Powerpoint Templates and Google slides for IT Security Admin
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Internet Gateway Security IT Secure Web Gateway Set Up Ongoing
Internet Gateway Security IT Secure Web Gateway Set Up OngoingThis slide represents the procedure for implementing Secure Web Gateway in network. The purpose of this slide is to explain the ongoing maintenance phase of SWG set-up. The key points included are inspect web gateway, examine security policies, etc. Introducing Internet Gateway Security IT Secure Web Gateway Set Up Ongoing to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Inspect Web Gateway, Examine Security Policies, Train Staff And Users, Update And Patch Software, Perform Routine Security Audits, using this template. Grab it now to reap its full benefits.
-
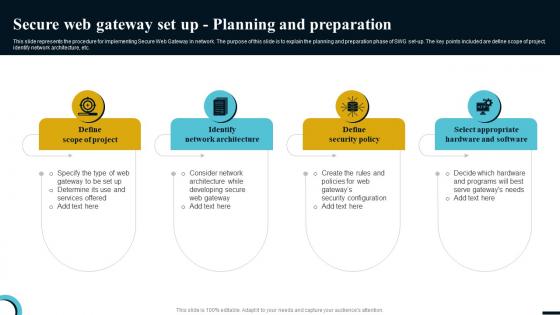 Internet Gateway Security IT Secure Web Gateway Set Up Planning
Internet Gateway Security IT Secure Web Gateway Set Up PlanningThis slide represents the procedure for implementing Secure Web Gateway in network. The purpose of this slide is to explain the planning and preparation phase of SWG set-up. The key points included are define scope of project, identify network architecture, etc. Introducing Internet Gateway Security IT Secure Web Gateway Set Up Planning to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Define Scope Of Project, Identify Network Architecture, Define Security Policy, Select Appropriate Hardware And Software, using this template. Grab it now to reap its full benefits.
-
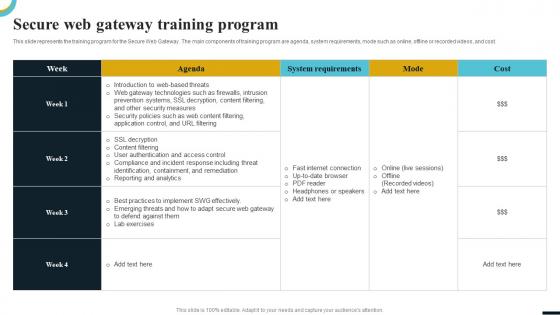 Internet Gateway Security IT Secure Web Gateway Training Program
Internet Gateway Security IT Secure Web Gateway Training ProgramThis slide represents the training program for the Secure Web Gateway. The main components of training program are agenda, system requirements, mode such as online, offline or recorded videos, and cost. Present the topic in a bit more detail with this Internet Gateway Security IT Secure Web Gateway Training Program. Use it as a tool for discussion and navigation on Agenda, System Requirements, Mode, Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
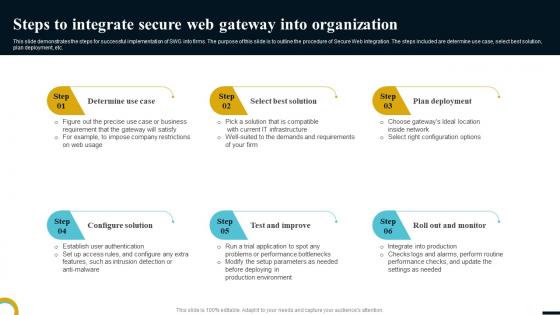 Internet Gateway Security IT Steps To Integrate Secure Web Gateway
Internet Gateway Security IT Steps To Integrate Secure Web GatewayThis slide demonstrates the steps for successful implementation of SWG into firms. The purpose of this slide is to outline the procedure of Secure Web integration. The steps included are determine use case, select best solution, plan deployment, etc. Introducing Internet Gateway Security IT Steps To Integrate Secure Web Gateway to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Determine Use Case, Select Best Solution, Plan Deployment, Configure Solution, Test And Improve, Roll Out And Monitor, using this template. Grab it now to reap its full benefits.
-
 Internet Gateway Security IT Steps To Select Next Generation Secure Web
Internet Gateway Security IT Steps To Select Next Generation Secure WebThis slide demonstrates the points to be kept in mind while choosing next generation secure web gateway. The purpose of this slide is to explain how to select a next generation SWG. These are adopt real cloud architecture, adapts to new threats, etc. Introducing Internet Gateway Security IT Steps To Select Next Generation Secure Web to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Adopt Real Cloud Architecture, Decodes Apps And Cloud Services, Adapts To New Threats, using this template. Grab it now to reap its full benefits.
-
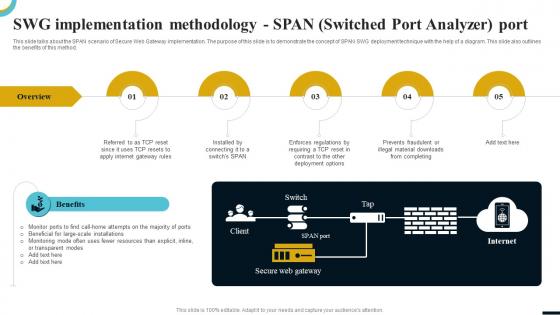 Internet Gateway Security IT Swg Implementation Methodology Span Switched
Internet Gateway Security IT Swg Implementation Methodology Span SwitchedThis slide talks about the SPAN scenario of Secure Web Gateway implementation. The purpose of this slide is to demonstrate the concept of SPAN SWG deployment technique with the help of a diagram. This slide also outlines the benefits of this method. Introducing Internet Gateway Security IT Swg Implementation Methodology Span Switched to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Internet Gateway Rules, Deployment, Monitoring, Transparent Modes, using this template. Grab it now to reap its full benefits.
-
 Internet Gateway Security IT Table Of Contents
Internet Gateway Security IT Table Of ContentsIntroducing Internet Gateway Security IT Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Secure Web Gateway Technology, Industries, using this template. Grab it now to reap its full benefits.
