Powerpoint Templates and Google slides for Attacking
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Working Of Phishing Training Programs Phishing Attacks And Strategies
Working Of Phishing Training Programs Phishing Attacks And StrategiesThis slide demonstrates the working of phishing training programs for organizations. These include start with employee training, make fictitious phishing campaigns, reinforce the phishing awareness training and track progress and upgrade.Increase audience engagement and knowledge by dispensing information using Working Of Phishing Training Programs Phishing Attacks And Strategies. This template helps you present information on four stages. You can also present information on Employee Training, Phishing Campaigns, Awareness Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Working Of Watering Hole Phishing Attack Phishing Attacks And Strategies
Working Of Watering Hole Phishing Attack Phishing Attacks And StrategiesThis slide represents the working process of watering hole phishing attacks. The purpose of this slide is to illustrate the flow diagram of watering hole phishing scams. The key points include research and identification, analysis, preparation and execution.Introducing Working Of Watering Hole Phishing Attack Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Watering Hole Cyberattack, Employ Exploit, Subdomain Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
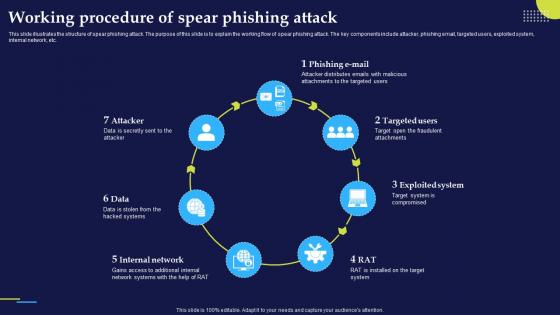 Working Procedure Of Spear Phishing Attack Phishing Attacks And Strategies
Working Procedure Of Spear Phishing Attack Phishing Attacks And StrategiesThis slide illustrates the structure of spear phishing attack. The purpose of this slide is to explain the working flow of spear phishing attack. The key components include attacker, phishing email, targeted users, exploited system, internal network, etc.Increase audience engagement and knowledge by dispensing information using Working Procedure Of Spear Phishing Attack Phishing Attacks And Strategies. This template helps you present information on seven stages. You can also present information on Attacker Distributes, Attachments Targeted, Fraudulent Attachments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Working Process Of Cyber Phishing Attacks Phishing Attacks And Strategies
Working Process Of Cyber Phishing Attacks Phishing Attacks And StrategiesThis slide talks about the implementation and working of phishing attacks. The purpose of this slide is to explain how are cyber phishing scams conducted. The components include hacker, phishing mail, target, phishing website and original website.Introducing Working Process Of Cyber Phishing Attacks Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information Website, Hacker Access Private, Credentials Victim, using this template. Grab it now to reap its full benefits.
-
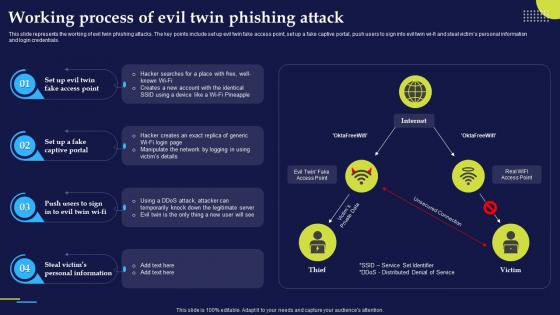 Working Process Of Evil Twin Phishing Attack Phishing Attacks And Strategies
Working Process Of Evil Twin Phishing Attack Phishing Attacks And StrategiesThis slide represents the working of evil twin phishing attacks. The key points include set up evil twin fake access point, set up a fake captive portal, push users to sign into evil twin wi fi and steal victims personal information and login credentials.Deliver an outstanding presentation on the topic using this Working Process Of Evil Twin Phishing Attack Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Personal Information, Captive Portal, Manipulate Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Measures For Successful Phishing Awareness Phishing Attacks And Strategies
Measures For Successful Phishing Awareness Phishing Attacks And StrategiesThis slide talks about the measures for successful phishing awareness campaign. These include recognize phish, train staff while keeping their individual needs in mind, action oriented employee engagement, plan constant training sessions, etc.Increase audience engagement and knowledge by dispensing information using Measures For Successful Phishing Awareness Phishing Attacks And Strategies. This template helps you present information on six stages. You can also present information on Employee Engagement, Interested Awareness Training, Training Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Types Social Engineering Attacks In Powerpoint And Google Slides Cpb
Types Social Engineering Attacks In Powerpoint And Google Slides CpbPresenting our Types Social Engineering Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Types Social Engineering Attacks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 High Level Builder Base Attacks In Powerpoint And Google Slides Cpb
High Level Builder Base Attacks In Powerpoint And Google Slides CpbPresenting our High Level Builder Base Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on High Level Builder Base Attacks. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Data Breach Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Breach Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Data Breach is a simple yet powerful visual representation of the risks associated with data security. It is perfect for presentations, reports, and other documents to help illustrate the dangers of data breaches. Its minimalistic design ensures it wont take away from the overall message.
