Powerpoint Templates and Google slides for Cyber Security Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
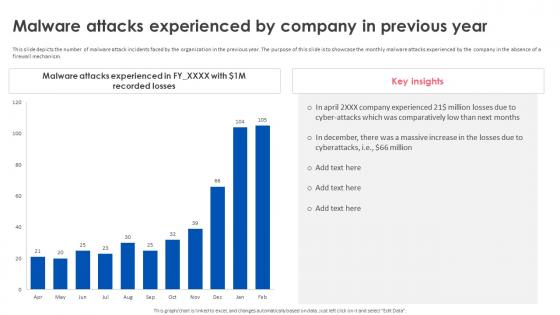 Firewall Implementation For Cyber Security Malware Attacks Experienced By Company In Previous Year
Firewall Implementation For Cyber Security Malware Attacks Experienced By Company In Previous YearThis slide depicts the number of malware attack incidents faced by the organization in the previous year. The purpose of this slide is to showcase the monthly malware attacks experienced by the company in the absence of a firewall mechanism. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Malware Attacks Experienced By Company In Previous Year. Use it as a tool for discussion and navigation on Malware Attacks Experienced, Firewall Mechanism. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
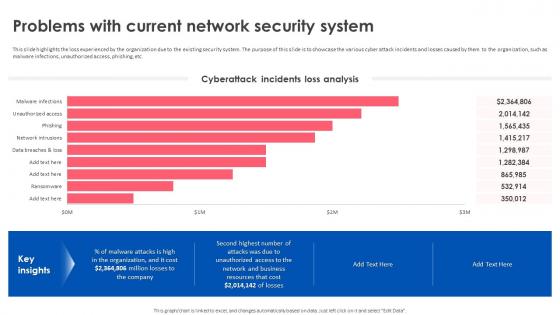 Firewall Implementation For Cyber Security Problems With Current Network Security System
Firewall Implementation For Cyber Security Problems With Current Network Security SystemThis slide highlights the loss experienced by the organization due to the existing security system. The purpose of this slide is to showcase the various cyber attack incidents and losses caused by them to the organization, such as malware infections, unauthorized access, phishing, etc. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Problems With Current Network Security System. Use it as a tool for discussion and navigation on Existing Security System, Cyber Attack Incidents, Malware Infections, Unauthorized Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
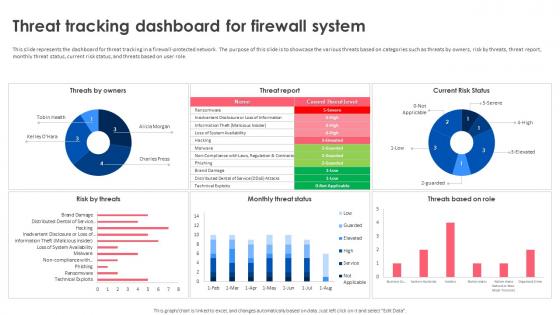 Firewall Implementation For Cyber Security Threat Tracking Dashboard For Firewall System
Firewall Implementation For Cyber Security Threat Tracking Dashboard For Firewall SystemThis slide represents the dashboard for threat tracking in a firewall-protected network. The purpose of this slide is to showcase the various threats based on categories such as threats by owners, risk by threats, threat report, monthly threat status, current risk status, and threats based on user role. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Threat Tracking Dashboard For Firewall System. Dispense information and present a thorough explanation of Threat Tracking Dashboard, Firewall System, Current Risk Status, Firewall Protected Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
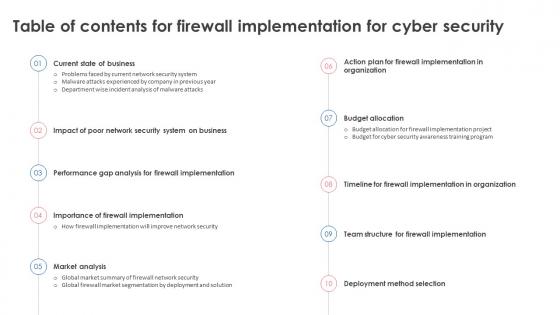 Table Of Contents For Firewall Implementation For Cyber Security Ppt Icon Slide Portrait
Table Of Contents For Firewall Implementation For Cyber Security Ppt Icon Slide PortraitIntroducing Table Of Contents For Firewall Implementation For Cyber Security Ppt Icon Slide Portrait to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Deployment Method Selection, Budget Allocation, Importance Of Firewall Implementation, using this template. Grab it now to reap its full benefits.
-
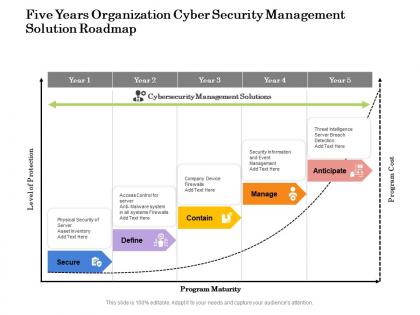 Five years organization cyber security management solution roadmap
Five years organization cyber security management solution roadmapPresenting Five Years Organization Cyber Security Management Solution Roadmap PowerPoint slide. This PPT slide is available at 4,3 and 16,9 aspect ratios. You can download this PPT theme in various formats like PDF, PNG, and JPG. This PowerPoint template is completely editable and you can modify the font size, font type, and shapes as per your requirements. Our PPT layout is compatible with Google Slides.
