Powerpoint Templates and Google slides for Information Security Management
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Q308 IT Professionals Certification Collection Certified Information Systems Security Professional
Q308 IT Professionals Certification Collection Certified Information Systems Security ProfessionalThis slide covers CISSP certification details such as what is the CISSP, how to become certified, how to prepare for CISSP and why to get CISSP certifications. Introducing Q308 IT Professionals Certification Collection Certified Information Systems Security Professional to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on CISS Certification, Network Security, Administrative Activities, using this template. Grab it now to reap its full benefits.
-
 Information Security Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Information security colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Information Security Lock Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Lock Colored Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Information security lock colored icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Information Security Lock Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Lock Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Information security lock monotone icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Information Security Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Information security monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Information Security Shield Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Shield Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Information security shield colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Information Security Shield Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Shield Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Information security shield monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
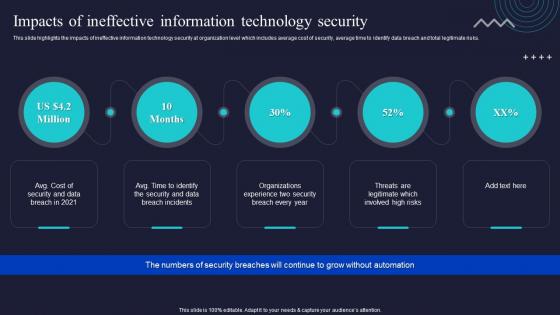 Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security Operations
Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security OperationsThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Increase audience engagement and knowledge by dispensing information using Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security Operations. This template helps you present information on four stages. You can also present information on Ineffective, Information, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
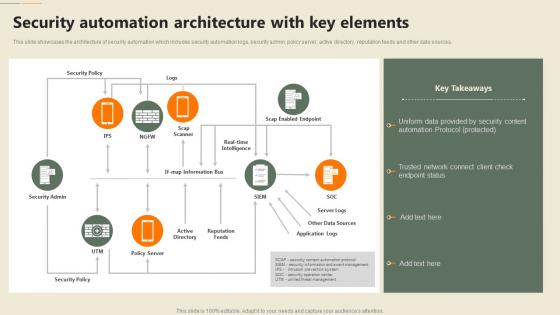 F651 Security Automation In Information Technology Security Automation Architecture With Key Elements
F651 Security Automation In Information Technology Security Automation Architecture With Key ElementsThis slide showcases the architecture of security automation which includes security automation logs, security admin, policy server, active directory, reputation feeds and other data sources. Present the topic in a bit more detail with this F651 Security Automation In Information Technology Security Automation Architecture With Key Elements. Use it as a tool for discussion and navigation on Security, Automation, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
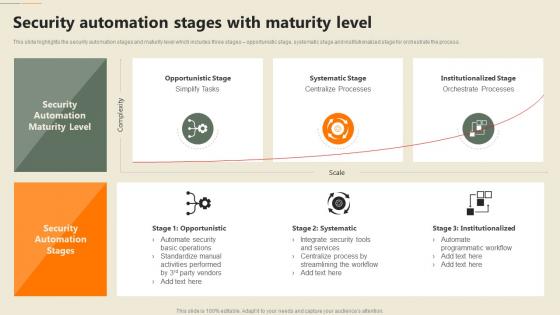 F653 Security Automation In Information Technology Security Automation Stages With Maturity Level
F653 Security Automation In Information Technology Security Automation Stages With Maturity LevelThis slide highlights the security automation stages and maturity level which includes three stages opportunistic stage, systematic stage and institutionalized stage for orchestrate the process. Present the topic in a bit more detail with this F653 Security Automation In Information Technology Security Automation Stages With Maturity Level. Use it as a tool for discussion and navigation on Systematic Stage, Institutionalized Stage, Opportunistic Stage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
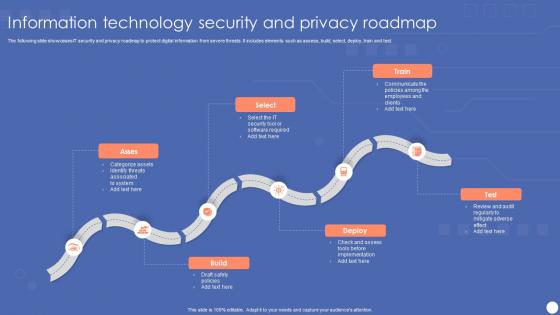 Information Technology Security And Privacy Roadmap
Information Technology Security And Privacy RoadmapThe following slide showcases IT security and privacy roadmap to protect digital information from severe threats. It includes elements such as assess, build, select, deploy, train and test. Introducing our premium set of slides with name Information Technology Security And Privacy Roadmap. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Categorize Assets, Security Tool, Software Required. So download instantly and tailor it with your information.
