Powerpoint Templates and Google slides for Aggression
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Child abuse template with man hitting child
Child abuse template with man hitting childPresenting this set of slides with name - Child Abuse Template With Man Hitting Child. This is a one stage process. The stages in this process are Child Abuse, Sexual Harm, Child Maltreatment.
-
 Child abuse template with man scaring kid
Child abuse template with man scaring kidPresenting this set of slides with name - Child Abuse Template With Man Scaring Kid. This is a one stage process. The stages in this process are Child Abuse, Sexual Harm, Child Maltreatment.
-
 Child crying abuse template asking for help image
Child crying abuse template asking for help imagePresenting this set of slides with name - Child Crying Abuse Template Asking For Help Image. This is a one stage process. The stages in this process are Child Abuse, Sexual Harm, Child Maltreatment.
-
 Girl child crying abuse template
Girl child crying abuse templatePresenting this set of slides with name - Girl Child Crying Abuse Template. This is a one stage process. The stages in this process are Child Abuse, Sexual Harm, Child Maltreatment.
-
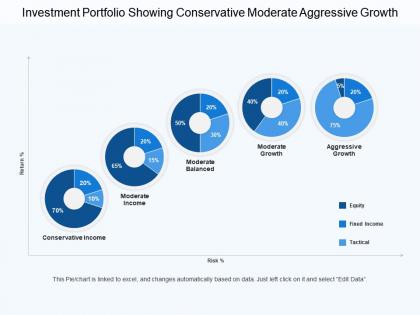 Investment portfolio showing conservative moderate aggressive growth
Investment portfolio showing conservative moderate aggressive growthPresenting this set of slides with name - Investment Portfolio Showing Conservative Moderate Aggressive Growth. This is a five stage process. The stages in this process are Investment Portfolio, Funding Portfolio, Expenditure Portfolio.
-
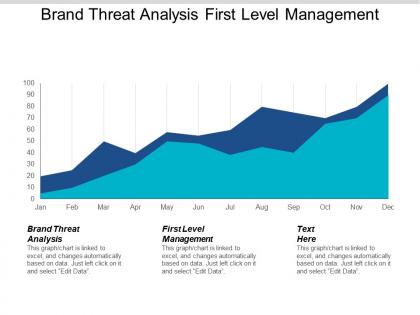 Brand threat analysis first level management company governance cpb
Brand threat analysis first level management company governance cpbPresenting this set of slides with name - Brand Threat Analysis First Level Management Company Governance Cpb. This is an editable three stages graphic that deals with topics like Brand Threat Analysis, First Level Management, Company Governance to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Biological hazard or biohazard pose threat to health
Biological hazard or biohazard pose threat to healthExhibiting biological hazard or biohazard pose threat to health PPT design. Fast download with easy to save options. Wonderful picture quality as pixels remains same even on large screen. PowerPoint template can be merged with Google Slides and also works well with JPG and PDF. Easy update company data such as logo, name and tagline. Fully amendable presentation layout as color, text and shape are editable. PowerPoint sample can be expected in standard and widescreen view.
-
 Biological hazard showing public threat
Biological hazard showing public threatDelivering biological hazard showing public threat PPT template. Amazing picture quality as comes with high resolution picture quality. Presentation slide is easy to download and save. Completely modifiable design as can be amended as you needed. Choice adds corporate name, logo, icon, image and tagline. PowerPoint design is accommodating with multiple softwares like JPG and PDF. PPT diagram merge well with Google Slides and can be presented with it when needed.
