Powerpoint Templates and Google slides for Phishing
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Checklist To Secure Organizations From Phishing Attacks And Strategies
Checklist To Secure Organizations From Phishing Attacks And StrategiesThis slide outlines the steps to be taken to protect the organization and its employees from phishing attacks. The key approaches include provide staff training, update software, enable MFA and spam filters, implement real time monitoring and develop an incident plan.Present the topic in a bit more detail with this Checklist To Secure Organizations From Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Key Approaches, Provide Staff Training, Alerting Impacted. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
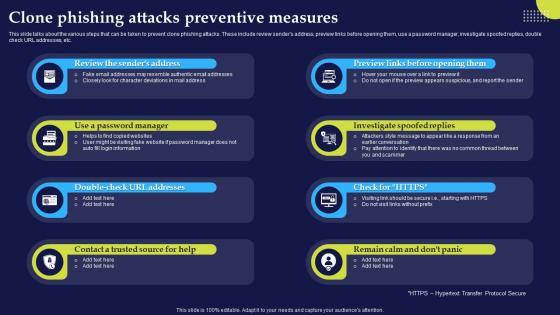 Clone Phishing Attacks Preventive Measures Phishing Attacks And Strategies
Clone Phishing Attacks Preventive Measures Phishing Attacks And StrategiesThis slide talks about the various steps that can be taken to prevent clone phishing attacks. These include review senders address, preview links before opening them, use a password manager, investigate spoofed replies, double check URL addresses, etc.Introducing Clone Phishing Attacks Preventive Measures Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Investigate Spoofed, Password Manager, Contact Trusted, using this template. Grab it now to reap its full benefits.
-
 Different Types Of Smishing Cyber Scams Phishing Attacks And Strategies
Different Types Of Smishing Cyber Scams Phishing Attacks And StrategiesThis slide talks about the various types of smishing cyber attacks. The purpose of this slide is to briefly explain different techniques of smishing scams used by the attackers to scam users. These are covid 19 smishing, financial services smishing, etc.Increase audience engagement and knowledge by dispensing information using Different Types Of Smishing Cyber Scams Phishing Attacks And Strategies. This template helps you present information on five stages. You can also present information on Confirmation Smishing, Services Smishing, Smishing Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Different Types Of Vishing Cyber Attacks Phishing Attacks And Strategies
Different Types Of Vishing Cyber Attacks Phishing Attacks And StrategiesThis slide talks about the various types of vishing cyber attacks. The purpose of this slide is to briefly explain different techniques of vishing scams used by the attackers to scam users. These are caller ID spoofing, dumpster diving, wardialing, etc.Introducing Different Types Of Vishing Cyber Attacks Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Protocol Transmission, Achieved Automatically, Phishing Attack Victims, using this template. Grab it now to reap its full benefits.
-
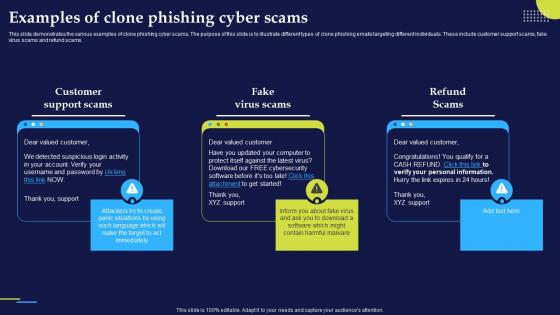 Examples Of Clone Phishing Cyber Scams Phishing Attacks And Strategies
Examples Of Clone Phishing Cyber Scams Phishing Attacks And StrategiesThis slide demonstrates the various examples of clone phishing cyber scams. The purpose of this slide is to illustrate different types of clone phishing emails targeting different individuals. These include customer support scams, fake virus scams and refund scams.Increase audience engagement and knowledge by dispensing information using Examples Of Clone Phishing Cyber Scams Phishing Attacks And Strategies. This template helps you present information on three stages. You can also present information on Detected Suspicious, Support Scams, Virus Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
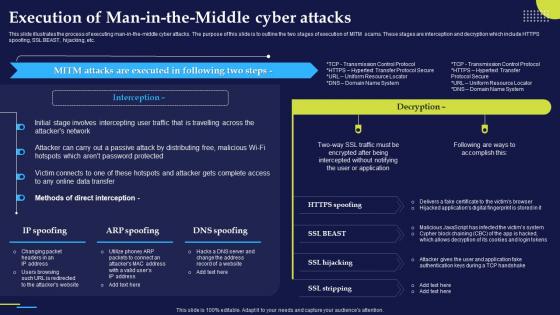 Execution Of Man In The Middle Cyber S Phishing Attacks And Strategies
Execution Of Man In The Middle Cyber S Phishing Attacks And StrategiesThis slide illustrates the process of executing man in the middle cyber attacks. The purpose of this slide is to outline the two stages of execution of MITM scams. These stages are interception and decryption which include HTTPS spoofing, SSL BEAST, hijacking, etc.Deliver an outstanding presentation on the topic using this Execution Of Man In The Middle Cyber S Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Data Transfer, Direct Interception, Password Protected using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Guidelines To Stay Safe From Phishing Scams Phishing Attacks And Strategies
Guidelines To Stay Safe From Phishing Scams Phishing Attacks And StrategiesThis slide outlines the various preventive measures to stay safe from phishing attacks. These include know how to spot phishing scams, avoid clicking that link, install free anti phishing extensions, change passwords regularly, install firewalls, never miss updates, etc.Introducing Guidelines To Stay Safe From Phishing Scams Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Sensitive Information, Install Firewalls, Between Your Computer, using this template. Grab it now to reap its full benefits.
