Powerpoint Templates and Google slides for Cyber Security It
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Csirt Cyber Security Icon For Data Safety
Csirt Cyber Security Icon For Data SafetyPresenting our set of slides with Csirt Cyber Security Icon For Data Safety. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Csirt Cyber Security, Data Safety.
-
 Csirt Cyber Security Icon For Protecting Data
Csirt Cyber Security Icon For Protecting DataIntroducing our premium set of slides with Csirt Cyber Security Icon For Protecting Data. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Csirt Cyber Security, Protecting Data. So download instantly and tailor it with your information.
-
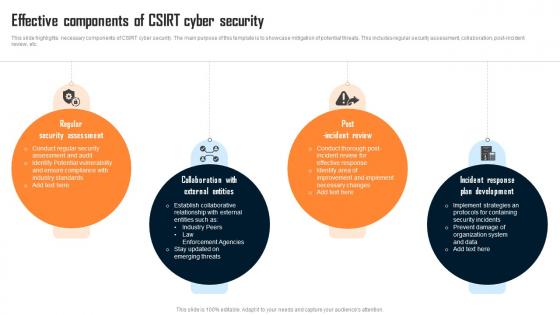 Effective Components Of Csirt Cyber Security
Effective Components Of Csirt Cyber SecurityThis slide highlights necessary components of CSIRT cyber security. The main purpose of this template is to showcase mitigation of potential threats. This includes regular security assessment, collaboration, post incident review, etc. Presenting our set of slides with Effective Components Of Csirt Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Assessment, External Entities, Incident Review.
-
 Organizational Csirt Cyber Security System
Organizational Csirt Cyber Security SystemThis slide showcases framework of CSIRT cyber security. The main purpose of this template is conflicting management and collective learning. This includes technology, CSIRT processes, CSIRT level situation, etc. Introducing our Organizational Csirt Cyber Security System set of slides. The topics discussed in these slides are Event Management, Conflict Management, Collective Learning. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
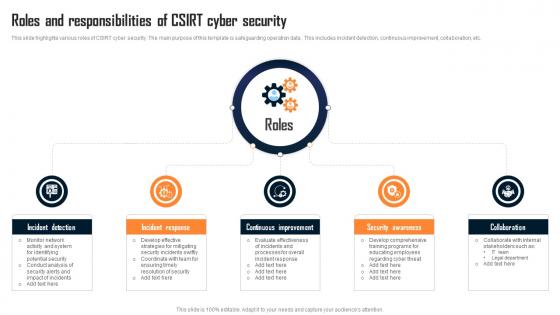 Roles And Responsibilities Of Csirt Cyber Security
Roles And Responsibilities Of Csirt Cyber SecurityThis slide highlights various roles of CSIRT cyber security. The main purpose of this template is safeguarding operation data . This includes incident detection, continuous improvement, collaboration, etc. Introducing our premium set of slides with Roles And Responsibilities Of Csirt Cyber Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Incident Detection, Incident Response, Continuous Improvement. So download instantly and tailor it with your information.
-
 Various Types Of Csirt Cyber Security
Various Types Of Csirt Cyber SecurityThis slide highlights different types of CSIRT cyber security. The main purpose of this template is showcasing various approaches of dealing with cyber security. This includes internal CSIRT, National CSIRT, Vendor CSIRT, etc. Presenting our set of slides with Various Types Of Csirt Cyber Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Maintaining Data, Cyber Threat, Cyber Security.
-
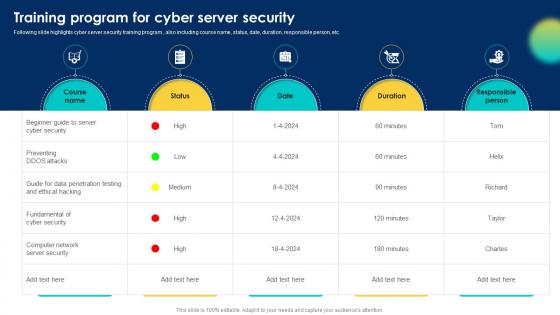 Training Program For Cyber Server Security
Training Program For Cyber Server SecurityFollowing slide highlights cyber server security training program , also including course name, status, date, duration, responsible person, etc. Presenting our well structured Training Program For Cyber Server Security. The topics discussed in this slide are Cyber Security, Server Security, Ethical Hacking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
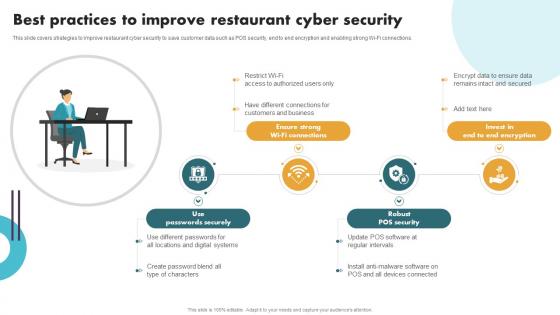 Securing Food Safety In Online Best Practices To Improve Restaurant Cyber Security
Securing Food Safety In Online Best Practices To Improve Restaurant Cyber SecurityThis slide covers strategies to improve restaurant cyber security to save customer data such as POS security, end to end encryption and enabling strong Wi-Fi connections. Introducing Securing Food Safety In Online Best Practices To Improve Restaurant Cyber Security to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Use Passwords Securely, Ensure Strong Wi-Fi Connections, Robust POS Security, using this template. Grab it now to reap its full benefits.
-
 Securing Food Safety In Online Major Cyber Security Challenges Faced By Restaurant
Securing Food Safety In Online Major Cyber Security Challenges Faced By RestaurantThis slide covers cyber security issues faced by restaurant businesses such as lack of uniformity in digital systems, untrained employees and ineffective POS system. Introducing Securing Food Safety In Online Major Cyber Security Challenges Faced By Restaurant to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Lack Of Uniformity In Digital Systems, Ineffective Security Management Software, Untrained Employees, Loop Holes In POS System, using this template. Grab it now to reap its full benefits.
