Powerpoint Templates and Google slides for Application Security Enterprise
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
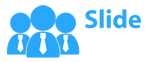
 Data Encryption Features In Application Security
Data Encryption Features In Application SecurityThis slide outlines the characteristics of encryption in application security such as security, easy-to-use, document support, etc. Introducing Data Encryption Features In Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Implement Strict Input Validation, Employ Bot Detection Mechanisms, Application Security Deployment, using this template. Grab it now to reap its full benefits.
-
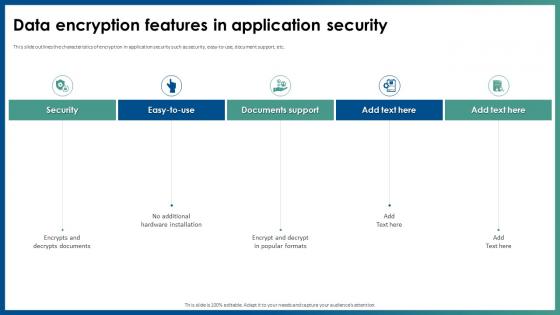
 Data Encryption Method In Application Security
Data Encryption Method In Application SecurityThis slide outlines the characteristics of encryption in application security such as security, easy-to-use, document support, etc. Increase audience engagement and knowledge by dispensing information using Data Encryption Method In Application Security. This template helps you present information on five stages. You can also present information on Encodes Plaintext To Ciphertext, Decryption Needs Specific Keys, Create Cryptographic Models using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
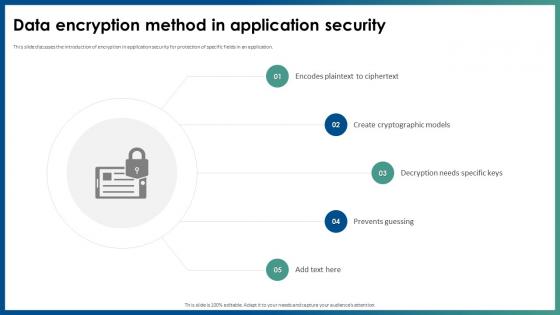
 Difference Between Authentication And Authorization In Application Security
Difference Between Authentication And Authorization In Application SecurityThis slide showcase the difference between authentication and authorization in application security on aspects such as purpose, operation, etc. Deliver an outstanding presentation on the topic using this Difference Between Authentication And Authorization In Application Security. Dispense information and present a thorough explanation of Confirms Credentials, Authentication, Authorization, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
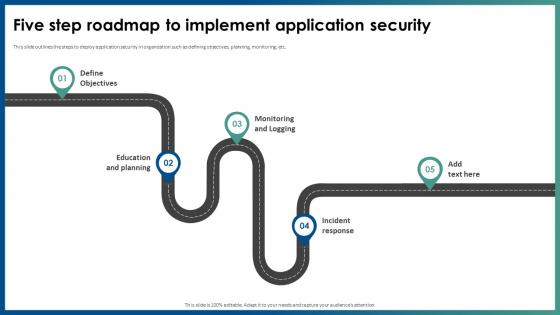 Five Step Roadmap To Implement Application Security
Five Step Roadmap To Implement Application SecurityThis slide outlines the steps to deploy application security in organization such as defining objectives, planning, monitoring, etc. Introducing Five Step Roadmap To Implement Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Monitoring And Logging, Education And Planning, Five Step Roadmap, Application Security, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Application Security Ppt File Designs Download
Icons Slide For Application Security Ppt File Designs DownloadPresenting our well crafted Icons Slide For Application Security Ppt File Designs Download set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Introduction Of Application Security For Data Privacy
Introduction Of Application Security For Data PrivacyThis slide discusses the overview of application security which includes its objectives such as protecting data, minimize risk, etc. Increase audience engagement and knowledge by dispensing information using Introduction Of Application Security For Data Privacy. This template helps you present information on four stages. You can also present information on Covers Post Deployment Protection, Protects Data And Code, Application Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Benefits Of Implementing Application Security
Key Benefits Of Implementing Application SecurityThis slide highlights the key advantages of application security which include minimum risk exposure, security, etc. Introducing Key Benefits Of Implementing Application Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Safeguards Sensitive Information, Preserves The Brand Reputation, Minimizes Risk, using this template. Grab it now to reap its full benefits.
-
 Log Management Process In Application Security
Log Management Process In Application SecurityThis slide showcases the introduction of log management in application security for decreasing the security threats. Increase audience engagement and knowledge by dispensing information using Log Management Process In Application Security. This template helps you present information on five stages. You can also present information on Handling Security Logs, Non Compliance Risks Attacks, Ensure Data Security, Log Management Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Main Features For Robust Application Security
Main Features For Robust Application SecurityThis slide outlines the key characteristics of application security which include authentication, authorization, encryption, logging, etc. Introducing Main Features For Robust Application Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Authorization, Application Security Testing, Robust Application Security, using this template. Grab it now to reap its full benefits.