-
 How Does A Phishing Attack Work Phishing Attacks And Strategies
How Does A Phishing Attack Work Phishing Attacks And StrategiesThis slide demonstrates the working flow of a phishing attack. The purpose of this slide is to outline the various phases of phishing scams such as campaign crafted, payloads, impersonation, execution, ransomware and encrypts on target.Increase audience engagement and knowledge by dispensing information using How Does A Phishing Attack Work Phishing Attacks And Strategies. This template helps you present information on six stages. You can also present information on Campaign Crafted, Targeted Individuals, Attacked System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
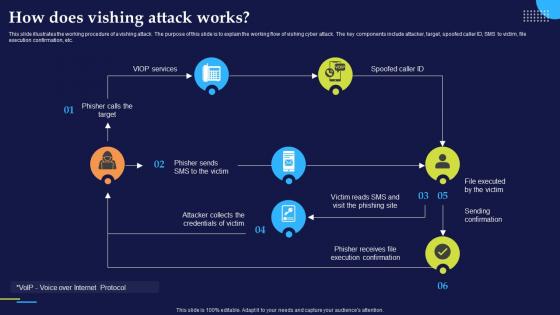 How Does Vishing Attack Works Phishing Attacks And Strategies
How Does Vishing Attack Works Phishing Attacks And StrategiesThis slide illustrates the working procedure of a vishing attack. The purpose of this slide is to explain the working flow of vishing cyber attack. The key components include attacker, target, spoofed caller ID, SMS to victim, file execution confirmation, etc.Deliver an outstanding presentation on the topic using this How Does Vishing Attack Works Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Execution Confirmation, Phisher Receives, Sending Confirmation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 How To Protect Users From Vishing Attacks Phishing Attacks And Strategies
How To Protect Users From Vishing Attacks Phishing Attacks And StrategiesThis slide talks about the ways to protect users from vishing attacks. These include avoid calls from robots, never respond to audio automated calls, verify the identity of the caller, never share personal information over the call, use multi factor authentication, etc.Present the topic in a bit more detail with this How To Protect Users From Vishing Attacks Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Multi Factor Authentication, Employees Family, Government Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide For Phishing Attacks And Strategies To Mitigate Them
Icons Slide For Phishing Attacks And Strategies To Mitigate ThemIntroducing our well researched set of slides titled Icons Slide For Phishing Attacks And Strategies To Mitigate Them. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
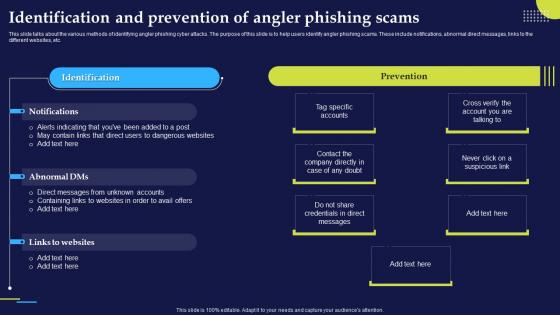 Identification And Prevention Of Angler Phishing Attacks And Strategies
Identification And Prevention Of Angler Phishing Attacks And StrategiesThis slide talks about the various methods of identifying angler phishing cyber attacks. The purpose of this slide is to help users identify angler phishing scams. These include notifications, abnormal direct messages, links to the different websites, etc.Present the topic in a bit more detail with this Identification And Prevention Of Angler Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Credentials Direct, Direct Messages, Unknown Accounts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Identification And Prevention Of Spear Phishing Attacks And Strategies
Identification And Prevention Of Spear Phishing Attacks And StrategiesThis slide talks about the various methods of identifying spear phishing cyber attacks. The purpose of this slide is to help users prevent spear phishing scams. The key signs include unusual request, shared drive links and documents with password protection.Introducing Identification And Prevention Of Spear Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Password Protection, Unusual Request, Appears Strange, using this template. Grab it now to reap its full benefits.
-
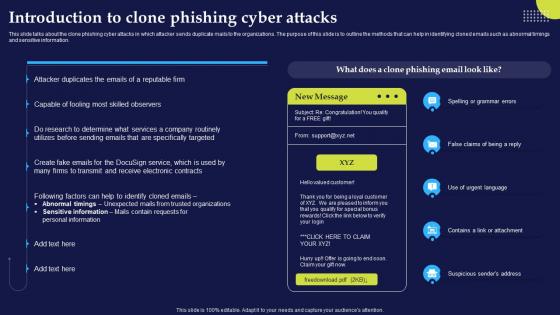 Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies
Introduction To Clone Phishing Cyber Attacks Phishing Attacks And StrategiesThis slide talks about the clone phishing cyber attacks in which attacker sends duplicate mails to the organizations. The purpose of this slide is to outline the methods that can help in identifying cloned emails such as abnormal timings and sensitive information.Present the topic in a bit more detail with this Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Personal Information, Sensitive Information, Abnormal Timings Unexpected. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
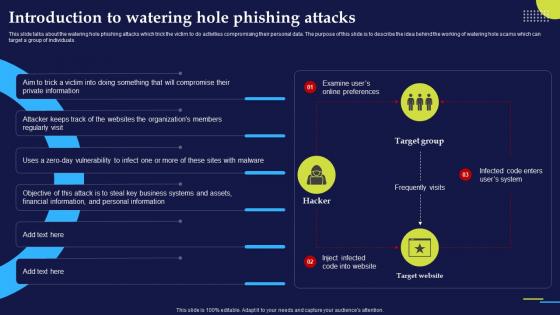 Introduction To Watering Hole Phishing Attacks Phishing Attacks And Strategies