-
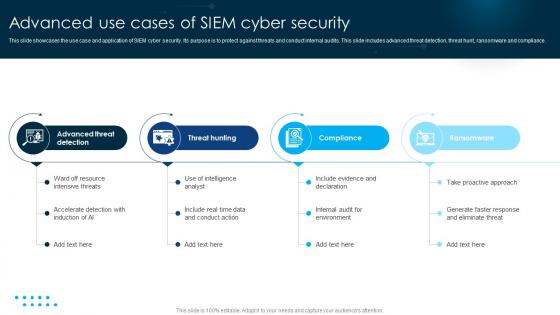 Advanced Use Cases Of SIEM Cyber Security
Advanced Use Cases Of SIEM Cyber SecurityThis slide showcases the use case and application of SIEM cyber security. Its purpose is to protect against threats and conduct internal audits. This slide includes advanced threat detection, threat hunt, ransomware and compliance. Presenting our set of slides with name Advanced Use Cases Of SIEM Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Advanced Threat Detection, Threat Hunting, Compliance.
-
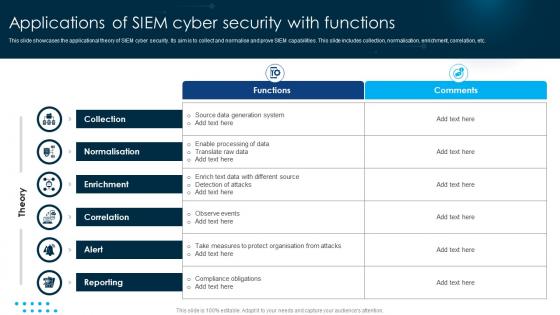 Applications Of SIEM Cyber Security With Functions
Applications Of SIEM Cyber Security With FunctionsThis slide showcases the applicational theory of SIEM cyber security. Its aim is to collect and normalise and prove SIEM capabilities. This slide includes collection, normalisation, enrichment, correlation, etc. Introducing our Applications Of SIEM Cyber Security With Functions set of slides. The topics discussed in these slides are Collection, Enrichment, Correlation . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Benefits Of Including SIEM Cyber Security
Benefits Of Including SIEM Cyber SecurityThis slide showcases the benefits of SIEM cyber security. Its aim is to make business capable of security workflow. This slide includes analysis of data, efficiency, value, tools, productivity and cybersecurity. Presenting our set of slides with name Benefits Of Including SIEM Cyber Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Increases Efficiency, Incident Response Tools, Reduce Cybersecurity.
-
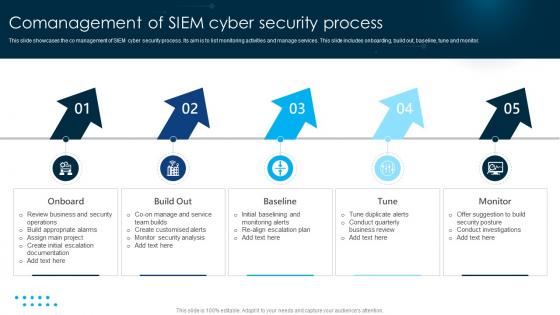 Comanagement Of SIEM Cyber Security Process
Comanagement Of SIEM Cyber Security ProcessThis slide showcases the co management of SIEM cyber security process. Its aim is to list monitoring activities and manage services. This slide includes onboarding, build out, baseline, tune and monitor. Introducing our premium set of slides with name Comanagement Of SIEM Cyber Security Process. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Onboard, Build Out, Baseline. So download instantly and tailor it with your information.
-
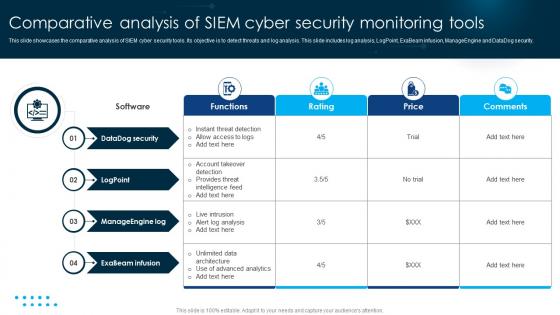 Comparative Analysis Of SIEM Cyber Security Monitoring Tools
Comparative Analysis Of SIEM Cyber Security Monitoring ToolsThis slide showcases the comparative analysis of SIEM cyber security tools. Its objective is to detect threats and log analysis. This slide includes log analysis, LogPoint, ExaBeam infusion, ManageEngine and DataDog security. Presenting our well structured Comparative Analysis Of SIEM Cyber Security Monitoring Tools. The topics discussed in this slide are Datadog Security, Logpoint, Manageengine Log. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
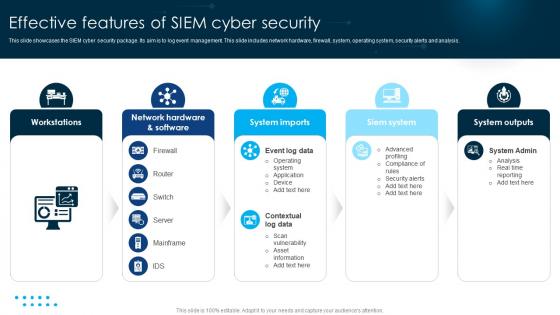 Effective Features Of SIEM Cyber Security
Effective Features Of SIEM Cyber SecurityThis slide showcases the SIEM cyber security package. Its aim is to log event management. This slide includes network hardware, firewall, system, operating system, security alerts and analysis. Introducing our premium set of slides with name Effective Features Of SIEM Cyber Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Workstations, System Imports, Siem System. So download instantly and tailor it with your information.
-
 Evolution Of Technological SIEM Cyber Security
Evolution Of Technological SIEM Cyber SecurityThis slide showcases the evolution of technology SIEM cyber security. Its aim is to set rule and awareness for threat data management. This slide includes machine learning, risk management, rules, event, etc. Presenting our set of slides with name Evolution Of Technological SIEM Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Early 2000s, Mid 2000s, Late 2000s.