-
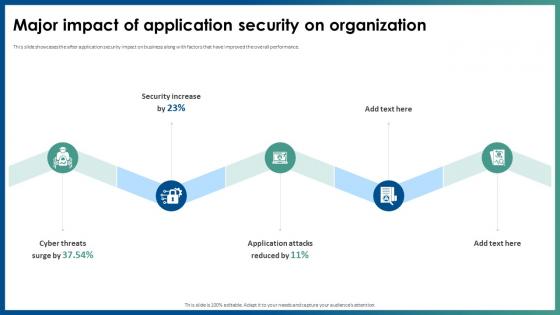 Major Impact Of Application Security On Organization
Major Impact Of Application Security On OrganizationThis slide showcases the after application security impact on business along with factors that have improved the overall performance. Increase audience engagement and knowledge by dispensing information using Major Impact Of Application Security On Organization. This template helps you present information on five stages. You can also present information on Application Attacks, Application Security, Security Increase using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
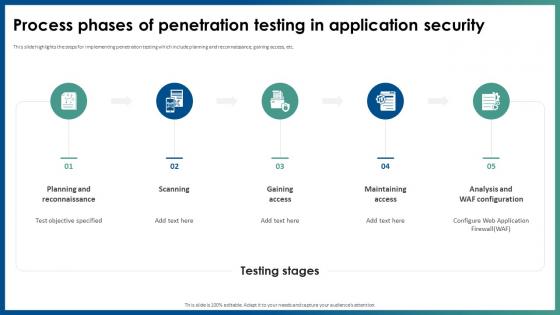 Process Phases Of Penetration Testing In Application Security
Process Phases Of Penetration Testing In Application SecurityThis slide highlights the steps for implementing penetration testing which include planning and reconnaissance, gaining access, etc. Introducing Process Phases Of Penetration Testing In Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Planning And Reconnaissance, Gaining Access, Maintaining Access, Analysis And WAF Configuration, using this template. Grab it now to reap its full benefits.
-
 Security Log Management Best Practices Application Security
Security Log Management Best Practices Application SecurityThis slide highlights the best approaches of logging implementation which include preventing inappropriate actions, employ logging tools, etc. Increase audience engagement and knowledge by dispensing information using Security Log Management Best Practices Application Security. This template helps you present information on five stages. You can also present information on Scrutinize Admin And Operators, Prevent Inappropriate Actions, Ensure Authorized Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
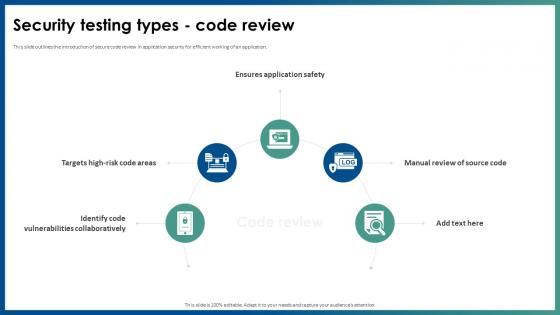 Security Testing Types Code Review Application Security
Security Testing Types Code Review Application SecurityThis slide outlines the introduction of secure code review in application security for efficient working of an application. Introducing Security Testing Types Code Review Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Ensures Application Safety, Identify Code Vulnerabilities Collaboratively, Manual Review Of Source Code, using this template. Grab it now to reap its full benefits.
-
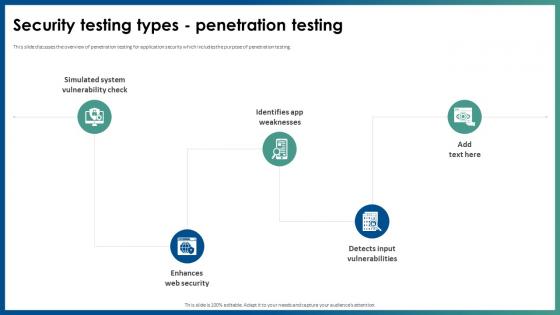 Security Testing Types Penetration Testing Application Security
Security Testing Types Penetration Testing Application SecurityThis slide discusses the overview of penetration testing for application security which includes the purpose of penetration testing. Increase audience engagement and knowledge by dispensing information using Security Testing Types Penetration Testing Application Security. This template helps you present information on five stages. You can also present information on Enhances Web Security, Simulated System Vulnerability Check, Identifies App Weaknesses, Detects Input Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
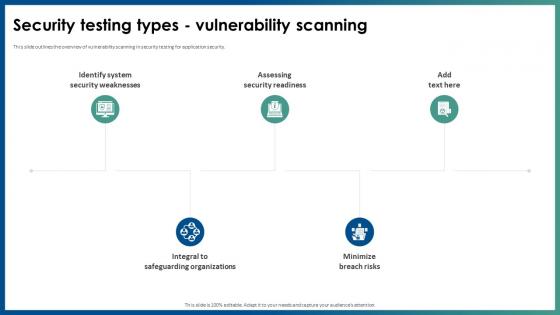 Security Testing Types Vulnerability Scanning Application Security
Security Testing Types Vulnerability Scanning Application SecurityThis slide outlines the overview of vulnerability scanning in security testing for application security. Introducing Security Testing Types Vulnerability Scanning Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assessing Security Readiness, Integral To Safeguarding Organizations, Identify System Security Weaknesses, using this template. Grab it now to reap its full benefits.