-
 Cyber Security Risks And Safety Statistics
Cyber Security Risks And Safety StatisticsIntroducing our captivating Infographic templates and one-pagers, designed to transform complex information into visually stunning stories. These user-friendly tools empower you to effortlessly communicate your ideas, data, and messages with clarity and impact. Our diverse collection offers a range of eye-catching designs, vibrant color schemes, and customizable elements, ensuring that every infographic or one-pager is tailored to your unique style and purpose. Whether you are presenting sales figures, explaining a process, or showcasing research findings, our templates provide the perfect canvas for your creativity. With intuitive editing features, even non-designers can effortlessly craft professional-grade visual content. You can simply tweak all the elements of the slide and enjoy the liberty of customizing all the components. Not only this, you can convert these slides in various formats including JPG, PNG, JPEG and PDF. Going well with Google Slides and major Microsoft versions, these templates can be presented on widescreen and standard screen seamlessly. the Grab attention, simplify complexity, and make a lasting impression with our Infographic templates and one-pagers, helping you turn information into unforgettable visual narrative. You can simply tweak all the elements of the slide and enjoy the liberty of customizing all the components. Not only this, you can convert these slides in various formats including JPG, PNG, JPEG and PDF. Going well with Google Slides and major Microsoft versions, these templates can be presented on widescreen and standard screen seamlessly.
-
 List Of Cyber Security Challenges Faced By Organization
List Of Cyber Security Challenges Faced By OrganizationIntroducing our captivating Infographic templates and one-pagers, designed to transform complex information into visually stunning stories. These user-friendly tools empower you to effortlessly communicate your ideas, data, and messages with clarity and impact. Our diverse collection offers a range of eye-catching designs, vibrant color schemes, and customizable elements, ensuring that every infographic or one-pager is tailored to your unique style and purpose. Whether you are presenting sales figures, explaining a process, or showcasing research findings, our templates provide the perfect canvas for your creativity. With intuitive editing features, even non-designers can effortlessly craft professional-grade visual content. You can simply tweak all the elements of the slide and enjoy the liberty of customizing all the components. Not only this, you can convert these slides in various formats including JPG, PNG, JPEG and PDF. Going well with Google Slides and major Microsoft versions, these templates can be presented on widescreen and standard screen seamlessly. the Grab attention, simplify complexity, and make a lasting impression with our Infographic templates and one-pagers, helping you turn information into unforgettable visual narrative. You can simply tweak all the elements of the slide and enjoy the liberty of customizing all the components. Not only this, you can convert these slides in various formats including JPG, PNG, JPEG and PDF. Going well with Google Slides and major Microsoft versions, these templates can be presented on widescreen and standard screen seamlessly.
-
 Cyber Security Home Users In Powerpoint And Google Slides Cpb
Cyber Security Home Users In Powerpoint And Google Slides CpbPresenting Cyber Security Home Users In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Home Users. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
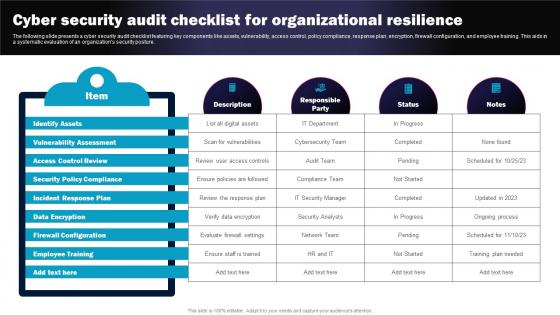 Cyber Security Audit Checklist For Organizational Resilience
Cyber Security Audit Checklist For Organizational ResilienceThe following slide presents a cyber security audit checklist featuring key components like assets, vulnerability, access control, policy compliance, response plan, encryption, firewall configuration, and employee training. This aids in a systematic evaluation of an organizations security posture. Presenting our well structured Cyber Security Audit Checklist For Organizational Resilience The topics discussed in this slide are Identify Assets, Vulnerability Assessment, Access Control Review. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Audit For Access Control Icon
Cyber Security Audit For Access Control IconPresenting our set of slides with Cyber Security Audit For Access Control Icon This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Audit, Access Control Icon
-
 Cyber Security Audit For Data Protection Icon
Cyber Security Audit For Data Protection IconIntroducing our premium set of slides with Cyber Security Audit For Data Protection Icon Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Audit, Data Protection. So download instantly and tailor it with your information.
-
 Cyber Security Audit For Data Protection
Cyber Security Audit For Data ProtectionPresenting our set of slides with Cyber Security Audit, Data Protection This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Audit, Data Protection
-
 Factors To Ensure Effective Cyber Security Audit
Factors To Ensure Effective Cyber Security AuditThe following slide emphasizes factors critical for an effective cyber security audit, including operations, network, data, system, and physical security. It aids in conducting a thorough and comprehensive assessment of an organizations security posture. Introducing our premium set of slides with Factors To Ensure Effective Cyber Security Audit Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Skilled Resourcing Shortages, Security Governance. So download instantly and tailor it with your information.