-
 Employee harassment ppt powerpoint presentation portfolio guidelines cpb
Employee harassment ppt powerpoint presentation portfolio guidelines cpbPresenting this set of slides with name - Employee Harassment Ppt Powerpoint Presentation Portfolio Guidelines Cpb. This is an editable four stages graphic that deals with topics like Employee Harassment to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Employee harassment ppt powerpoint presentation ideas master slide cpb
Employee harassment ppt powerpoint presentation ideas master slide cpbPresenting this set of slides with name - Employee Harassment Ppt Powerpoint Presentation Ideas Master Slide Cpb. This is an editable four stages graphic that deals with topics like Employee Harassment to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Types threats network security ppt powerpoint presentation ideas example cpb
Types threats network security ppt powerpoint presentation ideas example cpbPresenting this set of slides with name Types Threats Network Security Ppt Powerpoint Presentation Ideas Example Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Types Threats Network Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 It threat intelligence ppt powerpoint presentation ideas images cpb
It threat intelligence ppt powerpoint presentation ideas images cpbPresenting this set of slides with name IT Threat Intelligence Ppt Powerpoint Presentation Ideas Images Cpb. This is an editable Powerpoint three stages graphic that deals with topics like IT Threat Intelligence to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Threat risk assessment ppt powerpoint presentation gallery slide cpb
Threat risk assessment ppt powerpoint presentation gallery slide cpbPresenting this set of slides with name Threat Risk Assessment Ppt Powerpoint Presentation Gallery Slide Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Threat Risk Assessment to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
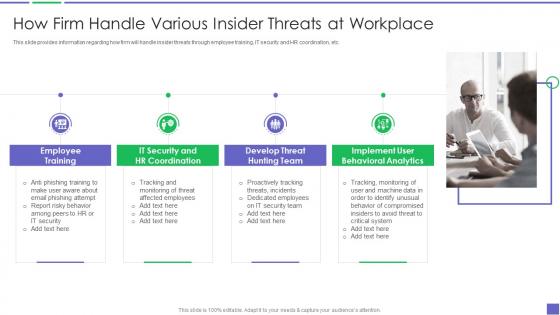 How Firm Handle Various Insider Threats At Workplace Building Business Analytics Architecture
How Firm Handle Various Insider Threats At Workplace Building Business Analytics ArchitectureThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Increase audience engagement and knowledge by dispensing information using How Firm Handle Various Insider Threats At Workplace Building Business Analytics Architecture. This template helps you present information on two stages. You can also present information on Employee Training, IT Security And HR Coordination, Develop Threat Hunting Team, Implement User Behavioral Analytics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
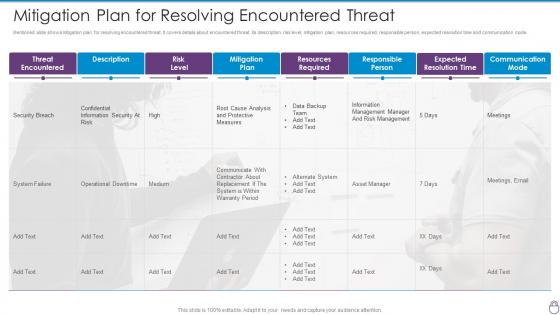 Cybersecurity Risk Management Framework Mitigation Plan For Resolving Encountered Threat
Cybersecurity Risk Management Framework Mitigation Plan For Resolving Encountered ThreatMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Mitigation Plan For Resolving Encountered Threat. Dispense information and present a thorough explanation of Security Breach, Data Backup Team, Asset Manager, Operational Downtime using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
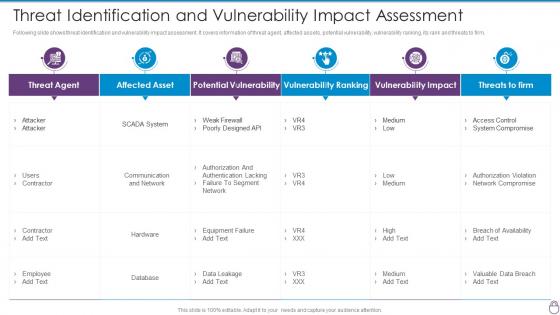 Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact
Cybersecurity Risk Management Framework Threat Identification And Vulnerability ImpactFollowing slide shows threat identification and vulnerability impact assessment. It covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Threat Identification And Vulnerability Impact. Dispense information and present a thorough explanation of Threat Agent, Affected Asset, Potential Vulnerability, Vulnerability Ranking, Vulnerability Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
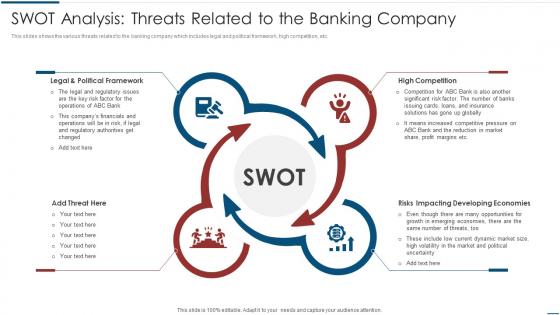 Implementation Latest Technologies SWOT Analysis Threats Related Banking Company
Implementation Latest Technologies SWOT Analysis Threats Related Banking CompanyThis slides shows the various threats related to the banking company which includes legal and political framework, high competition, etc. Introducing Implementation Latest Technologies SWOT Analysis Threats Related Banking Company to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Legal And Political Framework, High Competition, Impacting Developing Economies, Threat, using this template. Grab it now to reap its full benefits.
