Powerpoint Templates and Google slides for Cyber Security It
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Security Mesh Improved Scalability
Cyber Security Mesh Improved ScalabilityIntroducing our Cyber Security Mesh Improved Scalability set of slides. The topics discussed in these slides are Cyber Security Mesh, Improved Scalability. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Four Layers Of Cyber Security Mesh
Four Layers Of Cyber Security MeshThe following slide features essential elements such as security analytics, consolidated policy management, Distributed identity fabric, and unified dashboards to depict the four layers of cybersecurity mesh. This aids in understanding the comprehensive structure and capabilities of cyber mesh. Presenting our set of slides with Four Layers Of Cyber Security Mesh This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Posture Management, Distributed Identity Fabric, Consolidated Dashboards
-
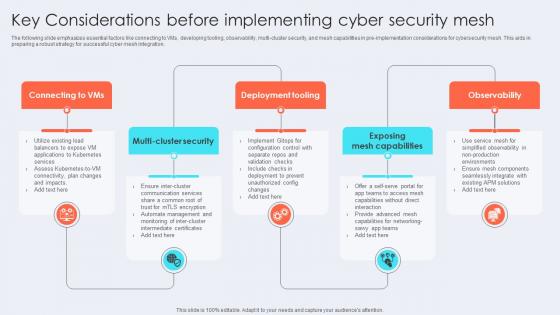 Key Considerations Before Implementing Cyber Security Mesh
Key Considerations Before Implementing Cyber Security MeshThe following slide emphasizes essential factors like connecting to VMs, developing tooling, observability, multi-cluster security, and mesh capabilities in pre-implementation considerations for cybersecurity mesh. This aids in preparing a robust strategy for successful cyber mesh integration. Presenting our set of slides with Key Considerations Before Implementing Cyber Security Mesh This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Deployment Tooling, Exposing Mesh Capabilities, Observability
-
 Reducing Attack Surface By Cyber Security Mesh Icon
Reducing Attack Surface By Cyber Security Mesh IconIntroducing our premium set of slides with Reducing Attack Surface By Cyber Security Mesh Icon Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Reducing Attack Surface, Cyber Security Mesh Icon. So download instantly and tailor it with your information.
-
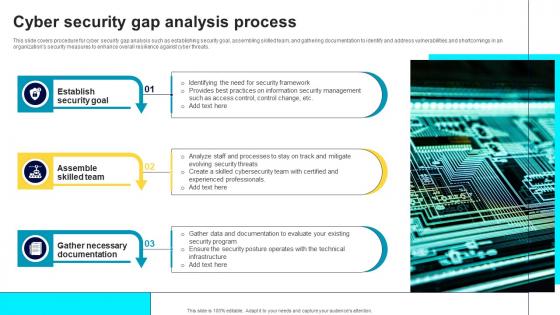 Cyber Security Gap Analysis Process
Cyber Security Gap Analysis ProcessThis slide covers procedure for cyber security gap analysis such as establishing security goal, assembling skilled team, and gathering documentation to identify and address vulnerabilities and shortcomings in an organizations security measures to enhance overall resilience against cyber threats. Presenting our set of slides with name Cyber Security Gap Analysis Process. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Establish Security Goal, Assemble Skilled Team, Gather Necessary Documentation.
-
 Cyber Security Threat Icon To Prevent Gap
Cyber Security Threat Icon To Prevent GapPresenting our set of slides with name Cyber Security Threat Icon To Prevent Gap. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Threat, Icon Prevent Gap.
