Powerpoint Templates and Google slides for Based Attacks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
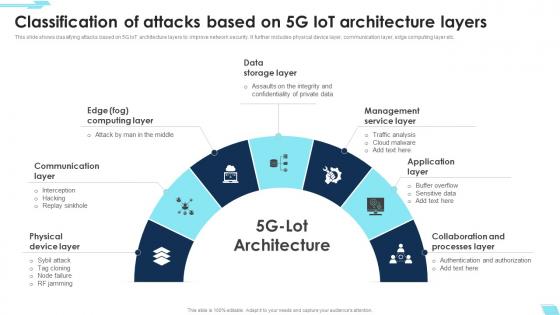 Classification Of Attacks Based On 5g Iot Architecture Layers
Classification Of Attacks Based On 5g Iot Architecture LayersThis Slide Shows Classifying Attacks Based On 5G Iot Architecture Layers To Improve Network Security. It Further Includes Physical Device Layer, Communication Layer, Edge Computing Layer Etc. Presenting Our Set Of Slides With Classification Of Attacks Based On 5g Iot Architecture Layers. This Exhibits Information On Seven Stages Of The Process. This Is An Easy To Edit And Innovatively Designed Powerpoint Template. So Download Immediately And Highlight Information On Data Storage Layer, Management Service Layer, Collaboration And Processes Layer.
-
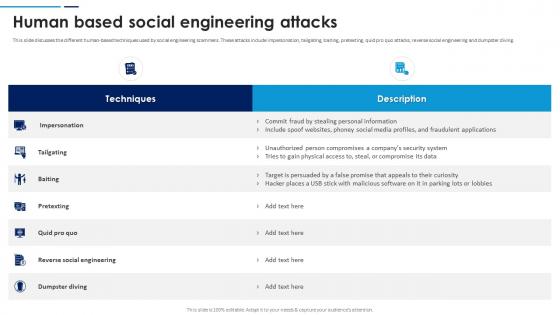 Social Engineering Attacks Prevention Human Based Social Engineering Attacks
Social Engineering Attacks Prevention Human Based Social Engineering AttacksThis slide discusses the different human-based techniques used by social engineering scammers. These attacks include impersonation, tailgating, baiting, pretexting, quid pro quo attacks, reverse social engineering and dumpster diving. Present the topic in a bit more detail with this Social Engineering Attacks Prevention Human Based Social Engineering Attacks. Use it as a tool for discussion and navigation on Reverse Social Engineering, Dumpster Diving, Social Engineering Attacks, Fraudulent Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
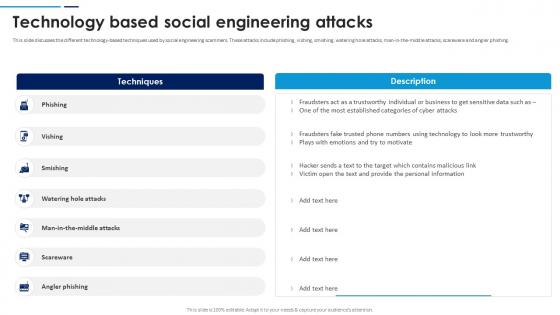 Social Engineering Attacks Prevention Technology Based Social Engineering Attacks
Social Engineering Attacks Prevention Technology Based Social Engineering AttacksThis slide discusses the different technology-based techniques used by social engineering scammers. These attacks include phishing, vishing, smishing, watering hole attacks, man-in-the-middle attacks, scareware and angler phishing. Deliver an outstanding presentation on the topic using this Social Engineering Attacks Prevention Technology Based Social Engineering Attacks. Dispense information and present a thorough explanation of Watering Hole Attacks, Social Engineering Attacks, Angler Phishing, Fraudsters Fake Trusted Phone using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Volume Based Dos Attacks In Powerpoint And Google Slides Cpb
Volume Based Dos Attacks In Powerpoint And Google Slides CpbPresenting Volume Based Dos Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase Three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Volume Based Dos Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Volume Based DDOS Attacks In Powerpoint And Google Slides Cpb
Volume Based DDOS Attacks In Powerpoint And Google Slides CpbPresenting Volume Based DDOS Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Volume Based DDOS Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
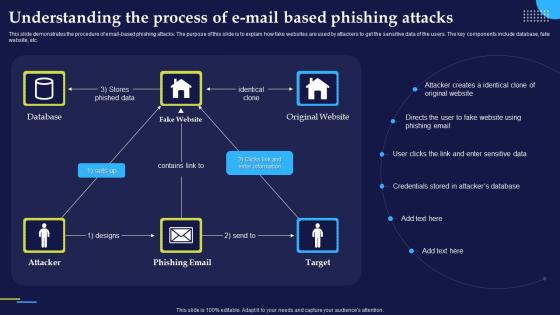 Understanding The Process Of E Mail Based Phishing Attacks And Strategies
Understanding The Process Of E Mail Based Phishing Attacks And StrategiesThis slide demonstrates the procedure of email based phishing attacks. The purpose of this slide is to explain how fake websites are used by attackers to get the sensitive data of the users. The key components include database, fake website, etc.Present the topic in a bit more detail with this Understanding The Process Of E Mail Based Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Enter Sensitive, Credentials Stored, Attacker Creates. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 High Level Builder Base Attacks In Powerpoint And Google Slides Cpb
High Level Builder Base Attacks In Powerpoint And Google Slides CpbPresenting our High Level Builder Base Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on High Level Builder Base Attacks. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Email Based Phishing Attacks Prevention IT Illustration
Email Based Phishing Attacks Prevention IT IllustrationThis colored PowerPoint Illustration provides a comprehensive overview of email-based phishing attacks and how to prevent them. It covers topics such as identifying suspicious emails, understanding phishing tactics, and implementing security measures.
-
 Hacker stealing backend data base through cyber attacks
Hacker stealing backend data base through cyber attacksIntroducing our premium set of slides with Web Portal For Online Educational Training. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Web Portal For Online Educational Training. So download instantly and tailor it with your information.
-
 Social Engineering Methods And Mitigation Understanding The Process Of E Mail Based Phishing Attacks
Social Engineering Methods And Mitigation Understanding The Process Of E Mail Based Phishing AttacksThis slide demonstrates the procedure of email-based phishing attacks. The purpose of this slide is to explain how fake websites are used by attackers to get the sensitive data of the users. The key components include database, fake website, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Understanding The Process Of E Mail Based Phishing Attacks. Dispense information and present a thorough explanation of Phishing Attacks, Fake Website, Email Based Phishing Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.