Introduction To Watering Hole Phishing Attacks Phishing Attacks And StrategiesThis slide talks about the watering hole phishing attacks which trick the victim to do activities compromising their personal data. The purpose of this slide is to describe the idea behind the working of watering hole scams which can target a group of individuals.Deliver an outstanding presentation on the topic using this Introduction To Watering Hole Phishing Attacks Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Vulnerability Infect, Organizations Members, Private Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
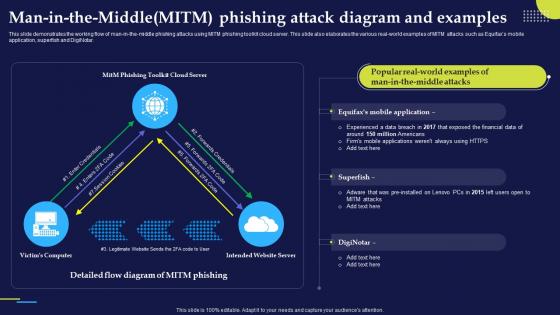 Man In The Middle Mitm Phishing Attack Diagram Phishing Attacks And Strategies
Man In The Middle Mitm Phishing Attack Diagram Phishing Attacks And StrategiesThis slide demonstrates the working flow of man in the middle phishing attacks using MITM phishing toolkit cloud server. This slide also elaborates the various real world examples of MITM attacks such as Equifaxs mobile application, superfish and DigiNotar.Present the topic in a bit more detail with this Man In The Middle Mitm Phishing Attack Diagram Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Experienced Data Breach, Exposed Financial, Man Middle Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Multi Layered Approach To Phishing Defenses Phishing Attacks And Strategies
Multi Layered Approach To Phishing Defenses Phishing Attacks And StrategiesThis slide represents the multi layered approach to phishing defenses. These include create difficulty for attackers to reach users, guide users in identifying and reporting phishing emails, save your organization from unexpected phishing scams, etc.Present the topic in a bit more detail with this Multi Layered Approach To Phishing Defenses Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Respond Immediately, Phishing Scams, Phishing Emails. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
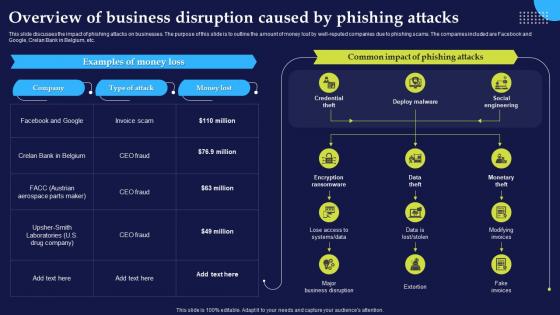 Overview Of Business Disruption Caused By Phishing Attacks And Strategies
Overview Of Business Disruption Caused By Phishing Attacks And StrategiesThis slide discusses the impact of phishing attacks on businesses. The purpose of this slide is to outline the amount of money lost by well reputed companies due to phishing scams. The companies included are Facebook and Google, Crelan Bank in Belgium, etc.Deliver an outstanding presentation on the topic using this Overview Of Business Disruption Caused By Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Examples Money Loss, Aerospace Parts, Common Impact Phishing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
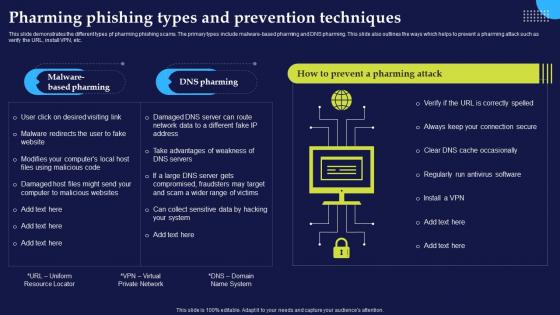 Pharming Phishing Types And Prevention Phishing Attacks And Strategies
Pharming Phishing Types And Prevention Phishing Attacks And StrategiesThis slide demonstrates the different types pf pharming phishing scams. The primary types include malware based pharming and DNS pharming. This slide also outlines the ways which helps to prevent a pharming attack such as verify the URL, install VPN, etc.Introducing Pharming Phishing Types And Prevention Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Run, Antivirus Software, Malware Redirects, using this template. Grab it now to reap its full benefits.
-
 Phishing Attacks And Strategies Overview Of Different Types Of Phishing Attacks
Phishing Attacks And Strategies Overview Of Different Types Of Phishing AttacksThis slide outlines the various types of cyber phishing attacks. The types include email phishing, HTTPS phishing, whaling, smishing, angler phishing, pharming, spear phishing, pop up phishing, clone phishing, evil twin scams, watering hole attacks, etc.Increase audience engagement and knowledge by dispensing information using Phishing Attacks And Strategies Overview Of Different Types Of Phishing Attacks. This template helps you present information on one stage. You can also present information on Overview Of Different, Types Phishing Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
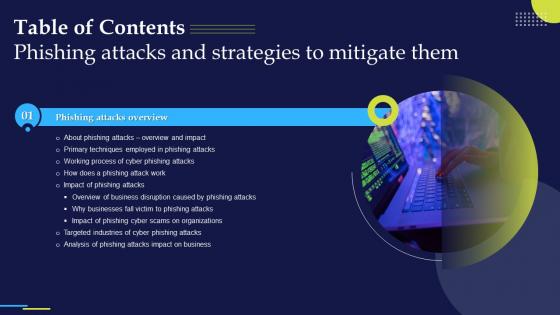 Phishing Attacks And Strategies To Mitigate Them Table Of Contents
Phishing Attacks And Strategies To Mitigate Them Table Of ContentsIntroducing Phishing Attacks And Strategies To Mitigate Them Table Of Contents to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks, Impact Business, Targeted Industries, using this template. Grab it now to reap its full benefits.