-
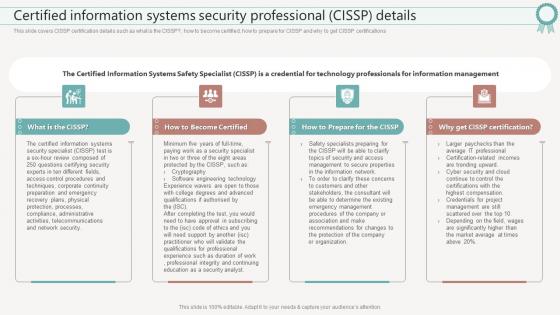 F638 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your Skillset
F638 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your SkillsetThis slide covers CISSP certification details such as what is the CISSP, how to become certified, how to prepare for CISSP and why to get CISSP certifications Deliver an outstanding presentation on the topic using this F638 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your Skillset. Dispense information and present a thorough explanation of Certification, Security Professional, Information Systems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
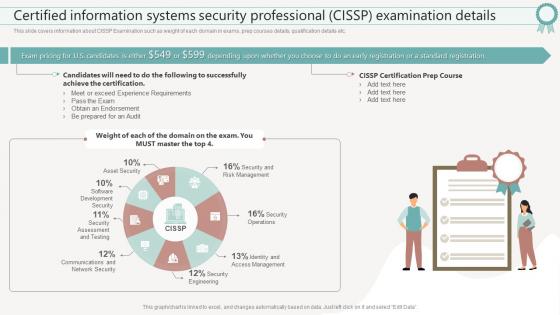 F639 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your Skillset
F639 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your SkillsetThis slide covers information about CISSP Examination such as weight of each domain in exams, prep courses details, qualification details etc. Present the topic in a bit more detail with this F639 Certified Information Systems Security Professional Cissp Details It Certifications To Expand Your Skillset. Use it as a tool for discussion and navigation on Examination, Information, Professional. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
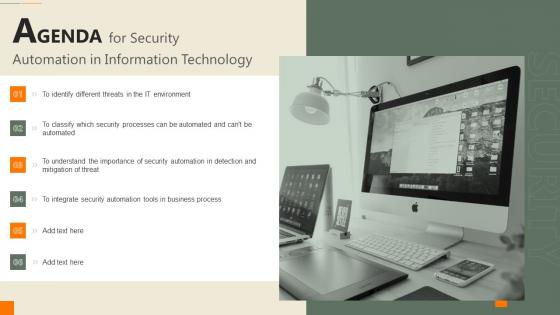 Agenda For Security Automation In Information Technology
Agenda For Security Automation In Information TechnologyIncrease audience engagement and knowledge by dispensing information using Agenda For Security Automation In Information Technology. This template helps you present information on six stages. You can also present information on Business, Process, Importance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determine Ideal Tasks For Security Automation Security Automation In Information Technology
Determine Ideal Tasks For Security Automation Security Automation In Information Technologyslide highlights which tasks and activities can be automated and which required human insights to detect and prevent security threat. It also covers key takeaways section. Present the topic in a bit more detail with this Determine Ideal Tasks For Security Automation Security Automation In Information Technology. Use it as a tool for discussion and navigation on Security Automation, Determine, Sensitive Tasks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
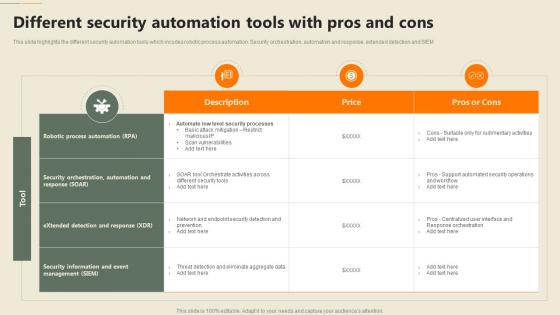 Different Security Automation Tools With Pros And Cons Security Automation In Information Technology
Different Security Automation Tools With Pros And Cons Security Automation In Information TechnologyThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM Deliver an outstanding presentation on the topic using this Different Security Automation Tools With Pros And Cons Security Automation In Information Technology. Dispense information and present a thorough explanation of Automation, Security Orchestration, Process Automation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
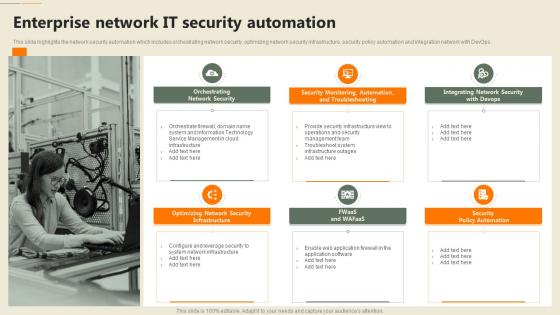 Enterprise Network It Security Automation Security Automation In Information Technology
Enterprise Network It Security Automation Security Automation In Information TechnologyThis slide highlights the network security automation which includes orchestrating network security, optimizing network security infrastructure, security policy automation and integration network with DevOps. Increase audience engagement and knowledge by dispensing information using Enterprise Network It Security Automation Security Automation In Information Technology. This template helps you present information on six stages. You can also present information on Orchestrating Network Security, Security Policy Automation, Infrastructure using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
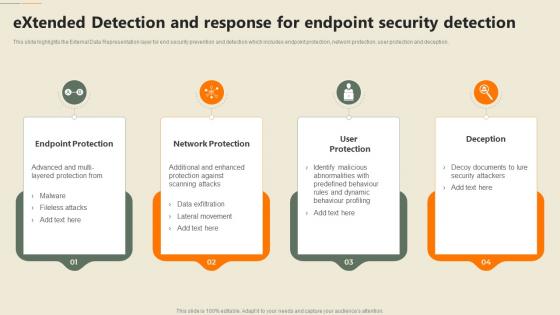 Extended Detection And Response For Endpoint Security Detection Security Automation In Information Technology