-
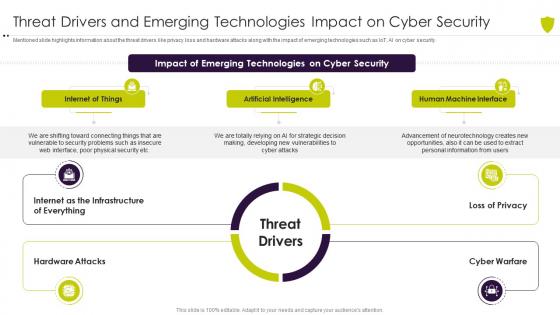 Threat drivers and emerging managing cyber risk in a digital age
Threat drivers and emerging managing cyber risk in a digital ageMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security. Introducing Threat Drivers And Emerging Managing Cyber Risk In A Digital Age to increase your presentation threshold. Encompassed with threee stages, this template is a great option to educate and entice your audience. Dispence information on Internet Of Things, Artificial Intelligence, Human Machine Interface, using this template. Grab it now to reap its full benefits.
-
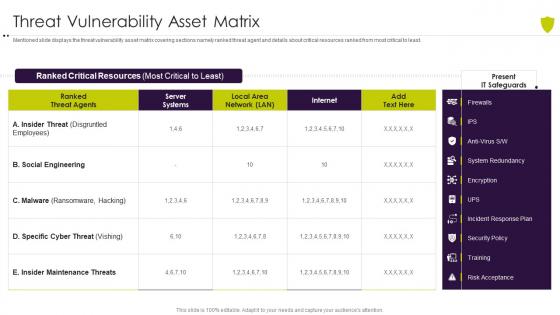 Threat vulnerability asset matrix managing cyber risk in a digital age
Threat vulnerability asset matrix managing cyber risk in a digital ageMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Threat Vulnerability Asset Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
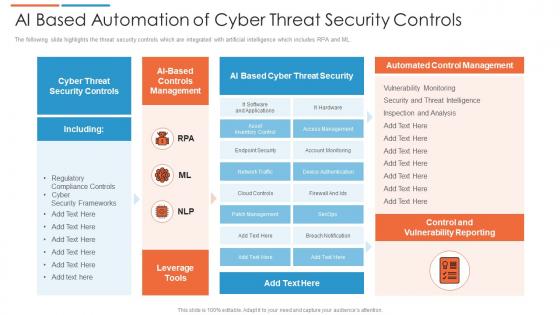 Ai based automation of cyber threat security controls
Ai based automation of cyber threat security controlsThe following slide highlights the threat security controls which are integrated with artificial intelligence which includes RPA and ML. Introducing our AI Based Automation Of Cyber Threat Security Controls set of slides. The topics discussed in these slides are Cyber Threat Security, Automated Control Management, Control And Vulnerability Reporting. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
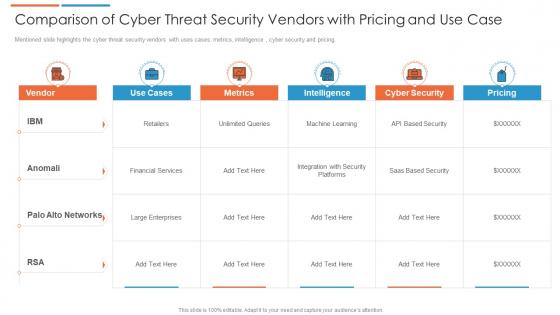 Comparison of cyber threat security vendors with pricing and use case
Comparison of cyber threat security vendors with pricing and use caseMentioned slide highlights the cyber threat security vendors with uses cases, metrics, intelligence , cyber security and pricing. Presenting our well structured Comparison Of Cyber Threat Security Vendors With Pricing And Use Case. The topics discussed in this slide are Financial Services, Cyber Security, Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
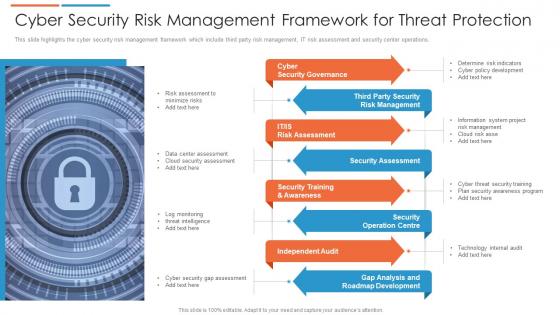 Cyber security risk management framework for threat protection
Cyber security risk management framework for threat protectionThis slide highlights the cyber security risk management framework which include third party risk management, IT risk assessment and security center operations. Presenting our set of slides with Cyber Security Risk Management Framework For Threat Protection. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Governance, Security Assessment, Independent Audit.
