Powerpoint Templates and Google slides for Computer Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
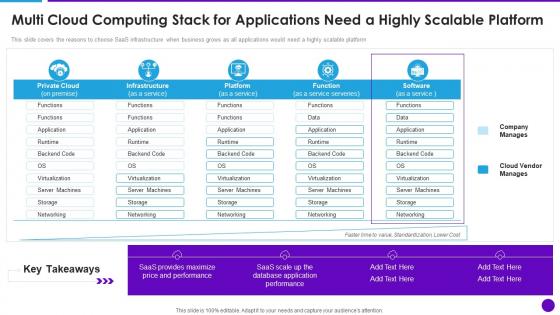 Cloud Architecture And Security Multi Cloud Computing Stack For Applications Need A Highly Scalable
Cloud Architecture And Security Multi Cloud Computing Stack For Applications Need A Highly ScalableThis slide covers the reasons to choose SaaS infrastructure when business grows as all applications would need a highly scalable platform. Present the topic in a bit more detail with this Cloud Architecture And Security Multi Cloud Computing Stack For Applications Need A Highly Scalable. Use it as a tool for discussion and navigation on Multi Cloud, Computing Stack, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Applications Of Confidential Computing Security Technology
Applications Of Confidential Computing Security TechnologyThe following slide contains the area of benefits where confidential computing is used to ensure data is secured and encrypted against malware attacks. Key uses are data protection, guard business process, collaboration and customer satisfaction. Presenting our set of slides with name Applications Of Confidential Computing Security Technology. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Guard Business Process, Collaboration, Customer Satisfaction.
-
 Cloud Computing Security Technology Framework
Cloud Computing Security Technology FrameworkThis slide illustrates a strategic framework for cloud security technology which is used in various aspects of data and network protection. Key components are disaster recovery, governance, monitoring, user access management, data security etc. Introducing our premium set of slides with Cloud Computing Security Technology Framework. Elucidate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Security, Network Security, Others, Monitoring, Governance. So download instantly and tailor it with your information.
-
 Cyber Security Strategy Icon Depicting Computer Protection
Cyber Security Strategy Icon Depicting Computer ProtectionIntroducing our premium set of slides with name Cyber Security Strategy Icon Depicting Computer Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security, Strategy Icon, Depicting Computer, Protection. So download instantly and tailor it with your information.
-
 Cloud Computing Security Architecture Icon
Cloud Computing Security Architecture IconPresenting our set of slides with Cloud Computing Security Architecture Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Computing, Security Architecture Icon
-
 Icon Showcasing Application Of Computer Vision In Digital Security
Icon Showcasing Application Of Computer Vision In Digital SecurityIntroducing our Icon Showcasing Application Of Computer Vision In Digital Security set of slides. The topics discussed in these slides are Application, Digital Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Factors For Cloud Computing Security Audit
Factors For Cloud Computing Security AuditThe slide highlights the factors to be considered while auditing the cloud services for data protection. Various factors considered are transparency, encryption and colocation. Introducing our premium set of slides with factors for Factors For Cloud Computing Security Audit. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Transparency, Encryption, Colocation . So download instantly and tailor it with your information.
-
 Agenda Deploying Computer Security Incident Management
Agenda Deploying Computer Security Incident ManagementIntroducing Agenda Deploying Computer Security Incident Management to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Agenda, using this template. Grab it now to reap its full benefits.
-
 B98 Table Of Contents For Deploying Computer Security Incident Management
B98 Table Of Contents For Deploying Computer Security Incident ManagementPresent the topic in a bit more detail with this B98 Table Of Contents For Deploying Computer Security Incident Management . Use it as a tool for discussion and navigation on Best Practices, Cyber Security, Incident Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
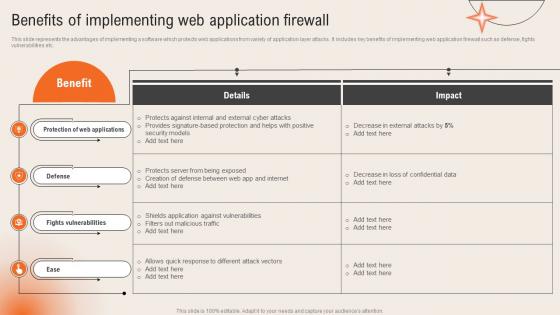 Benefits Of Implementing Web Application Firewall Deploying Computer Security Incident
Benefits Of Implementing Web Application Firewall Deploying Computer Security IncidentThis slide represents the advantages of implementing a software which protects web applications from variety of application layer attacks. It includes key benefits of implementing web application firewall such as defense, fights vulnerabilities etc.Present the topic in a bit more detail with this Benefits Of Implementing Web Application Firewall Deploying Computer Security Incident. Use it as a tool for discussion and navigation on Provides Signature, Protects Against, Fights Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Best Practices For Cybersecurity Incident Management Deploying Computer Security Incident
