Powerpoint Templates and Google slides for Operational Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
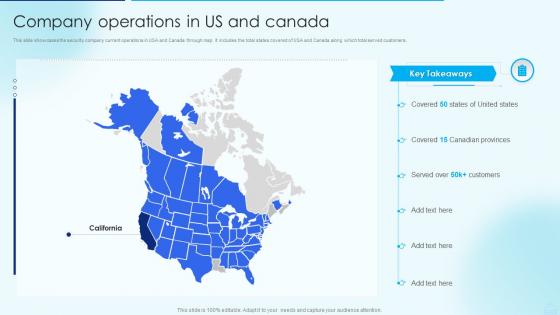 Company Operations In Us And Canada Security Alarm And Monitoring Systems Company Profile
Company Operations In Us And Canada Security Alarm And Monitoring Systems Company ProfileThis slide showcases the security company current operations in USA and Canada through map. It includes the total states covered of USA and Canada along which total served customers. Present the topic in a bit more detail with this Company Operations In Us And Canada Security Alarm And Monitoring Systems Company Profile. Use it as a tool for discussion and navigation on Company, Operations, Customers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
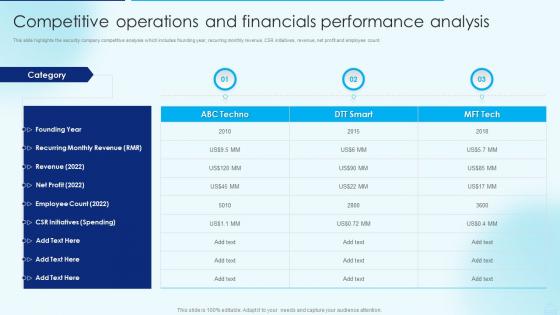 Competitive Operations And Financials Performance Security Alarm And Monitoring Systems Company Profile
Competitive Operations And Financials Performance Security Alarm And Monitoring Systems Company ProfileThis slide highlights the security company competitive analysis which includes founding year, recurring monthly revenue, CSR initiatives, revenue, net profit and employee count. Deliver an outstanding presentation on the topic using this Competitive Operations And Financials Performance Security Alarm And Monitoring Systems Company Profile. Dispense information and present a thorough explanation of Competitive, Operations, Performance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
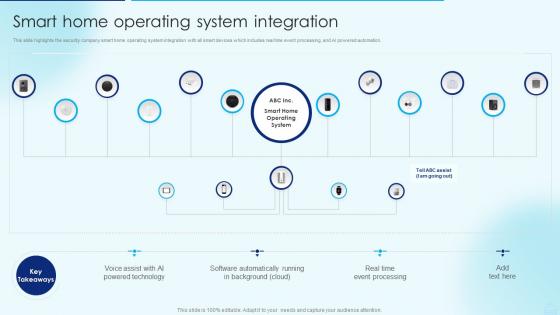 Smart Home Operating System Integration Security Alarm And Monitoring Systems Company Profile
Smart Home Operating System Integration Security Alarm And Monitoring Systems Company ProfileThis slide highlights the security company smart home operating system integration with all smart devices which includes real time event processing, and AI powered automation. Deliver an outstanding presentation on the topic using this Smart Home Operating System Integration Security Alarm And Monitoring Systems Company Profile. Dispense information and present a thorough explanation of Integration, Automation, Processing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
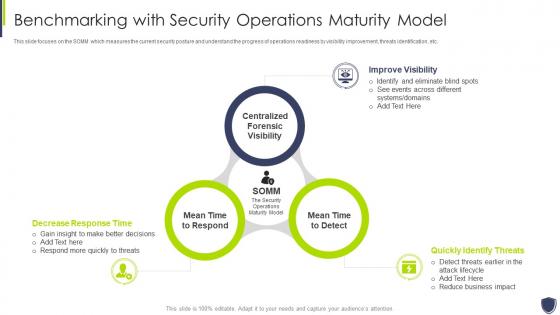
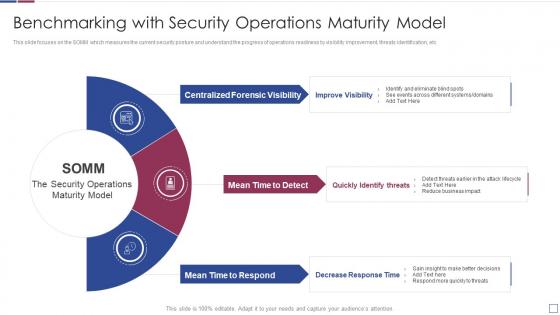 Real time analysis of security alerts benchmarking with security operations maturity model
Real time analysis of security alerts benchmarking with security operations maturity modelThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Introducing Real Time Analysis Of Security Alerts Benchmarking With Security Operations Maturity Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Forensic Visibility, Mean Time To Detect, Mean Time To Respond, using this template. Grab it now to reap its full benefits.
-
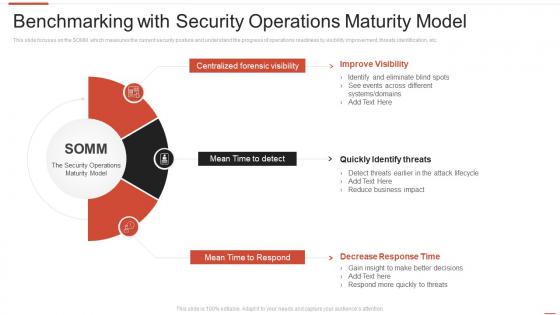
 Successful siem strategies audit compliance benchmarking security operations maturity
Successful siem strategies audit compliance benchmarking security operations maturityThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Increase audience engagement and knowledge by dispensing information using Successful Siem Strategies Audit Compliance Benchmarking Security Operations Maturity. This template helps you present information on three stages. You can also present information on Improve Visibility, Quickly Identify Threats, Decrease Response Time using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability benchmarking security operations maturity model
Improve it security with vulnerability benchmarking security operations maturity modelThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Introducing Improve It Security With Vulnerability Benchmarking Security Operations Maturity Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Improve Visibility, Quickly Identify Threats, Decrease Response Time, using this template. Grab it now to reap its full benefits.