-
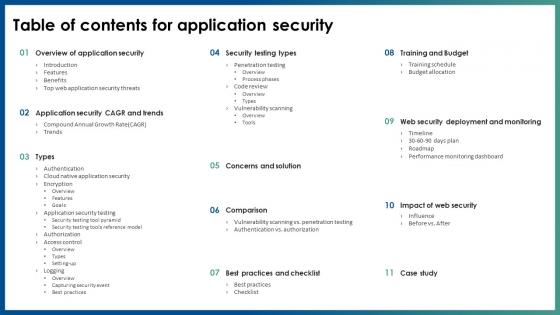 Table Of Contents For Application Security Ppt File Slide Download
Table Of Contents For Application Security Ppt File Slide DownloadIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Application Security Ppt File Slide Download. This template helps you present information on eleven stages. You can also present information on Concerns And Solution, Impact Of Web Security, Training And Budget, Security Testing Types using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
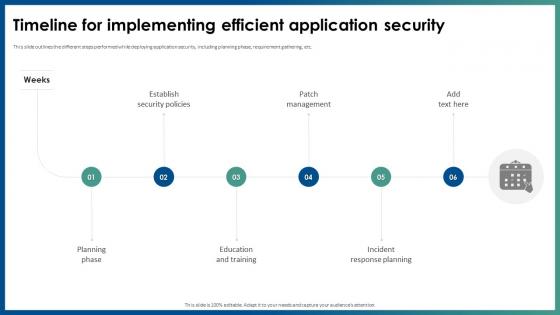 Timeline For Implementing Efficient Application Security
Timeline For Implementing Efficient Application SecurityThis slide outlines the different steps performed while deploying application security, including planning phase, requirement gathering, etc. Introducing Timeline For Implementing Efficient Application Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Patch Management, Incident Response Planning, Planning Phase, Education And Training, using this template. Grab it now to reap its full benefits.
-
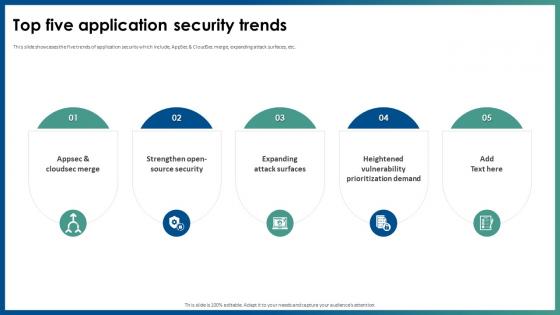 Top Five Application Security Trends Ppt File Example Introduction
Top Five Application Security Trends Ppt File Example IntroductionThis slide showcases the five trends of application security which include, AppSec and CloudSec merge, expanding attack surfaces, etc. Increase audience engagement and knowledge by dispensing information using Top Five Application Security Trends Ppt File Example Introduction. This template helps you present information on five stages. You can also present information on Heightened Vulnerability, Prioritization Demand, Expanding Attack Surfaces, Appsec And Cloudsec Merge using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Top Web Application Security Threats Ppt File Example Topics
Top Web Application Security Threats Ppt File Example TopicsThis slide discusses the vulnerabilities and security threats in web application such as SQL injection, cross-site scripting, etc. Deliver an outstanding presentation on the topic using this Top Web Application Security Threats Ppt File Example Topics. Dispense information and present a thorough explanation of Cross Site Request Forgery, Insecure Direct Object References, Web Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
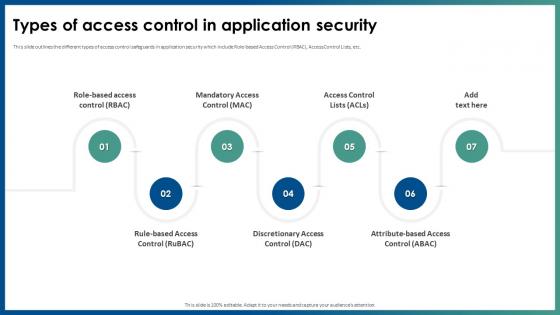 Types Of Access Control In Application Security
Types Of Access Control In Application SecurityThis slide outlines the different types of access control safeguards in application security which include Role-based Access Control RBAC, Access Control Lists, etc. Introducing Types Of Access Control In Application Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Mandatory Access Control, Discretionary Access Control, Application Security, using this template. Grab it now to reap its full benefits.
-
 Types Of Secure Code Review In Application Security
Types Of Secure Code Review In Application SecurityThis slide discusses the two types of secure code review in application security which are automated code review and manual code review. Increase audience engagement and knowledge by dispensing information using Types Of Secure Code Review In Application Security. This template helps you present information on four stages. You can also present information on Swiftly Analyzes Large Codebases, Identifies Nuanced Flaws, Real Time Vulnerability Detection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Micro Endpoint Security Application Control
Endpoint Security Micro Endpoint Security Application ControlThis slide discusses about one of the components of endpoint security which is application control for data protection in devices. Introducing Endpoint Security Micro Endpoint Security Application Control to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Increase In Malware Defense, Data Protection, Prevent Unauthorized Applications, Optimal Endpoint Security, using this template. Grab it now to reap its full benefits.