-
 Checklist To Enhance Cyber Security Of SCADA Networks
Checklist To Enhance Cyber Security Of SCADA NetworksThis slide represents checklist that assist IT companies to enhance their SCADA networks cyber security for improving data protection. It includes various elements such as recognizing connections, disconnecting irrelevant networks, etc. Introducing our Checklist To Enhance Cyber Security Of SCADA Networks set of slides. The topics discussed in these slides are Essential Connections, Inadvertent Disclosure, SCADA Network This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
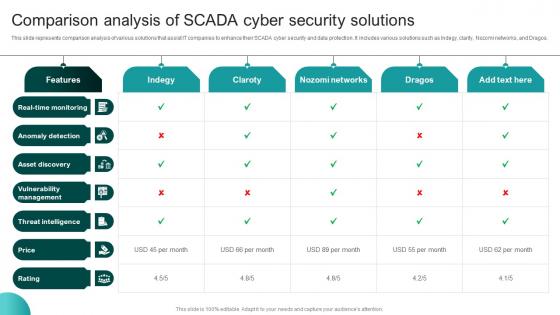 Comparison Analysis Of SCADA Cyber Security Solutions
Comparison Analysis Of SCADA Cyber Security SolutionsThis slide represents comparison analysis of various solutions that assist IT companies to enhance their SCADA cyber security and data protection. It includes various solutions such as Indegy, clarity, Nozomi networks, and Dragos. Presenting our well structured Comparison Analysis Of SCADA Cyber Security Solutions The topics discussed in this slide are Anomaly Detection, Asset Discovery, Vulnerability Management. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Framework For SCADA Cyber Security Policy
Framework For SCADA Cyber Security PolicyThis slide represents framework of various policies that assist IT companies to optimize their SCADA cyber security for effective data protection. It includes policies related to data security, platform security, communication security, audit, etc. Introducing our Framework For SCADA Cyber Security Policy set of slides. The topics discussed in these slides are System Security Program, Cyber Security Policy This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
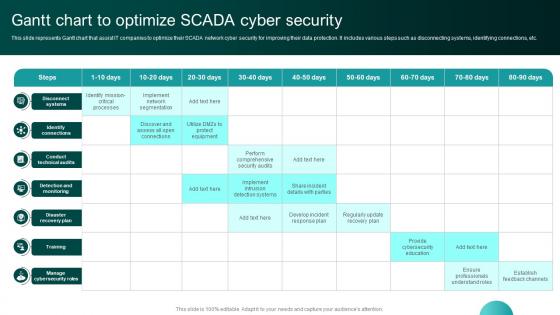 Gantt Chart To Optimize SCADA Cyber Security
Gantt Chart To Optimize SCADA Cyber SecurityThis slide represents Gantt chart that assist IT companies to optimize their SCADA network cyber security for improving their data protection. It includes various steps such as disconnecting systems, identifying connections, etc. Presenting our well structured Gantt Chart To Optimize SCADA Cyber Security The topics discussed in this slide are Identify Connections, Conduct Technical Audits. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
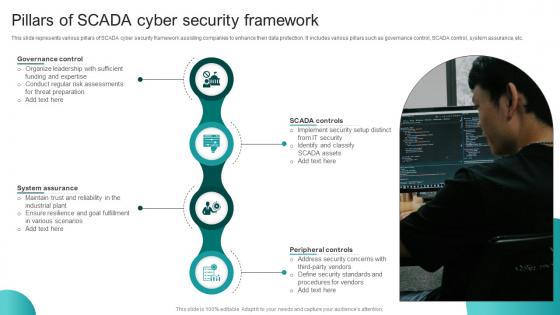 Pillars Of SCADA Cyber Security Framework
Pillars Of SCADA Cyber Security FrameworkThis slide represents various pillars of SCADA cyber security framework assisting companies to enhance their data protection. It includes various pillars such as governance control, SCADA control, system assurance, etc. Presenting our set of slides with Pillars Of SCADA Cyber Security Framework This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Governance Control, SCADA Controls, Peripheral Controls
-
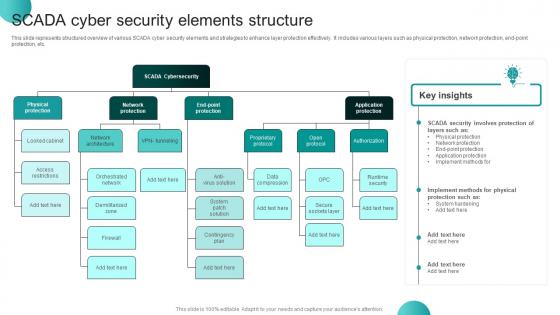 SCADA Cyber Security Elements Structure
SCADA Cyber Security Elements StructureThis slide represents structured overview of various SCADA cyber security elements and strategies to enhance layer protection effectively. It includes various layers such as physical protection, network protection, end-point protection, etc. Presenting our well structured SCADA Cyber Security Elements Structure The topics discussed in this slide are SCADA Security, SCADA Cybersecurity, Application Protection. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Training Schedule For Enhancing SCADA Cyber Security
Training Schedule For Enhancing SCADA Cyber SecurityThis slide represents training schedule that helps IT companies to plan education sessions on SCADA cyber security for their IT employees effectively. It includes various components such as course, details, duration, etc. Introducing our Training Schedule For Enhancing SCADA Cyber Security set of slides. The topics discussed in these slides are Duration, Platform, Deadline This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Simulation Based Cyber Security Training Program
Simulation Based Cyber Security Training ProgramThis slide represents simulation based training program for cyber security awareness including components such as session name, expected impact, duration, etc. Introducing our premium set of slides with Simulation Based Cyber Security Training Program Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Customer Data Protection, Attack Mitigation, Duration. So download instantly and tailor it with your information.