-
 Benchmarking with security operations maturity model automating threat identification
Benchmarking with security operations maturity model automating threat identificationThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Introducing Benchmarking With Security Operations Maturity Model Automating Threat Identification to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Forensic Visibility, Mean Time To Detect, Mean Time To Respond, using this template. Grab it now to reap its full benefits.
-
 Development operations skills software security skills
Development operations skills software security skillsThis slide provides the glimpse about the software security skills such as security training, code analysis, change management, compliance monitoring, threat investigation, vulnerability management, etc. Introducing Development Operations Skills Software Security Skills to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Security Training, Code Analysis, Change Management, using this template. Grab it now to reap its full benefits.
-
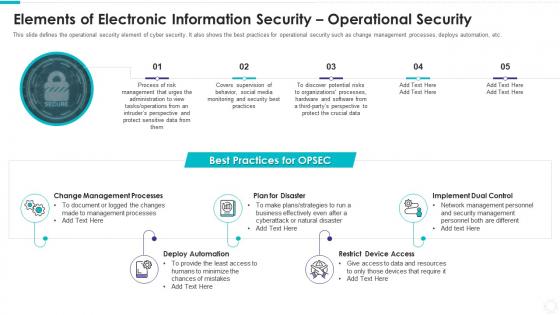 Elements of electronic information security operational security
Elements of electronic information security operational securityThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Increase audience engagement and knowledge by dispensing information using Elements Of Electronic Information Security Operational Security. This template helps you present information on five stages. You can also present information on Change Management Processes, Plan Disaster, Deploy Automation, Restrict Device Access, Implement Dual Control using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
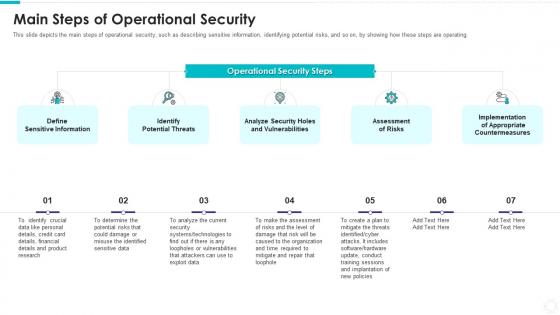 Electronic information security main steps of operational security
Electronic information security main steps of operational securityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Introducing Electronic Information Security Main Steps Of Operational Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Define Sensitive Information, Identify Potential Threats, Analyze Security Holes And Vulnerabilities, Assessment Risks, Implementation Appropriate Countermeasures, using this template. Grab it now to reap its full benefits.
-
 Elements Of Network Security Operational Security Ppt Styles Example File
Elements Of Network Security Operational Security Ppt Styles Example FileThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Introducing Elements Of Network Security Operational Security Ppt Styles Example File to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Management, Sensitive, Administration, Operations, using this template. Grab it now to reap its full benefits.
-
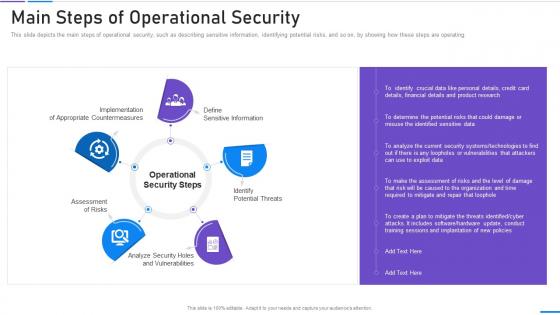 Network Security Main Steps Of Operational Security
Network Security Main Steps Of Operational SecurityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Increase audience engagement and knowledge by dispensing information using Network Security Main Steps Of Operational Security. This template helps you present information on five stages. You can also present information on Sensitive Information, Potential Threats, Vulnerabilities, Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
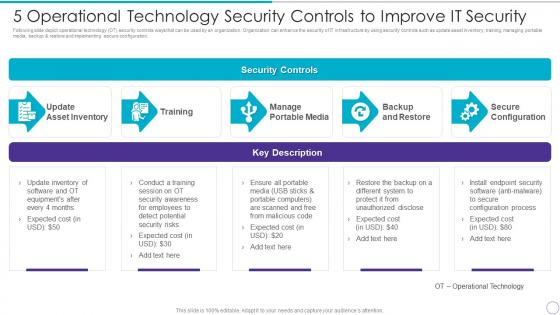 5 Operational Technology Security Controls To Improve It Security
5 Operational Technology Security Controls To Improve It SecurityFollowing slide depict operational technology OT security controls ways that can be used by an organization. Organization can enhance the security of IT infrastructure by using security controls such as update asset inventory, training, managing portable media, backup and restore and implementing secure configuration. Present the topic in a bit more detail with this 5 Operational Technology Security Controls To Improve IT Security. Use it as a tool for discussion and navigation on Update Asset Inventory, Training Manage, Portable Media, Backup And Restore, Secure Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
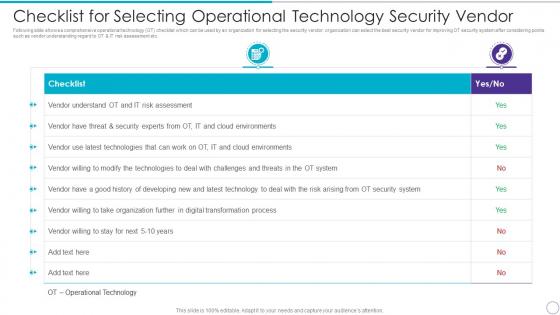 Checklist For Selecting Operational Technology Security Vendor
Checklist For Selecting Operational Technology Security VendorFollowing slide shows a comprehensive operational technology OT checklist which can be used by an organization for selecting the security vendor. organization can select the best security vendor for improving OT security system after considering points such as vendor understanding regard to OT and IT risk assessment etc. Deliver an outstanding presentation on the topic using this Checklist For Selecting Operational Technology Security Vendor. Dispense information and present a thorough explanation of Checklist, Vendor Understand OT, IT Risk Assessment, Digital Transformation Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