-
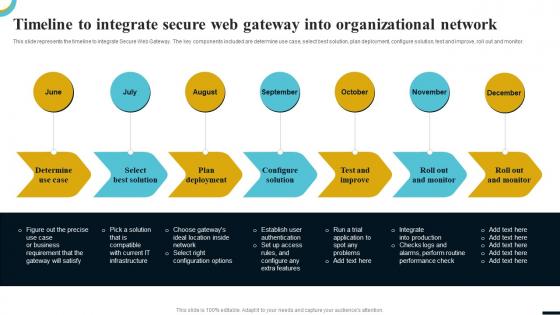 Internet Gateway Security IT Timeline To Integrate Secure Web Gateway
Internet Gateway Security IT Timeline To Integrate Secure Web GatewayThis slide represents the timeline to integrate Secure Web Gateway. The key components included are determine use case, select best solution, plan deployment, configure solution, test and improve, roll out and monitor. Introducing Internet Gateway Security IT Timeline To Integrate Secure Web Gateway to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Determine Use Case, Select Best Solution, Plan Deployment, Configure Solution, Test And Improve, using this template. Grab it now to reap its full benefits.
-
 Internet Gateway Security IT Understanding Real World Use Cases Of Secure
Internet Gateway Security IT Understanding Real World Use Cases Of SecureThis slide outlines the prominent features of Secure Web Gateway which provide protection to organizations from severe cyber threats. The purpose of this slide is to define the use cases of SWG such as real time web traffic surveillance, access management, etc. Introducing Internet Gateway Security IT Understanding Real World Use Cases Of Secure to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Real Time Web Traffic Surveillance, Blocking Of Harmful, Websites And Programs, Access Management, Rule Enforcement, On-Site And Remote Personnel, using this template. Grab it now to reap its full benefits.
-
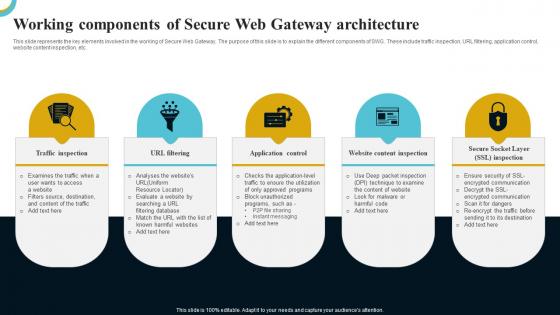 Internet Gateway Security IT Working Components Of Secure Web Gateway
Internet Gateway Security IT Working Components Of Secure Web GatewayThis slide represents the key elements involved in the working of Secure Web Gateway. The purpose of this slide is to explain the different components of SWG. These include traffic inspection, URL filtering, application control, website content inspection, etc. Introducing Internet Gateway Security IT Working Components Of Secure Web Gateway to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Traffic Inspection, URL Filtering, Application Control, Website Content Inspection, Secure Socket Layer SSL Inspection, using this template. Grab it now to reap its full benefits.
-
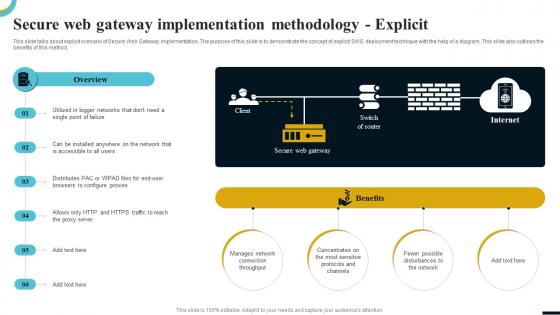 Secure Web Gateway Implementation Internet Gateway Security IT
Secure Web Gateway Implementation Internet Gateway Security ITThis slide talks about explicit scenario of Secure Web Gateway implementation. The purpose of this slide is to demonstrate the concept of explicit SWG deployment technique with the help of a diagram. This slide also outlines the benefits of this method. Introducing Secure Web Gateway Implementation Internet Gateway Security IT to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Manages Network Connection, Concentrates Most Sensitive, Protocols And Channels, Fewer Possible Disturbances Network, using this template. Grab it now to reap its full benefits.
-
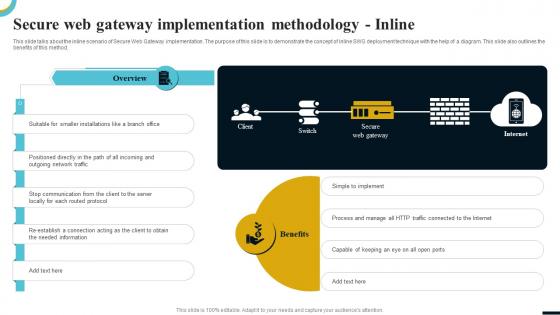 Secure Web Gateway Internet Gateway Security IT
Secure Web Gateway Internet Gateway Security ITThis slide talks about the inline scenario of Secure Web Gateway implementation. The purpose of this slide is to demonstrate the concept of inline SWG deployment technique with the help of a diagram. This slide also outlines the benefits of this method. Introducing Secure Web Gateway Internet Gateway Security IT to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Implement, Process And Manage, HTTP Traffic Connected, Internet, using this template. Grab it now to reap its full benefits.
-
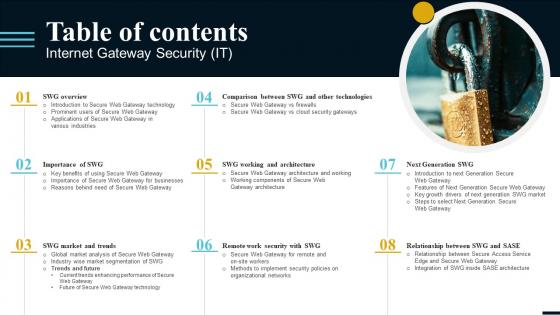 Table Of Contents Internet Gateway Security IT
Table Of Contents Internet Gateway Security ITIntroducing Table Of Contents Internet Gateway Security IT to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on SWG Budget And Training, Case Study And Use Cases, SWG Market And Trends, using this template. Grab it now to reap its full benefits.
-
 Shadow IT Management Lifecycle Overview CASB Cloud Security
Shadow IT Management Lifecycle Overview CASB Cloud SecurityThis slide outlines the lifecycle of shadow IT management for safely adopting cloud apps. The purpose of this slide is to showcase the various stages of the lifecycle, such as discovering shadow IT, knowing the risk level of apps, evaluating compliance, analyzing usage, governing cloud apps, and continuous monitoring. Introducing Shadow IT Management Lifecycle Overview CASB Cloud Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Evaluate Compliance, Govern Cloud Apps, Continuous Monitoring, Management Lifecycle Overview, using this template. Grab it now to reap its full benefits.