-
 Impact Of Integrating SIEM Cyber Security In Business
Impact Of Integrating SIEM Cyber Security In BusinessThis slide showcases the benefits of incorporation SIEM cyber security. Its objective is to propose a better threat detection system. This slide includes threat detection, staff and less spend. Introducing our premium set of slides with name Impact Of Integrating SIEM Cyber Security In Business. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Better Threat Detection, Fewer Staff, Less Spend. So download instantly and tailor it with your information.
-
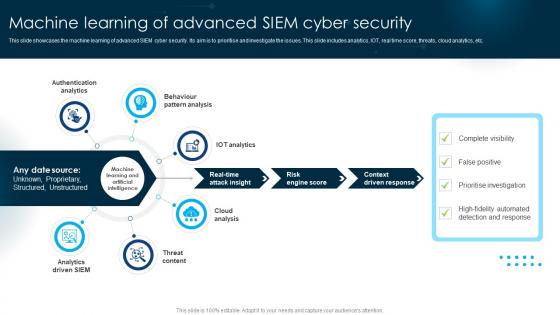 Machine Learning Of Advanced SIEM Cyber Security
Machine Learning Of Advanced SIEM Cyber SecurityThis slide showcases the machine learning of advanced SIEM cyber security. Its aim is to prioritise and investigate the issues. This slide includes analytics, IOT, real time score, threats, cloud analytics, etc. Presenting our set of slides with name Machine Learning Of Advanced SIEM Cyber Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication Analytics, Behaviour Pattern Analysis , IOT Analytics.
-
 Network SIEM Cyber Security Icon
Network SIEM Cyber Security IconIntroducing our Network SIEM Cyber Security Icon set of slides. The topics discussed in these slides are Network SIEM, Cyber Security, Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
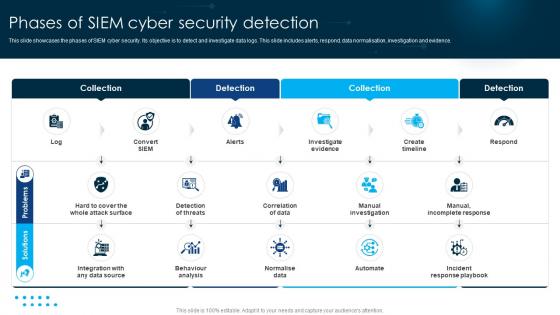 Phases Of SIEM Cyber Security Detection
Phases Of SIEM Cyber Security DetectionThis slide showcases the phases of SIEM cyber security. Its objective is to detect and investigate data logs. This slide includes alerts, respond, data normalisation, investigation and evidence. Presenting our set of slides with name Phases Of SIEM Cyber Security Detection. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Solutions, Problems, Business.
-
 Preparation Of Successful Steps To SIEM Cyber Security
Preparation Of Successful Steps To SIEM Cyber SecurityThis slide showcases the SIEM cyber security plan. Its aim is to manage and prepare the SIEM functions. This slide includes embedding, integration, preparation and success criteria. Introducing our premium set of slides with name Preparation Of Successful Steps To SIEM Cyber Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Success Criteria, Preparation, Integration. So download instantly and tailor it with your information.
-
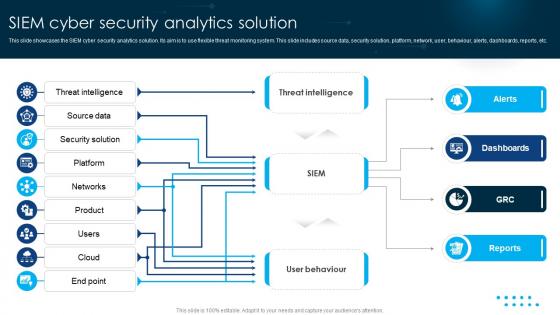 SIEM Cyber Security Analytics Solution
SIEM Cyber Security Analytics SolutionThis slide showcases the SIEM cyber security analytics solution. Its aim is to use flexible threat monitoring system. This slide includes source data, security solution, platform, network, user, behaviour, alerts, dashboards, reports, etc. Presenting our set of slides with name SIEM Cyber Security Analytics Solution. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Intelligence, Source Data, Security Solution.
-
 SIEM Cyber Security Architecture Platform
SIEM Cyber Security Architecture PlatformThis slide showcases the SIEM cyber security architecture. Its aim is to investigate security incidents and detect attacks. This slide includes network traffic, firewall, logs, reports, analyse and investigate. Presenting our set of slides with name SIEM Cyber Security Architecture Platform. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Investigate, Analyse, Reports.
-
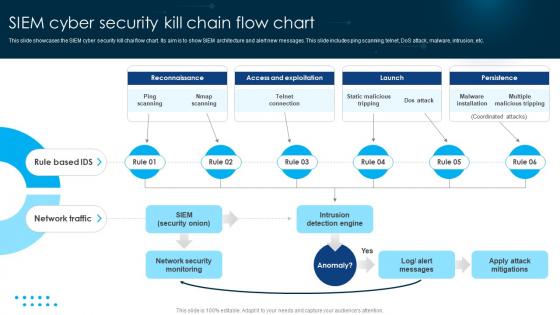 SIEM Cyber Security Kill Chain Flow Chart
SIEM Cyber Security Kill Chain Flow ChartThis slide showcases the SIEM cyber security kill chai flow chart. Its aim is to show SIEM architecture and alert new messages. This slide includes ping scanning, telnet, DoS attack, malware, intrusion, etc. Presenting our set of slides with name SIEM Cyber Security Kill Chain Flow Chart. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ping Scanning, Nmap Scanning, Telnet Connection.
-
 SIEM Cyber Security Protection Icon
SIEM Cyber Security Protection IconIntroducing our premium set of slides with name SIEM Cyber Security Protection Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like SIEM Cyber, Security Protection, Icon. So download instantly and tailor it with your information.