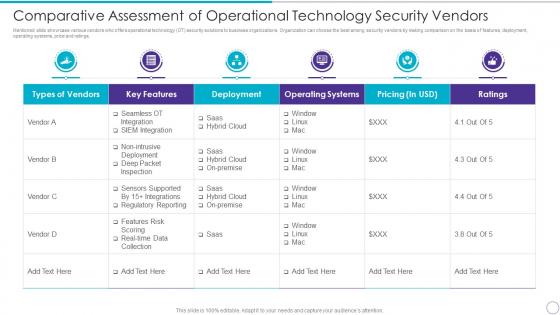 Comparative Assessment Of Operational Technology Security Vendors
Comparative Assessment Of Operational Technology Security VendorsMentioned slide showcase various vendors who offers operational technology OT security solutions to business organizations. Organization can choose the best among security vendors by making comparison on the basis of features, deployment, operating systems, price and ratings. Present the topic in a bit more detail with this Comparative Assessment Of Operational Technology Security Vendors. Use it as a tool for discussion and navigation on Types Vendors, Key Features, Deployment, Operating Systems, Pricing In USD, Ratings. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icon For Operational Technology Security
Icon For Operational Technology SecurityIntroducing Icon For Operational Technology Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Icon For Operational Technology Security, using this template. Grab it now to reap its full benefits.
-
 Operational Technology Icon For Security Threat Detection
Operational Technology Icon For Security Threat DetectionIntroducing Operational Technology Icon For Security Threat Detection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Operational Technology Icon For Security Threat Detection, using this template. Grab it now to reap its full benefits.
-
 Operational Technology Security Challenges And Solutions To Overcome
Operational Technology Security Challenges And Solutions To OvercomeMentioned slide illustrates various operational technology OT security challenges. It also cover information about the multiple solutions which will assist organization to overcome challenges and build a strong security IT system. Introducing Operational Technology Security Challenges And Solutions To Overcome to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Challenges, Solutions, Employees, using this template. Grab it now to reap its full benefits.
-
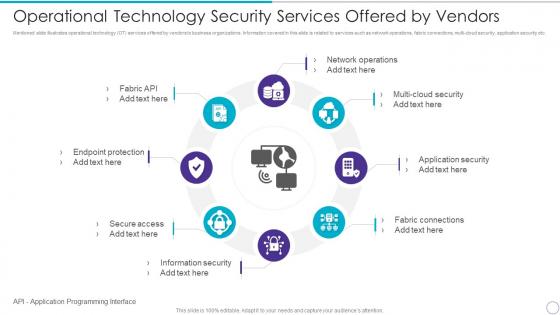 Operational Technology Security Services Offered By Vendors
Operational Technology Security Services Offered By VendorsMentioned slide illustrates operational technology OT services offered by vendors to business organizations. Information covered in this slide is related to services such as network operations, fabric connections, multi-cloud security, application security etc. Increase audience engagement and knowledge by dispensing information using Operational Technology Security Services Offered By Vendors. This template helps you present information on eight stages. You can also present information on Network Operations, Multi Cloud Security, Application Security, Fabric Connections, Information Security, Secure Access, Endpoint Protection, Fabric API using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Maturity Model Assessment To Improve Business Operations
Cloud Security Maturity Model Assessment To Improve Business OperationsThis slide represents cloud security maturity assessment model which helps improve cloud optimization and flexibility. It provides information regarding automation, manual scripts, managed stage and optimization. Introducing our premium set of slides with Cloud Security Maturity Model Assessment To Improve Business Operations. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Automation Optimized, Minimal Automation, Minimal Automation. So download instantly and tailor it with your information.
-
 Automated Enterprise Security Operation Icon
Automated Enterprise Security Operation IconPresenting our set of slides with Automated Enterprise Security Operation Icon. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Automated Enterprise, Security Operation Icon.
-
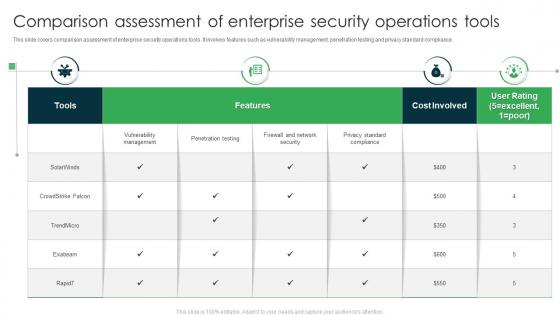 Comparison Assessment Of Enterprise Security Operations Tools
Comparison Assessment Of Enterprise Security Operations ToolsThis slide covers comparison assessment of enterprise security operations tools. It involves features such as vulnerability management, penetration testing and privacy standard compliance. Introducing our Comparison Assessment Of Enterprise Security Operations Tools set of slides. The topics discussed in these slides are Features, Cost Involved, User Rating. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Enterprise Cyber Security Operation Icon
Enterprise Cyber Security Operation IconIntroducing our premium set of slides with Enterprise Cyber Security Operation Icon. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Enterprise Cyber Security, Operation Icon. So download instantly and tailor it with your information.