-
 Impact Of Patch Management On IT Security
Impact Of Patch Management On IT SecurityThis slide shows multiple potential results of deploying a patch management process in an organization. It includes regular security updates, feature updates, bug fixes, and prioritization. Presenting our set of slides with name Impact Of Patch Management On IT Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Updates, Features Updates, Bug Fixes.
-
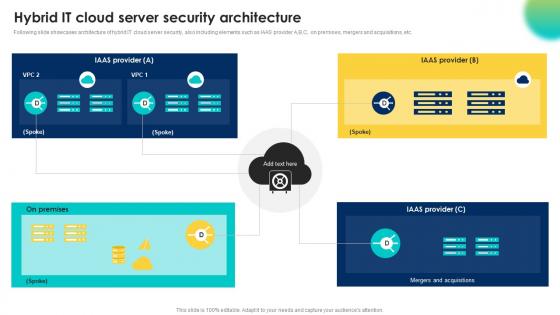 Hybrid It Cloud Server Security Architecture
Hybrid It Cloud Server Security ArchitectureFollowing slide showcases architecture of hybrid IT cloud server security, also including elements such as IAAS provider A,B,C, on premises, mergers and acquisitions, etc. Presenting our set of slides with Hybrid It Cloud Server Security Architecture. This exhibits information on fourstages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on On Premises, Mergers And Acquisitions, Security Architecture.
-
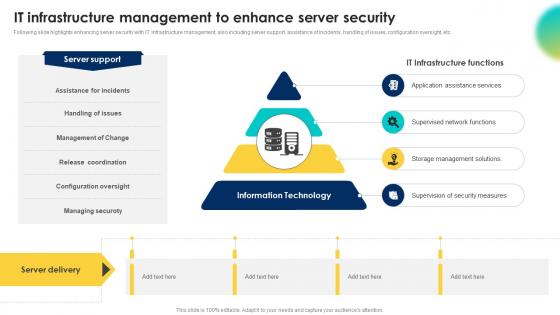 It Infrastructure Management To Enhance Server Security
It Infrastructure Management To Enhance Server SecurityFollowing slide highlights enhancing server security with IT infrastructure management, also including server support, assistance of incidents, handling of issues, configuration oversight, etc. Introducing our premium set of slides with It Infrastructure Management To Enhance Server Security. Ellicudate the fourstages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Supervised Network Functions, Storage Management Solutions, Management Of Change. So download instantly and tailor it with your information.
-
 It security layout example ppt presentation
It security layout example ppt presentationPresenting it security layout example ppt presentation. This is a it security layout example ppt presentation. This is eight stage process. The stages in this process are attack detection, system guard, file lock, process quarantine, passwords, antivirus, application guard, firewall.
-
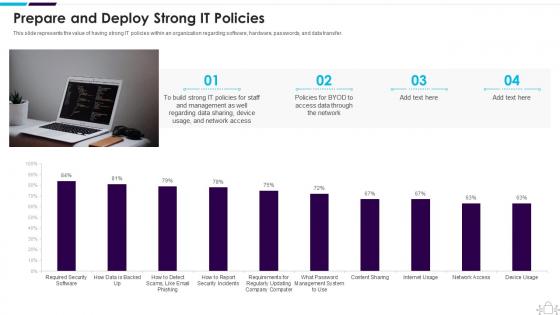 Information Technology Security Prepare And Deploy Strong It Policies
Information Technology Security Prepare And Deploy Strong It PoliciesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Deliver an outstanding presentation on the topic using this Information Technology Security Prepare And Deploy Strong It Policies. Dispense information and present a thorough explanation of Prepare And Deploy Strong IT Policies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
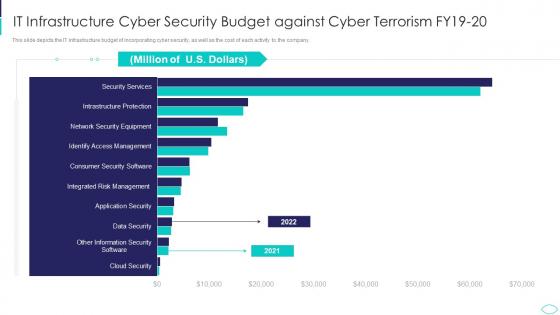 IT Infrastructure Cyber Security Budget Against Cyber Terrorism Attacks
IT Infrastructure Cyber Security Budget Against Cyber Terrorism AttacksThis slide depicts the IT infrastructure budget of incorporating cyber security, as well as the cost of each activity to the company. Present the topic in a bit more detail with this IT Infrastructure Cyber Security Budget Against Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on It Infrastructure Cyber Security Budget Against Cyber Terrorism Fy19 20. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
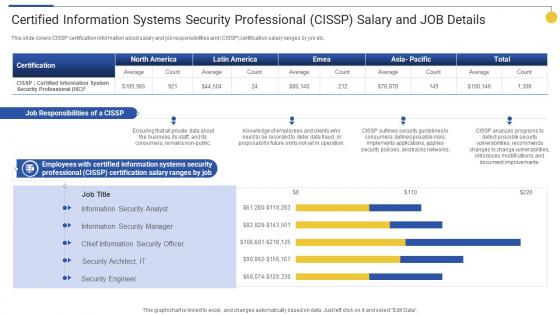 Certified Information Systems Security Top 15 IT Certifications In Demand For 2022
Certified Information Systems Security Top 15 IT Certifications In Demand For 2022This slide covers CISSP certification information about salary and job responsibilities and CISSP certification salary ranges by job etc. Present the topic in a bit more detail with this Certified Information Systems Security Top 15 IT Certifications In Demand For 2022. Use it as a tool for discussion and navigation on Job Responsibilities, Security Professional, Information Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
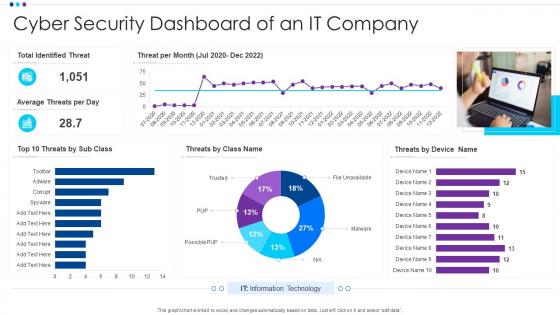 Cyber Security Dashboard Of An It Company
Cyber Security Dashboard Of An It CompanyIntroducing our Cyber Security Dashboard Of An It Company set of slides. The topics discussed in these slides are Identified Threat, Average Threats, Information Technology. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
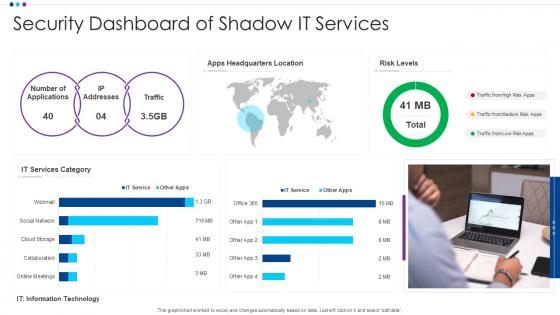 Security Dashboard Of Shadow It Services
Security Dashboard Of Shadow It ServicesPresenting our well structured Security Dashboard Of Shadow IT Services. The topics discussed in this slide are Social Network, It Services, Online Meeting. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