-
 Data Breach Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Breach Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Data Breach is a simple yet powerful visual representation of the risks associated with data security. It is perfect for presentations, reports, and other documents to help illustrate the dangers of data breaches. Its minimalistic design ensures it wont take away from the overall message.
-
 Order Stages Attacker Methodology In Powerpoint And Google Slides Cpb
Order Stages Attacker Methodology In Powerpoint And Google Slides CpbPresenting Order Stages Attacker Methodology In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Order Stages Attacker Methodology. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Eavesdropping Attack Cybersecurity Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Eavesdropping Attack Cybersecurity Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon depicts an Eavesdropping Attack, a malicious act of intercepting private communications. It is a great visual aid for presentations on cyber security and data privacy.
-
 Eavesdropping Attack Cybersecurity Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Eavesdropping Attack Cybersecurity Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone PowerPoint icon depicts an eavesdropping attack, a malicious attempt to intercept and view confidential information. It is a simple yet powerful visual representation of a real-world security threat. Ideal for presentations on cyber security and data protection.
-
 Eavesdropping Attack Privacy Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Eavesdropping Attack Privacy Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon depicts an Eavesdropping Attack, a malicious act of intercepting private communications. It is a great visual aid for presentations on cyber security and data privacy.
-
 Eavesdropping Attack Privacy Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Eavesdropping Attack Privacy Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone PowerPoint icon depicts an eavesdropping attack, a malicious attempt to intercept and view confidential information. It is a simple yet powerful visual representation of a real-world security threat. Ideal for presentations on cyber security and data protection.
-
 International Cyber Attacks In Powerpoint And Google Slides Cpb
International Cyber Attacks In Powerpoint And Google Slides CpbPresenting International Cyber Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase Three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like International Cyber Attacks. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Attacks Banking Industry In Powerpoint And Google Slides Cpb
Cyber Attacks Banking Industry In Powerpoint And Google Slides CpbPresenting our Cyber Attacks Banking Industry In Powerpoint And Google Slides Cpb. PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Cyber Attacks Banking Industry. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Adopt Cyber Security Data Policies Cyber Attack Risks Mitigation
Adopt Cyber Security Data Policies Cyber Attack Risks MitigationThe following slide highlights various cyber security policies to manage data control and breach. It includes elements such as network security, data, workstations, remote access etc. Introducing Adopt Cyber Security Data Policies Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Network Security Policies, Data Security Policies, Workstation Policies, using this template. Grab it now to reap its full benefits.
-
 Adopting Strategies By Cyber Attack Type Cyber Attack Risks Mitigation
Adopting Strategies By Cyber Attack Type Cyber Attack Risks MitigationThe following slide depicts the various strategies to manage data control and breach. It includes elements such as attrition, malware, hacking, social tactic, improper usage, train and educate employees, automate identification, data management etc. Present the topic in a bit more detail with this Adopting Strategies By Cyber Attack Type Cyber Attack Risks Mitigation. Use it as a tool for discussion and navigation on Educate Employees, Data Management, Automate Attack Identification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
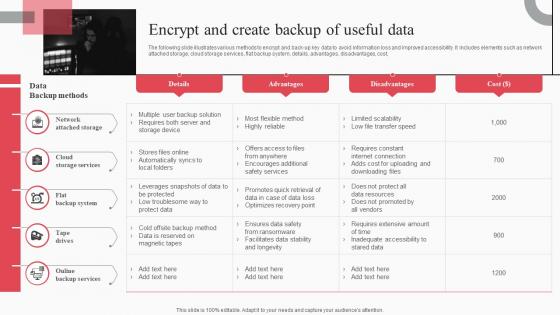 Encrypt And Create Backup Of Useful Data Cyber Attack Risks Mitigation
Encrypt And Create Backup Of Useful Data Cyber Attack Risks MitigationThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Cyber Attack Risks Mitigation. Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Cyber Security Policies And Practices Cyber Attack Risks Mitigation
Impact Of Cyber Security Policies And Practices Cyber Attack Risks MitigationThe following slide focuses on drafting cyber security policies to manage data control and breach. It mainly includes elements such as impact of existing cyber safety policies, mitigation actions, etc. Present the topic in a bit more detail with this Impact Of Cyber Security Policies And Practices Cyber Attack Risks Mitigation. Use it as a tool for discussion and navigation on Inadequate Security Guidelines, Inappropriate Privacy Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation
Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks MitigationThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti virus, preventing to open suspicious emails, keeping systems up to date etc. Introducing Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Opening Suspicious Emails, Keep Systems Up To Date, Leverage Firewalls, using this template. Grab it now to reap its full benefits.