-
 SIEM Data Cyber Security Icon
SIEM Data Cyber Security IconPresenting our set of slides with name SIEM Data Cyber Security Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on SIEM data cyber security icon.
-
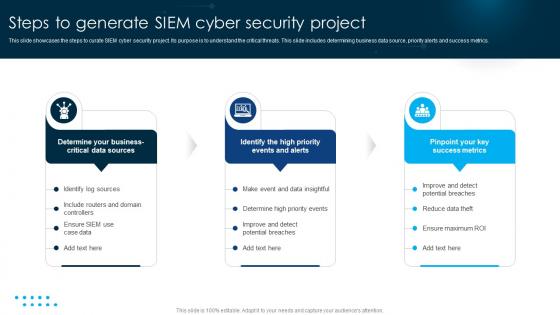 Steps To Generate SIEM Cyber Security Project
Steps To Generate SIEM Cyber Security ProjectThis slide showcases the steps to curate SIEM cyber security project. Its purpose is to understand the critical threats. This slide includes determining business data source, priority alerts and success metrics. Introducing our premium set of slides with name Steps To Generate SIEM Cyber Security Project. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Make Event, Data Insightful, Determine Business Critical. So download instantly and tailor it with your information.
-
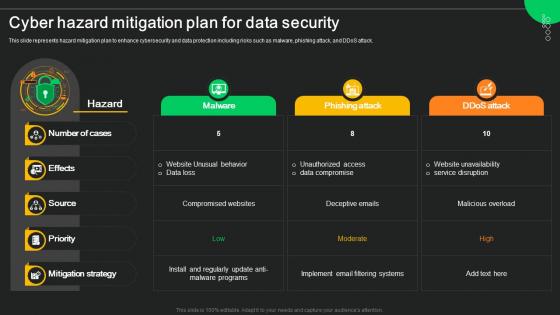 Cyber Hazard Mitigation Plan For Data Security
Cyber Hazard Mitigation Plan For Data SecurityThis slide represents hazard mitigation plan to enhance cybersecurity and data protection including risks such as malware, phishing attack, and DDoS attack. Presenting our well structured Cyber Hazard Mitigation Plan For Data Security. The topics discussed in this slide are Malware, Phishing Attack, Ddos Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
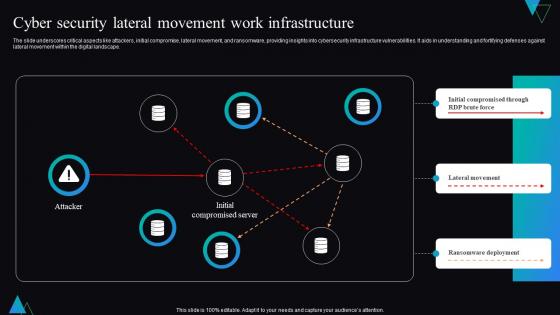 Cyber Security Lateral Movement Work Infrastructure
Cyber Security Lateral Movement Work InfrastructureThe slide underscores critical aspects like attackers, initial compromise, lateral movement, and ransomware, providing insights into cybersecurity infrastructure vulnerabilities. It aids in understanding and fortifying defenses against lateral movement within the digital landscape. Introducing our Cyber Security Lateral Movement Work Infrastructure set of slides. The topics discussed in these slides are Infrastructure, Lateral Movement, Ransomware Deployment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
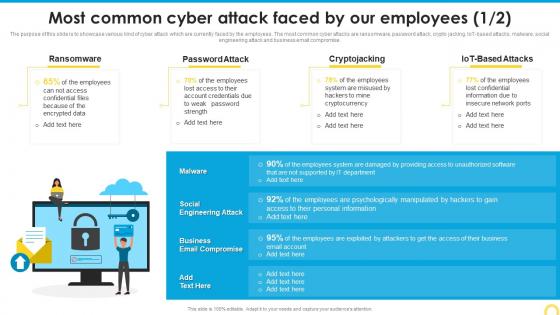 Most Common Cyber Attack Building A Security Awareness Program
Most Common Cyber Attack Building A Security Awareness ProgramThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT based attacks, malware, social engineering attack and business email compromise. Present the topic in a bit more detail with this Most Common Cyber Attack Building A Security Awareness Program. Use it as a tool for discussion and navigation on Ransomware, Password Attack, Cryptojacking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
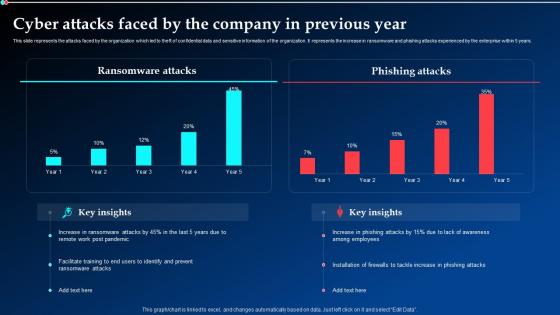 Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration
Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt DemonstrationThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks, Previous Year. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
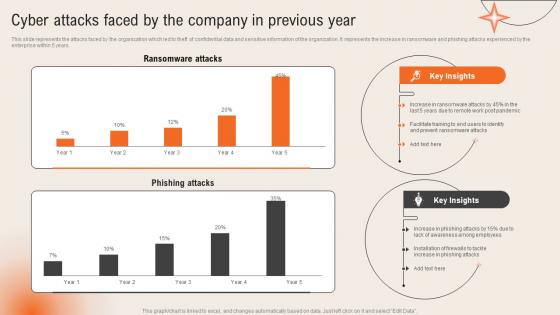 Cyber Attacks Faced By The Company In Previous Year Deploying Computer Security Incident Management
Cyber Attacks Faced By The Company In Previous Year Deploying Computer Security Incident ManagementThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years.Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks, Awareness Among Employees. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
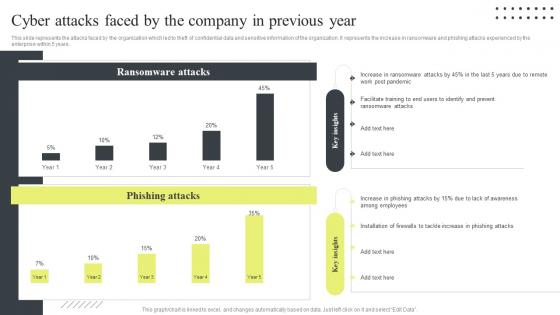 Cyber Security Attacks Response Plan Cyber Attacks Faced By The Company In Previous Year
Cyber Security Attacks Response Plan Cyber Attacks Faced By The Company In Previous YearThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Cyber Attacks Faced By The Company In Previous Year. Dispense information and present a thorough explanation of Ransomware Attacks, Phishing Attacks, Post Pandemic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key benefits of cyber security diagram powerpoint images
Key benefits of cyber security diagram powerpoint imagesPresenting key benefits of cyber security diagram powerpoint images. This is a key benefits of cyber security diagram powerpoint images. This is a eight stage process. The stages in this process are preparation, containment and remediation, malware analysis, campaigns, cyber security, log and event data, advertise, tools and tactics.
