions IAM Process For Effective AccessThis slide highlights the challenges associated with IAM. The purpose of this slide is to discuss the solutions provided to different challenges related to IAM. These include distributed workforce, distributed application, productive provisioning, BYOD, etc. Deliver an outstanding presentation on the topic using this Identity And Access Management Challenges And Solutions IAM Process For Effective Access. Dispense information and present a thorough explanation of Productive Provisioning, Distributed Applications, Password Problems, Access Management Challenges using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
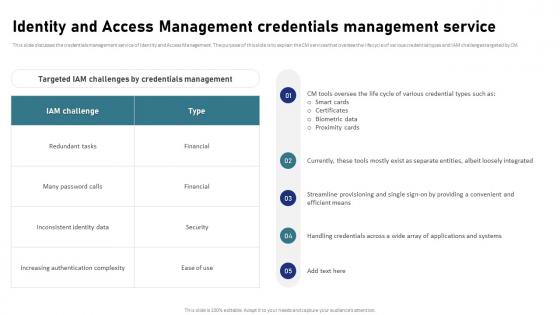 Identity And Access Management Credentials Management Service IAM Process For Effective Access
Identity And Access Management Credentials Management Service IAM Process For Effective AccessThis slide discusses the credentials management service of Identity and Access Management. The purpose of this slide is to explain the CM services that oversee the life cycle of various credential types and IAM challenges targeted by CM. Present the topic in a bit more detail with this Identity And Access Management Credentials Management Service IAM Process For Effective Access. Use it as a tool for discussion and navigation on Smart Cards, Certificates, Biometric Data, Proximity Cards. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
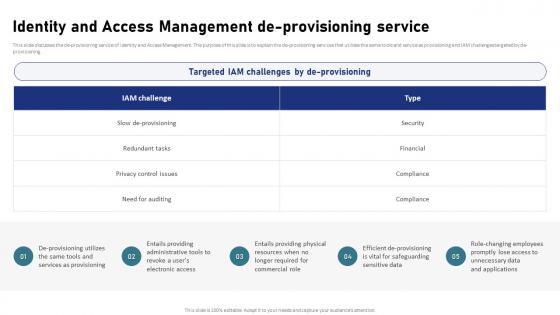 Identity And Access Management De Provisioning Service IAM Process For Effective Access
Identity And Access Management De Provisioning Service IAM Process For Effective AccessThis slide discusses the de-provisioning service of Identity and Access Management. The purpose of this slide is to explain the de-provisioning services that utilizes the same tools and service as provisioning and IAM challenges targeted by de-provisioning. Introducing Identity And Access Management De Provisioning Service IAM Process For Effective Access to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Redundant Tasks, Privacy Control Issues, Need For Auditing, using this template. Grab it now to reap its full benefits.
-
 Identity And Access Management Directory Technologies IAM Process For Effective Access
Identity And Access Management Directory Technologies IAM Process For Effective AccessThis slide discusses the directory technologies service of Identity and Access Management. The purpose of this slide is to explain the directory services that store and manage user identities and resource information and the IAM challenges targeted by the directory. Increase audience engagement and knowledge by dispensing information using Identity And Access Management Directory Technologies IAM Process For Effective Access. This template helps you present information on five stages. You can also present information on Identity And Access Management, Directory Technologies, Resource Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
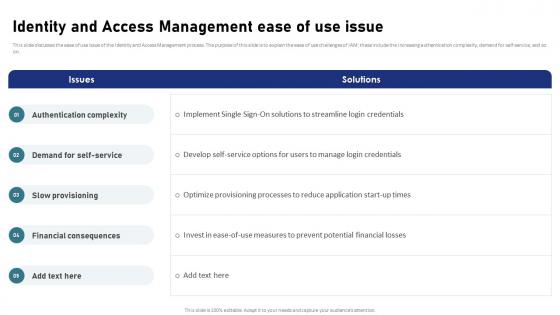 Identity And Access Management Ease Of Use Issue IAM Process For Effective Access