-
 Key Benefits Of Cyber Security Audit
Key Benefits Of Cyber Security AuditThe following slide underscores key benefits, including gap identification, compliance adherence, business continuity, reputation enhancement, and training awareness, in cyber security audits. This aids in comprehending the strategic advantages of conducting such audits. Presenting our set of slides with Key Benefits Of Cyber Security Audit This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Operations, Network Security, Data Security
-
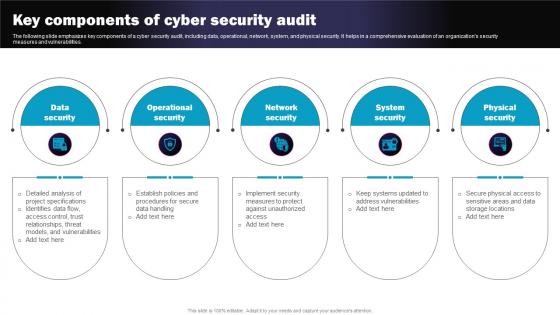 Key Components Of Cyber Security Audit
Key Components Of Cyber Security AuditThe following slide emphasizes key components of a cyber security audit, including data, operational, network, system, and physical security. It helps in a comprehensive evaluation of an organizations security measures and vulnerabilities. Presenting our set of slides with Key Components Of Cyber Security Audit This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Satisfying Compliance Regulations, Enforces Business Continuity
-
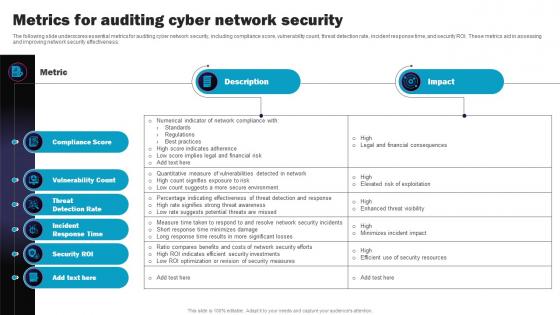 Metrics For Auditing Cyber Network Security
Metrics For Auditing Cyber Network SecurityThe following slide underscores essential metrics for auditing cyber network security, including compliance score, vulnerability count, threat detection rate, incident response time, and security ROI. These metrics aid in assessing and improving network security effectiveness. Introducing our Metrics For Auditing Cyber Network Security set of slides. The topics discussed in these slides are Manual Specification Analysis, Manual Review Of Documentation, Automating Testing. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
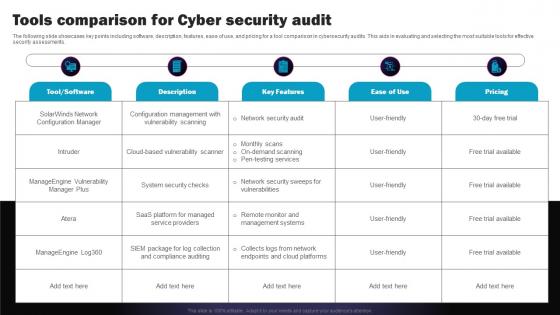 Tools Comparison For Cyber Security Audit
Tools Comparison For Cyber Security AuditThe following slide showcases key points including software, description, features, ease of use, and pricing for a tool comparison in cybersecurity audits. This aids in evaluating and selecting the most suitable tools for effective security assessments. Presenting our well structured Tools Comparison For Cyber Security Audit The topics discussed in this slide are Compliance Score, Vulnerability Count, Incident Response Time. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Audit Checklist Icon
Cyber Security Audit Checklist IconIntroducing our Cyber Security Audit Checklist Icon set of slides. The topics discussed in these slides are Cyber Security Audit Checklist Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 IT Cyber Security Audit Services
IT Cyber Security Audit ServicesThis slide shows auditing services for improvement of organizational cybersecurity system. The purpose of this slide is to help businesses in enhancing efficiency of security controls by providing professional IT audit services. It covers areas such as security configuration, access control, security log and network infrastructure management. Introducing our premium set of slides with IT Cyber Security Audit Services Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Configuration, Access Control Management, Security Log Management. So download instantly and tailor it with your information.
-
 Organizational Checklist For Cyber Security Audit
Organizational Checklist For Cyber Security AuditThis slide presents cyber security audit checklist to manage organizational information systems. It aims to help businesses in evaluating strength of their cyber security system and identifying areas of improvement. It covers elements such as physical security, network safety and incident response and recovery. Presenting our set of slides with Organizational Checklist For Cyber Security Audit. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Physical Security, Network Security, Incident Response And Recovery
-
 Major Types Of Cyber Security Audit
Major Types Of Cyber Security AuditThe following slide emphasizes crucial aspects such as compliance, information systems, website, vulnerability assessment, penetration testing, data privacy, and security audit. It serves to illustrate the diversity of cybersecurity audits, aiding in comprehensive audit planning and understanding. Presenting our set of slides with Major Types Of Cyber Security Audit This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Solarwinds Network, Configuration Manager, System Security Checks
-
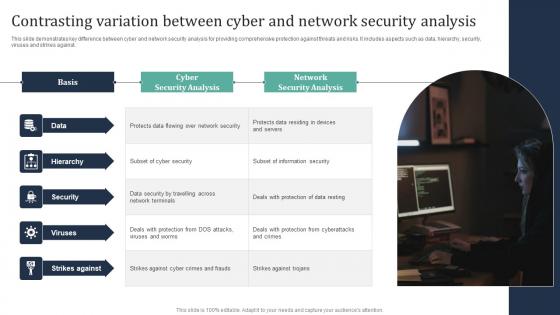 Contrasting Variation Between Cyber And Network Security Analysis
Contrasting Variation Between Cyber And Network Security AnalysisThis slide demonstrates key difference between cyber and network security analysis for providing comprehensive protection against threats and risks. It includes aspects such as data, hierarchy, security, viruses and strikes against. Introducing our premium set of slides with Contrasting Variation Between Cyber And Network Security Analysis. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Hierarchy, Security, Viruses. So download instantly and tailor it with your information.