Extended Detection And Response For Endpoint Security Detection Security Automation In Information TechnologyThis slide highlights the External Data Representation layer for end security prevention and detection which includes endpoint protection, network protection, user protection and deception. Increase audience engagement and knowledge by dispensing information using Extended Detection And Response For Endpoint Security Detection Security Automation In Information Technology. This template helps you present information on four stages. You can also present information on Endpoint Protection, Network Protection, Deception using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide Security Automation In Information Technology
Icons Slide Security Automation In Information TechnologyPresent the topic in a bit more detail with this Icons Slide Security Automation In Information Technology. Use it as a tool for discussion and navigation on Icons. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
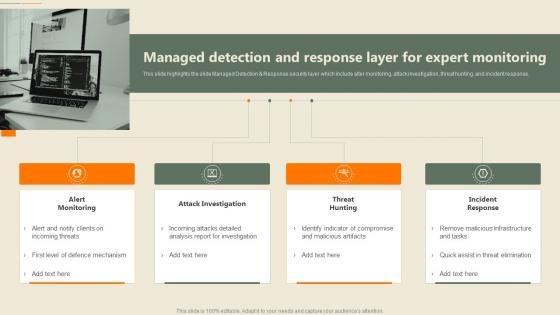 Managed Detection And Response Layer For Expert Monitoring Security Automation In Information Technology
Managed Detection And Response Layer For Expert Monitoring Security Automation In Information TechnologyThis slide highlights the slide Managed Detection and Response security layer which include alter monitoring, attack investigation, threat hunting, and incident response Increase audience engagement and knowledge by dispensing information using Managed Detection And Response Layer For Expert Monitoring Security Automation In Information Technology. This template helps you present information on four stages. You can also present information on Attack Investigation, Incident Response, Threat Hunting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
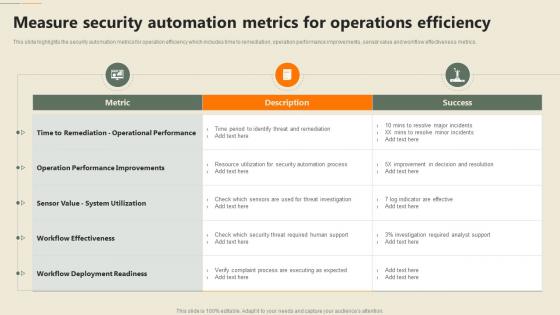 Measure Security Automation Metrics For Operations Efficiency Security Automation In Information Technology
Measure Security Automation Metrics For Operations Efficiency Security Automation In Information TechnologyThis slide highlights the security automation metrics for operation efficiency which includes time to remediation, operation performance improvements, sensor value and workflow effectiveness metrics. Present the topic in a bit more detail with this Measure Security Automation Metrics For Operations Efficiency Security Automation In Information Technology. Use it as a tool for discussion and navigation on Automation, Operations Efficiency, Performance Improvements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
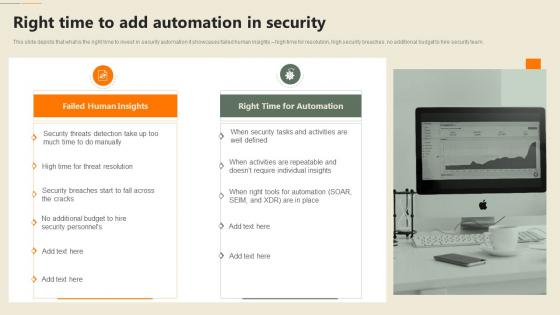 Right Time To Add Automation In Security Security Automation In Information Technology
Right Time To Add Automation In Security Security Automation In Information TechnologyThis slide depicts that what is the right time to invest in security automation it showcases failed human insights high time for resolution, high security breaches, no additional budget to hire security team. Deliver an outstanding presentation on the topic using this Right Time To Add Automation In Security Security Automation In Information Technology. Dispense information and present a thorough explanation of Individual, Insights, Automation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
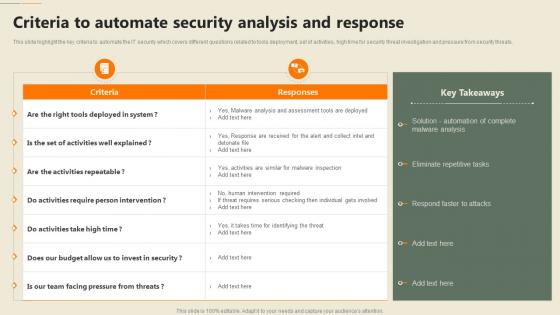 Security Automation In Information Technology Criteria To Automate Security Analysis And Response
Security Automation In Information Technology Criteria To Automate Security Analysis And ResponseThis slide highlight the key criteria to automate the IT security which covers different questions related to tools deployment, set of activities, high time for security threat investigation and pressure from security threats. Present the topic in a bit more detail with this Security Automation In Information Technology Criteria To Automate Security Analysis And Response. Use it as a tool for discussion and navigation on Analysis, Eliminate Repetitive Tasks, Respond Faster To Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Automation In Information Technology Impacts Of Ineffective Information Technology Security