-
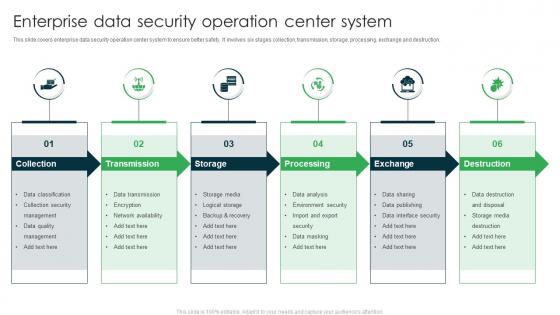 Enterprise Data Security Operation Center System
Enterprise Data Security Operation Center SystemThis slide covers enterprise data security operation center system to ensure better safety. It involves six stages collection, transmission, storage, processing, exchange and destruction. Presenting our set of slides with Enterprise Data Security Operation Center System. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Collection, Transmission, Processing .
-
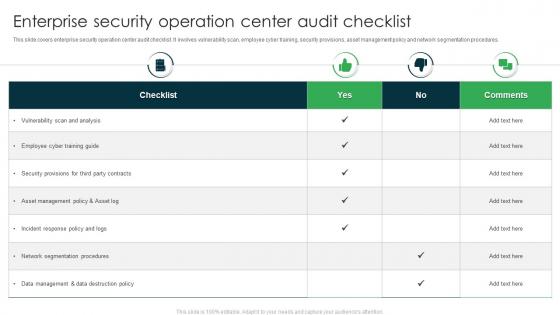 Enterprise Security Operation Center Audit Checklist
Enterprise Security Operation Center Audit ChecklistThis slide covers enterprise security operation center audit checklist. It involves vulnerability scan, employee cyber training, security provisions, asset management policy and network segmentation procedures. Introducing our Enterprise Security Operation Center Audit Checklist set of slides. The topics discussed in these slides are Employee Cyber Training Guide, Vulnerability Scan And Analysis, Incident Response Policy. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Enterprise Security Operation Center Best Practices
Enterprise Security Operation Center Best PracticesThis slide covers enterprise security operation center best practices. It involves practices such as setting up right time, align strategy with business goals, leverage best tools and continuously monitor network. Presenting our well structured Enterprise Security Operation Center Best Practices. The topics discussed in this slide are Leverage Best Tools, Continuously Monitor Network, Business Goals. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Enterprise Security Operation Center Icon
Enterprise Security Operation Center IconIntroducing our premium set of slides with Enterprise Security Operation Center Icon. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Enterprise Security Operation, Center Icon. So download instantly and tailor it with your information.
-
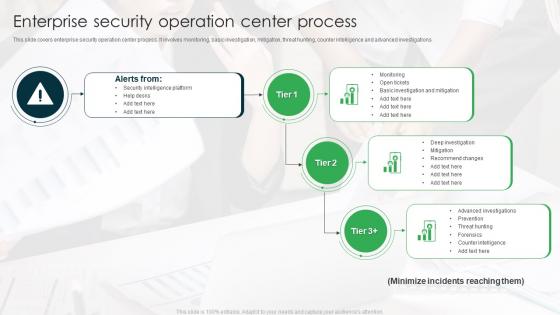 Enterprise Security Operation Center Process
Enterprise Security Operation Center ProcessThis slide covers enterprise security operation center process. It involves monitoring, basic investigation, mitigation, threat hunting, counter intelligence and advanced investigations. Introducing our Enterprise Security Operation Center Process set of slides. The topics discussed in these slides are Security Intelligence Platform, Help Desks, Monitoring. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
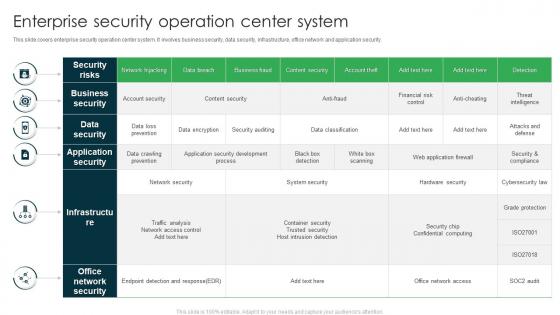 Enterprise Security Operation Center System
Enterprise Security Operation Center SystemThis slide covers enterprise security operation center system. It involves business security, data security, infrastructure, office network and application security. Presenting our well structured Enterprise Security Operation Center System. The topics discussed in this slide are Business Security, Data Security, Application Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Enterprise Security Operation Center Team Roles And Responsibilities
Enterprise Security Operation Center Team Roles And ResponsibilitiesThis slide covers enterprise security operation center team roles and responsibilities. It involves key roles such as incident responder, security investigator, advanced security analyst and SOC manager. Introducing our Enterprise Security Operation Center Team Roles And Responsibilities set of slides. The topics discussed in these slides are Security Investigator, Incident Responder, Advanced Security Analyst. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Enterprise Security Operation Center To Enhance Safety
Enterprise Security Operation Center To Enhance SafetyThis slide covers enterprise security operation center to enhance safety. It involves log collection, reporting, research and development, threat intelligence and aggregation. Presenting our set of slides with Enterprise Security Operation Center To Enhance Safety. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Knowledge Base, Ticketing, Log Collection.
-
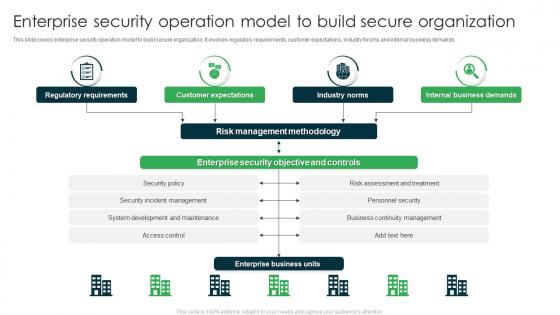 Enterprise Security Operation Model To Build Secure Organization
Enterprise Security Operation Model To Build Secure OrganizationThis slide covers enterprise security operation model to build secure organization. It involves regulatory requirements, customer expectations, industry forums and internal business demands. Introducing our premium set of slides with Enterprise Security Operation Model To Build Secure Organization. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regulatory Requirements, Customer Expectations, Industry Norms. So download instantly and tailor it with your information.