-
 Cyber Security Analysis Icon For Prioritizing Security Updates
Cyber Security Analysis Icon For Prioritizing Security UpdatesIntroducing our premium set of slides with Cyber Security Analysis Icon For Prioritizing Security Updates. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Analysis, Updates. So download instantly and tailor it with your information.
-
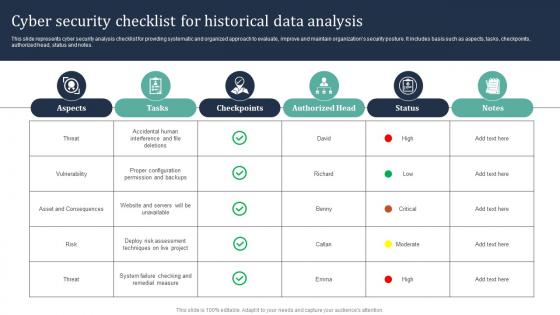 Cyber Security Checklist For Historical Data Analysis
Cyber Security Checklist For Historical Data AnalysisThis slide represents cyber security analysis checklist for providing systematic and organized approach to evaluate, improve and maintain organizations security posture. It includes basis such as aspects, tasks, checkpoints, authorized head, status and notes. Presenting our well structured Cyber Security Checklist For Historical Data Analysis. The topics discussed in this slide are Authorized, Status, Analysis. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
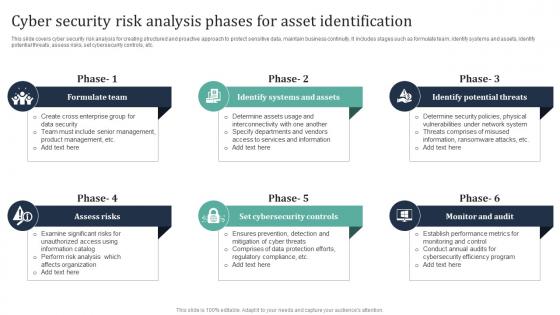 Cyber Security Risk Analysis Phases For Asset Identification
Cyber Security Risk Analysis Phases For Asset IdentificationThis slide covers cyber security risk analysis for creating structured and proactive approach to protect sensitive data, maintain business continuity. It includes stages such as formulate team, identify systems and assets, identify potential threats, assess risks, set cybersecurity controls, etc. Introducing our premium set of slides with Cyber Security Risk Analysis Phases For Asset Identification. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Team, Assess, Cybersecurity. So download instantly and tailor it with your information.
-
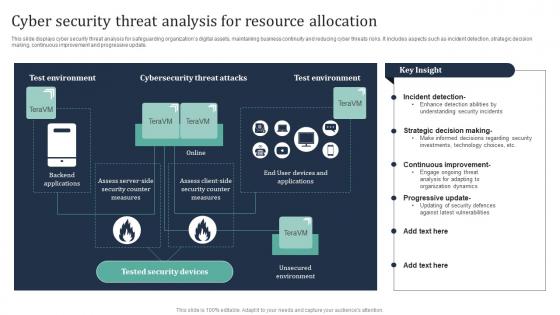 Cyber Security Threat Analysis For Resource Allocation
Cyber Security Threat Analysis For Resource AllocationThis slide displays cyber security threat analysis for safeguarding organizations digital assets, maintaining business continuity and reducing cyber threats risks. It includes aspects such as incident detection, strategic decision making, continuous improvement and progressive update. Introducing our Cyber Security Threat Analysis For Resource Allocation set of slides. The topics discussed in these slides are Cybersecurity, Environment, Incident. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Develop Comprehensive Cyber Security Intelligence Analysis Plan
Develop Comprehensive Cyber Security Intelligence Analysis PlanThis slide represents cybersecurity analysis purpose for protecting organizations digital assets, maintaining business continuity and reducing risks of threats. It includes aspects such as incident response, regulatory compliance and security posture evaluation. Introducing our premium set of slides with Develop Comprehensive Cyber Security Intelligence Analysis Plan. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Response, Compliance, Evaluation. So download instantly and tailor it with your information.
-
 Agenda For Firewall Implementation For Cyber Security Ppt Ideas Infographic Template
Agenda For Firewall Implementation For Cyber Security Ppt Ideas Infographic TemplateIntroducing Agenda For Firewall Implementation For Cyber Security Ppt Ideas Infographic Template to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Firewall Implementation, Cyber Security, Performance Gap Analysis, Team Structure, using this template. Grab it now to reap its full benefits.