Security Automation In Information Technology Impacts Of Ineffective Information Technology SecurityThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Increase audience engagement and knowledge by dispensing information using Security Automation In Information Technology Impacts Of Ineffective Information Technology Security. This template helps you present information on five stages. You can also present information on Information, Technology, Automation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
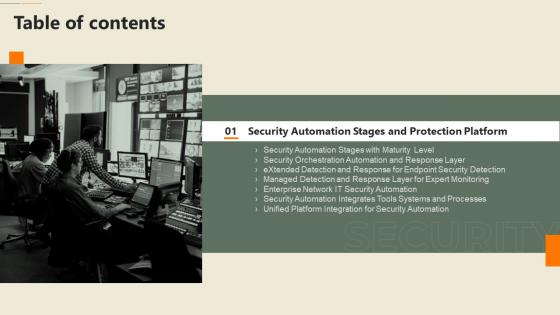 Security Automation In Information Technology Table Of Contents
Security Automation In Information Technology Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Security Automation In Information Technology Table Of Contents. This template helps you present information on one stages. You can also present information on Security Automation, Processes, Security Detection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
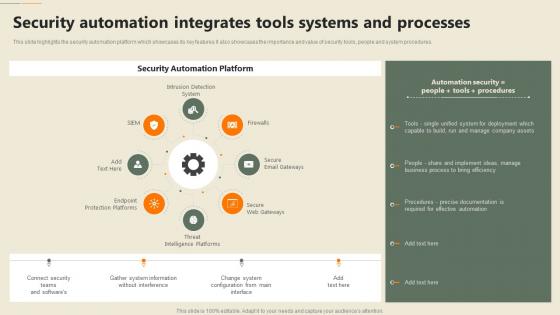 Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology
Security Automation Integrates Tools Systems And Processes Security Automation In Information TechnologyThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Increase audience engagement and knowledge by dispensing information using Security Automation Integrates Tools Systems And Processes Security Automation In Information Technology. This template helps you present information on eight stages. You can also present information on Automation, Integrates, Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
 Security Processes That Cant Be Automated Security Automation In Information Technology
Security Processes That Cant Be Automated Security Automation In Information TechnologyThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Increase audience engagement and knowledge by dispensing information using Security Processes That Cant Be Automated Security Automation In Information Technology. This template helps you present information on three stages. You can also present information on Threat Modeling, Penetration Testing, Bug Bounty using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Security Automation In Information Technology
Table Of Contents Security Automation In Information TechnologyPresent the topic in a bit more detail with this Table Of Contents Security Automation In Information Technology. Use it as a tool for discussion and navigation on Security Automation, Architecture And Importance, Automation Dashboards. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
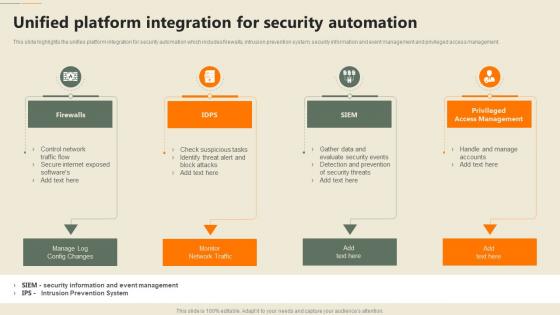 Unified Platform Integration For Security Automation Security Automation In Information Technology
Unified Platform Integration For Security Automation Security Automation In Information TechnologyThis slide highlights the unifies platform integration for security automation which includes firewalls, intrusion prevention system, security information and event management and privileged access management. Increase audience engagement and knowledge by dispensing information using Unified Platform Integration For Security Automation Security Automation In Information Technology. This template helps you present information on four stages. You can also present information on Access Management, Security Automation, Firewalls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
 Why To Automate The It Security Process Security Automation In Information Technology
Why To Automate The It Security Process Security Automation In Information TechnologyThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Security Automation In Information Technology. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security Staffing In Powerpoint And Google Slides Cpb
Information Security Staffing In Powerpoint And Google Slides CpbPresenting our Information Security Staffing In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Information Security Staffing This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
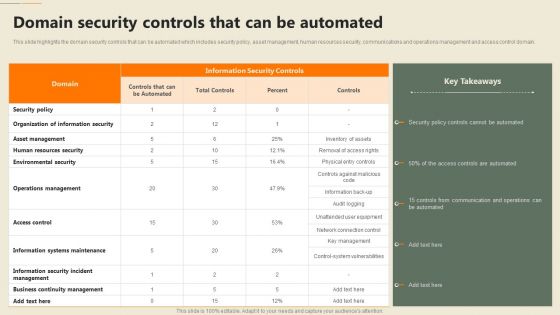 Security Automation In Information Technology Domain Security Controls That Can Be Automated