Best Practices For Cybersecurity Incident Management Deploying Computer Security IncidentThis slide represents the best practices to be adopted by the organizations which aim to minimize impact of cyber security incidents on business operations and prevent them from happening again. It includes best practices such as create cyber incident management plan etc.Increase audience engagement and knowledge by dispensing information using Best Practices For Cybersecurity Incident Management Deploying Computer Security Incident. This template helps you present information on five stages. You can also present information on Incident Management, Management Process, Responsibilities Members using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
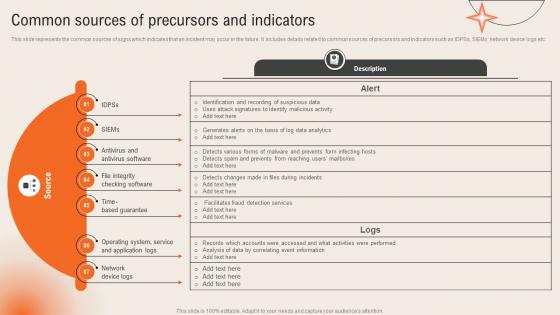 Common Sources Of Precursors And Indicators Deploying Computer Security Incident Management
Common Sources Of Precursors And Indicators Deploying Computer Security Incident ManagementThis slide represents the common sources of signs which indicates that an incident may occur in the future. It includes details related to common sources of precursors and indicators such as IDPSs, SIEMs, network device logs etc.Present the topic in a bit more detail with this Common Sources Of Precursors And Indicators Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Antivirus Software, Based Guarantee, Operating System. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
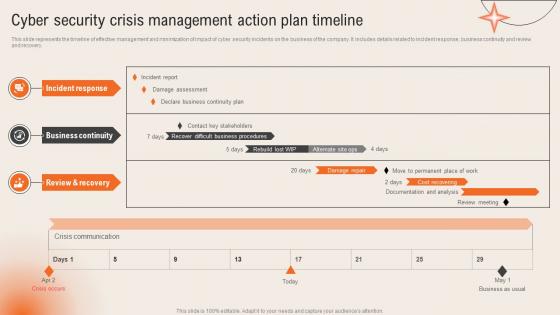 Cyber Security Crisis Management Action Plan Timeline Deploying Computer Security Incident Management
Cyber Security Crisis Management Action Plan Timeline Deploying Computer Security Incident ManagementThis slide represents the timeline of effective management and minimization of impact of cyber security incidents on the business of the company. It includes details related to incident response, business continuity and review and recovery.Present the topic in a bit more detail with this Cyber Security Crisis Management Action Plan Timeline Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Business Continuity, Incident Response, Review Recovery. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
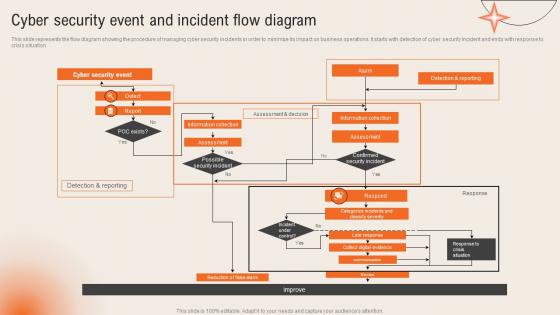 Cyber Security Event And Incident Flow Diagram Deploying Computer Security Incident Management
Cyber Security Event And Incident Flow Diagram Deploying Computer Security Incident ManagementThis slide represents the flow diagram showing the procedure of managing cyber security incidents in order to minimize its impact on business operations. It starts with detection of cyber security incident and ends with response to crisis situation.Present the topic in a bit more detail with this Cyber Security Event And Incident Flow Diagram Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Information Collection, Confirmed Security Incident, Categorize Incidents. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
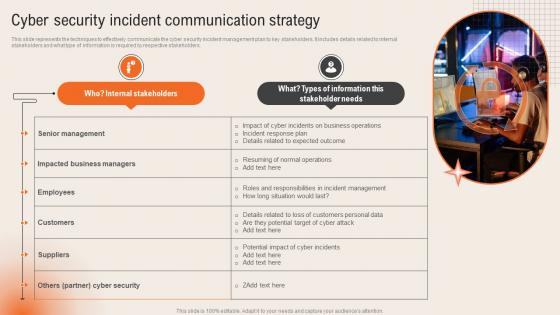 Cyber Security Incident Communication Strategy Deploying Computer Security Incident Management
Cyber Security Incident Communication Strategy Deploying Computer Security Incident ManagementThis slide represents the techniques to effectively communicate the cyber security incident management plan to key stakeholders. It includes details related to internal stakeholders and what type of information is required by respective stakeholders.Introducing Cyber Security Incident Communication Strategy Deploying Computer Security Incident Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Senior Management, Impacted Business, Incident Management, using this template. Grab it now to reap its full benefits.
-
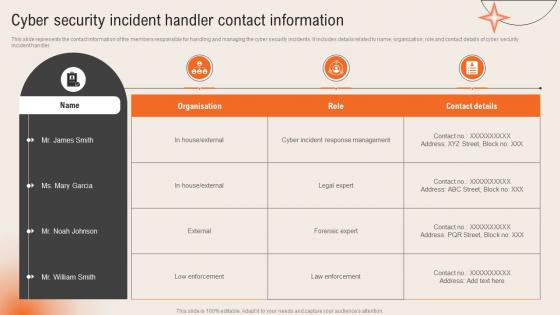 Cyber Security Incident Handler Contact Information Deploying Computer Security Incident Management
Cyber Security Incident Handler Contact Information Deploying Computer Security Incident ManagementThis slide represents the contact information of the members responsible for handling and managing the cyber security incidents. It includes details related to name, organization, role and contact details of cyber security incident handler.Present the topic in a bit more detail with this Cyber Security Incident Handler Contact Information Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Incident Response Management, Forensic Expert, Law Enforcement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
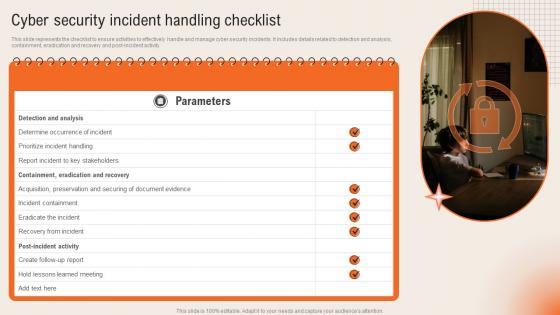 Cyber Security Incident Handling Checklist Deploying Computer Security Incident Management
Cyber Security Incident Handling Checklist Deploying Computer Security Incident ManagementThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity.Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Deploying Computer Security Incident Management. This template helps you present information on one stage. You can also present information on Containment Eradication, Acquisition Preservation, Incident Containment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
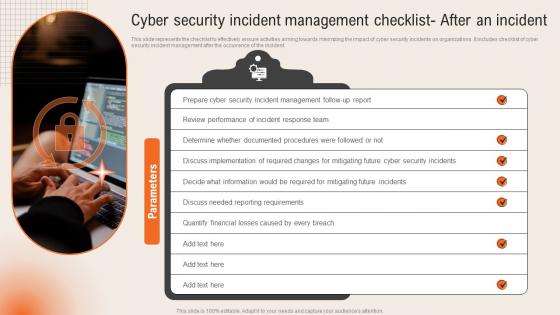 Cyber Security Incident Management Checklist After An Incident Deploying Computer Security
Cyber Security Incident Management Checklist After An Incident Deploying Computer SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management after the occurrence of the incident.Introducing Cyber Security Incident Management Checklist After An Incident Deploying Computer Security to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Incident Management, Reporting Requirements, Quantify Financial, using this template. Grab it now to reap its full benefits.