-
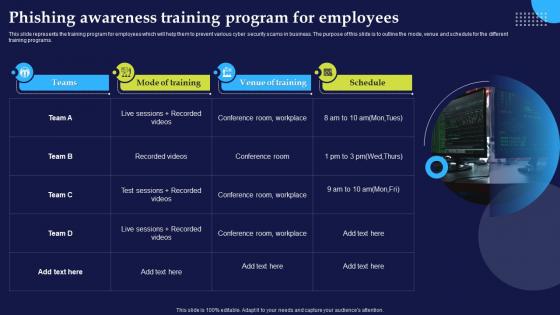 Phishing Awareness Training Program For Phishing Attacks And Strategies
Phishing Awareness Training Program For Phishing Attacks And StrategiesThis slide represents the training program for employees which will help them to prevent various cyber security scams in business. The purpose of this slide is to outline the mode, venue and schedule for the different training programs.Increase audience engagement and knowledge by dispensing information using Phishing Awareness Training Program For Phishing Attacks And Strategies. This template helps you present information on one stage. You can also present information on Venue Training, Conference Room, Model Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
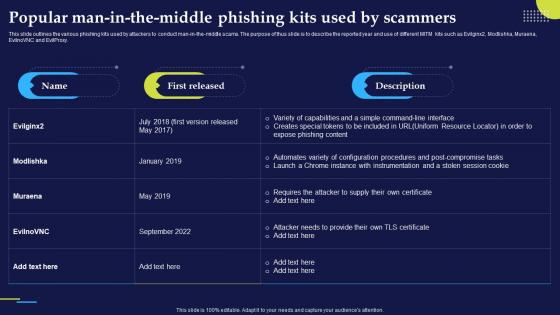 Popular Man In The Middle Phishing Kits Phishing Attacks And Strategies
Popular Man In The Middle Phishing Kits Phishing Attacks And StrategiesThis slide outlines the various phishing kits used by attackers to conduct man in the middle scams. The purpose of thus slide is to describe the reported year and use of different MITM kits such as Evilginx2, Modlishka, Muraena, EvilnoVNC and EvilProxy.Deliver an outstanding presentation on the topic using this Popular Man In The Middle Phishing Kits Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Instrumentation Stolen, Uniform Resource Locator, Expose Phishing Content using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
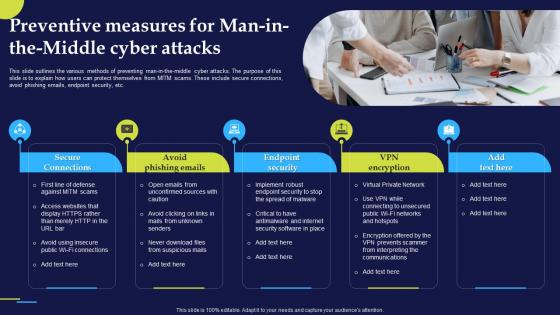 Preventive Measures For Man In The Middle Phishing Attacks And Strategies
Preventive Measures For Man In The Middle Phishing Attacks And StrategiesThis slide outlines the various methods of preventing man in the middle cyber attacks. The purpose of this slide is to explain how users can protect themselves from MITM scams. These include secure connections, avoid phishing emails, endpoint security, etc.Introducing Preventive Measures For Man In The Middle Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Secure Connections, Avoid Phishing Emails, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
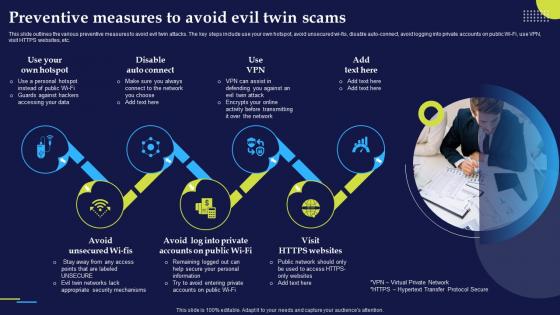 Preventive Measures To Avoid Evil Twin Scams Phishing Attacks And Strategies
Preventive Measures To Avoid Evil Twin Scams Phishing Attacks And StrategiesThis slide outlines the various preventive measures to avoid evil twin attacks. The key steps include use your own hotspot, avoid unsecured wi fis, disable auto connect, avoid logging into private accounts on public Wi Fi, use VPN, visit HTTPS websites, etc.Increase audience engagement and knowledge by dispensing information using Preventive Measures To Avoid Evil Twin Scams Phishing Attacks And Strategies. This template helps you present information on seven stages. You can also present information on Appropriate Security Mechanisms, Transfer Protocol Secure, Accessing Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
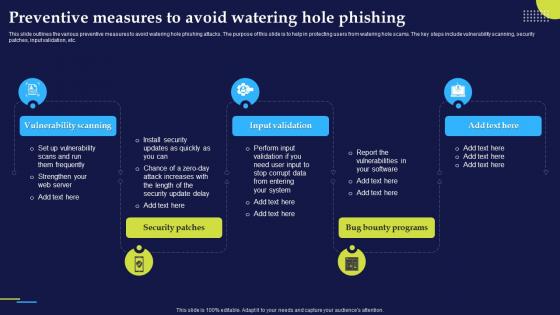 Preventive Measures To Avoid Watering Hole Phishing Attacks And Strategies
Preventive Measures To Avoid Watering Hole Phishing Attacks And StrategiesThis slide outlines the various preventive measures to avoid watering hole phishing attacks. The purpose of this slide is to help in protecting users from watering hole scams. The key steps include vulnerability scanning, security patches, input validation, etc.Introducing Preventive Measures To Avoid Watering Hole Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Scanning, Input Validation, Security Patches, using this template. Grab it now to reap its full benefits.