Security Automation In Information Technology Domain Security Controls That Can Be AutomatedThis slide highlights the domain security controls that can be automated which includes security policy, asset management, human resources security, communications and operations management and access control domain. Present the topic in a bit more detail with this Security Automation In Information Technology Domain Security Controls That Can Be Automated. Use it as a tool for discussion and navigation on Information Security, Organization, Operations Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
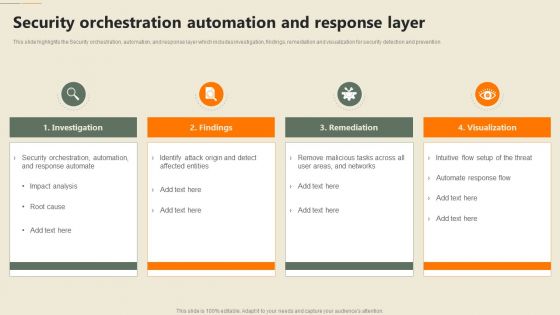 Security Automation In Information Technology Security Orchestration Automation And Response Layer
Security Automation In Information Technology Security Orchestration Automation And Response LayerThis slide highlights the Security orchestration, automation, and response layer which includes investigation, findings, remediation and visualization for security detection and prevention Increase audience engagement and knowledge by dispensing information using Security Automation In Information Technology Security Orchestration Automation And Response Layer. This template helps you present information on four stages. You can also present information on Investigation, Remediation, Visualization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations
-
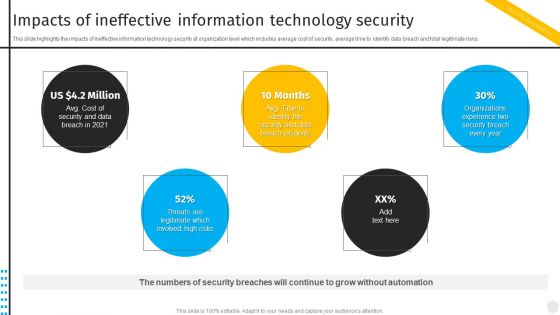 Impacts Of Ineffective Information Technology Security Automation To Investigate And Remediate Cyberthreats
Impacts Of Ineffective Information Technology Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Increase audience engagement and knowledge by dispensing information using Impacts Of Ineffective Information Technology Security Automation To Investigate And Remediate Cyberthreats. This template helps you present information on five stages. You can also present information on Ineffective, Information, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
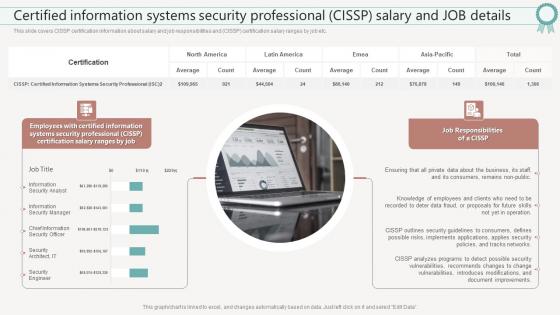 F645 It Certifications To Expand Your Skillset Certified Information Systems Security Professional
F645 It Certifications To Expand Your Skillset Certified Information Systems Security ProfessionalThis slide covers CISSP certification information about salary and job responsibilities and CISSP certification salary ranges by job etc. Deliver an outstanding presentation on the topic using this F645 It Certifications To Expand Your Skillset Certified Information Systems Security Professional. Dispense information and present a thorough explanation of Information, Professional, Responsibilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
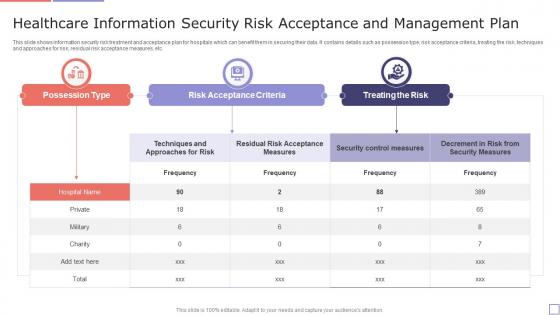 Healthcare Information Security Risk Acceptance And Management Plan
Healthcare Information Security Risk Acceptance And Management PlanThis slide shows information security risk treatment and acceptance plan for hospitals which can benefit them in securing their data. It contains details such as possession type, risk acceptance criteria, treating the risk, techniques and approaches for risk, residual risk acceptance measures, etc. Introducing our Healthcare Information Security Risk Acceptance And Management Plan set of slides. The topics discussed in these slides are Possession Type, Risk Acceptance Criteria, Treating The Risk. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
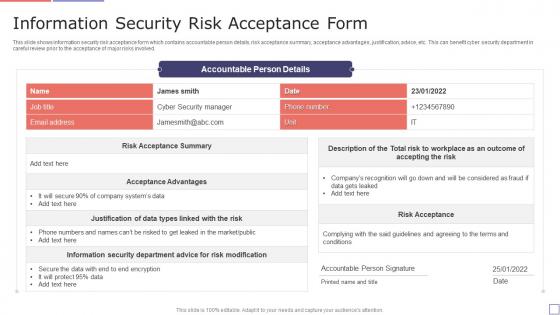 Information Security Risk Acceptance Form
Information Security Risk Acceptance FormThis slide shows information security risk acceptance form which contains accountable person details, risk acceptance summary, acceptance advantages, justification, advice, etc. This can benefit cyber security department in careful review prior to the acceptance of major risks involved. Introducing our Information Security Risk Acceptance Form set of slides. The topics discussed in these slides are Information Security, Risk Acceptance. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data Privacy Vs Data Security Information Privacy Ppt Powerpoint Presentation Summary Grid