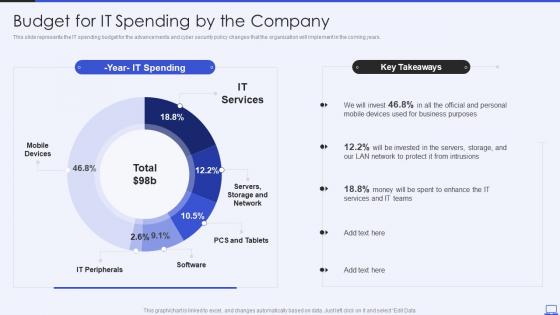 Security Hacker Budget For IT Spending By The Company Ppt Powerpoint Presentation Slides
Security Hacker Budget For IT Spending By The Company Ppt Powerpoint Presentation SlidesThis slide represents the IT spending budget for the advancements and cyber security policy changes that the organization will implement in the coming years. Present the topic in a bit more detail with this Security Hacker Budget For IT Spending By The Company Ppt Powerpoint Presentation Slides. Use it as a tool for discussion and navigation on IT Services, IT Peripherals, Mobile Devices. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
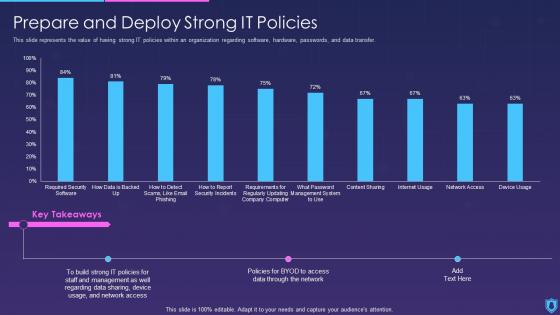 Information Security Prepare And Deploy Strong It Policies
Information Security Prepare And Deploy Strong It PoliciesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Information Security Prepare And Deploy Strong It Policies. Use it as a tool for discussion and navigation on Prepare And Deploy Strong IT Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
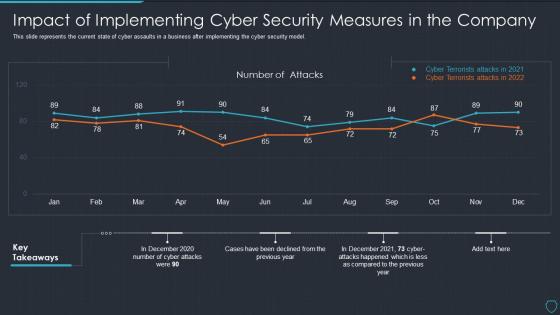 Cyberterrorism it impact of implementing cyber security measures in the company
Cyberterrorism it impact of implementing cyber security measures in the companyThis slide represents the current state of cyber assaults in a business after implementing the cyber security model. Present the topic in a bit more detail with this Cyberterrorism IT Impact Of Implementing Cyber Security Measures In The Company. Use it as a tool for discussion and navigation on Number Attacks, Cyber Terrorists Attacks 2021, Cyber Terrorists Attacks 2022. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
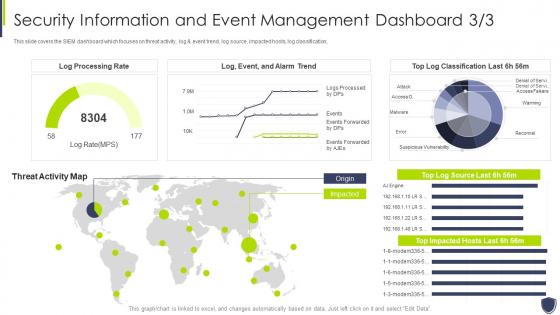 Improve it security vulnerability security information event management dashboard
Improve it security vulnerability security information event management dashboardThis slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification, Deliver an outstanding presentation on the topic using this Improve It Security Vulnerability Security Information Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
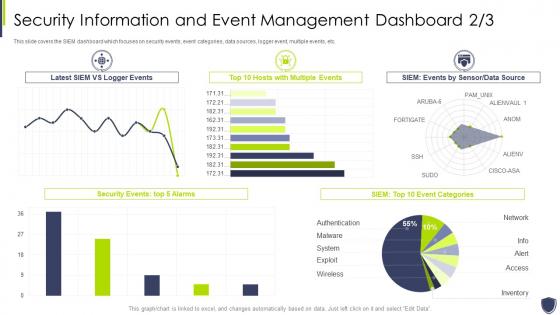 Improve it security with vulnerability event management dashboard snapshot
Improve it security with vulnerability event management dashboard snapshotThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Event Management Dashboard snapshot. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
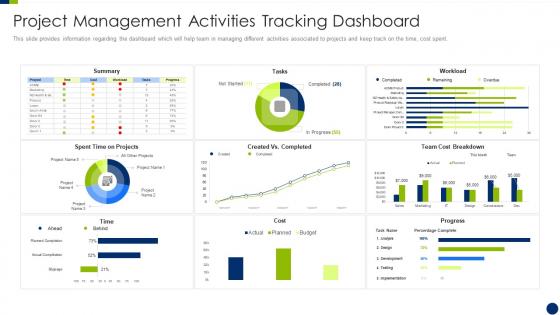 Enhancing overall project security it project management activities tracking dashboard
Enhancing overall project security it project management activities tracking dashboardThis slide provides information regarding the dashboard which will help team in managing different activities associated to projects and keep track on the time, cost spent. Present the topic in a bit more detail with this Enhancing Overall Project Security It Project Management Activities Tracking Dashboard. Use it as a tool for discussion and navigation on Project Management Activities Tracking Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
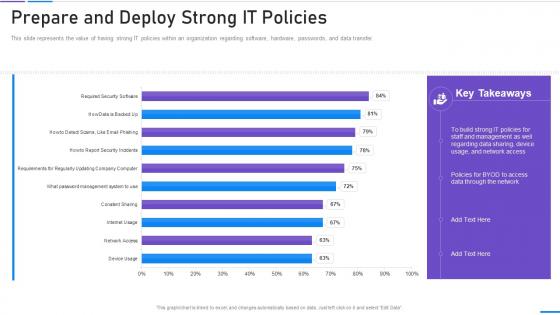 Network Security Prepare And Deploy Strong It Policies
Network Security Prepare And Deploy Strong It PoliciesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Deliver an outstanding presentation on the topic using this Network Security Prepare And Deploy Strong It Policies. Dispense information and present a thorough explanation of Prepare And Deploy Strong It Policies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
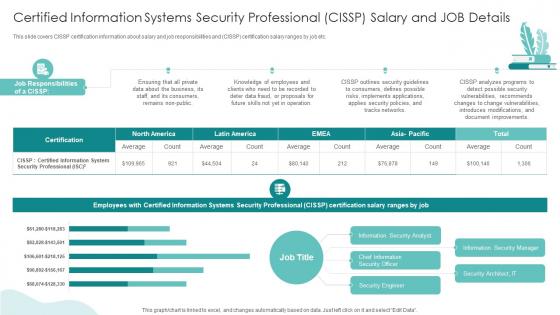 Certified Information Systems Security Professional IT Professionals Certification Collection
Certified Information Systems Security Professional IT Professionals Certification CollectionThis slide covers CISSP certification information about salary and job responsibilities and CISSP certification salary ranges by job etc. Deliver an outstanding presentation on the topic using this Certified Information Systems Security Professional IT Professionals Certification Collection. Dispense information and present a thorough explanation of Job Description, Certification, Employee using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 KPI Dashboard To Track IT Security Performance