-
 Primary Techniques Employed In Phishing Attacks And Strategies
Primary Techniques Employed In Phishing Attacks And StrategiesThis slide demonstrates the ways utilized by phishers to attack victims. The purpose of this slide is to outline the different methods used by attackers to trick victims. The primary means of attacks are text messages, emails and phone calls from unknown sources.Increase audience engagement and knowledge by dispensing information using Primary Techniques Employed In Phishing Attacks And Strategies. This template helps you present information on five stages. You can also present information on Malicious Websites, Victims Receive, Personal Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Real World Examples Of Smishing Attacks Phishing Attacks And Strategies
Real World Examples Of Smishing Attacks Phishing Attacks And StrategiesThis slide demonstrates the real world example of smishing cyber attacks which targeted different individuals and organizations. The popular scams are early access apple iPhone 12 scam, USPS and FedEx scams and mandatory online COVID 19 test scam.Introducing Real World Examples Of Smishing Attacks Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Better Business, Information Services, Texts Displayed, using this template. Grab it now to reap its full benefits.
-
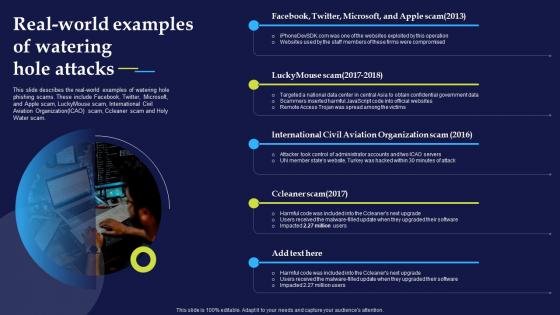 Real World Examples Of Watering Hole Attacks Phishing Attacks And Strategies
Real World Examples Of Watering Hole Attacks Phishing Attacks And StrategiesThis slide describes the real world examples of watering hole phishing scams. These include Facebook, Twitter, Microsoft, and Apple scam, LuckyMouse scam, International Civil Aviation OrganizationICAO scam, Ccleaner scam and Holy Water scam.Increase audience engagement and knowledge by dispensing information using Real World Examples Of Watering Hole Attacks Phishing Attacks And Strategies. This template helps you present information on one stage. You can also present information on Ccleaner Scam, International Civil Aviation, Luckymouse Scam using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
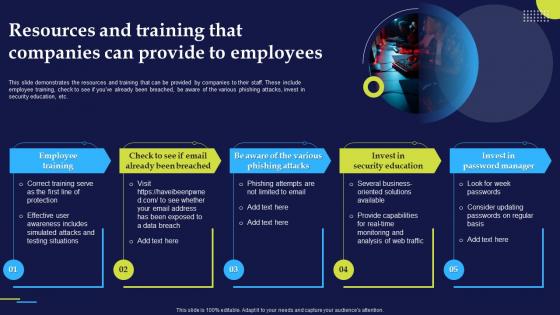 Resources And Training That Companies Can Phishing Attacks And Strategies
Resources And Training That Companies Can Phishing Attacks And StrategiesThis slide demonstrates the resources and training that can be provided by companies to their staff. These include employee training, check to see if you have already been breached, be aware of the various phishing attacks, invest in security education, etc.Introducing Resources And Training That Companies Can Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, Security Education, Password Manager, using this template. Grab it now to reap its full benefits.
-
 Roadmap To Secure Organizations From Phishing Attacks And Strategies
Roadmap To Secure Organizations From Phishing Attacks And StrategiesThis slide represents the roadmap to prevent phishing attacks in organizations. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc.Increase audience engagement and knowledge by dispensing information using Roadmap To Secure Organizations From Phishing Attacks And Strategies. This template helps you present information on five stages. You can also present information on Security Assessment, Technical Controls, Employee Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
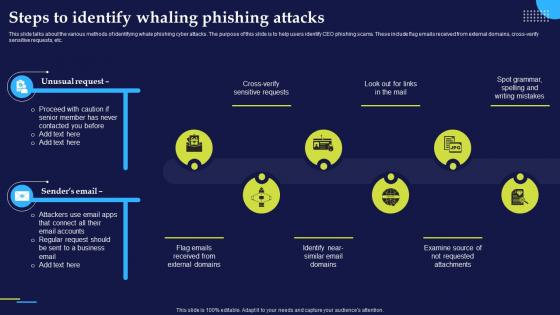 Steps To Identify Whaling Phishing Attacks Phishing Attacks And Strategies
Steps To Identify Whaling Phishing Attacks Phishing Attacks And StrategiesThis slide talks about the various methods of identifying whale phishing cyber attacks. The purpose of this slide is to help users identify CEO phishing scams. These include flag emails received from external domains, cross verify sensitive requests, etc.Introducing Steps To Identify Whaling Phishing Attacks Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Requested Attachments, External Domains, Sent Business, using this template. Grab it now to reap its full benefits.