-
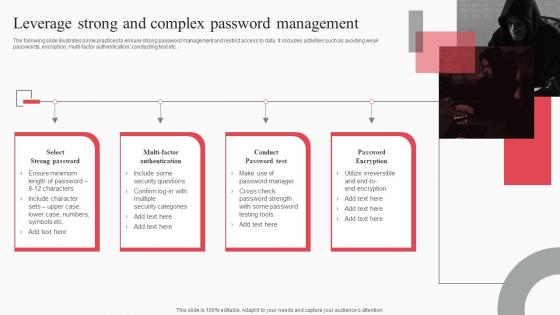 Leverage Strong And Complex Password Management Cyber Attack Risks Mitigation
Leverage Strong And Complex Password Management Cyber Attack Risks MitigationThe following slide illustrates some practices to ensure strong password management and restrict access to data. It includes activities such as avoiding weak passwords, encryption, multi-factor authentication, conducting test etc. Increase audience engagement and knowledge by dispensing information using Leverage Strong And Complex Password Management Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Select Strong Password, Multi Factor Authentication, Conduct Password Test using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation
Monitor And Assess Vendor Risk Management Cyber Attack Risks MitigationThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Introducing Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Web Application Security, Infrastructure Security, Vendor Management, using this template. Grab it now to reap its full benefits.
-
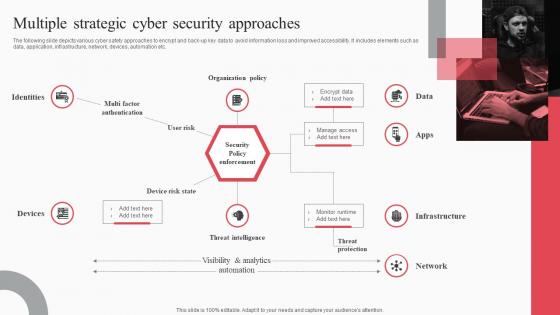 Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation
Multiple Strategic Cyber Security Approaches Cyber Attack Risks MitigationThe following slide depicts various cyber safety approaches to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as data, application, infrastructure, network, devices, automation etc. Increase audience engagement and knowledge by dispensing information using Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation. This template helps you present information on one stage. You can also present information on Identities, Organization Policy, Threat Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Organize Cyber Security Training For Employees Regularly Cyber Attack Risks Mitigation
Organize Cyber Security Training For Employees Regularly Cyber Attack Risks MitigationThe following slide depicts the staff cyber security training plan to educate them regarding technology threats and practices. It mainly includes elements such as topics to be covered, target audience, trainer name, mode, proposed date, timings etc. Introducing Organize Cyber Security Training For Employees Regularly Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Document Management, Response Process, Social Media Policy, using this template. Grab it now to reap its full benefits.