-
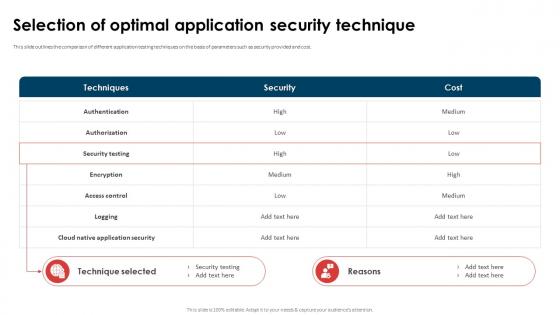 Application Security Implementation Plan Selection Of Optimal Application Security Technique
Application Security Implementation Plan Selection Of Optimal Application Security TechniqueThis slide outlines the comparison of different application testing techniques on the basis of parameters such as security provided and cost. Present the topic in a bit more detail with this Application Security Implementation Plan Selection Of Optimal Application Security Technique. Use it as a tool for discussion and navigation on Authorization, Encryption, Security Testing, Access Control. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Best Practices To Ensure Mobile Application Security Mobile Device Security Cybersecurity SS
Best Practices To Ensure Mobile Application Security Mobile Device Security Cybersecurity SSThis slide showcases best practices that can help to improve mobile application security. Its key elements are data encryption, security containers and secure KPIs Increase audience engagement and knowledge by dispensing information using Best Practices To Ensure Mobile Application Security Mobile Device Security Cybersecurity SS This template helps you present information on Three stages. You can also present information on Data Encryption, Secure Apis, Security Containers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Case Study 1 Mobile Application Security Mobile Device Security Cybersecurity SS
Case Study 1 Mobile Application Security Mobile Device Security Cybersecurity SSThis slide showcases case study regarding implementation of mobile application security solutions. Its key elements are objectives, challenges, solutions and impact Increase audience engagement and knowledge by dispensing information using Case Study 1 Mobile Application Security Mobile Device Security Cybersecurity SS This template helps you present information on Three stages. You can also present information on Enhanced Mobile Security, Objectives, Solution Implemented using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
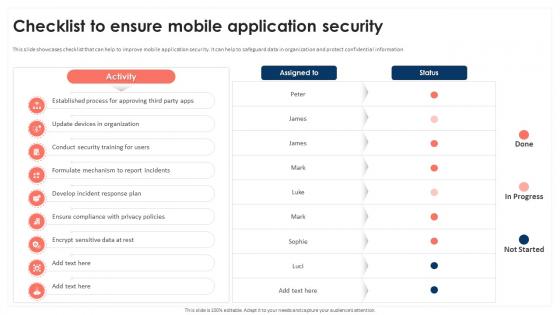 Checklist To Ensure Mobile Application Security Mobile Device Security Cybersecurity SS
Checklist To Ensure Mobile Application Security Mobile Device Security Cybersecurity SSThis slide showcases checklist that can help to improve mobile application security. It can help to safeguard data in organization and protect confidential information. Present the topic in a bit more detail with this Checklist To Ensure Mobile Application Security Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Update Devices In Organization, Conduct Security Training For Users This template is free to edit as deemed fit for your organization. Therefore download it now.
-
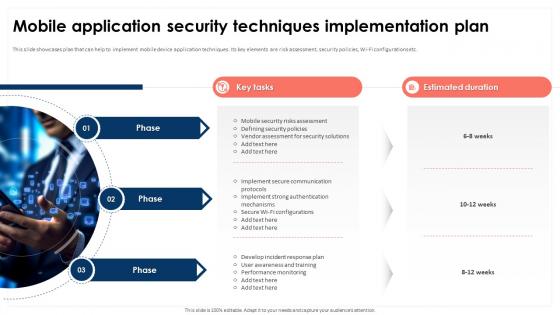 Mobile Application Security Techniques Mobile Device Security Cybersecurity SS
Mobile Application Security Techniques Mobile Device Security Cybersecurity SSThis slide showcases plan that can help to implement mobile device application techniques. Its key elements are risk assessment, security policies, Wi-Fi configurations etc. Introducing Mobile Application Security Techniques Mobile Device Security Cybersecurity SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Global Mobile Cyber Attacks, Telegram And Twitter using this template. Grab it now to reap its full benefits.
-
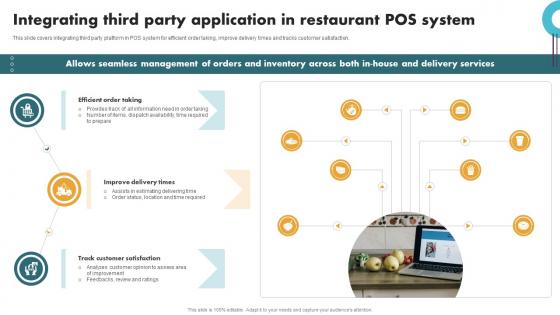 Securing Food Safety In Online Integrating Third Party Application In Restaurant Pos
Securing Food Safety In Online Integrating Third Party Application In Restaurant PosThis slide covers integrating third party platform in POS system for efficient order taking, improve delivery times and tracks customer satisfaction. Introducing Securing Food Safety In Online Integrating Third Party Application In Restaurant Pos to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Efficient Order Taking, Improve Delivery Times, Track Customer Satisfaction, using this template. Grab it now to reap its full benefits.
-
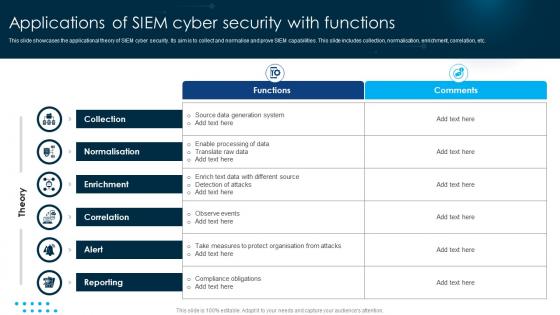 Applications Of SIEM Cyber Security With Functions
Applications Of SIEM Cyber Security With FunctionsThis slide showcases the applicational theory of SIEM cyber security. Its aim is to collect and normalise and prove SIEM capabilities. This slide includes collection, normalisation, enrichment, correlation, etc. Introducing our Applications Of SIEM Cyber Security With Functions set of slides. The topics discussed in these slides are Collection, Enrichment, Correlation . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Best Practices For Security Saas Applications On Cloud Platform
Best Practices For Security Saas Applications On Cloud PlatformThis slide represents various best practices that assist companies in securing their Software as a Service SaaS applications on cloud platforms enhancing operational efficiency. It includes best practices such as secure product engineering, use virtual private cloud, etc. Presenting our set of slides with Best Practices For Security Saas Applications On Cloud Platform. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Secure Product Engineering, Applications, Organization.