-
 Steps To Take After Clicking Spear Phishing Link Phishing Attacks And Strategies
Steps To Take After Clicking Spear Phishing Link Phishing Attacks And StrategiesThis slide illustrates the steps to be taken immediately after falling for a spear phishing scam. The purpose of this slide is to outline the various steps such as disconnect from internet, backup your files, change your passwords and conduct a hardware scan.Increase audience engagement and knowledge by dispensing information using Steps To Take After Clicking Spear Phishing Link Phishing Attacks And Strategies. This template helps you present information on four stages. You can also present information on Two Factor Authentication, Data Immediately, Ethernet Cable using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
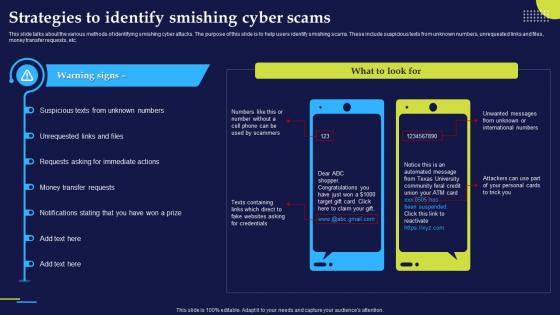 Strategies To Identify Smishing Cyber Scams Phishing Attacks And Strategies
Strategies To Identify Smishing Cyber Scams Phishing Attacks And StrategiesThis slide talks about the various methods of identifying smishing cyber attacks. The purpose of this slide is to help users identify smishing scams. These include suspicious texts from unknown numbers, unrequested links and files, money transfer requests, etc.Present the topic in a bit more detail with this Strategies To Identify Smishing Cyber Scams Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Requests Asking, Transfer Requests, Notifications Stating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
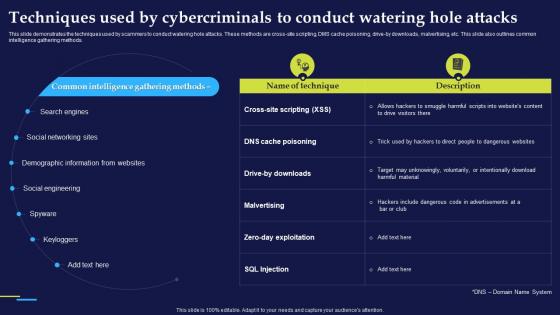 Techniques Used By Cybercriminals To Conduct Phishing Attacks And Strategies
Techniques Used By Cybercriminals To Conduct Phishing Attacks And StrategiesThis slide demonstrates the techniques used by scammers to conduct watering hole attacks. These methods are cross site scripting, DMS cache poisoning, drive by downloads, malvertising, etc. This slide also outlines common intelligence gathering methods.Deliver an outstanding presentation on the topic using this Techniques Used By Cybercriminals To Conduct Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Demographic Information, Social Engineering, Include Dangerous using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
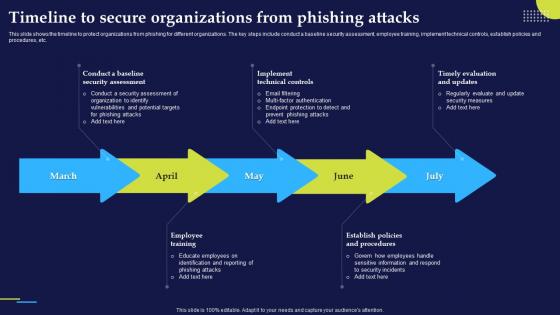 Timeline To Secure Organizations From Phishing Attacks And Strategies
Timeline To Secure Organizations From Phishing Attacks And StrategiesThis slide shows the timeline to protect organizations from phishing for different organizations. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc.Increase audience engagement and knowledge by dispensing information using Timeline To Secure Organizations From Phishing Attacks And Strategies. This template helps you present information on five stages. You can also present information on Security Assessment, Technical Controls, Educate Employees using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tools Provided By Google To Prevent Phishing Attacks And Strategies
Tools Provided By Google To Prevent Phishing Attacks And StrategiesThis slide demonstrates the different tools provided by Google to prevent and report cyber phishing scams. These include to spot phishing mails with the help of Gmail, utilize safe browsing in chrome, look for unsafe saved passwords, password alert for chrome, etc.Deliver an outstanding presentation on the topic using this Tools Provided By Google To Prevent Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Saved Passwords, Notifications Concerning, Ever Compromised using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tricks Employed By Malicious Websites To Phishing Attacks And Strategies
Tricks Employed By Malicious Websites To Phishing Attacks And StrategiesThis slide talks about various tricks utilized by fraudulent websites to scam the visitors. The purpose of this slide is to make users aware of such different tricks such as freeordiscount offers, low interest ratesorfree credit cards, employment opportunities, etc.Introducing Tricks Employed By Malicious Websites To Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Fictitious Businesses, Feel Emergency, Emergency Warnings, using this template. Grab it now to reap its full benefits.