Identity And Access Management Ease Of Use Issue IAM Process For Effective AccessThis slide discusses the ease of use issue of the Identity and Access Management process. The purpose of this slide is to explain the ease of use challenges of IAM these include the increasing authentication complexity, demand for self-service, and so on. Deliver an outstanding presentation on the topic using this Identity And Access Management Ease Of Use Issue IAM Process For Effective Access. Dispense information and present a thorough explanation of Authentication Complexity, Demand For Self Service, Financial Consequences using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Federation Service IAM Process For Effective Access
Identity And Access Management Federation Service IAM Process For Effective AccessThis slide discusses the federation service of Identity and Access Management. The purpose of this slide is to explain the federation services that bring together separately managed identity systems and IAM challenges targeted by the federation. Present the topic in a bit more detail with this Identity And Access Management Federation Service IAM Process For Effective Access. Use it as a tool for discussion and navigation on Low User Productivity, Redundant Tasks, Identity And Access Management, Federation Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
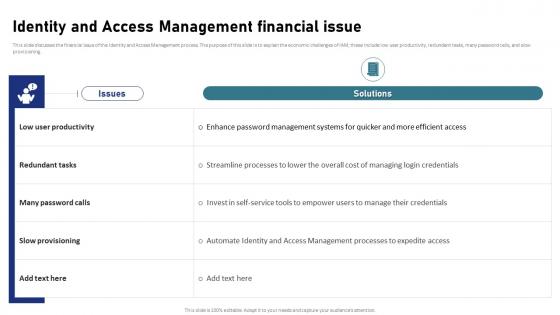 Identity And Access Management Financial Issue IAM Process For Effective Access
Identity And Access Management Financial Issue IAM Process For Effective AccessThis slide discusses the financial issue of the Identity and Access Management process. The purpose of this slide is to explain the economic challenges of IAM these include low user productivity, redundant tasks, many password calls, and slow provisioning. Deliver an outstanding presentation on the topic using this Identity And Access Management Financial Issue IAM Process For Effective Access. Dispense information and present a thorough explanation of Redundant Tasks, Many Password Calls, Identity And Access Management, Financial Issue using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Function As Security Tool IAM Process For Effective Access
Identity And Access Management Function As Security Tool IAM Process For Effective AccessThis slide showcases function of Identity and Access Management as a security tool. The purpose of this slide is to explain the function of IAM as an essential security tool these include context awareness, identity and access governance, and so on. Present the topic in a bit more detail with this Identity And Access Management Function As Security Tool IAM Process For Effective Access. Use it as a tool for discussion and navigation on Context Awareness, Identity And Access Governance, Management Function. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
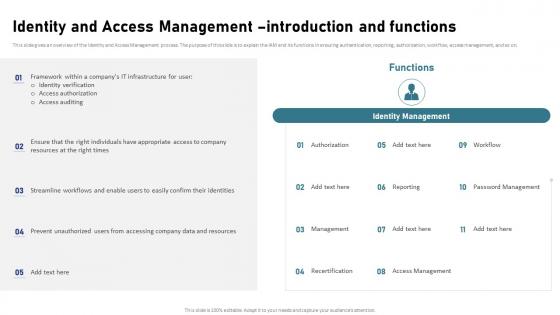 Identity And Access Management Introduction And Functions IAM Process For Effective Access
Identity And Access Management Introduction And Functions IAM Process For Effective AccessThis slide gives an overview of the Identity and Access Management process. The purpose of this slide is to explain the IAM and its functions in ensuring authentication, reporting, authorization, workflow, access management, and so on. Introducing Identity And Access Management Introduction And Functions IAM Process For Effective Access to increase your presentation threshold. Encompassed with eleven stages, this template is a great option to educate and entice your audience. Dispence information on Authorization, Password Management, Access Management, Recertification, using this template. Grab it now to reap its full benefits.