-
 Cyber security threat management system
Cyber security threat management systemThe following slide illustrates the cyber security threat management system which includes threat containment, logging and traceability management. Introducing our Cyber Security Threat Management System set of slides. The topics discussed in these slides are Threat Containment And Remediation, Identify Management, Application Visibility And Control. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
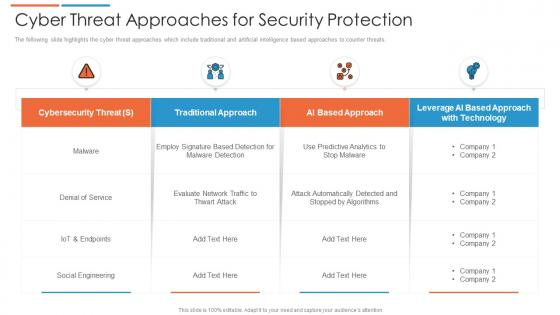 Cyber threat approaches for security protection
Cyber threat approaches for security protectionThe following slide highlights the cyber threat approaches which include traditional and artificial intelligence based approaches to counter threats. Presenting our well structured Cyber Threat Approaches For Security Protection. The topics discussed in this slide are Cybersecurity Threat, Social Engineering, Traditional Approach. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
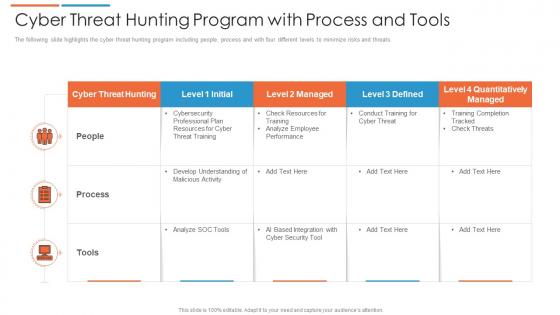 Cyber threat hunting program with process and tools
Cyber threat hunting program with process and toolsThe following slide highlights the cyber threat hunting program including people, process and with four different levels to minimize risks and threats. Introducing our Cyber Threat Hunting Program With Process And Tools set of slides. The topics discussed in these slides are Cyber Threat Hunting, Cyber Security Tool, Cyber Threat Training. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber threat icon indicating malware attack
Cyber threat icon indicating malware attackIntroducing our premium set of slides with Cyber Threat Icon Indicating Malware Attack. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Icon Indicating Malware Attack. So download instantly and tailor it with your information.
-
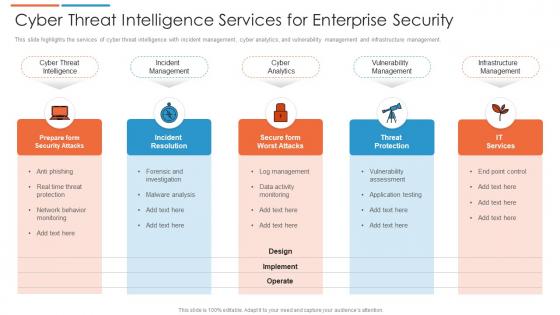 Cyber threat intelligence services for enterprise security
Cyber threat intelligence services for enterprise securityThis slide highlights the services of cyber threat intelligence with incident management, cyber analytics, and vulnerability management and infrastructure management. Presenting our set of slides with Cyber Threat Intelligence Services For Enterprise Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Infrastructure Management, Vulnerability Management, Cyber Analytics.
-
 Cyber threat report with risk indicator and affected systems
Cyber threat report with risk indicator and affected systemsPresenting our well structured Cyber Threat Report With Risk Indicator And Affected Systems. The topics discussed in this slide are Risk Level, Risk Indication, Potential Affected Systems. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
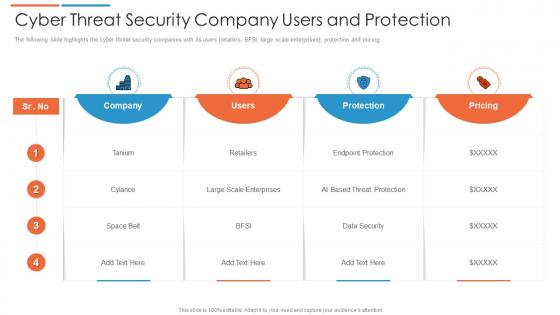 Cyber threat security company users and protection
Cyber threat security company users and protectionThe following slide highlights the cyber threat security companies with its users retailers, BFSI, large scale enterprises, protection and pricing. Introducing our Cyber Threat Security Company Users And Protection set of slides. The topics discussed in these slides are Pricing, Company, Users. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber threat security icon to capture sensitive information
Cyber threat security icon to capture sensitive informationIntroducing our premium set of slides with Cyber Threat Security Icon To Capture Sensitive Information. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Security Icon To Capture Sensitive Information. So download instantly and tailor it with your information.