-
 Strategic leadership for managing cyber security risks analysis powerpoint slide designs
Strategic leadership for managing cyber security risks analysis powerpoint slide designsPresenting strategic leadership for managing cyber security risks analysis powerpoint slide designs. This is a strategic leadership for managing cyber security risks analysis powerpoint slide designs. This is a three stage process. The stages in this process are threat agents, attack methods, attacker objectives.
-
 Cyber security template ppt background graphics
Cyber security template ppt background graphicsPresenting cyber security template ppt background graphics. This is a cyber security template ppt background graphics. This is a five stage process. The stages in this process are management policy, pro active threat assessment, protect, detect, respond.
-
 Cyber security consulting template ppt slide design
Cyber security consulting template ppt slide designPresenting cyber security consulting template ppt slide design. This is a cyber security consulting template ppt slide design. This is four stage process. The stages in this process are application security, cloud security, respond, monitor.
-
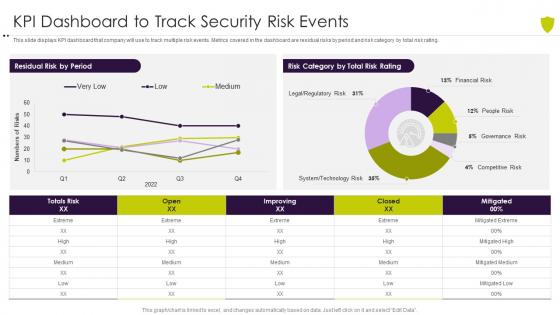 Kpi dashboard to track security risk events managing cyber risk in a digital age
Kpi dashboard to track security risk events managing cyber risk in a digital ageThis slide displays KPI dashboard that company will use to track multiple risk events. Metrics covered in the dashboard are residual risks by period and risk category by total risk rating. Deliver an outstanding presentation on the topic using this Kpi Dashboard To Track Security Risk Events Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of KPI Dashboard To Track Security Risk Events using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
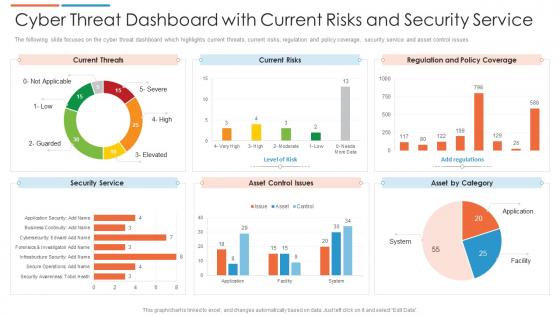 Cyber threat dashboard with current risks and security service
Cyber threat dashboard with current risks and security serviceThe following slide focuses on the cyber threat dashboard which highlights current threats, current risks, regulation and policy coverage, security service and asset control issues. Presenting our well structured Cyber Threat Dashboard With Current Risks And Security Service. The topics discussed in this slide are Current Risks, Current Threats, Security Service. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
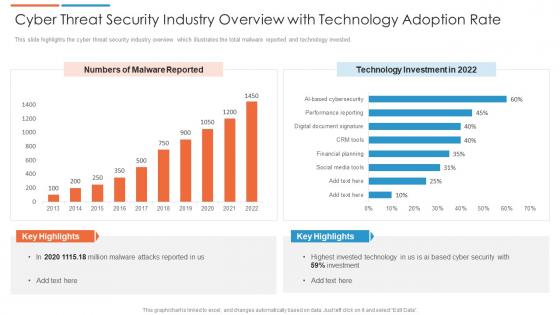 Cyber threat security industry overview with technology adoption rate
Cyber threat security industry overview with technology adoption rateThis slide highlights the cyber threat security industry overview which illustrates the total malware reported and technology invested. Presenting our well structured Cyber Threat Security Industry Overview With Technology Adoption Rate. The topics discussed in this slide are Technology Investment. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
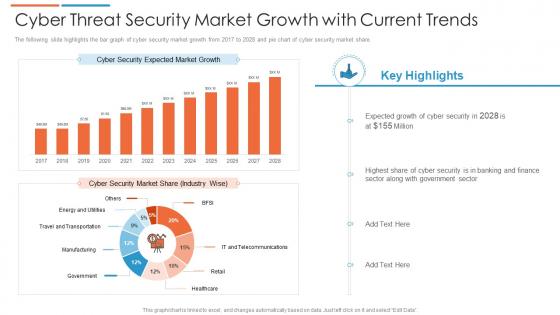 Cyber threat security market growth with current trends
Cyber threat security market growth with current trendsThe following slide highlights the bar graph of cyber security market growth from 2017 to 2028 and pie chart of cyber security market share. Introducing our Cyber Threat Security Market Growth With Current Trends set of slides. The topics discussed in these slides are Cyber Security Market Share, Market Growth, Banking And Finance. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Global Market Insights Cyber Security Risk Based Methodology To Cyber
Global Market Insights Cyber Security Risk Based Methodology To CyberFollowing slide illustrates the global market insights of cybersecurity covering statistics related to integrated risk management, investment in cybersecurity and digital transformation.Present the topic in a bit more detail with this Global Market Insights Cyber Security Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Global Market Insights-Cybersecurity This template is free to edit as deemed fit for your organization. Therefore download it now.