-
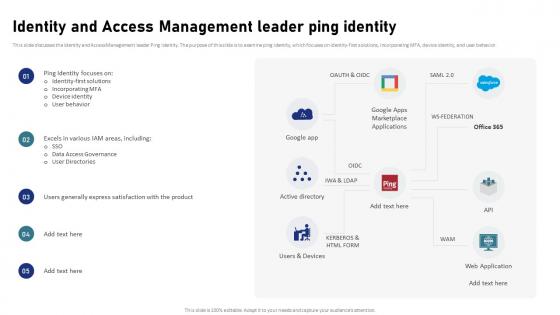 Identity And Access Management Leader Ping Identity IAM Process For Effective Access
Identity And Access Management Leader Ping Identity IAM Process For Effective AccessThis slide discusses the Identity and Access Management leader Ping identity. The purpose of this slide is to examine ping identity, which focuses on identity-first solutions, incorporating MFA, device identity, and user behavior. Present the topic in a bit more detail with this Identity And Access Management Leader Ping Identity IAM Process For Effective Access. Use it as a tool for discussion and navigation on Identity First Solutions, Incorporating MFA, Device Identity, User Behavior. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
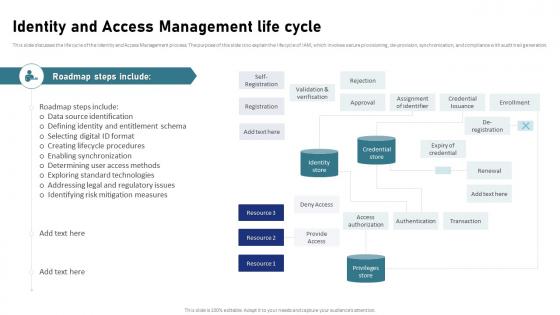 Identity And Access Management Life Cycle IAM Process For Effective Access
Identity And Access Management Life Cycle IAM Process For Effective AccessThis slide discusses the life cycle of the Identity and Access Management process. The purpose of this slide is to explain the life cycle of IAM, which involves secure provisioning, de-provision, synchronization, and compliance with audit trail generation. Deliver an outstanding presentation on the topic using this Identity And Access Management Life Cycle IAM Process For Effective Access. Dispense information and present a thorough explanation of Data Source Identification, Creating Lifecycle Procedures, Enabling Synchronization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
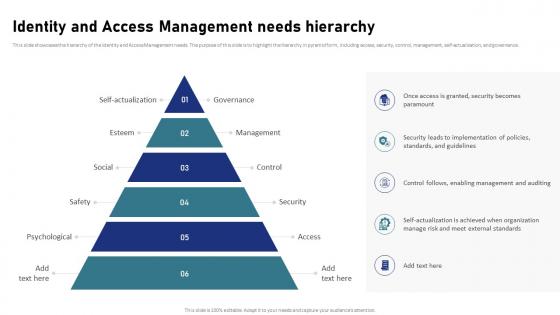 Identity And Access Management Needs Hierarchy IAM Process For Effective Access
Identity And Access Management Needs Hierarchy IAM Process For Effective AccessThis slide showcases the hierarchy of the Identity and Access Management needs. The purpose of this slide is to highlight the hierarchy in pyramid form, including access, security, control, management, self-actualization, and governance. Increase audience engagement and knowledge by dispensing information using Identity And Access Management Needs Hierarchy IAM Process For Effective Access. This template helps you present information on six stages. You can also present information on Identity And Access Management, Security, Control, Management, Self Actualization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
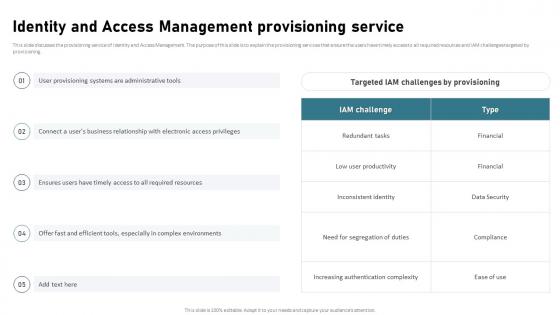 Identity And Access Management Provisioning Service IAM Process For Effective Access
Identity And Access Management Provisioning Service IAM Process For Effective AccessThis slide discusses the provisioning service of Identity and Access Management. The purpose of this slide is to explain the provisioning services that ensure the users have timely access to all required resources and IAM challenges targeted by provisioning. Deliver an outstanding presentation on the topic using this Identity And Access Management Provisioning Service IAM Process For Effective Access. Dispense information and present a thorough explanation of Identity And Access Management, Provisioning Service, Inconsistent Identity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Regulatory Compliance Issue IAM Process For Effective Access
Identity And Access Management Regulatory Compliance Issue IAM Process For Effective AccessThis slide discusses the regulatory compliance issue of the Identity and Access Management process. The purpose of this slide is to explain the regulatory challenges of IAM these include the need for auditing, privacy control, and segregation of duties, etc. Present the topic in a bit more detail with this Identity And Access Management Regulatory Compliance Issue IAM Process For Effective Access. Use it as a tool for discussion and navigation on Identity And Access Management, Regulatory Compliance Issue, Segregation Of Duties, Privacy Control. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
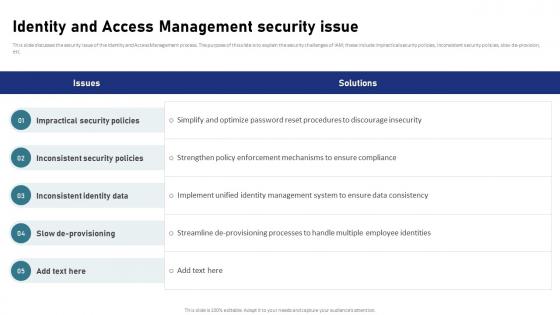 Identity And Access Management Security Issue IAM Process For Effective Access