-
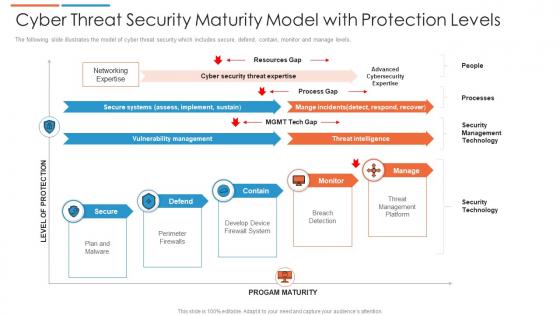 Cyber threat security maturity model with protection levels
Cyber threat security maturity model with protection levelsThe following slide illustrates the model of cyber threat security which includes secure, defend, contain, monitor and manage levels. Presenting our well structured Cyber Threat Security Maturity Model With Protection Levels. The topics discussed in this slide are Security Management Technology, Threat Management Platform, Threat Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
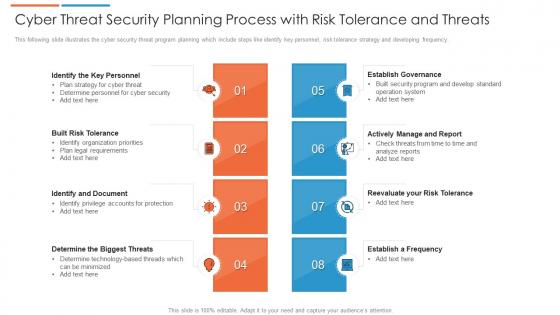 Cyber threat security planning process with risk tolerance and threats
Cyber threat security planning process with risk tolerance and threatsThis following slide illustrates the cyber security threat program planning which include steps like identify key personnel, risk tolerance strategy and developing frequency. Presenting our set of slides with Cyber Threat Security Planning Process With Risk Tolerance And Threats. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Built Risk Tolerance, Identify And Document, Establish Governance.
-
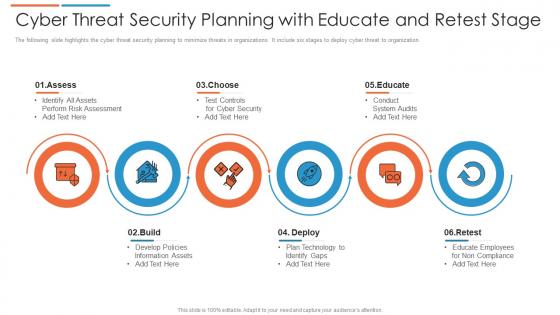 Cyber threat security planning with educate and retest stage
Cyber threat security planning with educate and retest stageThe following slide highlights the cyber threat security planning to minimize threats in organizations. It include six stages to deploy cyber threat to organization. Introducing our premium set of slides with Cyber Threat Security Planning With Educate And Retest Stage. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Deploy, Retest, Educate. So download instantly and tailor it with your information.
-
 Cyber threat strategies for security protection
Cyber threat strategies for security protectionThis slide highlights the cyber threat strategies that include risk assessment, phishing program, software protocols and end point protection. Presenting our set of slides with Cyber Threat Strategies For Security Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Program, Software Protocols, End Point Protection.
-
 Key cyber security threat to organizations
Key cyber security threat to organizationsThis slide displays different types of cyber security threats which impacts organization negatively. It include malware, emotet, phishing and SQL injection. Introducing our premium set of slides with Key Cyber Security Threat To Organizations. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Malware, Phishing, SQL Injection. So download instantly and tailor it with your information.
-
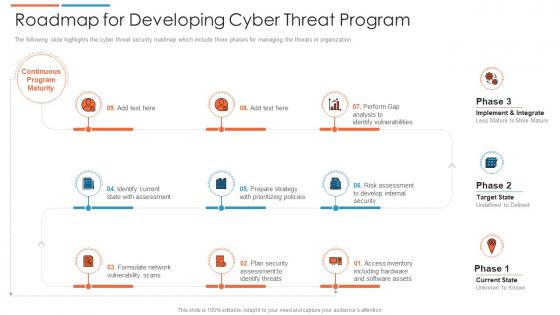 Roadmap for developing cyber threat program
Roadmap for developing cyber threat programThe following slide highlights the cyber threat security roadmap which include three phases for managing the threats in organization. Presenting our set of slides with Roadmap For Developing Cyber Threat Program. This exhibits information on nine stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implement And Integrate, Risk Assessment, Identify Vulnerabilities.
-
 Major Factors Leading To Russias Aggression Ukraine Vs Russia Analyzing Conflict
Major Factors Leading To Russias Aggression Ukraine Vs Russia Analyzing ConflictThis slide provides information regarding the major factors leading to Russias aggression to invade Ukraine in terms of economic, geo political and strategies factors NATOs enlargement is also considered as one the leading factor. Present the topic in a bit more detail with this Major Factors Leading To Russias Aggression Ukraine Vs Russia Analyzing Conflict Use it as a tool for discussion and navigation on Economic Factors, Strategic Factors, Enlargement This template is free to edit as deemed fit for your organization. Therefore download it now.