-
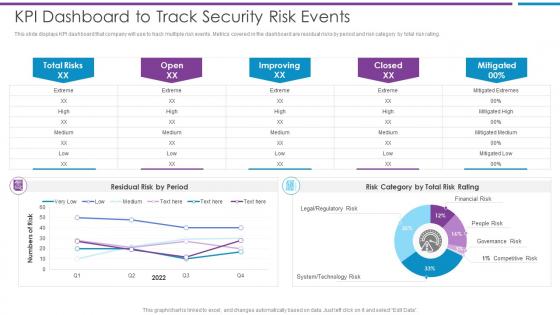 KPI Dashboard To Track Security Risk Events Risk Based Methodology To Cyber
KPI Dashboard To Track Security Risk Events Risk Based Methodology To CyberThis slide displays KPI dashboard that company will use to track multiple risk events. Metrics covered in the dashboard are residual risks by period and risk category by total risk rating.Deliver an outstanding presentation on the topic using this KPI Dashboard To Track Security Risk Events Risk Based Methodology To Cyber Dispense information and present a thorough explanation of KPI Dashboard To Track Security Risk Events using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
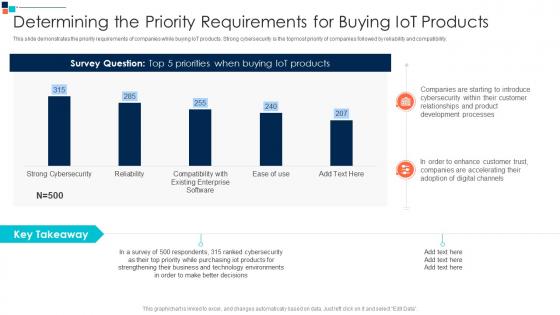 Determining The Priority A Risk Based Approach To Cyber Security
Determining The Priority A Risk Based Approach To Cyber SecurityThis slide demonstrates the priority requirements of companies while buying IoT products. Strong cybersecurity is the topmost priority of companies followed by reliability and compatibility.Deliver an outstanding presentation on the topic using this Determining The Priority A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Companies Are Starting, Relationships And Product, Development Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Global Market Insights Cybersecurity Introducing A Risk Based Approach To Cyber Security
Global Market Insights Cybersecurity Introducing A Risk Based Approach To Cyber SecurityFollowing slide illustrates the global market insights of cybersecurity covering statistics related to integrated risk management, investment in cybersecurity and digital transformation.Present the topic in a bit more detail with this Global Market Insights Cybersecurity Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Fastest Growing Market, Largest Market, Approach To Digital Risk This template is free to edit as deemed fit for your organization. Therefore download it now.
-
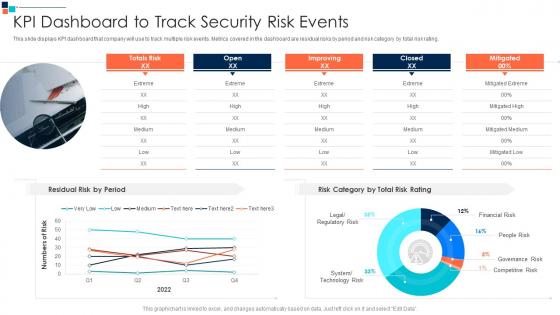 KPI Dashboard To Track Security Risk Events Introducing A Risk Based Approach To Cyber Security
KPI Dashboard To Track Security Risk Events Introducing A Risk Based Approach To Cyber SecurityThis slide displays KPI dashboard that company will use to track multiple risk events. Metrics covered in the dashboard are residual risks by period and risk category by total risk rating.Present the topic in a bit more detail with this KPI Dashboard To Track Security Risk Events Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Kpi Dashboard To Track Security Risk Events This template is free to edit as deemed fit for your organization. Therefore download it now.
-
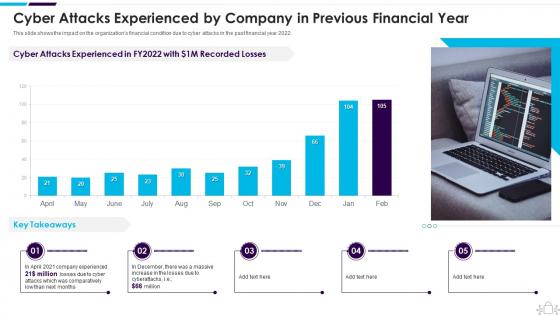 Cyber Attacks Experienced By Company In Previous Information Technology Security
Cyber Attacks Experienced By Company In Previous Information Technology SecurityThis slide shows the impact on the organizations financial condition due to cyber attacks in the past financial year 2022. Present the topic in a bit more detail with this Cyber Attacks Experienced By Company In Previous Information Technology Security. Use it as a tool for discussion and navigation on Experienced, Previous, Financial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
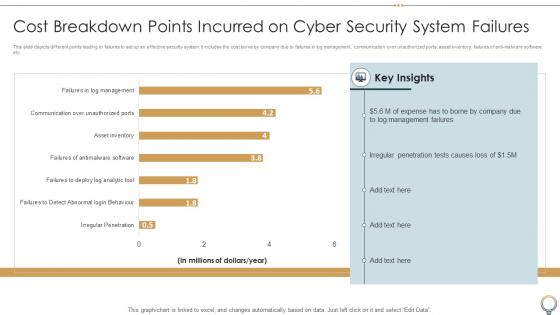 Cost Breakdown Points Incurred On Cyber Security System Failures
Cost Breakdown Points Incurred On Cyber Security System FailuresThis slide depicts different points leading to failures to set up an effective security system. It includes the cost borne by company due to failures in log management, communication over unauthorized ports, asset inventory, failures of anti-malware software, etc. Introducing our Cost Breakdown Points Incurred On Cyber Security System Failures set of slides. The topics discussed in these slides are Cost Breakdown Points, Cyber Security, System Failures. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