Data Privacy Vs Data Security Information Privacy Ppt Powerpoint Presentation Summary GridThis slide compares data privacy with data security, indicating that security is concerned with safeguarding data, and privacy is about responsible data usage.Introducing Data Privacy Vs Data Security Information Privacy Ppt Powerpoint Presentation Summary Grid to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Concerned, Sensitive Information, Security Concerned, using this template. Grab it now to reap its full benefits.
-
 Agenda For Information Security Risk Management And Mitigation Plan Ppt Tips
Agenda For Information Security Risk Management And Mitigation Plan Ppt TipsIntroducing Agenda For Information Security Risk Management And Mitigation Plan Ppt Tips to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Organization, Information Security, Risk Management, using this template. Grab it now to reap its full benefits.
-
 Allocating Budget For Information Security Risk Management Programme
Allocating Budget For Information Security Risk Management ProgrammeThis slide showcase budget to be allocated for conducting training for information security risk management. It showcases budget for area like cybersecurity awareness, threat detection and risk management. Increase audience engagement and knowledge by dispensing information using Allocating Budget For Information Security Risk Management Programme. This template helps you present information on three stages. You can also present information on Functional Areas, Description, Training Cost using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Analysing The Impact Of Security Threats On Organization Information Security Risk Management
Analysing The Impact Of Security Threats On Organization Information Security Risk ManagementDeliver an outstanding presentation on the topic using this Analysing The Impact Of Security Threats On Organization Information Security Risk Management. Dispense information and present a thorough explanation of Analysing, Security Threats, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Analyzing The Impact On Assets Due To Information Breach Information Security Risk Management
Analyzing The Impact On Assets Due To Information Breach Information Security Risk ManagementThis slide showcases impact of information breach on different assets which can help organization in formulating risk monitoring policy. Its key components are criterion, criterion weight and information assets. Present the topic in a bit more detail with this Analyzing The Impact On Assets Due To Information Breach Information Security Risk Management. Use it as a tool for discussion and navigation on Impact On Revenue, Analyzing, Information Breach. This template is free to edit as deemed fit for your organization. Therefore download it now
-
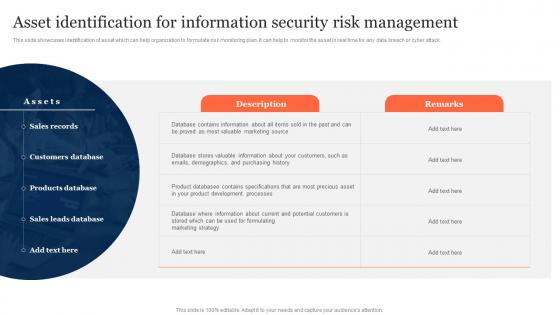 Asset Identification For Information Security Risk Management Ppt Slides
Asset Identification For Information Security Risk Management Ppt SlidesThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help to monitor the asset in real time for any data breach or cyber attack. Present the topic in a bit more detail with this Asset Identification For Information Security Risk Management Ppt Slides. Use it as a tool for discussion and navigation on Sales Records, Customers Database, Products Database. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Assigning Criticality Rating To Information Assets Information Security Risk Management
Assigning Criticality Rating To Information Assets Information Security Risk ManagementThis slide showcases criticality rating that can be allocation to assets for identifying critical assets. Its key elements are asset, failure cost, failure impact and criticality rating. Introducing Assigning Criticality Rating To Information Assets Information Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Sales Records, Customer Database, Product Database, using this template. Grab it now to reap its full benefits.