-
 Firewall Implementation For Cyber Security Budget Allocation For Firewall Implementation Project
Firewall Implementation For Cyber Security Budget Allocation For Firewall Implementation ProjectThis slide outlines the budget allocation plan for firewall implementation in an organization. The purpose of this slide is to showcase the allocated cost and cost components such as hardware software, licensing fees, professional services, training and staff education, etc. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Budget Allocation For Firewall Implementation Project. Use it as a tool for discussion and navigation on Professional Services, Network Assessment And Design, Testing And Quality Assurance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
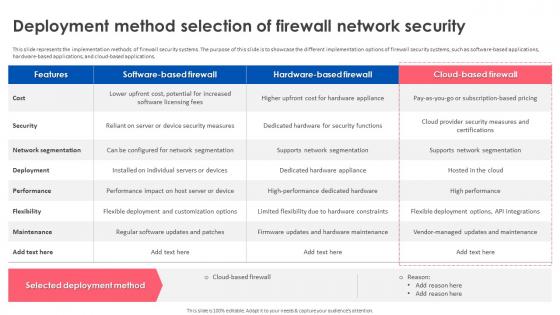 Firewall Implementation For Cyber Security Deployment Method Selection Of Firewall Network Security
Firewall Implementation For Cyber Security Deployment Method Selection Of Firewall Network SecurityThis slide represents the implementation methods of firewall security systems. The purpose of this slide is to showcase the different implementation options of firewall security systems, such as software-based applications, hardware-based applications, and cloud-based applications. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Deployment Method Selection Of Firewall Network Security. Use it as a tool for discussion and navigation on Network Segmentation, Supports Network Segmentation, Hardware For Security Functions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
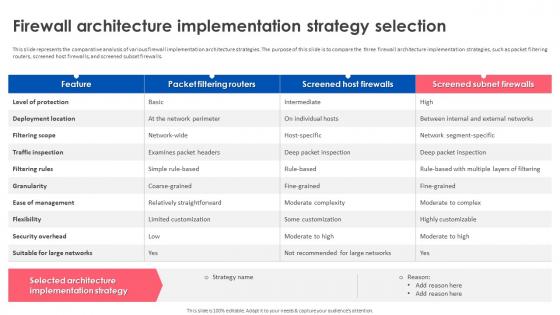 Firewall Implementation For Cyber Security Firewall Architecture Implementation Strategy Selection
Firewall Implementation For Cyber Security Firewall Architecture Implementation Strategy SelectionThis slide represents the comparative analysis of various firewall implementation architecture strategies. The purpose of this slide is to compare the three firewall architecture implementation strategies, such as packet filtering routers, screened host firewalls, and screened subset firewalls. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Firewall Architecture Implementation Strategy Selection. Dispense information and present a thorough explanation of Firewall Architecture, Strategy Selection, Screened Host Firewalls, Screened Subset Firewalls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
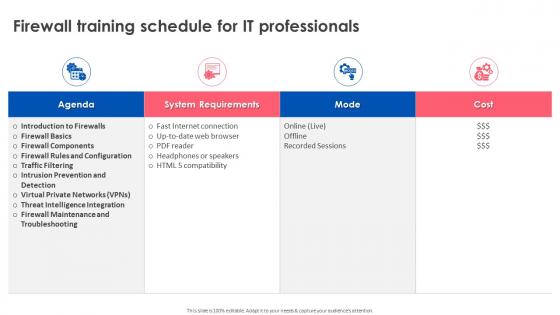 Firewall Implementation For Cyber Security Firewall Training Schedule For It Professionals
Firewall Implementation For Cyber Security Firewall Training Schedule For It ProfessionalsPresent the topic in a bit more detail with this Firewall Implementation For Cyber Security Firewall Training Schedule For It Professionals. Use it as a tool for discussion and navigation on Firewall Components, Intrusion Prevention And Detection, Firewall Maintenance And Troubleshooting. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Firewall Implementation For Cyber Security For Table Of Contents Ppt Ideas Inspiration
Firewall Implementation For Cyber Security For Table Of Contents Ppt Ideas InspirationDeliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security For Table Of Contents Ppt Ideas Inspiration. Dispense information and present a thorough explanation of Firewall Implementation, Cyber Security, Firewall Network Performance, Tracking Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
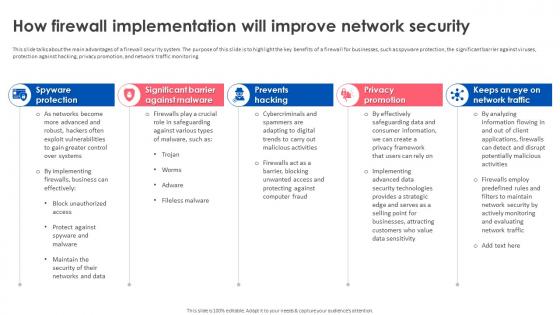 Firewall Implementation For Cyber Security How Firewall Implementation Will Improve Network Security
Firewall Implementation For Cyber Security How Firewall Implementation Will Improve Network SecurityThis slide talks about the main advantages of a firewall security system. The purpose of this slide is to highlight the key benefits of a firewall for businesses, such as spyware protection, the significant barrier against viruses, protection against hacking, privacy promotion, and network traffic monitoring. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security How Firewall Implementation Will Improve Network Security. Use it as a tool for discussion and navigation on Prevents Hacking, Privacy Promotion, Spyware Protection, Network Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