Identity And Access Management Security Issue IAM Process For Effective AccessThis slide discusses the security issue of the Identity and Access Management process. The purpose of this slide is to explain the security challenges of IAM these include impractical security policies, inconsistent security policies, slow de-provision, etc. Deliver an outstanding presentation on the topic using this Identity And Access Management Security Issue IAM Process For Effective Access. Dispense information and present a thorough explanation of Impractical Security Policies, Inconsistent Security Policies, Inconsistent Identity Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Rope Access Technician In Powerpoint And Google Slides Cpp
Rope Access Technician In Powerpoint And Google Slides CppPresenting our Rope Access Technician In Powerpoint And Google Slides Cpp PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Rope Access Technician This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cloud Access Security Broker And Encryption CASB Cloud Security
Cloud Access Security Broker And Encryption CASB Cloud SecurityThis slide describes the improved encryption with CASB version 2.0. The purpose of this slide is to showcase the various encryption features of cloud access security broker version 2.0, including security that follows the data, content access that can be revoked at any time, and multi-platform compatibility. Present the topic in a bit more detail with this Cloud Access Security Broker And Encryption CASB Cloud Security. Use it as a tool for discussion and navigation on Security That Tracks Data, Multi Platform Compatibility, Personally Identifiable Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Access Security Broker And Secure Web Gateway CASB Cloud Security
Cloud Access Security Broker And Secure Web Gateway CASB Cloud SecurityThis slide represents how CASB 2.0 not just discovers the shadow IT but helps to control it too. The purpose of this slide is to showcase how CASB 2.0 improves the SWG model by empowering it with rich cloud app data, getting dynamic control of shadow IT and simplifying deployment. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker And Secure Web Gateway CASB Cloud Security. Dispense information and present a thorough explanation of Cloud App Data, Dynamic Control Of Shadow, Secure Web Gateway, Cloud App Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker And User Authentication CASB Cloud Security
Cloud Access Security Broker And User Authentication CASB Cloud SecurityThis slide represents the improved user authentication method in cloud access security broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Present the topic in a bit more detail with this Cloud Access Security Broker And User Authentication CASB Cloud Security. Use it as a tool for discussion and navigation on Cloud Access Security Broker, User Authentication, Multifactor Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
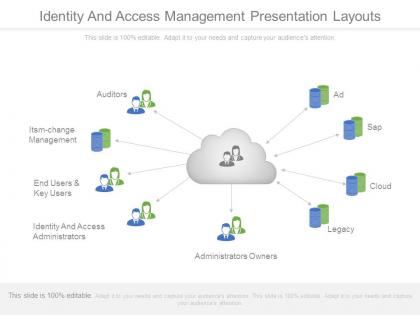 Identity and access management presentation layouts
Identity and access management presentation layoutsImpressive picture quality. High resolution of visuals ensures clear projection on wide screen. Compatible with multiple online and offline software. Harmonious with numerous formats like JPEG/JPG/PDF. Ease of executing changes in presentation as per individual preferences. Easy inclusion and exclusion of slide content as per the need of an hour. Personalize the content with your company name, logo and trademark. Professionally equipped and aesthetically designed set of slides. Widely accessible by students, teachers, engineers, entrepreneurs and IT professionals.
-
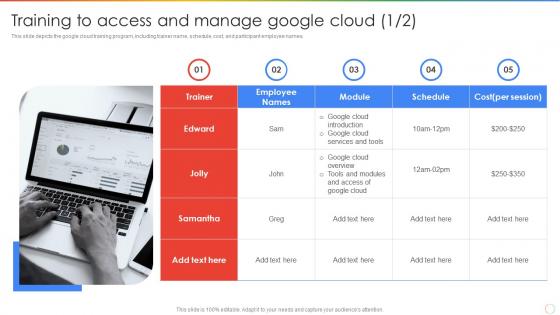 Training To Access And Manage Google Cloud Ppt Powerpoint Presentation Outline Introduction
Training To Access And Manage Google Cloud Ppt Powerpoint Presentation Outline IntroductionThis slide depicts the google cloud training program, including trainer name, schedule, cost, and participant employee names. Introducing Training To Access And Manage Google Cloud Ppt Powerpoint Presentation Outline Introduction to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Training To Access, Manage Google Cloud, using this template. Grab it now to reap its full benefits.