-
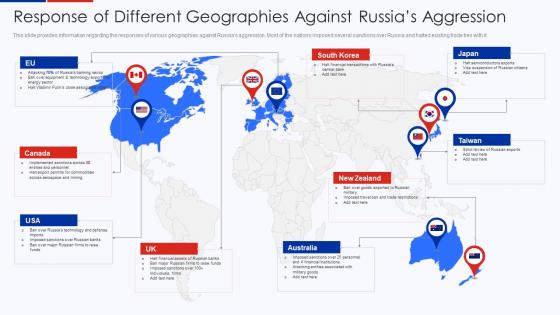 Response Of Different Geographies Against Russias Aggression Ukraine Vs Russia Analyzing Conflict
Response Of Different Geographies Against Russias Aggression Ukraine Vs Russia Analyzing ConflictThis slide provides information regarding the responses of various geographies against Russias aggression. Most of the nations imposed several sanctions over Russia and halted existing trade ties with it.Introducing Response Of Different Geographies Against Russias Aggression Ukraine Vs Russia Analyzing Conflict to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Semiconductors Exports, Suspension Of Russian, Imposed Sanctions using this template. Grab it now to reap its full benefits.
-
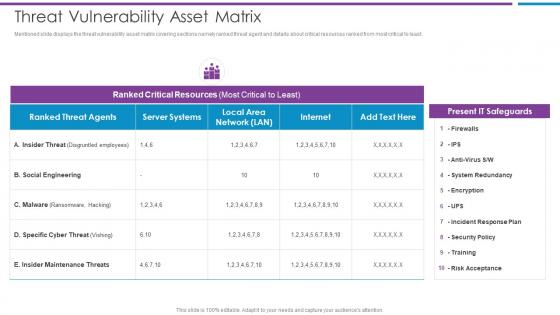 Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber
Threat Vulnerability Asset Matrix Risk Based Methodology To CyberMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Social Engineering, Ranked Critical Resources, Present IT Safeguards This template is free to edit as deemed fit for your organization. Therefore download it now.
-
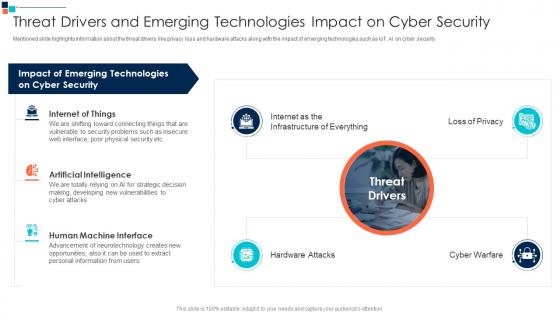 Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber Security
Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber SecurityMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security.Increase audience engagement and knowledge by dispensing information using Threat Drivers And Emerging Introducing A Risk Based Approach To Cyber Security This template helps you present information on one stage. You can also present information on Internet Of Things, Artificial Intelligence, Human Machine Interface using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
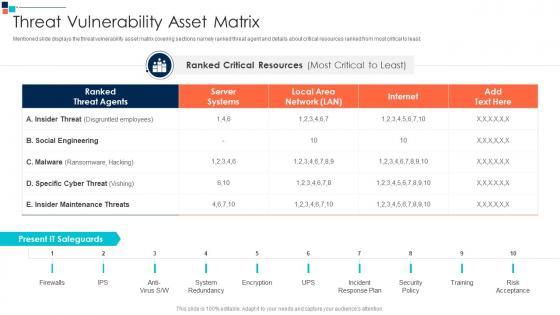 Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security
Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on System Redundancy, Incident Response Plan, Security Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
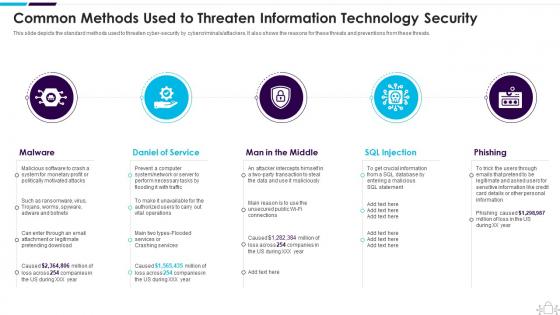 Information Technology Security Common Methods Used Threaten Information Security
Information Technology Security Common Methods Used Threaten Information SecurityThis slide depicts the standard methods used to threaten cyber security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Introducing Information Technology Security Common Methods Used Threaten Information Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Daniel Of Service, Man In The Middle, SQL Injection , using this template. Grab it now to reap its full benefits.