-
 Enterprise Security Operation System Icon
Enterprise Security Operation System IconPresenting our set of slides with Enterprise Security Operation System Icon. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Enterprise Security Operation, System Icon.
-
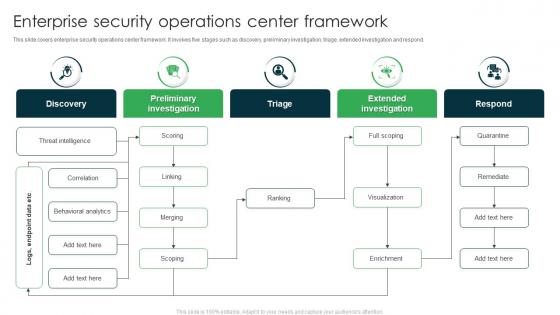 Enterprise Security Operations Center Framework
Enterprise Security Operations Center FrameworkThis slide covers enterprise security operations center framework. It involves five stages such as discovery, preliminary investigation, triage, extended investigation and respond. Introducing our premium set of slides with Enterprise Security Operations Center Framework. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Preliminary Investigation, Extended Investigation, Triage. So download instantly and tailor it with your information.
-
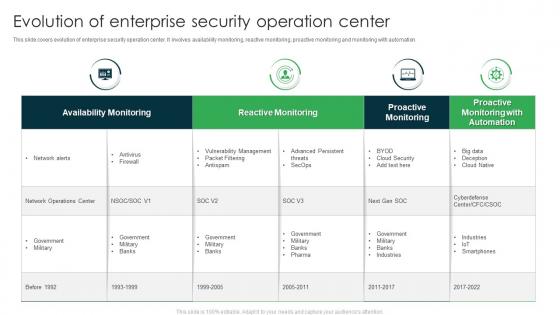 Evolution Of Enterprise Security Operation Center
Evolution Of Enterprise Security Operation CenterThis slide covers evolution of enterprise security operation center. It involves availability monitoring, reactive monitoring, proactive monitoring and monitoring with automation. Introducing our Evolution Of Enterprise Security Operation Center set of slides. The topics discussed in these slides are Reactive Monitoring, Availability Monitoring, Proactive Monitoring. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
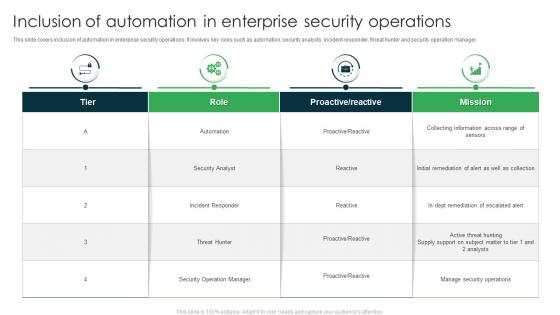 Inclusion Of Automation In Enterprise Security Operations
Inclusion Of Automation In Enterprise Security OperationsThis slide covers inclusion of automation in enterprise security operations. It involves key roles such as automation, security analysts, incident responder, threat hunter and security operation manager. Presenting our well structured Inclusion Of Automation In Enterprise Security Operations. The topics discussed in this slide are Security Analyst, Incident Responder, Security Operation Manager. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
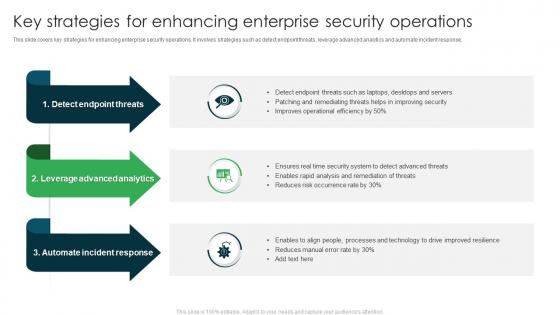 Key Strategies For Enhancing Enterprise Security Operations
Key Strategies For Enhancing Enterprise Security OperationsThis slide covers key strategies for enhancing enterprise security operations. It involves strategies such as detect endpoint threats, leverage advanced analytics and automate incident response. Introducing our premium set of slides with Key Strategies For Enhancing Enterprise Security Operations. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Detect Endpoint Threats, Leverage Advanced Analytics, Automate Incident Response. So download instantly and tailor it with your information.
-
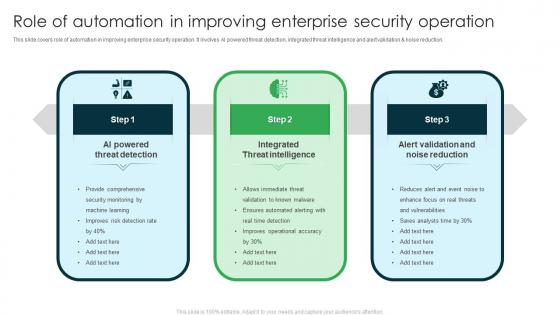 Role Of Automation In Improving Enterprise Security Operation
Role Of Automation In Improving Enterprise Security OperationThis slide covers role of automation in improving enterprise security operation. It involves AI powered threat detection, integrated threat intelligence and alert validation and noise reduction. Presenting our set of slides with Role Of Automation In Improving Enterprise Security Operation. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on AI Powered Threat Detection, Integrated Threat Intelligence, Alert Validation And Noise Reduction.