KPI Dashboard To Track IT Security PerformanceThis slide shows the dashboard of cyber security with incident and threat management. It includes overall progress, risk identified, number of critical incidents, initiatives, incident and threat management etc. Introducing our KPI Dashboard To Track IT Security Performance set of slides. The topics discussed in these slides are Critital Risks Identified, Incident Management, Threat Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
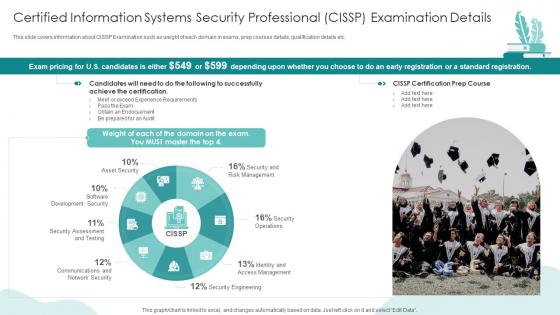 IT Professionals Certification Collection Certified Information Systems Security Professional CISSP
IT Professionals Certification Collection Certified Information Systems Security Professional CISSPThis slide covers information about CISSP Examination such as weight of each domain in exams, prep courses details, qualification details etc. Deliver an outstanding presentation on the topic using this IT Professionals Certification Collection Certified Information Systems Security Professional CISSP. Dispense information and present a thorough explanation of Security Operations, Asset Security, Security Engineering using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Statistics Of It Security Automation System
Key Statistics Of It Security Automation SystemThe following slide highlights critical statistics of security automation in the IT industry. The statistics mentioned in the slide are alert processing, IR processing and preventing security exposures to network. Introducing our Key Statistics Of It Security Automation System set of slides. The topics discussed in these slides are Key Statistics, IT Security, Automation System. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 IT Security Technology User Market
IT Security Technology User MarketThe following slide provides the statistical data for user market of IT risk assessment and mitigation software to make business process efficient. The technology used are authentication, firewalls, encryption, data masking and data backup. Introducing our IT Security Technology User Market set of slides. The topics discussed in these slides are IT Security Technology, User Market. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
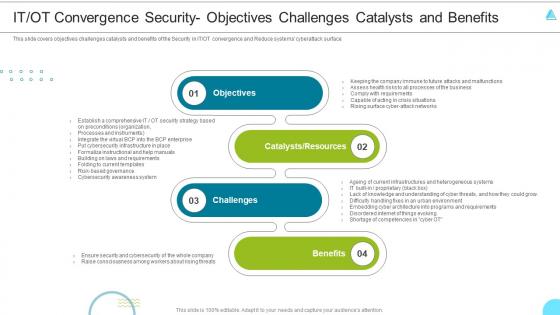 F516 It Ot Convergence Security Objectives Challenges Managing The Successful Convergence Of It And Ot
F516 It Ot Convergence Security Objectives Challenges Managing The Successful Convergence Of It And OtThis slide covers objectives challenges catalysts and benefits of the Security in IT or OT convergence and Reduce systems cyberattack surface Increase audience engagement and knowledge by dispensing information using F516 It Ot Convergence Security Objectives Challenges Managing The Successful Convergence Of It And Ot. This template helps you present information on four stages. You can also present information on Objectives, Resources, Convergence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
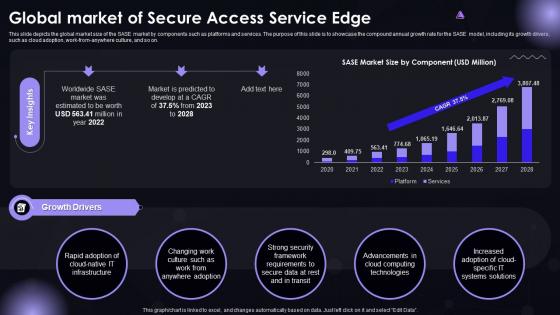 SASE IT Global Market Of Secure Access Service Edge Ppt Powerpoint Slides
SASE IT Global Market Of Secure Access Service Edge Ppt Powerpoint SlidesThis slide depicts the global market size of the SASE market by components such as platforms and services. The purpose of this slide is to showcase the compound annual growth rate for the SASE model, including its growth drivers, such as cloud adoption, work-from-anywhere culture, and so on. Present the topic in a bit more detail with this SASE IT Global Market Of Secure Access Service Edge Ppt Powerpoint Slides. Use it as a tool for discussion and navigation on Changing Work Culture, Security Framework, Computing Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V
Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding effective IT cost optimization strategies for IT executives such as revamping technology procurement, DevOps deployment, enabling business process reengineering, etc. Increase audience engagement and knowledge by dispensing information using Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V. This template helps you present information on four stages. You can also present information on Revamping Technology Procurement, Enabling Business Process Reengineering, Optimization Initiatives using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