-
 Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks Mitigation
Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks MitigationThe following slide showcases passive, active and offensive cyber safety techniques to ensure customer data safety. It includes elements such as inspecting vulnerabilities, penetration testing, deception technology, threat hunting etc. Increase audience engagement and knowledge by dispensing information using Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on three stages. You can also present information on Passive Safety, Active Safety, Offensive Safety using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
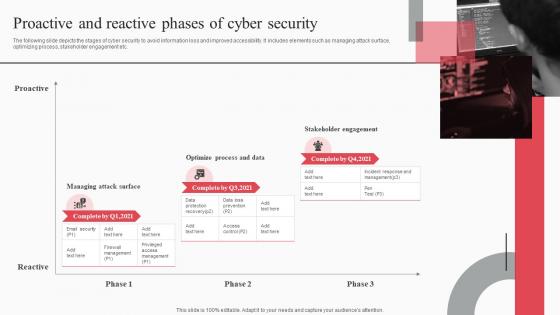 Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks Mitigation
Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks MitigationThe following slide depicts the stages of cyber security to avoid information loss and improved accessibility. It includes elements such as managing attack surface, optimizing process, stakeholder engagement etc. Introducing Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Proactive, Managing Attack Surface, Optimize Process, Stakeholder Engagement, using this template. Grab it now to reap its full benefits.
-
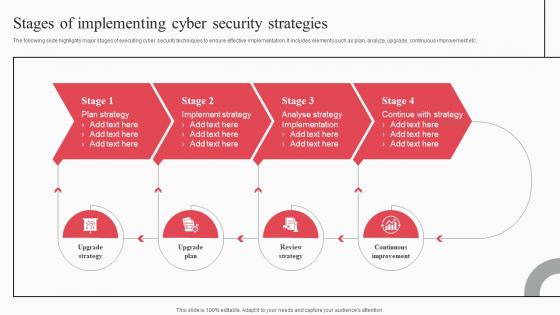 Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation
Stages Of Implementing Cyber Security Strategies Cyber Attack Risks MitigationThe following slide highlights major stages of executing cyber security techniques to ensure effective implementation. It includes elements such as plan, analyze, upgrade, continuous improvement etc. Increase audience engagement and knowledge by dispensing information using Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Plan Strategy, Implement Strategy, Analyse Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
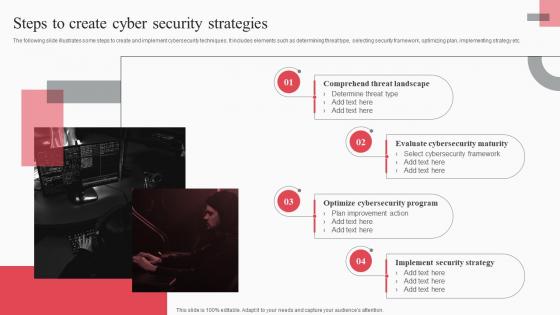 Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation
Steps To Create Cyber Security Strategies Cyber Attack Risks MitigationThe following slide illustrates some steps to create and implement cybersecurity techniques. It includes elements such as determining threat type, selecting security framework, optimizing plan, implementing strategy etc. Introducing Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Comprehend Threat Landscape, Evaluate Cybersecurity Maturity, Optimize Cybersecurity Program, using this template. Grab it now to reap its full benefits.
-
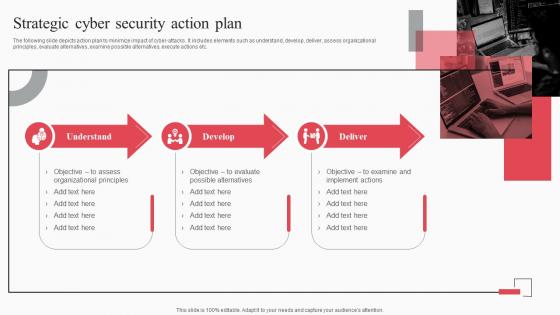 Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation
Strategic Cyber Security Action Plan Cyber Attack Risks MitigationThe following slide depicts action plan to minimize impact of cyber attacks. It includes elements such as understand, develop, deliver, assess organizational principles, evaluate alternatives, examine possible alternatives, execute actions etc. Increase audience engagement and knowledge by dispensing information using Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation. This template helps you present information on three stages. You can also present information on Understand, Develop, Deliver, Organizational Principles using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
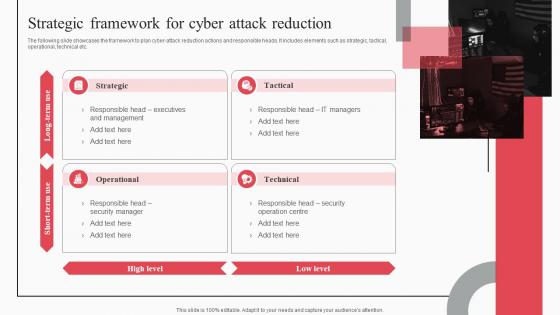 Strategic Framework For Cyber Attack Reduction Cyber Attack Risks Mitigation
Strategic Framework For Cyber Attack Reduction Cyber Attack Risks MitigationThe following slide showcases the framework to plan cyber-attack reduction actions and responsible heads. It includes elements such as strategic, tactical, operational, technical etc. Introducing Strategic Framework For Cyber Attack Reduction Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strategic, Tactical, Operational, Technical, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt Slides
Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt SlidesIntroducing Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt Slides to increase your presentation threshold. Encompassed with fifteen stages, this template is a great option to educate and entice your audience. Dispence information on Security Strategies, Strategic Framework, Password Management, using this template. Grab it now to reap its full benefits.