-
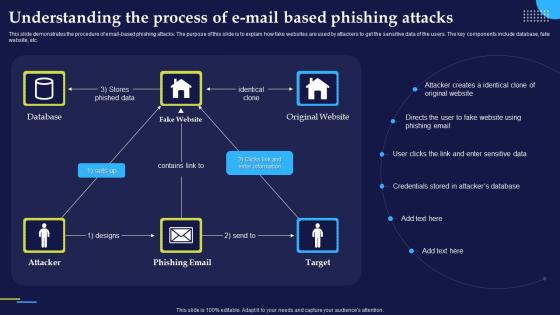 Understanding The Process Of E Mail Based Phishing Attacks And Strategies
Understanding The Process Of E Mail Based Phishing Attacks And StrategiesThis slide demonstrates the procedure of email based phishing attacks. The purpose of this slide is to explain how fake websites are used by attackers to get the sensitive data of the users. The key components include database, fake website, etc.Present the topic in a bit more detail with this Understanding The Process Of E Mail Based Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Enter Sensitive, Credentials Stored, Attacker Creates. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vishing Attacks Prevention Email Signing phishing Attacks And Strategies
Vishing Attacks Prevention Email Signing phishing Attacks And StrategiesThis slide talks about the techniques which can help in protecting organizations from phishing and vishing attacks. The purpose of this slide is to explain two important methods of preventing cyber scams. These techniques are email signing and code signing.Deliver an outstanding presentation on the topic using this Vishing Attacks Prevention Email Signing phishing Attacks And Strategies. Dispense information and present a thorough explanation of Malicious Software, Code Signing, Code Signing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
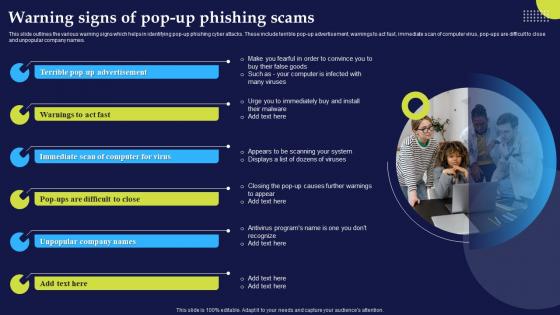 Warning Signs Of Pop Up Phishing Scams Phishing Attacks And Strategies
Warning Signs Of Pop Up Phishing Scams Phishing Attacks And StrategiesThis slide outlines the various warning signs which helps in identifying pop up phishing cyber attacks. These include terrible pop up advertisement, warnings to act fast, immediate scan of computer virus, pop ups are difficult to close and unpopular company names.Increase audience engagement and knowledge by dispensing information using Warning Signs Of Pop Up Phishing Scams Phishing Attacks And Strategies. This template helps you present information on five stages. You can also present information on Unpopular Company, Immediate Scan, Warnings Act Fast using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Warning Signs To Recognize Phishing Email Phishing Attacks And Strategies
Warning Signs To Recognize Phishing Email Phishing Attacks And StrategiesThis slide talks about the warning signs that can help the user to recognize phishing email. The purpose of this slide is to outline the signs of phishing mails such as no greeting, misleading hyperlinks, unauthorized attachments, spelling and grammatical errors, etc.Deliver an outstanding presentation on the topic using this Warning Signs To Recognize Phishing Email Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Information Immediately, Unauthorised Attachments, Generic Greeting using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Why Businesses Fall Victim To Phishing Attacks Phishing Attacks And Strategies
Why Businesses Fall Victim To Phishing Attacks Phishing Attacks And StrategiesThis slide outlines the various reasons responsible for businesses to fall victim to different phishing attacks. These include inadequate employee training, never evaluate the success of the training, careless browsing habits of the employees, etc.Introducing Why Businesses Fall Victim To Phishing Attacks Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Careless Browsing, Policy Improvement, Inadequate Employee Training, using this template. Grab it now to reap its full benefits.
-
 Working Of Phishing Training Programs Phishing Attacks And Strategies
Working Of Phishing Training Programs Phishing Attacks And StrategiesThis slide demonstrates the working of phishing training programs for organizations. These include start with employee training, make fictitious phishing campaigns, reinforce the phishing awareness training and track progress and upgrade.Increase audience engagement and knowledge by dispensing information using Working Of Phishing Training Programs Phishing Attacks And Strategies. This template helps you present information on four stages. You can also present information on Employee Training, Phishing Campaigns, Awareness Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Working Of Watering Hole Phishing Attack Phishing Attacks And Strategies
Working Of Watering Hole Phishing Attack Phishing Attacks And StrategiesThis slide represents the working process of watering hole phishing attacks. The purpose of this slide is to illustrate the flow diagram of watering hole phishing scams. The key points include research and identification, analysis, preparation and execution.Introducing Working Of Watering Hole Phishing Attack Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Watering Hole Cyberattack, Employ Exploit, Subdomain Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
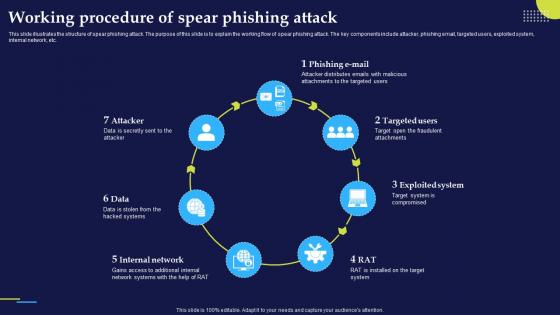 Working Procedure Of Spear Phishing Attack Phishing Attacks And Strategies
Working Procedure Of Spear Phishing Attack Phishing Attacks And StrategiesThis slide illustrates the structure of spear phishing attack. The purpose of this slide is to explain the working flow of spear phishing attack. The key components include attacker, phishing email, targeted users, exploited system, internal network, etc.Increase audience engagement and knowledge by dispensing information using Working Procedure Of Spear Phishing Attack Phishing Attacks And Strategies. This template helps you present information on seven stages. You can also present information on Attacker Distributes, Attachments Targeted, Fraudulent Attachments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Working Process Of Cyber Phishing Attacks Phishing Attacks And Strategies
Working Process Of Cyber Phishing Attacks Phishing Attacks And StrategiesThis slide talks about the implementation and working of phishing attacks. The purpose of this slide is to explain how are cyber phishing scams conducted. The components include hacker, phishing mail, target, phishing website and original website.Introducing Working Process Of Cyber Phishing Attacks Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information Website, Hacker Access Private, Credentials Victim, using this template. Grab it now to reap its full benefits.