-
 Cyber Security Technology Stack Icon
Cyber Security Technology Stack IconIntroducing our Cyber Security Technology Stack Icon set of slides. The topics discussed in these slides are Cyber Security Technology Stack Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Technological Stacks Enhancing Cyber Security
Technological Stacks Enhancing Cyber SecurityThis slide showcases the technological stacks accelerating cyber security which helps an organization to ensure maintaining and setting powerful password and email filtering. It include details such as endpoint detection and response, mobile threat defense, etc. Presenting our set of slides with name Technological Stacks Enhancing Cyber Security This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Endpoint Protection Platform, Endpoint Detection And Response
-
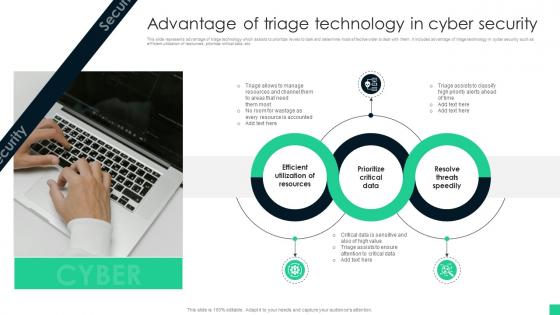 Advantage Of Triage Technology In Cyber Security
Advantage Of Triage Technology In Cyber SecurityThis slide represents advantage of triage technology which assists to prioritize levels to task and determine most effective order to deal with them. It includes advantage of triage technology in cyber security such as efficient utilization of resources, prioritize critical data, etc Presenting our set of slides with name Advantage Of Triage Technology In Cyber Security This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Utilization Of Resources, Prioritize Critical Data, Resolve Threats Speedily
-
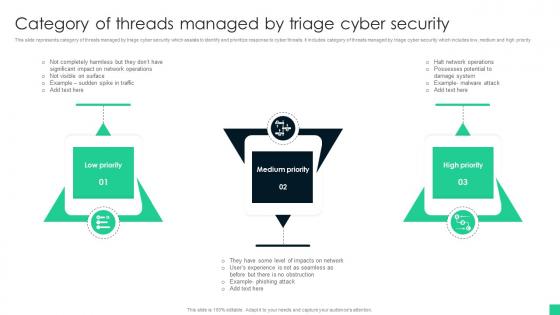 Category Of Threads Managed By Triage Cyber Security
Category Of Threads Managed By Triage Cyber SecurityThis slide represents category of threats managed by triage cyber security which assists to identify and prioritize response to cyber threats. It includes category of threats managed by triage cyber security which includes low, medium and high priority Introducing our premium set of slides with name Category Of Threads Managed By Triage Cyber Security Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Low Priority, Medium Priority, High Priority . So download instantly and tailor it with your information.
-
 Checklist To Establish Triage Capability In Cyber Security
Checklist To Establish Triage Capability In Cyber SecurityThis slide represents checklist to establish triage capability in cyber security which assists to analyse threat alerts and effectively response cyber threats. It includes checklist to establish triage capability in cyber security which includes steps such as type of events, skill levels, etc Introducing our Checklist To Establish Triage Capability In Cyber Security set of slides. The topics discussed in these slides are Types Of Events, Skills Levels, Channels Of Support. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
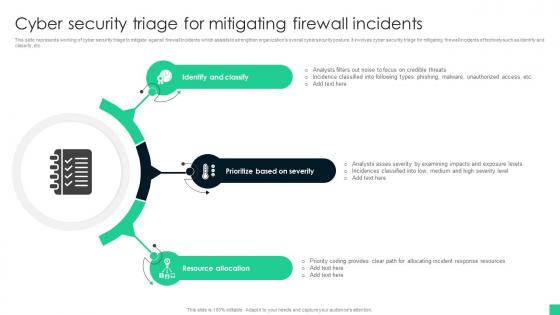 Cyber Security Triage For Mitigating Firewall Incidents
Cyber Security Triage For Mitigating Firewall IncidentsThis slide represents working of cyber security triage to mitigate against firewall incidents which assists to strengthen organizations overall cybersecurity posture. It involves cyber security triage for mitigating firewall incidents effectively such as identify and classify, etc Presenting our set of slides with name Cyber Security Triage For Mitigating Firewall Incidents This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify And Classify, Prioritize Based On Severity, Resource Allocation
-
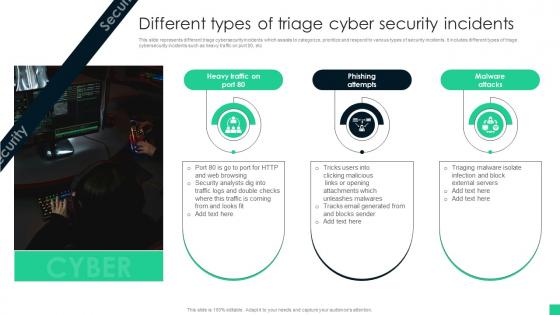 Different Types Of Triage Cyber Security Incidents
Different Types Of Triage Cyber Security IncidentsThis slide represents different triage cybersecurity incidents which assists to categorize, prioritize and respond to various types of security incidents. It includes different types of triage cybersecurity incidents such as heavy traffic on port 80, etc Introducing our premium set of slides with name Different Types Of Triage Cyber Security Incidents Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Phishing Attempts, Malware Attacks. So download instantly and tailor it with your information.