-
 Four Phases Social Engineering Attack Cycle In Powerpoint And Google Slides Cpb
Four Phases Social Engineering Attack Cycle In Powerpoint And Google Slides CpbPresenting Four Phases Social Engineering Attack Cycle In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Four Phases Social Engineering Attack Cycle. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Banks Cyber Attacks In Powerpoint And Google Slides Cpb
Banks Cyber Attacks In Powerpoint And Google Slides CpbPresenting Banks Cyber Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Banks Cyber Attacks. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
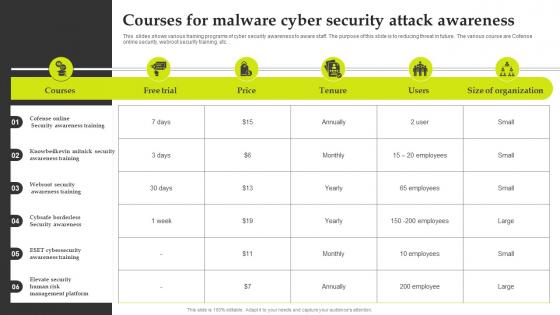 Courses For Malware Cyber Security Attack Awareness
Courses For Malware Cyber Security Attack AwarenessThis slides shows various training programs of cyber security awareness to aware staff. The purpose of this slide is to reducing threat in future. The various course are Cofense online security, webroot security training, etc.Introducing our Courses For Malware Cyber Security Attack Awareness set of slides. The topics discussed in these slides are Awareness Training, Security Awareness Training, Security Awareness. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
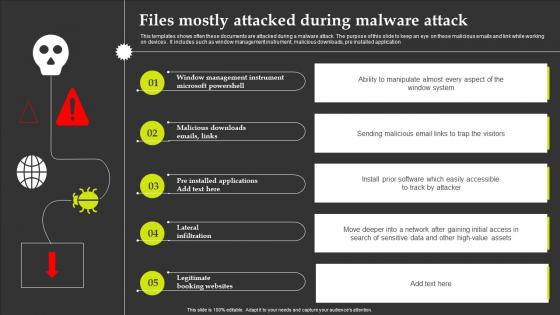 Files Mostly Attacked During Malware Attack
Files Mostly Attacked During Malware AttackThis templates shows often these documents are attacked during a malware attack. The purpose of this slide to keep an eye on these malicious emails and link while working on devices . It includes such as window management instrument, malicious downloads, pre installed application.Presenting our well structured Files Mostly Attacked During Malware Attack. The topics discussed in this slide are Management Instrument, Lateral Infiltration, Legitimate Booking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Malware Attack Icon Corrupting Devices Files
Malware Attack Icon Corrupting Devices FilesPresenting our well structured Malware Attack Icon Corrupting Devices Files. The topics discussed in this slide are Malware Attack Icon, Corrupting Devices Files. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Malware Attack Icon Sending Malicious Emails
Malware Attack Icon Sending Malicious EmailsIntroducing our Malware Attack Icon Sending Malicious Emails set of slides. The topics discussed in these slides are Malware Attack Icon, Sending Malicious Emails. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Malware Attack Icon To Prevent Threat
Malware Attack Icon To Prevent ThreatPresenting our well structured Malware Attack Icon To Prevent Threat. The topics discussed in this slide are Malware Attack Icon, Prevent Threat. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Malware Device Icon To Prevent Form Malicious Attacks
Malware Device Icon To Prevent Form Malicious AttacksPresenting our well structured Malware Device Icon To Prevent Form Malicious Attacks. The topics discussed in this slide are Malware Device Icon, Prevent Form Malicious Attacks. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