-
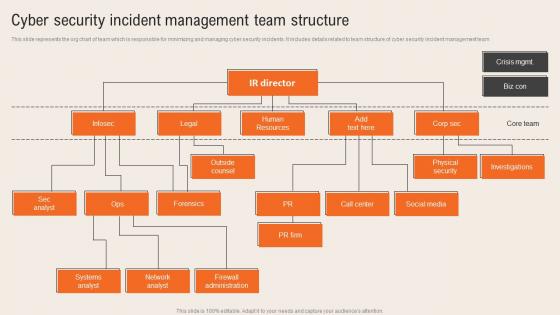 Cyber Security Incident Management Team Structure Deploying Computer Security Incident Management
Cyber Security Incident Management Team Structure Deploying Computer Security Incident ManagementThis slide represents the org chart of team which is responsible for minimizing and managing cyber security incidents. It includes details related to team structure of cyber security incident management team.Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Team Structure Deploying Computer Security Incident Management. This template helps you present information on five stages. You can also present information on Systems Analyst, Network Analyst, Firewall Administration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
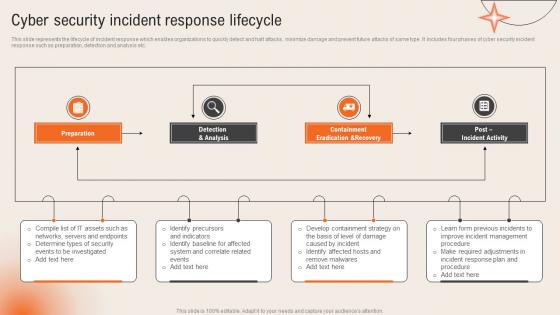 Cyber Security Incident Response Lifecycle Deploying Computer Security Incident Management
Cyber Security Incident Response Lifecycle Deploying Computer Security Incident ManagementThis slide represents the lifecycle of incident response which enables organizations to quickly detect and halt attacks, minimize damage and prevent future attacks of same type. It includes four phases of cyber security incident response such as preparation, detection and analysis etc.Introducing Cyber Security Incident Response Lifecycle Deploying Computer Security Incident Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Eradication Recovery, Post Incident Activity, Remove Malwares, using this template. Grab it now to reap its full benefits.
-
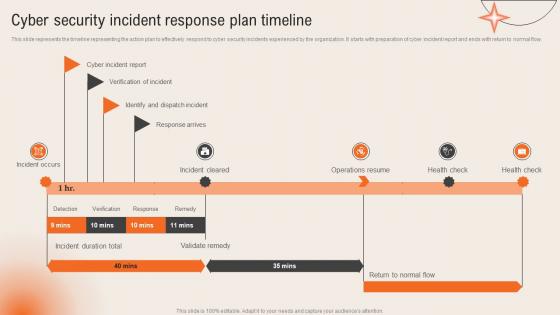 Cyber Security Incident Response Plan Timeline Deploying Computer Security Incident Management
Cyber Security Incident Response Plan Timeline Deploying Computer Security Incident ManagementThis slide represents the timeline representing the action plan to effectively respond to cyber security incidents experienced by the organization. It starts with preparation of cyber incident report and ends with return to normal flow.Present the topic in a bit more detail with this Cyber Security Incident Response Plan Timeline Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Cyber Incident, Verification Incident, Dispatch Incident. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
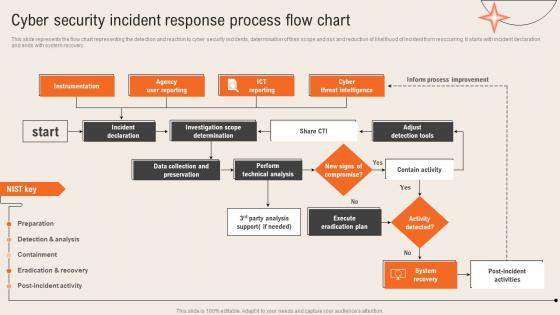 Cyber Security Incident Response Process Flow Chart Deploying Computer Security Incident Management
Cyber Security Incident Response Process Flow Chart Deploying Computer Security Incident ManagementThis slide represents the flow chart representing the detection and reaction to cyber security incidents, determination of their scope and risk and reduction of likelihood of incident from reoccurring. It starts with incident declaration and ends with system recovery.Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Response Process Flow Chart Deploying Computer Security Incident Management. This template helps you present information on Two stages. You can also present information on Agency Reporting, Investigation Scope Determination, Collection Preservation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
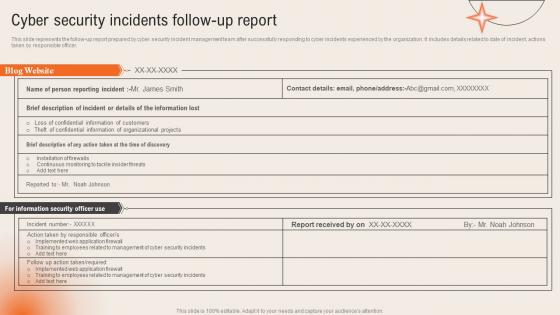 Cyber Security Incidents Follow Up Report Deploying Computer Security Incident Management
Cyber Security Incidents Follow Up Report Deploying Computer Security Incident ManagementThis slide represents the follow up report prepared by cyber security incident management team after successfully responding to cyber incidents experienced by the organization. It includes details related to date of incident, actions taken by responsible officer.Present the topic in a bit more detail with this Cyber Security Incidents Follow Up Report Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Confidential Information, Training Employees, Organizational Projects. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