-
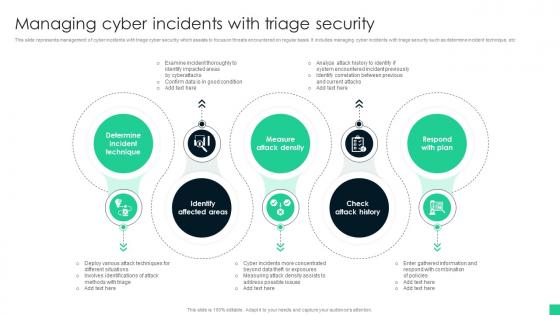 Managing Cyber Incidents With Triage Security
Managing Cyber Incidents With Triage SecurityThis slide represents management of cyber incidents with triage cyber security which assists to focus on threats encountered on regular basis. It includes managing cyber incidents with triage security such as determine incident technique, etc Presenting our set of slides with name Managing Cyber Incidents With Triage Security This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Determine Incident Technique, Identify Affected Areas, Measure Attack Density
-
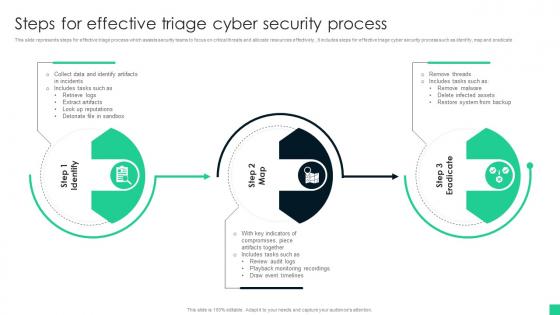 Steps For Effective Triage Cyber Security Process
Steps For Effective Triage Cyber Security ProcessThis slide represents steps for effective triage process which assists security teams to focus on critical threats and allocate resources effectively., It includes steps for effective triage cyber security process such as identify, map and eradicate Introducing our premium set of slides with name Steps For Effective Triage Cyber Security Process Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Artifacts, Draw Event Timelines, System From Backup. So download instantly and tailor it with your information.
-
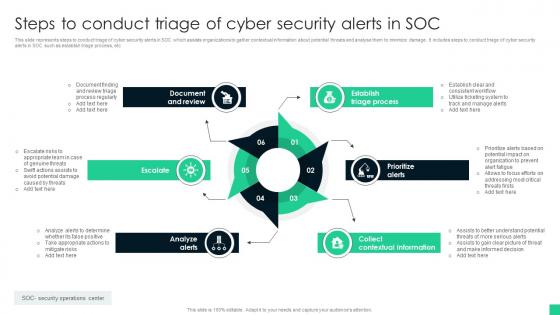 Steps To Conduct Triage Of Cyber Security Alerts In Soc
Steps To Conduct Triage Of Cyber Security Alerts In SocThis slide represents steps to conduct triage of cyber security alerts in SOC which assists organizations to gather contextual information about potential threats and analyse them to minimize damage. It includes steps to conduct triage of cyber security alerts in SOC such as establish triage process, etc Presenting our set of slides with name Steps To Conduct Triage Of Cyber Security Alerts In Soc This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Establish Triage Process, Prioritize Alerts, Collect Contextual Information
-
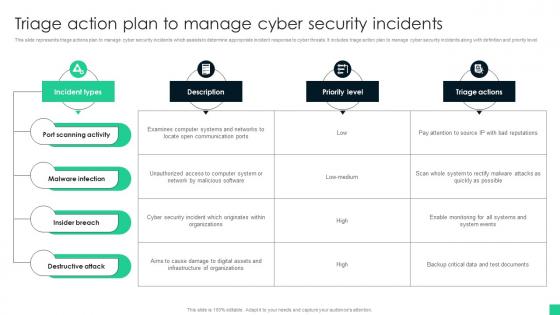 Triage Action Plan To Manage Cyber Security Incidents
Triage Action Plan To Manage Cyber Security IncidentsThis slide represents triage actions plan to manage cyber security incidents which assists to determine appropriate incident response to cyber threats. It includes triage action plan to manage cyber security incidents along with definition and priority level. Introducing our Triage Action Plan To Manage Cyber Security Incidents set of slides. The topics discussed in these slides are Port Scanning Activity, Malware Infection, Insider Breach. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Triage Cyber Security For System Protection Icon
Triage Cyber Security For System Protection IconPresenting our set of slides with name Triage Cyber Security For System Protection Icon This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Triage Cyber Security, System Protection Icon
-
 Triage Cyber Security To Identify Cyber Threats Icon
Triage Cyber Security To Identify Cyber Threats IconIntroducing our premium set of slides with name Triage Cyber Security To Identify Cyber Threats Icon Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Triage Cyber Security, Identify Cyber Threats Icon. So download instantly and tailor it with your information.