-
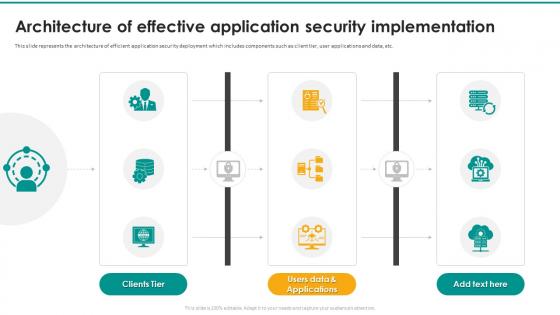 Architecture Of Effective Application Security Implementation
Architecture Of Effective Application Security ImplementationThis slide represents the architecture of efficient application security deployment which includes components such as client tier, user applications and data, etc. Presenting our well structured Architecture Of Effective Application Security Implementation The topics discussed in this slide are Clients Tier, Users Data and ApplicationsThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Authentication For Web Application Security Icon
Authentication For Web Application Security IconPresenting our set of slides with Authentication For Web Application Security Icon This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication For Web, Application Security Icon
-
 Authorization Working Process For Application Security
Authorization Working Process For Application SecurityThis slide discusses the workflow of authorization for application security which includes authorized user, resource owner, etc. Introducing our Authorization Working Process For Application Security set of slides. The topics discussed in these slides are Resource Owner, Authorized UserThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
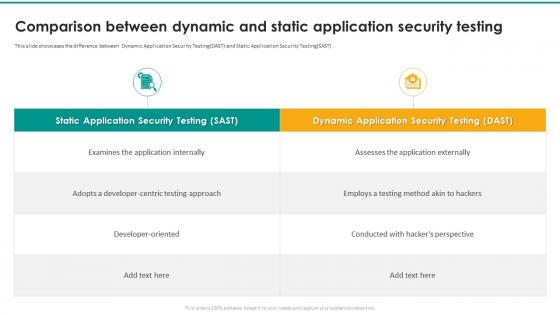 Comparison Between Dynamic And Static Application Security Testing
Comparison Between Dynamic And Static Application Security TestingThis slide showcases the difference between Dynamic Application Security TestingDAST and Static Application Security TestingSAST . Presenting our well structured Comparison Between Dynamic And Static Application Security Testing The topics discussed in this slide are Static Application Security Testing, Dynamic Application Security TestingThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Key Principles Of Application Security Testing
Key Principles Of Application Security TestingIntroducing our Key Principles Of Application Security Testing set of slides. The topics discussed in these slides are Integrity, Authorization, ConfidentialityThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
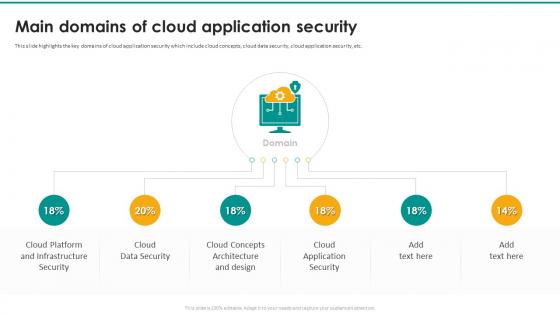 Main Domains Of Cloud Application Security
Main Domains Of Cloud Application SecurityIntroducing our premium set of slides with Main Domains Of Cloud Application Security Ellicudate the Six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Infrastructure Security, Cloud Data Security, Architecture And Design So download instantly and tailor it with your information.
-
 Main Tools For Deploying Application Security
Main Tools For Deploying Application SecurityThis slide discusses the tools used for implementing application security such as Static Application Security Testing, Dynamic Application Security Testing, etc. Presenting our well structured Main Tools For Deploying Application Security The topics discussed in this slide are Security Scanning Tools, Runtime Protection ToolsThis is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Major Types Of Application Security Strategies
Major Types Of Application Security StrategiesThis slide showcases the different techniques of application security which include authentication, authorization, encryption, logging, and security testing. Presenting our set of slides with Major Types Of Application Security Strategies This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Spot Potential, Recognize Valuable Data, Vulnerable Areas
-
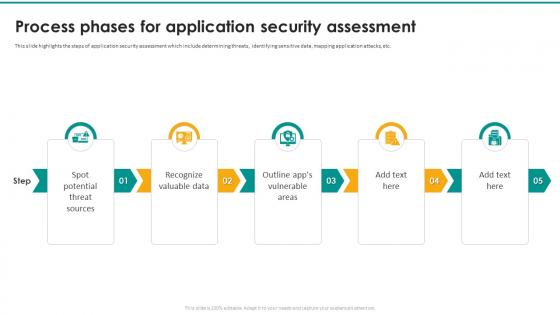 Process Phases For Application Security Assessment
Process Phases For Application Security AssessmentThis slide highlights the steps of application security assessment which include determining threats, identifying sensitive data, mapping application attacks, etc. Introducing our premium set of slides with Process Phases For Application Security Assessment Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Application Security, Statistical Representation So download instantly and tailor it with your information.