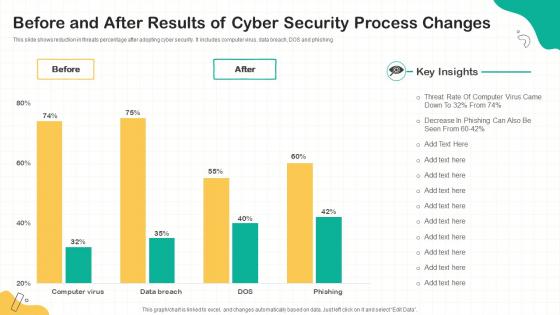 Before And After Results Of Cyber Security Process Changes
Before And After Results Of Cyber Security Process ChangesThis slide shows reduction in threats percentage after adopting cyber security. It includes computer virus, data breach, DOS and phishing. Introducing our Before And After Results Of Cyber Security Process Changes set of slides. The topics discussed in these slides are Computer Virus, Data Breach, DOS. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
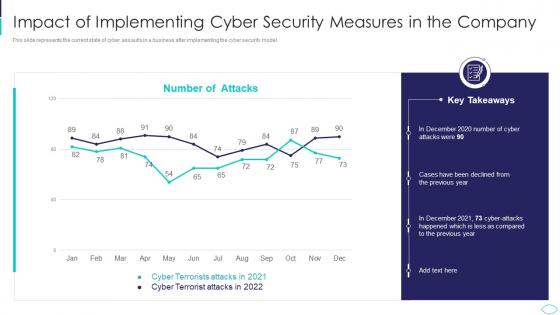 Cyber Terrorism Attacks Impact Of Implementing Cyber Security
Cyber Terrorism Attacks Impact Of Implementing Cyber SecurityThis slide represents the current state of cyber assaults in a business after implementing the cyber security model. Deliver an outstanding presentation on the topic using this Cyber Terrorism Attacks Impact Of Implementing Cyber Security. Dispense information and present a thorough explanation of Impact Of Implementing Cyber Security Measures In The Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
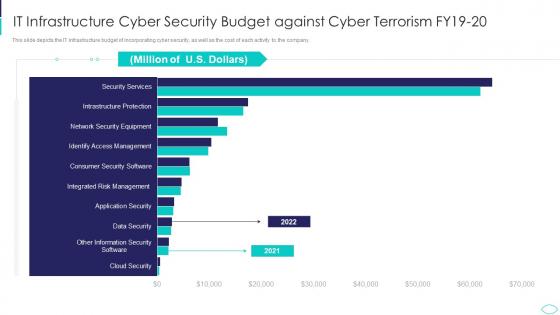 IT Infrastructure Cyber Security Budget Against Cyber Terrorism Attacks
IT Infrastructure Cyber Security Budget Against Cyber Terrorism AttacksThis slide depicts the IT infrastructure budget of incorporating cyber security, as well as the cost of each activity to the company. Present the topic in a bit more detail with this IT Infrastructure Cyber Security Budget Against Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on It Infrastructure Cyber Security Budget Against Cyber Terrorism Fy19 20. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
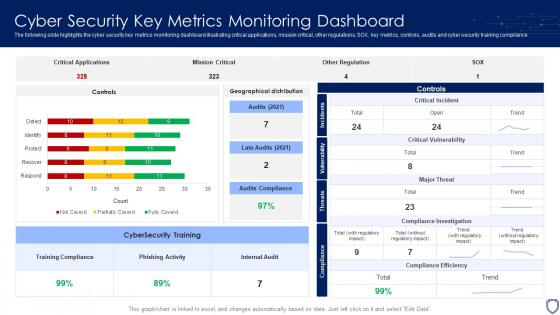 Cyber Security Key Metrics Monitoring Dashboard
Cyber Security Key Metrics Monitoring DashboardThe following slide highlights the cyber security key metrics monitoring dashboard illustrating critical applications, mission critical, other regulations, SOX, key metrics, controls, audits and cyber security training compliance. Introducing our Cyber Security Key Metrics Monitoring Dashboard set of slides. The topics discussed in these slides are Training Compliance, Phishing Activity, Internal Audit. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
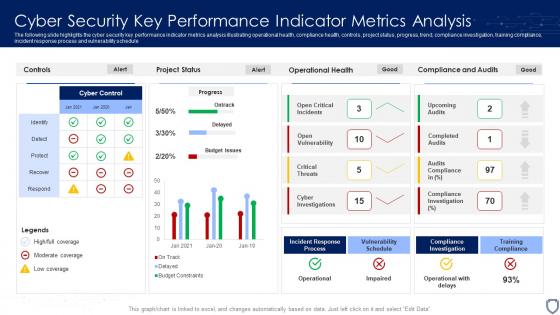 Cyber Security Key Performance Indicator Metrics Analysis
Cyber Security Key Performance Indicator Metrics AnalysisThe following slide highlights the cyber security key performance indicator metrics analysis illustrating operational health, compliance health, controls, project status, progress, trend, compliance investigation, training compliance, incident response process and vulnerability schedule. Presenting our well structured Cyber Security Key Performance Indicator Metrics Analysis. The topics discussed in this slide are Incident Response Process, Vulnerability Schedule, Training Compliance. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
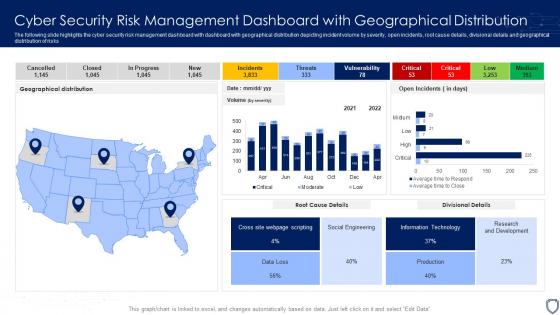 Cyber Security Risk Management Dashboard With Geographical Distribution
Cyber Security Risk Management Dashboard With Geographical DistributionThe following slide highlights the cyber security risk management dashboard with dashboard with geographical distribution depicting incident volume by severity, open incidents, root cause details, divisional details and geographical distribution of risks. Introducing our Cyber Security Risk Management Dashboard With Geographical Distribution set of slides. The topics discussed in these slides are Geographical Distribution, Information Technology, Research And Development. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Threat Activity Discovery Dashboard