-
 Triage Process For Cyber Security Icon
Triage Process For Cyber Security IconPresenting our set of slides with name Triage Process For Cyber Security Icon This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Triage Process, Cyber Security Icon
-
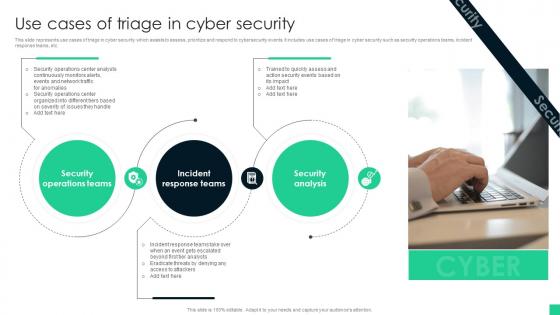 Use Cases Of Triage In Cyber Security
Use Cases Of Triage In Cyber SecurityThis slide represents use cases of triage in cyber security which assists to assess, prioritize and respond to cybersecurity events. It includes use cases of triage in cyber security such as security operations teams, incident response teams, etc. Introducing our premium set of slides with name Use Cases Of Triage In Cyber Security Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Operations Teams, Incident Response Teams, Security Analysis. So download instantly and tailor it with your information.
-
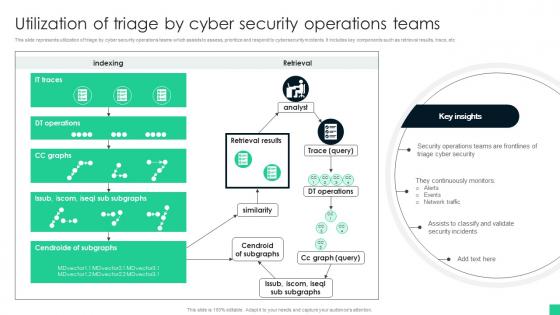 Utilization Of Triage By Cyber Security Operations Teams
Utilization Of Triage By Cyber Security Operations TeamsThis slide represents utilization of triage by cyber security operations teams which assists to assess, prioritize and respond to cybersecurity incidents. It includes key components such as retrieval results, trace, etc Introducing our Utilization Of Triage By Cyber Security Operations Teams set of slides. The topics discussed in these slides are Triage Cyber Security, Network Traffic, Security Incidents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
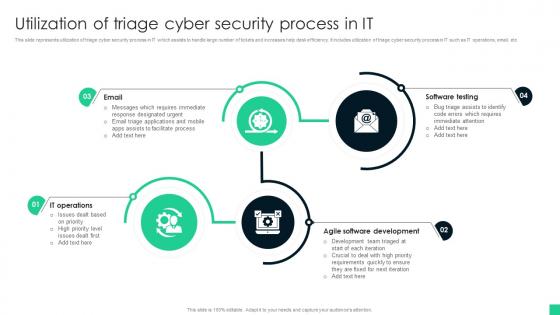 Utilization Of Triage Cyber Security Process In It
Utilization Of Triage Cyber Security Process In ItThis slide represents utilization of triage cyber security process in IT which assists to handle large number of tickets and increases help desk efficiency. It includes utilization of triage cyber security process in IT such as IT operations, email, etc Presenting our set of slides with name Utilization Of Triage Cyber Security Process In It This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Software Testing, Agile Software Development, IT Operations
-
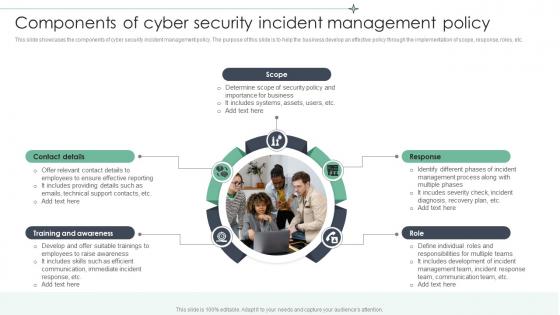 Components Of Cyber Security Incident Management Policy
Components Of Cyber Security Incident Management PolicyThis slide showcases the components of cyber security incident management policy. The purpose of this slide is to help the business develop an effective policy through the implementation of scope, response, roles, etc. Presenting our set of slides with Components Of Cyber Security Incident Management Policy. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Contact Details, Training And Awareness, Includes Systems.
-
 Security Incident Icon To Prevent Cyber Attacks
Security Incident Icon To Prevent Cyber AttacksPresenting our set of slides with Security Incident Icon To Prevent Cyber Attacks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Incident, Prevent Cyber Attacks.
-
 ATP Against Cyber Security Virus Types
ATP Against Cyber Security Virus TypesThis slide depicts ATP importance in cyber security against viruses. Its objective is to include anti threat protection to keep up with growing virus. This slide includes man in middle attack, bot, brute force, manipulation, log injection and path traversal, etc. Introducing our ATP Against Cyber Security Virus Types set of slides. The topics discussed in these slides are Virus Possibility, Protection, Remarks, Social Engineering, Manipulate Mobile Code. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 ATP Computer Cyber Security Flow Icon
ATP Computer Cyber Security Flow IconPresenting our set of slides with name ATP Computer Cyber Security Flow Icon. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on ATP Computer, Cyber Security Flow Icon.