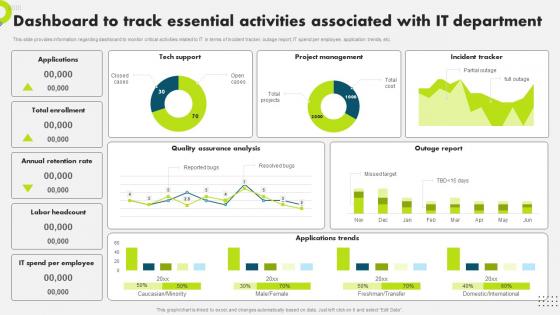 F1471 Dashboard To Track Essential Activities Strategic Plan To Secure It Infrastructure Strategy SS V
F1471 Dashboard To Track Essential Activities Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding dashboard to monitor critical activities related to IT in terms of incident tracker, outage report, IT spend per employee, application trends, etc. Present the topic in a bit more detail with this F1471 Dashboard To Track Essential Activities Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Dashboard, Associated, Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It Performance Dashboard To Track Customer Strategic Plan To Secure It Infrastructure Strategy SS V
It Performance Dashboard To Track Customer Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the dashboard to monitor overall IT performance. The dashboard tracks occupancy rate, net promoter score, avg. first contact resolution rate, etc. Present the topic in a bit more detail with this It Performance Dashboard To Track Customer Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Performance, Dashboard, Satisfaction. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
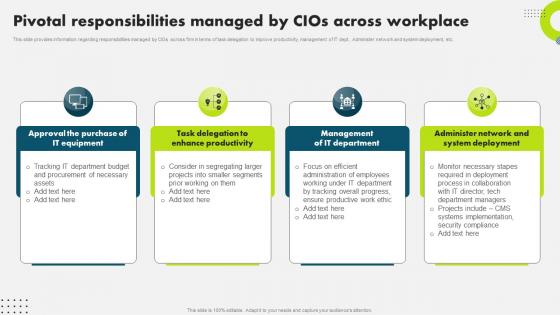 Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS V
Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding responsibilities managed by CIOs across firm in terms of task delegation to improve productivity, management of IT dept., Administer network and system deployment, etc. Present the topic in a bit more detail with this Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Responsibilities, Management, Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
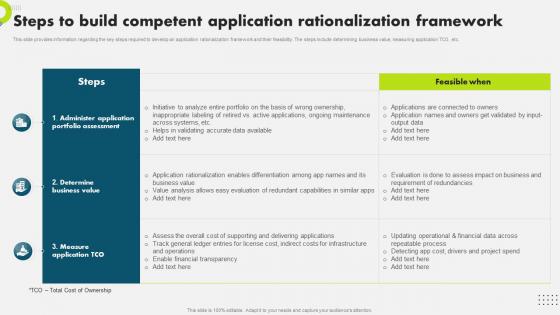 Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V
Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the key steps required to develop an application rationalization framework and their feasibility. The steps include determining business value, measuring application TCO, etc. Present the topic in a bit more detail with this Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Application, Rationalization, Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps To Develop Targeted Marketing Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V
Steps To Develop Targeted Marketing Initiatives Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information various steps required to develop target marketing initiatives for IT department. The initiatives include detect target market, conduct market research, develop objectives and goals, etc. Introducing Steps To Develop Targeted Marketing Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Marketing, Initiatives, Department, using this template. Grab it now to reap its full benefits.
-
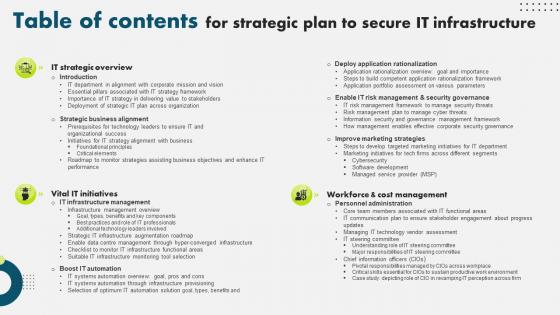 Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS V
Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS VPresent the topic in a bit more detail with this Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Strategic Business Alignment, Workforce And Cost Management, Deploy Application Rationalization . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
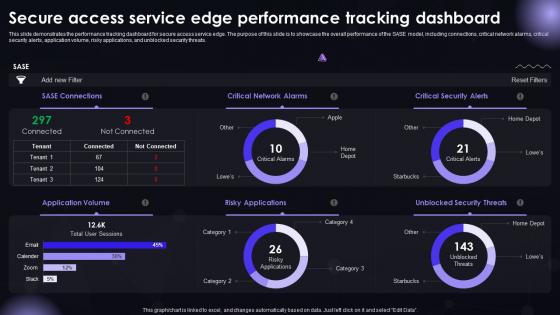 SASE IT Secure Access Service Edge Performance Tracking Dashboard Ppt Powerpoint Topics
SASE IT Secure Access Service Edge Performance Tracking Dashboard Ppt Powerpoint TopicsThis slide demonstrates the performance tracking dashboard for secure access service edge. The purpose of this slide is to showcase the overall performance of the SASE model, including connections, critical network alarms, critical security alerts, application volume, risky applications, and unblocked security threats. Present the topic in a bit more detail with this SASE IT Secure Access Service Edge Performance Tracking Dashboard Ppt Powerpoint Topics. Use it as a tool for discussion and navigation on SASE Connections, Critical Network Alarms, Critical Security Alerts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
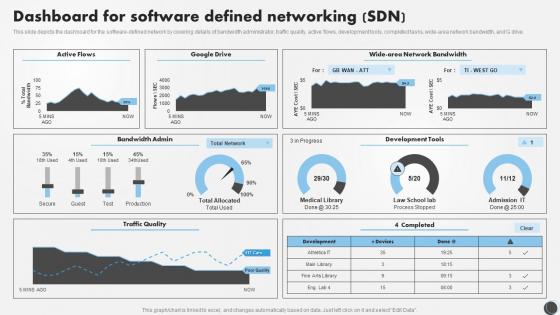 SDN Security IT Dashboard For Software Defined Networking SDN