-
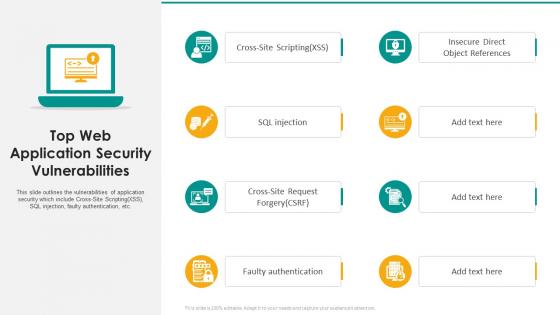 Top Web Application Security Vulnerabilities
Top Web Application Security VulnerabilitiesIntroducing our premium set of slides with Top Web Application Security Vulnerabilities Ellicudate the Eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Faulty Authentication, Object References So download instantly and tailor it with your information.
-
 Vulnerability Monitoring For Application Security Icon
Vulnerability Monitoring For Application Security IconIntroducing our Vulnerability Monitoring For Application Security Icon set of slides. The topics discussed in these slides are Vulnerability Monitoring, Application Security IconThis is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
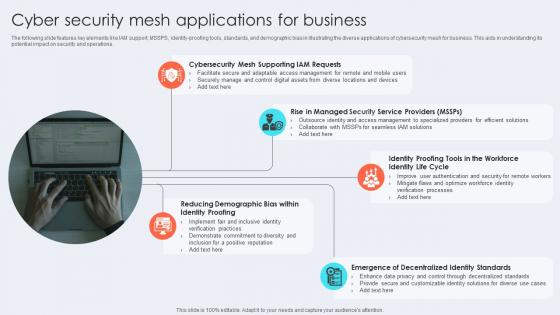 Cyber Security Mesh Applications For Business
Cyber Security Mesh Applications For BusinessThe following slide features key elements like IAM support, MSSPS, identity-proofing tools, standards, and demographic bias in illustrating the diverse applications of cybersecurity mesh for business. This aids in understanding its potential impact on security and operations. Presenting our set of slides with Cyber Security Mesh Applications For Business This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Mesh Supporting Iam Requests, Identity Life Cycle, Decentralized Identity Standards
-
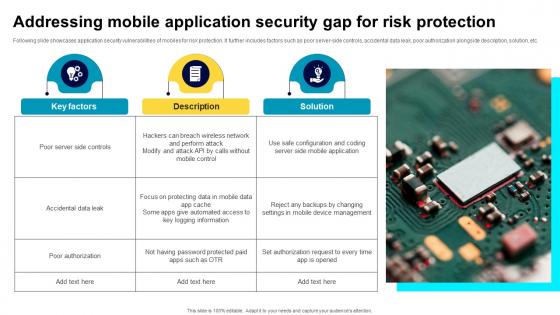 Addressing Mobile Application Security Gap For Risk Protection
Addressing Mobile Application Security Gap For Risk ProtectionFollowing slide showcases application security vulnerabilities of mobiles for risk protection. It further includes factors such as poor server-side controls, accidental data leak, poor authorization alongside description, solution, etc. Introducing our Addressing Mobile Application Security Gap For Risk Protection set of slides. The topics discussed in these slides are Poor Server Side Controls, Accidental Data Leak, Poor Authorization, Solution. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
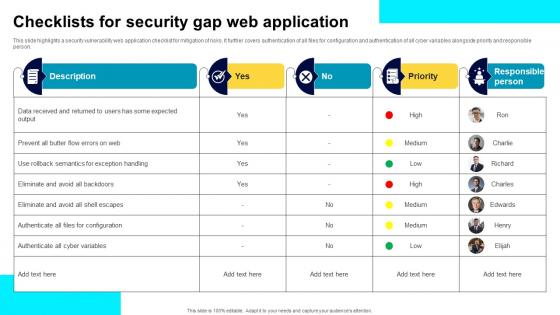 Checklists For Security Gap Web Application
Checklists For Security Gap Web ApplicationThis slide highlights a security vulnerability web application checklist for mitigation of risks. It further covers authentication of all files for configuration and authentication of all cyber variables alongside priority and responsible person. Introducing our Checklists For Security Gap Web Application set of slides. The topics discussed in these slides are Data Received, Semantics For Exception Handling, Cyber Variables. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
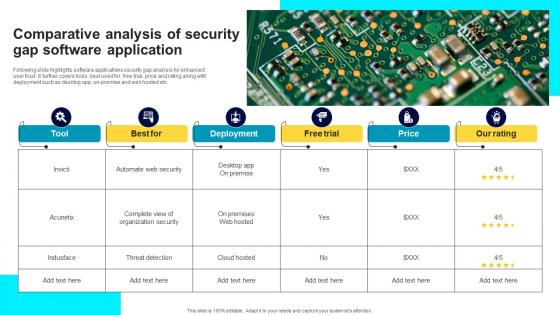 Comparative Analysis Of Security Gap Software Application
Comparative Analysis Of Security Gap Software ApplicationFollowing slide highlights software applications security gap analysis for enhanced user trust. It further covers tools, best used for, free trial, price and rating along with deployment such as desktop app, on-premise and web hosted etc. Introducing our Comparative Analysis Of Security Gap Software Application set of slides. The topics discussed in these slides are Tool, Deployment, Free Trial, Price, Our Rating. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Analyzing Mobile Application Security Checklist
Analyzing Mobile Application Security ChecklistThis slide covers checklist to analyze mobile security for long-term scenarios and includes tasks, applicable and not applicable. Presenting our set of slides with name Analyzing Mobile Application Security Checklist. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Tasks, Applicable, Not Applicable.