-
 ATP Cyber Network Security Icon
ATP Cyber Network Security IconPresenting our set of slides with name ATP Cyber Network Security Icon. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on ATP Cyber Network, Security Icon.
-
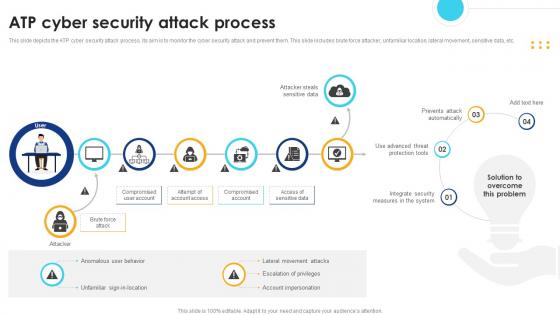 ATP Cyber Security Attack Process
ATP Cyber Security Attack ProcessThis slide depicts the ATP cyber security attack process. Its aim is to monitor the cyber security attack and prevent them. This slide includes brute force attacker, unfamiliar location, lateral movement, sensitive data, etc. Presenting our set of slides with name ATP Cyber Security Attack Process. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Integrate Security, Measures In The System, Prevents Attack Automatically, Access Of Sensitive Data.
-
 ATP Cyber Security Features Checklist
ATP Cyber Security Features ChecklistThis slide depicts the essential features checklist for cyber security ATP. Its aim is to include the essential features during advanced threat protection of a system. This slide includes file analytics, attacks surface management, combined prevention and rich threat intelligence, etc. Presenting our set of slides with name ATP Cyber Security Features Checklist. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on File Analytics, Attack Surface Management, Combined Prevention, Rich Threat Intelligence.
-
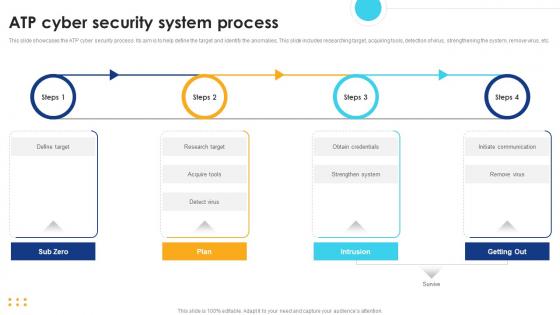 ATP Cyber Security System Process
ATP Cyber Security System ProcessThis slide showcases the ATP cyber security process. Its aim is to help define the target and identify the anomalies. This slide includes researching target, acquiring tools, detection of virus, strengthening the system, remove virus, etc. Presenting our set of slides with name ATP Cyber Security System Process. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Plan, Intrusion, Getting Out, Sub Zero.
-
 ATP Cyber Security Threat Detection System
ATP Cyber Security Threat Detection SystemThis slide depicts the ATP cyber security detection system. Its aim is to use various approach to kill off any threats during cyber attack. This slide includes multilayer approach, behavioural analysis, machine learning, sand boxing, threat intelligence, etc. Presenting our set of slides with name ATP Cyber Security Threat Detection System. This exhibits information on Nine stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Multilayered Approach, Behavioural Analysis, Machine Learning, Threat Intelligence, Endpoint Detection.
-
 ATP Cyber Technology Security Icon
ATP Cyber Technology Security IconPresenting our set of slides with name ATP Cyber Technology Security Icon. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on ATP Cyber Technology, Security Icon.
-
 Best Practices For Managing ATP Cyber Security
Best Practices For Managing ATP Cyber SecurityThis slide covers the best practices for ATP cyber security. Its aim is to use the best practice available for anti threat protection for cyber security. This slide includes practices such as evaluation of security, training staff, choose effective solution, evaluate existing security, etc. Introducing our Best Practices For Managing ATP Cyber Security set of slides. The topics discussed in these slides are Assess Organisation Needs, Identify Vulnerabilities, Evaluate Existing Security, Choose Effective Solution. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
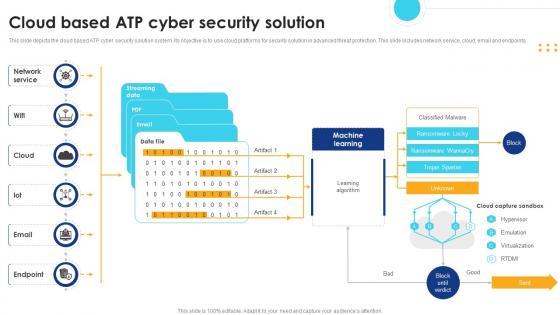 Cloud Based ATP Cyber Security Solution
Cloud Based ATP Cyber Security SolutionThis slide depicts the cloud based ATP cyber security solution system. Its objective is to use cloud platforms for security solution in advanced threat protection. This slide includes network service, cloud, email and endpoints. Presenting our set of slides with name Cloud Based ATP Cyber Security Solution. This exhibits information on One stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Service, Learning Algorithm, Machine Learning.