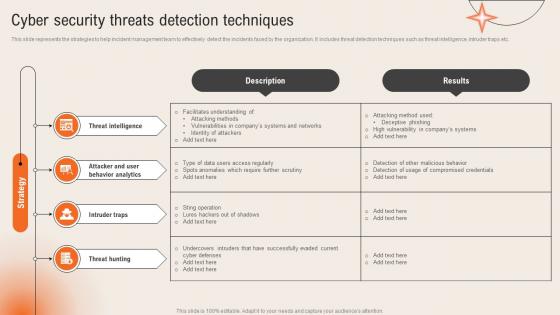 Cyber Security Threats Detection Techniques Deploying Computer Security Incident Management
Cyber Security Threats Detection Techniques Deploying Computer Security Incident ManagementThis slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc.Present the topic in a bit more detail with this Cyber Security Threats Detection Techniques Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Threat Intelligence, Access Regularly, Undercovers Intruders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
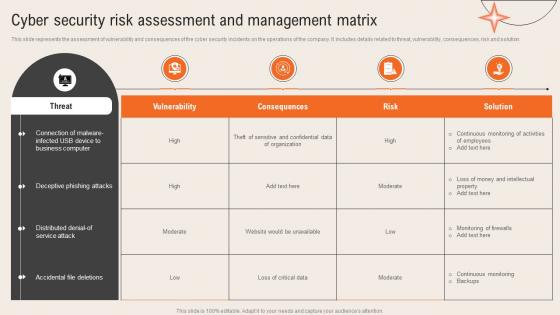 Deploying Computer Security Incident Cyber Security Risk Assessment And Management Matrix
Deploying Computer Security Incident Cyber Security Risk Assessment And Management MatrixThis slide represents the assessment of vulnerability and consequences of the cyber security incidents on the operations of the company. It includes details related to threat, vulnerability, consequences, risk and solution.Present the topic in a bit more detail with this Deploying Computer Security Incident Cyber Security Risk Assessment And Management Matrix. Use it as a tool for discussion and navigation on Deceptive Phishing, Business Computer, Accidental File Deletions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
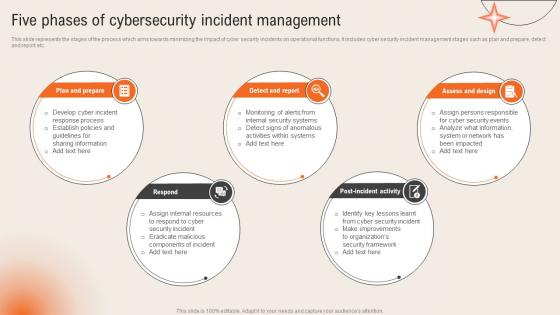 Five Phases Of Cybersecurity Incident Management Deploying Computer Security Incident Management
Five Phases Of Cybersecurity Incident Management Deploying Computer Security Incident ManagementThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc.Introducing Five Phases Of Cybersecurity Incident Management Deploying Computer Security Incident Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Sharing Information, Establish Policies, Response Process, using this template. Grab it now to reap its full benefits.
-
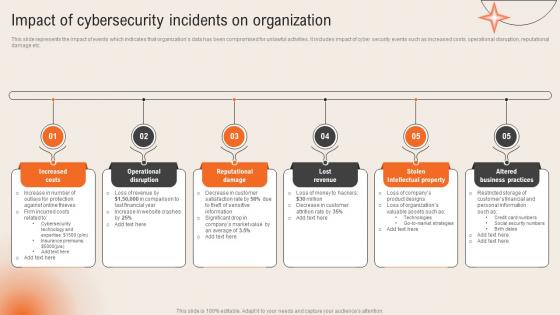 Impact Of Cybersecurity Incidents On Organization Deploying Computer Security Incident Management
Impact Of Cybersecurity Incidents On Organization Deploying Computer Security Incident ManagementThis slide represents the impact of events which indicates that organizations data has been compromised for unlawful activities. It includes impact of cyber security events such as increased costs, operational disruption, reputational damage etc.Increase audience engagement and knowledge by dispensing information using Impact Of Cybersecurity Incidents On Organization Deploying Computer Security Incident Management. This template helps you present information on five stages. You can also present information on Increased Costs, Operational Disruption, Reputational Damage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Parameters To Select Cyber Security Containment Strategy Deploying Computer Security Incident
Key Parameters To Select Cyber Security Containment Strategy Deploying Computer Security IncidentThis slide represents the various parameters to look for before choosing an effective and efficient cyber security containment strategy. It includes key parameters such as higher potential damages and theft of organizational resources etc.Introducing Key Parameters To Select Cyber Security Containment Strategy Deploying Computer Security Incident to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Potential Damages, Organizational Resources, Containment Strategy, using this template. Grab it now to reap its full benefits.