-
 Impactful Areas Of Mobile Application Security
Impactful Areas Of Mobile Application SecurityThis slide exhibits key areas of testing applications based on mobile security and includes customer information, financial information, and cloning. Presenting our set of slides with name Impactful Areas Of Mobile Application Security. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Customer Information, Financial Information, Cloning.
-
 Mobile Application Security Risk Assessment
Mobile Application Security Risk AssessmentThis slide demonstrates mobile application security to assess risks and includes improper platform usage, insecure data storage, and insecure communication. Presenting our set of slides with name Mobile Application Security Risk Assessment. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Improper Platform Usage, Insecure Data Storage, Insecure Communication.
-
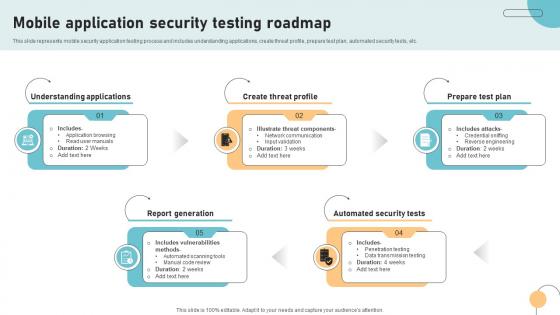 Mobile Application Security Testing Roadmap
Mobile Application Security Testing RoadmapThis slide represents mobile security application testing process and includes understanding applications, create threat profile, prepare test plan, automated security tests, etc. Presenting our set of slides with name Mobile Application Security Testing Roadmap. This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Understanding Applications, Report Generation, Create Threat Profile, Automated Security Tests, Prepare Test Plan.
-
 Internet Gateway Security IT Applications Of Secure Web Gateway In Various
Internet Gateway Security IT Applications Of Secure Web Gateway In VariousThis slide talks about how Secure Web Gateway is used in several industrial domains. The purpose of this slide is to explain how SWG is used in different sectors. The industries covered are financial services, healthcare, education, manufacturing, etc. Introducing Internet Gateway Security IT Applications Of Secure Web Gateway In Various to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Financial Services, Healthcare, Education, Manufacturing, Government, Retail, using this template. Grab it now to reap its full benefits.
-
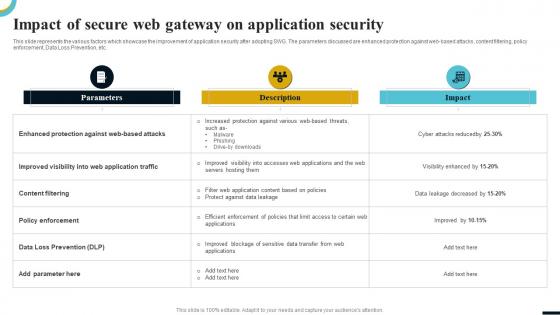 Internet Gateway Security IT Impact Of Secure Web Gateway On Application
Internet Gateway Security IT Impact Of Secure Web Gateway On ApplicationThis slide represents the various factors which showcase the improvement of application security after adopting SWG. The parameters discussed are enhanced protection against web-based attacks, content filtering, policy enforcement, Data Loss Prevention, etc. Present the topic in a bit more detail with this Internet Gateway Security IT Impact Of Secure Web Gateway On Application. Use it as a tool for discussion and navigation on Parameters, Content Filtering, Policy Enforcement, Data Loss Prevention. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 CASB Application In Accounting And Finance Sector CASB Cloud Security
CASB Application In Accounting And Finance Sector CASB Cloud SecurityThis slide outlines the application of the CASB model in the accounting and banking sectors. The purpose of this slide is to give an overview and represent the challenges that occur due to cloud data exchange and how CASB can overcome those challenges. Introducing CASB Application In Accounting And Finance Sector CASB Cloud Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Accounting And Banking Sectors, Substantial Changes In Administration, Wealth Management Organizations, using this template. Grab it now to reap its full benefits.
-
 CASB Application In Learning And Education Sector CASB Cloud Security
CASB Application In Learning And Education Sector CASB Cloud SecurityThis slide represents the application of a cloud access security broker in the learning and education department. The purpose of this slide is to highlight the overview, challenges caused by the transition in education, and CASB solutions. Increase audience engagement and knowledge by dispensing information using CASB Application In Learning And Education Sector CASB Cloud Security. This template helps you present information on three stages. You can also present information on Application In Learning, Education Sector, Transition In Education, Cloud Access Security Broker using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
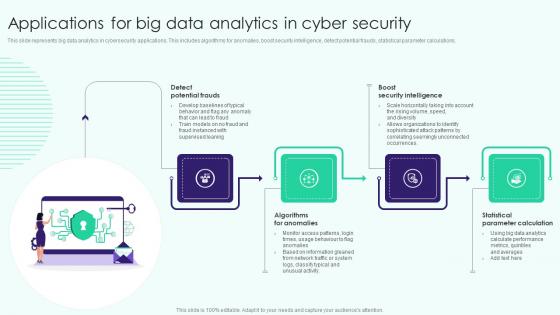 Applications For Big Data Analytics In Cyber Security
Applications For Big Data Analytics In Cyber SecurityThis slide represents big data analytics in cybersecurity applications. This includes algorithms for anomalies, boost security intelligence, detect potential frauds, statistical parameter calculations. Presenting our set of slides with name Applications For Big Data Analytics In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detect Potential Frauds, Algorithms For Anomalies, Statistical Parameter Calculation .