-
 Budget For Information Security Risk Management Ppt Microsoft
Budget For Information Security Risk Management Ppt MicrosoftThis slide showcases budget that can should be allocated for different information security risk management activities. It provides information about employees training, software implementation, risk monitoring and data backup. Increase audience engagement and knowledge by dispensing information using Budget For Information Security Risk Management Ppt Microsoft. This template helps you present information on one stage. You can also present information on Budget, Information Security, Risk Management using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Challenges And Solutions In Information Security Risk Management
Challenges And Solutions In Information Security Risk ManagementThis slide showcases challenges involved in formulating risk management program for information security. It also shows solutions to tackle the challenges and impact of implementing them. Introducing Challenges And Solutions In Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Fighting Frauds, Internal Vulnerabilities, Employee Awareness, using this template. Grab it now to reap its full benefits.
-
 Checklist For Information Security Risk Management Ppt Microsoft
Checklist For Information Security Risk Management Ppt MicrosoftThis slide showcases checklist that can help to ensure formulate and implementing data security risk management program in organization. Its key components are activity, assigned to and status. Deliver an outstanding presentation on the topic using this Checklist For Information Security Risk Management Ppt Microsoft. Dispense information and present a thorough explanation of Checklist, Information Security, Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Current Information And Data Security Capabilities Of Firm Information Security Risk Management
Current Information And Data Security Capabilities Of Firm Information Security Risk ManagementThis slide showcases current capabilities of organization regarding information and data security. Its key component are risk management functions, required standard rating and actual standard rating. Introducing Current Information And Data Security Capabilities Of Firm Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Risk Management Functions, Required Standard Rating, Actual Standard Rating, using this template. Grab it now to reap its full benefits.
-
 Current Information Security Issues Faced By Organization Information Security Risk Management
Current Information Security Issues Faced By Organization Information Security Risk ManagementIncrease audience engagement and knowledge by dispensing information using Current Information Security Issues Faced By Organization Information Security Risk Management. This template helps you present information on four stages. You can also present information on Untrained Employees, Complex Risk Management Policy, Frequent Data Breaches using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
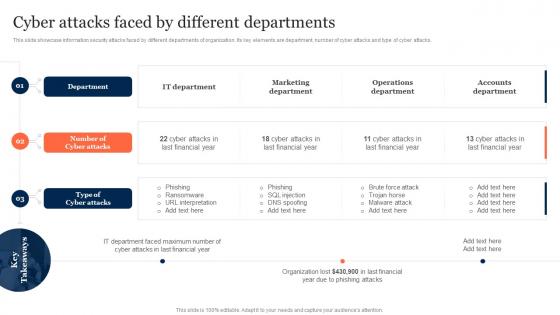 Cyber Attacks Faced By Different Departments Information Security Risk Management
Cyber Attacks Faced By Different Departments Information Security Risk ManagementThis slide showcase information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks. Introducing Cyber Attacks Faced By Different Departments Information Security Risk Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Department, Number Of Cyber Attacks, Type Of Cyber Attacks, using this template. Grab it now to reap its full benefits.
-
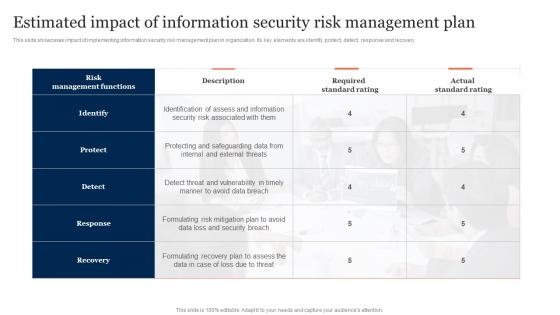 Estimated Impact Of Information Security Risk Management Plan Ppt Grid
Estimated Impact Of Information Security Risk Management Plan Ppt GridThis slide showcases impact of implementing information security risk management plan in organization. Its key elements are identify, protect, detect, response and recovery. Deliver an outstanding presentation on the topic using this Estimated Impact Of Information Security Risk Management Plan Ppt Grid. Dispense information and present a thorough explanation of Risk Management Functions, Required Standard Rating, Actual Standard Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
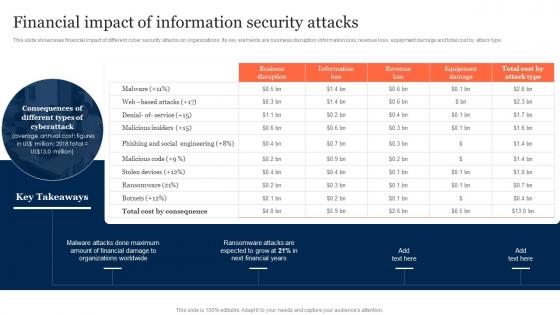 Financial Impact Of Information Security Attacks Information Security Risk Management
Financial Impact Of Information Security Attacks Information Security Risk ManagementThis slide showcases financial impact of different cyber security attacks on organizations. Its key elements are business disruption, information loss, revenue loss, equipment damage and total cost by attack type. Present the topic in a bit more detail with this Financial Impact Of Information Security Attacks Information Security Risk Management. Use it as a tool for discussion and navigation on Malicious Insiders, Social Engineering, Information Security Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now