-
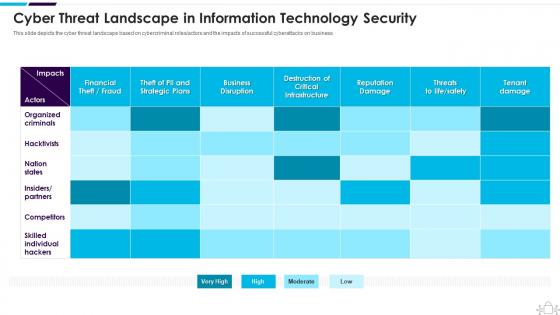 Information Technology Security Cyber Threat Landscape In Information Technology Security
Information Technology Security Cyber Threat Landscape In Information Technology SecurityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Deliver an outstanding presentation on the topic using this Information Technology Security Cyber Threat Landscape In Information Technology Security. Dispense information and present a thorough explanation of Landscape, Information, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Security Latest Threats In Information Technology Security
Information Technology Security Latest Threats In Information Technology SecurityThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Deliver an outstanding presentation on the topic using this Information Technology Security Latest Threats In Information Technology Security. Dispense information and present a thorough explanation of Latest Threats In Information Technology Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Security Threats In Information Technology Security
Information Technology Security Threats In Information Technology SecurityThis slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Introducing Information Technology Security Threats In Information Technology Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Types Of Threats In Information Technology Security, using this template. Grab it now to reap its full benefits.
-
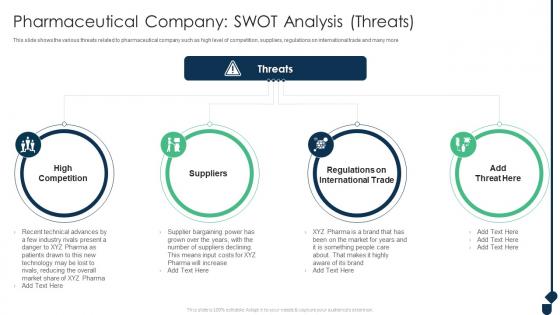 Pharmaceutical Company S W O T Analysis Threats Achieving Sustainability Evolving
Pharmaceutical Company S W O T Analysis Threats Achieving Sustainability EvolvingThis slide shows the various threats related to pharmaceutical company such as high level of competition, suppliers, regulations on international trade and many more Increase audience engagement and knowledge by dispensing information using Pharmaceutical Company S W O T Analysis Threats Achieving Sustainability Evolving. This template helps you present information on four stages. You can also present information on High Competition, Suppliers, Regulations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Contingency Plan For Threat Handling In Building Business Analytics Architecture
Contingency Plan For Threat Handling In Building Business Analytics ArchitectureThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Present the topic in a bit more detail with this Contingency Plan For Threat Handling In Building Business Analytics Architecture. Use it as a tool for discussion and navigation on Contingency Solutions, Contingency Considerations, Local Area Network, Wide Area Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
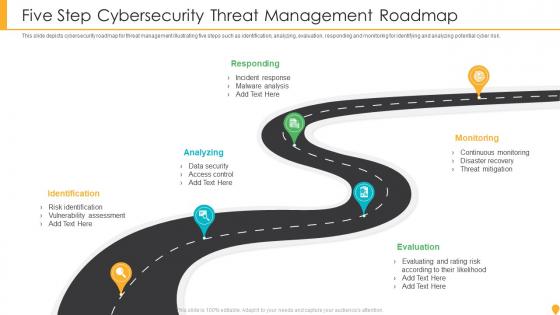 Five Step Cybersecurity Threat Management Roadmap
Five Step Cybersecurity Threat Management RoadmapThis slide depicts cybersecurity roadmap for threat management illustrating five steps such as identification, analyzing, evaluation, responding and monitoring for identifying and analyzing potential cyber risk. Presenting our set of slides with name Five Step Cybersecurity Threat Management Roadmap. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Analyzing, Identification, Responding, Monitoring, Evaluation.