-
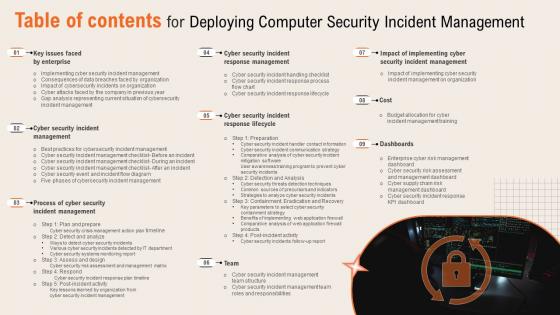 Table Of Contents For Deploying Computer Security Incident Management
Table Of Contents For Deploying Computer Security Incident ManagementPresent the topic in a bit more detail with this Table Of Contents For Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Key Issues Faced, Cyber Security Incident, Incident Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
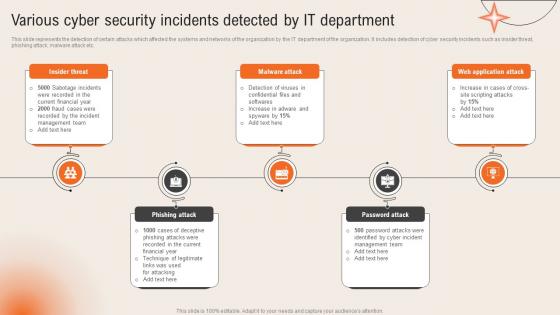 Various Cyber Security Incidents Detected By It Department Deploying Computer Security
Various Cyber Security Incidents Detected By It Department Deploying Computer SecurityThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc.Introducing Various Cyber Security Incidents Detected By It Department Deploying Computer Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Current Financial, Sabotage Incidents, Technique Legitimate, using this template. Grab it now to reap its full benefits.
-
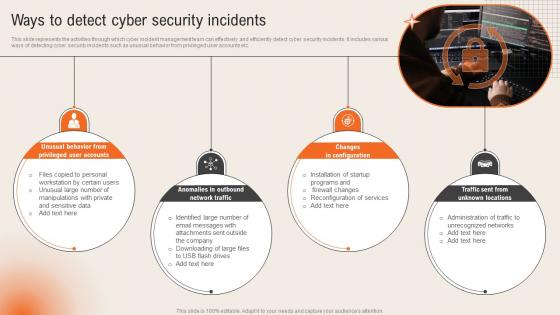 Ways To Detect Cyber Security Incidents Deploying Computer Security Incident Management
Ways To Detect Cyber Security Incidents Deploying Computer Security Incident ManagementThis slide represents the activities through which cyber incident management team can effectively and efficiently detect cyber security incidents. It includes various ways of detecting cyber security incidents such as unusual behavior from privileged user accounts etc.Increase audience engagement and knowledge by dispensing information using Ways To Detect Cyber Security Incidents Deploying Computer Security Incident Management. This template helps you present information on four stages. You can also present information on Unusual Behavior, Privileged Accounts, Anomalies Outbound using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer Crime Security Survey In Powerpoint And Google Slides Cpb
Computer Crime Security Survey In Powerpoint And Google Slides CpbPresenting our Computer Crime Security Survey In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases eight stages. It is useful to share insightful information on Computer Crime Security Survey This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
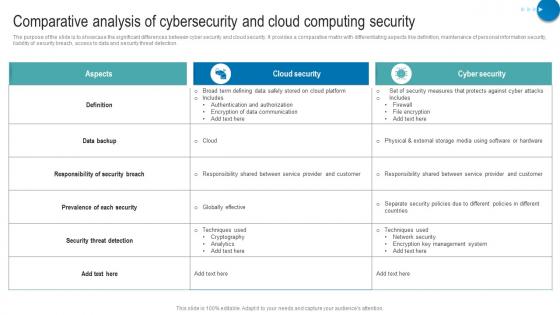 Comparative Analysis Of Cybersecurity And Cloud Computing Security
Comparative Analysis Of Cybersecurity And Cloud Computing SecurityThe purpose of the slide is to showcase the significant differences between cyber security and cloud security. It provides a comparative matrix with differentiating aspects like definition, maintenance of personal information security, liability of security breach, access to data and security threat detection. Presenting our well structured Comparative Analysis Of Cybersecurity And Cloud Computing Security. The topics discussed in this slide are Aspects, Cloud Security, Cyber Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security And Cloud Computing Icon
Cyber Security And Cloud Computing IconPresenting our set of slides with Cyber Security And Cloud Computing Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security, Cloud Computing, Icon.