-
 Comparative Analysis Of ATP Cyber Security Tools
Comparative Analysis Of ATP Cyber Security ToolsThis slide depicts the comparative analysis of ATP cyber security tools. Its aim is to use the tools to protect the system from advanced threats. This slide include Microsoft defender, ESET endpoint, Palo Alto network, Fortinet sandbox. Presenting our set of slides with name Comparative Analysis Of ATP Cyber Security Tools. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Microsoft Defender, ESET Endpoint, Palo Alto Network, Fortinet Sandbox.
-
 Essential Components Of ATP Cyber Security
Essential Components Of ATP Cyber SecurityThis slide depicts the essential components of ATP cyber security. Its aim is to use these components to safeguard organisational system against any threats. This slide include detection of stealthy threats, software behaviour and analysis of data. Presenting our set of slides with name Essential Components Of ATP Cyber Security. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detect Stealthy Threats, Analysis Of Data, Benign Software Behaviour.
-
 Impact Of ATP Cyber Security Automation
Impact Of ATP Cyber Security AutomationThis slide depicts the ATP cyber security automation to detect virus. Its aim is to help prevent the virus in the system. This slide includes prevention, detection and mitigate. Presenting our set of slides with name Impact Of ATP Cyber Security Automation. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prevent, Detec, Mitigate.
-
 Implement ATP Cyber Security Strategies In Organisation
Implement ATP Cyber Security Strategies In OrganisationThis slide depicts the strategies for cyber security ATP. Its objective is to help formulate advanced strategies for threat protection. This slide includes broad test repository, benign software behaviour, analysis of data, etc. Presenting our set of slides with name Implement ATP Cyber Security Strategies In Organisation. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Broad Test Repository, Benign Software Behaviour, Analysis Of Data.
-
 Measure ATP Cyber Security Solution Metrics
Measure ATP Cyber Security Solution MetricsThis slide showcases the measures taken for ATP cyber security solution metrics. Its aim is to detect and calculate the amount of response generated by metrics. This slide includes false positive rate, time to detection, threat coverage, incident response, etc. Presenting our set of slides with name Measure ATP Cyber Security Solution Metrics. This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Coverage, Incident Response, Detection Rate, False Positive Rate, Time To Detection.
-
 Cloud Cyber Security SaaS Risk Management
Cloud Cyber Security SaaS Risk ManagementThis slide showcases the cloud cyber security SaaS risk management. Its aim is to control profile and manage the risk involved. This slide includes authorization, monitor, cloud based, continuously monitor, etc. Introducing Cloud Cyber Security SaaS Risk Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Control Profiles, Cloud Security Risk Management, Security Categorization, using this template. Grab it now to reap its full benefits.
-
 Types Of SaaS Cyber Security Risk Management
Types Of SaaS Cyber Security Risk ManagementThis slide showcases the types of SaaS cyber security risks. Its purpose is to use SaaS based methods for organizations situation. This slide includes cloud misconfigure, third party, supply chain, vulnerabilities, due diligence and non compliance. Increase audience engagement and knowledge by dispensing information using Types Of SaaS Cyber Security Risk Management. This template helps you present information on six stages. You can also present information on Supply Chain Attacks, Zero Day Vulnerabilities, Due Diligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Firewall Security Icon Protecting From Cyber Threats
Firewall Security Icon Protecting From Cyber ThreatsIntroducing our Firewall Security Icon Protecting From Cyber Threats set of slides. The topics discussed in these slides are Firewall Security, Protecting. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
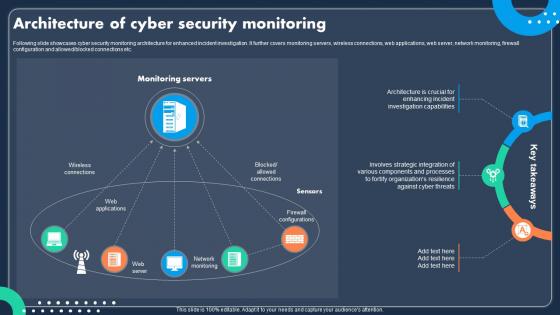 Architecture Of Cyber Security Monitoring
Architecture Of Cyber Security MonitoringFollowing slide showcases cyber security monitoring architecture for enhanced incident investigation. It further covers monitoring servers, wireless connections, web applications, web server, network monitoring, firewall configuration and allowed or blocked connections etc. Presenting our set of slides with Architecture Of Cyber Security Monitoring This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Firewall Configurations, Network Monitoring, Web Server.