-
 Web Application Security Testing Process Phases
Web Application Security Testing Process PhasesThis slide showcases the process phases of implementing web application security which include information gathering, planning analysis, etc. Introducing our premium set of slides with name Web Application Security Testing Process Phases. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Gathering, Vulnerability Detection, Reporting, Planning Analysis. So download instantly and tailor it with your information.
-
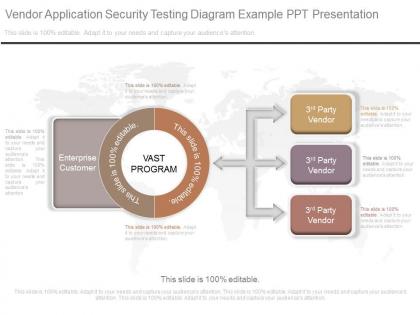 A vendor application security testing diagram example ppt presentation
A vendor application security testing diagram example ppt presentationPresenting a vendor application security testing diagram example ppt presentation. This is a vendor application security testing diagram example ppt presentation. This is a three stage process. The stages in this process are enterprise customer, vast program, 3rd party vendor.
-
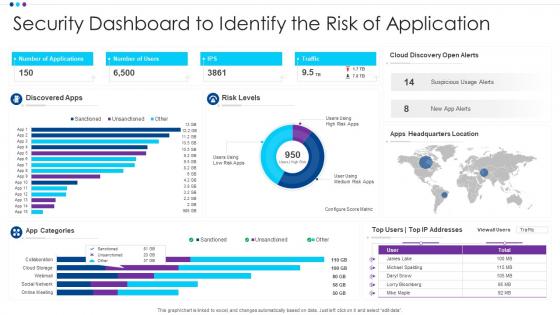 Security Dashboard To Identify The Risk Of Application
Security Dashboard To Identify The Risk Of ApplicationIntroducing our Security Dashboard To Identify The Risk Of Application set of slides. The topics discussed in these slides are App Categories, Discovered Apps, Risk Levels. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
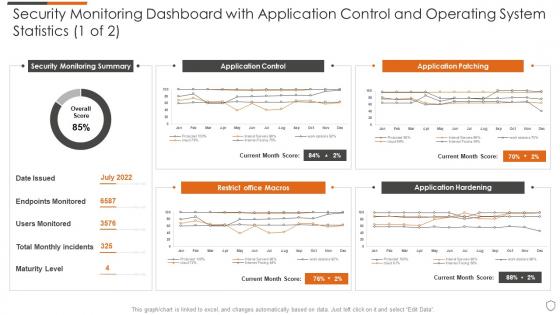 Advanced security monitoring plan security monitoring dashboard with application
Advanced security monitoring plan security monitoring dashboard with applicationPresent the topic in a bit more detail with this Advanced Security Monitoring Plan Security Monitoring Dashboard With Application. Use it as a tool for discussion and navigation on Application Control, Application Patching, Restrict Office Macros, Application Hardening. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
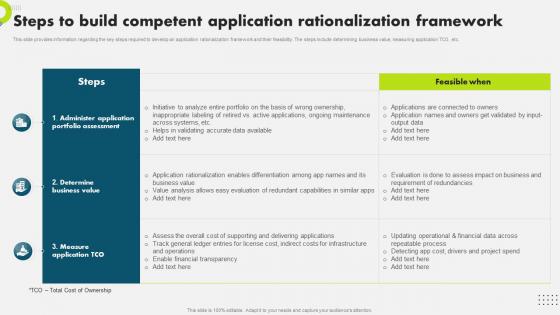 Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V
Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the key steps required to develop an application rationalization framework and their feasibility. The steps include determining business value, measuring application TCO, etc. Present the topic in a bit more detail with this Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Application, Rationalization, Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
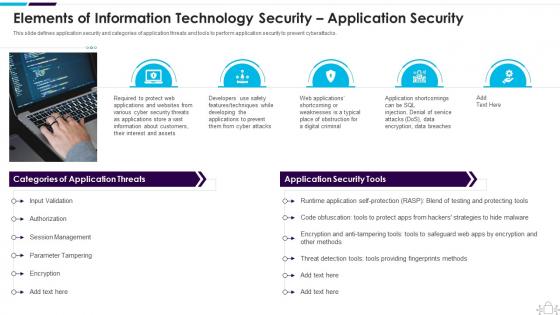 Elements Of Information Technology Security Application Security Information Technology Security
Elements Of Information Technology Security Application Security Information Technology SecurityThis slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. Increase audience engagement and knowledge by dispensing information using Elements Of Information Technology Security Application Security Information Technology Security. This template helps you present information on five stages. You can also present information on Session Management, Parameter Tampering, Authorization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.