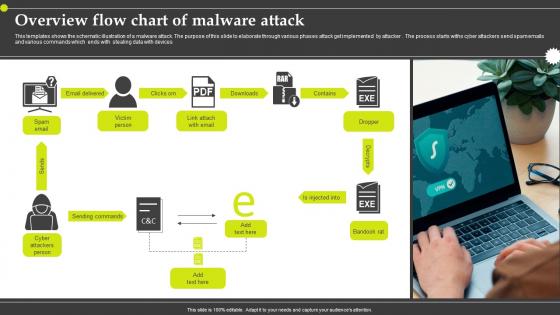 Overview Flow Chart Of Malware Attack
Overview Flow Chart Of Malware AttackThis templates shows the schematic illustration of a malware attack. The purpose of this slide to elaborate through various phases attack get implemented by attacker. The process starts withs cyber attackers send spam emails and various commands which ends with stealing data with devices.Presenting our well structured Overview Flow Chart Of Malware Attack. The topics discussed in this slide are Overview Flow Chart, Malware Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
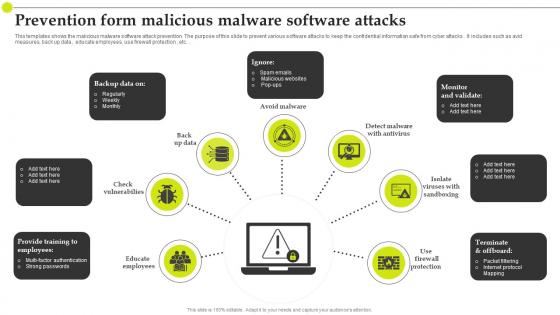 Prevention Form Malicious Malware Software Attacks
Prevention Form Malicious Malware Software AttacksThis templates shows the malicious malware software attack prevention. The purpose of this slide to prevent various software attacks to keep the confidential information safe from cyber attacks . It includes such as avid measures, back up data , educate employees, use firewall protection , etc.Introducing our premium set of slides with Prevention Form Malicious Malware Software Attacks. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Packet Filtering, Internet Protocol, Educate Employees. So download instantly and tailor it with your information.
-
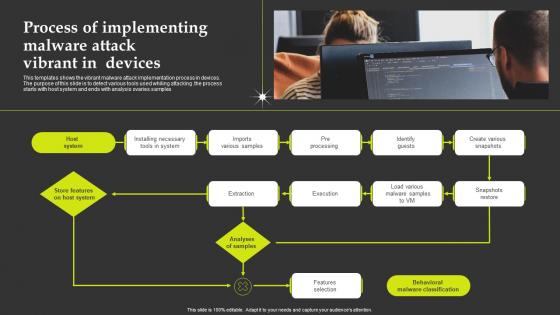 Process Of Implementing Malware Attack Vibrant In Devices
Process Of Implementing Malware Attack Vibrant In DevicesThis templates shows the vibrant malware attack implementation process in devices. The purpose of this slide is to detect various tools used whiling attacking .the process starts with host system and ends with analysis ovaries samples.Presenting our set of slides with Process Of Implementing Malware Attack Vibrant In Devices. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Installing Necessary, Various Snapshots, Snapshots Restore.
-
 Reason For Malware Attack On Target Audience
Reason For Malware Attack On Target AudienceThis templates shows the reason for the malware attack on the target audience. The purpose of this slide to ensure the reason why attacker easily access the software . It includes various challenges such as weak passwords, lack of encryption, backdoors, etc.Presenting our well structured Reason For Malware Attack On Target Audience. The topics discussed in this slide are Avoid Connecting, Passwords Irrespective, Technical Knowledge. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
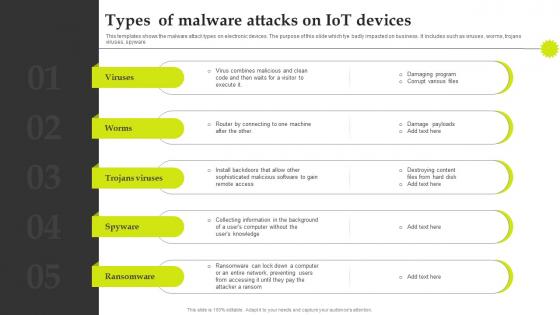 Types Of Malware Attacks On Iot Devices
Types Of Malware Attacks On Iot DevicesThis templates shows the malware attack types on electronic devices. The purpose of this slide which tye badly impacted on business . It includes such as viruses , worms, trojans viruses, spyware.Introducing our premium set of slides with Types Of Malware Attacks On Iot Devices. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Sophisticated Malicious, Router Connecting, Damaging Program. So download instantly and tailor it with your information.