-
 Cyber Security Monitoring Framework In Organization
Cyber Security Monitoring Framework In OrganizationFollowing slide showcases organization framework of cyber security monitoring for improved network protection posture. It further covers identify, protect, detect, respond and recover, etc. Presenting our set of slides with Cyber Security Monitoring Framework In Organization This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Recovery Planning, Responsive Planning, Business Environment.
-
 Monitoring Computer Safety Lock Icon For Cyber Security
Monitoring Computer Safety Lock Icon For Cyber SecurityPresenting our set of slides with Monitoring Computer Safety Lock Icon For Cyber Security This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Monitoring Computer Safety, Cyber Security.
-
 Monitoring Cyber Risk Icon For Computer Security
Monitoring Cyber Risk Icon For Computer SecurityIntroducing our premium set of slides with Monitoring Cyber Risk Icon For Computer Security Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Monitoring Cyber Risk, Computer Security. So download instantly and tailor it with your information.
-
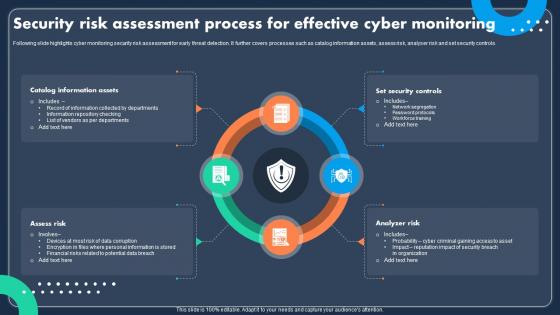 Security Risk Assessment Process For Effective Cyber Monitoring
Security Risk Assessment Process For Effective Cyber MonitoringFollowing slide highlights cyber monitoring security risk assessment for early threat detection. It further covers processes such as catalog information assets, assess risk, analyser risk and set security controls. Introducing our premium set of slides with Security Risk Assessment Process For Effective Cyber Monitoring Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Assets, Security Controls, Analyzer Risk. So download instantly and tailor it with your information.
-
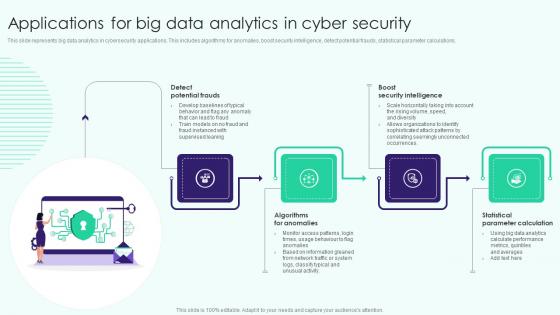 Applications For Big Data Analytics In Cyber Security
Applications For Big Data Analytics In Cyber SecurityThis slide represents big data analytics in cybersecurity applications. This includes algorithms for anomalies, boost security intelligence, detect potential frauds, statistical parameter calculations. Presenting our set of slides with name Applications For Big Data Analytics In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detect Potential Frauds, Algorithms For Anomalies, Statistical Parameter Calculation .
-
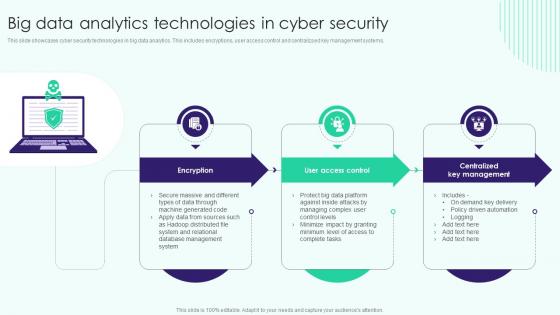 Big Data Analytics Technologies In Cyber Security
Big Data Analytics Technologies In Cyber SecurityThis slide showcases cyber security technologies in big data analytics. This includes encryptions, user access control and centralizsed key management systems. Presenting our set of slides with name Big Data Analytics Technologies In Cyber Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Big Data Analytics, Centralized Key Management, Technologies In Cyber Security.
-
 Best Practices Of Csirt Cyber Security
Best Practices Of Csirt Cyber SecurityThis slide provides best practices of CSIRT cyber security. The main purpose of this template is showcasing various strategies for enhancing cyber security. This includes clear protocol, regular training , etc. Presenting our set of slides with Best Practices Of Csirt Cyber Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Incident Detection, Security Protocol, Potential Vulnerability.
-
 Comparative Analysis Of Csirt And Soc Cyber Security
Comparative Analysis Of Csirt And Soc Cyber SecurityThis slide showcases difference between CSIRT and SOC cyber security. The main purpose of this template is assisting business in determining most suitable approach for cyber security. This I Introducing our premium set of slides with Comparative Analysis Of Csirt And Soc Cyber Security. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Through Investigation, Analysis And Improvement, Forensics Analysis. So download instantly and tailor it with your information.