-
 Why Enterprise Security Operation Center Is Required
Why Enterprise Security Operation Center Is RequiredThis slide covers need of enterprise security operation center. It involves reasons such as continuous monitoring, centralized visibility, reduced cybersecurity costs and ensures better collaboration. Introducing our premium set of slides with Why Enterprise Security Operation Center Is Required. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Continuous Monitoring, Centralized Visibility, Reduced Cybersecurity Costs. So download instantly and tailor it with your information.
-
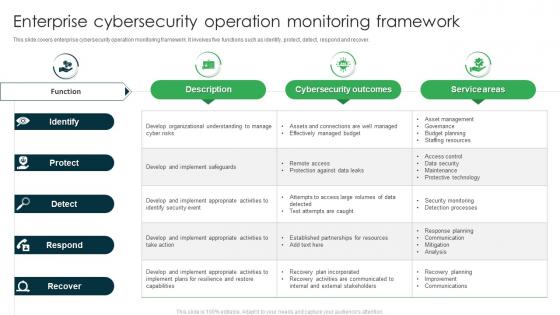 Enterprise Cyber security Operation Monitoring Framework
Enterprise Cyber security Operation Monitoring FrameworkThis slide covers enterprise cyber security operation monitoring framework. It involves five functions such as identify, protect, detect, respond and recover. Presenting our well structured Enterprise Cybersecurity Operation Monitoring Framework. The topics discussed in this slide are Cybersecurity Outcomes, Service Areas, Identify. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
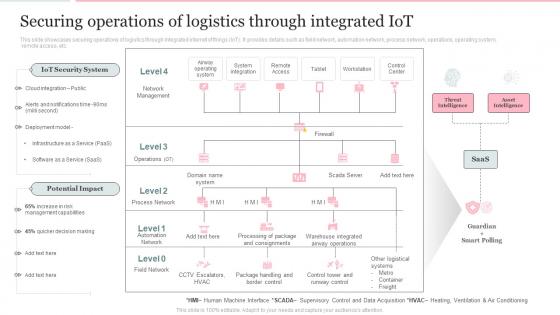 Deploying Internet Logistics Efficient Operations Securing Operations Of Logistics Through Integrated Iot
Deploying Internet Logistics Efficient Operations Securing Operations Of Logistics Through Integrated IotThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc. Present the topic in a bit more detail with this Deploying Internet Logistics Efficient Operations Securing Operations Of Logistics Through Integrated Iot. Use it as a tool for discussion and navigation on Operations, Logistics, Potential Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
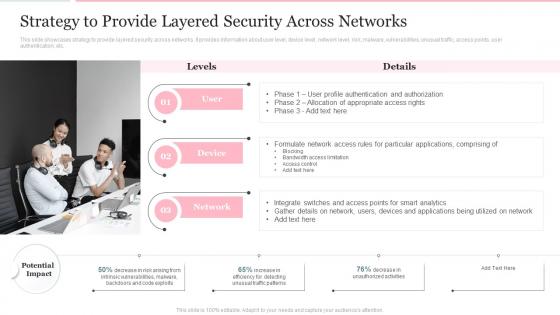 Strategy To Provide Layered Security Across Networks Deploying Internet Logistics Efficient Operations
Strategy To Provide Layered Security Across Networks Deploying Internet Logistics Efficient OperationsThis slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Deliver an outstanding presentation on the topic using this Strategy To Provide Layered Security Across Networks Deploying Internet Logistics Efficient Operations. Dispense information and present a thorough explanation of Strategy, Information, Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
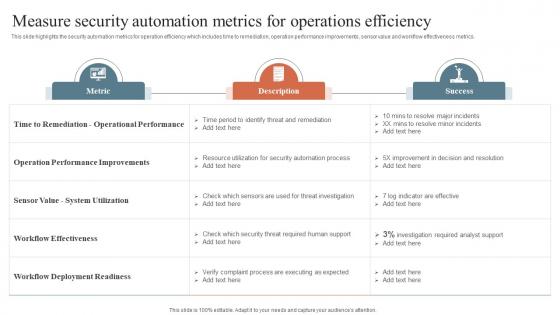 Security Orchestration Automation Measure Security Automation Metrics For Operations Efficiency
Security Orchestration Automation Measure Security Automation Metrics For Operations EfficiencyThis slide highlights the security automation metrics for operation efficiency which includes time to remediation, operation performance improvements, sensor value and workflow effectiveness metrics. Present the topic in a bit more detail with this Security Orchestration Automation Measure Security Automation Metrics For Operations Efficiency. Use it as a tool for discussion and navigation on Operational Performance, Deployment Readiness, System Utilization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
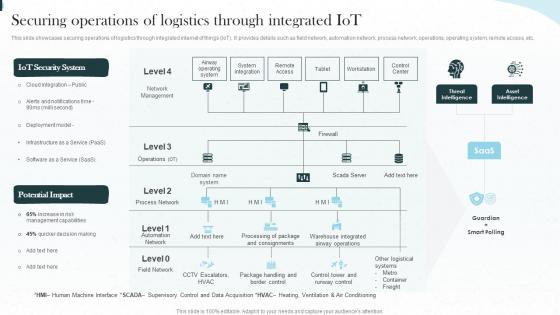 Implementing Iot Architecture In Shipping Business Securing Operations Of Logistics Through Integrated Iot
Implementing Iot Architecture In Shipping Business Securing Operations Of Logistics Through Integrated IotThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc. Present the topic in a bit more detail with this Implementing Iot Architecture In Shipping Business Securing Operations Of Logistics Through Integrated Iot. Use it as a tool for discussion and navigation on Operations, Integrated, Workstation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Elements IT Operational Security Element Of Cyber Security Ppt Introduction
Cyber Security Elements IT Operational Security Element Of Cyber Security Ppt IntroductionThis slide defines the operational security element of cyber security. It also shows the best practices for operational security, such as changing management processes, deploying automation, planning for disasters, restricting device access, and implementing dual control. Increase audience engagement and knowledge by dispensing information using Cyber Security Elements IT Operational Security Element Of Cyber Security Ppt Introduction. This template helps you present information on five stages. You can also present information on Deploy Automation, Restrict Device Access, Change Management Processes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategies To Enhance Retail Store Security Analysis Of Retail Store Operations Efficiency
Strategies To Enhance Retail Store Security Analysis Of Retail Store Operations EfficiencyThis slide provides information regarding the strategies to enhance retail store security such as integrate access control technology, deploy video surveillance, utilizes electronic article surveillance, install monitored alarms. Increase audience engagement and knowledge by dispensing information using Strategies To Enhance Retail Store Security Analysis Of Retail Store Operations Efficiency. This template helps you present information on four stages. You can also present information on Integrate Access Control Technology, Utilizes Electronic Article Surveillance, Install Monitored Alarm using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Project Estimation Plan To Safeguard Business Operation
Cyber Security Project Estimation Plan To Safeguard Business OperationThis slide signifies the cyber security project evaluation plan for safeguarding organisation operations. It covers information regarding to the stages like initiation, planning, execution, implement and monitor. Introducing our premium set of slides with Cyber Security Project Estimation Plan To Safeguard Business Operation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Initiation, Planning, Execution. So download instantly and tailor it with your information.