-
 Difference Between Weakness Threat In Powerpoint And Google Slides Cpb
Difference Between Weakness Threat In Powerpoint And Google Slides CpbPresenting Difference Between Weakness Threat In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase two stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Difference Between Weakness Threat. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Bug Threat Hunting Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Bug Threat Hunting Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Bug threat hunting colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Bug Threat Hunting Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Bug Threat Hunting Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Bug threat hunting monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Computer Threat Hunting Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Computer Threat Hunting Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Computer threat hunting colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Computer Threat Hunting Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Computer Threat Hunting Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Computer threat hunting monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Threat Hunting And Gear Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Hunting And Gear Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Threat hunting and gear colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Threat Hunting And Gear Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Hunting And Gear Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Threat hunting and gear monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
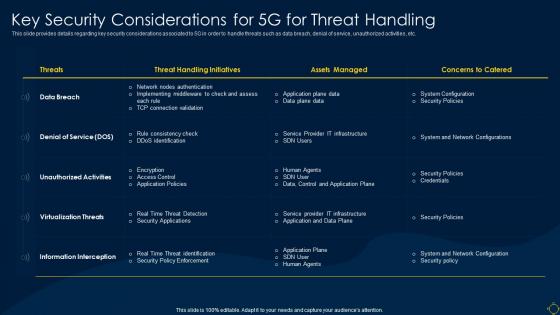 Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System
Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless SystemThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System. Use it as a tool for discussion and navigation on Considerations, Service, Unauthorized. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
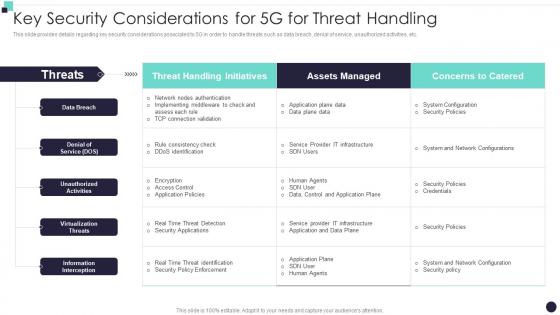 Key Security Considerations For 5G For Threat Handling Building 5G Wireless Mobile Network
Key Security Considerations For 5G For Threat Handling Building 5G Wireless Mobile NetworkThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5G For Threat Handling Building 5G Wireless Mobile Network. Use it as a tool for discussion and navigation on Threat Handling Initiatives, Assets Managed, Denial Of Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
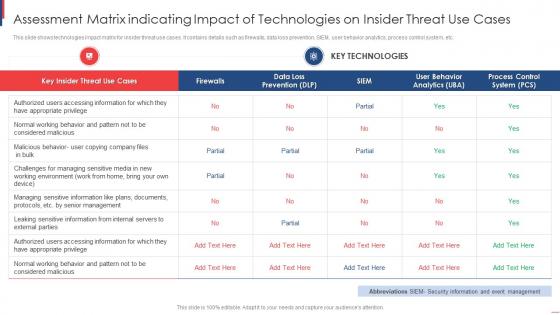 Assessment Matrix Indicating Impact Of Technologies On Insider Threat Use Cases
Assessment Matrix Indicating Impact Of Technologies On Insider Threat Use CasesThis slide shows technologies impact matrix for insider threat use cases. It contains details such as firewalls, data loss prevention, SIEM, user behavior analytics, process control system, etc. Introducing our Assessment Matrix Indicating Impact Of Technologies On Insider Threat Use Cases set of slides. The topics discussed in these slides are Assessment Matrix, Indicating Impact, Technologies On Insider, Threat Use Cases. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
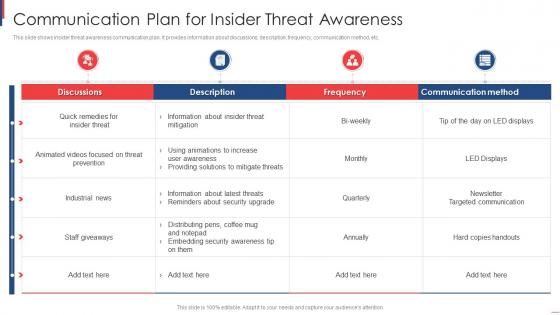 Communication Plan For Insider Threat Awareness
Communication Plan For Insider Threat AwarenessThis slide shows insider threat awareness communication plan. It provides information about discussions, description, frequency, communication method, etc. Presenting our well-structured Communication Plan For Insider Threat Awareness. The topics discussed in this slide are Communication Plan, Insider, Threat Awareness. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
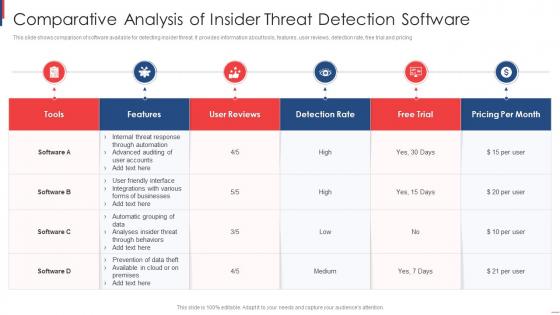 Comparative Analysis Of Insider Threat Detection Software
Comparative Analysis Of Insider Threat Detection SoftwareThis slide shows comparison of software available for detecting insider threat. It provides information about tools, features, user reviews, detection rate, free trial and pricing Introducing our Comparative Analysis Of Insider Threat Detection Software set of slides. The topics discussed in these slides are Comparative Analysis, Insider, Threat Detection Software. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.