-
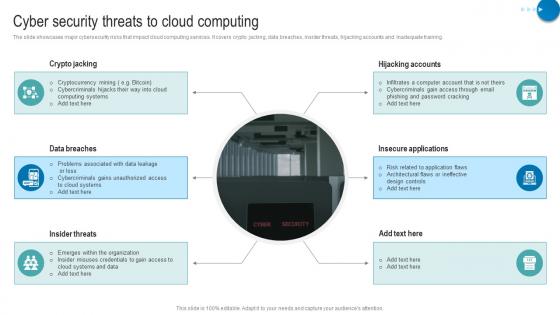 Cyber Security Threats To Cloud Computing
Cyber Security Threats To Cloud ComputingThe slide showcases major cybersecurity risks that impact cloud computing services. it covers crypto jacking, data breaches, insider threats, hijacking accounts and inadequate training. Introducing our premium set of slides with Cyber Security Threats To Cloud Computing. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Crypto Jacking, Hijacking Accounts, Insecure Applications, Data Breaches. So download instantly and tailor it with your information.
-
 Icon For Cloud Computing Cyber Security Services For Smes
Icon For Cloud Computing Cyber Security Services For SmesPresenting our set of slides with Icon For Cloud Computing Cyber Security Services For Smes. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon, Cloud Computing, Cyber Security, Services For Smes.
-
 Key Benefits Of Cognitive Computing Cyber Security
Key Benefits Of Cognitive Computing Cyber SecurityThe purpose of the slide is to show major advantages associated with adopting a cognitive cyber security like fast detection, enhanced incident response and security automation. Introducing our premium set of slides with Key Benefits Of Cognitive Computing Cyber Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Fast Detection, Enhanced Incident Response, Security Automation. So download instantly and tailor it with your information.
-
 Ways Cloud Computing Strengthening Industrial Cyber Security And Productivity
Ways Cloud Computing Strengthening Industrial Cyber Security And ProductivityThe slide showcases the benefits associated with cloud computing at global industrial level. it shows how cloud computing is enhancing global industries productivity and cyber security and dealing with financial barriers. Introducing our premium set of slides with Ways Cloud Computing Strengthening Industrial Cyber Security And Productivity. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Computing, Booting Industrial Production, Cloud Computing Industrial, Cyber Security. So download instantly and tailor it with your information.
-
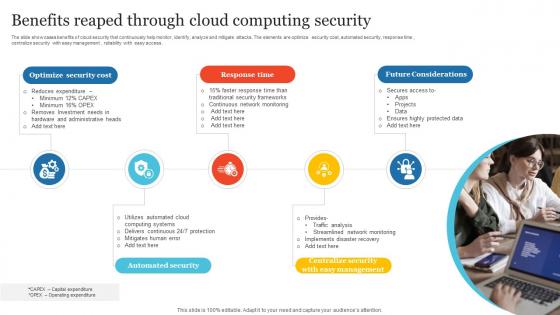 Benefits Reaped Through Cloud Computing Security
Benefits Reaped Through Cloud Computing SecurityThe slide showcases benefits of cloud security that continuously help monitor, identify, analyze and mitigate attacks. The elements are optimize security cost, automated security, response time , centralize security with easy management , reliability with easy access . Presenting our set of slides with Benefits Reaped Through Cloud Computing Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Optimize Security Cost, Response Time, Future Considerations.
-
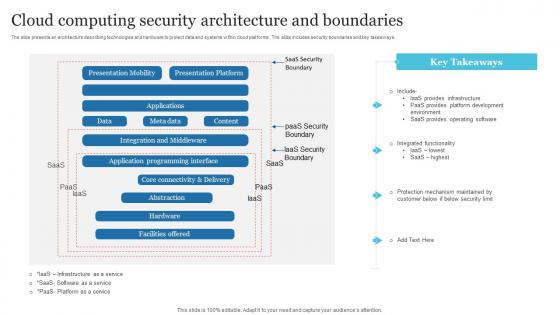 Cloud Computing Security Architecture And Boundaries
Cloud Computing Security Architecture And BoundariesThe slide presents an architecture describing technologies and hardware to protect data and systems within cloud platforms . The slide includes security boundaries and key takeaways. Introducing our Cloud Computing Security Architecture And Boundaries set of slides. The topics discussed in these slides are Presentation Mobility, Presentation Platform, Boundaries This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
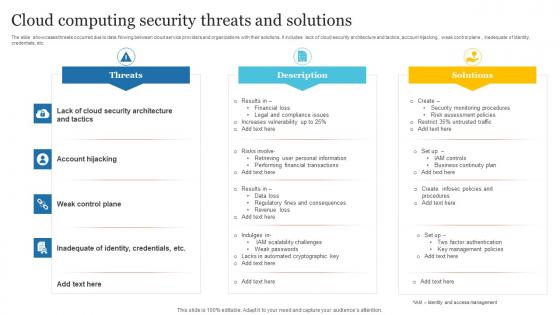 Cloud Computing Security Threats And Solutions
Cloud Computing Security Threats And SolutionsThe slide showcases threats occurred due to data flowing between cloud service providers and organizations with their solutions. It includes lack of cloud security architecture and tactics, account hijacking , weak control plane , inadequate of identity, credentials, etc. Presenting our well structured Cloud Computing Security Threats And Solutions. The topics discussed in this slide are Account Hijacking, Weak Control Plane, Threats This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
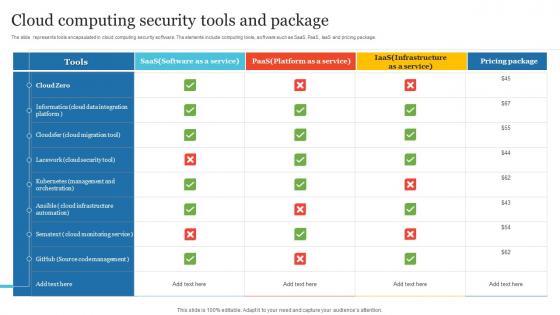 Cloud Computing Security Tools And Package
Cloud Computing Security Tools And PackageThe slide represents tools encapsulated in cloud computing security software. The elements include computing tools, software such as SaaS, PaaS, IaaS and pricing package. Introducing our Cloud Computing Security Tools And Package set of slides. The topics discussed in these slides are Cloud, Computing, Tools This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
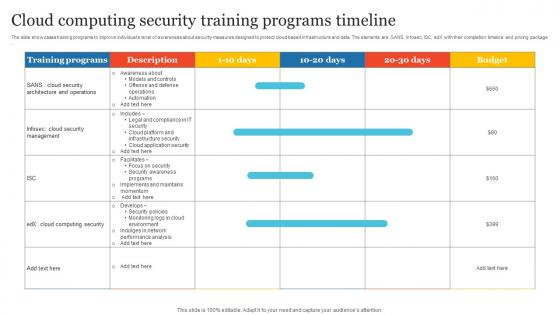 Cloud Computing Security Training Programs Timeline
Cloud Computing Security Training Programs TimelineThe slide showcases training programs to improve individuals level of awareness about security measures designed to protect cloud based infrastructure and data. The elements are SANS, infosec, ISC, edX with their completion timeline and pricing package. Presenting our well structured Cloud Computing Security Training Programs Timeline. The topics discussed in this slide are Computing, Cloud, Training This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Digital Cloud Computing Cyber Security Icon
Digital Cloud Computing Cyber Security IconIntroducing our premium set of slides with Digital Cloud Computing Cyber Security Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Digital Cloud Computing, Cyber Security Icon So download instantly and tailor it with your information.