Cyber Security Threat Activity Discovery DashboardThe following slide highlights the dashboard for cyber security threat activity discovery to monitor the threats and their management, it includes remote activity security, active remote sessions, threat action, compliance, software patch, asset alarm and threat discovery. Presenting our well structured Cyber Security Threat Activity Discovery Dashboard. The topics discussed in this slide are Cyber Security, Threat Activity, Discovery Dashboard. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
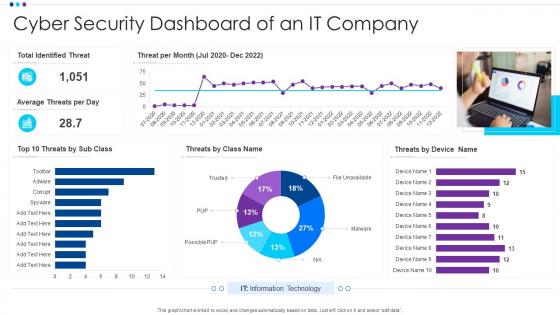 Cyber Security Dashboard Of An It Company
Cyber Security Dashboard Of An It CompanyIntroducing our Cyber Security Dashboard Of An It Company set of slides. The topics discussed in these slides are Identified Threat, Average Threats, Information Technology. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
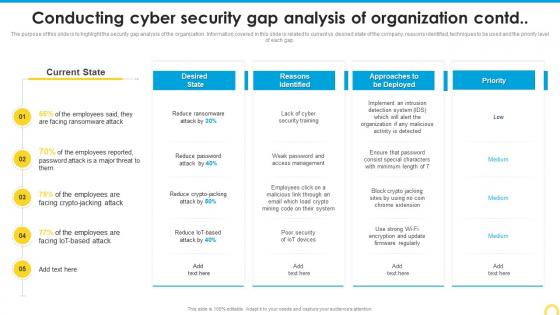 Conducting Cyber Security Building A Security Awareness Program
Conducting Cyber Security Building A Security Awareness ProgramThe purpose of this slide is to highlight the security gap analysis of the organization. Information covered in this slide is related to current vs desired state of the company, reasons identified, techniques to be used and the priority level of each gap. Present the topic in a bit more detail with this Conducting Cyber Security Building A Security Awareness Program. Use it as a tool for discussion and navigation on Reasons Identified, Analysis, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
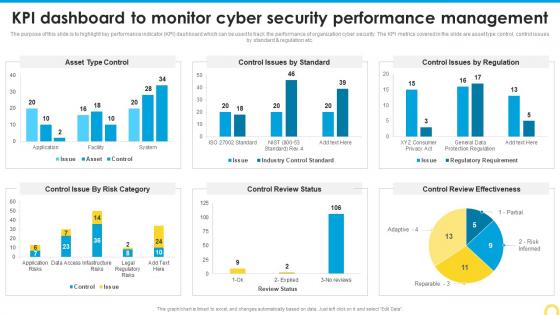 Kpi Dashboard To Monitor Cyber Building A Security Awareness Program
Kpi Dashboard To Monitor Cyber Building A Security Awareness ProgramThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Deliver an outstanding presentation on the topic using this KPI Dashboard To Monitor Cyber Building A Security Awareness Program. Dispense information and present a thorough explanation of Control Review Effectiveness, Performance Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
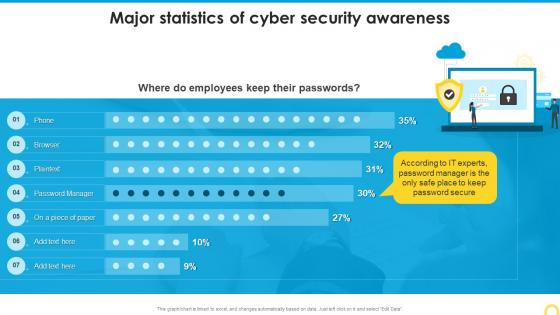 Major Statistics Of Cyber Security Awareness Building A Security Awareness Program
Major Statistics Of Cyber Security Awareness Building A Security Awareness ProgramDeliver an outstanding presentation on the topic using this Major Statistics Of Cyber Security Awareness Building A Security Awareness Program. Dispense information and present a thorough explanation of Major Statistics, Cyber Security Awareness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
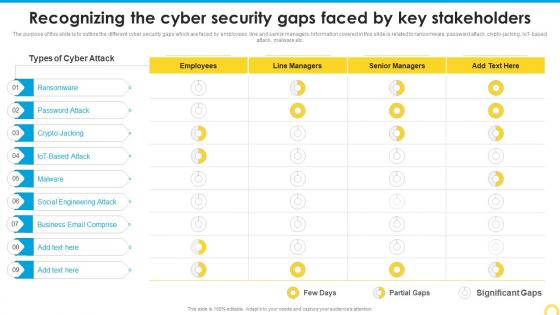 Recognizing The Cyber Security Building A Security Awareness Program
Recognizing The Cyber Security Building A Security Awareness ProgramThe purpose of this slide is to outline the different cyber security gaps which are faced by employees, line and senior managers. Information covered in this slide is related to ransomware, password attack, crypto-jacking, IoT based attack, malware etc. Present the topic in a bit more detail with this Recognizing The Cyber Security Building A Security Awareness Program. Use it as a tool for discussion and navigation on Ransomware, Social Engineering Attack, Business Email Comprise. This template is free to edit as deemed fit for your organization. Therefore download it now.