-
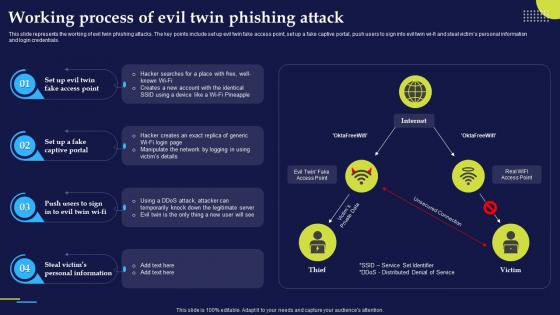 Working Process Of Evil Twin Phishing Attack Phishing Attacks And Strategies
Working Process Of Evil Twin Phishing Attack Phishing Attacks And StrategiesThis slide represents the working of evil twin phishing attacks. The key points include set up evil twin fake access point, set up a fake captive portal, push users to sign into evil twin wi fi and steal victims personal information and login credentials.Deliver an outstanding presentation on the topic using this Working Process Of Evil Twin Phishing Attack Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Personal Information, Captive Portal, Manipulate Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Measures For Successful Phishing Awareness Phishing Attacks And Strategies
Measures For Successful Phishing Awareness Phishing Attacks And StrategiesThis slide talks about the measures for successful phishing awareness campaign. These include recognize phish, train staff while keeping their individual needs in mind, action oriented employee engagement, plan constant training sessions, etc.Increase audience engagement and knowledge by dispensing information using Measures For Successful Phishing Awareness Phishing Attacks And Strategies. This template helps you present information on six stages. You can also present information on Employee Engagement, Interested Awareness Training, Training Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Phishing Social Engineering In Powerpoint And Google Slides Cpb
Phishing Social Engineering In Powerpoint And Google Slides CpbPresenting our Phishing Social Engineering In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Phishing Social Engineering This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Email Based Phishing Attacks Prevention IT Illustration
Email Based Phishing Attacks Prevention IT IllustrationThis colored PowerPoint Illustration provides a comprehensive overview of email-based phishing attacks and how to prevent them. It covers topics such as identifying suspicious emails, understanding phishing tactics, and implementing security measures.
-
 General ledger auto banker business leaders spear phishing
General ledger auto banker business leaders spear phishingPresenting this set of slides with name - General Ledger Auto Banker Business Leaders Spear Phishing. This is an editable four graphic that deals with topics like General Ledger, Auto Banker, Business Leaders, Spear Phishing to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
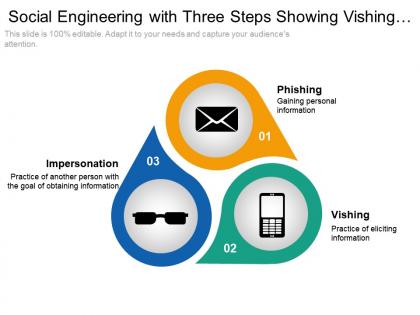 Social engineering with three steps showing vishing phishing and impersonation
Social engineering with three steps showing vishing phishing and impersonationPresenting this set of slides with name - Social Engineering With Three Steps Showing Vishing Phishing And Impersonation. This is a three stage process. The stages in this process are Social Engineering, Information Security, Psychological Manipulation.
-
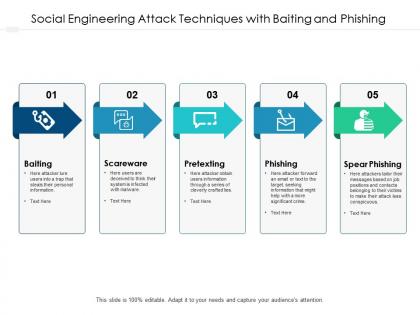 Social engineering attack techniques with baiting and phishing
Social engineering attack techniques with baiting and phishingPresenting this set of slides with name Social Engineering Attack Techniques With Baiting And Phishing. This is a five process. The stages in this process are stages Social Engineering, Technology, Social, Network. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Phishing security awareness ppt powerpoint presentation pictures demonstration cpb
Phishing security awareness ppt powerpoint presentation pictures demonstration cpbPresenting this set of slides with name Phishing Security Awareness Ppt Powerpoint Presentation Pictures Demonstration Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Phishing Security Awareness to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
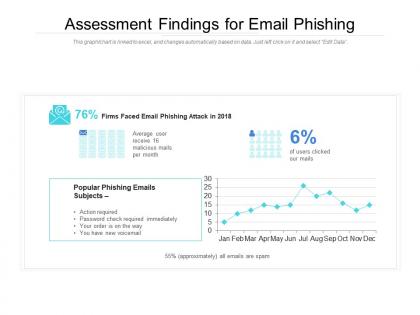 Assessment findings for email phishing
Assessment findings for email phishingPresenting this set of slides with name Assessment Findings For Email Phishing. The topics discussed in these slides are Assessment Findings For Email Phishing. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Urgent care services e mail phishing ppt powerpoint presentation portfolio clipart images cpb
Urgent care services e mail phishing ppt powerpoint presentation portfolio clipart images cpbPresenting this set of slides with name Urgent Care Services E Mail Phishing Ppt Powerpoint Presentation Portfolio Clipart Images Cpb. This is an editable Powerpoint seven stages graphic that deals with topics like Urgent Care Services E Mail Phishing to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Spear phishing vs phishing ppt powerpoint presentation infographics icons cpb
Spear phishing vs phishing ppt powerpoint presentation infographics icons cpbPresenting this set of slides with name Spear Phishing Vs Phishing Ppt Powerpoint Presentation Infographics Icons Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Spear Phishing Vs Phishing to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Resell phishing protection ppt powerpoint presentation pictures show cpb
Resell phishing protection ppt powerpoint presentation pictures show cpbPresenting this set of slides with name Resell Phishing Protection Ppt Powerpoint Presentation Pictures Show Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Resell Phishing Protection to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Employee phishing awareness training ppt powerpoint presentation file inspiration cpb
Employee phishing awareness training ppt powerpoint presentation file inspiration cpbPresenting this set of slides with name Employee Phishing Awareness Training Ppt Powerpoint Presentation File Inspiration Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Employee Phishing Awareness Training to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.