-
 Key Cloud Computing Security Challenges
Key Cloud Computing Security ChallengesThe slide includes security challenges faced by users and providers in cloud computing. The elements are Ddos and denial of service attacks , data breaches , data loss , insecure access control points, metastructure and applistructure failures. Presenting our set of slides with Key Cloud Computing Security Challenges. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Breaches, Data Loss, Security
-
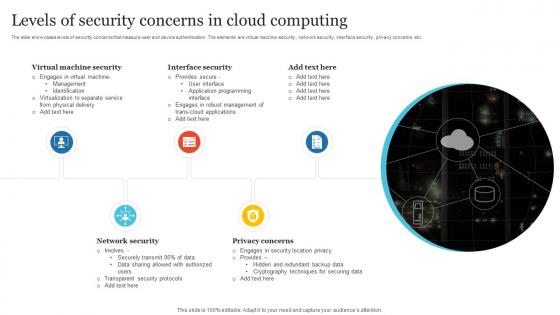 Levels Of Security Concerns In Cloud Computing
Levels Of Security Concerns In Cloud ComputingThe slide showcases levels of security concerns that measure user and device authentication. The elements are virtual machine security , network security , interface security , privacy concerns etc. Introducing our premium set of slides with Levels Of Security Concerns In Cloud Computing. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Virtual Machine Security, Interface Security, Network Security So download instantly and tailor it with your information.
-
 Network Cloud Computing Security Analysis Icon
Network Cloud Computing Security Analysis IconPresenting our set of slides with Network Cloud Computing Security Analysis Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network, Cloud Computing, Security Analysis Icon
-
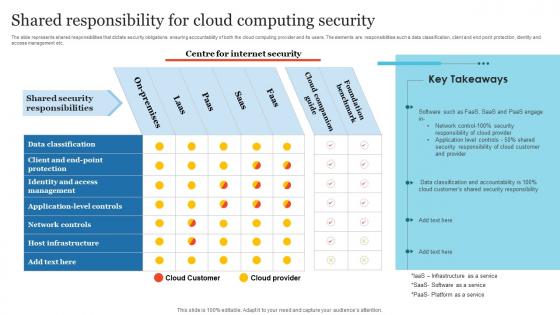 Shared Responsibility For Cloud Computing Security
Shared Responsibility For Cloud Computing SecurityThe slide represents shared responsibilities that dictate security obligations ensuring accountability of both the cloud computing provider and its users. The elements are responsibilities such a data classification, client and end point protection, identity and access management etc. Introducing our Shared Responsibility For Cloud Computing Security set of slides. The topics discussed in these slides are Management, Data Classification, Host Infrastructure This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security Architecture Review Of A Cloud Cloud Computing Software Opportunities And Innovation
Security Architecture Review Of A Cloud Cloud Computing Software Opportunities And InnovationThis slide covers the current situation of cloud computing and software covering new opportunities and innovation for those willing to implement the change. Introducing Security Architecture Review Of A Cloud Cloud Computing Software Opportunities And Innovation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Computing, Software Opportunities, Innovation, using this template. Grab it now to reap its full benefits.
-
 Cloud Computing Infrastructure Security Icon
Cloud Computing Infrastructure Security IconIntroducing Cloud Computing Infrastructure Security Icon to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Computing, Infrastructure, Security Icon, using this template. Grab it now to reap its full benefits.
-
 Best Computer Security System In Powerpoint And Google Slides Cpb
Best Computer Security System In Powerpoint And Google Slides CpbPresenting our Best Computer Security System In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Best Computer Security System. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 F1470 Key Components Of Grid Computing Security Grid Computing Types
F1470 Key Components Of Grid Computing Security Grid Computing TypesThis slide talks about the security component of a grid computing network and how it protects the system by offering authentication and authorization processes. It also contains the OpenSSL deployment that permit users to execute operations within the grid. Introducing F1470 Key Components Of Grid Computing Security Grid Computing Types to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Data Management, Workload And Resource Management, Scheduler, using this template. Grab it now to reap its full benefits.