-
 Various Stages Of Web Malware Attack
Various Stages Of Web Malware AttackThis templates shows the different phases of a web malware attack. The purpose of this slide to give brief pictures regarding approximately how much sites are hacked and recovered . The phase starts withs entry point and ends with execution.Presenting our well structured Various Stages Of Web Malware Attack. The topics discussed in this slide are Flex Techniques, Personal Information, Credential Banking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
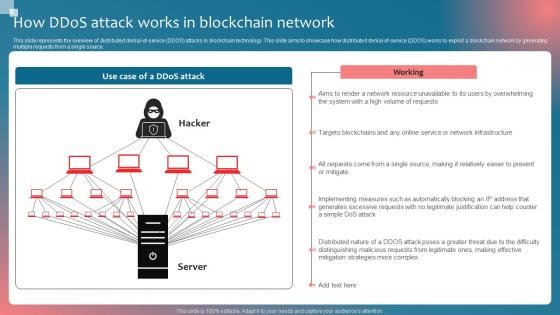 How Ddos Attack Works In Implementing Blockchain Security Solutions
How Ddos Attack Works In Implementing Blockchain Security SolutionsThis slide represents the overview of distributed denialofservice DDOS attacks in blockchain technology. This slide aims to showcase how distributed denialofservice DDOS works to exploit a blockchain network by generating multiple requests from a single source.Present the topic in a bit more detail with this How Ddos Attack Works In Implementing Blockchain Security Solutions. Use it as a tool for discussion and navigation on Network Resource Unavailable, Mitigation Strategies, Distinguishing Malicious. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
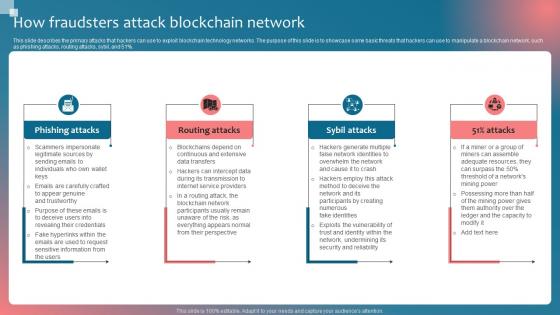 How Fraudsters Attack Implementing Blockchain Security Solutions
How Fraudsters Attack Implementing Blockchain Security SolutionsThis slide describes the primary attacks that hackers can use to exploit blockchain technology networks. The purpose of this slide is to showcase some basic threats that hackers can use to manipulate a blockchain network, such as phishing attacks, routing attacks, sybil, and 51 precent.Increase audience engagement and knowledge by dispensing information using How Fraudsters Attack Implementing Blockchain Security Solutions. This template helps you present information on four stages. You can also present information on Phishing Attacks, Routing Attacks, Sybil Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
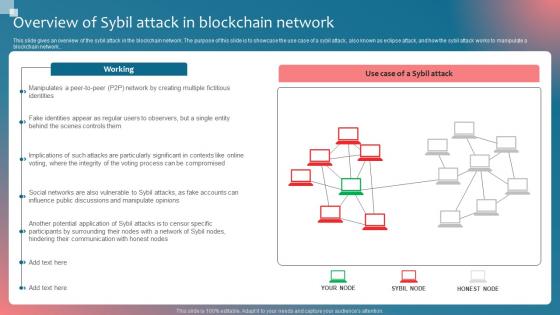 Overview Of Sybil Attack In Implementing Blockchain Security Solutions
Overview Of Sybil Attack In Implementing Blockchain Security SolutionsThis slide gives an overview of the sybil attack in the blockchain network. The purpose of this slide is to showcase the use case of a sybil attack, also known as eclipse attack, and how the sybil attack works to manipulate a blockchain network.Deliver an outstanding presentation on the topic using this Overview Of Sybil Attack In Implementing Blockchain Security Solutions. Dispense information and present a thorough explanation of Hindering Communication, Potential Application, Fake Identities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icon For Minimizing Digital Risk And Cyber Attacks
Icon For Minimizing Digital Risk And Cyber AttacksIntroducing our Icon For Minimizing Digital Risk And Cyber Attacks set of slides. The topics discussed in these slides are Minimizing Digital Risk Cyber Attacks This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Email Based Phishing Attacks Prevention IT Illustration
Email Based Phishing Attacks Prevention IT IllustrationThis colored PowerPoint Illustration provides a comprehensive overview of email-based phishing attacks and how to prevent them. It covers topics such as identifying suspicious emails, understanding phishing tactics, and implementing security measures.