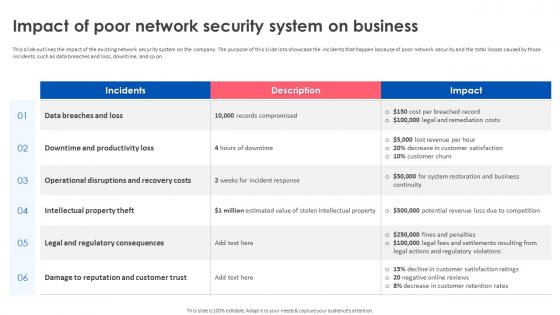 Firewall Implementation For Cyber Security Impact Of Poor Network Security System On Business
Firewall Implementation For Cyber Security Impact Of Poor Network Security System On BusinessThis slide outlines the impact of the existing network security system on the company. The purpose of this slide is to showcase the incidents that happen because of poor network security and the total losses caused by those incidents, such as data breaches and loss, downtime, and so on. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Impact Of Poor Network Security System On Business. Dispense information and present a thorough explanation of Downtime And Productivity Loss, Intellectual Property Theft, Legal And Regulatory Consequences using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
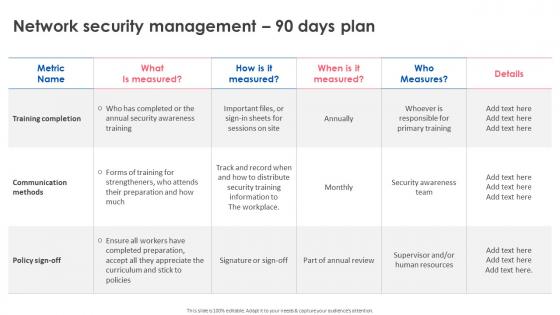 Firewall Implementation For Cyber Security Network Security Management 90 Days Plan
Firewall Implementation For Cyber Security Network Security Management 90 Days PlanDeliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Network Security Management 90 Days Plan. Dispense information and present a thorough explanation of Training Completion, Communication Methods, Network Security Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
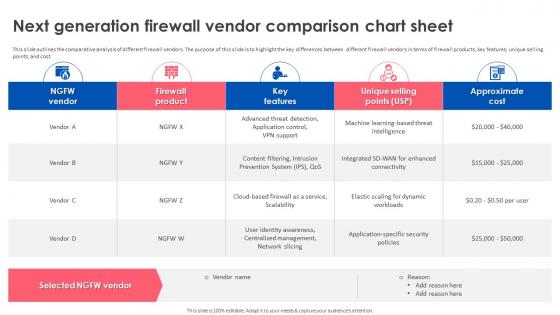 Firewall Implementation For Cyber Security Next Generation Firewall Vendor Comparison Chart Sheet
Firewall Implementation For Cyber Security Next Generation Firewall Vendor Comparison Chart SheetThis slide outlines the comparative analysis of different firewall vendors. The purpose of this slide is to highlight the key differences between different firewall vendors in terms of firewall products, key features, unique selling points, and cost. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Next Generation Firewall Vendor Comparison Chart Sheet. Use it as a tool for discussion and navigation on Comparative Analysis, Firewall Vendors, Firewall Products, Unique Selling Points, Vendor Comparison Chart. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
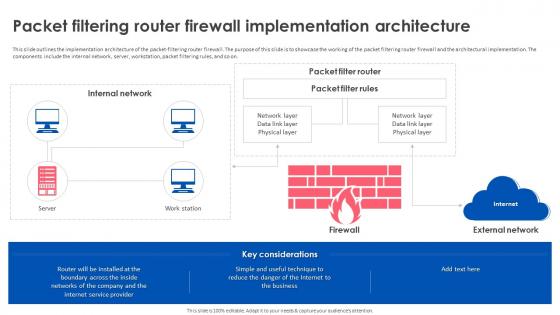 Firewall Implementation For Cyber Security Packet Filtering Router Firewall Implementation Architecture
Firewall Implementation For Cyber Security Packet Filtering Router Firewall Implementation ArchitectureThis slide outlines the implementation architecture of the packet-filtering router firewall. The purpose of this slide is to showcase the working of the packet filtering router firewall and the architectural implementation. The components include the internal network, server, workstation, packet filtering rules, and so on. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Packet Filtering Router Firewall Implementation Architecture. Dispense information and present a thorough explanation of Packet Filtering Router Firewall, Architectural Implementation, Internal Network, Workstation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
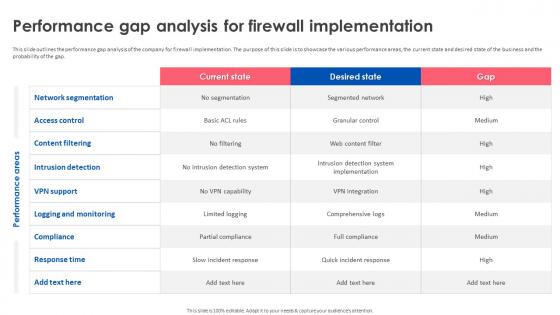 Firewall Implementation For Cyber Security Performance Gap Analysis For Firewall Implementation
Firewall Implementation For Cyber Security Performance Gap Analysis For Firewall ImplementationThis slide outlines the performance gap analysis of the company for firewall implementation. The purpose of this slide is to showcase the various performance areas, the current state and desired state of the business and the probability of the gap. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Performance Gap Analysis For Firewall Implementation. Use it as a tool for discussion and navigation on Network Segmentation, Logging And Monitoring, Intrusion Detection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
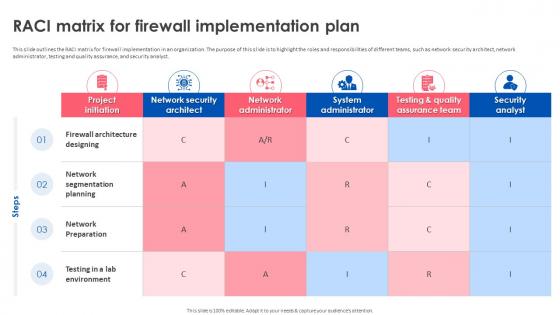 Firewall Implementation For Cyber Security RACI Matrix For Firewall Implementation Plan
Firewall Implementation For Cyber Security RACI Matrix For Firewall Implementation PlanThis slide outlines the RACI matrix for firewall implementation in an organization. The purpose of this slide is to highlight the roles and responsibilities of different teams, such as network security architect, network administrator, testing and quality assurance, and security analyst. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security RACI Matrix For Firewall Implementation Plan. Dispense information and present a thorough explanation of Firewall Architecture Designing, Network Segmentation Planning, Network Preparation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