SDN Security IT Dashboard For Software Defined Networking SDNThis slide depicts the dashboard for the software defined network by covering details of bandwidth administrator, traffic quality, active flows, development tools, completed tasks, wide-area network bandwidth, and G drive. Deliver an outstanding presentation on the topic using this SDN Security IT Dashboard For Software Defined Networking SDN. Dispense information and present a thorough explanation of Software, Networking, Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 It security ppt powerpoint presentation ideas display cpb
It security ppt powerpoint presentation ideas display cpbPresenting this set of slides with name IT Security Ppt Powerpoint Presentation Ideas Display Cpb. This is an editable Powerpoint six stages graphic that deals with topics like IT Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
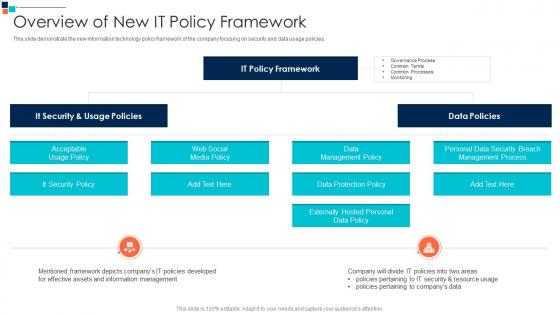 Overview Of New It Policy Framework Introducing A Risk Based Approach To Cyber Security
Overview Of New It Policy Framework Introducing A Risk Based Approach To Cyber SecurityThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies.Deliver an outstanding presentation on the topic using this Overview Of New It Policy Framework Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Data Management Policy, Data Protection Policy, Externally Hosted Personal using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
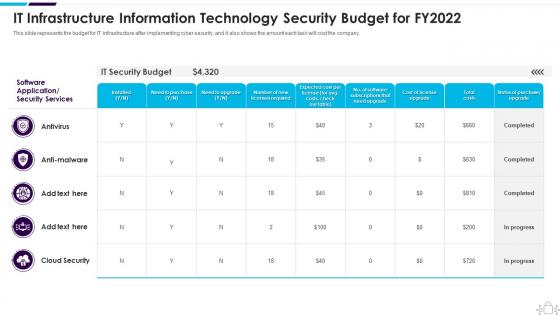 Information Technology Security It Infrastructure Information Budget For Fy2022
Information Technology Security It Infrastructure Information Budget For Fy2022This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Information Technology Security It Infrastructure Information Budget For Fy2022. Use it as a tool for discussion and navigation on Infrastructure, Information, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Security What Is Information Technology Security And How Does It Work
Information Technology Security What Is Information Technology Security And How Does It WorkThis slide defines the meaning of cyber security and how it helps to prevent data through different methods and techniques. Introducing Information Technology Security What Is Information Technology Security And How Does It Work to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information, Technology, Security, using this template. Grab it now to reap its full benefits.
-
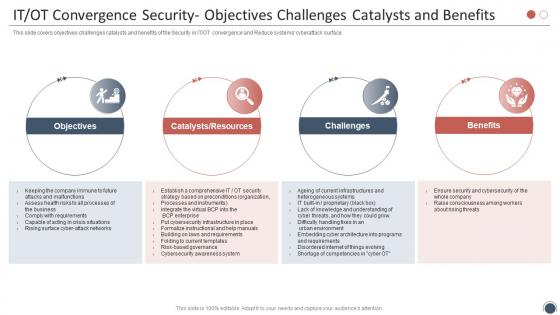 Smart Enterprise Digitalization IT OT Convergence Security Objectives Challenges Catalysts
Smart Enterprise Digitalization IT OT Convergence Security Objectives Challenges CatalystsThis slide covers objectives challenges catalysts and benefits of the Security in IT or OT convergence and Reduce systems cyberattack surface. Increase audience engagement and knowledge by dispensing information using Smart Enterprise Digitalization IT OT Convergence Security Objectives Challenges Catalysts. This template helps you present information on four stages. You can also present information on Objectives, Catalysts, Resources, Challenges, Benefits using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
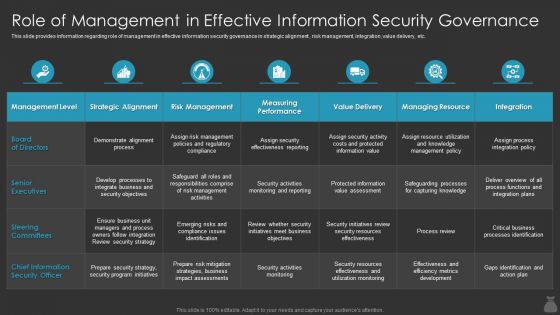 F472 Role Of Management In Effective Information Security It Cost Optimization Priorities By Cios
F472 Role Of Management In Effective Information Security It Cost Optimization Priorities By CiosThis slide provides information regarding role of management in effective information security governance in strategic alignment , risk management, integration, value delivery, etc. Deliver an outstanding presentation on the topic using this F472 Role Of Management In Effective Information Security It Cost Optimization Priorities By Cioss. Dispense information and present a thorough explanation of Information, Security, Governance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
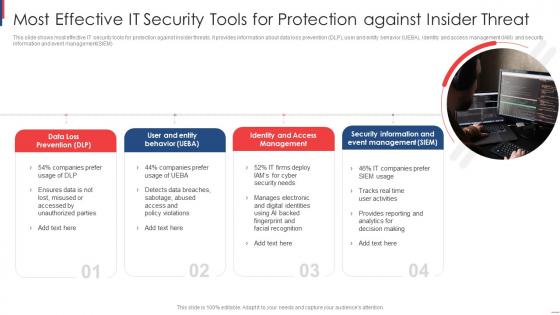 Most Effective It Security Tools For Protection Against Insider Threat
Most Effective It Security Tools For Protection Against Insider ThreatThis slide shows most effective IT security tools for protection against insider threats. It provides information about data loss prevention DLP, user and entity behavior UEBA, identity and access management IAM and security information and event management SIEM Introducing our premium set of slides with Most Effective It Security Tools For Protection Against Insider Threat. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Loss Prevention, User Entity Behavior, Identity Access Management. So download instantly and tailor it with your information.