-
 Hacker attacking social media websites
Hacker attacking social media websitesPresenting this set of slides with name Hacker Attacking Social Media Websites. The topics discussed in these slides are Hacker, Network, Computer. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
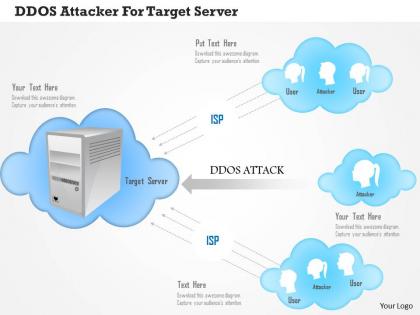 Ddos attacker for target server ppt slides
Ddos attacker for target server ppt slidesPresenting ddos attacker for target server ppt slides. This is a DDOS attacker for target server ppt slides. This is a four stage process. The stages in this process are servers, cloud computing.
-
 Protection from cyber attacks ppt slide examples
Protection from cyber attacks ppt slide examplesPresenting protection from cyber attacks ppt slides examples PPT slide. The tension-free download is possible. Once downloaded, the presentation can be modified to any format like JPG, JPEG, PDF, etc. It’s also compatible with multiple software and Google Slides. The provided executive summary PPT presentation template can easily be used solely or as part of your pre-built presentation. Be happy to customize and personalize the presentation with company specifications.There is no hassle when any facts, figures or text is to be included or excluded in the presentation. Picture quality compatible with widescreen exposure.
-
 Air force attack phase icon
Air force attack phase iconPresenting air force attack phase icon. This is a air force attack phase icon. This is a two stage process. The stages in this process are aerospace force, air army, air force.
-
 Market challenger strategies market follower strategies attack strategies
Market challenger strategies market follower strategies attack strategiesPresenting this set of slides with name - Market Challenger Strategies Market Follower Strategies Attack Strategies. This is an editable one stages graphic that deals with topics like Market Challenger Strategies, Market Follower Strategies, Attack Strategies to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Broad marketing strategies strategic objectives opponents attack strategies
Broad marketing strategies strategic objectives opponents attack strategiesPresenting this set of slides with name - Broad Marketing Strategies Strategic Objectives Opponents Attack Strategies. This is an editable six graphic that deals with topics like Broad Marketing Strategies, Strategic Objectives Opponents, Attack Strategies to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Specific attack strategies customer size specialist fastest source
Specific attack strategies customer size specialist fastest sourcePresenting this set of slides with name - Specific Attack Strategies Customer Size Specialist Fastest Source. This is an editable five stages graphic that deals with topics like Specific Attack Strategies, Customer Size Specialist, Fastest Source to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
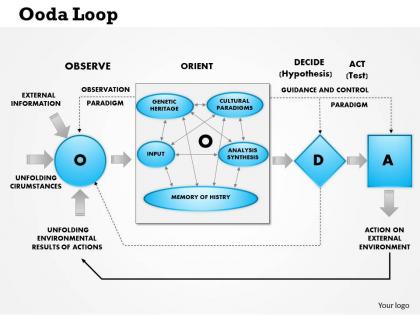 0514 ooda loop observe orient decide attack powerpoint presentation
0514 ooda loop observe orient decide attack powerpoint presentationWe are proud to present our 0514 ooda loop observe orient decide attack powerpoint presentation. OODA Loop model outlines a four point decision loop that supports quick, effective and proactive decision making. You continue to cycle through the OODA Loop by observing the results of your actions.