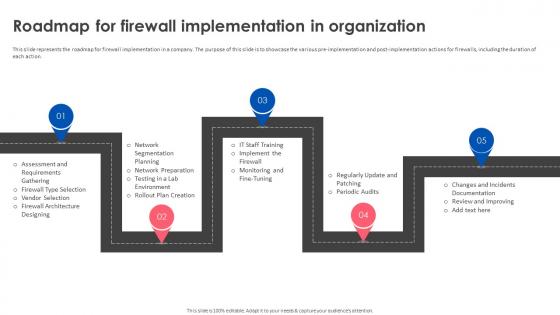 Firewall Implementation For Cyber Security Roadmap For Firewall Implementation In Organization
Firewall Implementation For Cyber Security Roadmap For Firewall Implementation In OrganizationThis slide represents the roadmap for firewall implementation in a company. The purpose of this slide is to showcase the various pre-implementation and post-implementation actions for firewalls, including the duration of each action. Increase audience engagement and knowledge by dispensing information using Firewall Implementation For Cyber Security Roadmap For Firewall Implementation In Organization. This template helps you present information on five stages. You can also present information on Network Segmentation Planning, Network Preparation, Testing In A Lab Environment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
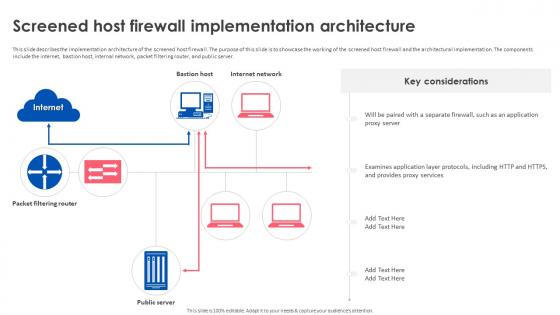 Firewall Implementation For Cyber Security Screened Host Firewall Implementation Architecture
Firewall Implementation For Cyber Security Screened Host Firewall Implementation ArchitectureThis slide describes the implementation architecture of the screened host firewall. The purpose of this slide is to showcase the working of the screened host firewall and the architectural implementation. The components include the internet, bastion host, internal network, packet filtering router, and public server. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Screened Host Firewall Implementation Architecture. Use it as a tool for discussion and navigation on Screened Host Firewall, Implementation Architecture, Bastion Host, Internal Network, Packet Filtering Router. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
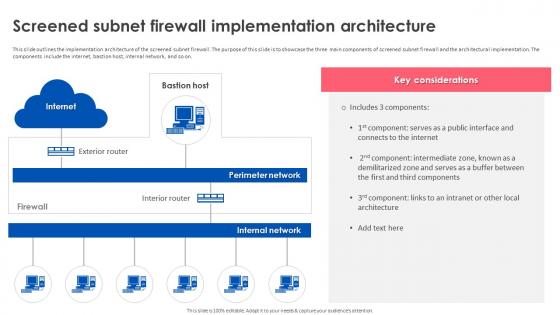 Firewall Implementation For Cyber Security Screened Subnet Firewall Implementation Architecture
Firewall Implementation For Cyber Security Screened Subnet Firewall Implementation ArchitectureThis slide outlines the implementation architecture of the screened subnet firewall. The purpose of this slide is to showcase the three main components of screened subnet firewall and the architectural implementation. The components include the internet, bastion host, internal network, and so on. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Screened Subnet Firewall Implementation Architecture. Dispense information and present a thorough explanation of Screened Subnet Firewall, Implementation Architecture, Bastion Host, Internal Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
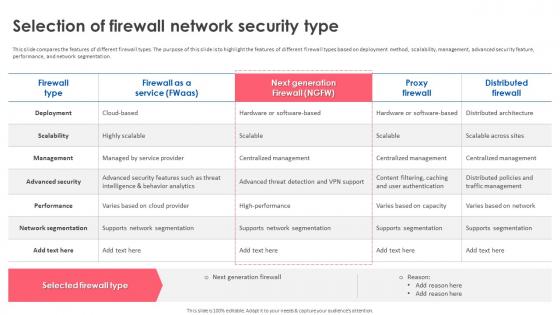 Firewall Implementation For Cyber Security Selection Of Firewall Network Security Type
Firewall Implementation For Cyber Security Selection Of Firewall Network Security TypeThis slide compares the features of different firewall types. The purpose of this slide is to highlight the features of different firewall types based on deployment method, scalability, management, advanced security feature, performance, and network segmentation. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Selection Of Firewall Network Security Type. Use it as a tool for discussion and navigation on Advanced Security, Network Segmentation, Supports Network Segmentation, Centralized Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
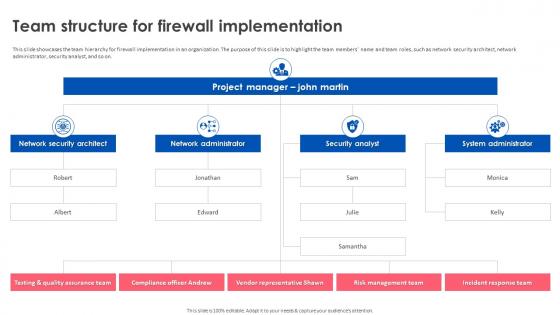 Firewall Implementation For Cyber Security Team Structure For Firewall Implementation
Firewall Implementation For Cyber Security Team Structure For Firewall ImplementationThis slide showcases the team hierarchy for firewall implementation in an organization. The purpose of this slide is to highlight the team members name and team roles, such as network security architect, network administrator, security analyst, and so on. Introducing Firewall Implementation For Cyber Security Team Structure For Firewall Implementation to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Vendor Representative Shawn, Management Team, Incident Response Team, Compliance Officer Andrew, using this template. Grab it now to reap its full benefits.