-
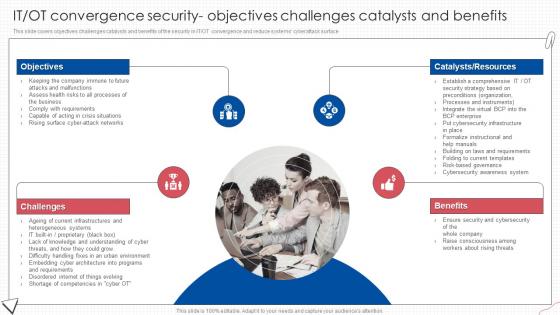 IT OT Convergence Security Objectives Digital Transformation Of Operational Industries
IT OT Convergence Security Objectives Digital Transformation Of Operational IndustriesThis slide covers objectives challenges catalysts and benefits of the security in IT OT convergence and reduce systems cyberattack surface.Introducing IT OT Convergence Security Objectives Digital Transformation Of Operational Industries to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Objectives, Benefits, Consciousness Among, using this template. Grab it now to reap its full benefits.
-
 It Security Audit With Risk Level Digital Audit To Evaluate Brand Ppt Themes
It Security Audit With Risk Level Digital Audit To Evaluate Brand Ppt ThemesThis slide highlights the security audit which showcase the risks related to accounts and user computers and also states the data which are at high risk. Deliver an outstanding presentation on the topic using this It Security Audit With Risk Level Digital Audit To Evaluate Brand Ppt Themes. Dispense information and present a thorough explanation of IT Security Audit With Risk Level using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Digital Transformation Trends in IT and Cyber Security
Digital Transformation Trends in IT and Cyber SecurityThis slide signifies digital transformation in Information technology and cyber security. It includes trends like securing assets, cloud computing, data analytics, security and automation. Introducing our premium set of slides with Digital Transformation Trends in IT and Cyber Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Securing Digital Assets, Cloud Computing, Data Analytics. So download instantly and tailor it with your information
-
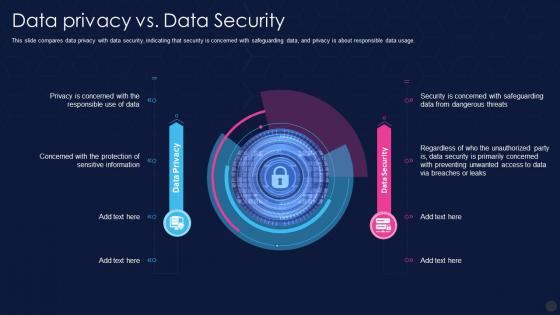 F41 Data Privacy It Data Privacy Vs Data Security
F41 Data Privacy It Data Privacy Vs Data SecurityThis slide compares data privacy with data security, indicating that security is concerned with safeguarding data, and privacy is about responsible data usage. Deliver an outstanding presentation on the topic using this F41 Data Privacy It Data Privacy Vs Data Security. Dispense information and present a thorough explanation of Information, Unauthorized, Dangerous using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
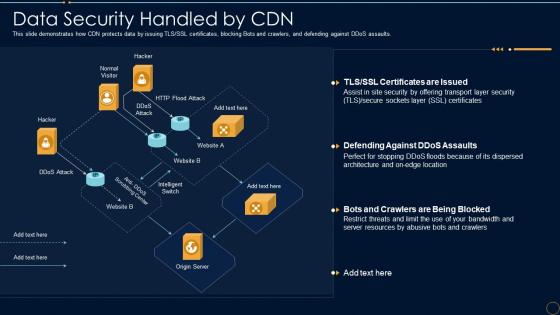 Content Delivery Network It Data Security Handled By Cdn
Content Delivery Network It Data Security Handled By CdnThis slide demonstrates how CDN protects data by issuing TLS or SSL certificates, blocking Bots and crawlers, and defending against DDoS assaults. Deliver an outstanding presentation on the topic using this Content Delivery Network It Data Security Handled By Cdn. Dispense information and present a thorough explanation of Data Security Handled By CDN using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
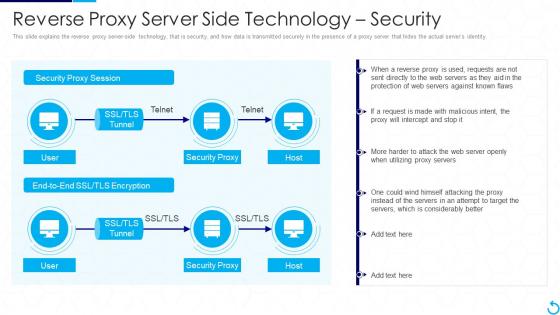 F58 Reverse Proxy It Reverse Proxy Server Side Technology Security
F58 Reverse Proxy It Reverse Proxy Server Side Technology SecurityThis slide explains the reverse proxy server side technology, that is security, and how data is transmitted securely in the presence of a proxy server that hides the actual servers identity. Deliver an outstanding presentation on the topic using this F58 Reverse Proxy It Reverse Proxy Server Side Technology Security. Dispense information and present a thorough explanation of Security Proxy, Technology, Transmitted Securely using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
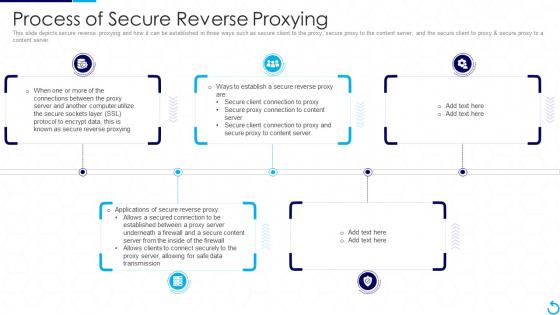 Reverse Proxy It Process Of Secure Reverse Proxying
Reverse Proxy It Process Of Secure Reverse ProxyingThis slide depicts secure reverse proxying and how it can be established in three ways such as secure client to the proxy, secure proxy to the content server, and the secure client to proxy and secure proxy to a content server. Increase audience engagement and knowledge by dispensing information using Reverse Proxy It Process Of Secure Reverse Proxying. This template helps you present information on five stages. You can also present information on Process Of Secure Reverse Proxying using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