-
 Strategies To Improve Business Security Operations
Strategies To Improve Business Security OperationsThis slide shows various strategies which can be used by organizations to enhance business operations security. These strategies are detect endpoint threats, leverage advanced analytics and automate incident response. Presenting our set of slides with Strategies To Improve Business Security Operations. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detect Endpoint Threats, Leverage Advanced Analytics, Automate Incident Response.
-
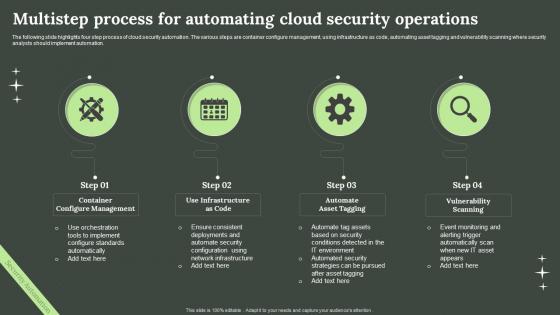 Multistep Process For Automating Cloud Security Operations
Multistep Process For Automating Cloud Security OperationsThe following slide highlights four step process of cloud security automation. The various steps are container configure management, using infrastructure as code, automating asset tagging and vulnerability scanning where security analysts should implement automation. Introducing our premium set of slides with Multistep Process For Automating Cloud Security Operations. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Container Configure Management, Infrastructure As Code, Vulnerability Scanning. So download instantly and tailor it with your information.
-
 Agenda Enabling Automation In Cyber Security Operations Ppt Slides Background Images
Agenda Enabling Automation In Cyber Security Operations Ppt Slides Background ImagesIntroducing Agenda Enabling Automation In Cyber Security Operations Ppt Slides Background Images to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Environment, Business, Process, using this template. Grab it now to reap its full benefits.
-
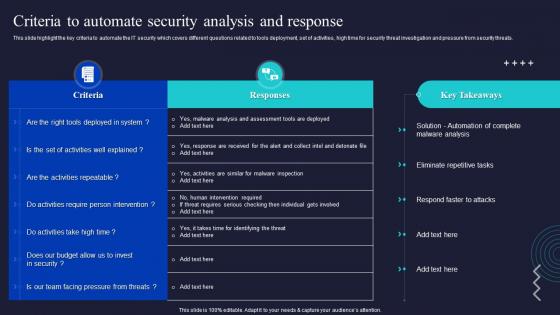 Criteria To Automate Security Analysis And Response Enabling Automation In Cyber Security Operations
Criteria To Automate Security Analysis And Response Enabling Automation In Cyber Security OperationsThis slide highlight the key criteria to automate the IT security which covers different questions related to tools deployment, set of activities, high time for security threat investigation and pressure from security threats. Present the topic in a bit more detail with this Criteria To Automate Security Analysis And Response Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Intervention, Malware Analysis, Automate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
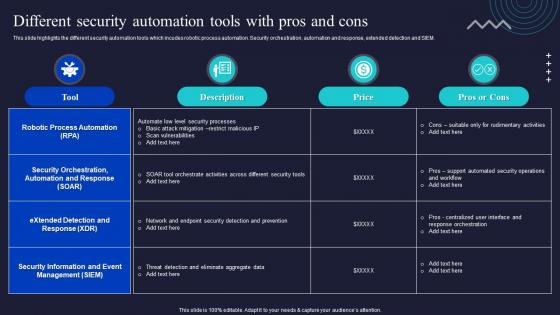 Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations
Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security OperationsThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Present the topic in a bit more detail with this Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Security Information, Management, Automation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
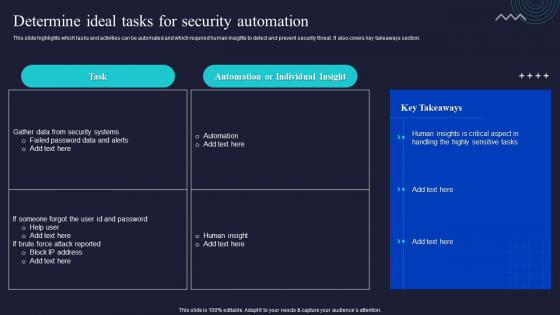 Enabling Automation In Cyber Security Operations Determine Ideal Tasks For Security Automation
Enabling Automation In Cyber Security Operations Determine Ideal Tasks For Security AutomationThis slide highlights which tasks and activities can be automated and which required human insights to detect and prevent security threat. It also covers key takeaways section. Deliver an outstanding presentation on the topic using this Enabling Automation In Cyber Security Operations Determine Ideal Tasks For Security Automation. Dispense information and present a thorough explanation of Automation, Individual, Takeaways Section using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
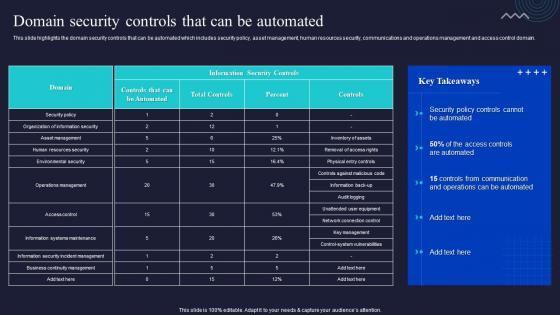 Enabling Automation In Cyber Security Operations Domain Security Controls That Can Be Automated