-
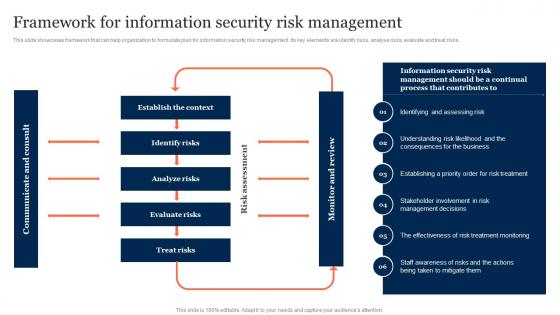 Framework For Information Security Risk Management Information Security Risk Management
Framework For Information Security Risk Management Information Security Risk ManagementThis slide showcases framework that can help organization to formulate plan for information security risk management. Its key elements are identify risks, analyse risks, evaluate and treat risks. Deliver an outstanding presentation on the topic using this Framework For Information Security Risk Management Information Security Risk Management. Dispense information and present a thorough explanation of Identify Risks, Analyze Risks, Evaluate Risks, Treat Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
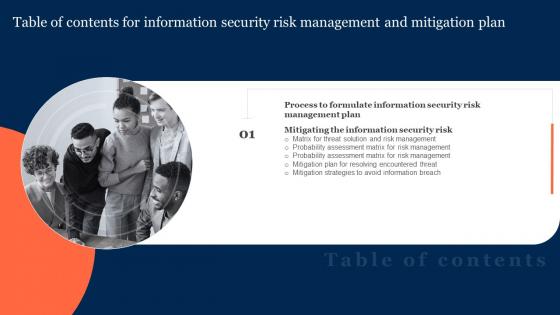 G9 Table Of Contents For Information Security Risk Management And Mitigation Plan
G9 Table Of Contents For Information Security Risk Management And Mitigation PlanIntroducing G9 Table Of Contents For Information Security Risk Management And Mitigation Plan to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Information Security Risk, Management Plan, Process, using this template. Grab it now to reap its full benefits.
-
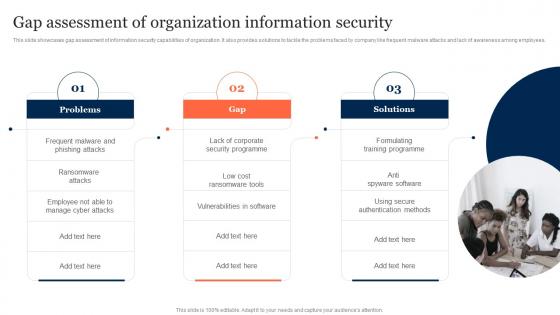 Gap Assessment Of Organization Information Security Information Security Risk Management
Gap Assessment Of Organization Information Security Information Security Risk ManagementThis slide showcases gap assessment of information security capabilities of organization. It also provides solutions to tackle the problems faced by company like frequent malware attacks and lack of awareness among employees. Increase audience engagement and knowledge by dispensing information using Gap Assessment Of Organization Information Security Information Security Risk Management. This template helps you present information on three stages. You can also present information on Gap Assessment, Organization Information Security, Ransomware Attacks using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Icons Slide Information Security Risk Management And Mitigation Plan
Icons Slide Information Security Risk Management And Mitigation PlanPresenting our well crafted Icons Slide Information Security Risk Management And Mitigation Plan set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly
-
 Identifying Employees For Information Information Security Risk Management
Identifying Employees For Information Information Security Risk ManagementThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner. Introducing Identifying Employees For Information Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Threat Scanning, Identifying Employees, Security Training Programme, using this template. Grab it now to reap its full benefits.
-
 Identifying Information Security Threats And Impact Information Security Risk Management
Identifying Information Security Threats And Impact Information Security Risk ManagementThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Increase audience engagement and knowledge by dispensing information using Identifying Information Security Threats And Impact Information Security Risk Management. This template helps you present information on one stage. You can also present information on Errors And Omissions, Employee Sabotage, Physical Infrastructure Loss using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Impact Of Information Security Loss On Organization Information Security Risk Management
Impact Of Information Security Loss On Organization Information Security Risk ManagementIntroducing Impact Of Information Security Loss On Organization Information Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Financial Loss To Organization, Loss Of Productivity, Reputational Loss, using this template. Grab it now to reap its full benefits.
-
 Information Security And Risk Management User Information Security Risk Management
Information Security And Risk Management User Information Security Risk ManagementThis slide showcases expenses done by organization in different segments of information security and risk management. Key segments include - application security, cloud security, data security, identify access management, infrastructure protection, integrated risk management, security services etc. Introducing Information Security And Risk Management User Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Marketing Segment, Identity Access Management, Information Security, using this template. Grab it now to reap its full benefits.