-
 Firewall Implementation For Cyber Security Timeline For Firewall Implementation In Organization
Firewall Implementation For Cyber Security Timeline For Firewall Implementation In OrganizationThis slide represents the timeline for firewall implementation in a company. The purpose of this slide is to showcase the various pre-implementation and post-implementation actions for firewalls, including the duration of each action. Increase audience engagement and knowledge by dispensing information using Firewall Implementation For Cyber Security Timeline For Firewall Implementation In Organization. This template helps you present information on seven stages. You can also present information on Network Preparation, Assessment And Requirements Gathering, Network Segmentation Planning using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
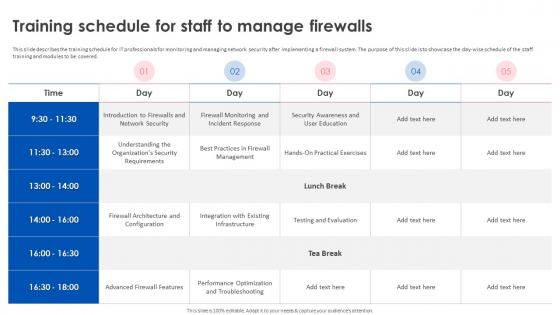 Firewall Implementation For Cyber Security Training Schedule For Staff To Manage Firewalls
Firewall Implementation For Cyber Security Training Schedule For Staff To Manage FirewallsThis slide describes the training schedule for IT professionals for monitoring and managing network security after implementing a firewall system. The purpose of this slide is to showcase the day-wise schedule of the staff training and modules to be covered. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Training Schedule For Staff To Manage Firewalls. Use it as a tool for discussion and navigation on Firewall Monitoring And Incident Response, Firewall Architecture And Configuration, Performance Optimization And Troubleshooting. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide For Firewall Implementation For Cyber Security Ppt Ideas Background Images
Icons Slide For Firewall Implementation For Cyber Security Ppt Ideas Background ImagesIntroducing our well researched set of slides titled Icons Slide For Firewall Implementation For Cyber Security Ppt Ideas Background Images. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
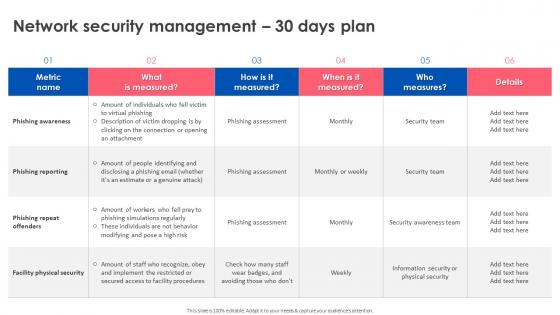 Network Security Management 30 Days Plan Firewall Implementation For Cyber Security
Network Security Management 30 Days Plan Firewall Implementation For Cyber SecurityPresent the topic in a bit more detail with this Network Security Management 30 Days Plan Firewall Implementation For Cyber Security. Use it as a tool for discussion and navigation on Phishing Awareness, Phishing Reporting, Facility Physical Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
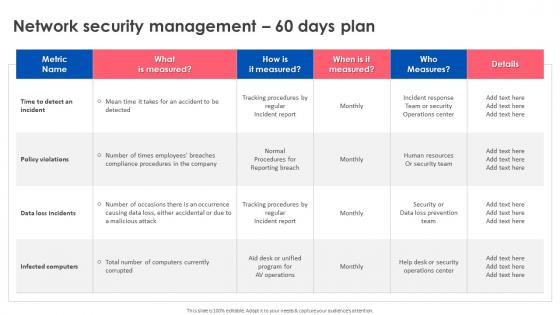 Network Security Management 60 Days Plan Firewall Implementation For Cyber Security
Network Security Management 60 Days Plan Firewall Implementation For Cyber SecurityDeliver an outstanding presentation on the topic using this Network Security Management 60 Days Plan Firewall Implementation For Cyber Security. Dispense information and present a thorough explanation of Policy Violations, Data Loss Incidents, Security Operations Center using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Email Security Icon To Defense Cyber Threats
Email Security Icon To Defense Cyber ThreatsIntroducing our premium set of slides with Email Security Icon To Defense Cyber Threats. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Email Security, Defense Cyber Threats. So download instantly and tailor it with your information.