Enabling Automation In Cyber Security Operations Domain Security Controls That Can Be AutomatedThis slide highlights the domain security controls that can be automated which includes security policy, asset management, human resources security, communications and operations management and access control domain. Present the topic in a bit more detail with this Enabling Automation In Cyber Security Operations Domain Security Controls That Can Be Automated. Use it as a tool for discussion and navigation on Communication, Management, Human Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enabling Automation In Cyber Security Operations Table Of Contents Ppt Slides Infographic Template
Enabling Automation In Cyber Security Operations Table Of Contents Ppt Slides Infographic TemplateDeliver an outstanding presentation on the topic using this Enabling Automation In Cyber Security Operations Table Of Contents Ppt Slides Infographic Template. Dispense information and present a thorough explanation of Protection Platform, Security Automation, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
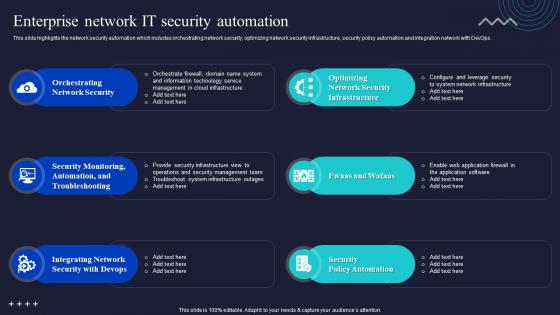 Enterprise Network It Security Automation Enabling Automation In Cyber Security Operations
Enterprise Network It Security Automation Enabling Automation In Cyber Security OperationsThis slide highlights the network security automation which includes orchestrating network security, optimizing network security infrastructure, security policy automation and integration network with DevOps. Deliver an outstanding presentation on the topic using this Enterprise Network It Security Automation Enabling Automation In Cyber Security Operations. Dispense information and present a thorough explanation of Orchestrating Network Security, Troubleshooting, Integrating Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
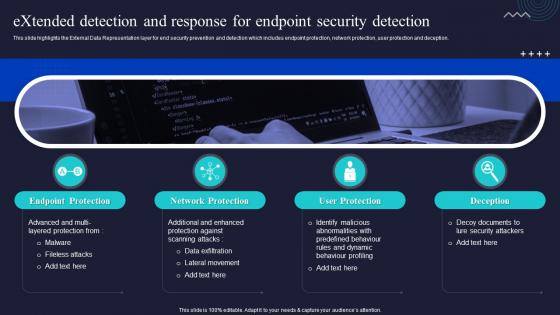 Extended Detection And Response For Endpoint Security Enabling Automation In Cyber Security Operations
Extended Detection And Response For Endpoint Security Enabling Automation In Cyber Security OperationsThis slide highlights the External Data Representation layer for end security prevention and detection which includes endpoint protection, network protection, user protection and deceptio Increase audience engagement and knowledge by dispensing information using Extended Detection And Response For Endpoint Security Enabling Automation In Cyber Security Operations. This template helps you present information on four stages. You can also present information on Endpoint Protection, Network Protection, User Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Enabling Automation In Cyber Security Operations Ppt Slides Background Designs
Icons Slide For Enabling Automation In Cyber Security Operations Ppt Slides Background DesignsDeliver an outstanding presentation on the topic using this Icons Slide For Enabling Automation In Cyber Security Operations Ppt Slides Background Designs. Dispense information and present a thorough explanation of Icons using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
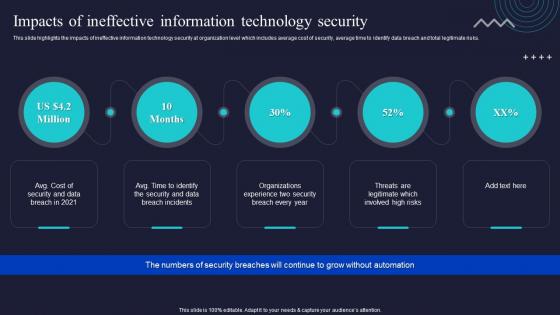 Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security Operations
Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security OperationsThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Increase audience engagement and knowledge by dispensing information using Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security Operations. This template helps you present information on four stages. You can also present information on Ineffective, Information, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Managed Detection And Response Layer For Expert Monitoring Enabling Automation In Cyber Security Operations
Managed Detection And Response Layer For Expert Monitoring Enabling Automation In Cyber Security OperationsThis slide highlights the slide Managed Detection and Response security layer which include alter monitoring, attack investigation, threat hunting, and incident response. Introducing Managed Detection And Response Layer For Expert Monitoring Enabling Automation In Cyber Security Operations to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Alert Monitoring, Attack Investigation, Threat Hunting, using this template. Grab it now to reap its full benefits.