-
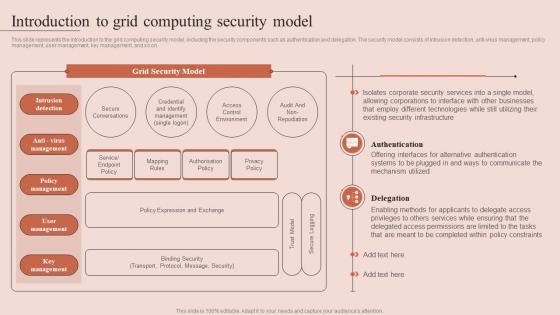 Introduction To Grid Computing Security Model Grid Computing Types
Introduction To Grid Computing Security Model Grid Computing TypesThis slide represents the introduction to the grid computing security model, including the security components such as authentication and delegation. The security model consists of intrusion detection, anti-virus management, policy management, user management, key management, and so on. Deliver an outstanding presentation on the topic using this Introduction To Grid Computing Security Model Grid Computing Types. Dispense information and present a thorough explanation of Intrusion Detection, Policy Management, User Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
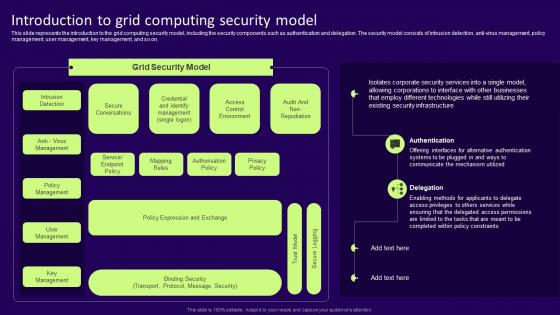 Introduction To Grid Computing Security Model Grid Computing Services
Introduction To Grid Computing Security Model Grid Computing ServicesThis slide represents the introduction to the grid computing security model, including the security components such as authentication and delegation. The security model consists of intrusion detection, anti virus management, policy management, user management, key management, and so on. Deliver an outstanding presentation on the topic using this Introduction To Grid Computing Security Model Grid Computing Services. Dispense information and present a thorough explanation of Authentication, Delegation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
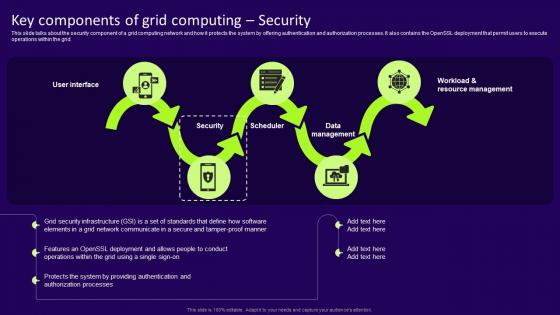 Grid Computing Services Key Components Of Grid Computing Security
Grid Computing Services Key Components Of Grid Computing SecurityThis slide talks about the security component of a grid computing network and how it protects the system by offering authentication and authorization processes. It also contains the OpenSSL deployment that permit users to execute operations within the grid. Present the topic in a bit more detail with this Grid Computing Services Key Components Of Grid Computing Security. Use it as a tool for discussion and navigation on Security, Scheduler, Data Management This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Introduction To Grid Computing Security Model Grid Computing Components
Introduction To Grid Computing Security Model Grid Computing ComponentsThis slide represents the introduction to the grid computing security model, including the security components such as authentication and delegation. The security model consists of intrusion detection, anti virus management, policy management, user management, key management, and so on. Deliver an outstanding presentation on the topic using this Introduction To Grid Computing Security Model Grid Computing Components. Dispense information and present a thorough explanation of Mapping Rules, Service Or Endpoint Policy, Policy Management, Key Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Components Of Grid Computing Security Grid Computing Components
Key Components Of Grid Computing Security Grid Computing ComponentsThis slide talks about the security component of a grid computing network and how it protects the system by offering authentication and authorization processes. It also contains the OpenSSL deployment that permit users to execute operations within the grid. Increase audience engagement and knowledge by dispensing information using Key Components Of Grid Computing Security Grid Computing Components. This template helps you present information on five stages. You can also present information on Grid Computing, Workload, Resource Management, Data Management, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Unauthorized Computer Access Icon Causing Cyber Security Threat
Unauthorized Computer Access Icon Causing Cyber Security ThreatPresenting our set of slides with Unauthorized Computer Access Icon Causing Cyber Security Threat. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Unauthorized, Computer Access.
-
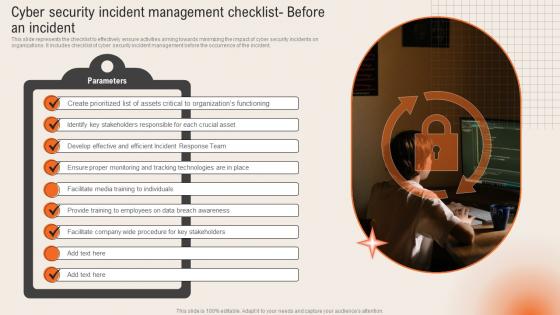 Cyber Security Incident Deploying Computer Security
Cyber Security Incident Deploying Computer SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management before the occurrence of the incident.Introducing Cyber Security Incident Deploying Computer Security to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Organizations Functioning, Stakeholders Responsible, Breach Awareness, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Incident Management Deploying Computer Security
Cyber Security Incident Management Deploying Computer SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management after the occurrence of the incident.Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Deploying Computer Security. This template helps you present information on one stage. You can also present information on Prepare Cyber, Documented Procedures, Quantify Financial using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



